Introduction to Unix CS 21 Lecture 3 Lecture
- Slides: 39
Introduction to Unix – CS 21 Lecture 3
Lecture Overview n n Lab review More on files and listings Disk usage and compressing files Permissions and ownership
How Did Lab Go? n n What was missing? What did I want you to get out of it? n n 1. Basic differences between Windows and Unix 2. Difference between a good design and a bad design n A, b, x don’t really make good descriptions
Lab Continued n n n 3. Getting used to navigating the system 4. rmdir can only remove empty directories 5. A lot of environment variables are automatically set, but not every one will be used every time 6. Difference between an environment variable and a local variable 7. Get used to reading man pages 8. Think about the future
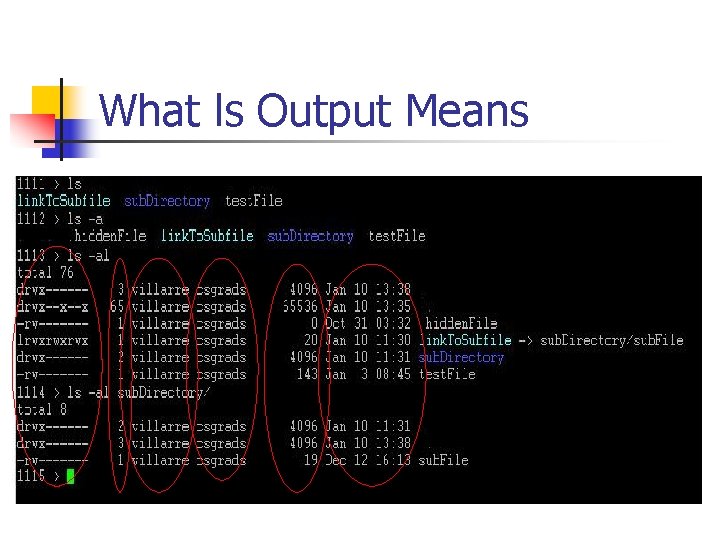
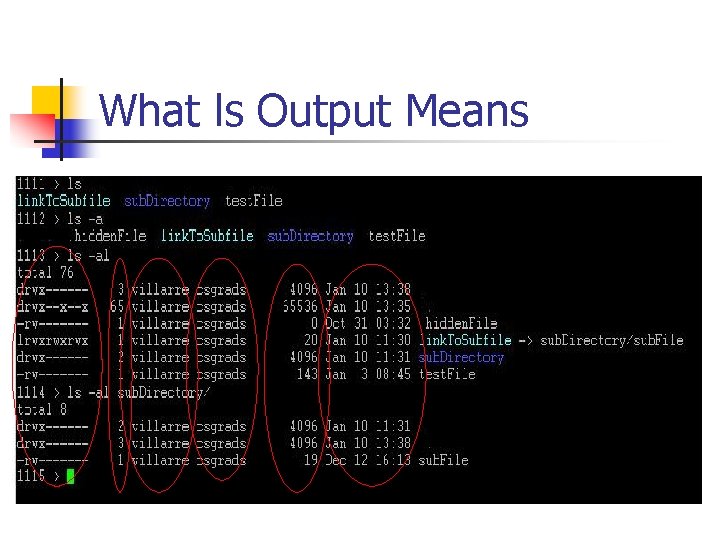
What ls Output Means
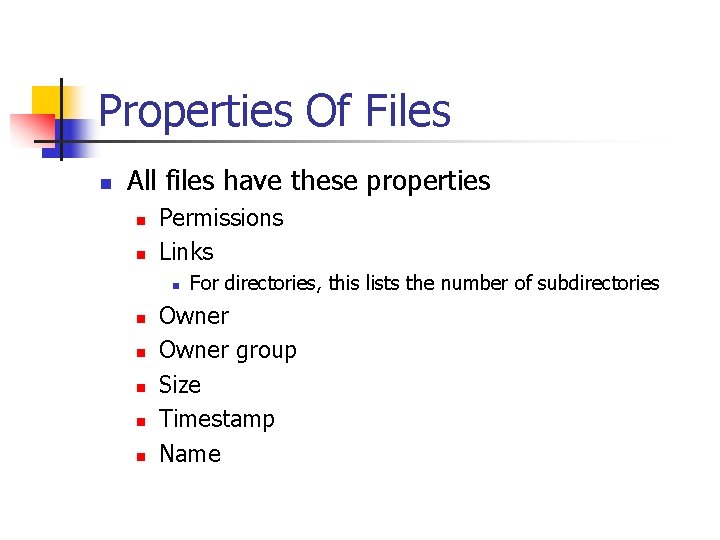
Properties Of Files n All files have these properties n n Permissions Links n n n For directories, this lists the number of subdirectories Owner group Size Timestamp Name
