Modeling and Measuring Botnets David Dagon Wenke Lee
Modeling and Measuring Botnets David Dagon, Wenke Lee Georgia Institute of Technology Cliff C. Zou Univ. of Central Florida 1
Outline n Motivation n Diurnal modeling of botnet propagation n Botnet population estimation n Botnet threat assessment n Advanced botnet 2
Motivation n n Botnet becomes a serious threat Not much research on botnet yet u Empirical analysis of captured botnets Ø n Mainly based on honeypot spying Need understanding of the network of botnet Botnet growth dynamics u Botnet (on-line) population, threat level … u n Well prepared for next generation botnet 3
Outline n Motivation n Diurnal modeling of botnet propagation n Botnet population estimation n Botnet threat assessment n Advanced botnet 4
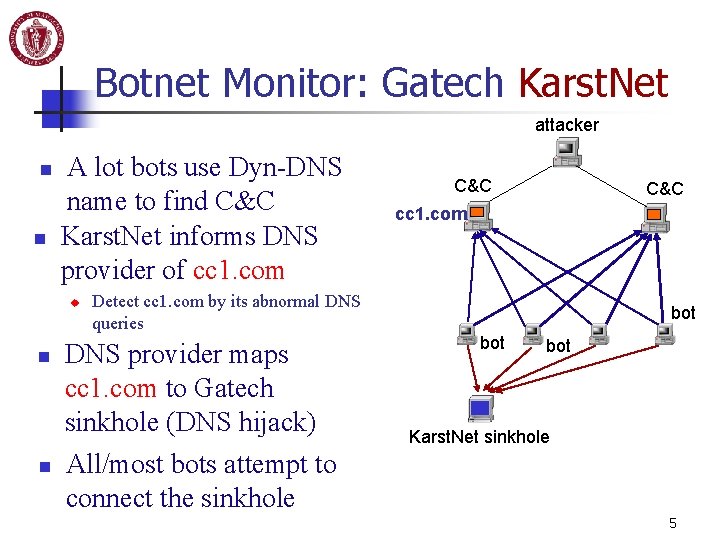
Botnet Monitor: Gatech Karst. Net attacker n n A lot bots use Dyn-DNS name to find C&C Karst. Net informs DNS provider of cc 1. com u n n Detect cc 1. com by its abnormal DNS queries DNS provider maps cc 1. com to Gatech sinkhole (DNS hijack) C&C cc 1. com bot bot Karst. Net sinkhole All/most bots attempt to connect the sinkhole 5
Diurnal Pattern in Monitored Botnets n n Diurnal pattern affects botnet propagation rate Diurnal pattern affects botnet attack strength 6
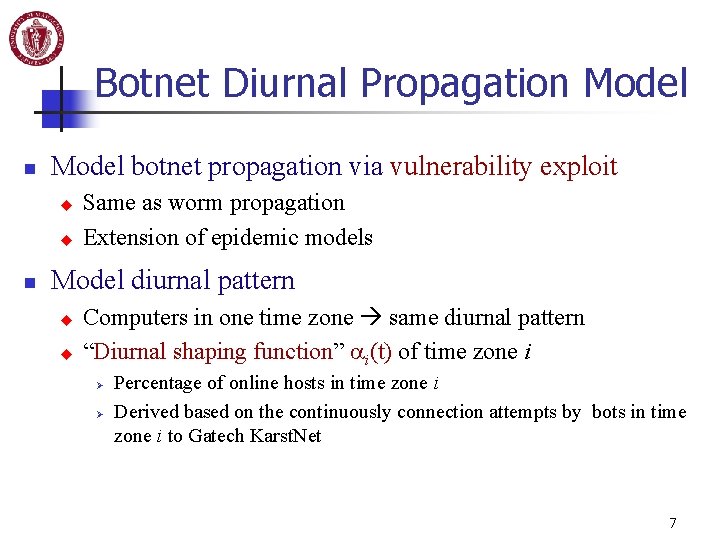
