Logical vulnerabilities Web Village Beched Logic vulns Wide

Logical vulnerabilities Web Village Beched
Logic vulns? • Wide range of vulnerability types • Vague definition • How do they differ from other bugs?
Injections • Most of vulnerabilities are injections • Injections change the way how some executable text is parsed • Thus, they break an intended syntax tree of the program
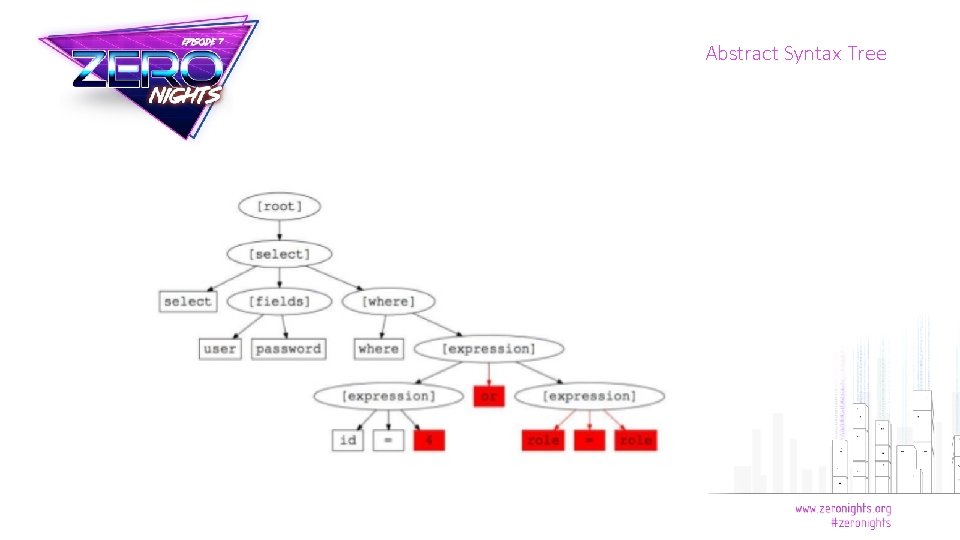
Abstract Syntax Tree

Logical vulnerabilities • Logical vulns do something unexpected • It can be breaking authorization, transaction integrity, process sequence • Thus, they usually do not create new execution paths • Instead, they exploit existence of unintended paths in CFG
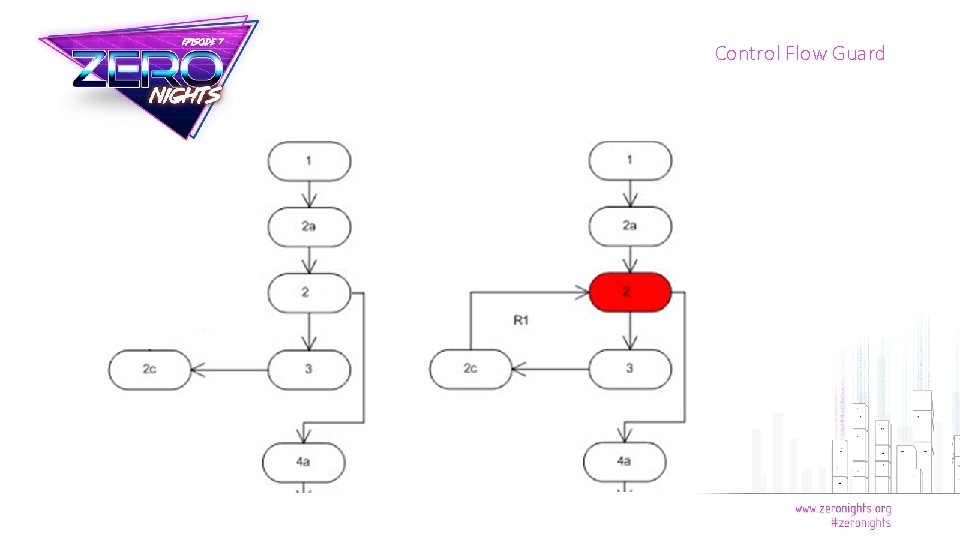
Control Flow Guard
Input validation
Input validation • Input validation is useful not only against injections • Type juggling is painful • There lots of ways you can exploit coding mistake without injection new code • Reason: application expects input of type A with certain contraints but doesn’t validate that
Examples