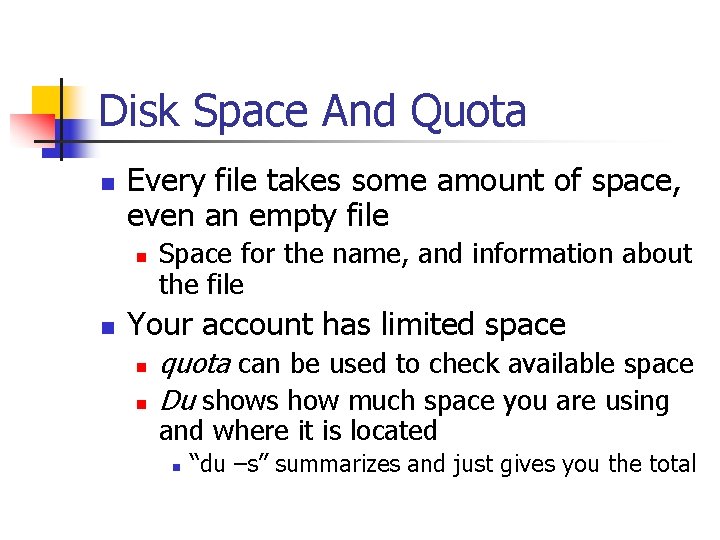
Disk Space And Quota n Every file takes some amount of space, even an empty file n n Space for the name, and information about the file Your account has limited space n n quota can be used to check available space Du shows how much space you are using and where it is located n “du –s” summarizes and just gives you the total
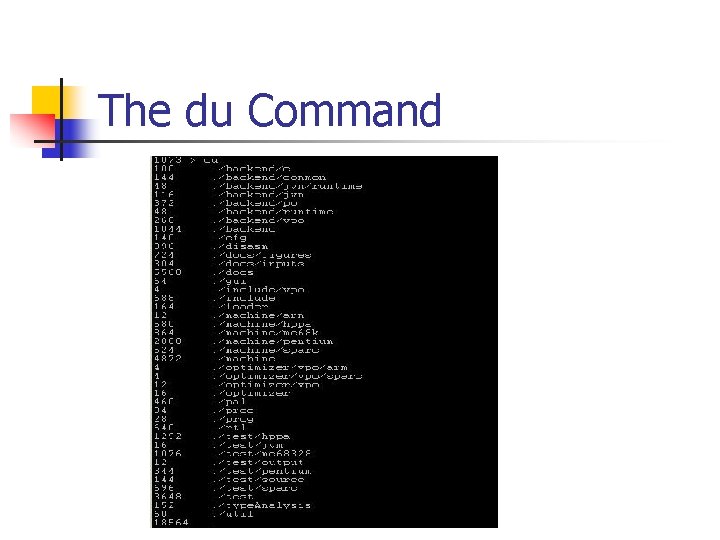
The du Command
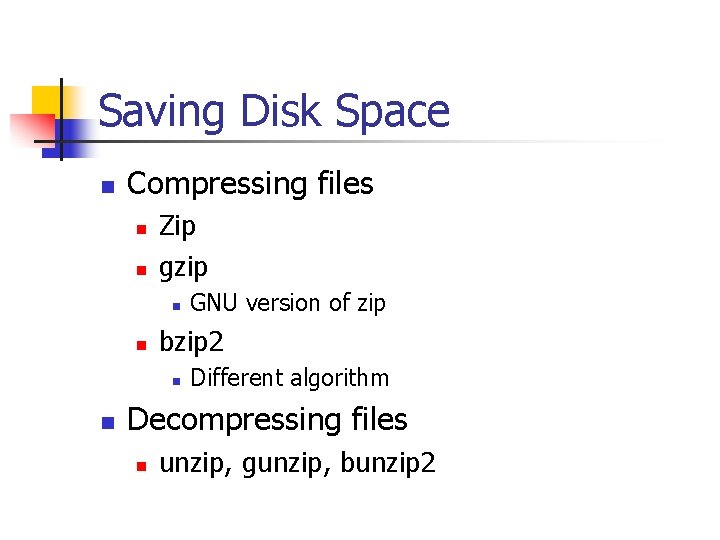
Saving Disk Space n Compressing files n n Zip gzip n n bzip 2 n n GNU version of zip Different algorithm Decompressing files n unzip, gunzip, bunzip 2
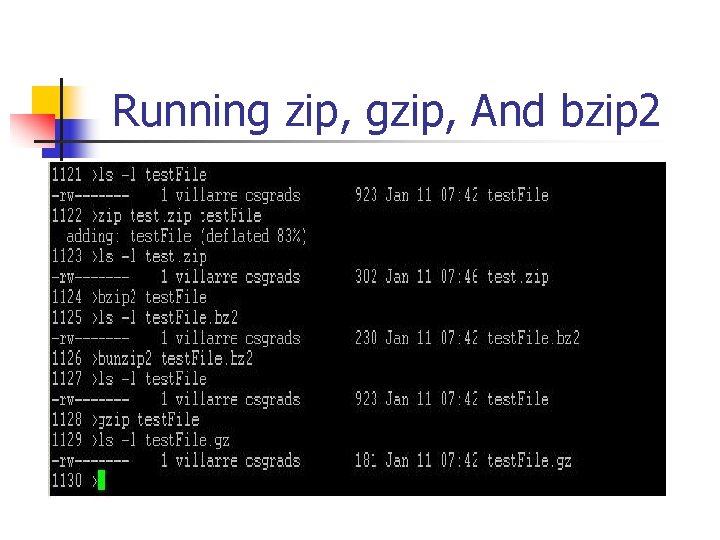
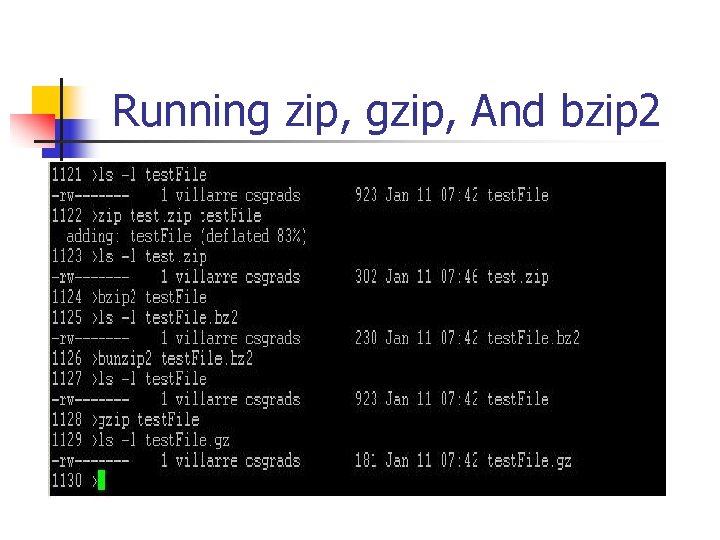
Running zip, gzip, And bzip 2
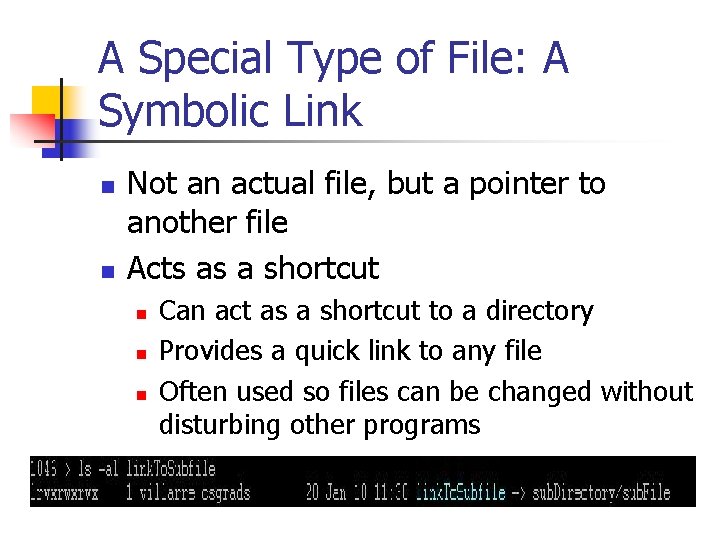
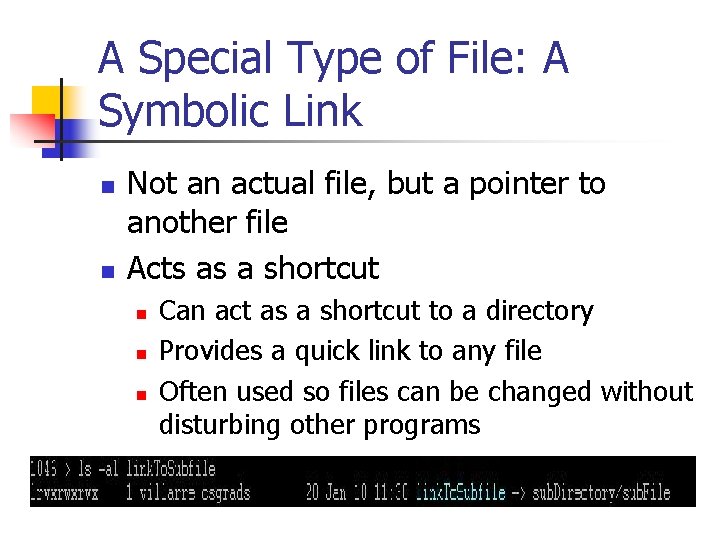
A Special Type of File: A Symbolic Link n n Not an actual file, but a pointer to another file Acts as a shortcut n n n Can act as a shortcut to a directory Provides a quick link to any file Often used so files can be changed without disturbing other programs