Botnet Diurnal Propagation Model botnet propagation via vulnerability exploit u u n Same as worm propagation Extension of epidemic models Model diurnal pattern u u Computers in one time zone same diurnal pattern “Diurnal shaping function” i(t) of time zone i Ø Ø Percentage of online hosts in time zone i Derived based on the continuously connection attempts by bots in time zone i to Gatech Karst. Net 7
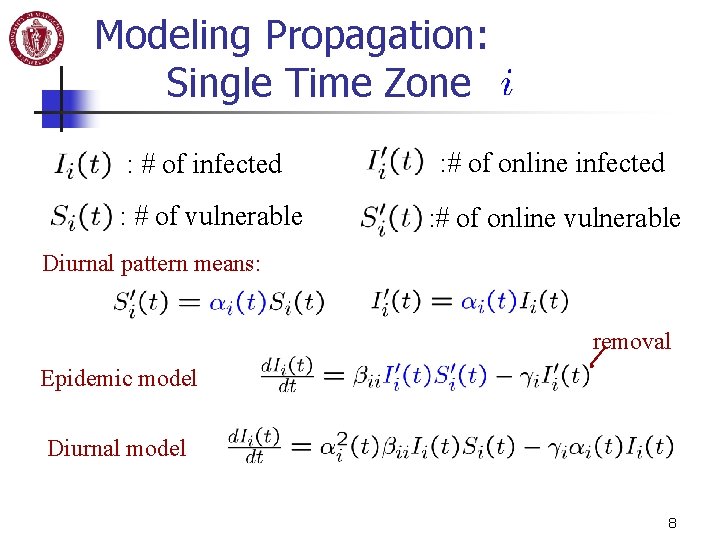
Modeling Propagation: Single Time Zone : # of infected : # of online infected : # of vulnerable : # of online vulnerable Diurnal pattern means: removal Epidemic model Diurnal model 8
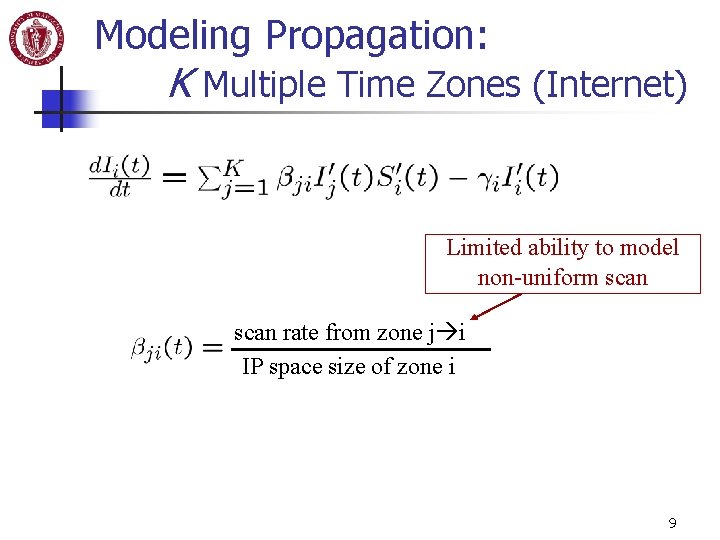
Modeling Propagation: K Multiple Time Zones (Internet) Limited ability to model non-uniform scan rate from zone j i IP space size of zone i 9
Validation: Fitting model to botnet data n Diurnal model is more accurate than traditional epidemic model 10
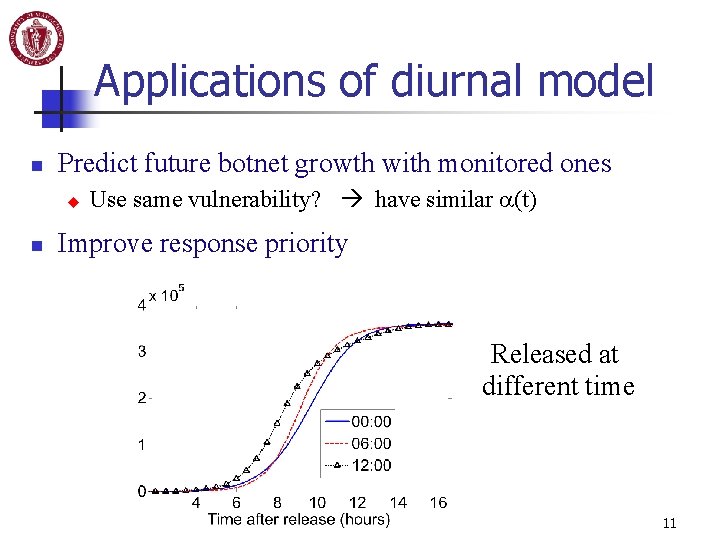
Applications of diurnal model n Predict future botnet growth with monitored ones u n Use same vulnerability? have similar (t) Improve response priority Released at different time 11
Outline n Motivation n Diurnal modeling of botnet propagation n Botnet population estimation n Botnet threat assessment n Advanced botnet 12
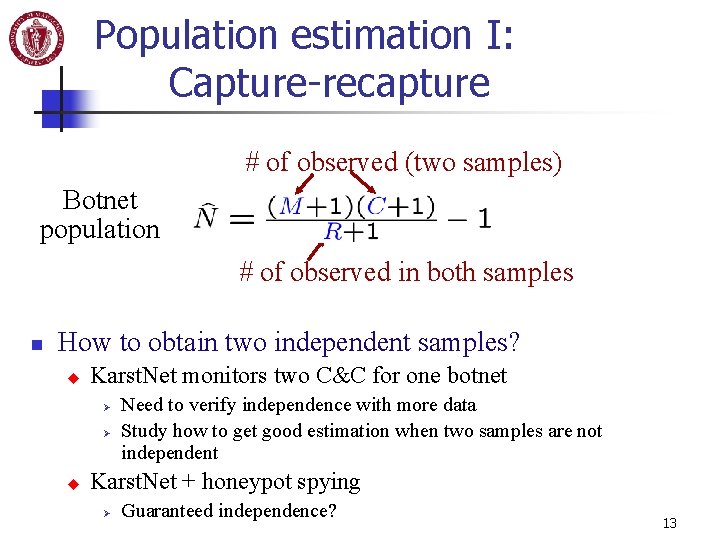
