INFORMATION SECURITY MANAGEMENT LECTURE 6 SECURITY MANAGEMENT MODELS




- Slides: 61
INFORMATION SECURITY MANAGEMENT LECTURE 6: SECURITY MANAGEMENT MODELS You got to be careful if you don’t know where you’re going, because you might not get there. – Yogi Berra
Access Control Models • Access controls – Regulate the admission of users into trusted areas of the organization • Key principles of access control – Least privilege – Need to Know – Separation of Duties
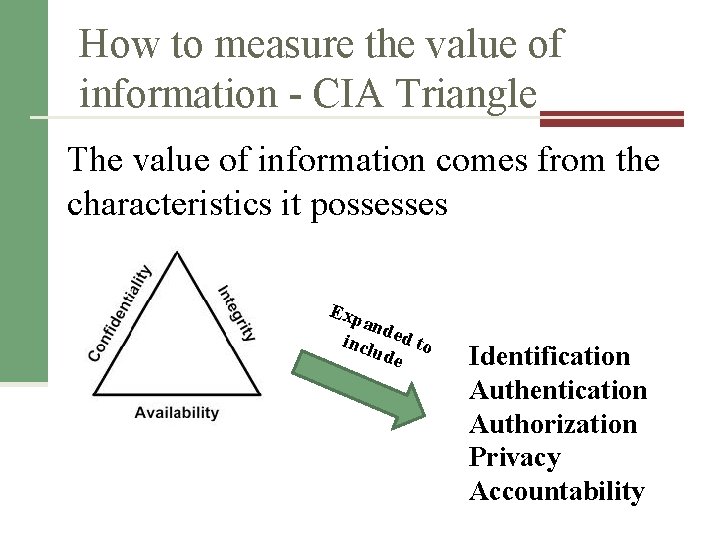
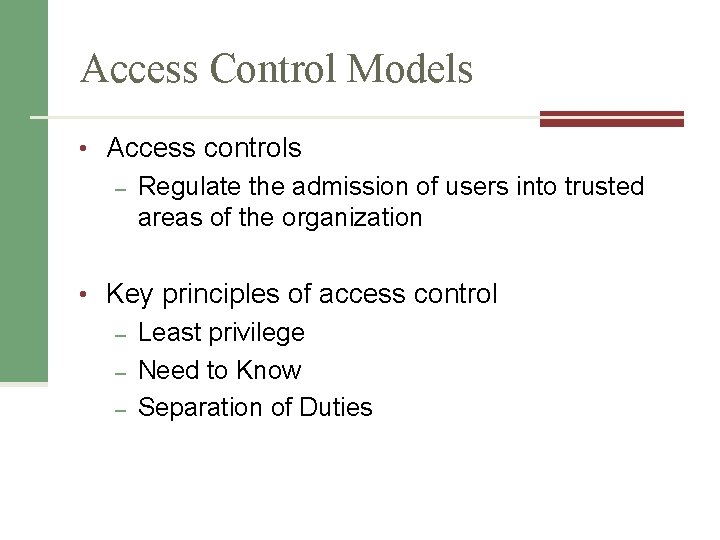
How to measure the value of information - CIA Triangle The value of information comes from the characteristics it possesses Exp and incl ed to ude Identification Authentication Authorization Privacy Accountability
Privacy Information collected, used, and stored by an organization is to be used only for the purposes stated to the data owner at the time it was collected Privacy as a characteristic of information does not signify freedom from observation n Means that information will be used only in ways known to the person providing it
Accountability Exists when a control provides assurance that every activity undertaken can be attributed to a named person or automated process
Identification and Authentication Identification – – An information system possesses the characteristic of identification when it is able to recognize individual users Identification and authentication are essential to establishing the level of access or authorization that an individual is granted Authentication – Occurs when a control proves that a user possesses the identity that he or she claims
Authorization Assures that the user has been specifically and explicitly authorized by the proper authority to access, update, or delete the contents of an information asset Authorization occurs after authentication

