Lecture 5 LowLevel Vulnerabilities Avishai Wool 2018 Based

Lecture 5 Low-Level Vulnerabilities Avishai Wool, 2018 Based on slides by Dan Gittik
Course Agenda • • Bring you up to scratch on: • Some Cryptography • Some Assembly • Some Linux Then talk information security: • Low-level vulnerabilities • Network vulnerabilities • Web vulnerabilities 2 Introduction to Information Security, Tel-Aviv University Lecture 5, Low-Level Vulnerabilities
Today’s Agenda • (Tips and Tools) • Buffer overflows on the stack • • Return to libc • Return-oriented programming Buffer overflows on the heap • Heap overflow • Use after free • Metadata corruption 3 Introduction to Information Security, Tel-Aviv University Lecture 5, Low-Level Vulnerabilities
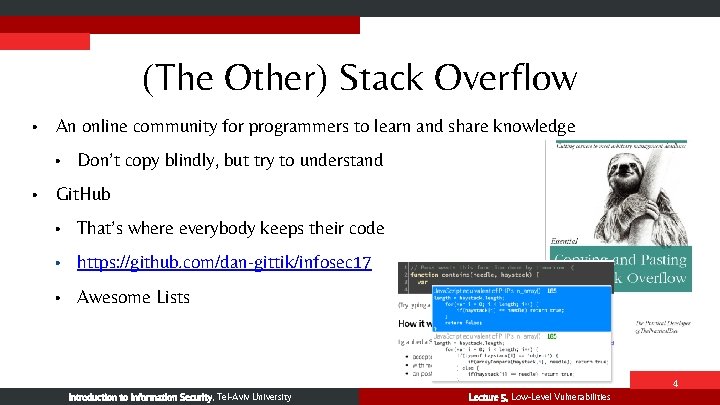
(The Other) Stack Overflow • An online community for programmers to learn and share knowledge • • Don’t copy blindly, but try to understand Git. Hub • That’s where everybody keeps their code • https: //github. com/dan-gittik/infosec 17 • Awesome Lists 4 Introduction to Information Security, Tel-Aviv University Lecture 5, Low-Level Vulnerabilities
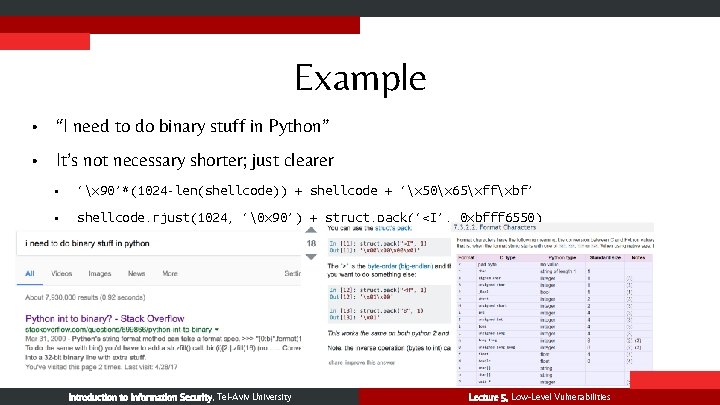
Example • “I need to do binary stuff in Python” • It’s not necessary shorter; just clearer • ‘x 90’*(1024 -len(shellcode)) + shellcode + ‘x 50x 65xffxbf’ • shellcode. rjust(1024, ‘� x 90’) + struct. pack(‘<I’, 0 xbfff 6550) 5 Introduction to Information Security, Tel-Aviv University Lecture 5, Low-Level Vulnerabilities
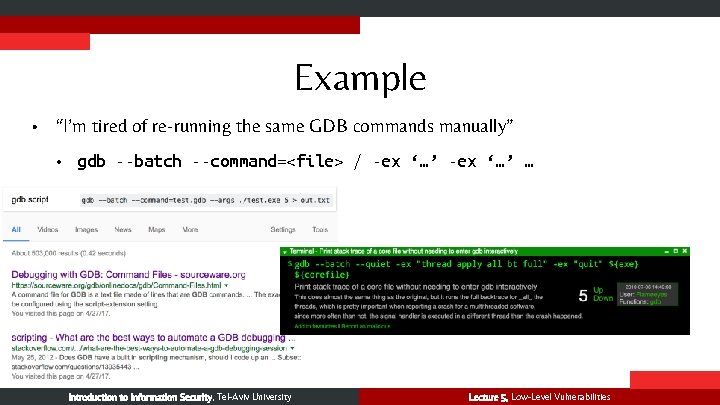
Example • “I’m tired of re-running the same GDB commands manually” • gdb --batch --command=<file> / -ex ‘…’ … 6 Introduction to Information Security, Tel-Aviv University Lecture 5, Low-Level Vulnerabilities
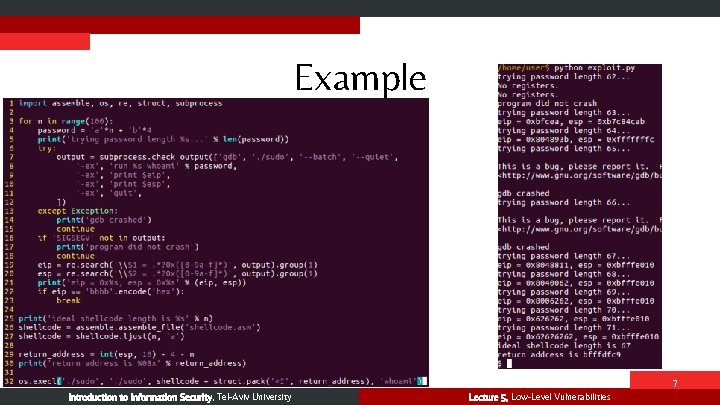
Example 7 Introduction to Information Security, Tel-Aviv University Lecture 5, Low-Level Vulnerabilities