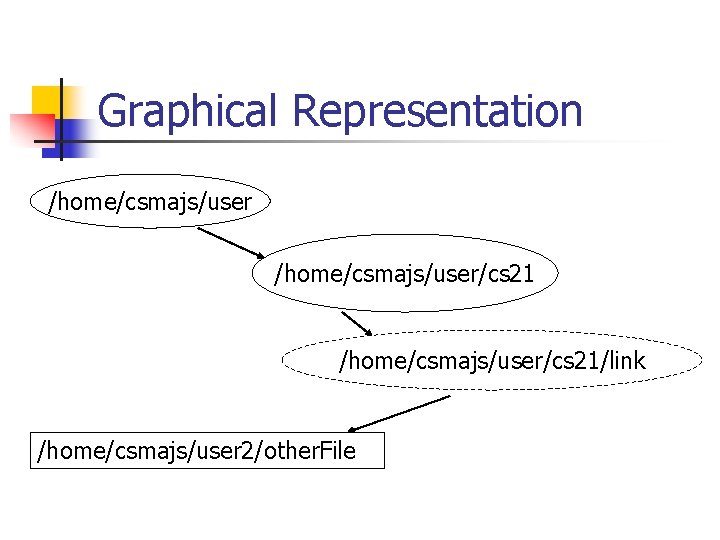
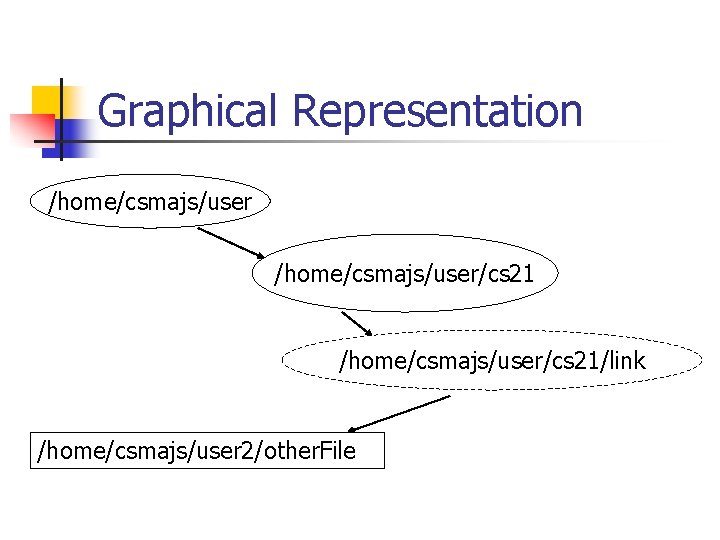
Graphical Representation /home/csmajs/user/cs 21/link /home/csmajs/user 2/other. File
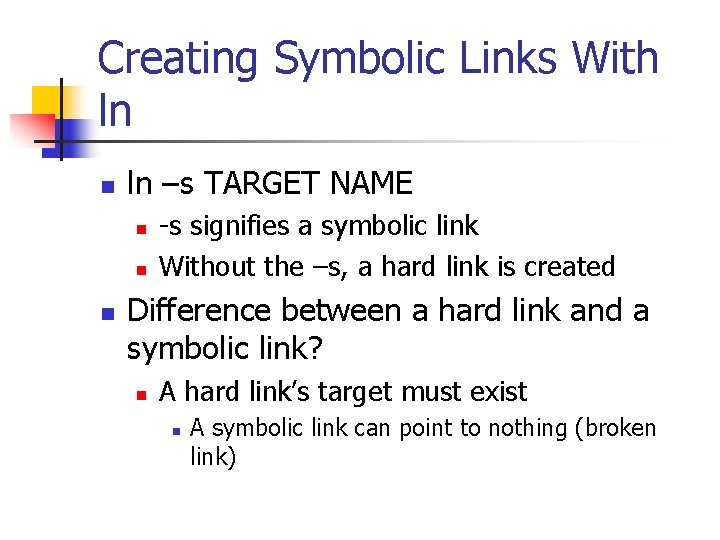
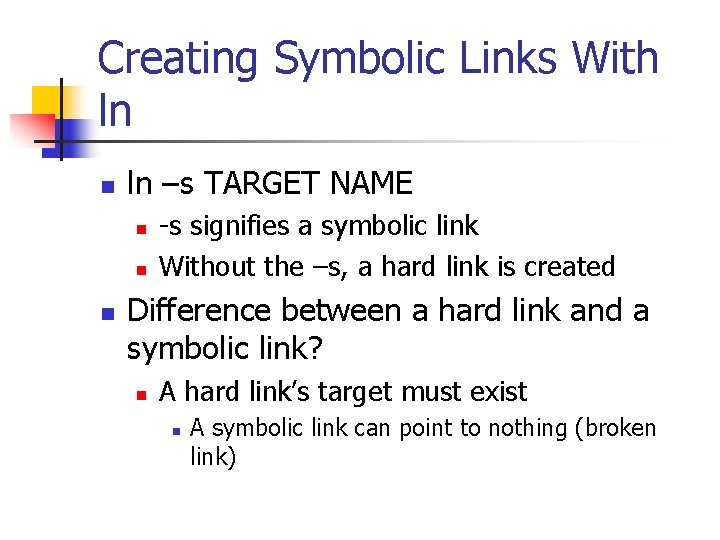
Creating Symbolic Links With ln n ln –s TARGET NAME n n n -s signifies a symbolic link Without the –s, a hard link is created Difference between a hard link and a symbolic link? n A hard link’s target must exist n A symbolic link can point to nothing (broken link)
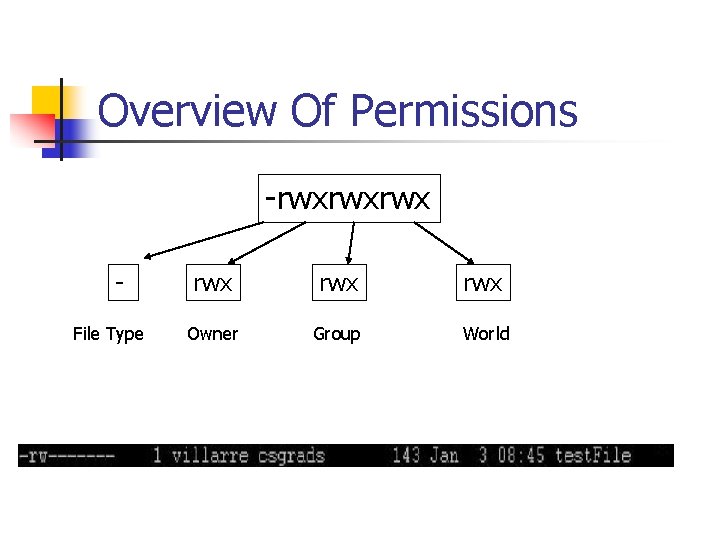
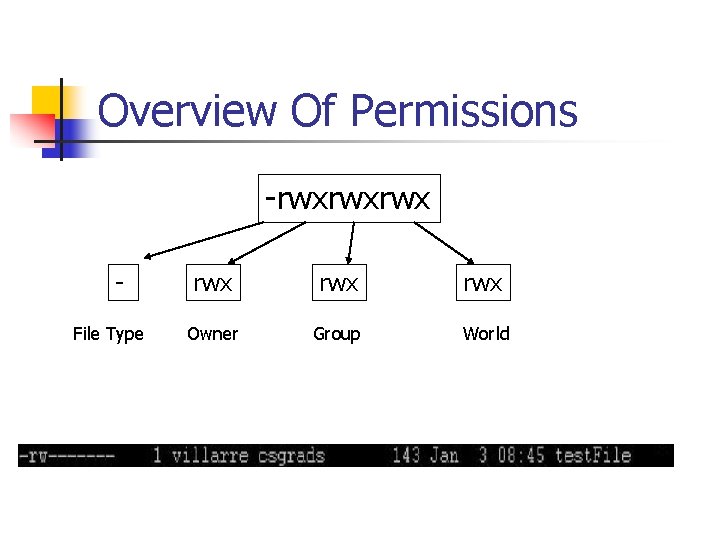
Overview Of Permissions -rwxrwxrwx File Type rwx rwx Owner Group World
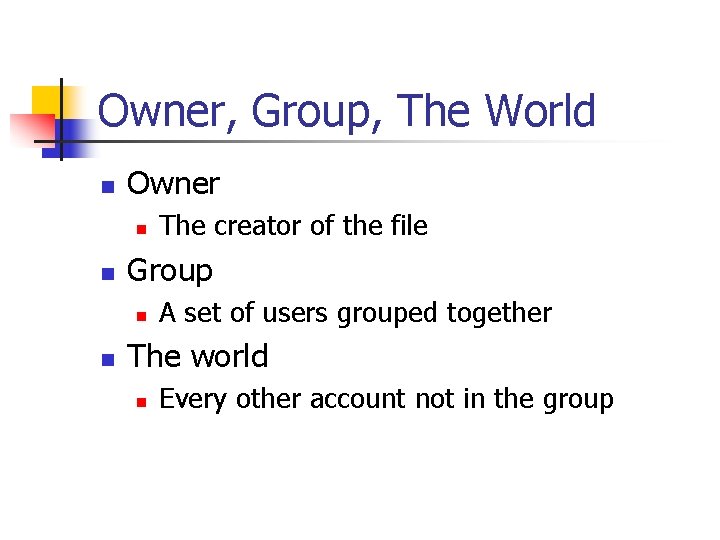
Owner, Group, The World n Owner n n Group n n The creator of the file A set of users grouped together The world n Every other account not in the group
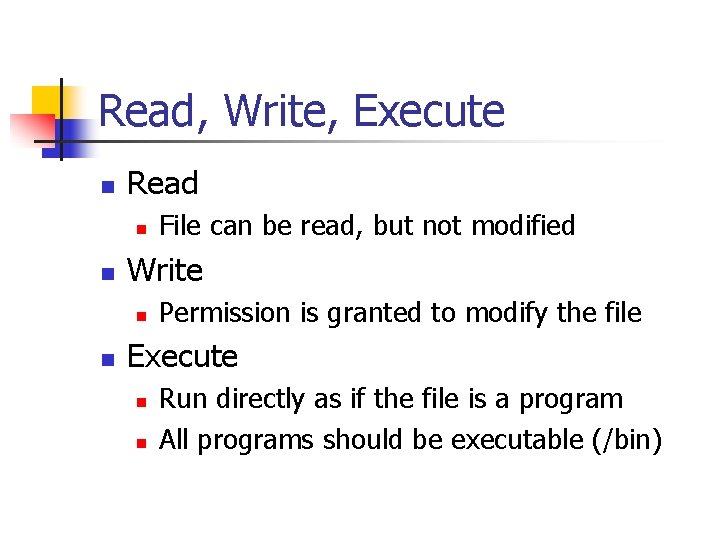
Read, Write, Execute n Read n n Write n n File can be read, but not modified Permission is granted to modify the file Execute n n Run directly as if the file is a program All programs should be executable (/bin)