Controlling Access
Identification and Authentication n Identification: unproven assertion of identity n “My name is…” n Userid n Authentication: proven assertion of identity n Userid and password n Userid and PIN n Biometric
Authentication Methods n What the user knows n What the user has n What the user is
How Information Systems Authenticate Users n Request userid and password n Hash password n Retrieve stored userid and hashed password n Compare n Make a function call to a network based authentication service
How a System Stores Userids and Passwords n Typically stored in a database table n Application database or authentication database n Userid stored in plaintext n Password stored encrypted or hashed
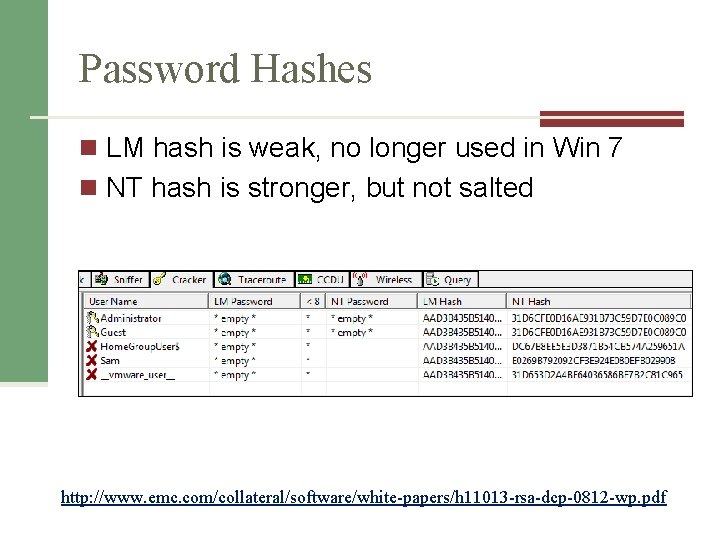
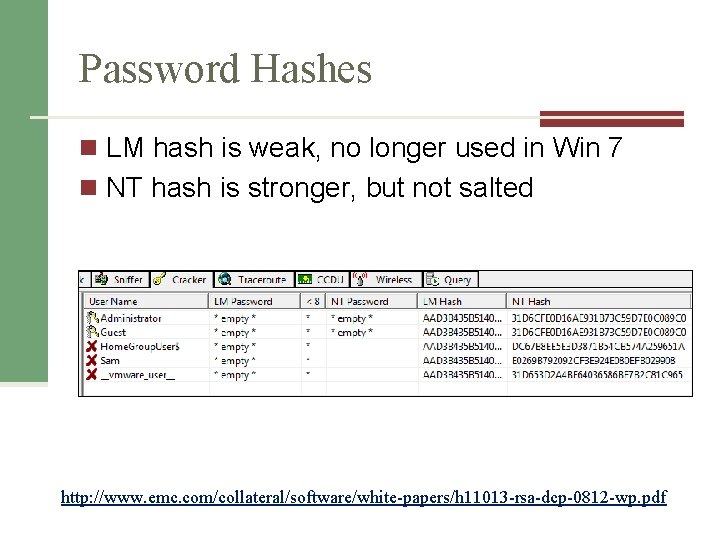
Password Hashes n LM hash is weak, no longer used in Win 7 n NT hash is stronger, but not salted http: //www. emc. com/collateral/software/white-papers/h 11013 -rsa-dcp-0812 -wp. pdf
Strong Authentication n Traditional userid + password authentication has known weaknesses n Stronger types of authentication available, usually referred to as “strong authentication”
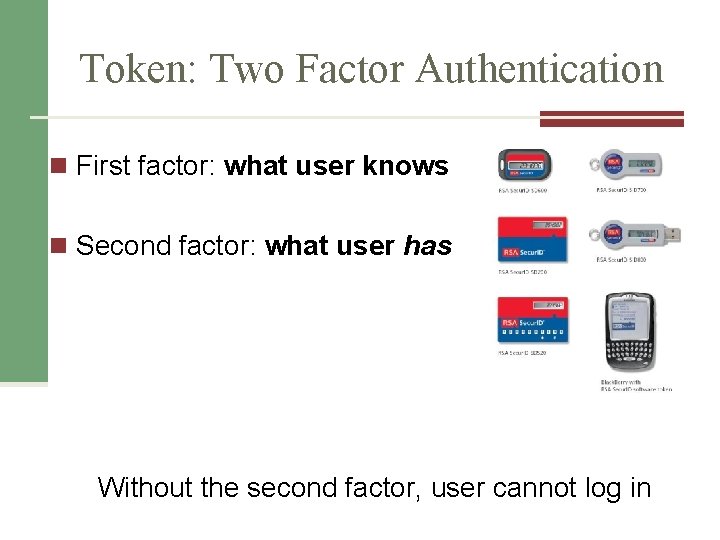
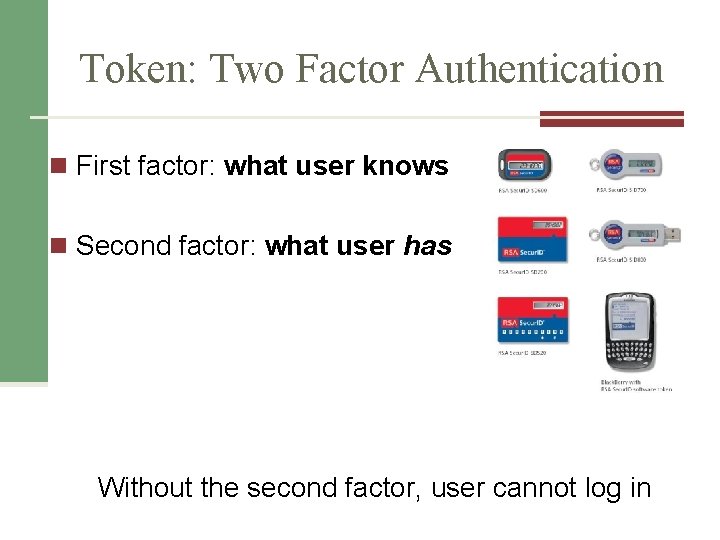
Token: Two Factor Authentication n First factor: what user knows n Second factor: what user has Without the second factor, user cannot log in
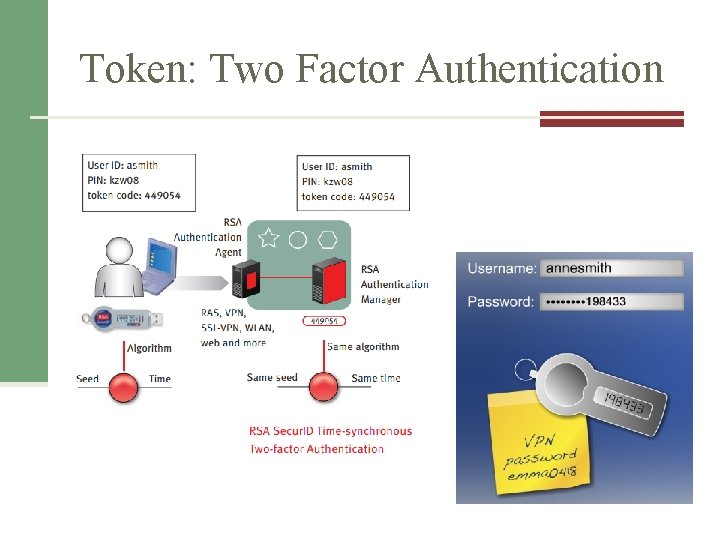
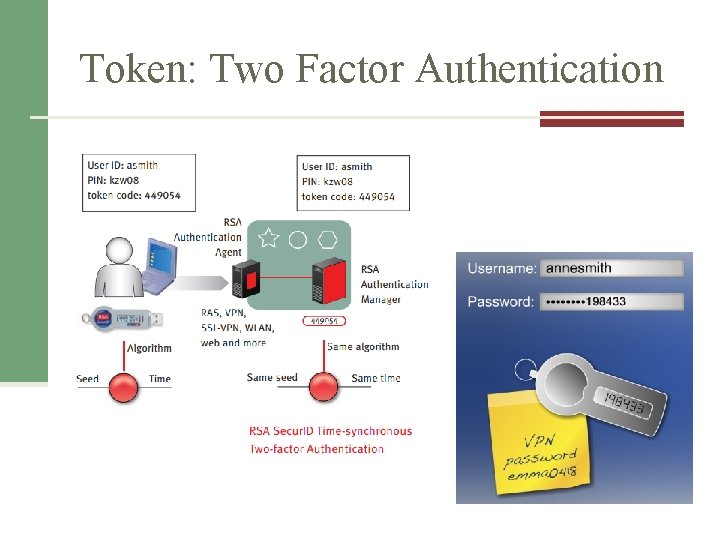
Token: Two Factor Authentication
Biometric Authentication n Stronger than userid + password n Stronger than two-factor? n Can be hacked
Authentication Issues n Password quality n Consistency of user credentials across multiple environments n Too many userids and passwords n Handling password resets n Dealing with compromised passwords n Staff terminations