Moxie • “It’s not working” • • OK… which part? • Understand what it is you don’t understand • Isolate variables • If you hate debugging, programming is probably not for you • IRL, nobody has any idea what’s going on “I don’t know GDB” • At which point is it worth it to read a 30 -minutes GDB tutorial? 8 Introduction to Information Security, Tel-Aviv University Lecture 5, Low-Level Vulnerabilities
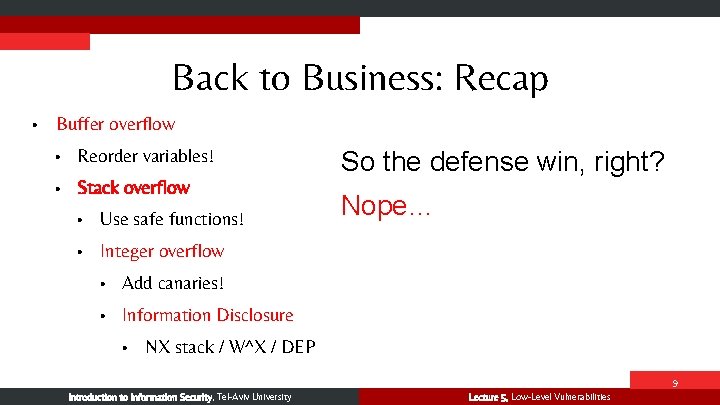
Back to Business: Recap • Buffer overflow • Reorder variables! • Stack overflow • Use safe functions! • Integer overflow • Add canaries! • Information Disclosure • So the defense win, right? Nope… NX stack / W^X / DEP 9 Introduction to Information Security, Tel-Aviv University Lecture 5, Low-Level Vulnerabilities
Return to libc Introduction to Information Security, Tel-Aviv University Lecture 5, Low-Level Vulnerabilities
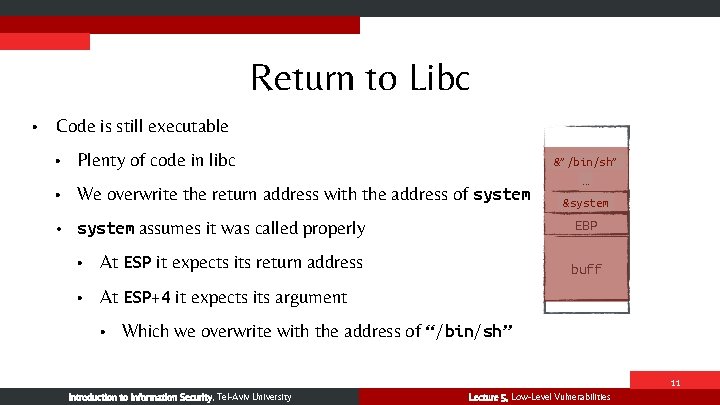
Return to Libc • Code is still executable • Plenty of code in libc • We overwrite the return address with the address of system • system assumes it was called properly EBP • At ESP it expects its return address buff • At ESP+4 it expects its argument • &”/bin/sh” … &system EIP Which we overwrite with the address of “/bin/sh” 11 Introduction to Information Security, Tel-Aviv University Lecture 5, Low-Level Vulnerabilities
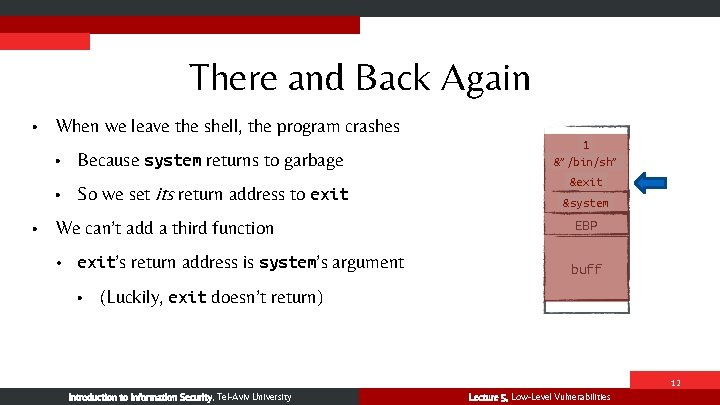
There and Back Again • • When we leave the shell, the program crashes • Because system returns to garbage • So we set its return address to exit We can’t add a third function • exit’s return address is system’s argument • 1 &”/bin/sh” … &exit &system EIP EBP buff (Luckily, exit doesn’t return) 12 Introduction to Information Security, Tel-Aviv University Lecture 5, Low-Level Vulnerabilities
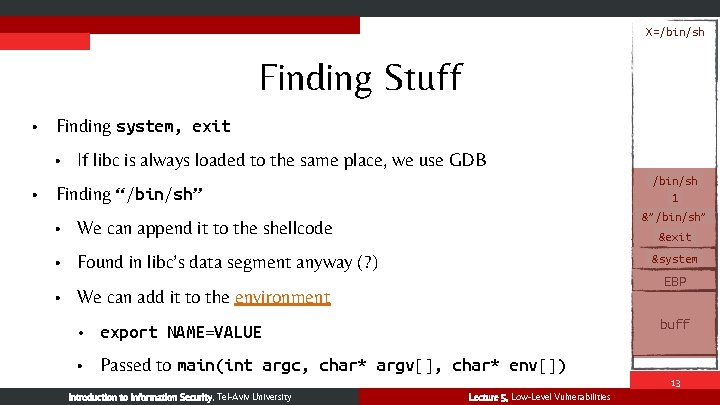
X=/bin/sh Finding Stuff • Finding system, exit • • If libc is always loaded to the same place, we use GDB /bin/sh 1 &”/bin/sh” &exit Finding “/bin/sh” • We can append it to the shellcode • Found in libc’s data segment anyway (? ) • &system EIP EBP We can add it to the environment buff • export NAME=VALUE • Passed to main(int argc, char* argv[], char* env[]) 13 Introduction to Information Security, Tel-Aviv University Lecture 5, Low-Level Vulnerabilities
