Exterminator Automatically Correcting Memory Errors with High Probability
Exterminator: Automatically Correcting Memory Errors with High Probability Gene Novark Emery Berger University of Massachusetts Amherst Ben Zorn Microsoft Research UNIVERSITY OF MASSACHUSETTS AMHERST • Department of Computer Science • 2007
Problems with Unsafe Languages n n C, C++: pervasive apps, but unsafe Numerous opportunities for security vulnerabilities, errors n n n Double/Invalid free Uninitialized reads Dangling pointers Buffer overflows (stack & heap) Die. Hard: eliminates some, probabilistically avoids others [PLDI 2006] n Exterminator: builds on Die. Hard UNIVERSITY OF MASSACHUSETTS AMHERST • Department of Computer Science • 2007
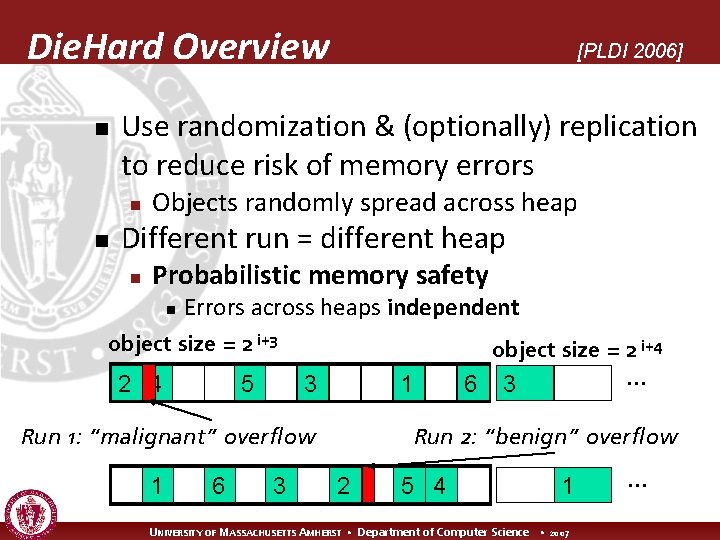
Die. Hard Overview n Use randomization & (optionally) replication to reduce risk of memory errors n n [PLDI 2006] Objects randomly spread across heap Different run = different heap n Probabilistic memory safety n Errors across heaps independent object size = 2 i+3 2 4 5 3 1 Run 1: “malignant” overflow 1 6 3 object size = 2 i+4 … 6 3 Run 2: “benign” overflow 2 5 4 1 UNIVERSITY OF MASSACHUSETTS AMHERST • Department of Computer Science • 2007 …
