Introduction to Computer Security Lecture 8 Key Management
- Slides: 48
Introduction to Computer Security Lecture 8 Key Management Nov 4, 2003 Courtesy of Professors Chris Clifton & Matt Bishop INFSCI 2935: Introduction of Computer Security 1
Issues l Authentication and distribution of keys ¡ Session key ¡ Key exchange protocols l Mechanisms to bind an identity to a key l Generation, maintenance and revoking of keys INFSCI 2935: Introduction to Computer Security 2
Notation l X Y : { Z || W } k. X, Y ¡ l X sends Y the message produced by concatenating Z and W enciphered by key k. X, Y, which is shared by users X and Y A T : { Z } k. A || { W } k. A, T ¡ A sends T a message consisting of the concatenation of Z enciphered using k. A, A’s key, and W enciphered using k. A, T, the key shared by A and T l r 1 , r 2 nonces (nonrepeating random numbers) INFSCI 2935: Introduction to Computer Security 3
Session, Interchange Keys l Alice wants to send a message m to Bob ¡ ¡ Assume public key encryption Alice generates a random cryptographic key ks and uses it to encipher m l l ¡ She enciphers ks with Bob’s public key k. B l l ¡ To be used for this message only Called a session key k. B enciphers all session keys Alice uses to communicate with Bob Called an interchange key Alice sends { m } ks { ks } k. B INFSCI 2935: Introduction to Computer Security 4
Benefits l Limits amount of traffic enciphered with single key ¡ Standard practice, to decrease the amount of traffic an attacker can obtain Makes replay attack less effective l Prevents some attacks l ¡ ¡ ¡ Example: Alice will send Bob message that is either “BUY” or “SELL”. Eve computes possible ciphertexts {“BUY”} k. B and {“SELL”} k. B. Eve intercepts enciphered message, compares, and gets plaintext at once INFSCI 2935: Introduction to Computer Security 5
Key Exchange Algorithms Goal: Alice, Bob use a shared key to communicate secretely l Criteria l ¡ Key cannot be sent in clear l l ¡ ¡ Attacker can listen in Key can be sent enciphered, or derived from exchanged data plus data not known to an eavesdropper Alice, Bob may trust third party All cryptosystems, protocols publicly known l l Only secret data is the keys, ancillary information known only to Alice and Bob needed to derive keys Anything transmitted is assumed known to attacker INFSCI 2935: Introduction to Computer Security 6
Classical Key Exchange l How do Alice, Bob begin? ¡ Alice can’t send it to Bob in the clear! l Assume trusted third party, Cathy ¡ Alice and Cathy share secret key k. A ¡ Bob and Cathy share secret key k. B l Use this to exchange shared key ks INFSCI 2935: Introduction to Computer Security 7