Categories of Access Control
Categories of Access Control • Preventative • Deterrent • Detective • Corrective • Recovery • Compensating
Preventive Controls n Block or control specific events n Firewalls n Anti-virus software n Encryption n Key card systems n Bollards stop cars (as shown)
Deterrent/Detective Controls n Deterrent Controls n Highly visible n Prevent offenses by influencing choices of would-be intruders n Detective Controls n Monitor and record specific types of events n Does not stop or directly influence events
Corrective/Recovery Controls n Corrective Controls n Post-event controls to prevent recurrence n “Corrective” refers to when it is implemented n Examples (if implemented after an incident) n n n Spam filter Anti-virus on e-mail server WPA Wi-Fi encryption n Recovery Control n Post-incident controls to recover systems
Compensating Controls n Control that is introduced that compensates for the absence or failure of a control n “Compensating” refers to why it is implemented n Examples n Daily monitoring of anti-virus console n Monthly review of administrative logins n Web Application Firewall used to protect buggy application
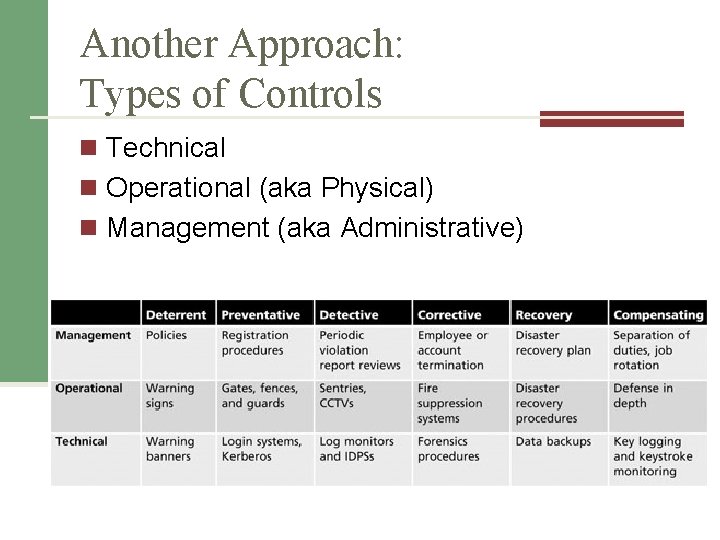
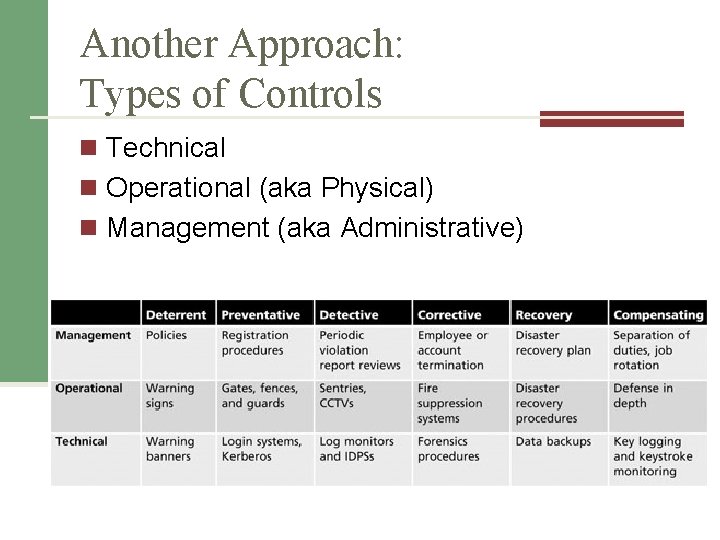
Another Approach: Types of Controls n Technical n Operational (aka Physical) n Management (aka Administrative)
Another Approach: Degree of Authority n Mandatory Access Controls n Discretionary Access Controls n Role Based Access Controls
Mandatory Access Control (MAC) Security Model • Data classification scheme • Rates collection of info and user with sensitivity levels • When implemented, users and data owners have limited control over access