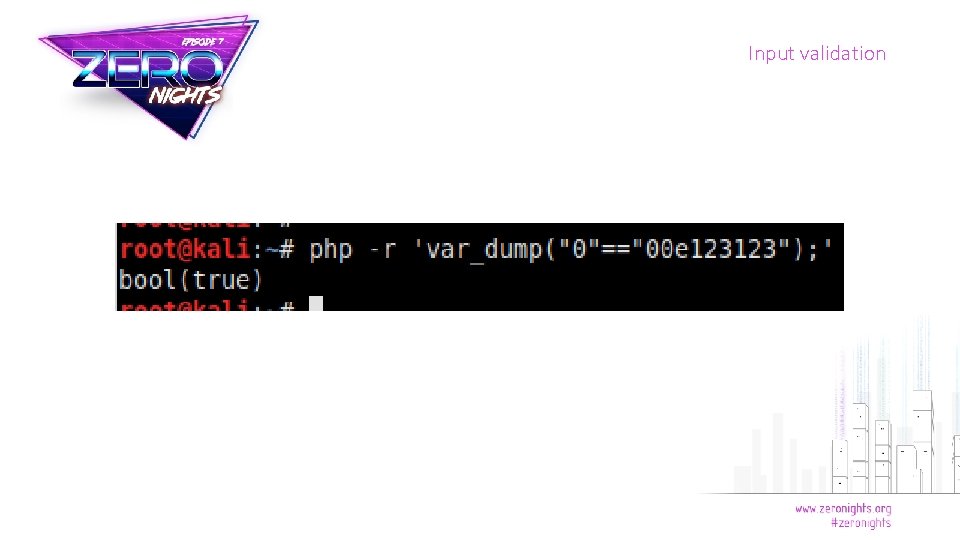
Input validation
Input validation
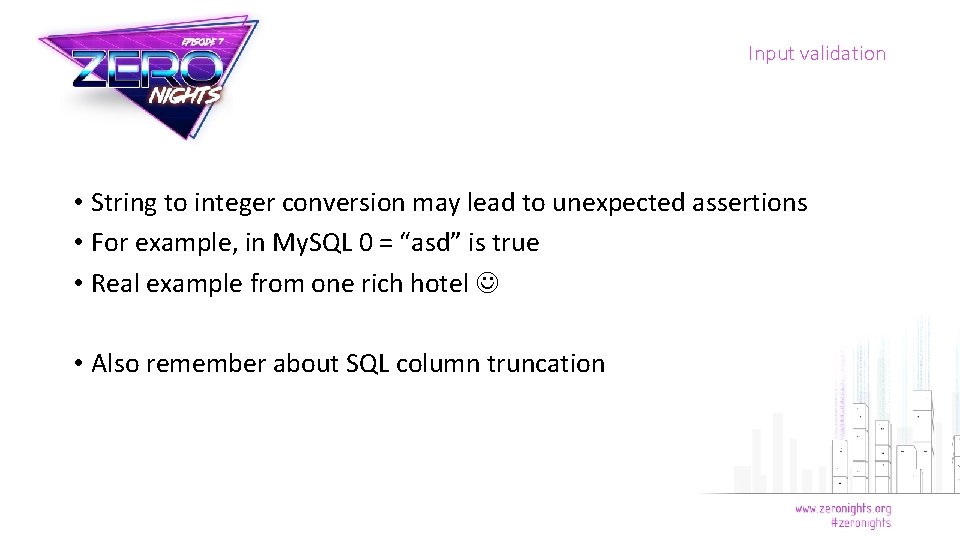
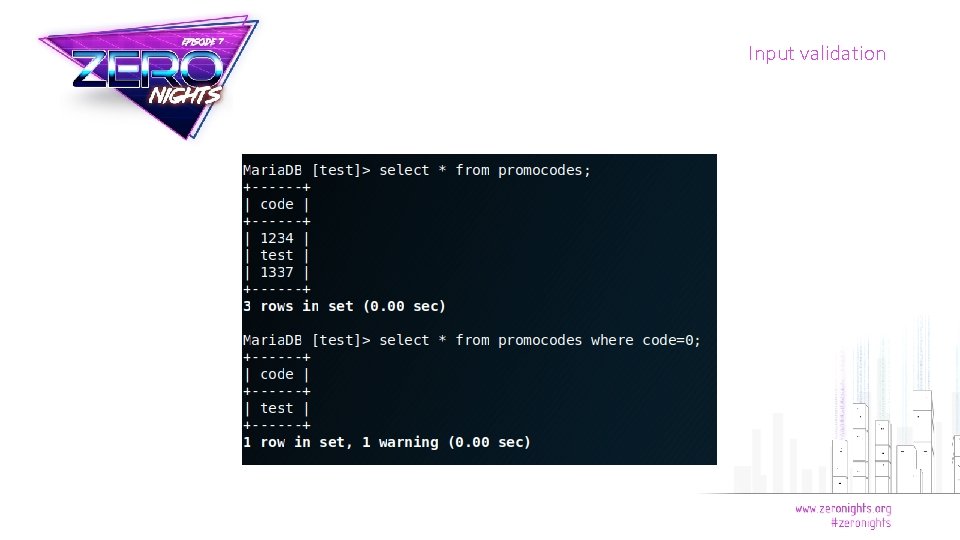
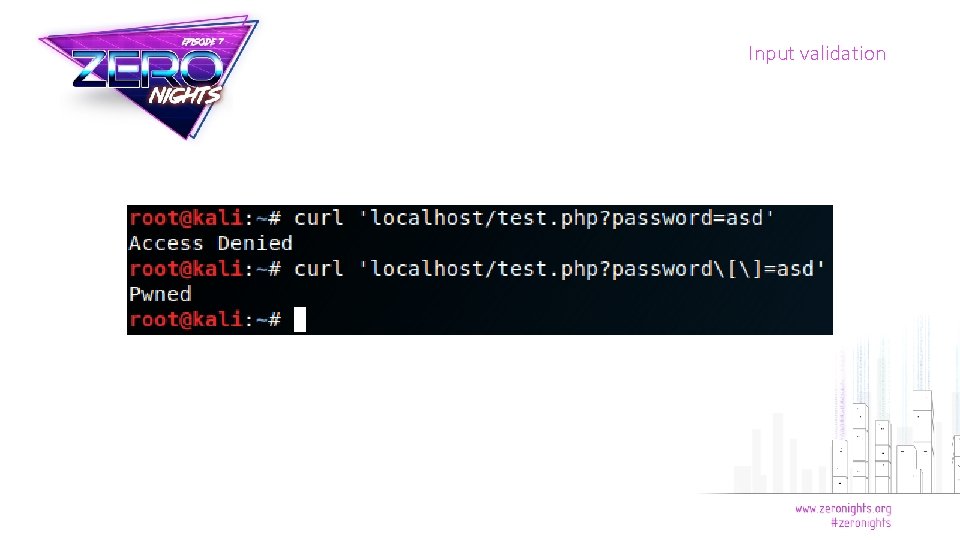
Input validation • String to integer conversion may lead to unexpected assertions • For example, in My. SQL 0 = “asd” is true • Real example from one rich hotel • Also remember about SQL column truncation