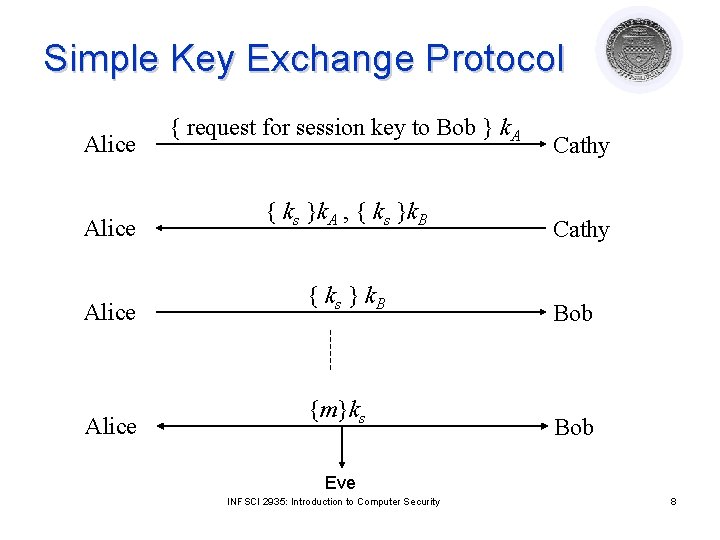
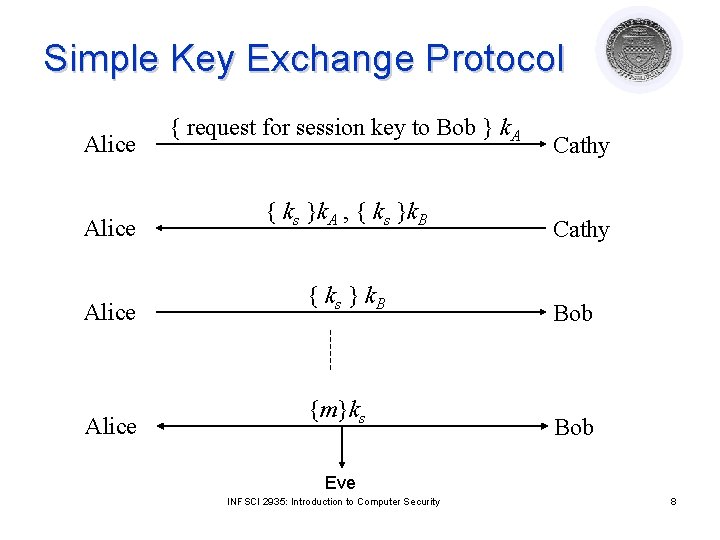
Simple Key Exchange Protocol Alice { request for session key to Bob } k. A { ks }k. A , { ks }k. B { ks } k. B {m}ks Cathy Bob Eve INFSCI 2935: Introduction to Computer Security 8
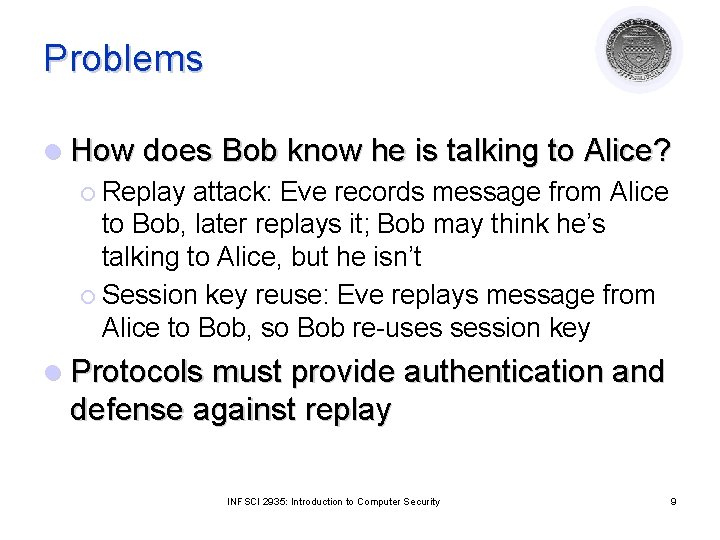
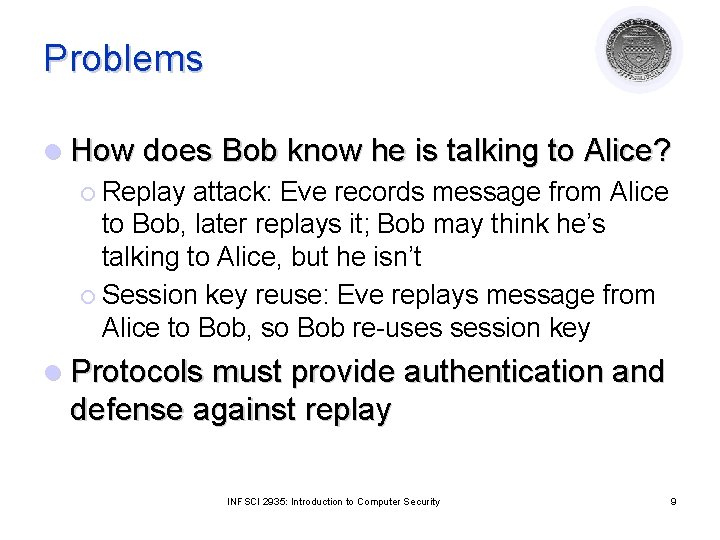
Problems l How does Bob know he is talking to Alice? ¡ Replay attack: Eve records message from Alice to Bob, later replays it; Bob may think he’s talking to Alice, but he isn’t ¡ Session key reuse: Eve replays message from Alice to Bob, so Bob re-uses session key l Protocols must provide authentication and defense against replay INFSCI 2935: Introduction to Computer Security 9
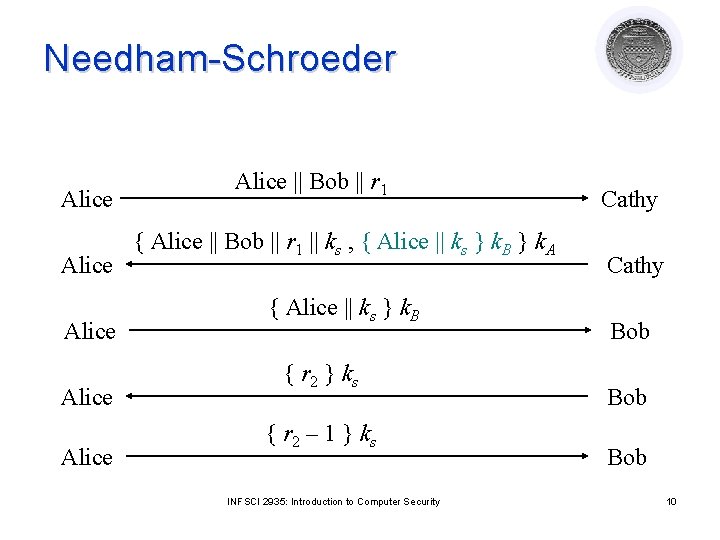
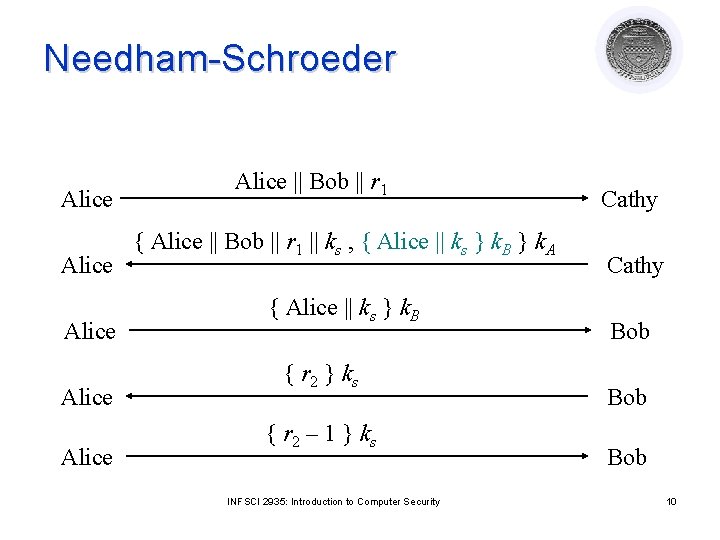
Needham-Schroeder Alice Alice || Bob || r 1 { Alice || Bob || r 1 || ks , { Alice || ks } k. B } k. A { Alice || ks } k. B { r 2 } k s { r 2 – 1 } k s INFSCI 2935: Introduction to Computer Security Cathy Bob Bob 10
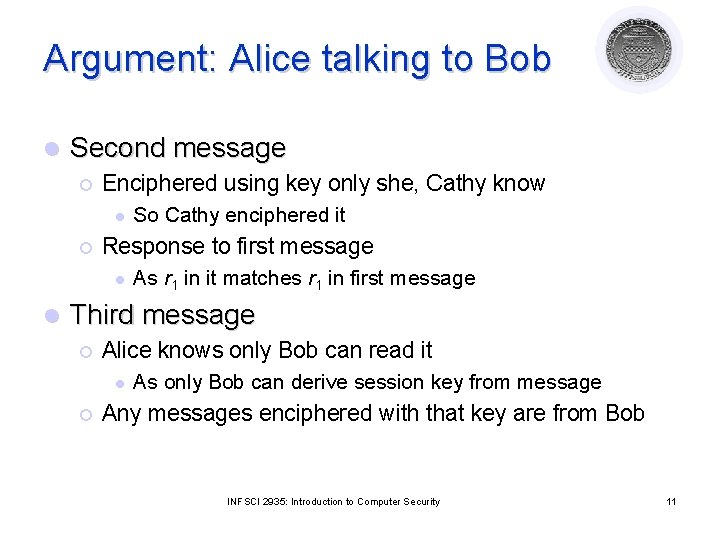
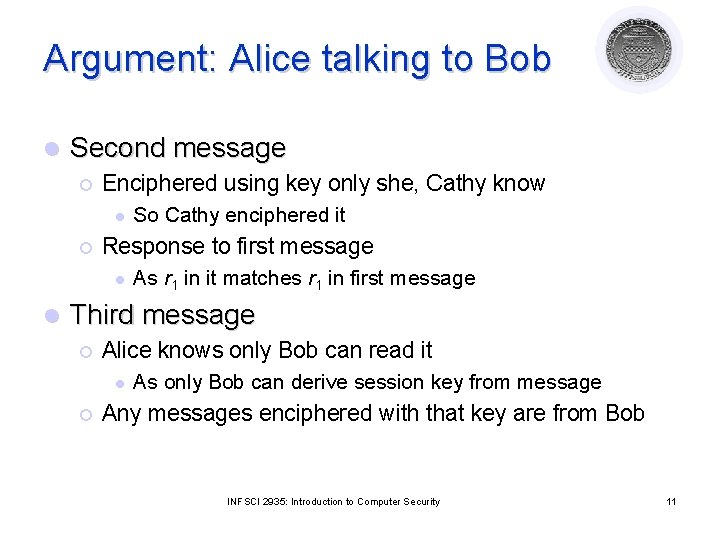
Argument: Alice talking to Bob l Second message ¡ Enciphered using key only she, Cathy know l ¡ Response to first message l l So Cathy enciphered it As r 1 in it matches r 1 in first message Third message ¡ Alice knows only Bob can read it l ¡ As only Bob can derive session key from message Any messages enciphered with that key are from Bob INFSCI 2935: Introduction to Computer Security 11
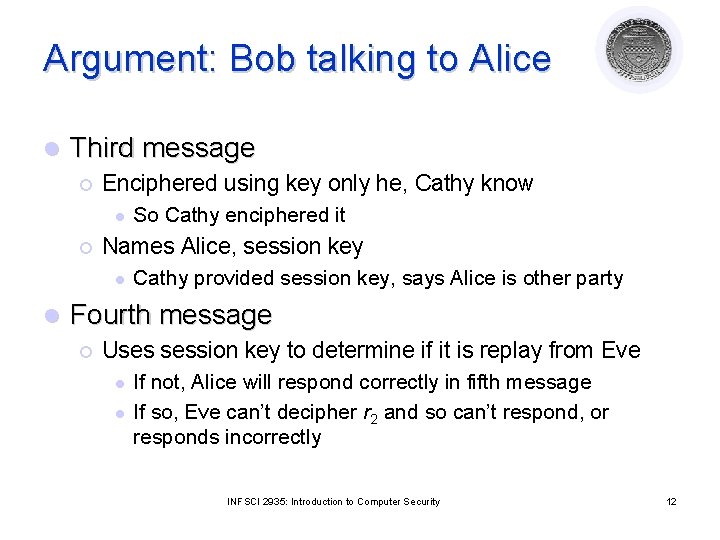
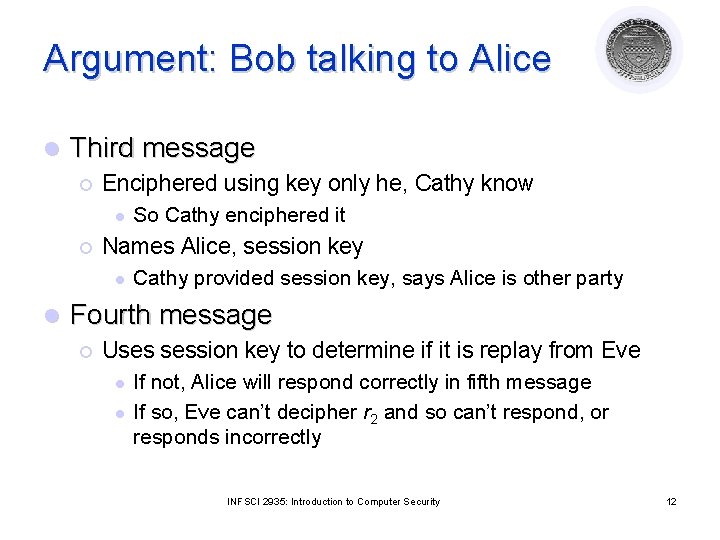
Argument: Bob talking to Alice l Third message ¡ Enciphered using key only he, Cathy know l ¡ Names Alice, session key l l So Cathy enciphered it Cathy provided session key, says Alice is other party Fourth message ¡ Uses session key to determine if it is replay from Eve l l If not, Alice will respond correctly in fifth message If so, Eve can’t decipher r 2 and so can’t respond, or responds incorrectly INFSCI 2935: Introduction to Computer Security 12
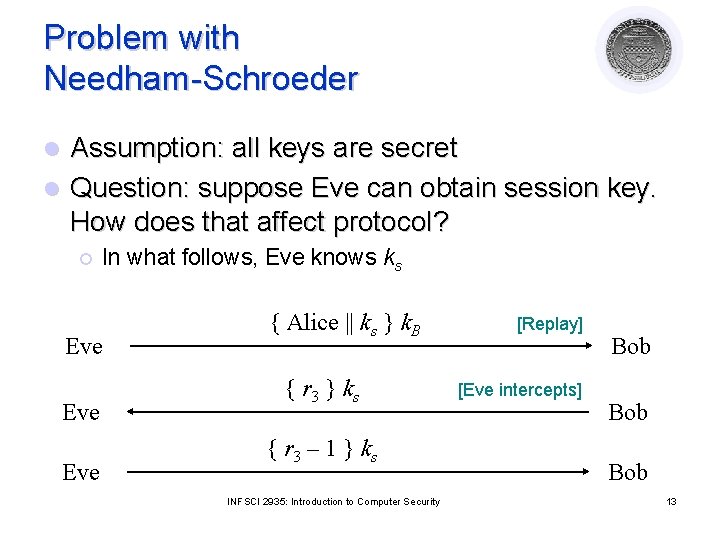
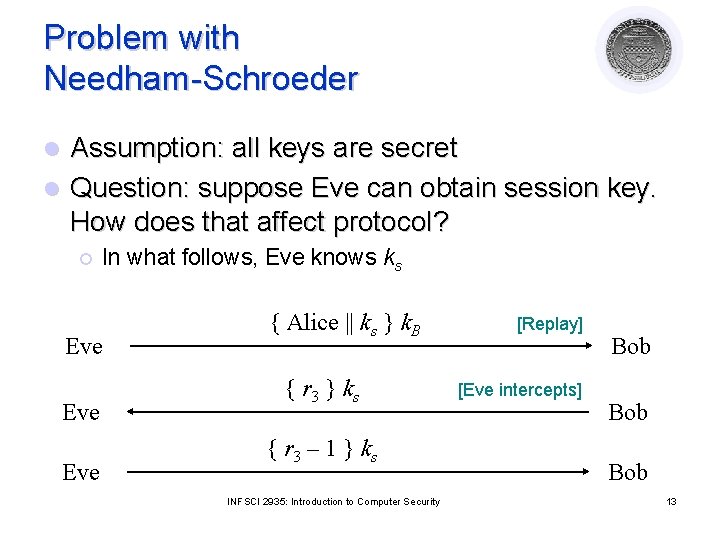
Problem with Needham-Schroeder Assumption: all keys are secret l Question: suppose Eve can obtain session key. How does that affect protocol? l ¡ In what follows, Eve knows ks Eve Eve { Alice || ks } k. B { r 3 } k s { r 3 – 1 } k s INFSCI 2935: Introduction to Computer Security [Replay] [Eve intercepts] Bob Bob 13
