Public Key Crypto RSA CSCI 284 Spring 2009
- Public Key Crypto - RSA CSCI 284 Spring 2009 GWU Sections 5. 1, 5. 2. 2, 5. 3 CS 284 -162/Spring 09/GWU/Vora/RSA
How does Alice send Bob the decryption key in private key crypto? • If Alice wants it such that anyone can decrypt her messages, but know that they came from her – Suppose she could make the decryption key available in a public place – This would require that the decryption key should not give any information on the encryption key, in particular it should not be equal to it 12/24/2021 CS 284 -162/Spring 09/GWU/Vora/RSA 2
How does Alice send Bob the decryption key in private key crypto? contd • If she wants it so that only Bob can read her messages, and Bob is ok with anyone sending him messages in this way – Suppose Bob makes his encryption key available publicly – No one should be able to compute the decryption key from the encryption key – This is the dual of the previous case 12/24/2021 CS 284 -162/Spring 09/GWU/Vora/RSA 3
Public Key Cryptography Two injective functions f and g such that fg=I i. e. messages encrypted with one can be decrypted with the other; functions include association with key f cannot be used to find g and vice versa One is made public, the other kept private Encryption with public function provides confidential transmission, decryption with public function provides authentication 12/24/2021 CS 284 -162/Spring 09/GWU/Vora/RSA 4
One-way function A one-way function is easy in the forward direction, difficult in the reverse direction. Example: f(x) = xa mod m 12/24/2021 CS 284 -162/Spring 09/GWU/Vora/RSA 5