Mandatory Access Control (MAC) Security Model • Data classification scheme/model – Data owners classify the information assets – Reviews periodically • Security clearance structure – Each user assigned an authorization level – Roles and corresponding security clearances
Discretionary Access Control (DAC) Security Model n The owner of an object controls who and what may access it. n Access is at the owner’s discretion. n Most personal computer operating systems are designed based on the DAC model
Role-based Access Control (RBAC) Security Model n Nondiscretionary Controls n An improvement over the mandatory access control (MAC) security model • • Role-based controls Task-based controls n Simplifies management in a complex system with many users and objects
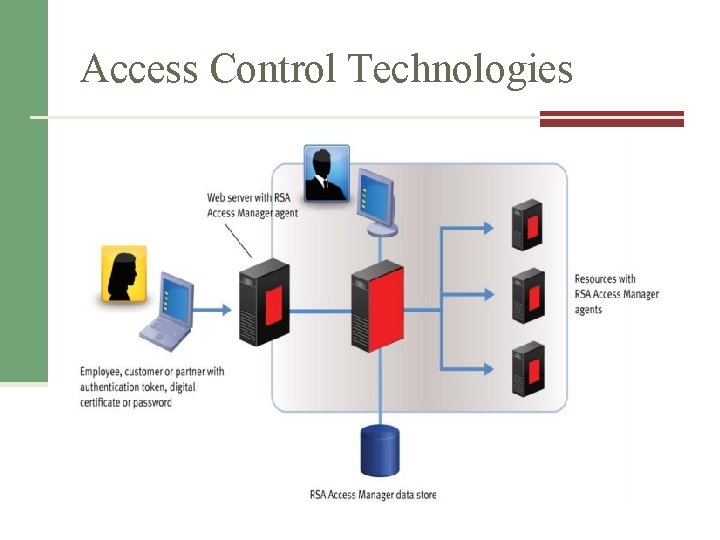
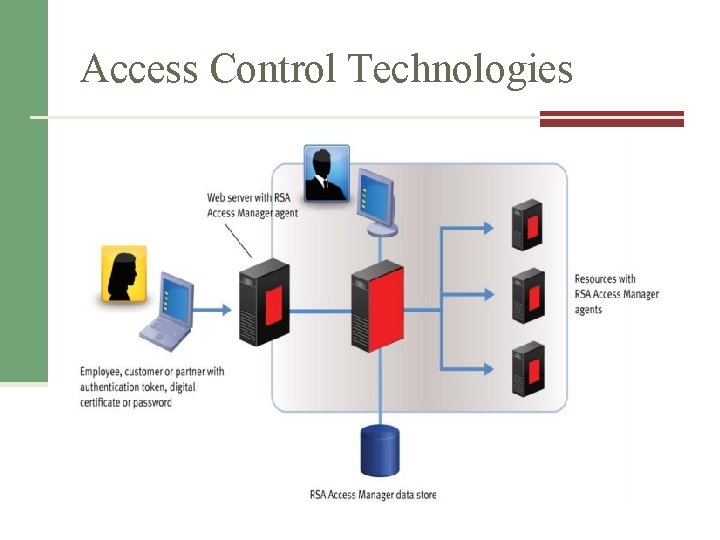
Access Control Technologies

Testing Access Controls
Testing Access Controls n Access controls are the primary defense that protect assets n Types of tests: n Penetration tests n Application vulnerability tests n Code reviews http: //secunia. com/community/
Penetration Testing n Automatic scans to discover vulnerabilities n Example tools: Nessus, Nikto, SAINT, Superscan, Retina, ISS, Microsoft Baseline Security Analyzer
Application Vulnerability Testing n Discover vulnerabilities in an application n Automated tools and manual tools n Example vulnerabilities n Cross-site scripting, injection flaws, malicious file execution, broken authentication, broken session management, information leakage, insecure use of encryption, and many more
Audit Log Analysis n Regular examination of audit and event logs n Detect unwanted events n Audit log protection

Access Control Attacks
Access Control Attacks n Intruders will try to defeat, bypass, or trick access controls in order to reach their target n Attack objectives n Guess credentials n Malfunction of access controls n Bypass access controls n Replay known good logins n Trick people into giving up credentials