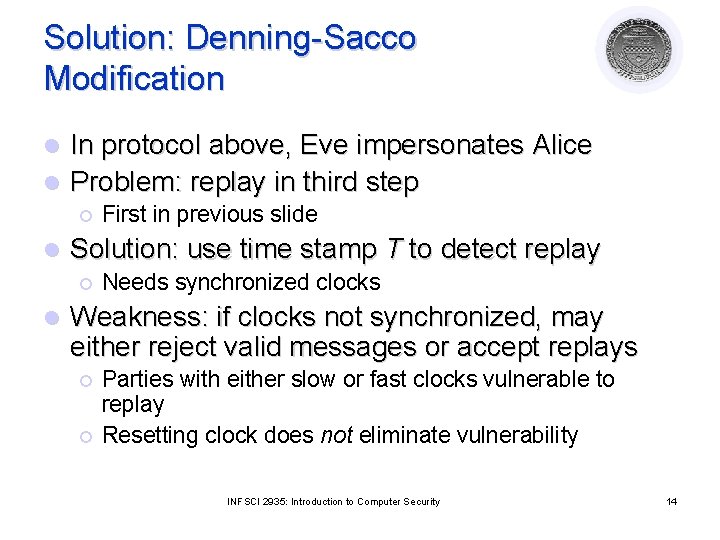
Solution: Denning-Sacco Modification In protocol above, Eve impersonates Alice l Problem: replay in third step l ¡ l Solution: use time stamp T to detect replay ¡ l First in previous slide Needs synchronized clocks Weakness: if clocks not synchronized, may either reject valid messages or accept replays ¡ ¡ Parties with either slow or fast clocks vulnerable to replay Resetting clock does not eliminate vulnerability INFSCI 2935: Introduction to Computer Security 14
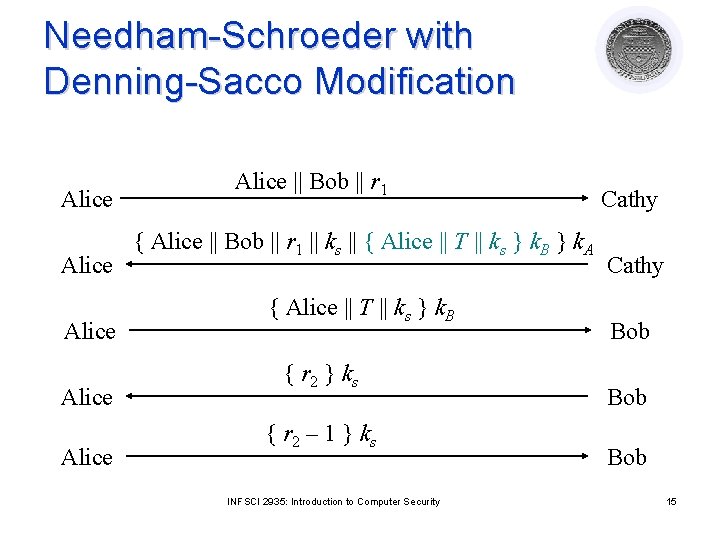
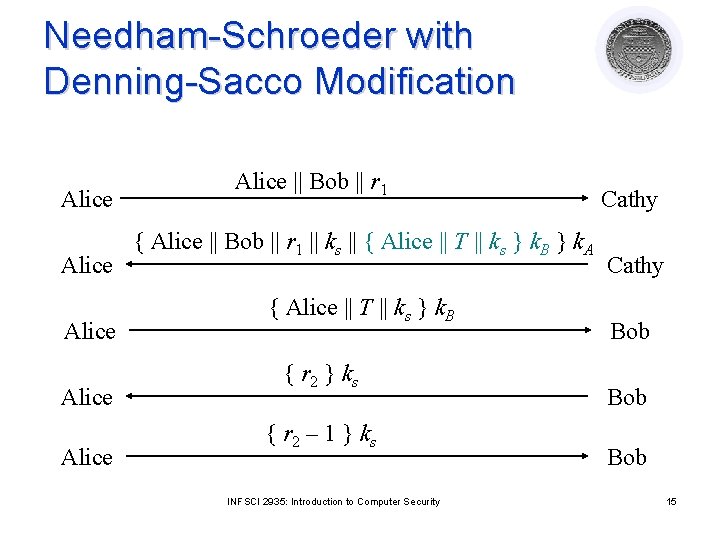
Needham-Schroeder with Denning-Sacco Modification Alice Alice || Bob || r 1 { Alice || Bob || r 1 || ks || { Alice || T || ks } k. B } k. A { Alice || T || ks } k. B { r 2 } k s { r 2 – 1 } k s INFSCI 2935: Introduction to Computer Security Cathy Bob Bob 15
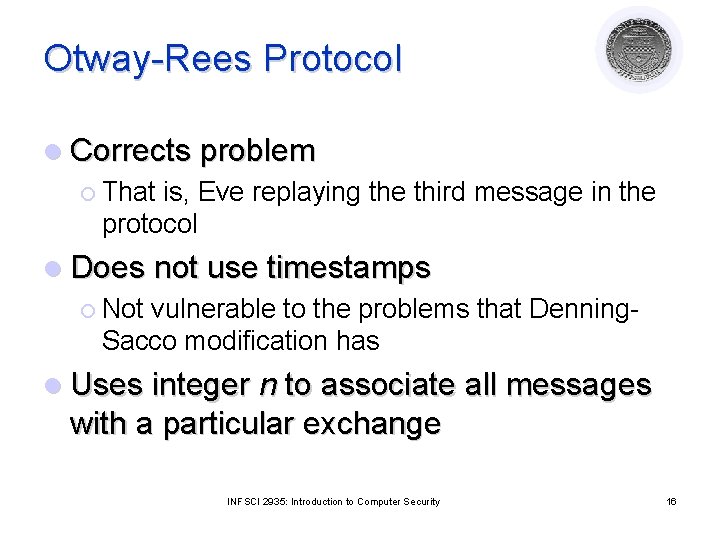
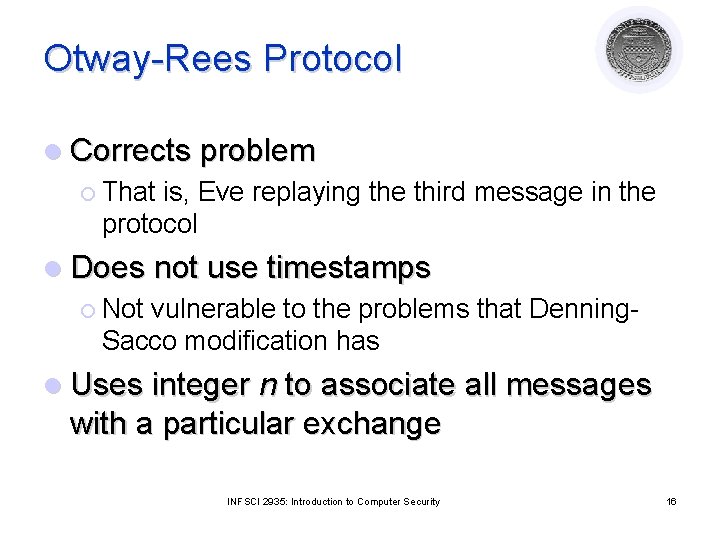
Otway-Rees Protocol l Corrects problem ¡ That is, Eve replaying the third message in the protocol l Does not use timestamps ¡ Not vulnerable to the problems that Denning. Sacco modification has l Uses integer n to associate all messages with a particular exchange INFSCI 2935: Introduction to Computer Security 16
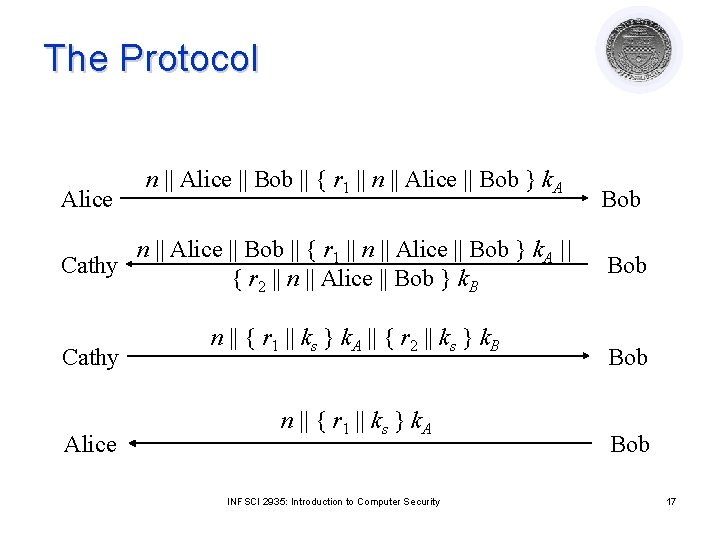
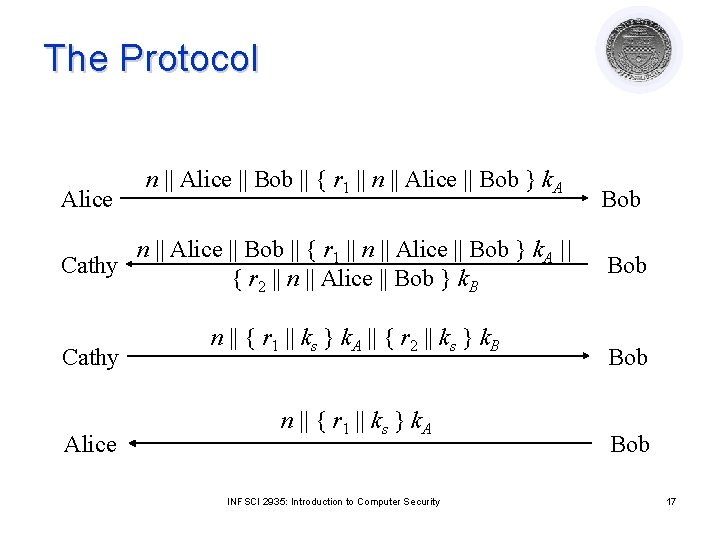
The Protocol Alice n || Alice || Bob || { r 1 || n || Alice || Bob } k. A || Cathy { r 2 || n || Alice || Bob } k. B Cathy Alice n || { r 1 || ks } k. A || { r 2 || ks } k. B n || { r 1 || ks } k. A INFSCI 2935: Introduction to Computer Security Bob Bob 17
Argument: Alice talking to Bob l Fourth message ¡ If n matches first message, Alice knows it is part of this protocol exchange ¡ Cathy generated ks because only she, Alice know k. A ¡ Enciphered part belongs to exchange as r 1 matches r 1 in encrypted part of first message INFSCI 2935: Introduction to Computer Security 18
Argument: Bob talking to Alice l Third message ¡ If n matches second message, Bob knows it is part of this protocol exchange ¡ Cathy generated ks because only she, Bob know k. B ¡ Enciphered part belongs to exchange as r 2 matches r 2 in encrypted part of second message INFSCI 2935: Introduction to Computer Security 19