Population estimation I: Capture-recapture # of observed (two samples) Botnet population # of observed in both samples n How to obtain two independent samples? u Karst. Net monitors two C&C for one botnet Ø Ø u Need to verify independence with more data Study how to get good estimation when two samples are not independent Karst. Net + honeypot spying Ø Guaranteed independence? 13
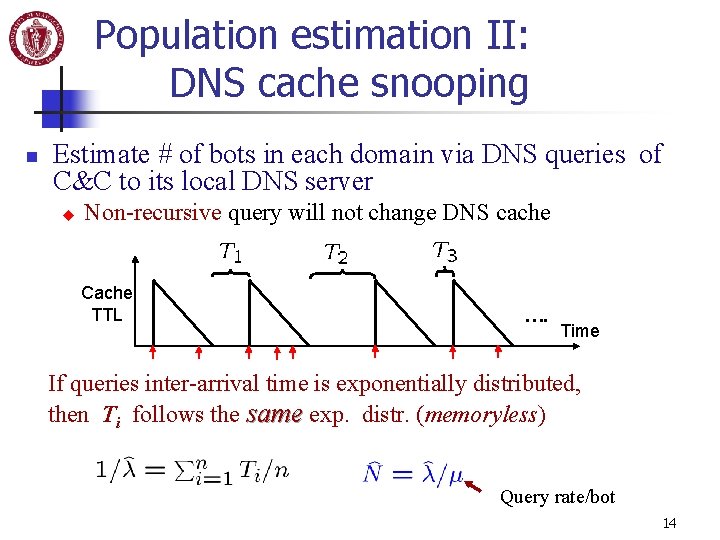
Population estimation II: DNS cache snooping n Estimate # of bots in each domain via DNS queries of C&C to its local DNS server u Non-recursive query will not change DNS cache Cache TTL …. Time If queries inter-arrival time is exponentially distributed, then Ti follows the same exp. distr. (memoryless) Query rate/bot 14
Outline n Motivation n Diurnal modeling of botnet propagation n Botnet population estimation n Botnet threat assessment n Advanced botnet 15
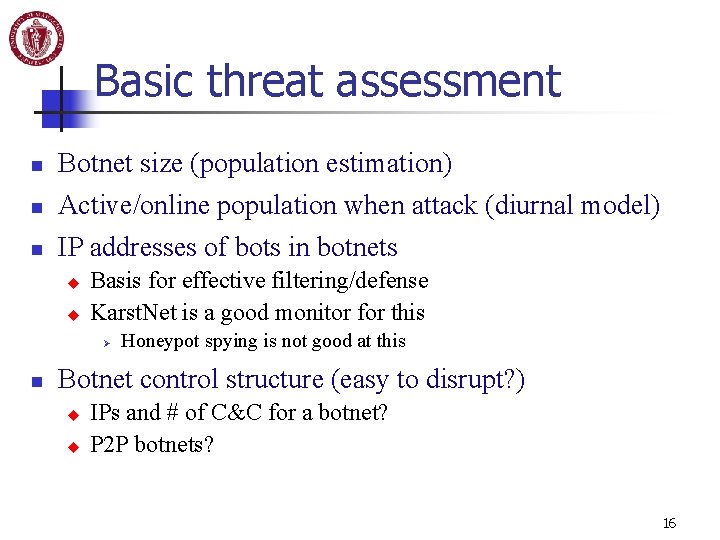
Basic threat assessment n Botnet size (population estimation) n Active/online population when attack (diurnal model) n IP addresses of bots in botnets u u Basis for effective filtering/defense Karst. Net is a good monitor for this Ø n Honeypot spying is not good at this Botnet control structure (easy to disrupt? ) u u IPs and # of C&C for a botnet? P 2 P botnets? 16
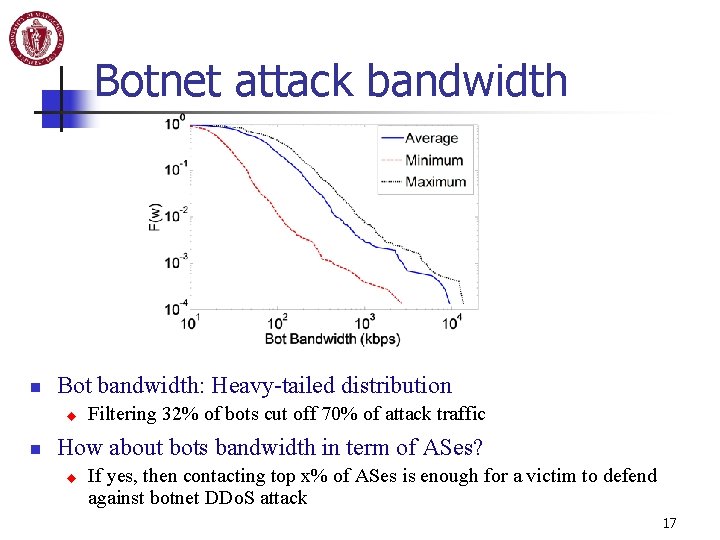