Trapdoor One-way Function A trapdoor one-way function is easy in the reverse direction for someone with access to a trapdoor (secret information enabling easy inversion). Example: if f(x) = xa mod m where gcd(a, (m)) = 1, and (m) = pq for primes p and q, knowledge of p or q is a trapdoor 12/24/2021 CS 284 -162/Spring 09/GWU/Vora/RSA 6
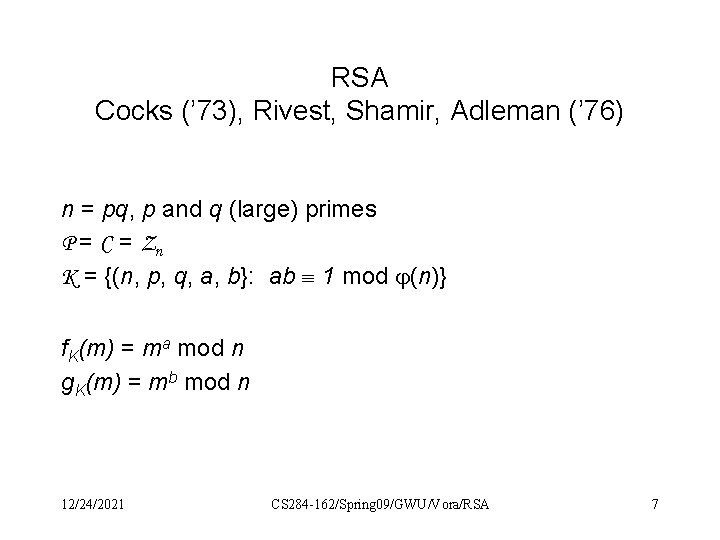
RSA Cocks (’ 73), Rivest, Shamir, Adleman (’ 76) n = pq, p and q (large) primes P = C = Zn K = {(n, p, q, a, b}: ab 1 mod (n)} f. K(m) = ma mod n g. K(m) = mb mod n 12/24/2021 CS 284 -162/Spring 09/GWU/Vora/RSA 7
RSA: Key generation Find p and q (two large random primes) n pq (n) (p-1)(q-1) Choose random a invertible mod (n) s. t 1 < a < (n) i. e. a s. t gcd(a, (n)) = 1 Use Euclidean algorithm to find b=a-1 mod (n) Not known how to determine (n) without p and q One key: (n, a) other key (n, b) 12/24/2021 CS 284 -162/Spring 09/GWU/Vora/RSA 8
Example 12/24/2021 CS 284 -162/Spring 09/GWU/Vora/RSA 9
A Trapdoor One-way Function? • RSA encryption is believed to be a one-way function with the factorization of n as the trapdoor. • It is not known if encryption really is one-way • It is not known if there are other trapdoors • However, for security, it is certainly required that it not be possible to factor n 12/24/2021 CS 284 -162/Spring 09/GWU/Vora/RSA 10
Security of RSA Is it based on hardness of factoring n? • It is not known if: – factoring a product of two primes into its prime components is • solvable in polynomial time • NP-complete – there are other trapdoors to RSA, i. e. other ways of breaking it in general • Factoring is an easy problem in the quantum computing model. 12/24/2021 CS 284 -162/Spring 09/GWU/Vora/RSA 11
