Security Assertion Markup Language An Introduction to SAML
- Slides: 25
Security Assertion Markup Language An Introduction to SAML 2. 0 Tom Scavo trscavo@ncsa. uiuc. edu NCSA saml-v 2_0 -intro-dec 05 1
Prerequisites • Familiarity with SAML 1. 1 is assumed • J. Hughes et al. Technical Overview of the OASIS Security Assertion Markup Language (SAML) V 1. 1. OASIS, May 2004. Document ID sstc-saml-techoverview-1. 1 -cd • SAML on Wikipedia http: //en. wikipedia. org/wiki/SAML saml-v 2_0 -intro-dec 05 2
SAML 2. 0 Background • SAML 2. 0 became an OASIS standard in Mar 2005 • Some 30 individuals were involved with the creation of this specification • Project Liberty donated its ID-FF spec to OASIS, which became the basis of SAML 2. 0 saml-v 2_0 -intro-dec 05 3
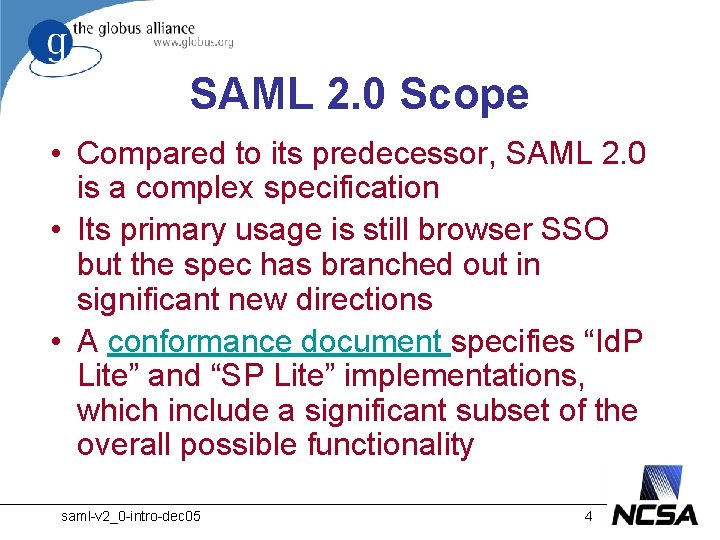
SAML 2. 0 Scope • Compared to its predecessor, SAML 2. 0 is a complex specification • Its primary usage is still browser SSO but the spec has branched out in significant new directions • A conformance document specifies “Id. P Lite” and “SP Lite” implementations, which include a significant subset of the overall possible functionality saml-v 2_0 -intro-dec 05 4
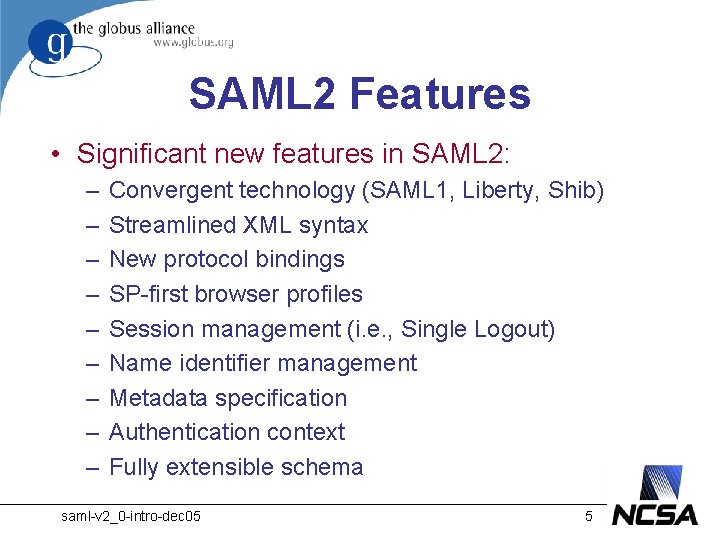