Botnet attack bandwidth n Bot bandwidth: Heavy-tailed distribution u n Filtering 32% of bots cut off 70% of attack traffic How about bots bandwidth in term of ASes? u If yes, then contacting top x% of ASes is enough for a victim to defend against botnet DDo. S attack 17
Outline n Motivation n Diurnal modeling of botnet propagation n Botnet population estimation n Botnet threat assessment n Advanced botnet 18
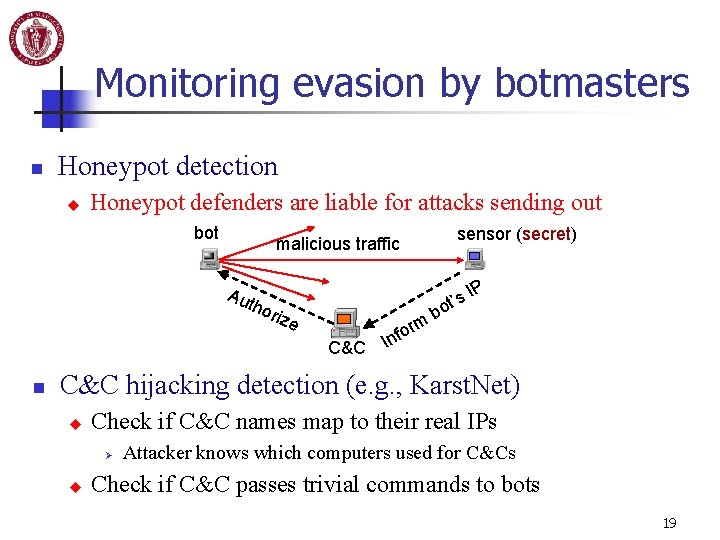
Monitoring evasion by botmasters n Honeypot detection u Honeypot defenders are liable for attacks sending out bot malicious traffic Au tho rize C&C n rm o f In sensor (secret) t’s bo IP C&C hijacking detection (e. g. , Karst. Net) u Check if C&C names map to their real IPs Ø u Attacker knows which computers used for C&Cs Check if C&C passes trivial commands to bots 19
Advanced hybrid P 2 P botnet n Why use P 2 P by attackers? u u Remove control bottleneck (C&C) C&Cs are easy to be monitored Ø Ø u n One honeypot spy reveals all C&Cs One captured/hijacked C&C reveals all bots C&C are easy to be shut down (limited number) Current P 2 P protocols will not work for botnets u u u Bootstrap process is vulnerable to be blocked Disable global view from each bot (prevent monitoring) Must consider DHCP, private IP, firewall, capture, removal 20
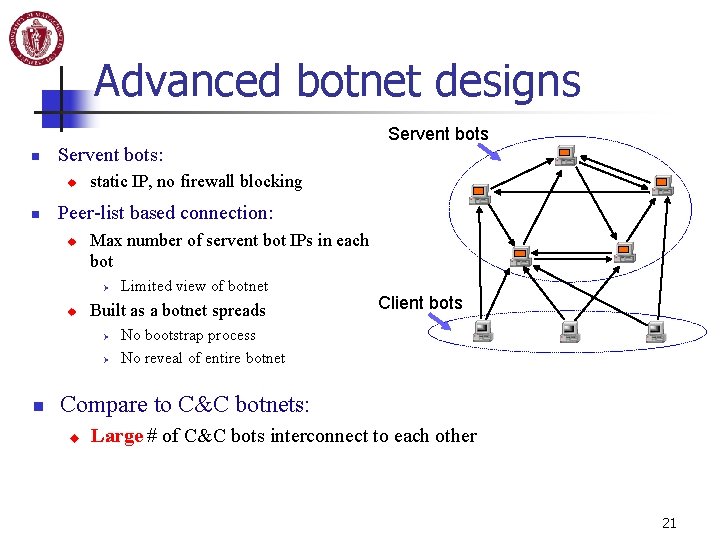