RSA: Computational complexity • • 512 bit primes, n is 1024 bits Encryption: b 3 where a plaintext character is b-bits Decryption by brute force: 2 bb 3 Key generation: Primes? O(b 2), O(b 3) 12/24/2021 CS 284 -162/Spring 09/GWU/Vora/RSA 12
Encryption of blocks of symbols Block ABCD…, each symbol is base N (e. g. N=2, 16) Convert a block of a few symbols to an integer mod n RSA encrypt Convert back to base N Example. 12/24/2021 CS 284 -162/Spring 09/GWU/Vora/RSA 13
RSA Decryption Show that f. K and g. K are inverses f(g(x)) = xba mod n = xt (n)+1 mod n = x xt (n) mod n What do we do now? 12/24/2021 CS 284 -162/Spring 09/GWU/Vora/RSA 14
We will need • Chinese Remainder Theorem (CRT) • Lagrange’s Theorem 12/24/2021 CS 284 -162/Spring 09/GWU/Vora/RSA 15
CRT: Solve congruences What is x? 17 x 3 mod 101 5 x 2 mod 7 12/24/2021 CS 284 -162/Spring 09/GWU/Vora/RSA 16

Chinese Remainder Theorem There is exactly one number modulo xy which is bmodx and Bmody if x and y are relatively prime. Proof: Suppose not. Then: First number = ax + b = Ay + B Second number = cx + b = Cy + B (a-c)x = (A-C)y y | (a-c)x y | (a-c) because x and y rel. prime a = my + c first number = mxy + cx + b = second number modulo xy 12/24/2021 CS 284 -162/Spring 09/GWU/Vora/RSA 17
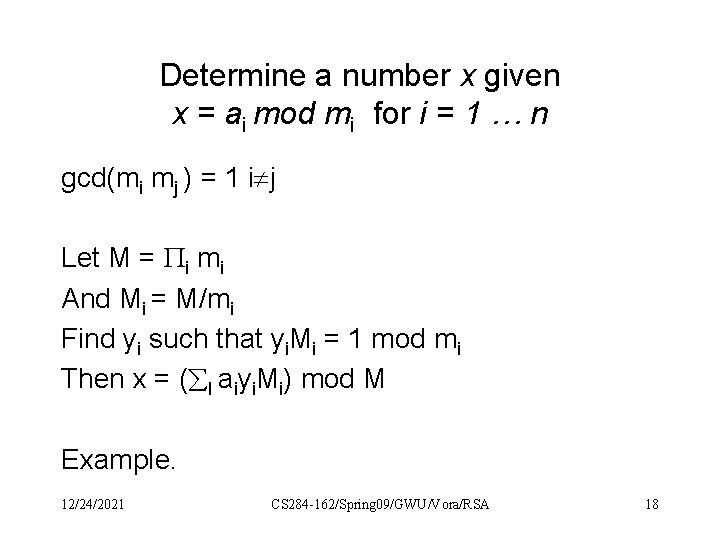
Determine a number x given x = ai mod mi for i = 1 … n gcd(mi mj ) = 1 i j Let M = i mi And Mi = M/mi Find yi such that yi. Mi = 1 mod mi Then x = ( I aiyi. Mi) mod M Example. 12/24/2021 CS 284 -162/Spring 09/GWU/Vora/RSA 18
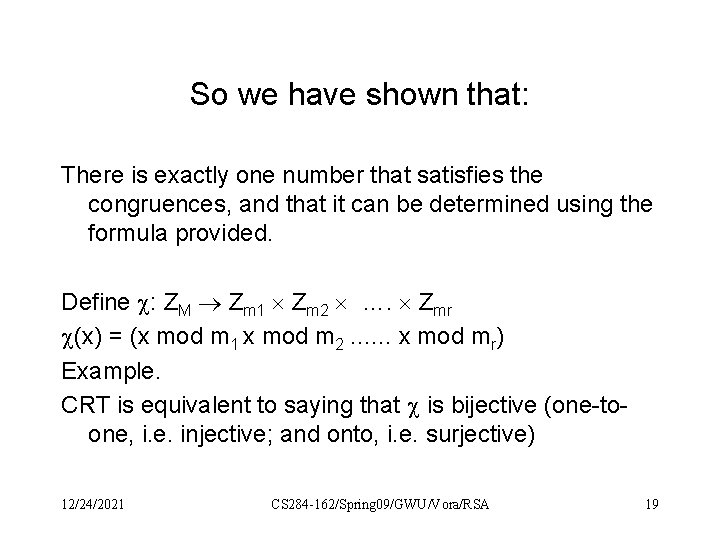