SAML 2 Features • Significant new features in SAML 2: – – – – – Convergent technology (SAML 1, Liberty, Shib) Streamlined XML syntax New protocol bindings SP-first browser profiles Session management (i. e. , Single Logout) Name identifier management Metadata specification Authentication context Fully extensible schema saml-v 2_0 -intro-dec 05 5
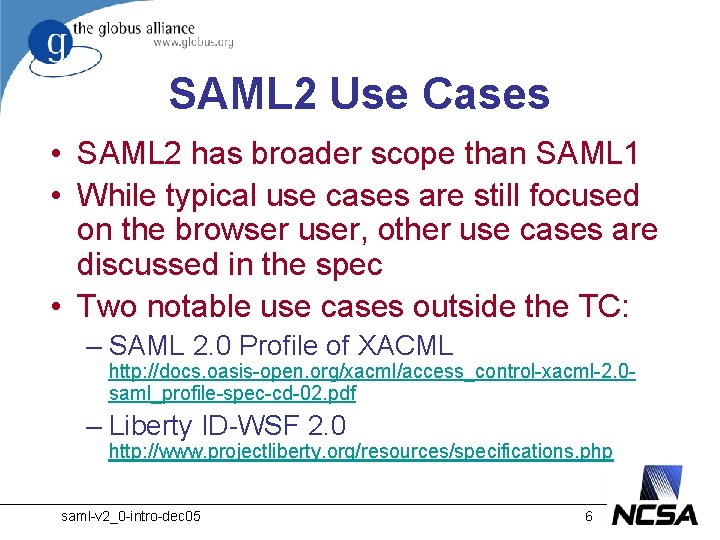
SAML 2 Use Cases • SAML 2 has broader scope than SAML 1 • While typical use cases are still focused on the browser user, other use cases are discussed in the spec • Two notable use cases outside the TC: – SAML 2. 0 Profile of XACML http: //docs. oasis-open. org/xacml/access_control-xacml-2. 0 saml_profile-spec-cd-02. pdf – Liberty ID-WSF 2. 0 http: //www. projectliberty. org/resources/specifications. php saml-v 2_0 -intro-dec 05 6
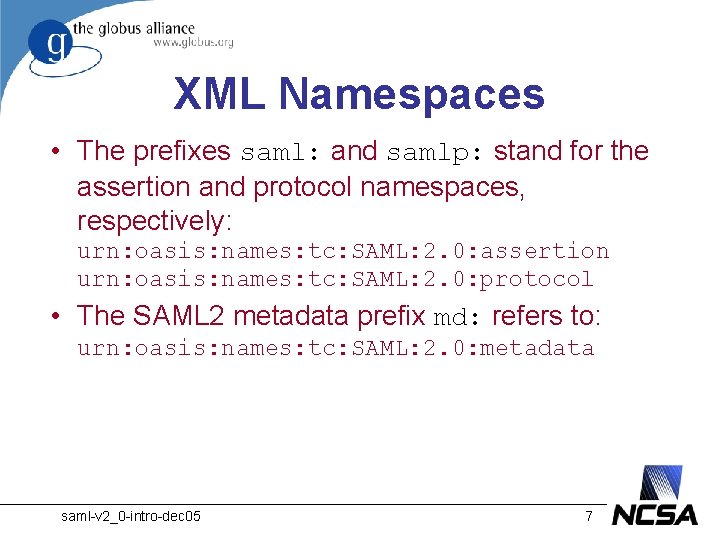
XML Namespaces • The prefixes saml: and samlp: stand for the assertion and protocol namespaces, respectively: urn: oasis: names: tc: SAML: 2. 0: assertion urn: oasis: names: tc: SAML: 2. 0: protocol • The SAML 2 metadata prefix md: refers to: urn: oasis: names: tc: SAML: 2. 0: metadata saml-v 2_0 -intro-dec 05 7
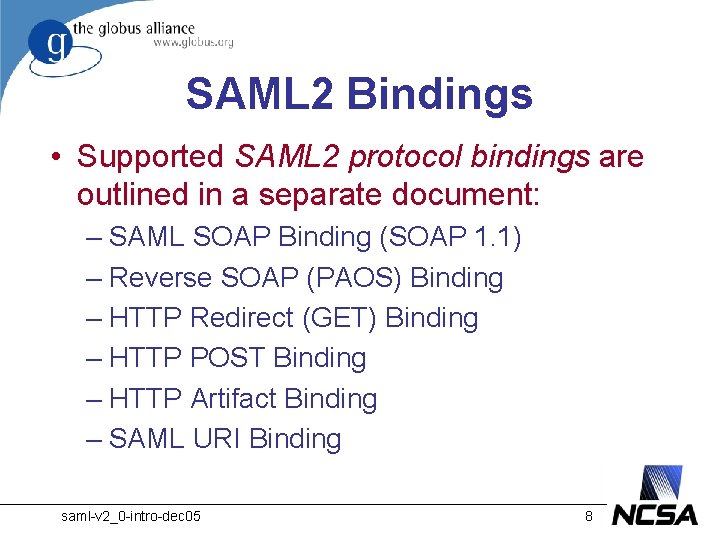