Replay Attack l Eve acquires old ks, message in third step ¡ l n || { r 1 || ks } k. A || { r 2 || ks } k. B Eve forwards appropriate part to Alice ¡ ¡ Alice has no ongoing key exchange with Bob: n matches nothing, so is rejected Alice has ongoing key exchange with Bob: n does not match, so is again rejected l If replay is for the current key exchange, and Eve sent the relevant part before Bob did, Eve could simply listen to traffic; no replay involved INFSCI 2935: Introduction to Computer Security 20
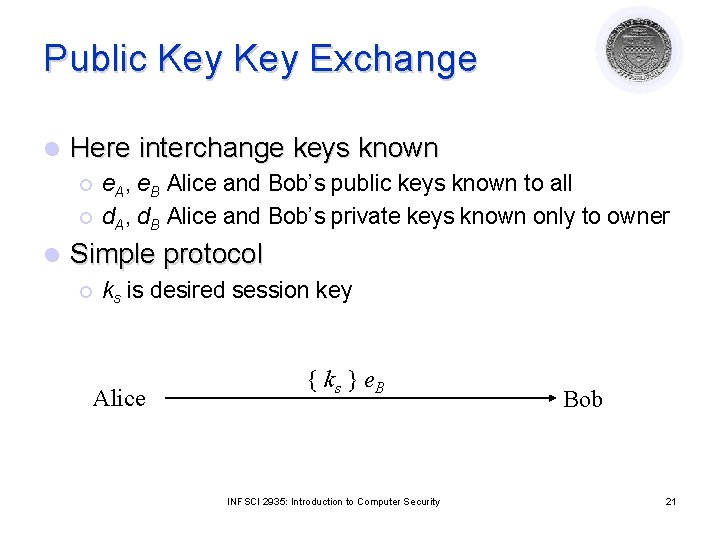
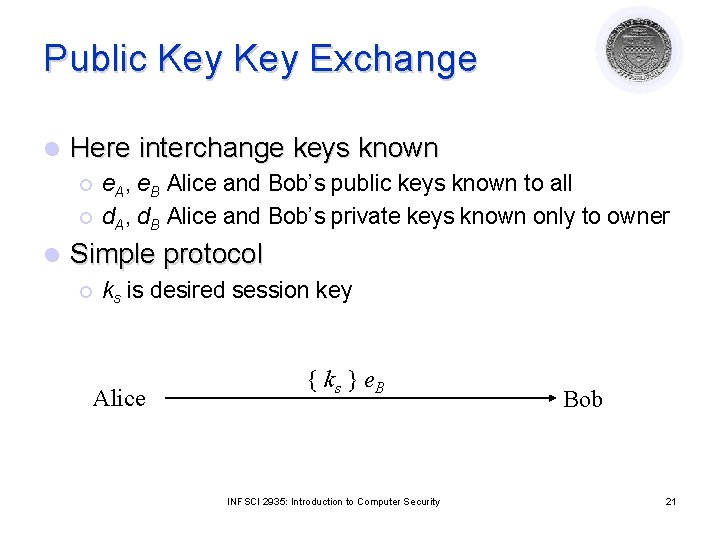
Public Key Exchange l Here interchange keys known ¡ ¡ l e. A, e. B Alice and Bob’s public keys known to all d. A, d. B Alice and Bob’s private keys known only to owner Simple protocol ¡ ks is desired session key Alice { ks } e. B INFSCI 2935: Introduction to Computer Security Bob 21
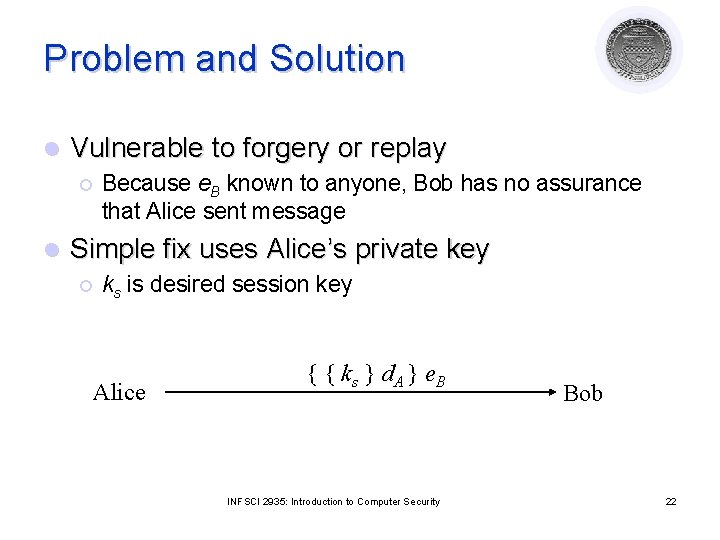
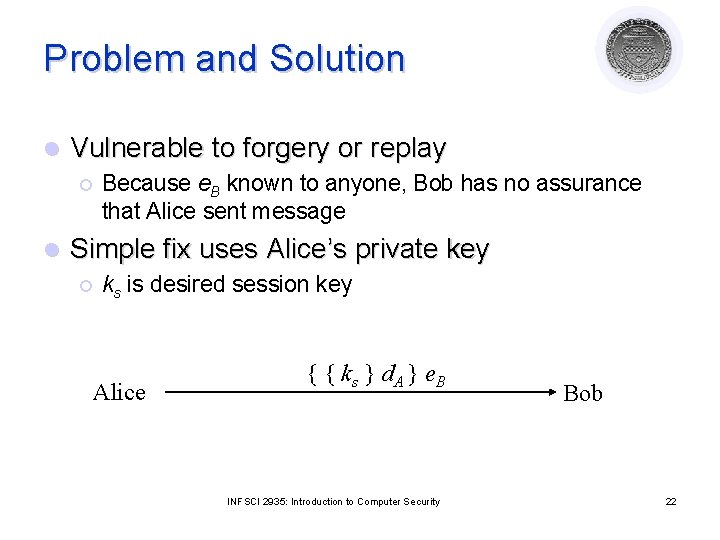
Problem and Solution l Vulnerable to forgery or replay ¡ l Because e. B known to anyone, Bob has no assurance that Alice sent message Simple fix uses Alice’s private key ¡ ks is desired session key Alice { { ks } d. A } e. B INFSCI 2935: Introduction to Computer Security Bob 22
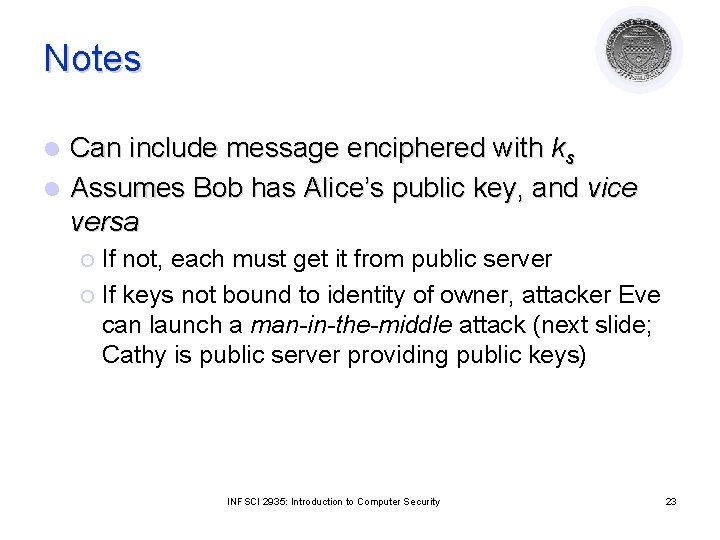
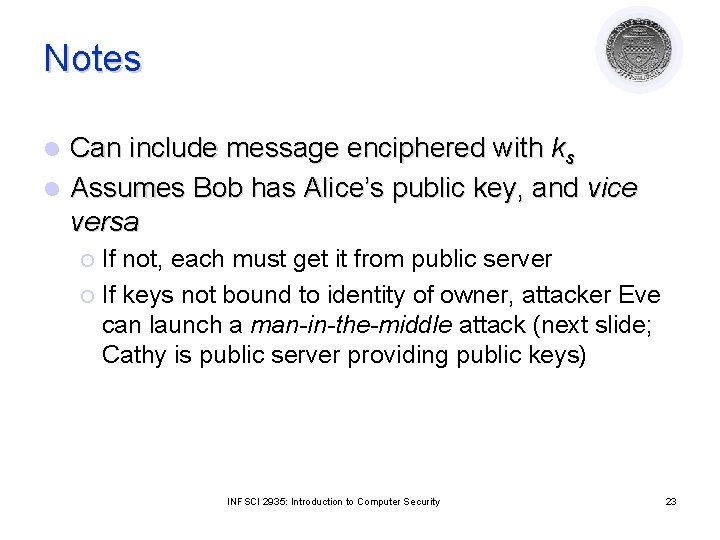
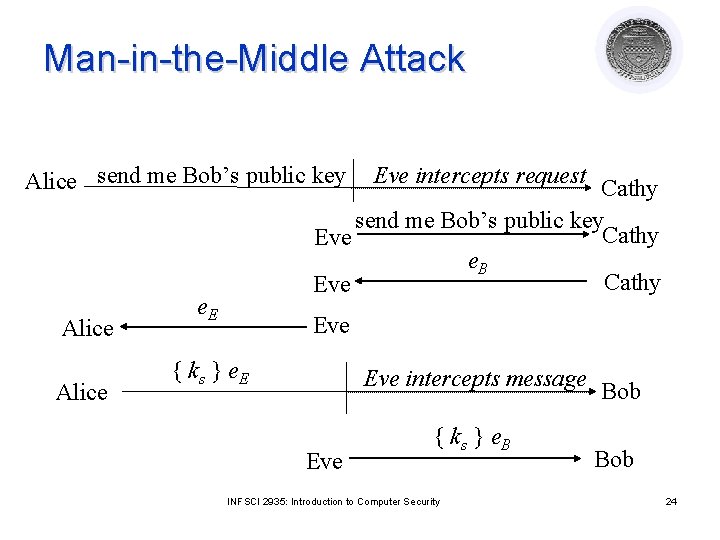
Notes Can include message enciphered with ks l Assumes Bob has Alice’s public key, and vice versa l If not, each must get it from public server ¡ If keys not bound to identity of owner, attacker Eve can launch a man-in-the-middle attack (next slide; Cathy is public server providing public keys) ¡ INFSCI 2935: Introduction to Computer Security 23
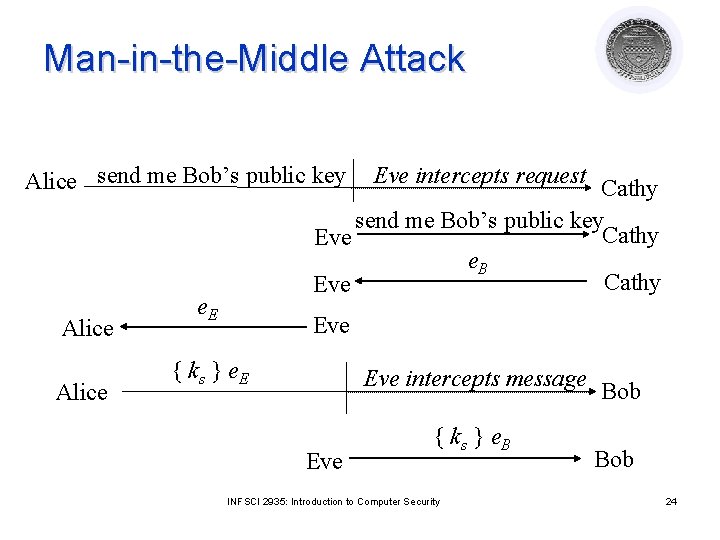
Man-in-the-Middle Attack Alice send me Bob’s public key Alice Eve intercepts request Cathy send me Bob’s public key Cathy Eve e. B Cathy Eve e. E Eve { ks } e. E Eve intercepts message Eve { ks } e. B INFSCI 2935: Introduction to Computer Security Bob 24
Key Generation Goal: generate difficult to guess keys l Problem statement: given a set of K potential keys, choose one randomly l ¡ l Equivalent to selecting a random number between 0 and K– 1 inclusive Why is this hard: generating random numbers ¡ Actually, numbers are usually pseudo-random, that is, generated by an algorithm INFSCI 2935: Introduction to Computer Security 25
What is “Random”? l Sequence of cryptographically random numbers: a sequence of numbers n 1, n 2, … such that for any integer k > 0, an observer cannot predict nk even if all of n 1, …, nk– 1 are known ¡ Best: physical source of randomness Electromagnetic phenomena l Characteristics of computing environment such as disk latency l Ambient background noise l INFSCI 2935: Introduction to Computer Security 26