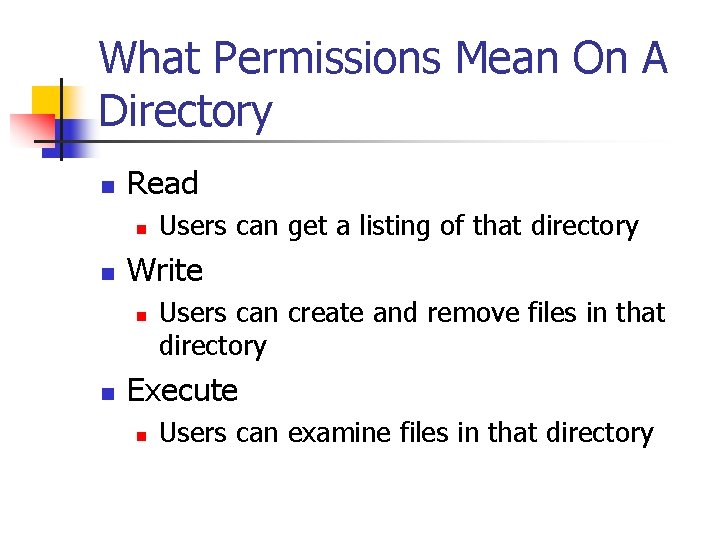
What Permissions Mean On A Directory n Read n n Write n n Users can get a listing of that directory Users can create and remove files in that directory Execute n Users can examine files in that directory
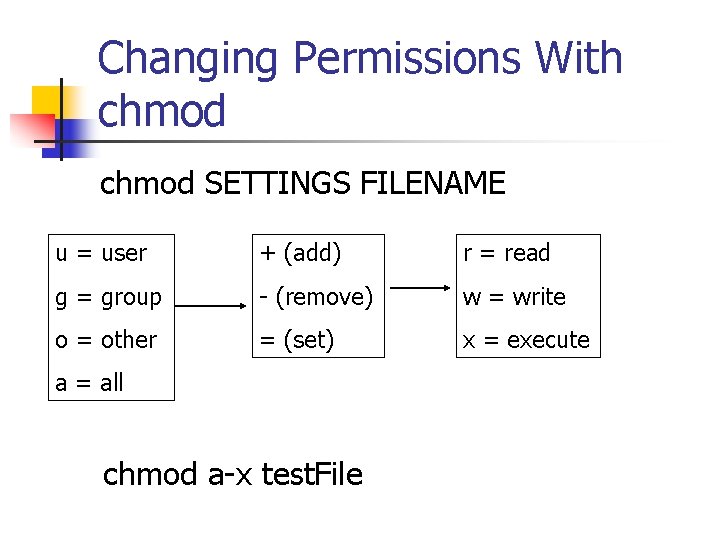
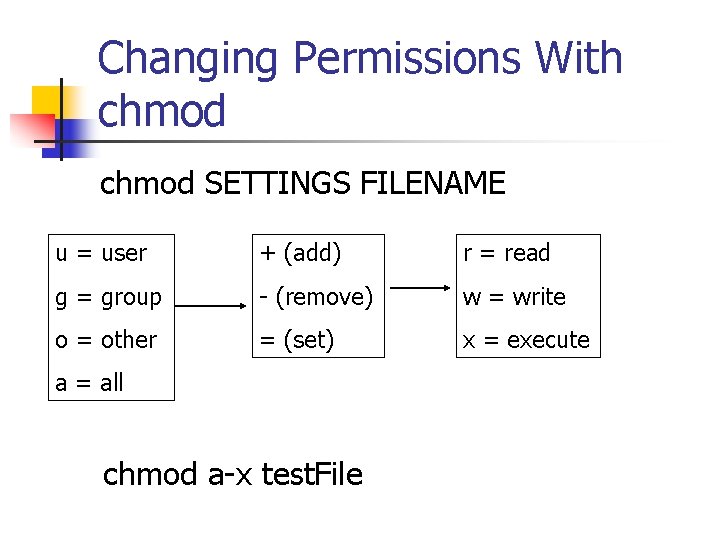
Changing Permissions With chmod SETTINGS FILENAME u = user + (add) r = read g = group - (remove) w = write o = other = (set) x = execute a = all chmod a-x test. File
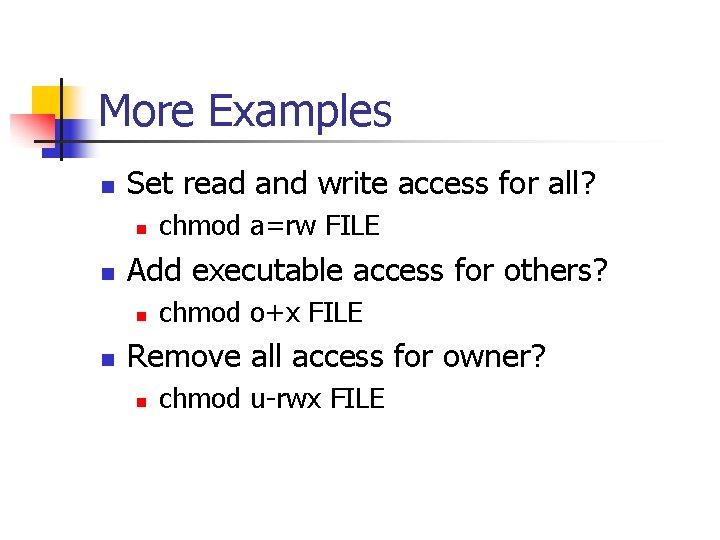
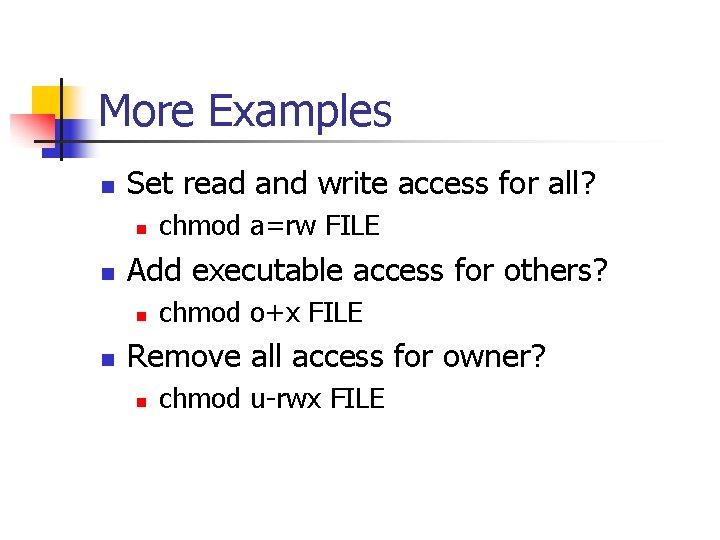
More Examples n Set read and write access for all? n n Add executable access for others? n n chmod a=rw FILE chmod o+x FILE Remove all access for owner? n chmod u-rwx FILE
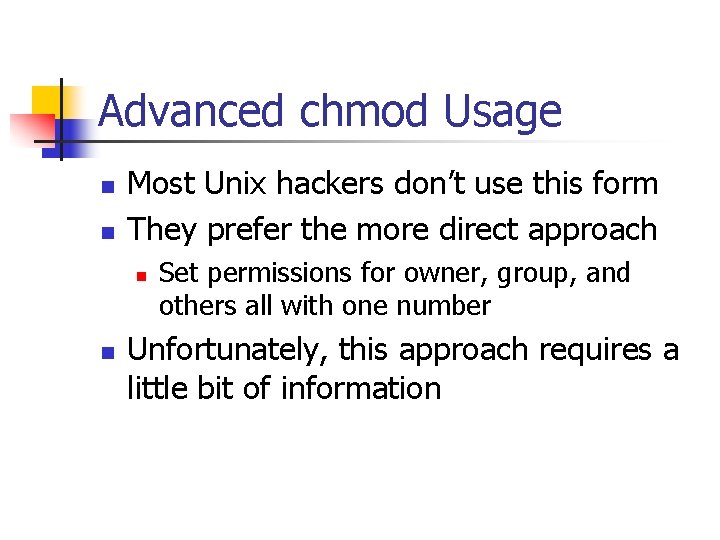
Advanced chmod Usage n n Most Unix hackers don’t use this form They prefer the more direct approach n n Set permissions for owner, group, and others all with one number Unfortunately, this approach requires a little bit of information