SAML 2 Bindings • Supported SAML 2 protocol bindings are outlined in a separate document: – SAML SOAP Binding (SOAP 1. 1) – Reverse SOAP (PAOS) Binding – HTTP Redirect (GET) Binding – HTTP POST Binding – HTTP Artifact Binding – SAML URI Binding saml-v 2_0 -intro-dec 05 8
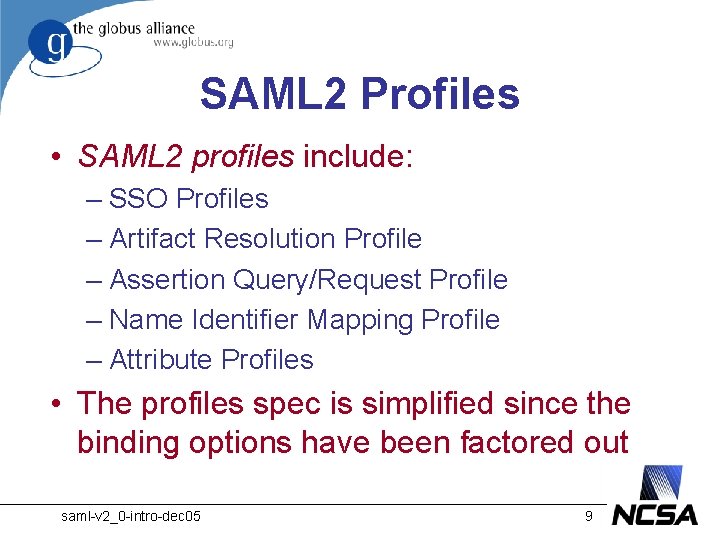
SAML 2 Profiles • SAML 2 profiles include: – SSO Profiles – Artifact Resolution Profile – Assertion Query/Request Profile – Name Identifier Mapping Profile – Attribute Profiles • The profiles spec is simplified since the binding options have been factored out saml-v 2_0 -intro-dec 05 9
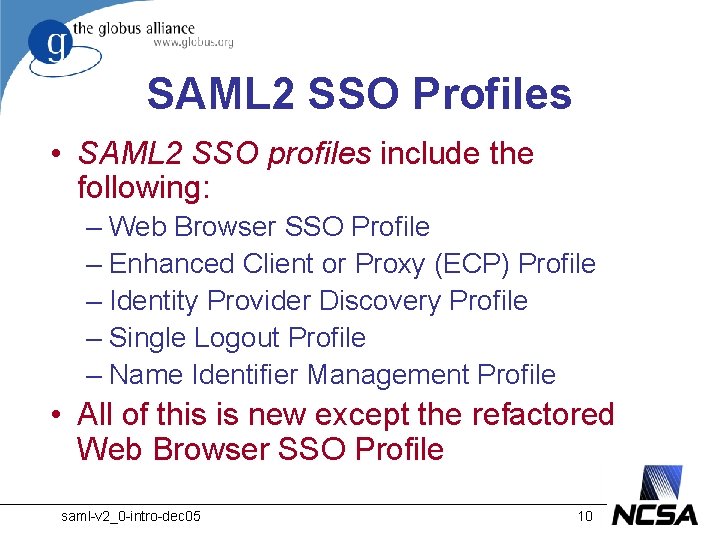
SAML 2 SSO Profiles • SAML 2 SSO profiles include the following: – Web Browser SSO Profile – Enhanced Client or Proxy (ECP) Profile – Identity Provider Discovery Profile – Single Logout Profile – Name Identifier Management Profile • All of this is new except the refactored Web Browser SSO Profile saml-v 2_0 -intro-dec 05 10
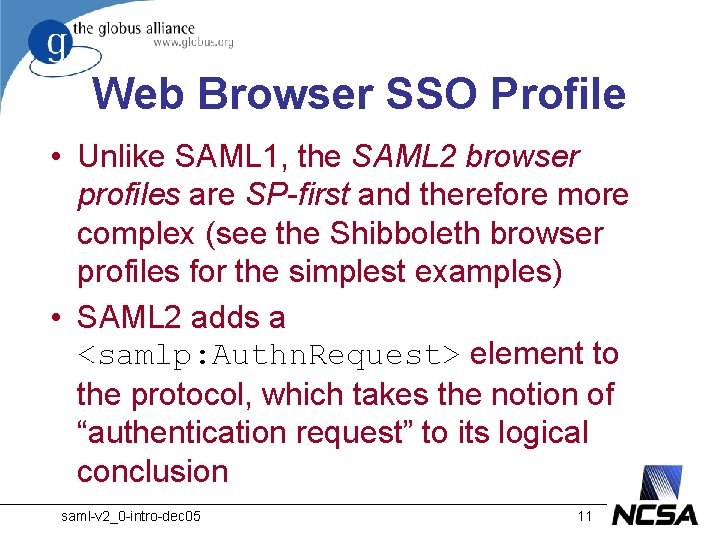
Web Browser SSO Profile • Unlike SAML 1, the SAML 2 browser profiles are SP-first and therefore more complex (see the Shibboleth browser profiles for the simplest examples) • SAML 2 adds a <samlp: Authn. Request> element to the protocol, which takes the notion of “authentication request” to its logical conclusion saml-v 2_0 -intro-dec 05 11