What is “Pseudorandom”? l Sequence of cryptographically pseudorandom numbers: sequence of numbers intended to simulate a sequence of cryptographically random numbers but generated by an algorithm ¡ Very difficult to do this well l Linear congruential generators [nk = (ank– 1 + b) mod n] broken (a, b and n are relatively prime) Polynomial congruential generators [nk = (ajnk– 1 j + … + a 1 nk– 1 a 0) mod n] broken too Here, “broken” means next number in sequence can be determined INFSCI 2935: Introduction to Computer Security 27
Best Pseudorandom Numbers l Strong mixing function: function of 2 or more inputs with each bit of output depending on some nonlinear function of all input bits ¡ Examples: DES, MD 5, SHA-1 ¡ Use on UNIX-based systems: (date; ps gaux) | md 5 where “ps gaux” lists all information about all processes on system INFSCI 2935: Introduction to Computer Security 28
Digital Signature Construct that authenticates origin, contents of message in a manner provable to a disinterested third party (“judge”) l Sender cannot deny having sent message (service is “nonrepudiation”) l ¡ Limited to technical proofs l ¡ Inability to deny one’s cryptographic key was used to sign One could claim the cryptographic key was stolen or compromised l Legal proofs, etc. , probably required; INFSCI 2935: Introduction to Computer Security 29
Common Error l Classical: Alice, Bob share key ¡ Alice sends m || { m }k to Bob k This is a digital signature WRONG l This is not a digital signature ¡ Why? Third party cannot determine whether Alice or Bob generated message INFSCI 2935: Introduction to Computer Security 30
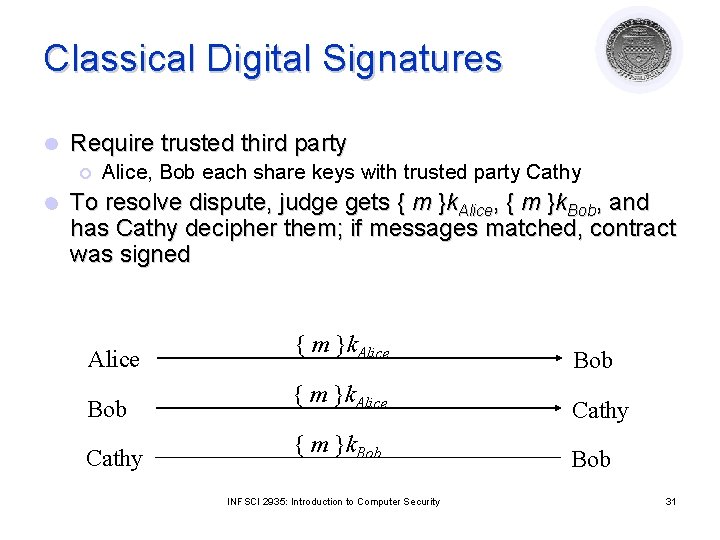
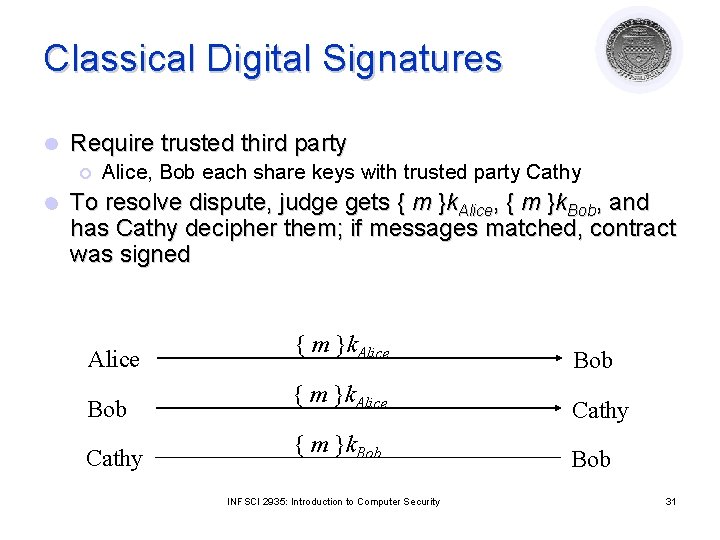
Classical Digital Signatures l Require trusted third party ¡ l Alice, Bob each share keys with trusted party Cathy To resolve dispute, judge gets { m }k. Alice, { m }k. Bob, and has Cathy decipher them; if messages matched, contract was signed Alice { m }k. Alice Bob { m }k. Alice Cathy { m }k. Bob INFSCI 2935: Introduction to Computer Security 31
Public Key Digital Signatures l Alice’s keys are d. Alice, e. Alice l Alice sends Bob m || { m }d. Alice l In case of dispute, judge computes { { m }d. Alice }e. Alice l and if it is m, Alice signed message ¡ She’s the only one who knows d. Alice! INFSCI 2935: Introduction to Computer Security 32
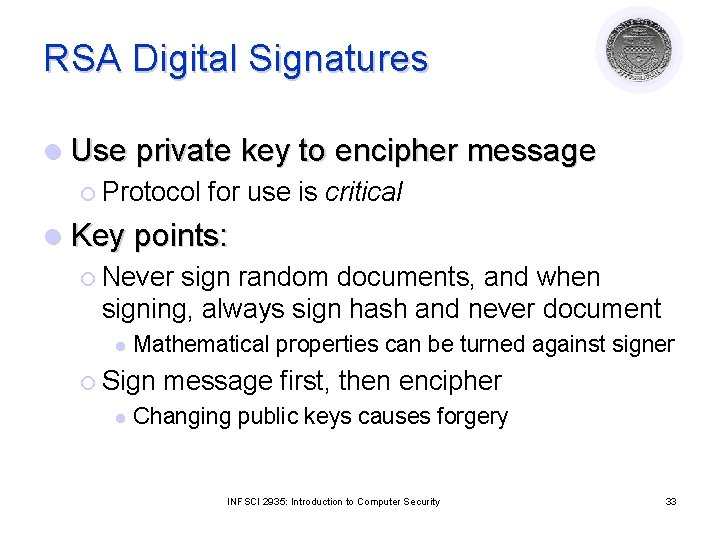
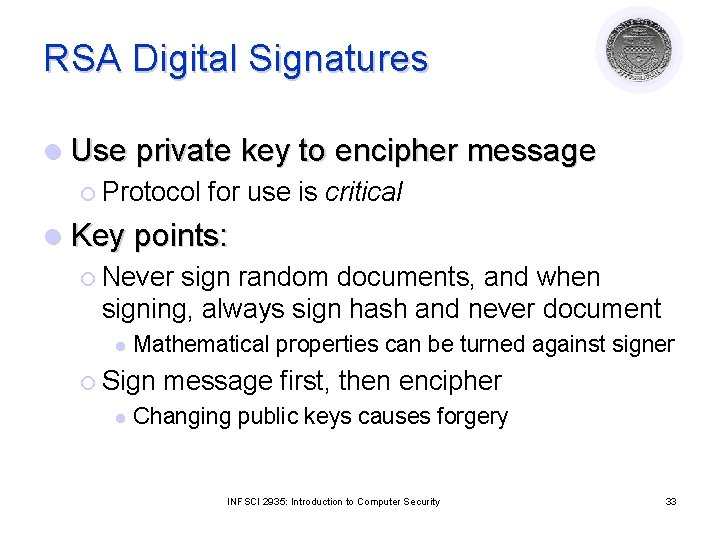