Input validation
Input validation

Input validation • PHP Warning: strcmp() expects parameter 2 to be string, array given • strcmp(‘asd’, []) returns NULL • NULL == 0 is true • Real example from CSAW CTF scoreboard lol
Input validation

Input validation
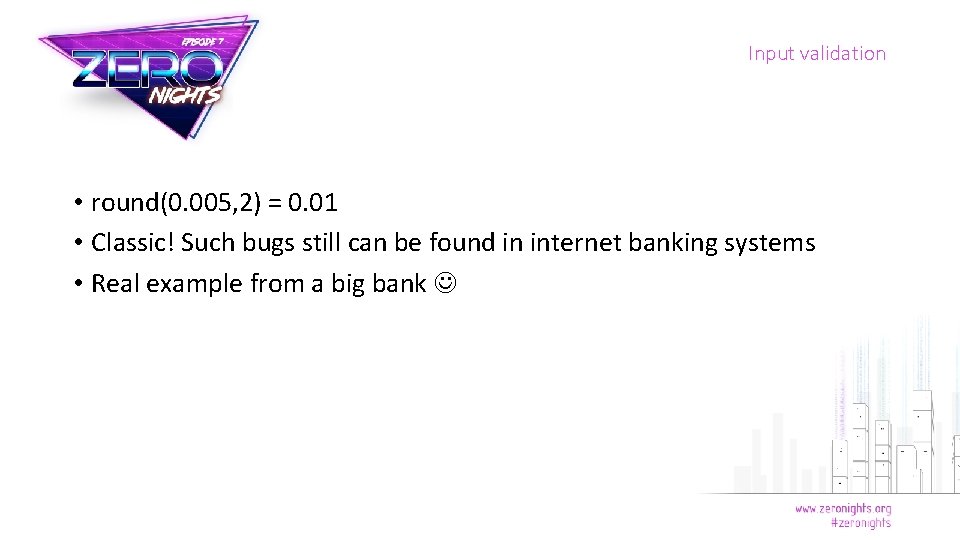
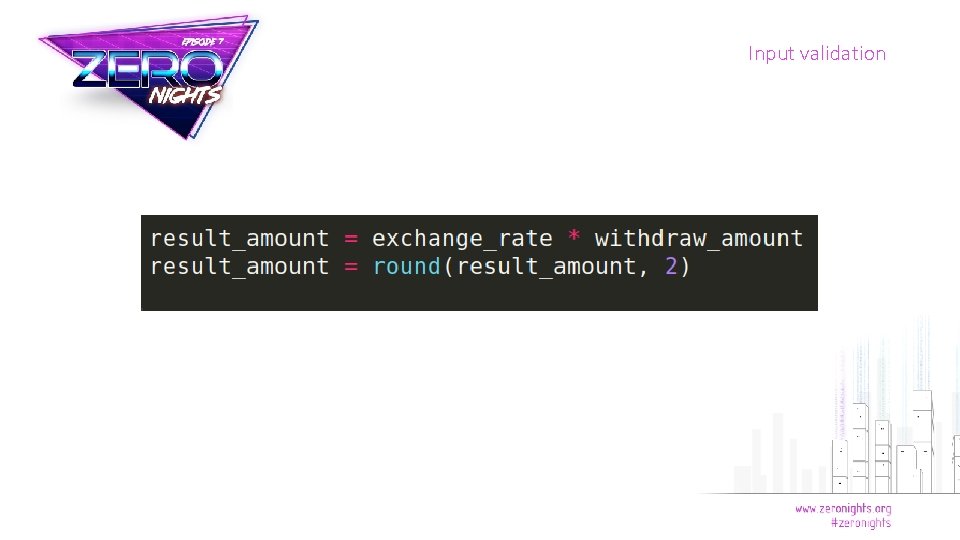
Input validation • round(0. 005, 2) = 0. 01 • Classic! Such bugs still can be found in internet banking systems • Real example from a big bank
Input validation
Input validation

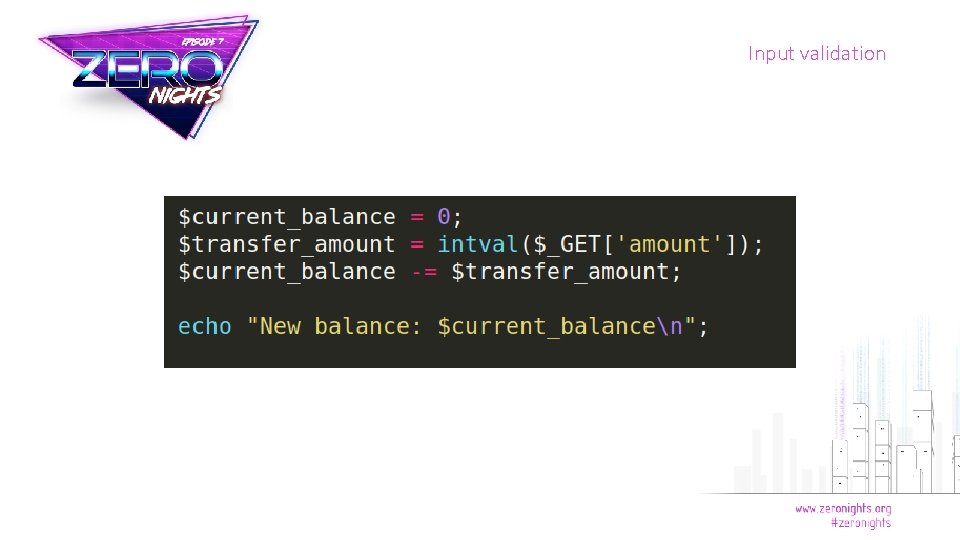
Input validation • Stupid and obvious negative sum transaction • Still can be found in online gaming and other products with custom financial logic • Real example from some Chinese game
Input validation