Browser Profile Examples • In SAML 2, the Browser SSO Profile is specified in very general terms • An implementation is free to choose any combination of bindings, which leads to some interesting variations • We’ll give just two examples here: – SAML 2 version of SAML 1 Browser/POST – SAML 2 Browser/Artifact with a “double artifact” binding saml-v 2_0 -intro-dec 05 12
Browser/POST Profile • A SAML 2. 0 Browser/POST Profile (others are possible) consists of eight steps: 1. 2. 3. 4. 5. 6. 7. 8. Request the target resource [SP] Redirect to the Single Sign-on (SSO) Service Request the SSO Service [Id. P] Respond with an HTML form Request the Assertion Consumer Service [SP] Redirect to the target resource Request the target resource again [SP] Respond with the requested resource saml-v 2_0 -intro-dec 05 13
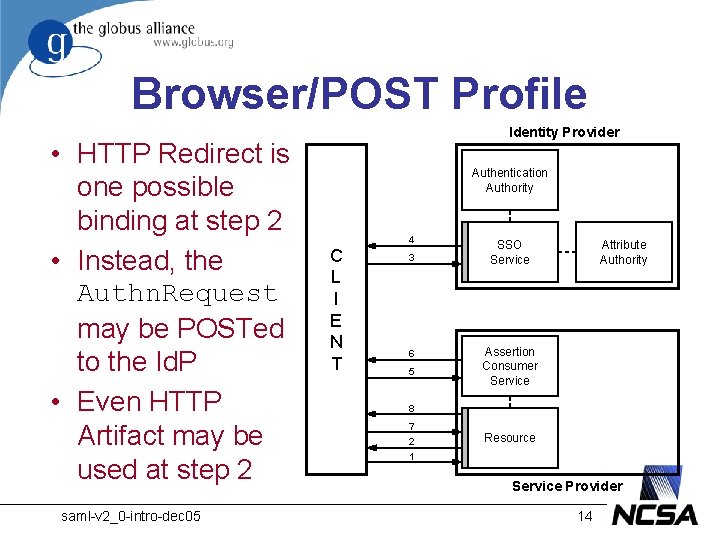
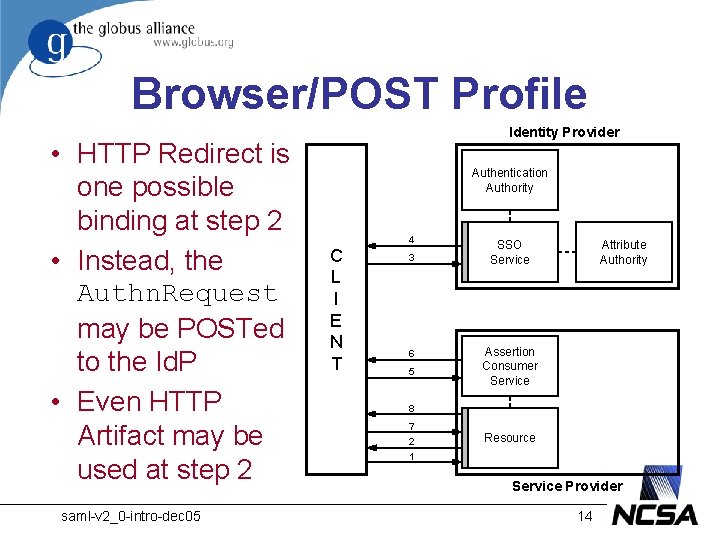
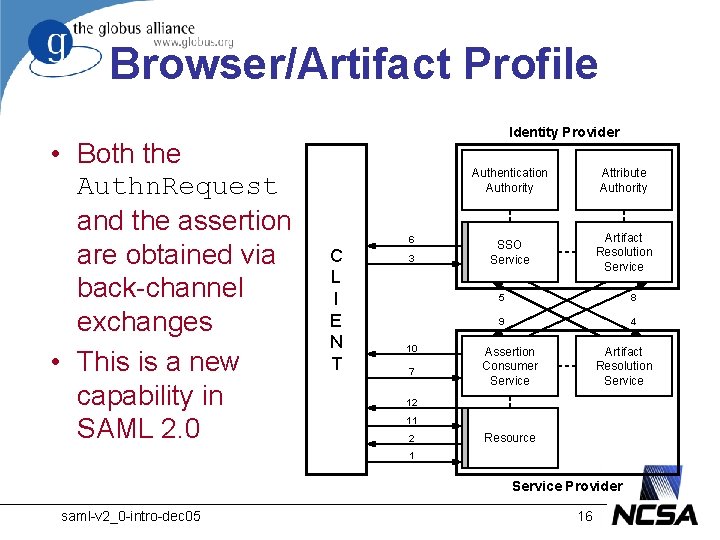
