RSA Public Key Algorithm CRYPTOGRA PHY RSA Algorithm
RSA Public Key Algorithm CRYPTOGRA PHY
RSA Algorithm history � Invented in 1977 at MIT � Named for Ron Rivest, Adi Shamir, and Len Adleman � Based on 2 keys, 1 public and 1 private
Basic Algorithm �A private and a public key are generated by a user. � The public key is given to a sender, who encrypts the message using that key. � The user then decrypts the message using the private key
Key generation 2 large prime numbers P and Q are randomly chosen �N=P*Q � S = (P-1) (Q-1) � Value E is chosen where 1<E<N and the greatest common denominator of E and S is 1 � A value D is calculated where (D*E) mod. S =1 � D is the private key � (N, E) is published as the public key �
Encryption � To send a message a person uses the public key � The plaintext message is broken into binary segments no larger than N � Each segment is encrypted with the algorithm ciphertext = plaintext. E mod N
Decryption � To decrypt the message, the recipient will calculate each segment with plaintext = ciphertext. D mod N
Confused ?
Alfred chooses 2 primes �P = 19 and Q = 31 �N = P*Q = 589
Alfred finds e � (P-1)(Q-1) �E = 540 needs to have no GCD with 540 � Can be found with Euclid’s algorithm (Example 27. 6, p 614 Automata) �E = 49
Alfred finds D �D is computed using an extension of Euclid’s algorithm �D = 1069 � 1069 is the private key � (589, 49) is the public key
Batman wants to send message � The message will be “A” � ASCII code for A is 65 � The encryption algorithm is then: � 6549 mod 589 � However, 6549 don’t actually need to compute
Batman exploits 2 facts � Ni+j = N i * Nj � (N*M) mod K = �(N mod K)(M mod K) mod K � This is called modular exponentiation � Note that 6549 = 651+16+32
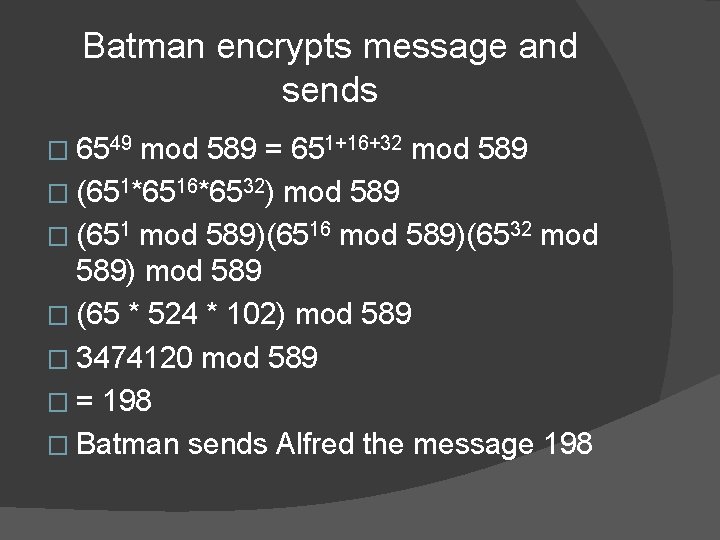
Batman encrypts message and sends � 6549 mod 589 = 651+16+32 mod 589 � (651*6516*6532) mod 589 � (651 mod 589)(6516 mod 589)(6532 mod 589) mod 589 � (65 * 524 * 102) mod 589 � 3474120 mod 589 � = 198 � Batman sends Alfred the message 198
Alfred decrypts message � Alfred uses the private key 1069 and computes 1981069 mod 589 � This is done with the same process used in encryption to retrieve the message “A”
Why it’s effective � Larger integers increase effectiveness � Encryption and decryption are inverses of each other � User A can find E and D efficiently � Modular exponentiation allows both users to compute encryption and decryption efficiently
Why it’s effective � Any eavesdropper will not be able to recreate the enciphered text because the modular exponentiation is not an invertible function � Also, the private key D cannot be calculated from the public keys N and E
References � Automata, Computability, and Complexity. Elaine Rich. Pearson Prentice Hall, 2008. � RSA Laboratories' Frequently Asked Questions About Today's Cryptography, Version 4. 1. RSA Laboratories Inc, 2000. http: //www. rsa. com/rsalabs/node. asp? id =2152#
- Slides: 17