Die. Hard Limitations n Die. Hard: n Fine for single error n n n Tolerates errors n n n But multiple errors eventually swamp probabilistic protection Not great for large overflows But doesn’t find them No information for programmer Exterminator: Automatically isolate and fix memory errors UNIVERSITY OF MASSACHUSETTS AMHERST • Department of Computer Science • 2007
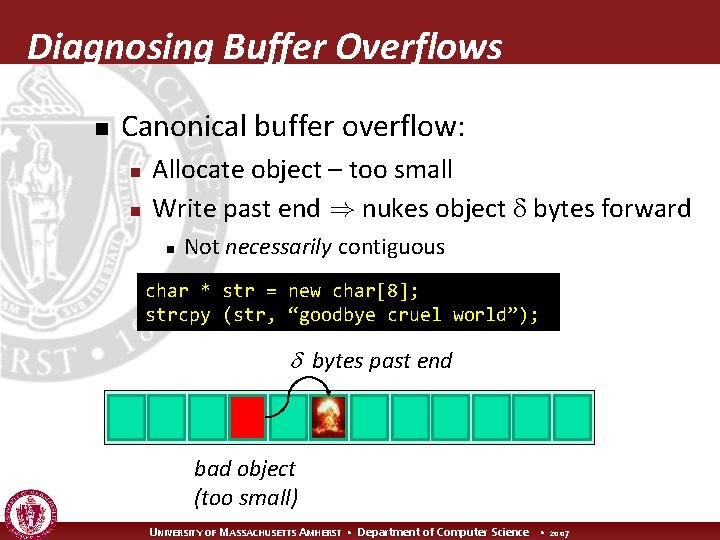
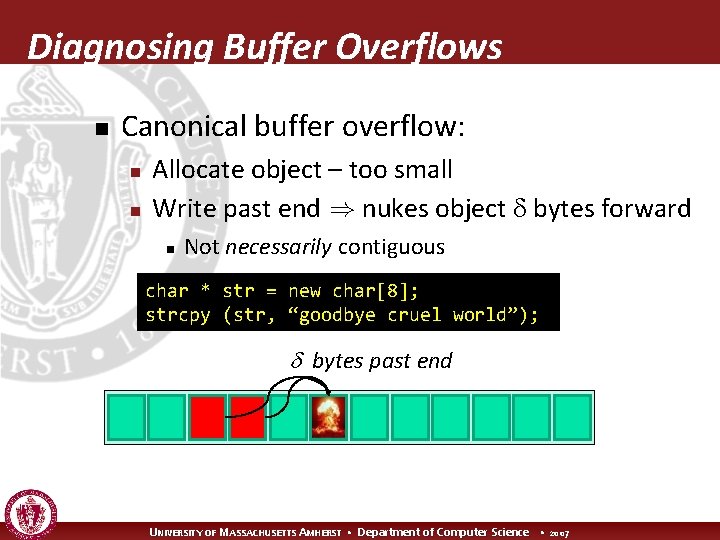
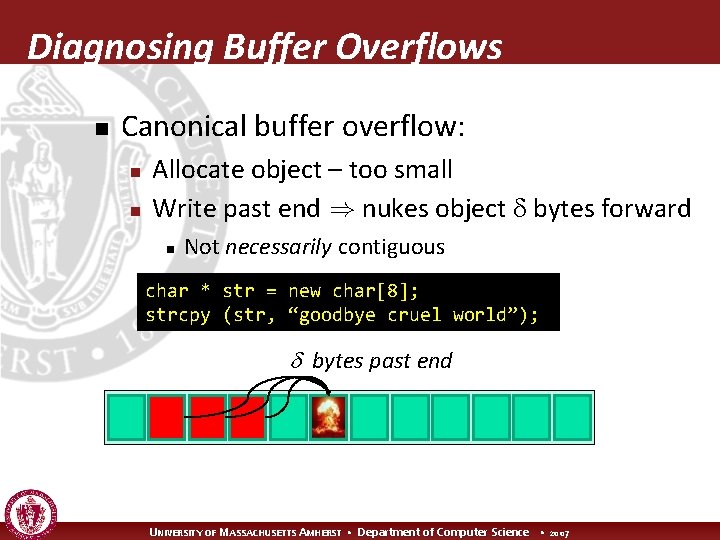
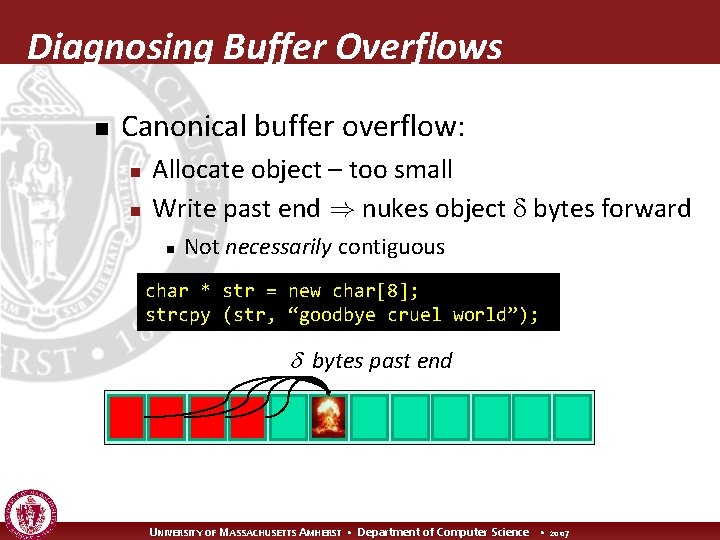
Diagnosing Buffer Overflows n Canonical buffer overflow: n n Allocate object – too small Write past end ) nukes object bytes forward n Not necessarily contiguous char * str = new char[8]; strcpy (str, “goodbye cruel world”); UNIVERSITY OF MASSACHUSETTS AMHERST • Department of Computer Science • 2007
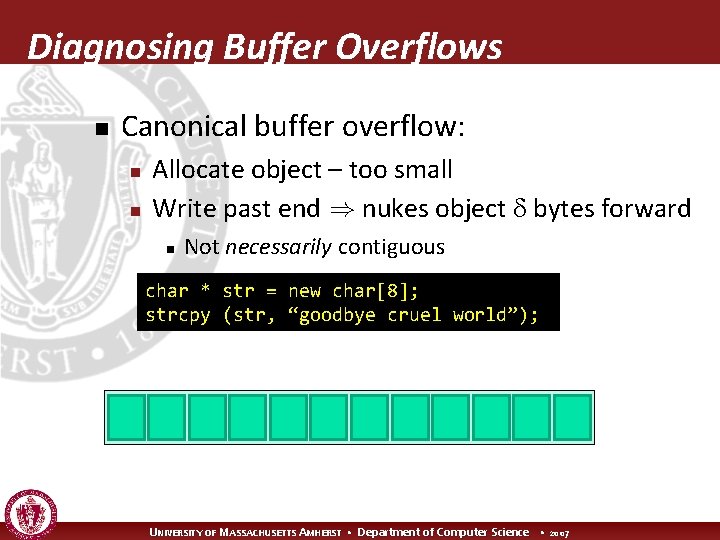
Diagnosing Buffer Overflows n Canonical buffer overflow: n n Allocate object – too small Write past end ) nukes object bytes forward n Not necessarily contiguous char * str = new char[8]; strcpy (str, “goodbye cruel world”); UNIVERSITY OF MASSACHUSETTS AMHERST • Department of Computer Science • 2007