Browser/POST Profile • HTTP Redirect is one possible binding at step 2 • Instead, the Authn. Request may be POSTed to the Id. P • Even HTTP Artifact may be used at step 2 saml-v 2_0 -intro-dec 05 Identity Provider Authentication Authority 4 C L I E N T 3 6 5 SSO Service Attribute Authority Assertion Consumer Service 8 7 2 1 Resource Service Provider 14
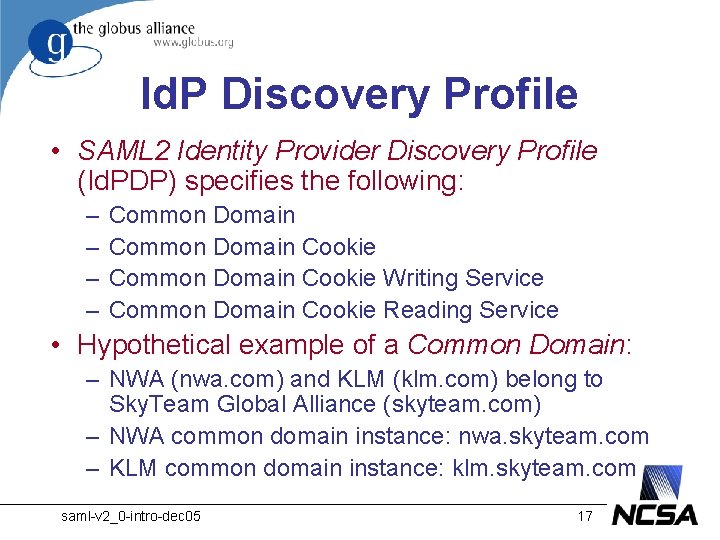
Browser/Artifact Profile • A SAML 2 Browser/Artifact Profile with 12 steps: 1. 2. 3. 4. 5. 6. 7. 8. 9. 10. 11. 12. Request the target resource [SP] Redirect to the Single Sign-on (SSO) Service Request the SSO Service [Id. P] Request the Artifact Resolution Service [SP] Respond with a SAML Authn. Request Redirect to the Assertion Consumer Service Request the Assertion Consumer Service [SP] Request the Artifact Resolution Service [Id. P] Respond with a SAML Assertion Redirect to the target resource Request the target resource again [SP] Respond with the requested resource saml-v 2_0 -intro-dec 05 15
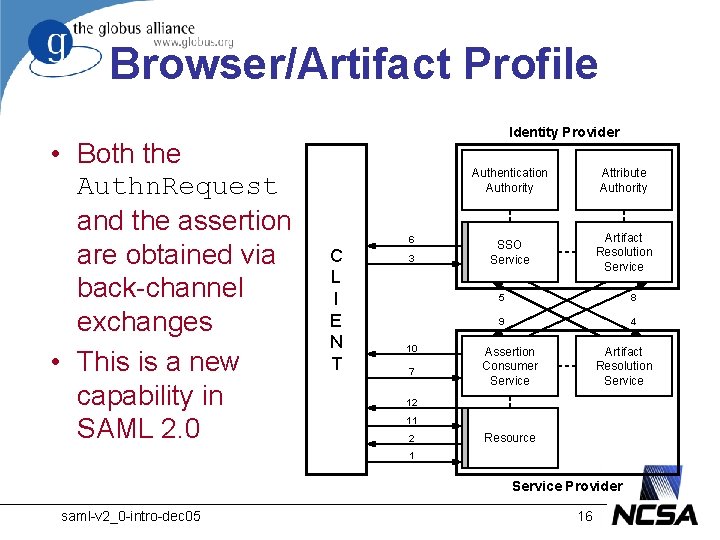
Browser/Artifact Profile • Both the Authn. Request and the assertion are obtained via back-channel exchanges • This is a new capability in SAML 2. 0 Identity Provider 6 C L I E N T 3 10 7 Authentication Authority Attribute Authority SSO Service Artifact Resolution Service 5 8 9 4 Assertion Consumer Service Artifact Resolution Service 12 11 2 Resource 1 Service Provider saml-v 2_0 -intro-dec 05 16