Advanced botnet designs n Servent bots: u n static IP, no firewall blocking Peer-list based connection: u Max number of servent bot IPs in each bot Ø u Limited view of botnet Built as a botnet spreads Ø Ø n Servent bots Client bots No bootstrap process No reveal of entire botnet Compare to C&C botnets: u Large # of C&C bots interconnect to each other 21
Advanced botnet designs n Public key in bot code, private key in botmaster u n Ensure command authentication/integrity Individualized encryption, service port Peer list: u u Defeat traffic-based detection Limited exposure when one bot is captured 22
Advanced botnet designs n Easy monitoring by botmaster u Command all bots report to a “sensor” host Ø u Different sensor hosts in each round of report command Ø n Each bot report: peer list, encryption key, service port, IP, diurnal property, IP property, link bandwidth…. Prevent sensors from being blocked, captured Robust botnet construction by peer-list updating u u With few re-infections, initial servent bots are highly connected (each connecting to >60% of bots in a botnet) “Peer-list Update” command: each bot goes to a “sensor” host to get its new peer list Ø Peer list randomly selected from previous reported servent bots 23
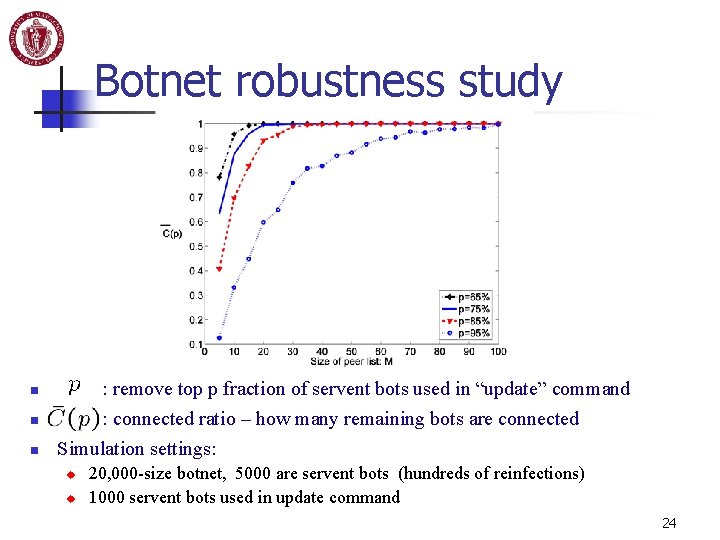