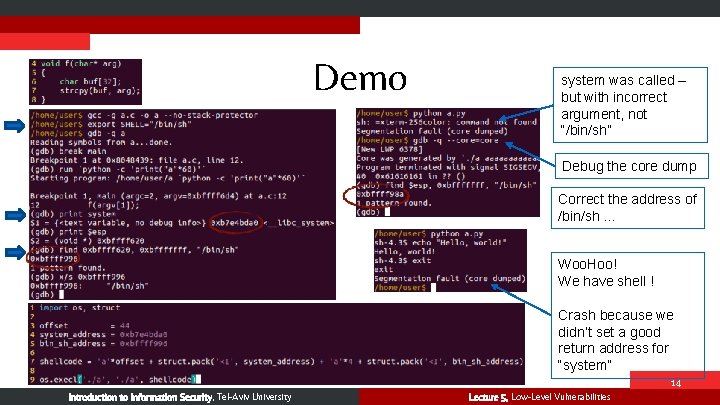
Demo system was called – but with incorrect argument, not “/bin/sh” Debug the core dump Correct the address of /bin/sh … Woo. Hoo! We have shell ! Crash because we didn’t set a good return address for “system” 14 Introduction to Information Security, Tel-Aviv University Lecture 5, Low-Level Vulnerabilities
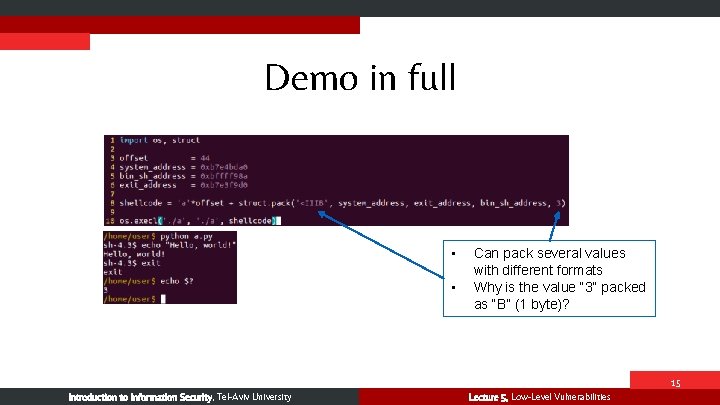
Demo in full • • Can pack several values with different formats Why is the value “ 3” packed as “B” (1 byte)? 15 Introduction to Information Security, Tel-Aviv University Lecture 5, Low-Level Vulnerabilities
Return Oriented Programming (ROP) Introduction to Information Security, Tel-Aviv University Lecture 5, Low-Level Vulnerabilities
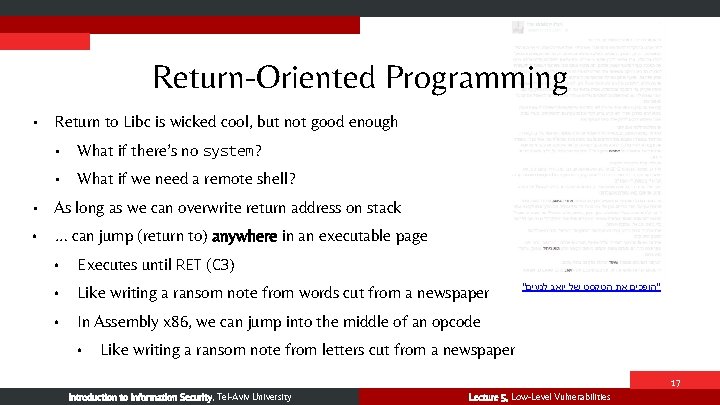
Return-Oriented Programming • Return to Libc is wicked cool, but not good enough • What if there’s no system? • What if we need a remote shell? • As long as we can overwrite return address on stack • … can jump (return to) anywhere in an executable page • Executes until RET (C 3) • Like writing a ransom note from words cut from a newspaper • In Assembly x 86, we can jump into the middle of an opcode • " "הופכים את הטקסט של יואב לנעים Like writing a ransom note from letters cut from a newspaper 17 Introduction to Information Security, Tel-Aviv University Lecture 5, Low-Level Vulnerabilities
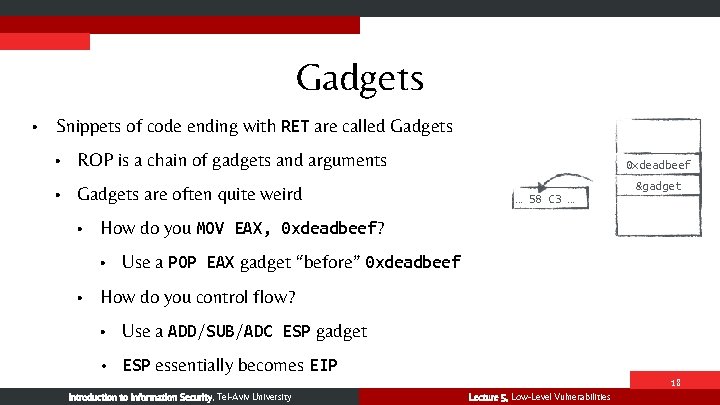
Gadgets • Snippets of code ending with RET are called Gadgets • ROP is a chain of gadgets and arguments • Gadgets are often quite weird • … 58 C 3 … &gadget How do you MOV EAX, 0 xdeadbeef? • • 0 xdeadbeef Use a POP EAX gadget “before” 0 xdeadbeef How do you control flow? • Use a ADD/SUB/ADC ESP gadget • ESP essentially becomes EIP 18 Introduction to Information Security, Tel-Aviv University Lecture 5, Low-Level Vulnerabilities