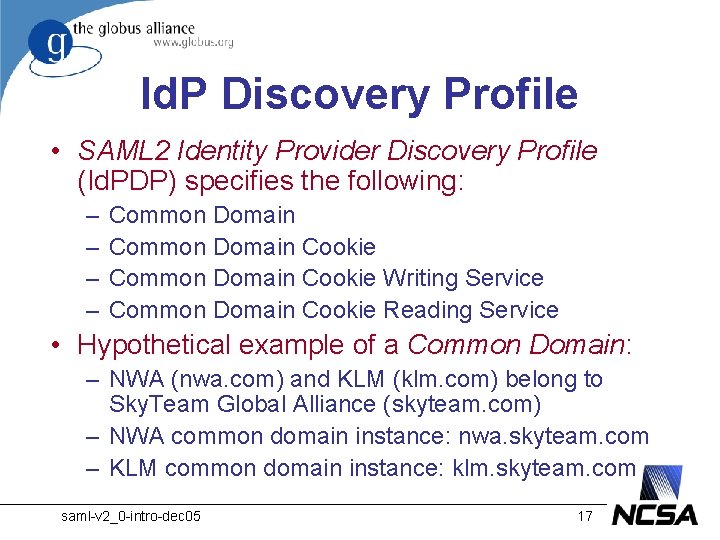
Id. P Discovery Profile • SAML 2 Identity Provider Discovery Profile (Id. PDP) specifies the following: – – Common Domain Cookie Writing Service Common Domain Cookie Reading Service • Hypothetical example of a Common Domain: – NWA (nwa. com) and KLM (klm. com) belong to Sky. Team Global Alliance (skyteam. com) – NWA common domain instance: nwa. skyteam. com – KLM common domain instance: klm. skyteam. com saml-v 2_0 -intro-dec 05 17
Id. P Discovery Profile (cont’d) • Common Domain Cookie – Stores a history list of recently visited Id. Ps • Common Domain Cookie Writing Service – The Id. P requests this service after a successful authn event • Common Domain Cookie Reading Service – The SP requests this service to discover the user's most recently used Id. P saml-v 2_0 -intro-dec 05 18
Single Logout Profile • Like Liberty, SAML 2 specifies a Single Logout (SLO) Profile • SLO requires session management capability • SLO is complicated, requiring significant new functionality in a conforming implementation saml-v 2_0 -intro-dec 05 19
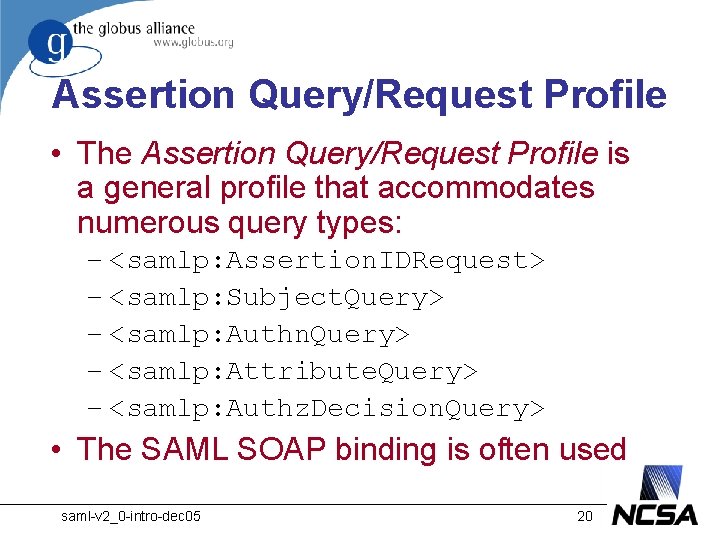