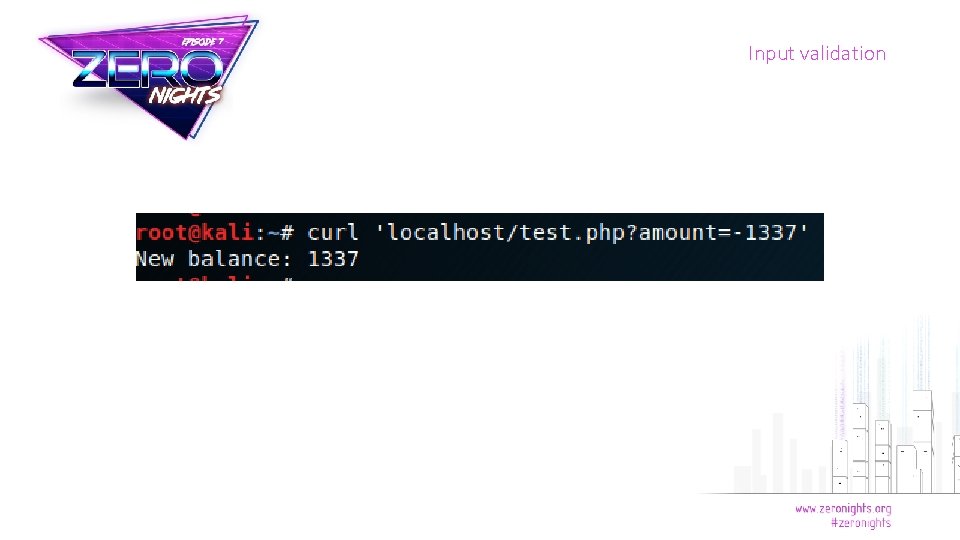
Input validation • Merchant’s callback may ignore LMI_PAYMENT_AMOUNT value • We can buy anything for 0. 01 WMR • Real old bug from many shops

Input validation
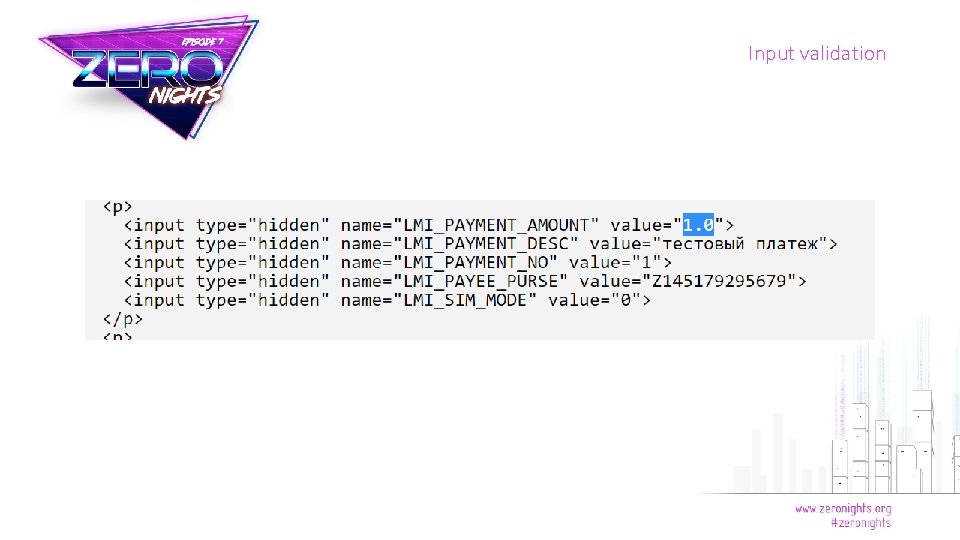
Input validation
Input validation • How to check for such bug: https: //github. com/beched/php_hash_collision_finder • Real bug from some payment API