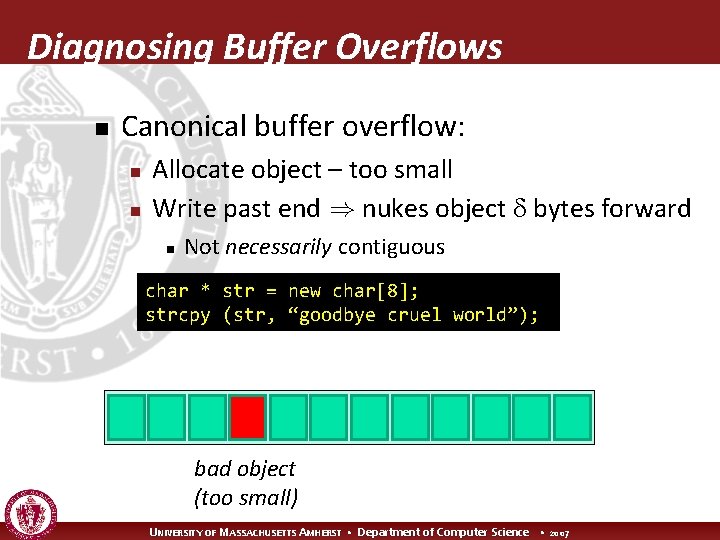
Diagnosing Buffer Overflows n Canonical buffer overflow: n n Allocate object – too small Write past end ) nukes object bytes forward n Not necessarily contiguous char * str = new char[8]; strcpy (str, “goodbye cruel world”); bad object (too small) UNIVERSITY OF MASSACHUSETTS AMHERST • Department of Computer Science • 2007
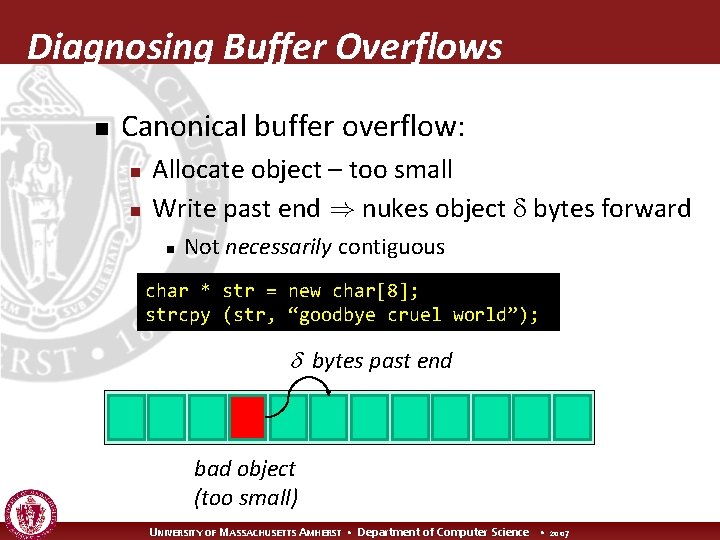
Diagnosing Buffer Overflows n Canonical buffer overflow: n n Allocate object – too small Write past end ) nukes object bytes forward n Not necessarily contiguous char * str = new char[8]; strcpy (str, “goodbye cruel world”); bytes past end bad object (too small) UNIVERSITY OF MASSACHUSETTS AMHERST • Department of Computer Science • 2007
Diagnosing Buffer Overflows n Canonical buffer overflow: n n Allocate object – too small Write past end ) nukes object bytes forward n Not necessarily contiguous char * str = new char[8]; strcpy (str, “goodbye cruel world”); bytes past end bad object (too small) UNIVERSITY OF MASSACHUSETTS AMHERST • Department of Computer Science • 2007