Buffer Overflow n Cause malfunction in a way that permits illicit access n Send more data than application was designed to handle properly n Countermeasure: “safe” coding that limits length of input data; filter input data to remove unsafe characters
Script Injection n Insertion of scripting language characters into application input fields Execute script on server side n Execute script on client side – trick user or browser n n Countermeasures: strip “unsafe” characters from input
Data Remanence n Literally: data that remains after it has been “deleted” n Examples n Deleted hard drive files n Erased files n Discarded / lost media: USB keys, backup tapes, CDs n Countermeasures: improve media physical controls (e. g. post Wikileaks controls)
Denial of Service (Do. S) n Actions that cause target system to fail, thereby denying service to legitimate users n Distributed Denial of Service (DDo. S) n Countermeasures: input filters, patches, high capacity
Eavesdropping n Interception of data transmissions n Methods n Countermeasures: encryption, stronger encryption
Spoofing and Masquerading n Specially crafted network packets that contain forged address of origin n Countermeasures: router / firewall configuration to drop forged packets, judicious use of e-mail for signaling or data transfer http: //www. techrepublic. com/blog/security/how-to-spoof-a-mac-address/395
Social Engineering n Tricking people into giving out sensitive information by making them think they are helping someone n Methods n Schemes n Countermeasures: security awareness training
Phishing n Incoming, fraudulent e-mail messages designed to give the appearance of origin from a legitimate institution n Tricks user into providing sensitive data via a forged web site (common) or return e-mail (less common) n Countermeasure: security awareness training