RSA Digital Signatures l Use private key to encipher message ¡ Protocol for use is critical l Key points: ¡ Never sign random documents, and when signing, always sign hash and never document l Mathematical properties can be turned against signer ¡ Sign l message first, then encipher Changing public keys causes forgery INFSCI 2935: Introduction to Computer Security 33
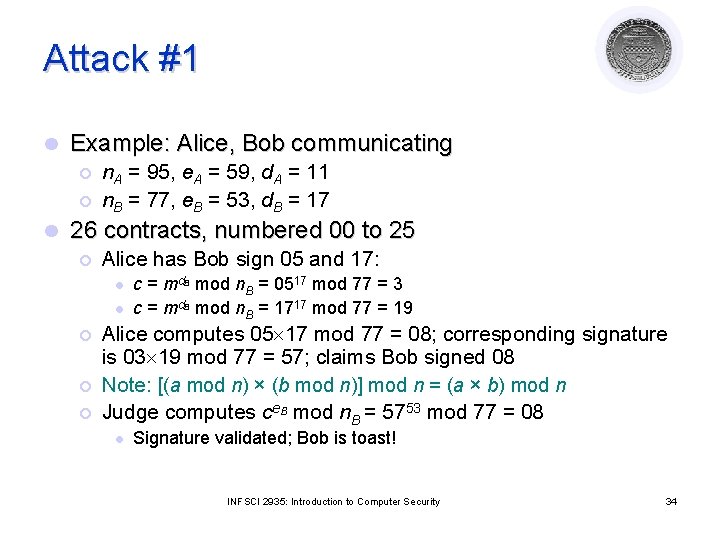
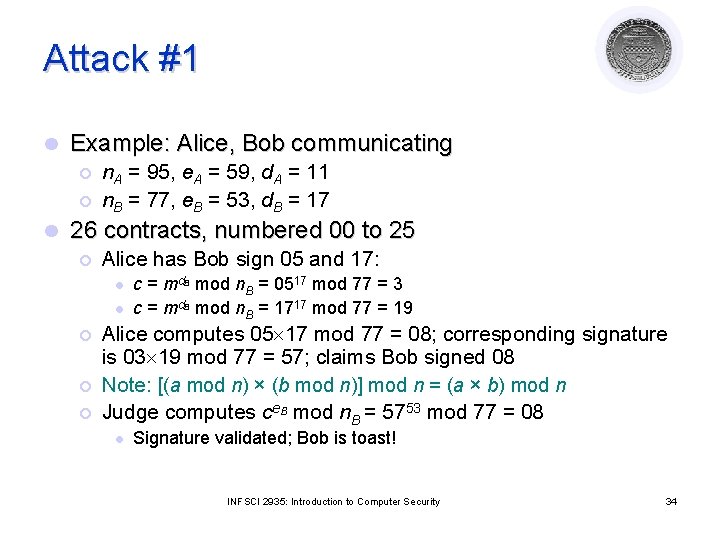
Attack #1 l Example: Alice, Bob communicating ¡ ¡ l n. A = 95, e. A = 59, d. A = 11 n. B = 77, e. B = 53, d. B = 17 26 contracts, numbered 00 to 25 ¡ Alice has Bob sign 05 and 17: l l ¡ ¡ ¡ c = md. B mod n. B = 0517 mod 77 = 3 c = md. B mod n. B = 1717 mod 77 = 19 Alice computes 05 17 mod 77 = 08; corresponding signature is 03 19 mod 77 = 57; claims Bob signed 08 Note: [(a mod n) × (b mod n)] mod n = (a × b) mod n Judge computes ce. B mod n. B = 5753 mod 77 = 08 l Signature validated; Bob is toast! INFSCI 2935: Introduction to Computer Security 34
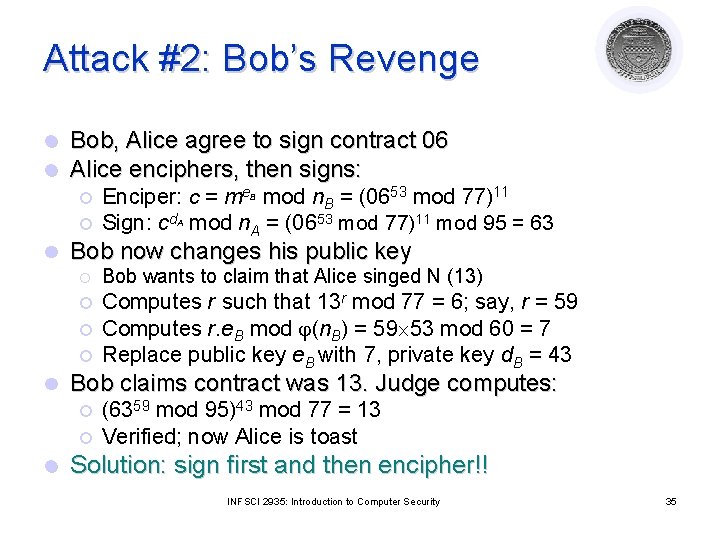
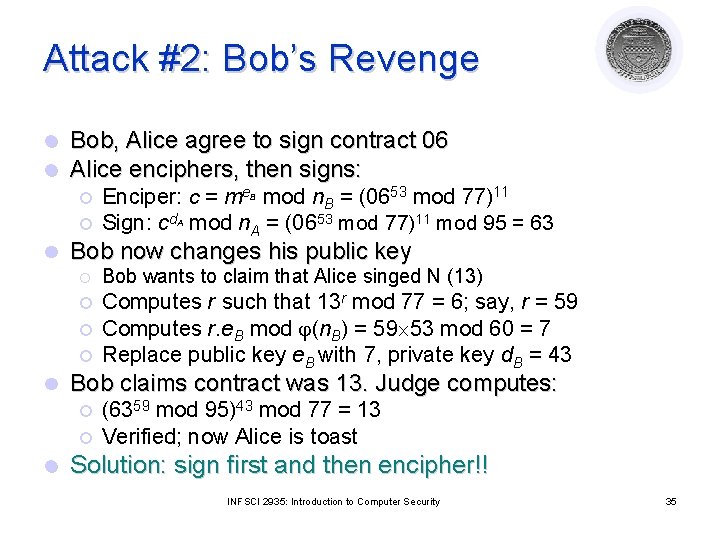
Attack #2: Bob’s Revenge l l Bob, Alice agree to sign contract 06 Alice enciphers, then signs: ¡ ¡ l Bob now changes his public key ¡ Bob wants to claim that Alice singed N (13) ¡ Computes r such that 13 r mod 77 = 6; say, r = 59 Computes r. e. B mod (n. B) = 59 53 mod 60 = 7 Replace public key e. B with 7, private key d. B = 43 ¡ ¡ l Bob claims contract was 13. Judge computes: ¡ ¡ l Enciper: c = me. B mod n. B = (0653 mod 77)11 Sign: cd. A mod n. A = (0653 mod 77)11 mod 95 = 63 (6359 mod 95)43 mod 77 = 13 Verified; now Alice is toast Solution: sign first and then encipher!! INFSCI 2935: Introduction to Computer Security 35
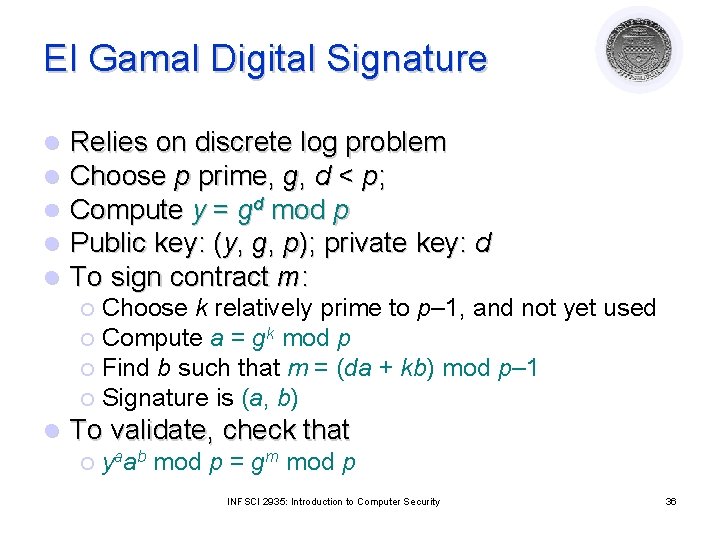
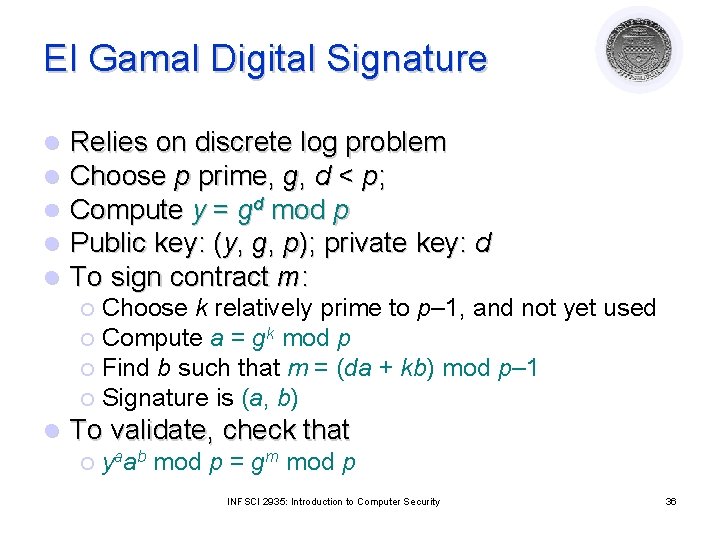
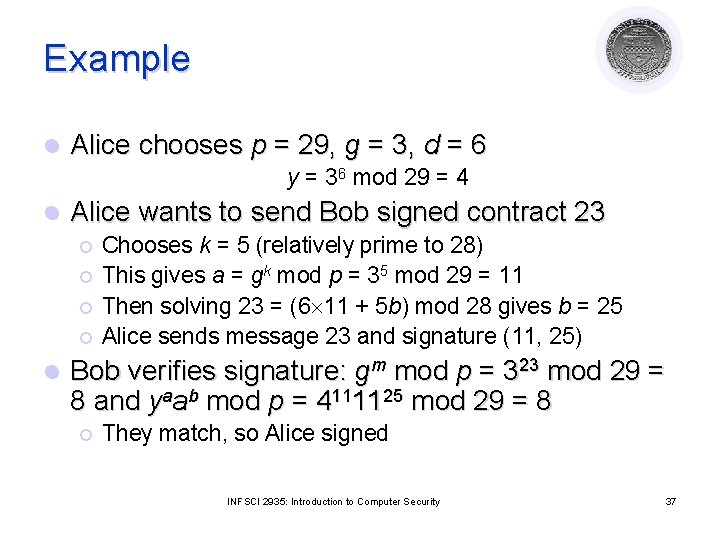
El Gamal Digital Signature l l l Relies on discrete log problem Choose p prime, g, d < p; Compute y = gd mod p Public key: (y, g, p); private key: d To sign contract m: Choose k relatively prime to p– 1, and not yet used ¡ Compute a = gk mod p ¡ Find b such that m = (da + kb) mod p– 1 ¡ Signature is (a, b) ¡ l To validate, check that ¡ yaab mod p = gm mod p INFSCI 2935: Introduction to Computer Security 36
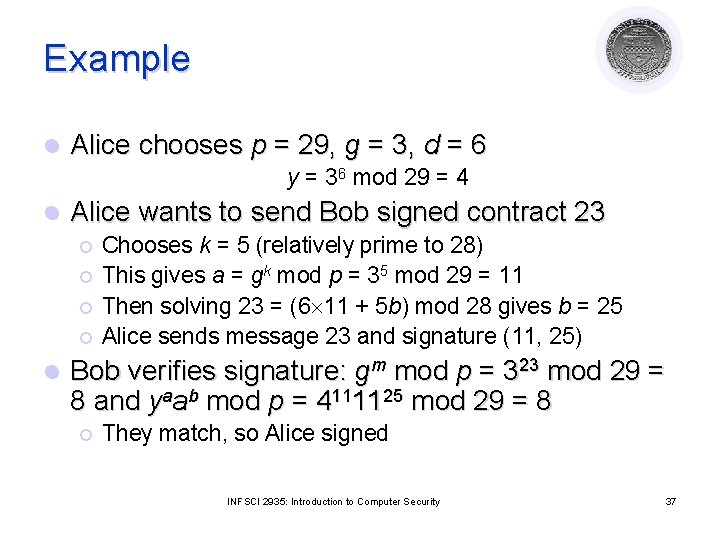
Example l Alice chooses p = 29, g = 3, d = 6 y = 36 mod 29 = 4 l Alice wants to send Bob signed contract 23 ¡ ¡ l Chooses k = 5 (relatively prime to 28) This gives a = gk mod p = 35 mod 29 = 11 Then solving 23 = (6 11 + 5 b) mod 28 gives b = 25 Alice sends message 23 and signature (11, 25) Bob verifies signature: gm mod p = 323 mod 29 = 8 and yaab mod p = 4111125 mod 29 = 8 ¡ They match, so Alice signed INFSCI 2935: Introduction to Computer Security 37