So we have shown that: There is exactly one number that satisfies the congruences, and that it can be determined using the formula provided. Define : ZM Zm 1 Zm 2 …. Zmr (x) = (x mod m 1 x mod m 2. . . … x mod mr) Example. CRT is equivalent to saying that is bijective (one-toone, i. e. injective; and onto, i. e. surjective) 12/24/2021 CS 284 -162/Spring 09/GWU/Vora/RSA 19
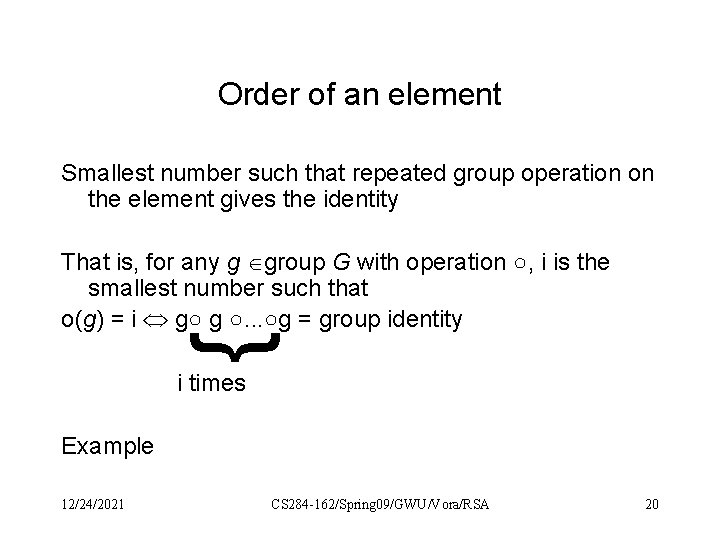
Order of an element Smallest number such that repeated group operation on the element gives the identity { That is, for any g group G with operation ○, i is the smallest number such that o(g) = i g○ g ○. . . ○g = group identity i times Example 12/24/2021 CS 284 -162/Spring 09/GWU/Vora/RSA 20
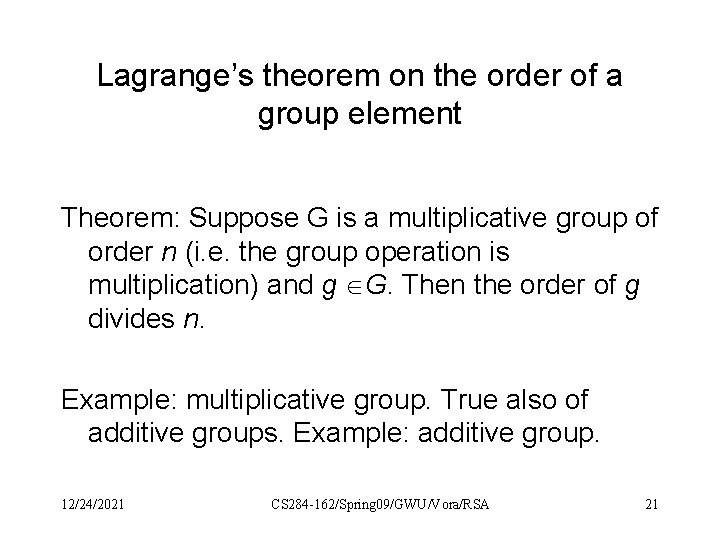
Lagrange’s theorem on the order of a group element Theorem: Suppose G is a multiplicative group of order n (i. e. the group operation is multiplication) and g G. Then the order of g divides n. Example: multiplicative group. True also of additive groups. Example: additive group. 12/24/2021 CS 284 -162/Spring 09/GWU/Vora/RSA 21
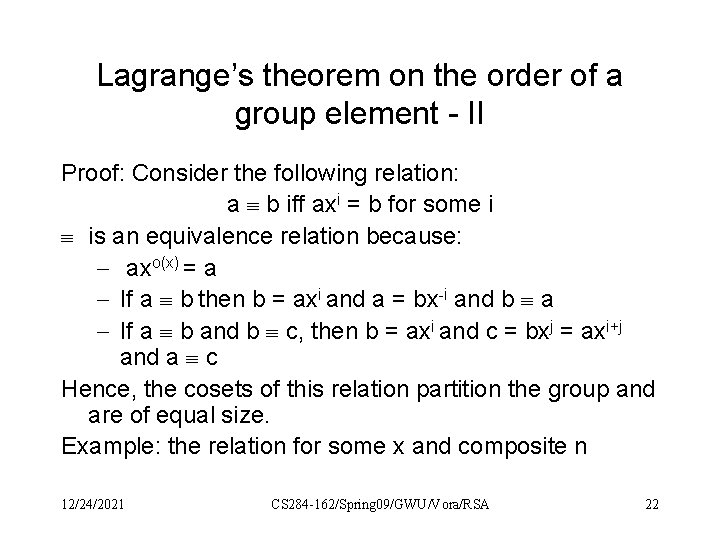
Lagrange’s theorem on the order of a group element - II Proof: Consider the following relation: a b iff axi = b for some i is an equivalence relation because: - axo(x) = a - If a b then b = axi and a = bx-i and b a - If a b and b c, then b = axi and c = bxj = axi+j and a c Hence, the cosets of this relation partition the group and are of equal size. Example: the relation for some x and composite n 12/24/2021 CS 284 -162/Spring 09/GWU/Vora/RSA 22
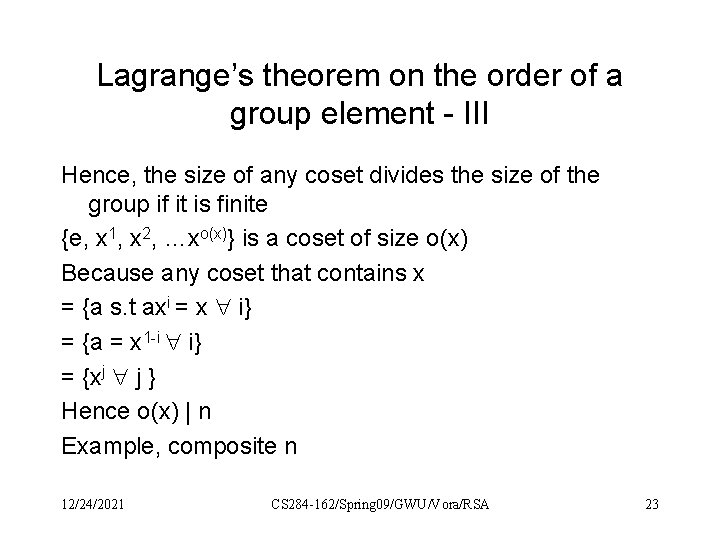
Lagrange’s theorem on the order of a group element - III Hence, the size of any coset divides the size of the group if it is finite {e, x 1, x 2, …xo(x)} is a coset of size o(x) Because any coset that contains x = {a s. t axi = x i} = {a = x 1 -i i} = {xj j } Hence o(x) | n Example, composite n 12/24/2021 CS 284 -162/Spring 09/GWU/Vora/RSA 23