Assertion Query/Request Profile • The Assertion Query/Request Profile is a general profile that accommodates numerous query types: – <samlp: Assertion. IDRequest> – <samlp: Subject. Query> – <samlp: Authn. Query> – <samlp: Attribute. Query> – <samlp: Authz. Decision. Query> • The SAML SOAP binding is often used saml-v 2_0 -intro-dec 05 20
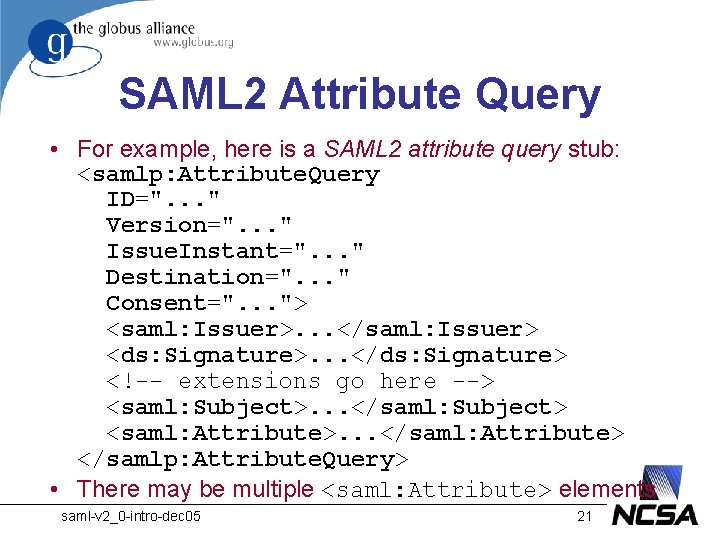
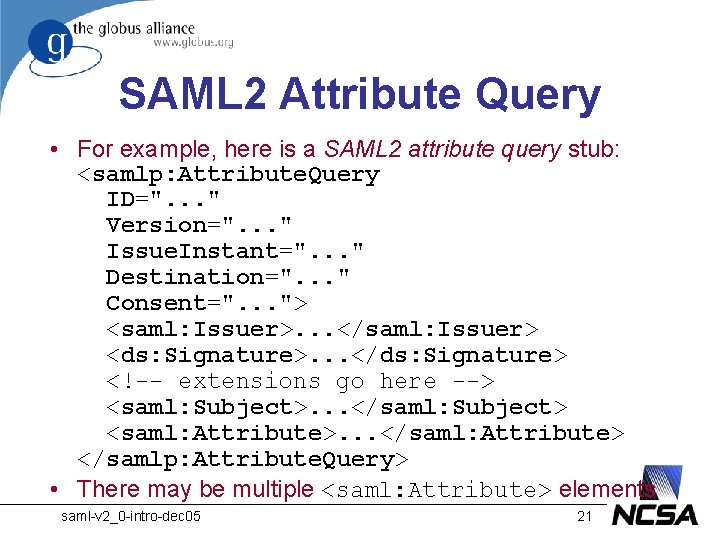
SAML 2 Attribute Query • For example, here is a SAML 2 attribute query stub: <samlp: Attribute. Query ID=". . . " Version=". . . " Issue. Instant=". . . " Destination=". . . " Consent=". . . "> <saml: Issuer>. . . </saml: Issuer> <ds: Signature>. . . </ds: Signature> <!-- extensions go here --> <saml: Subject>. . . </saml: Subject> <saml: Attribute>. . . </saml: Attribute> </samlp: Attribute. Query> • There may be multiple <saml: Attribute> elements saml-v 2_0 -intro-dec 05 21
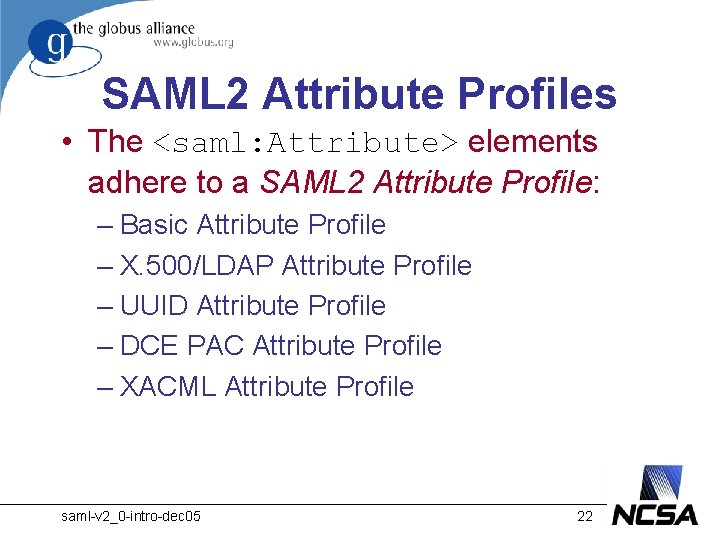
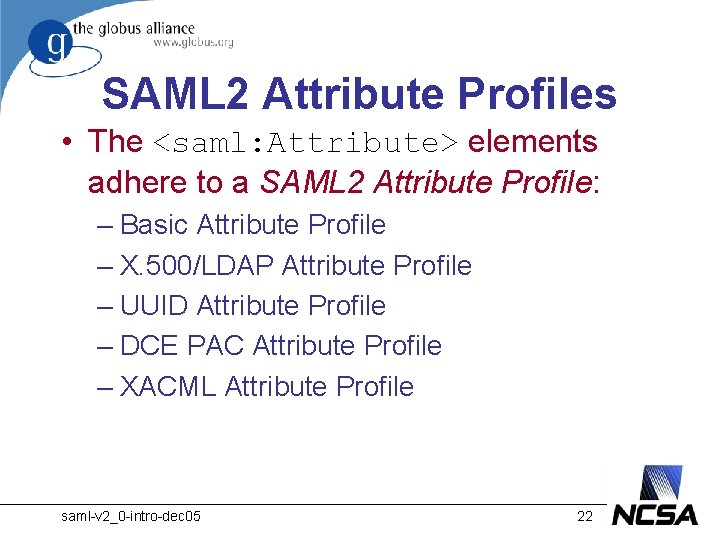
SAML 2 Attribute Profiles • The <saml: Attribute> elements adhere to a SAML 2 Attribute Profile: – Basic Attribute Profile – X. 500/LDAP Attribute Profile – UUID Attribute Profile – DCE PAC Attribute Profile – XACML Attribute Profile saml-v 2_0 -intro-dec 05 22