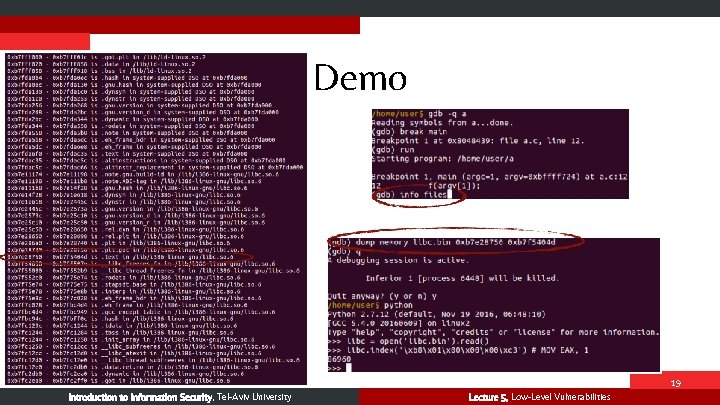
Demo 19 Introduction to Information Security, Tel-Aviv University Lecture 5, Low-Level Vulnerabilities

Gadget finder rop. py 20 Introduction to Information Security, Tel-Aviv University Lecture 5, Low-Level Vulnerabilities
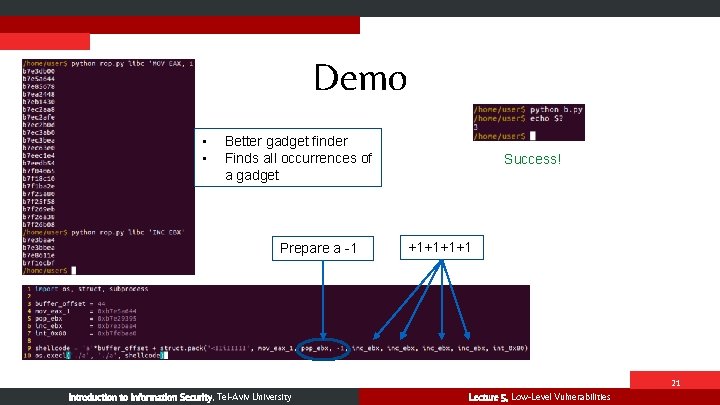
Demo • • Better gadget finder Finds all occurrences of a gadget Prepare a -1 Success! +1+1 21 Introduction to Information Security, Tel-Aviv University Lecture 5, Low-Level Vulnerabilities
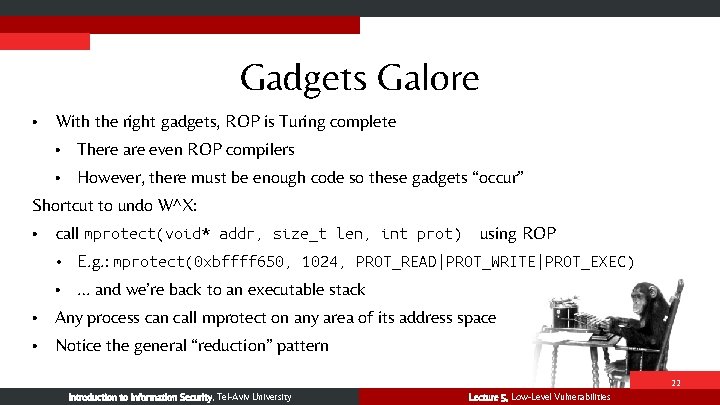
Gadgets Galore • With the right gadgets, ROP is Turing complete • There are even ROP compilers • However, there must be enough code so these gadgets “occur” Shortcut to undo W^X: • call mprotect(void* addr, size_t len, int prot) using ROP • E. g. : mprotect(0 xbffff 650, 1024, PROT_READ|PROT_WRITE|PROT_EXEC) • … and we’re back to an executable stack • Any process can call mprotect on any area of its address space • Notice the general “reduction” pattern 22 Introduction to Information Security, Tel-Aviv University Lecture 5, Low-Level Vulnerabilities
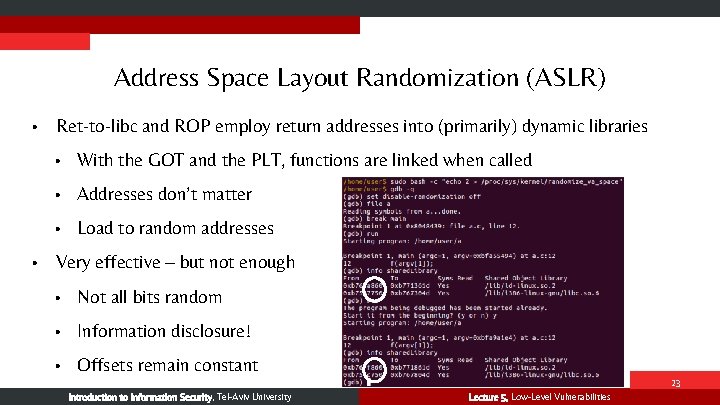
Address Space Layout Randomization (ASLR) • • Ret-to-libc and ROP employ return addresses into (primarily) dynamic libraries • With the GOT and the PLT, functions are linked when called • Addresses don’t matter • Load to random addresses Very effective – but not enough • Not all bits random • Information disclosure! • Offsets remain constant 23 Introduction to Information Security, Tel-Aviv University Lecture 5, Low-Level Vulnerabilities
A Solid Defense: Shadow Stack • CALL pushes to both the stack and the shadow stack • RET pops from both the stack and the shadow stack • If the addresses don’t match, the program crashes The shadow stack can’t be tampered • • • Intel Control-Flow Enforcement Technology (CET) • Shadow stack to be controlled in hardware; • not available yet (Oct/2017) … Once deployed - RIP ROP? 24 Introduction to Information Security, Tel-Aviv University Lecture 5, Low-Level Vulnerabilities