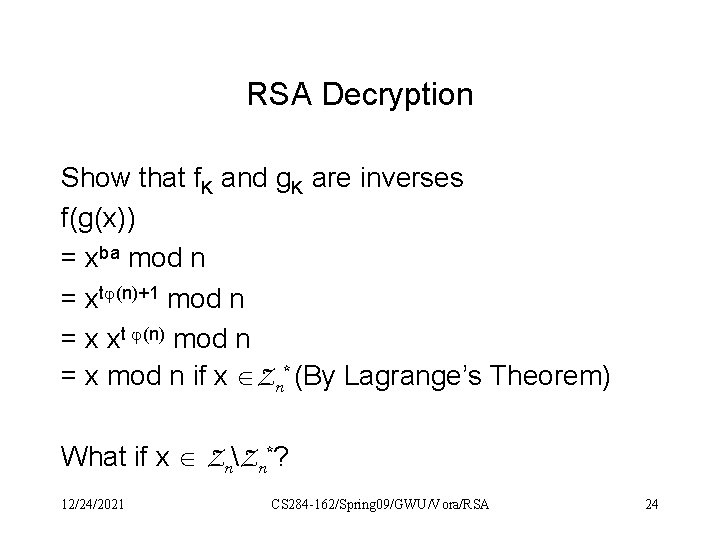
RSA Decryption Show that f. K and g. K are inverses f(g(x)) = xba mod n = xt (n)+1 mod n = x xt (n) mod n = x mod n if x Zn* (By Lagrange’s Theorem) What if x ZnZn*? 12/24/2021 CS 284 -162/Spring 09/GWU/Vora/RSA 24
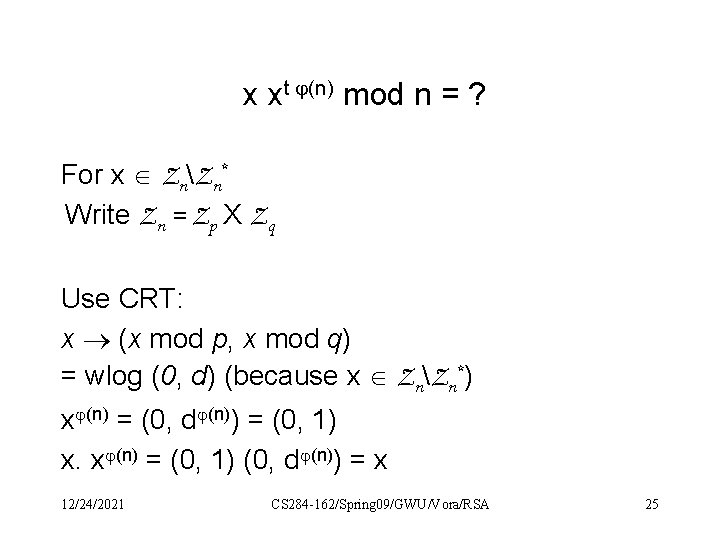
x xt (n) mod n = ? For x ZnZn* Write Zn = Zp X Zq Use CRT: x (x mod p, x mod q) = wlog (0, d) (because x ZnZn*) x (n) = (0, d (n)) = (0, 1) x. x (n) = (0, 1) (0, d (n)) = x 12/24/2021 CS 284 -162/Spring 09/GWU/Vora/RSA 25
A simple inefficient algorithm for generating a prime • Generate a b-bit random number • It is prime with probability 1/ln 2 b = 1/(ln 2 b) = O(1/b) • Generate enough and will be done, in O(b) complexity. • How do you check if it is prime? 12/24/2021 CS 284 -162/Spring 09/GWU/Vora/RSA 26
Eratosthenes Sieve If want a prime of length b bits, list the numbers 2 to 2 b/2 Starting from the beginning, delete all multiples of each prime: delete 4, 6, 8, …; 6, 9, …… At the end will be left with the primes Check if these primes divide your randomly generated number If not, it is prime. 12/24/2021 CS 284 -162/Spring 09/GWU/Vora/RSA 27
Euler Phi function (number of invertible elements in Zm) If m = pq, 1, 2, 3, …p, . . 2 p, . . 3 p, …qp q numbers divisible by p 1, 2, 3, …q, . . 2 q, . . 3 q, …pq p numbers divisible by q pq only number counted twice. No other numbers. pq – p – q + 1 = (p-1)(q-1) invertible elements 12/24/2021 CS 284 -162/Spring 09/GWU/Vora/RSA 28
Can also show previous result using CRT 12/24/2021 CS 284 -162/Spring 09/GWU/Vora/RSA 29
- Slides: 29