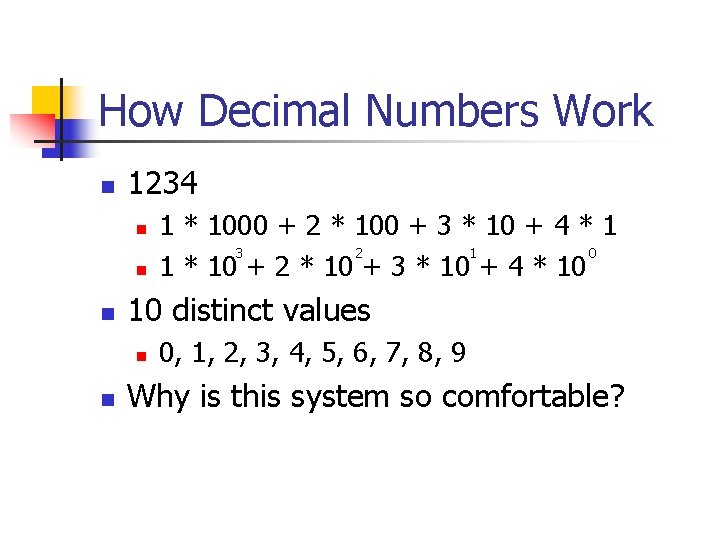
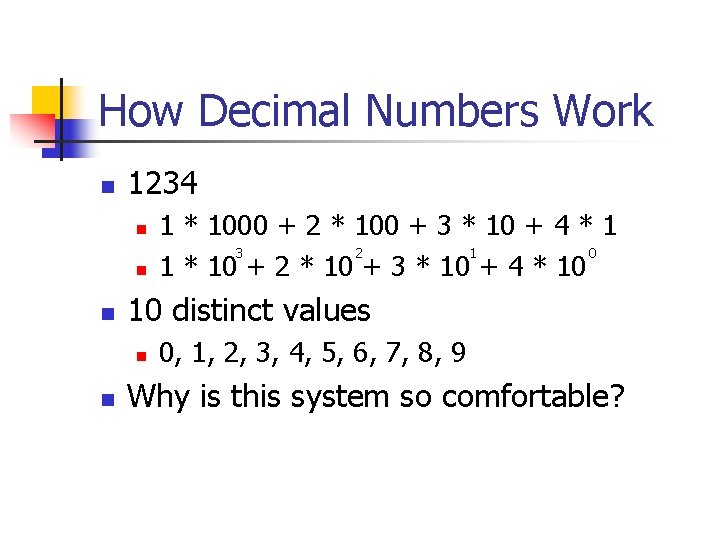
How Decimal Numbers Work n 1234 n n n 10 distinct values n n 1 * 1000 + 2 * 100 + 3 * 10 + 4 * 1 3 2 1 0 1 * 10 + 2 * 10 + 3 * 10 + 4 * 10 0, 1, 2, 3, 4, 5, 6, 7, 8, 9 Why is this system so comfortable?
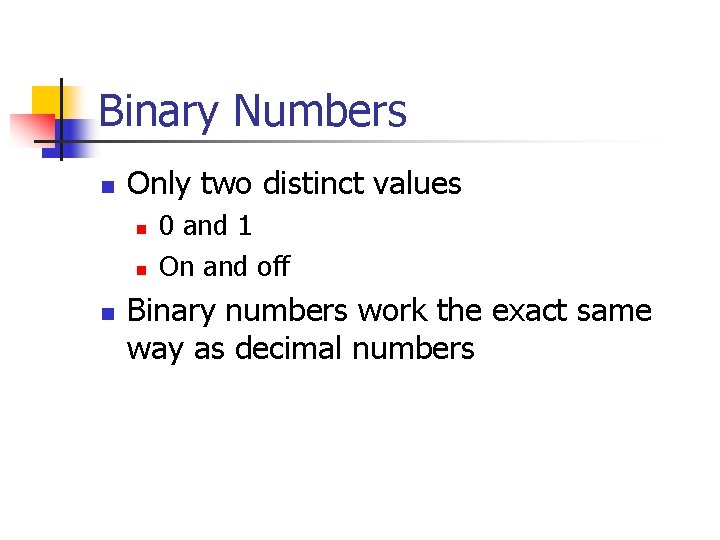
Binary Numbers n Only two distinct values n n n 0 and 1 On and off Binary numbers work the exact same way as decimal numbers
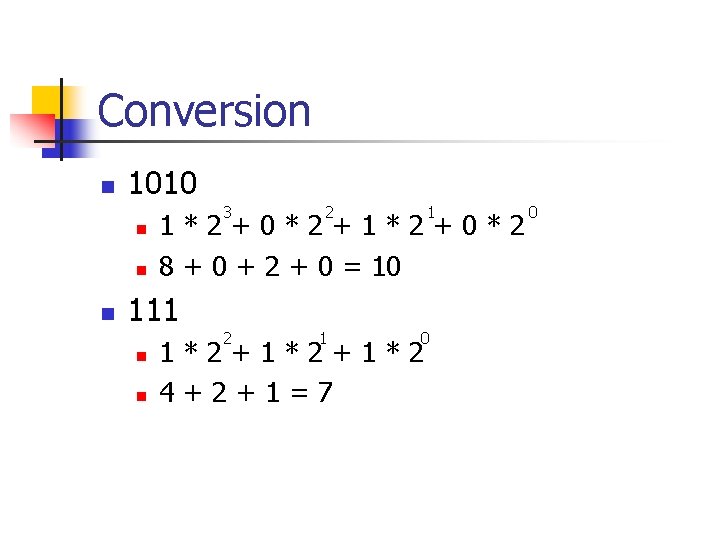
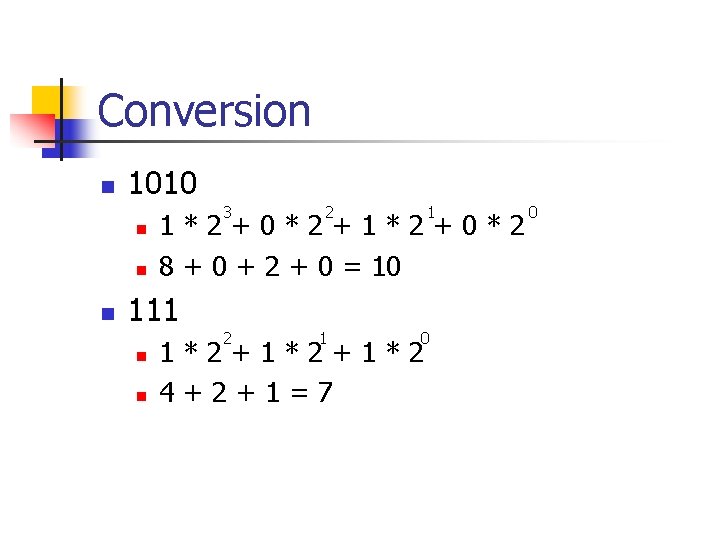
Conversion n 1010 3 n n 1 1*2+0*2+1*2+0*2 8 + 0 + 2 + 0 = 10 111 n 2 2 1 0 1*2+1*2 4+2+1=7 0
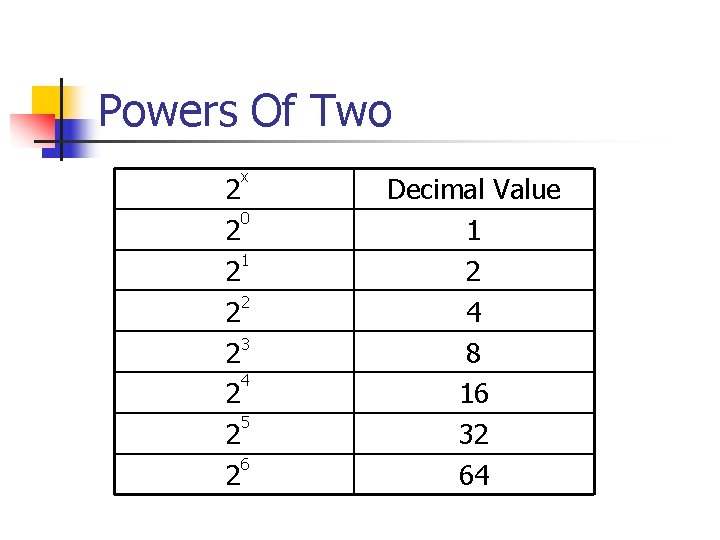
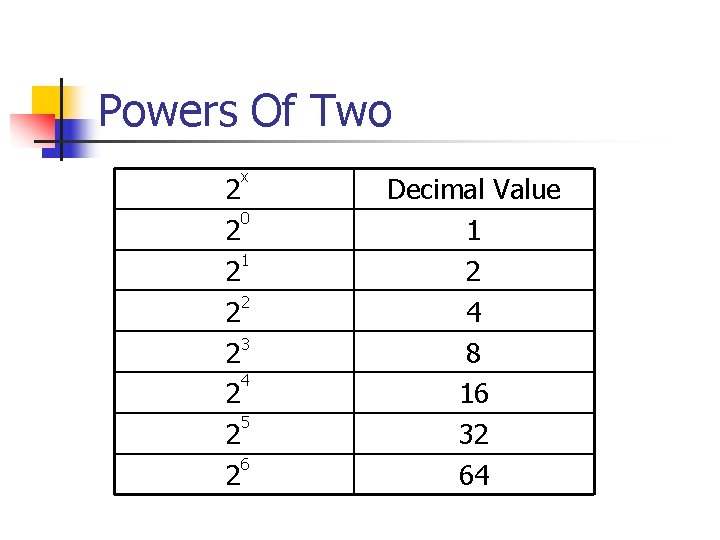
Powers Of Two x 2 0 2 1 2 23 4 2 5 2 6 2 Decimal Value 1 2 4 8 16 32 64
Octal Numbers n Eight distinct numbers n n 0, 1, 2, 3, 4, 5, 6, 7 Binary numbers can be split into groups of three and represented by an octal number exactly
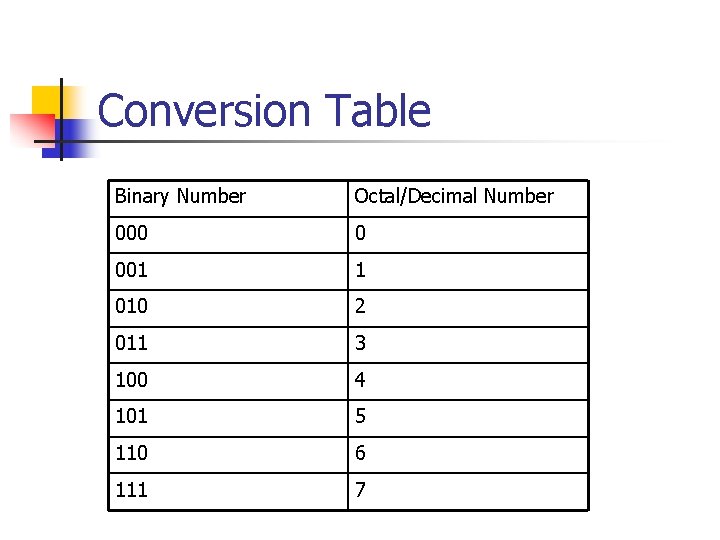
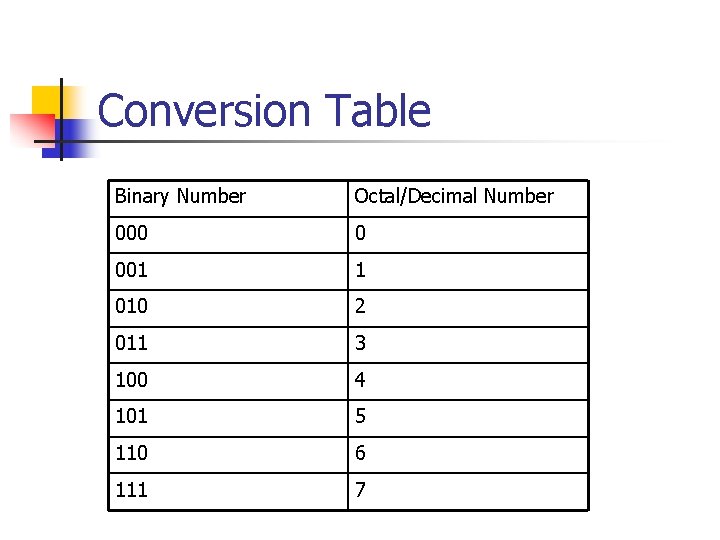