Heap Overflows Introduction to Information Security, Tel-Aviv University Lecture 5, Low-Level Vulnerabilities
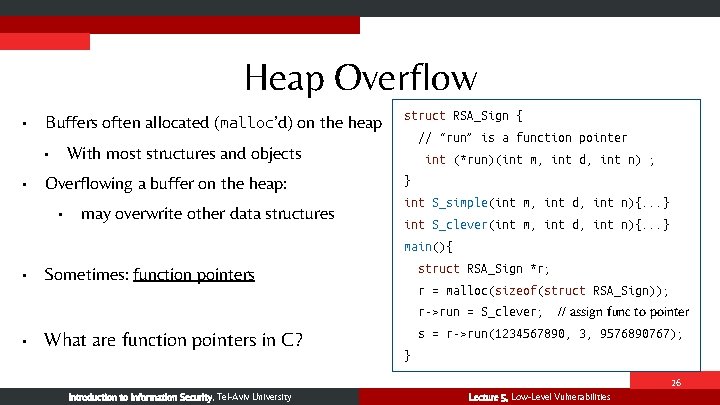
Heap Overflow • Buffers often allocated (malloc’d) on the heap // “run” is a function pointer With most structures and objects • • struct RSA_Sign { Overflowing a buffer on the heap: • may overwrite other data structures int (*run)(int m, int d, int n) ; } int S_simple(int m, int d, int n){. . . } int S_clever(int m, int d, int n){. . . } main(){ • struct RSA_Sign *r; Sometimes: function pointers r = malloc(sizeof(struct RSA_Sign)); r->run = S_clever; // assign func to pointer • What are function pointers in C? s = r->run(1234567890, 3, 9576890767); } 26 Introduction to Information Security, Tel-Aviv University Lecture 5, Low-Level Vulnerabilities
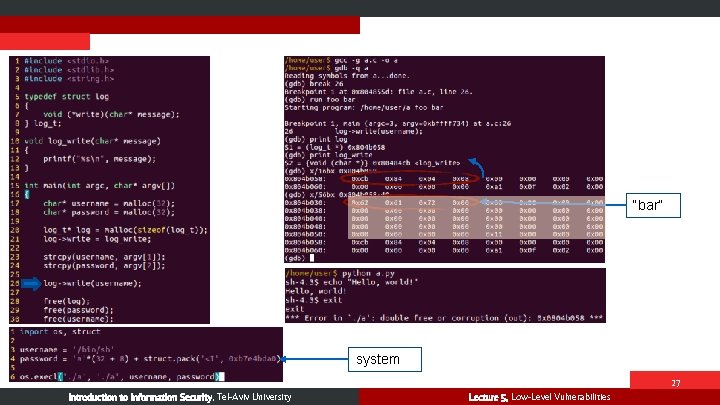
Demo “bar” system 27 Introduction to Information Security, Tel-Aviv University Lecture 5, Low-Level Vulnerabilities
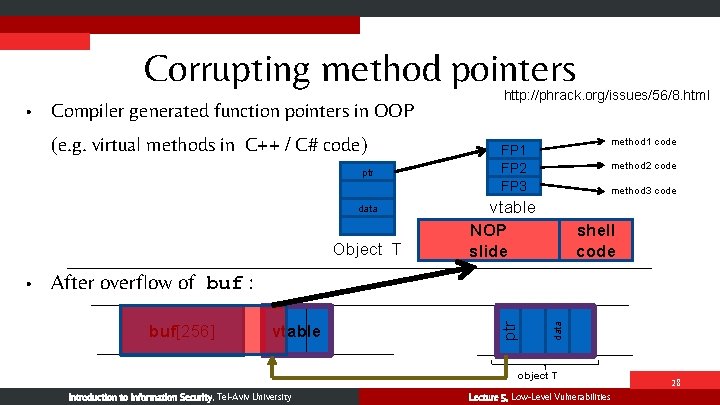
Corrupting method pointers Compiler generated function pointers in OOP (e. g. virtual methods in C++ / C# code) ptr data Object T method 2 code method 3 code vtable NOP slide shell code After overflow of buf : buf[256] vtable data • method 1 code FP 1 FP 2 FP 3 ptr • http: //phrack. org/issues/56/8. html object T Introduction to Information Security, Tel-Aviv University Lecture 5, Low-Level Vulnerabilities 28
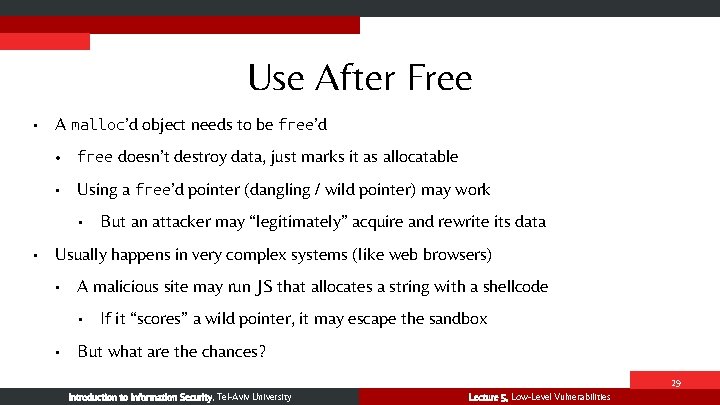
Use After Free • A malloc’d object needs to be free’d • free doesn’t destroy data, just marks it as allocatable • Using a free’d pointer (dangling / wild pointer) may work • • But an attacker may “legitimately” acquire and rewrite its data Usually happens in very complex systems (like web browsers) • A malicious site may run JS that allocates a string with a shellcode • • If it “scores” a wild pointer, it may escape the sandbox But what are the chances? 29 Introduction to Information Security, Tel-Aviv University Lecture 5, Low-Level Vulnerabilities