Authorization
Authorization • Authorization controls often consider only intended ways of interaction • Often controls are applied only on client side • Also there may be no controls, and objects may have predictable identifiers • Logical vulnerabilities can abuse different aspects of authorization and ACL • Very typical for mobile interfaces
Examples
Authorization • Remember payment gateway? • You can search callback location and test it directly • Does it allow requests from any IP address? • Does it properly check for signature?
Authorization
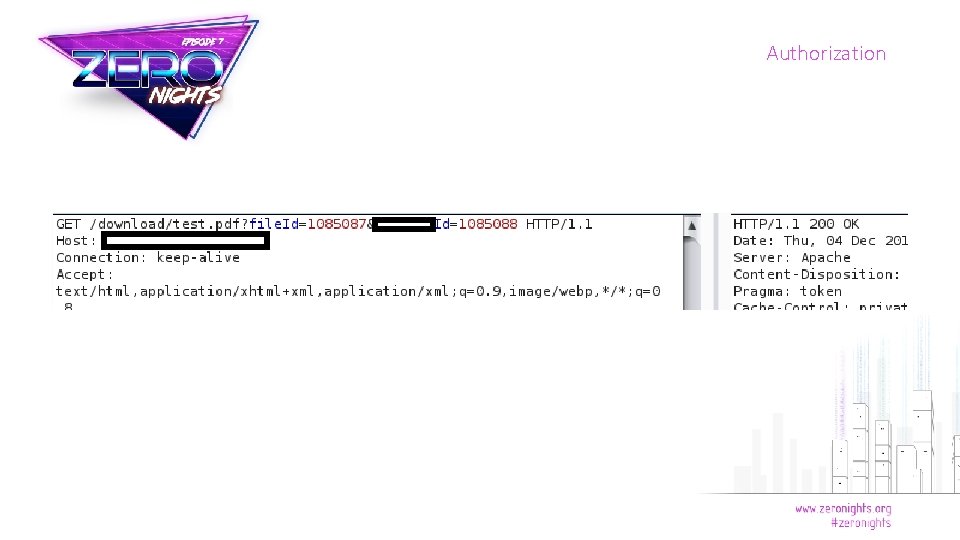
Authorization • This is Insecure Direct Object Reference • Ubiquitous vulnerability • Parameter file. Id is predictable (incrementing integer) • We can view documents of other users • Real bug from tender platform

Authorization
Authorization • Administrative interface accessible for everybody • PHP’s header function does not terminate execution • It only redirects the browser • Real bug from a lot of shitty sites
Authorization
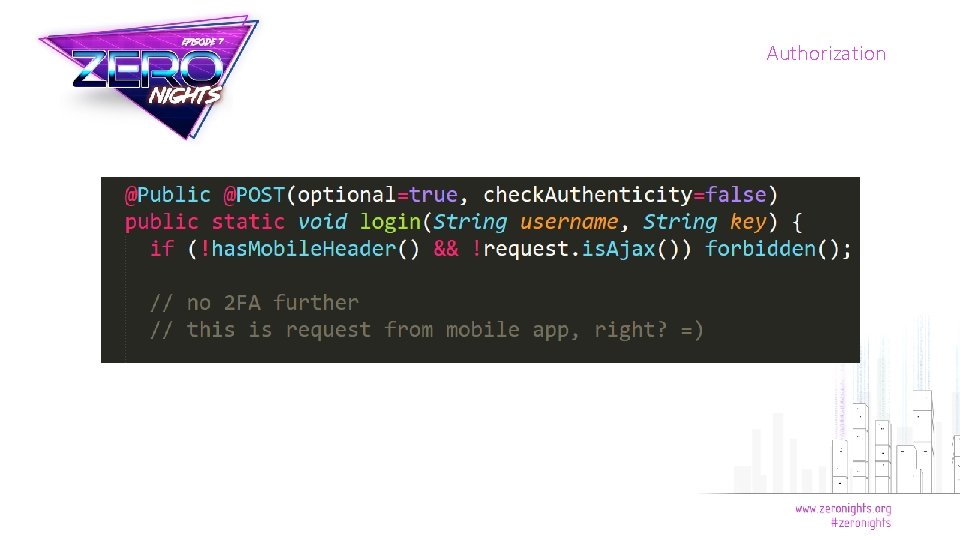
Authorization • Mobile interface lacks 2 FA • But the sessions are shared with main website • Thus we can bypass 2 FA if we send appropriate header mimicking mobile app • Real bug from internet banking system

Time Magic
Time Magic • A lot of logical vulnerabilities exist due to incorrect management of time • Those include: • • Timing information leakage Request reissue, token reuse Race conditions. . .

