On Cellular Botnets Measuring the Impact of Malicious
On Cellular Botnets: Measuring the Impact of Malicious Devices on a Cellular Network Core Patrick Traynor, Michael Lin, Machigar Ongtang, Vikhyath Rao, Trent Jaeger, Patrick Mc. Daniel, and Thomas La Porta 2/29/2012
Overview � Objectives � Cellular Networks � Describing the Attack � Quantifying the Attack � Mitigating the Attack � Conclusions 2/29/2012 2
Objectives � Characterize an attack on cellular network core � Test the attack � Optimize it � Propose defenses 2/29/2012 3
Background � Cellular networks have § Home Location Register (HLR) § Mobile Switching Centers (MSC) § Visiting Location Register (VLR) § Serving GPRS Support Node (SGSN) § Base Station Subsystem (BSS) 2/29/2012 4
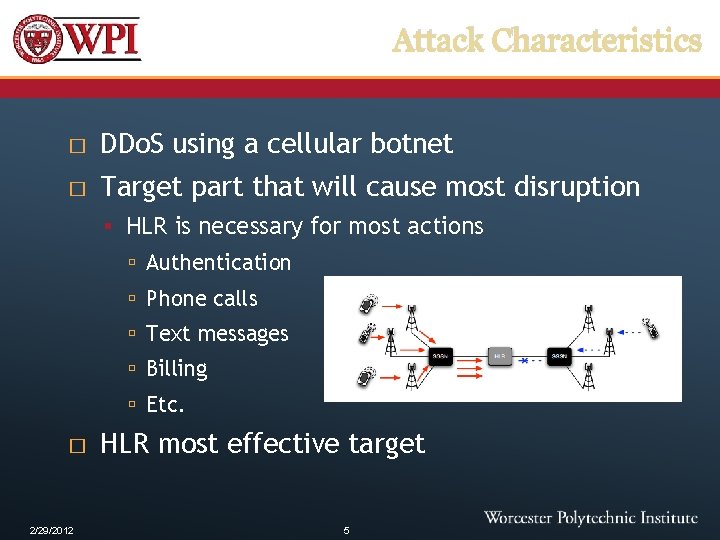
Attack Characteristics � DDo. S using a cellular botnet � Target part that will cause most disruption § HLR is necessary for most actions Authentication Phone calls Text messages Billing Etc. � 2/29/2012 HLR most effective target 5
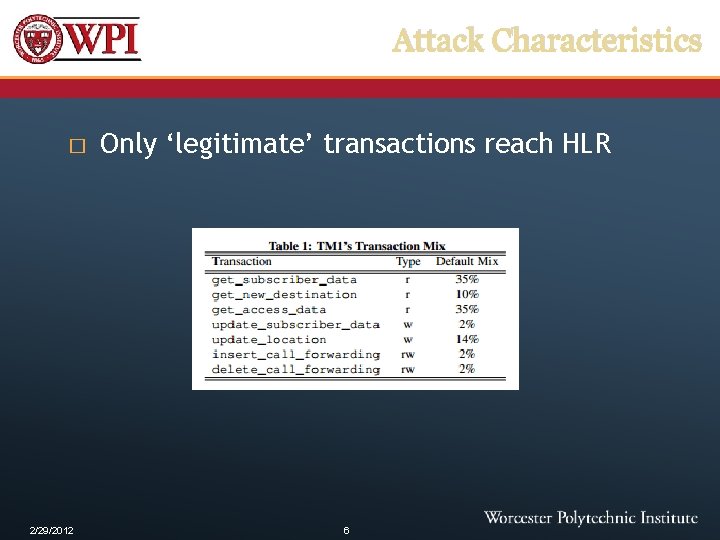
Attack Characteristics � 2/29/2012 Only ‘legitimate’ transactions reach HLR 6
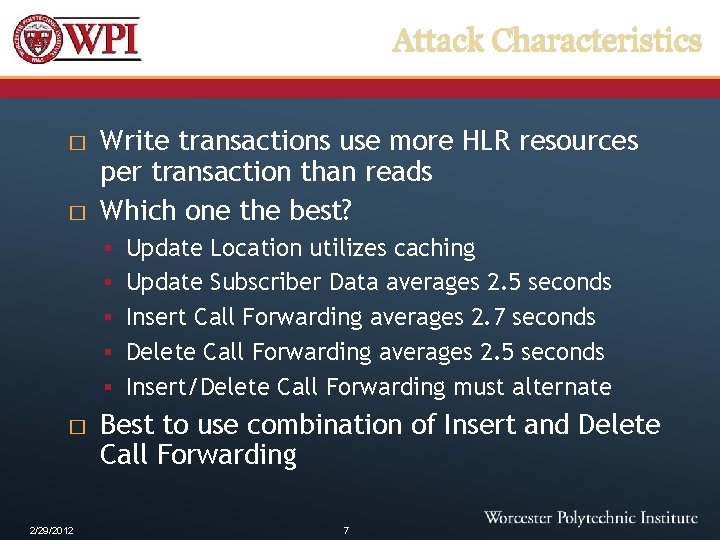
Attack Characteristics � � Write transactions use more HLR resources per transaction than reads Which one the best? § Update Location utilizes caching § Update Subscriber Data averages 2. 5 seconds § Insert Call Forwarding averages 2. 7 seconds § Delete Call Forwarding averages 2. 5 seconds § Insert/Delete Call Forwarding must alternate � 2/29/2012 Best to use combination of Insert and Delete Call Forwarding 7