![Heap Spraying [Sky. Lined 2004] Idea: • use Javascript to spray heap with shellcode Heap Spraying [Sky. Lined 2004] Idea: • use Javascript to spray heap with shellcode](http://slidetodoc.com/presentation_image_h/05a3b2f2e403eac1e68e70bc8b955751/image-30.jpg)
Heap Spraying [Sky. Lined 2004] Idea: • use Javascript to spray heap with shellcode (and NOP slides) • then overwrite vtable ptr to point anywhere in spray area NOP slide shellcode heap vtable heap spray area Introduction to Information Security, Tel-Aviv University 30 Lecture 5, Low-Level Vulnerabilities
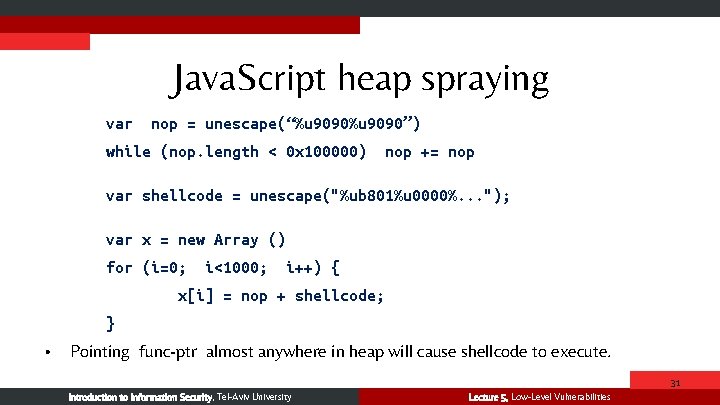
Java. Script heap spraying var nop = unescape(“%u 9090”) while (nop. length < 0 x 100000) nop += nop var shellcode = unescape("%ub 801%u 0000%. . . "); var x = new Array () for (i=0; i<1000; i++) { x[i] = nop + shellcode; } • Pointing func-ptr almost anywhere in heap will cause shellcode to execute. 31 Introduction to Information Security, Tel-Aviv University Lecture 5, Low-Level Vulnerabilities
Properties of Heap Spray • In 32 -bit systems, this is quite useful • In 64 -bit systems, not so much • • Although targeted heap sprays are still used Note: heap spray is not a vulnerability, but a method to boost one 32 Introduction to Information Security, Tel-Aviv University Lecture 5, Low-Level Vulnerabilities
Attacking malloc/free subsystems Introduction to Information Security, Tel-Aviv University Lecture 5, Low-Level Vulnerabilities
Metadata Corruption • The heap is actually a data structure managed by malloc and free • Various implementations exist • Each implementation has some metadata… • • • The block size, whether it’s allocated, etc. … And the data itself (the pointer returned by malloc) We can overwrite the metadata • And crash the program on subsequent mallocs / frees 34 Introduction to Information Security, Tel-Aviv University Lecture 5, Low-Level Vulnerabilities