Pharming n Redirection of traffic to a forged website n Countermeasures: user awareness training, patches, better controls
Malicious Code n Viruses, worms, Trojan horses, spyware, key logger n Harvest data or cause system malfunction n Countermeasures: anti-virus, anti-spyware, security awareness training
Security Architecture Models
Security Architecture Models • Can help organizations quickly make improvements through adaptation • Can focus on: – computer hardware and software – policies and practices – the confidentiality of information – the integrity of the information Pick one and go with it
Bell-La. Padula Confidentiality Model • A state machine model that helps ensure the confidentiality of an information system – Using mandatory access controls (MACs), data classification, and security clearances
Biba Integrity Model • Provides access controls to ensure that objects or subjects cannot have less integrity as a result of read/write operations • Ensures no information from a subject can be passed on to an object in a higher security level – This prevents contaminating data of higher integrity with data of lower integrity
Clark-Wilson Integrity Model • Built upon principles of change control rather than integrity levels • Its change control principles – No changes by unauthorized subjects – No unauthorized changes by authorized subjects – The maintenance of internal and external consistency
Graham-Denning Access Control Model • Composed of three parts – A set of objects – A set of subjects (a process and a domain) – A set of rights • • Primitive protection rights – Create or delete object, create or delete subject – Read, grant, transfer and delete access rights