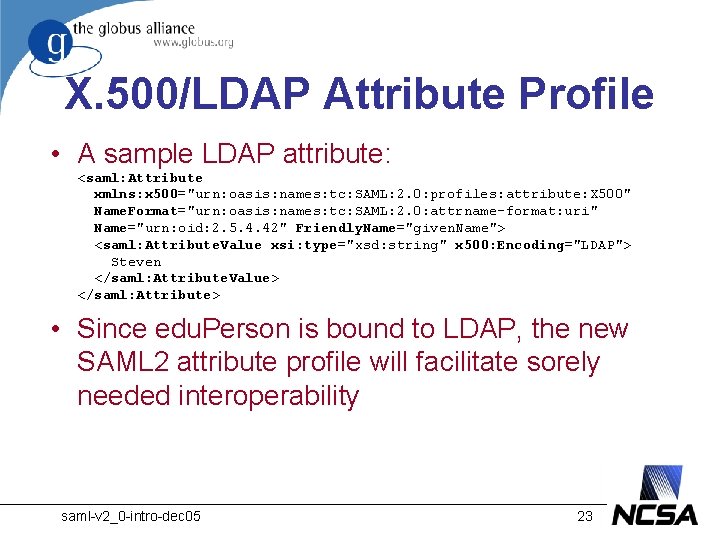
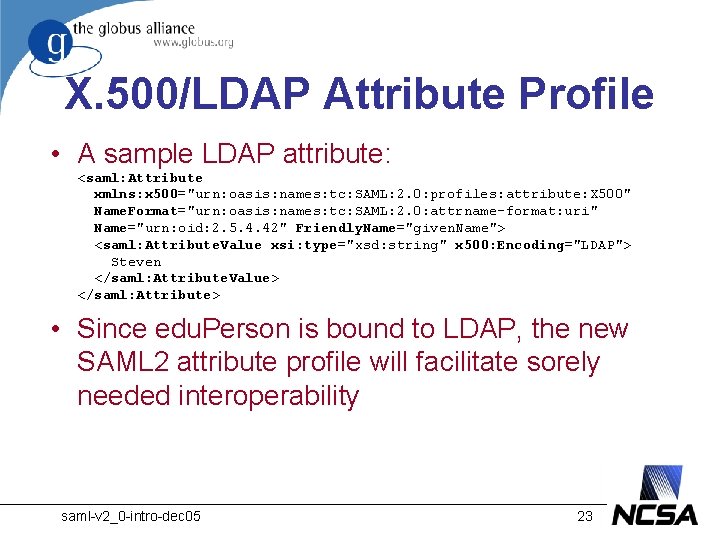
X. 500/LDAP Attribute Profile • A sample LDAP attribute: <saml: Attribute xmlns: x 500="urn: oasis: names: tc: SAML: 2. 0: profiles: attribute: X 500" Name. Format="urn: oasis: names: tc: SAML: 2. 0: attrname-format: uri" Name="urn: oid: 2. 5. 4. 42" Friendly. Name="given. Name"> <saml: Attribute. Value xsi: type="xsd: string" x 500: Encoding="LDAP"> Steven </saml: Attribute. Value> </saml: Attribute> • Since edu. Person is bound to LDAP, the new SAML 2 attribute profile will facilitate sorely needed interoperability saml-v 2_0 -intro-dec 05 23
Metadata Specification • Metadata standards are important for interoperability • SAML 2 specifies a significant metadata framework, which is completely new • Many of the metadata elements have already filtered down into SAML 1 and Shibboleth saml-v 2_0 -intro-dec 05 24
Authentication Context • The Authentication. Method attribute in SAML 1. 1 is replaced by an authentication context in SAML 2. 0 • The authn context formalism is very general, but numerous predefined classes (25 in fact) have been included to make it easier to use saml-v 2_0 -intro-dec 05 25