35 Introduction to Information Security, Tel-Aviv University Lecture 5, Low-Level Vulnerabilities
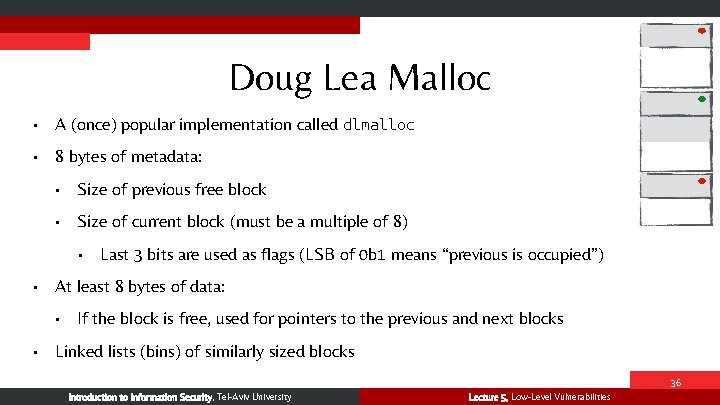
Doug Lea Malloc • A (once) popular implementation called dlmalloc • 8 bytes of metadata: • Size of previous free block • Size of current block (must be a multiple of 8) • • At least 8 bytes of data: • • Last 3 bits are used as flags (LSB of 0 b 1 means “previous is occupied”) If the block is free, used for pointers to the previous and next blocks Linked lists (bins) of similarly sized blocks 36 Introduction to Information Security, Tel-Aviv University Lecture 5, Low-Level Vulnerabilities
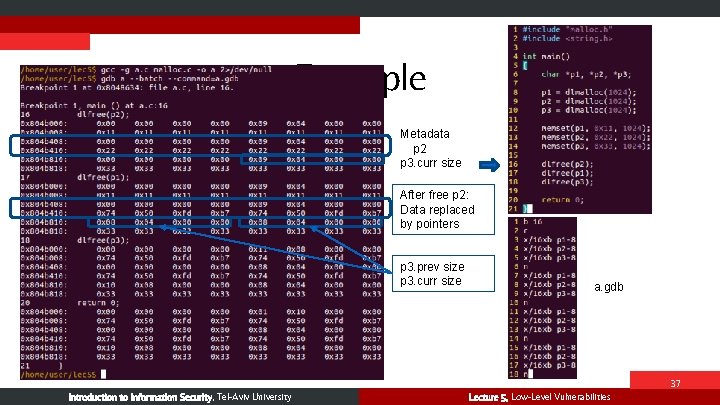
Example Metadata p 2 p 3. curr size After free p 2: Data replaced by pointers p 3. prev size p 3. curr size a. gdb 37 Introduction to Information Security, Tel-Aviv University Lecture 5, Low-Level Vulnerabilities
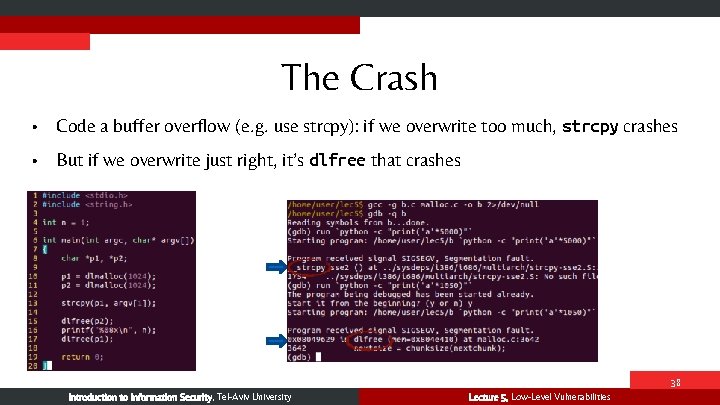
The Crash • Code a buffer overflow (e. g. use strcpy): if we overwrite too much, strcpy crashes • But if we overwrite just right, it’s dlfree that crashes 38 Introduction to Information Security, Tel-Aviv University Lecture 5, Low-Level Vulnerabilities
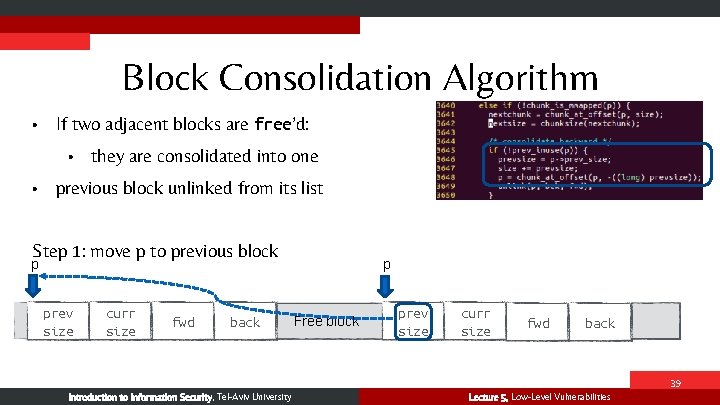
Block Consolidation Algorithm • If two adjacent blocks are free’d: • • they are consolidated into one previous block unlinked from its list Step 1: move p to previous block p prev size curr size fwd back p Free block prev size curr size fwd back 39 Introduction to Information Security, Tel-Aviv University Lecture 5, Low-Level Vulnerabilities
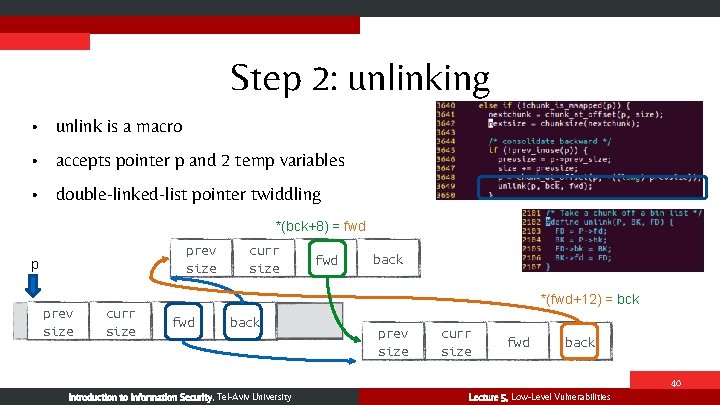
Step 2: unlinking • unlink is a macro • accepts pointer p and 2 temp variables • double-linked-list pointer twiddling *(bck+8) = fwd prev size p prev size curr size fwd back *(fwd+12) = bck fwd back prev size curr size fwd back 40 Introduction to Information Security, Tel-Aviv University Lecture 5, Low-Level Vulnerabilities
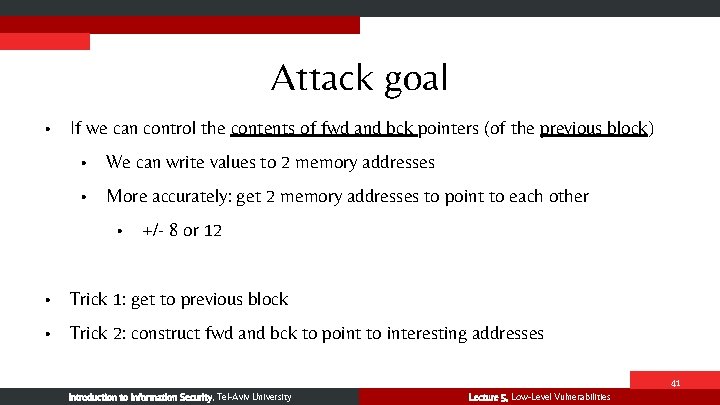