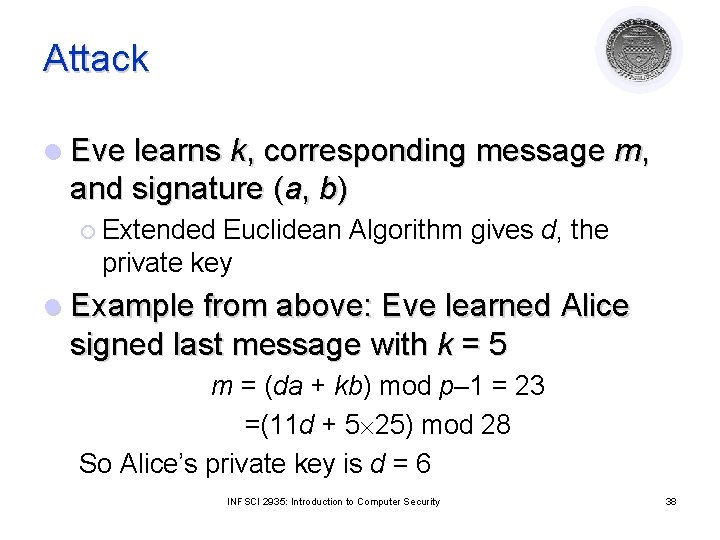
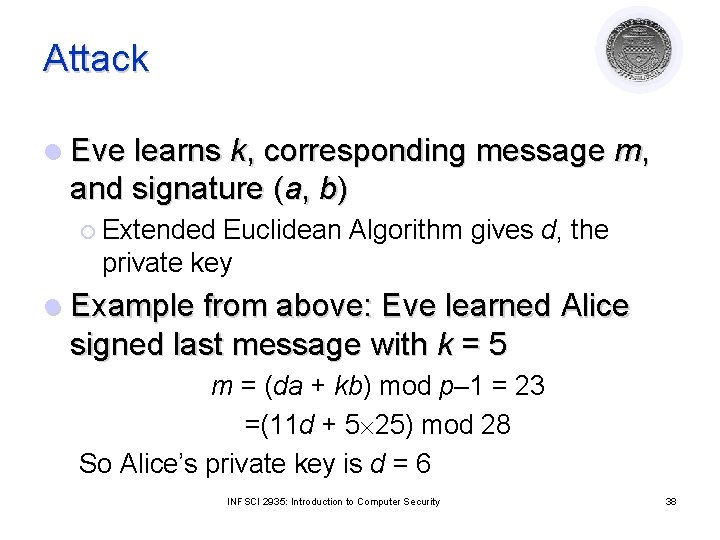
Attack l Eve learns k, corresponding message m, and signature (a, b) ¡ Extended Euclidean Algorithm gives d, the private key l Example from above: Eve learned Alice signed last message with k = 5 m = (da + kb) mod p– 1 = 23 =(11 d + 5 25) mod 28 So Alice’s private key is d = 6 INFSCI 2935: Introduction to Computer Security 38
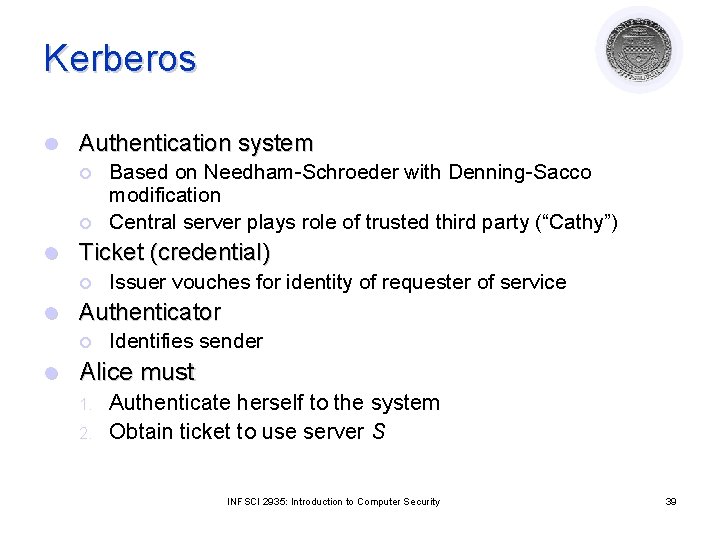
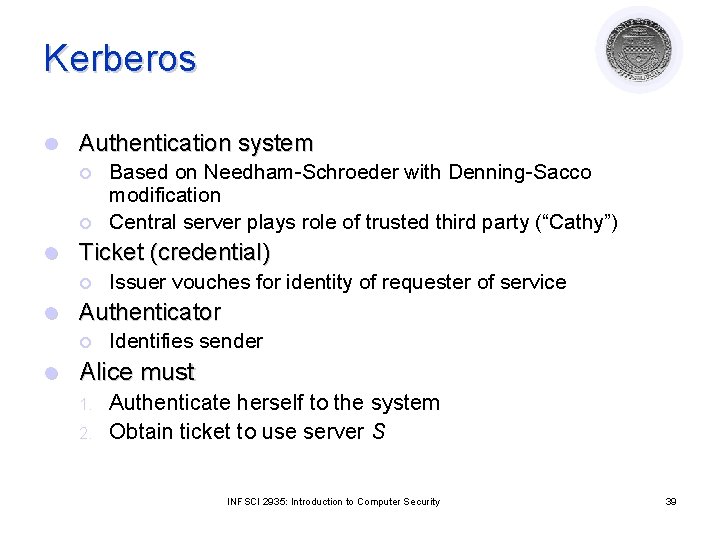
Kerberos l Authentication system ¡ ¡ l Ticket (credential) ¡ l Issuer vouches for identity of requester of service Authenticator ¡ l Based on Needham-Schroeder with Denning-Sacco modification Central server plays role of trusted third party (“Cathy”) Identifies sender Alice must 1. 2. Authenticate herself to the system Obtain ticket to use server S INFSCI 2935: Introduction to Computer Security 39
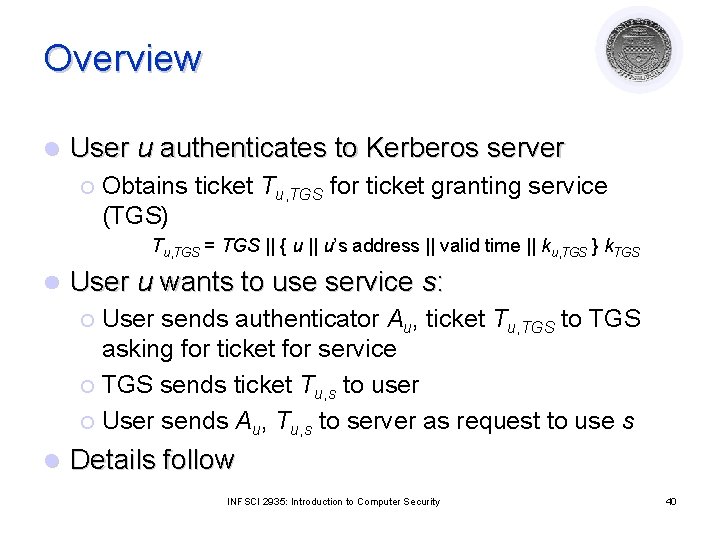
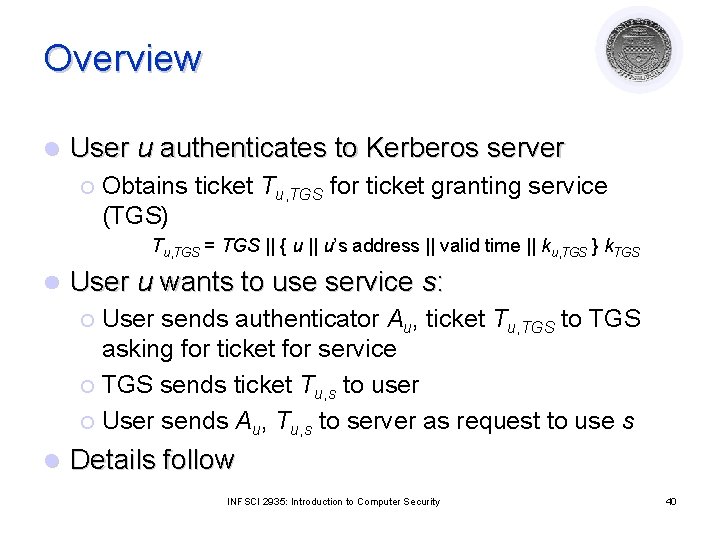
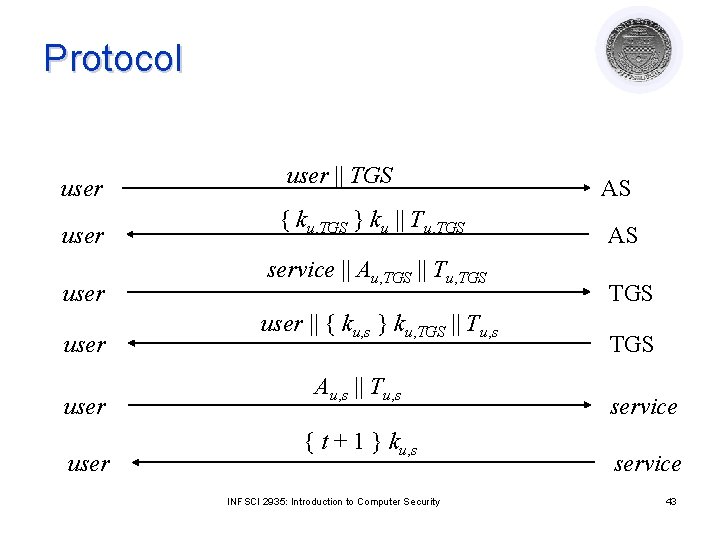
Overview l User u authenticates to Kerberos server ¡ Obtains ticket Tu, TGS for ticket granting service (TGS) Tu, TGS = TGS || { u || u’s address || valid time || ku, TGS } k. TGS l User u wants to use service s: User sends authenticator Au, ticket Tu, TGS to TGS asking for ticket for service ¡ TGS sends ticket Tu, s to user ¡ User sends Au, Tu, s to server as request to use s ¡ l Details follow INFSCI 2935: Introduction to Computer Security 40
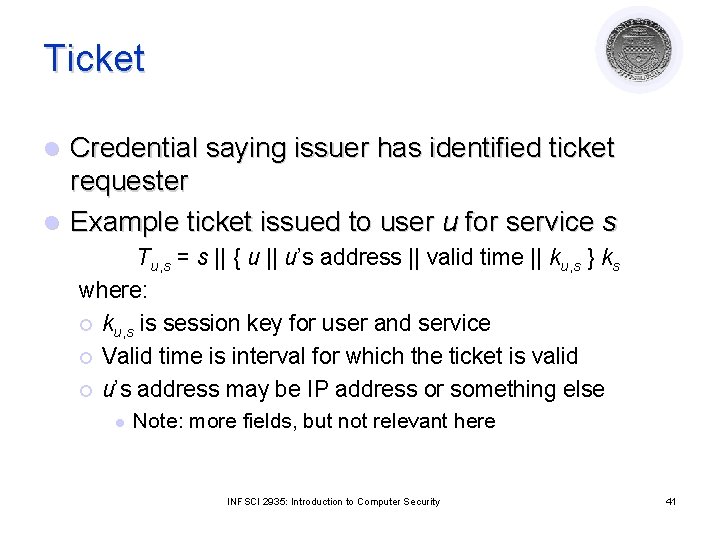
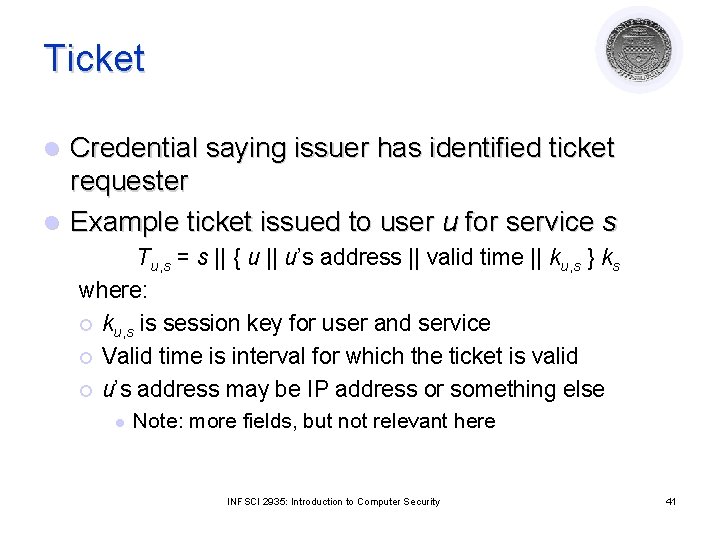
Ticket Credential saying issuer has identified ticket requester l Example ticket issued to user u for service s l Tu, s = s || { u || u’s address || valid time || ku, s } ks where: ¡ ku, s is session key for user and service ¡ Valid time is interval for which the ticket is valid ¡ u’s address may be IP address or something else l Note: more fields, but not relevant here INFSCI 2935: Introduction to Computer Security 41
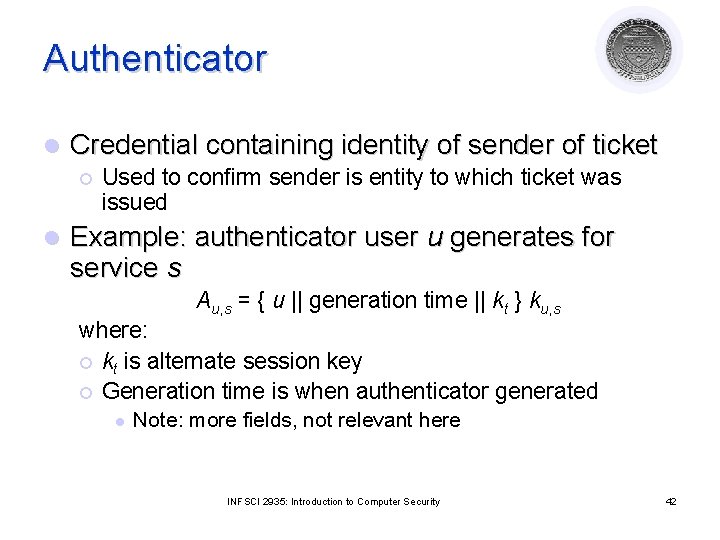
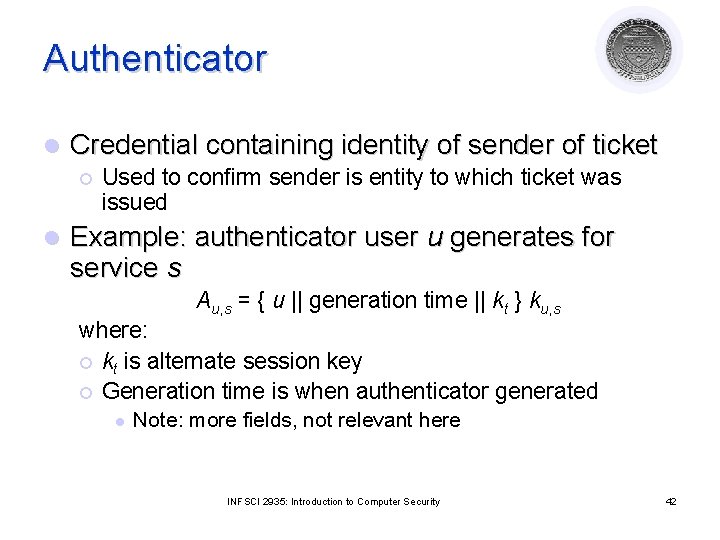
Authenticator l Credential containing identity of sender of ticket ¡ l Used to confirm sender is entity to which ticket was issued Example: authenticator user u generates for service s Au, s = { u || generation time || kt } ku, s where: ¡ kt is alternate session key ¡ Generation time is when authenticator generated l Note: more fields, not relevant here INFSCI 2935: Introduction to Computer Security 42