Botnet robustness study n n n : remove top p fraction of servent bots used in “update” command : connected ratio – how many remaining bots are connected Simulation settings: u u 20, 000 -size botnet, 5000 are servent bots (hundreds of reinfections) 1000 servent bots used in update command 24
Future work n Propagation modeling u u n Population estimation: u u n Validate the independence of monitor samples Validate the Poisson arrival in C&C DNS queries Threat assessment u u n Diurnal model of email-based propagation Parameters: (t), , removal dynamics AS-level botnet bandwidth (heavy tailed? ) Bot access link speed --- better representation? Monitor and model of advanced botnets 25
Reference n NSF Cyber Trust grant: CNS-0627318 u u n n "Collaborative Research: CT-ISG: Modeling and Measuring Botnets" PI: Cliff Zou, PI: Wenke Lee David Dagon, Cliff C. Zou, and Wenke Lee. "Modeling Botnet Propagation Using Time Zones, " in 13 th Annual Network and Distributed System Security Symposium (NDSS), Feb. , San Diego, 2006 (Acceptance ratio: 17/127=13. 4%). Cliff C. Zou and Ryan Cunningham. "Honeypot-Aware Advanced Botnet Construction and Maintenance, " in the International Conference on Dependable Systems and Networks (DSN), Jun. , Philadelphia, 2006 (Acceptance ratio: 34/187=18. 2%). n Ping Wang, Sherri Sparks, Cliff C. Zou. “An Advanced Hybrid Peer-to-Peer Botnet, ” in submission. n Cliff Zou homepage: http: //www. cs. ucf. edu/~czou/ 26
- Slides: 26