Attack goal • If we can control the contents of fwd and bck pointers (of the previous block) • We can write values to 2 memory addresses • More accurately: get 2 memory addresses to point to each other • +/- 8 or 12 • Trick 1: get to previous block • Trick 2: construct fwd and bck to point to interesting addresses 41 Introduction to Information Security, Tel-Aviv University Lecture 5, Low-Level Vulnerabilities
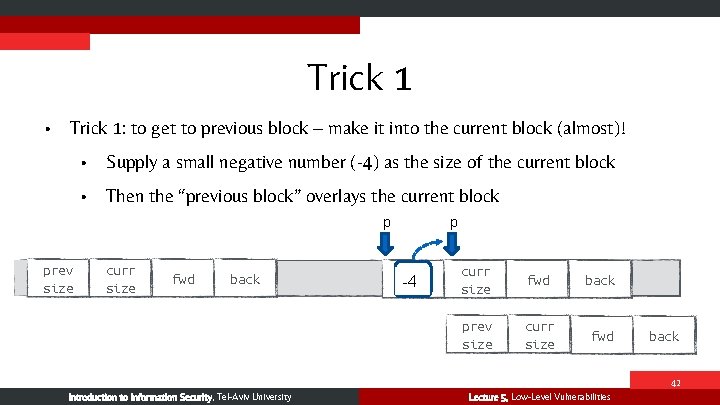
Trick 1 • Trick 1: to get to previous block – make it into the current block (almost)! • Supply a small negative number (-4) as the size of the current block • Then the “previous block” overlays the current block p prev size curr size fwd back p prev -4 size curr size fwd back prev size curr size fwd back 42 Introduction to Information Security, Tel-Aviv University Lecture 5, Low-Level Vulnerabilities
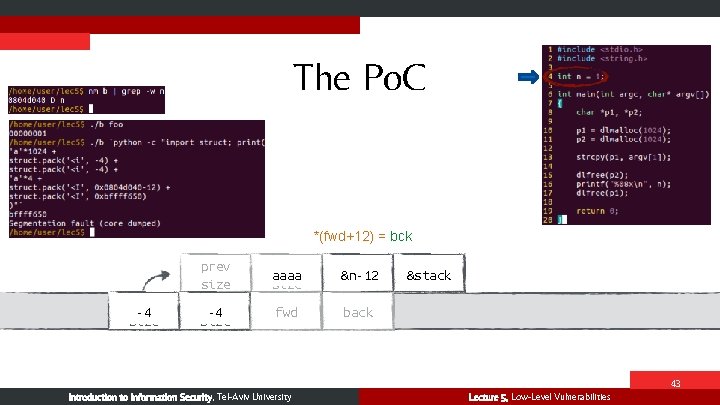
The Po. C *(fwd+12) = bck prev -4 size prev size curr -4 size curr aaaa size &n-12 fwd back &stack 43 Introduction to Information Security, Tel-Aviv University Lecture 5, Low-Level Vulnerabilities
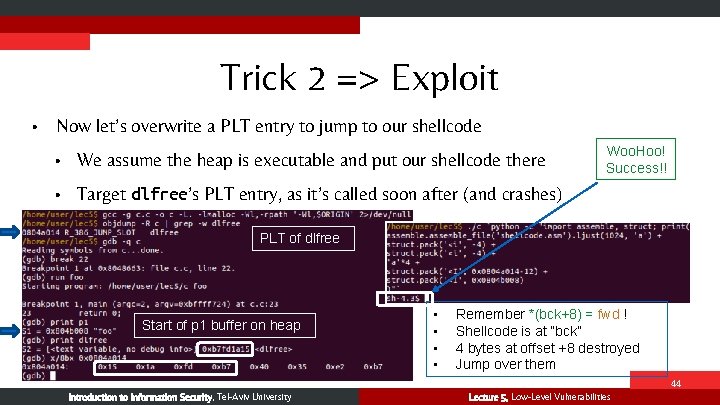
Trick 2 => Exploit • Now let’s overwrite a PLT entry to jump to our shellcode • We assume the heap is executable and put our shellcode there • Target dlfree’s PLT entry, as it’s called soon after (and crashes) Woo. Hoo! Success!! PLT of dlfree Start of p 1 buffer on heap • • Remember *(bck+8) = fwd ! Shellcode is at “bck” 4 bytes at offset +8 destroyed Jump over them 44 Introduction to Information Security, Tel-Aviv University Lecture 5, Low-Level Vulnerabilities
45 Introduction to Information Security, Tel-Aviv University Lecture 5, Low-Level Vulnerabilities
Malloc Maleficarum • In 2004, glibc malloc was hardened • • In 2005, Phantasmal Phantasmagoria released 5 (!) heap exploits Pretty intense • https: //sploitfun. wordpress. com/2015/03/04/heap-overflow-using-malloc-maleficarum/ 46 Introduction to Information Security, Tel-Aviv University Lecture 5, Low-Level Vulnerabilities
- Slides: 46