Conversion Table Binary Number Octal/Decimal Number 000 0 001 1 010 2 011 3 100 4 101 5 110 6 111 7
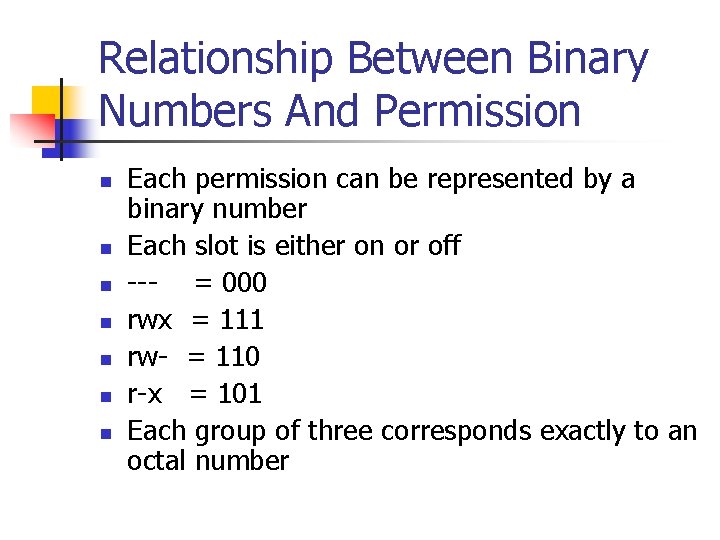
Relationship Between Binary Numbers And Permission n n n Each permission can be represented by a binary number Each slot is either on or off --- = 000 rwx = 111 rw- = 110 r-x = 101 Each group of three corresponds exactly to an octal number
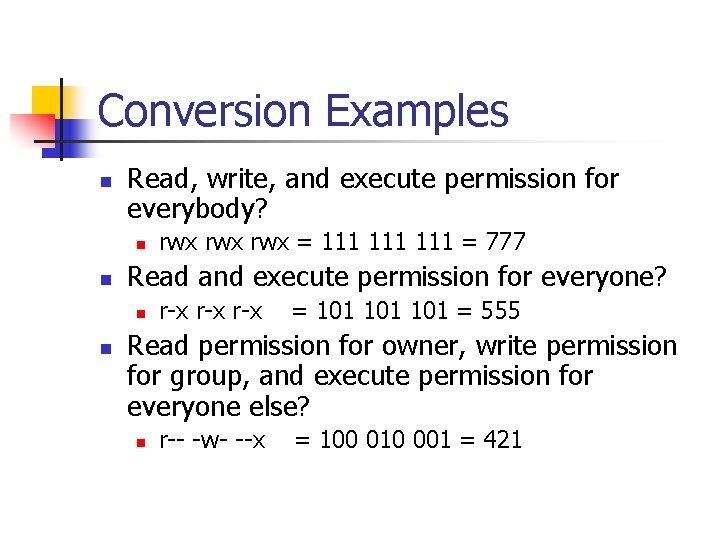
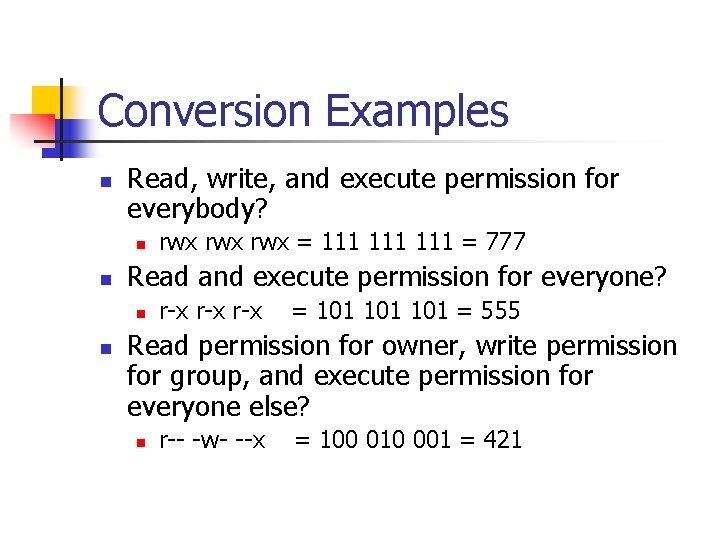
Conversion Examples n Read, write, and execute permission for everybody? n n Read and execute permission for everyone? n n rwx rwx = 111 111 = 777 r-x r-x = 101 101 = 555 Read permission for owner, write permission for group, and execute permission for everyone else? n r-- -w- --x = 100 010 001 = 421
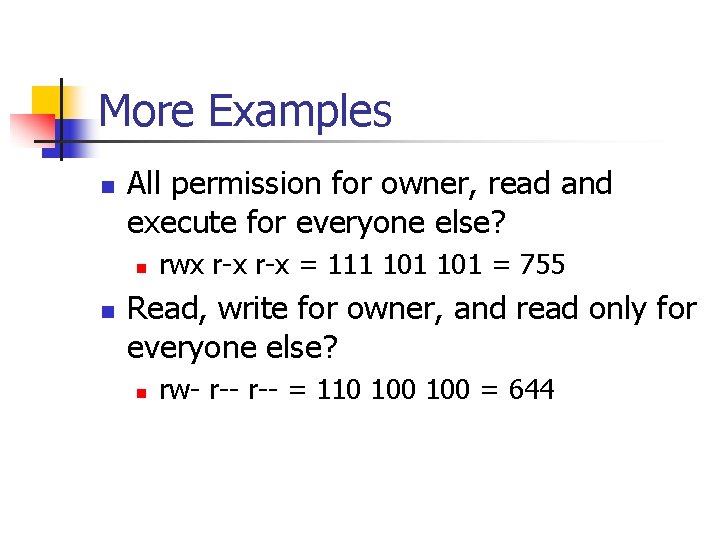
More Examples n All permission for owner, read and execute for everyone else? n n rwx r-x = 111 101 = 755 Read, write for owner, and read only for everyone else? n rw- r-- = 110 100 = 644
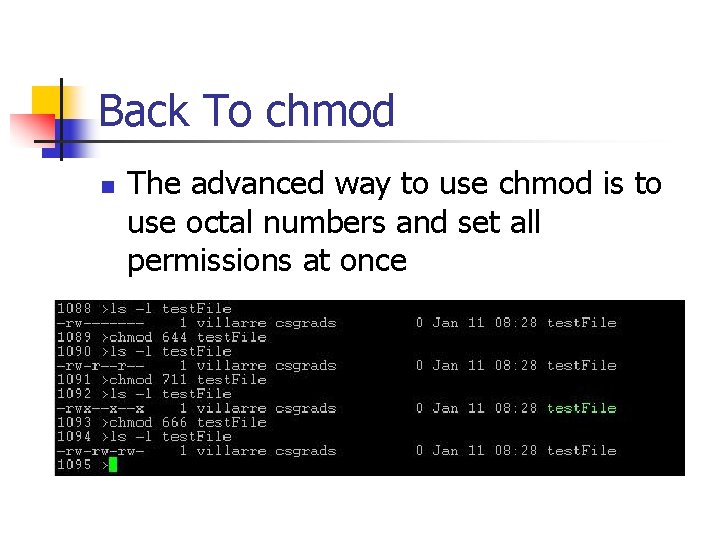
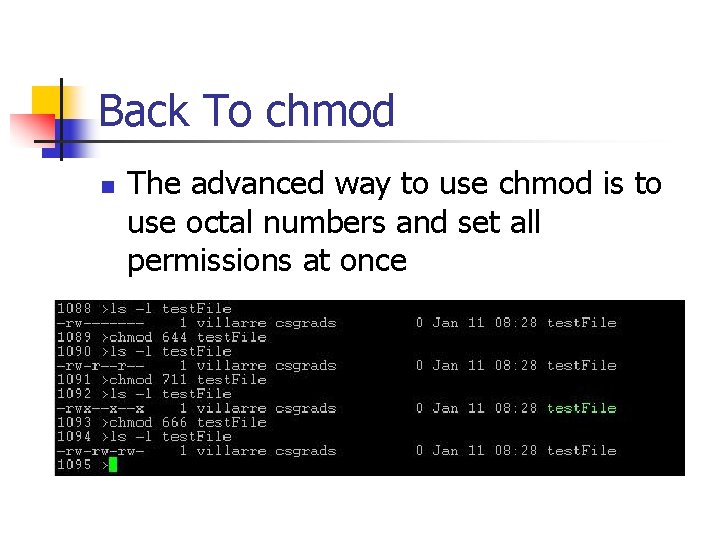