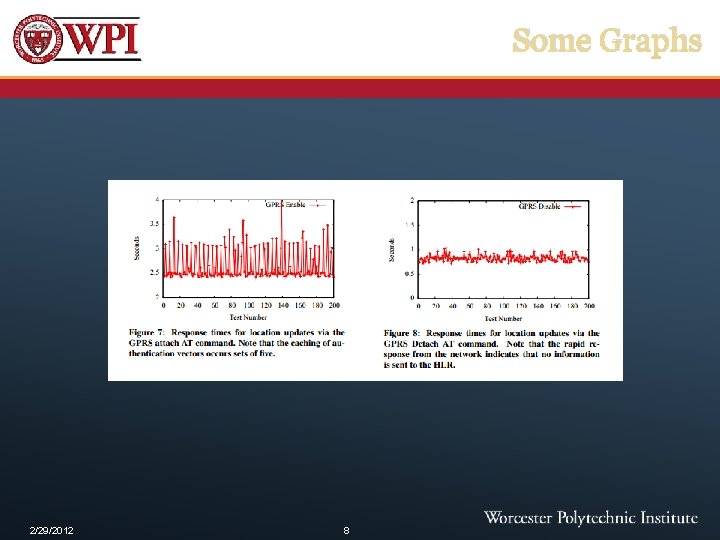
Some Graphs 2/29/2012 8
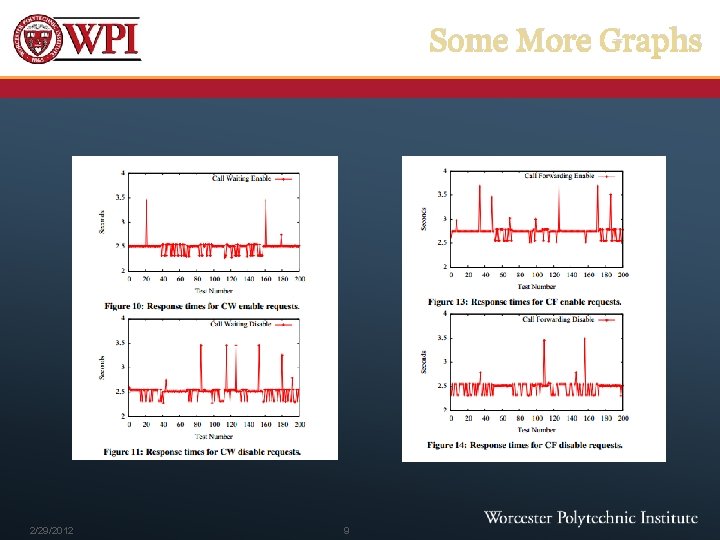
Some More Graphs 2/29/2012 9
Attack Considerations � Why most resource usage per message? § Why not just send more messages? � When sending that many messages, will clog up communications channels and never reach HLR § Deny service for base station, not whole network � 2/29/2012 Need to distribute attack across multiple base stations 10
Attack Numbers � � � 2/29/2012 Testbed system dropped 93% of traffic under a simulated call-forwarding attack with 5000 messages/sec Need to be distributed evenly across 21 base stations to not DDo. S the random access channel before getting to HLR Need 375 base stations to not DDo. S control channels 11
Command Control � Tried and true (Internet coordination) § Easy to identify/snoop § Clogs communication channels � Local Wireless Coordination § Short range � Indirect Local Coordination § Using exponential backoff? 2/29/2012 12
Mitigation � Filtering § Can be aggressive because call forwarding is not critical § What if call forwarding is not the transaction used? � Shedding § How to deploy effective rules during an attack? � 2/29/2012 Make phone security better 13
Conclusions � Cellular network are vulnerable to DDo. S attacks � Single points of failure are bad � Botnet must be fairly sophisticated � Is there a way to distribute HLR data? 2/29/2012 14
- Slides: 14