Harrison-Ruzzo-Ullman Model • Defines a method to allow changes to access rights and the addition and removal of subjects and objects – Since systems change over time, their protective states need to change • Built on an access control matrix • Includes a set of generic rights and a specific set of commands
Brewer-Nash Model (aka Chinese Wall) • Designed to prevent a conflict of interest between two parties • Requires users to select one of two conflicting sets of data, after which they cannot access the conflicting data
The ISO 27000 Series • Information Technology – Code of Practice for Information Security Management – – – One of the most widely referenced and discussed security models Originally published as British Standard 7799 and then later as ISO/IEC 17799 Since been renamed ISO/IEC 27002 • Establishes guidelines for initiating, implementing, maintaining, and improving information security management
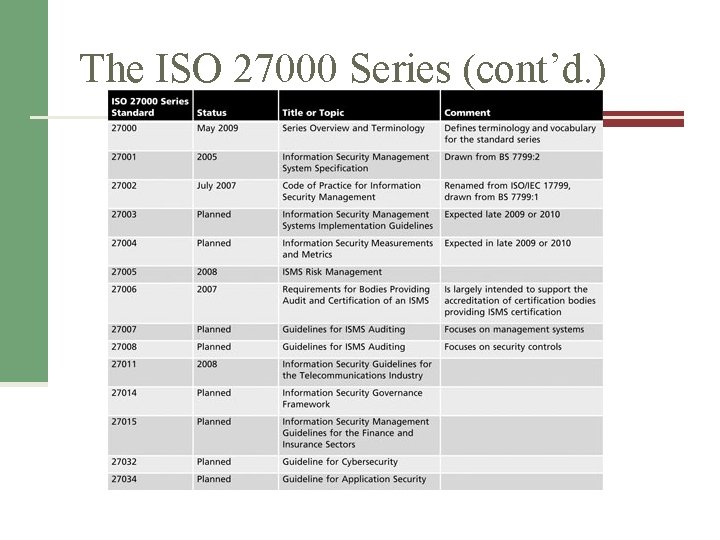
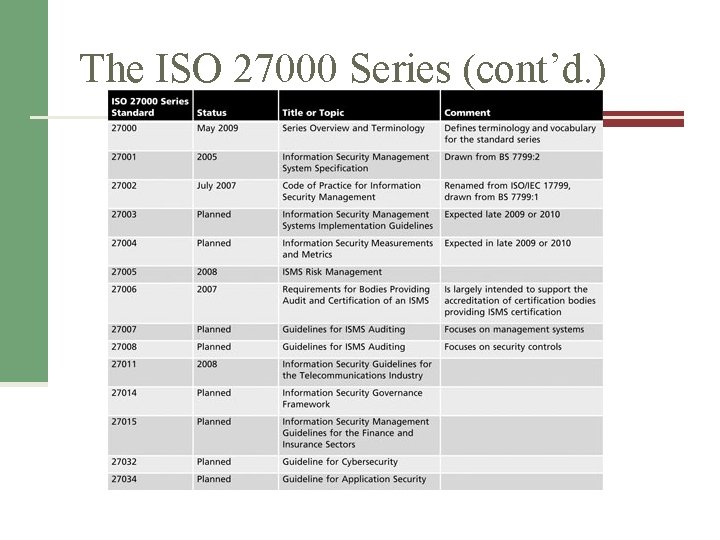
The ISO 27000 Series (cont’d. )
Control Objectives for Information and Related Technology (COBIT) • Control Objectives for Information and Related Technology (COBIT) – Provides advice about the implementation of sound controls and control objectives for Info. Sec – Created by the Information Systems Audit and Control Association (ISACA) and the IT Governance Institute (ITGI) in 1992
COSO • A U. S. private-sector initiative – Major Objective: identify factors that cause fraudulent financial reporting and to make recommendations to reduce its incidence – Has established a common definition of internal controls, standards and criteria – Helps organizations comply with critical regulations like Sarbanes-Oxley
COSO (cont’d. ) • Built on five interrelated components: – Control environment – Risk assessment – Control activities – Information and communication – Monitoring