Back To chmod n The advanced way to use chmod is to use octal numbers and set all permissions at once
chgrp And chown n chgrp will change the group setting of a file to another that you are a member of n n You probably don’t belong to more than one group chown will change the owner of a file n Only the owner may chown a file n Once chown’ed, the new owner is the only one who can grant permission back
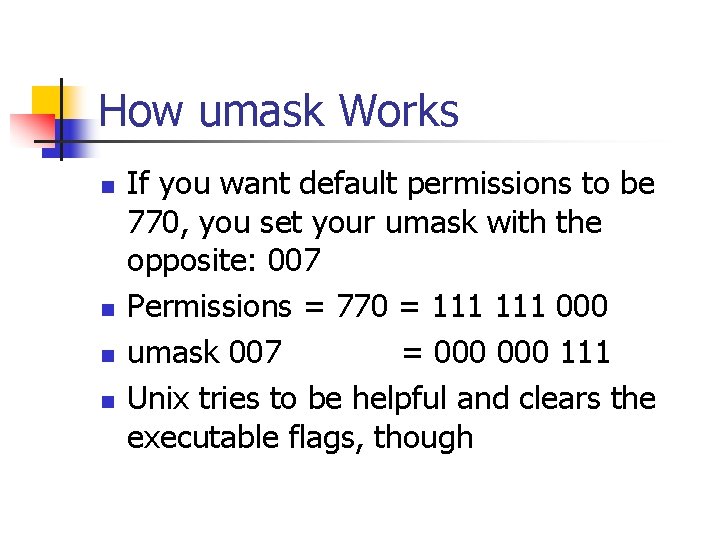
Using umask To Set Default Permissions n n n Every time you create a file, the permissions are set to a default umask will set this default Unfortunately, it does it the exact opposite way than you would think
How umask Works n n If you want default permissions to be 770, you set your umask with the opposite: 007 Permissions = 770 = 111 000 umask 007 = 000 111 Unix tries to be helpful and clears the executable flags, though
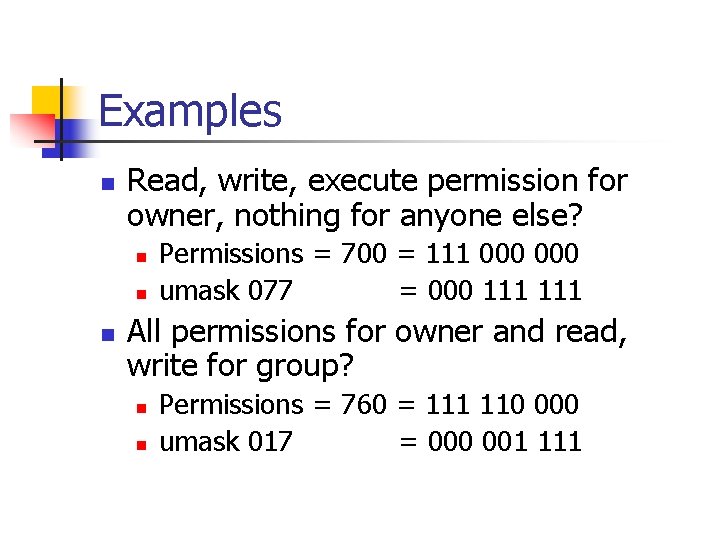
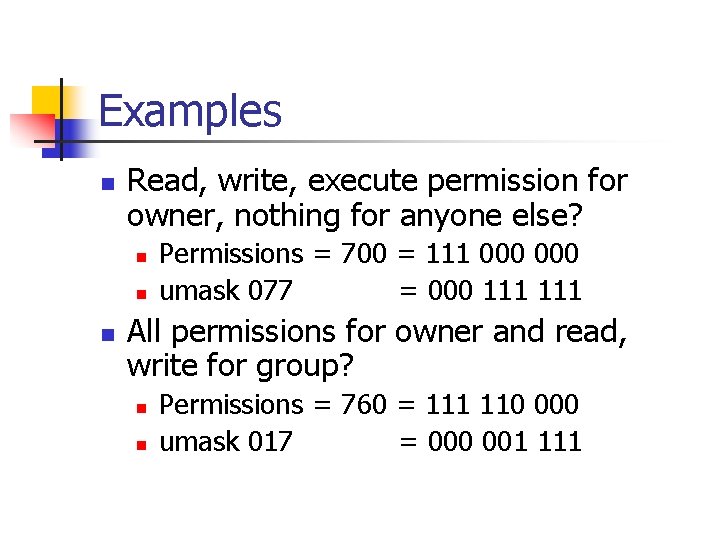
Examples n Read, write, execute permission for owner, nothing for anyone else? n n n Permissions = 700 = 111 000 umask 077 = 000 111 All permissions for owner and read, write for group? n n Permissions = 760 = 111 110 000 umask 017 = 000 001 111