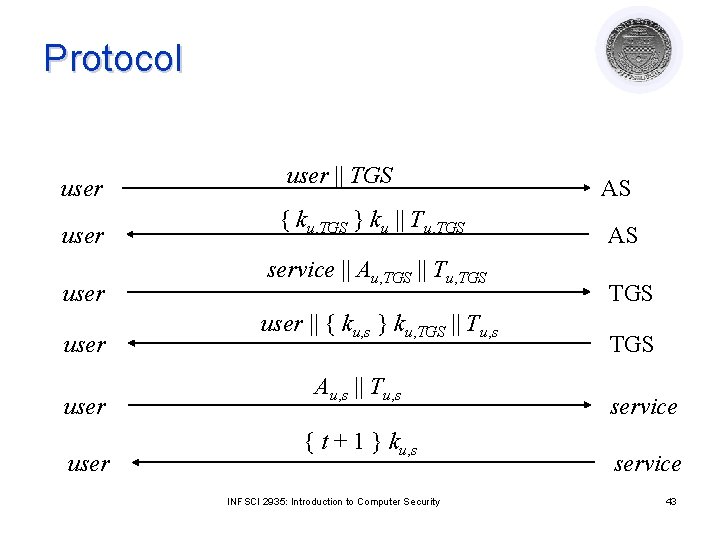
Protocol user user || TGS { ku, TGS } ku || Tu, TGS service || Au, TGS || Tu, TGS user || { ku, s } ku, TGS || Tu, s Au, s || Tu, s { t + 1 } ku, s INFSCI 2935: Introduction to Computer Security AS AS TGS service 43
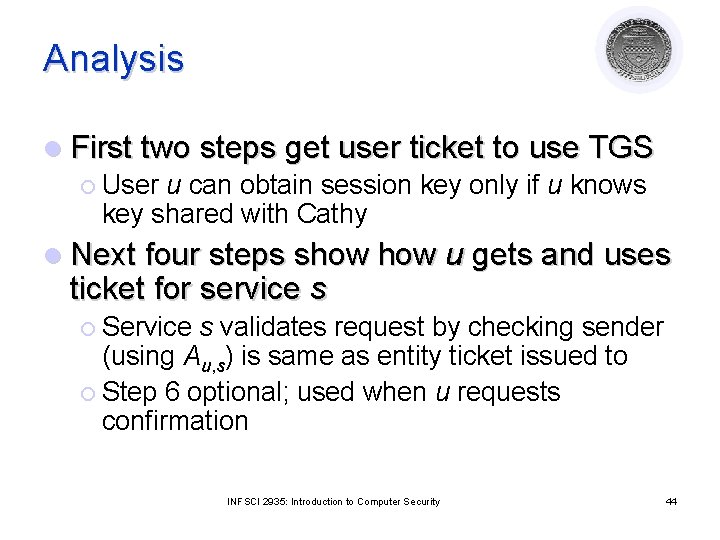
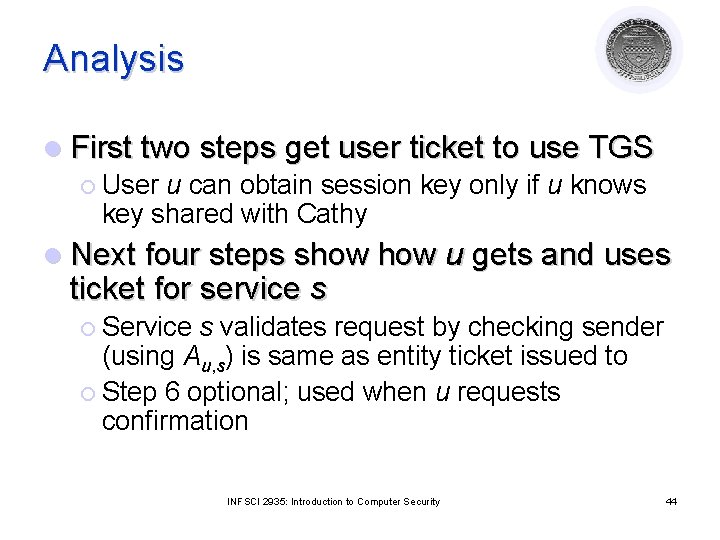
Analysis l First two steps get user ticket to use TGS ¡ User u can obtain session key only if u knows key shared with Cathy l Next four steps show ticket for service s u gets and uses ¡ Service s validates request by checking sender (using Au, s) is same as entity ticket issued to ¡ Step 6 optional; used when u requests confirmation INFSCI 2935: Introduction to Computer Security 44
Problems l Relies on synchronized clocks ¡ If not synchronized and old tickets, authenticators not cached, replay is possible l Tickets have some fixed fields ¡ Dictionary attacks possible ¡ Kerberos 4 session keys weak (had much less than 56 bits of randomness); researchers at Purdue found them from tickets in minutes INFSCI 2935: Introduction to Computer Security 45
Project l Implementation ¡ ¡ l Survey type paper ¡ ¡ ¡ l l Reasonable sophistication Up to 3 people Comparative/tradeoff studies Current trends, challenges, possible approaches One person! Number of references should be adequate (depends on area) No introductory stuff! New idea/research ? ? Others: Case studies? ? INFSCI 2935: Introduction to Computer Security 46
Project Topics (not limited to these only!) ¡ ¡ ¡ ¡ XML security Implementation of Access Control and Authentication Cryptographic protocols Database security Ad hoc network security Cyber Security Privacy Web service security / Java security Intrusion detection Auditing Systems Security and ethics/Usability/Economics Smartcards and standards for smartcards E-commerce security (secure transaction) Multimedia security Security in wireless/mobile environments Case studies from a specific domain INFSCI 2935: Introduction to Computer Security 47
Project Schedule l Proposal (by Nov 18) ¡ ¡ ¡ l Up to 2 pages (identify a group) State the goals State the significance Final project report ¡ ¡ By the last day of the semester Article format, or conference format l ¡ Each person should state his contribution Implementation projects should demonstrate to TA and/or me INFSCI 2935: Introduction to Computer Security 48