Examples

Time Magic
Time Magic • What if SQL servers get too busy during user_exists() execution? • Real bug from CMS • Hint: you can find some kind of 0 -days with example
Time Magic
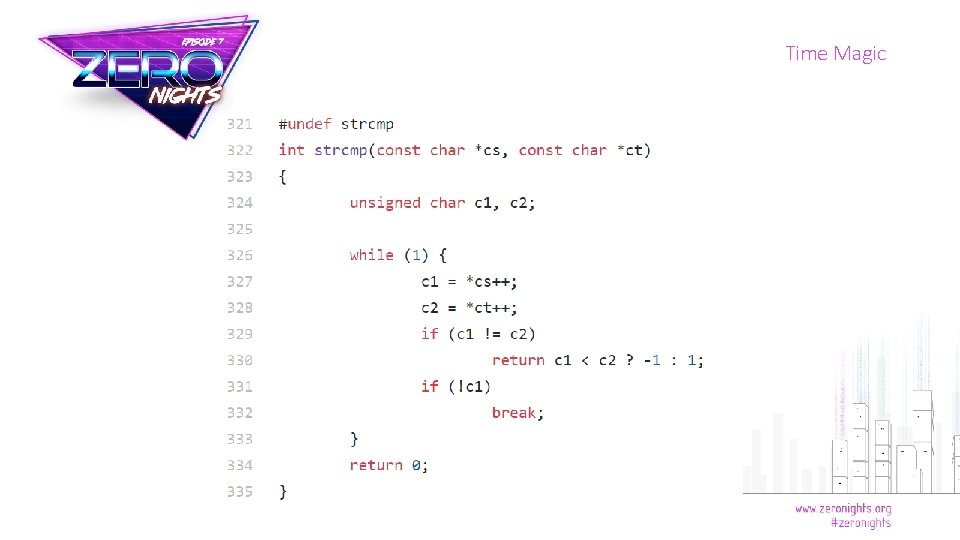
Time Magic • Standard implementation of strcmp function in Libc is vulnerable to timing attacks • You should use cryptographically secure bitwise comparison • Such attacks are not very easy to carry out remotely
Time Magic • Sequence breaking – omit or shuffle the steps of some process to get unexpected results • For instance, skip user activation after registration and access site immediately • Or skip token check for password restore and jump directly to password change
Time Magic
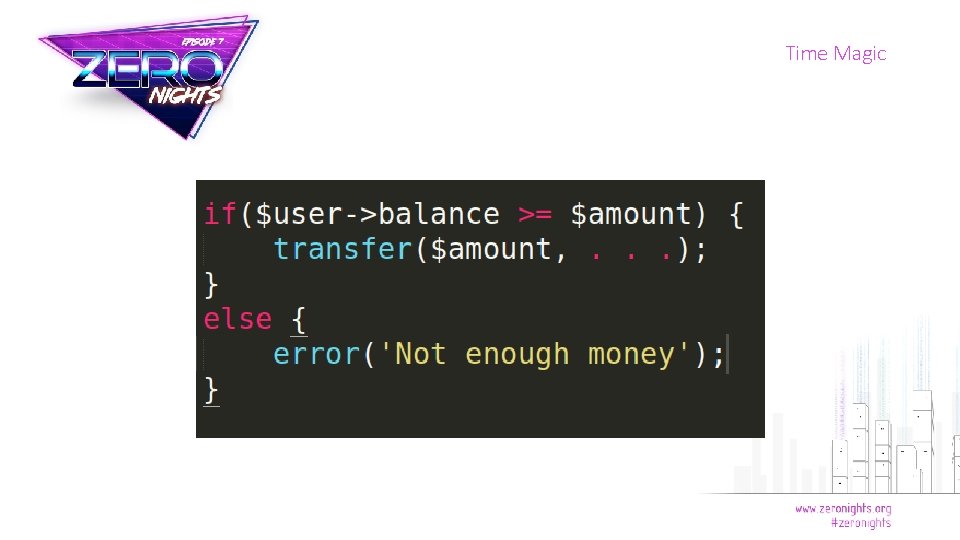
Time Magic • Typical race condition vulnerability • Send several requests at once and drain the balance below 0 • One should use SQL transactions to fix this • Real bug from different payment systems

Request Forgery
Request Forgery • A lot of logical attacks can be classified as request forgery • This is general name for attacks which send unexpected input to an application • Many examples from this talk are input forgery attacks
Request Forgery • Cross-Site Request Forgery • Logical vulnerability? Yes, in some way • Requires user interaction • Anyway, often quite underestimated • You can do a lot!

- Slides: 50