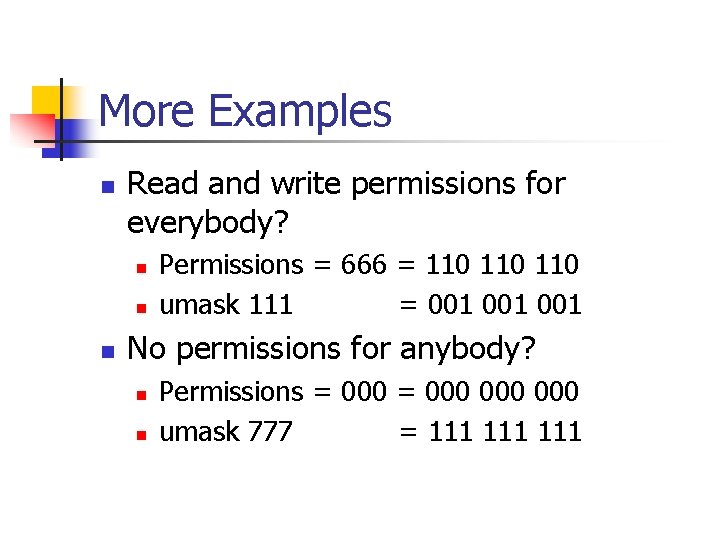
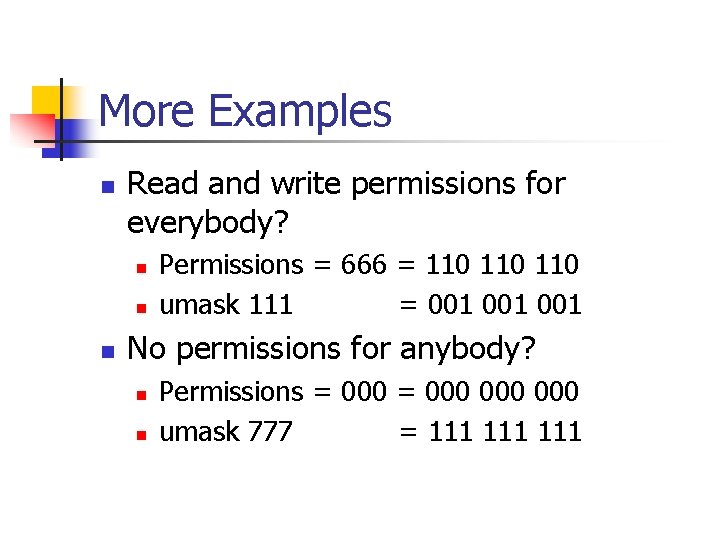
More Examples n Read and write permissions for everybody? n n n Permissions = 666 = 110 110 umask 111 = 001 001 No permissions for anybody? n n Permissions = 000 000 umask 777 = 111 111
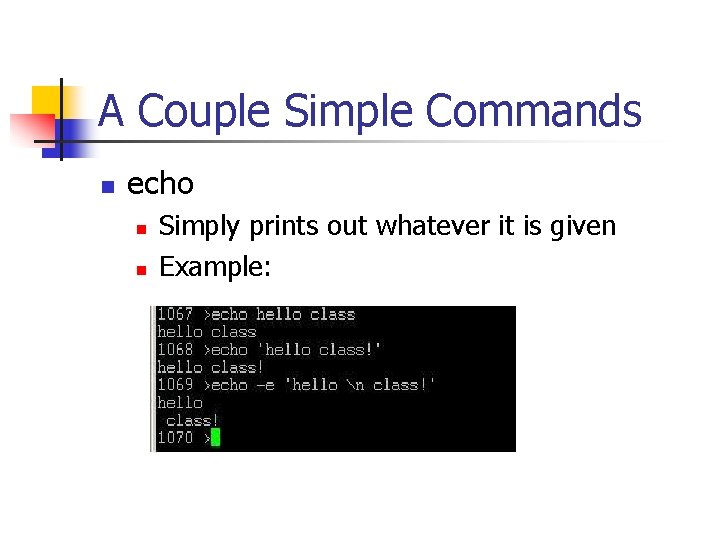
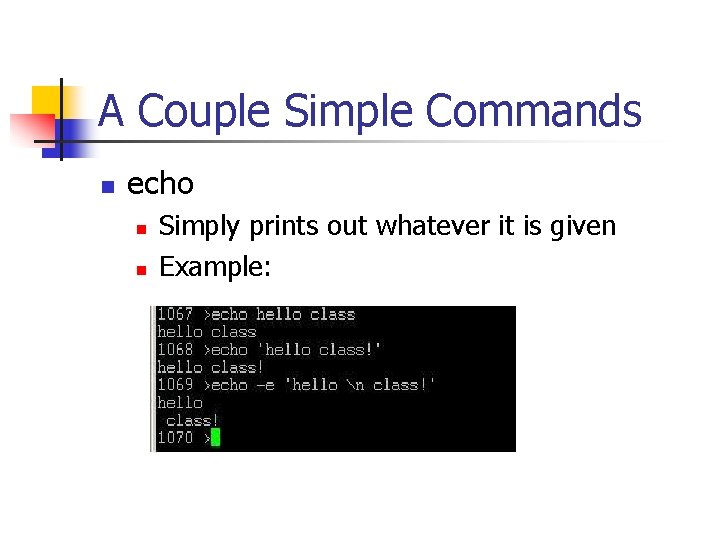
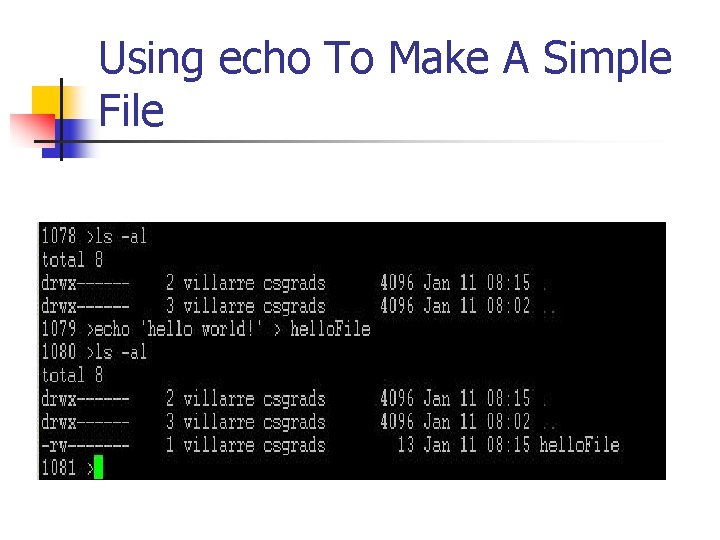
A Couple Simple Commands n echo n n Simply prints out whatever it is given Example:
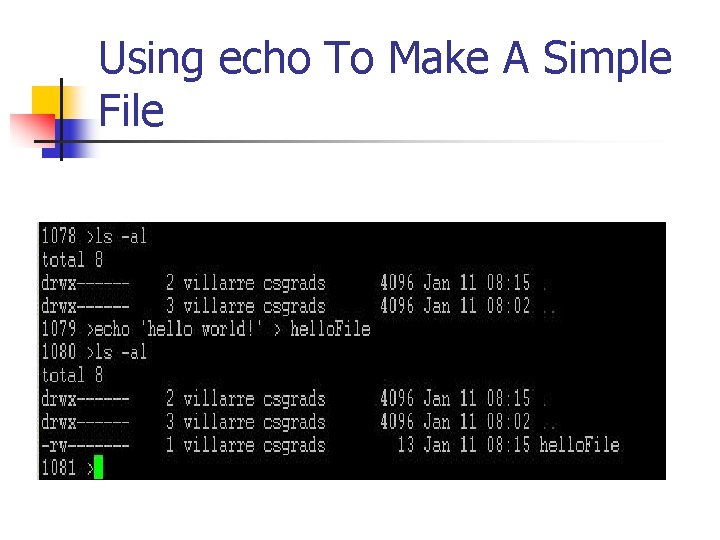
Using echo To Make A Simple File
Timestamps n touch command n n Without any flags, it will make the modification time of that file the current time Can be used to create a new file, but the file will be empty (0 byte size)
Final Notes For Today n n We have covered up through chapter 5 in the book, so you will be expected to have read these chapters Next time we will delve deeper into creating files and moving them around in the file system