Diagnosing Buffer Overflows n Canonical buffer overflow: n n Allocate object – too small Write past end ) nukes object bytes forward n Not necessarily contiguous char * str = new char[8]; strcpy (str, “goodbye cruel world”); bytes past end UNIVERSITY OF MASSACHUSETTS AMHERST • Department of Computer Science • 2007
Diagnosing Buffer Overflows n Canonical buffer overflow: n n Allocate object – too small Write past end ) nukes object bytes forward n Not necessarily contiguous char * str = new char[8]; strcpy (str, “goodbye cruel world”); bytes past end UNIVERSITY OF MASSACHUSETTS AMHERST • Department of Computer Science • 2007
Diagnosing Buffer Overflows n Canonical buffer overflow: n n Allocate object – too small Write past end ) nukes object bytes forward n Not necessarily contiguous char * str = new char[8]; strcpy (str, “goodbye cruel world”); bytes past end UNIVERSITY OF MASSACHUSETTS AMHERST • Department of Computer Science • 2007
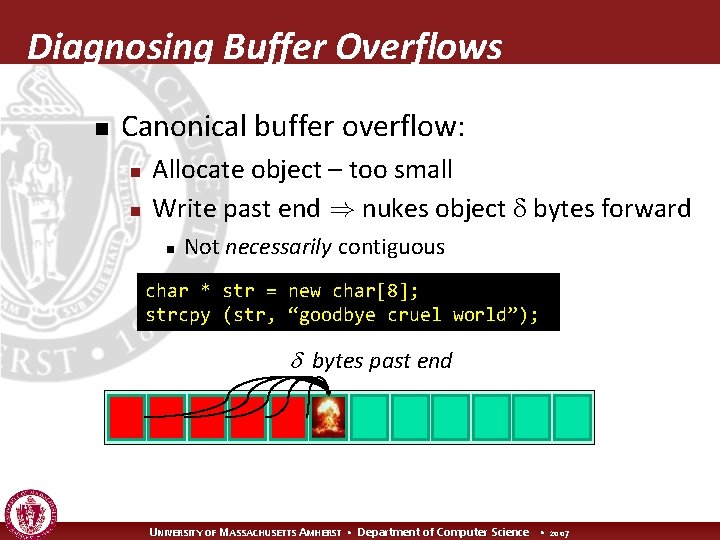
Diagnosing Buffer Overflows n Canonical buffer overflow: n n Allocate object – too small Write past end ) nukes object bytes forward n Not necessarily contiguous char * str = new char[8]; strcpy (str, “goodbye cruel world”); bytes past end UNIVERSITY OF MASSACHUSETTS AMHERST • Department of Computer Science • 2007
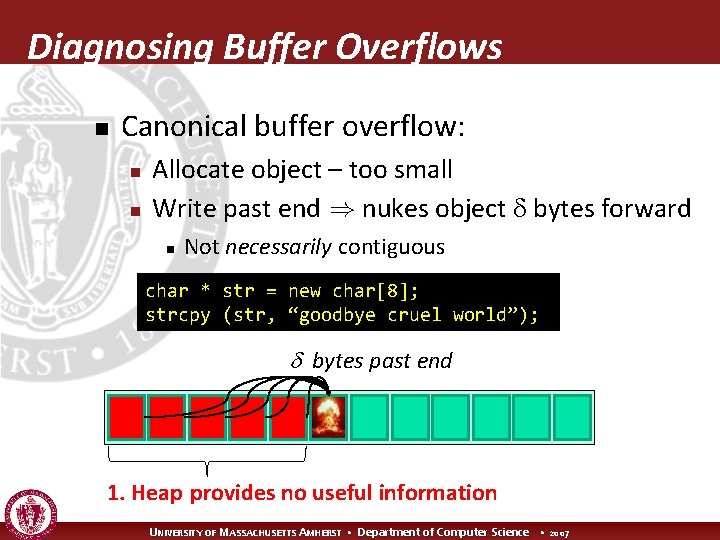
Diagnosing Buffer Overflows n Canonical buffer overflow: n n Allocate object – too small Write past end ) nukes object bytes forward n Not necessarily contiguous char * str = new char[8]; strcpy (str, “goodbye cruel world”); bytes past end 1. Heap provides no useful information UNIVERSITY OF MASSACHUSETTS AMHERST • Department of Computer Science • 2007
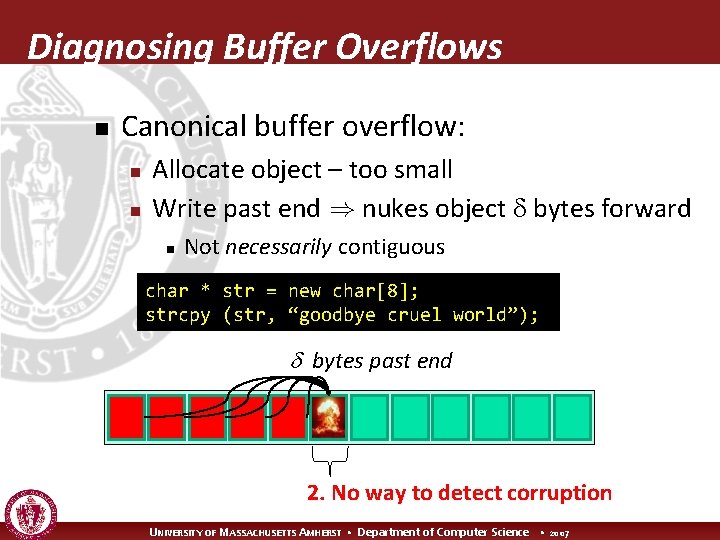
Diagnosing Buffer Overflows n Canonical buffer overflow: n n Allocate object – too small Write past end ) nukes object bytes forward n Not necessarily contiguous char * str = new char[8]; strcpy (str, “goodbye cruel world”); bytes past end 2. No way to detect corruption UNIVERSITY OF MASSACHUSETTS AMHERST • Department of Computer Science • 2007
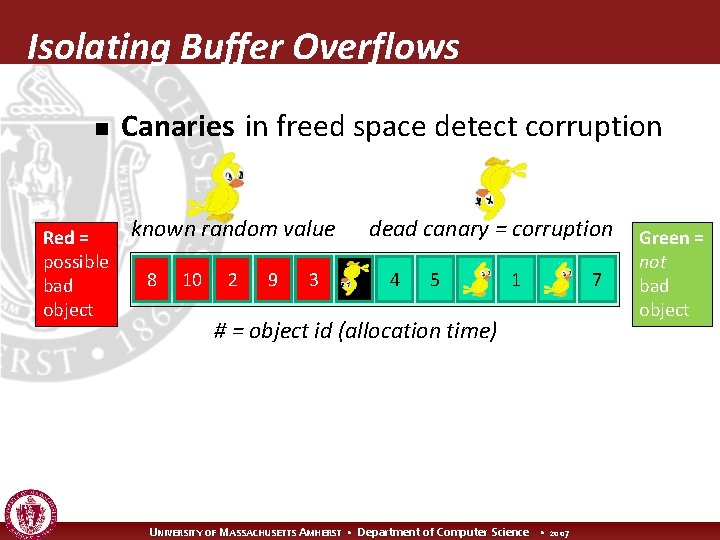
Isolating Buffer Overflows n Red = possible bad object Canaries in freed space detect corruption known random value 8 10 2 9 3 dead canary = corruption 4 5 1 # = object id (allocation time) UNIVERSITY OF MASSACHUSETTS AMHERST • Department of Computer Science • 2007 7 Green = not bad object
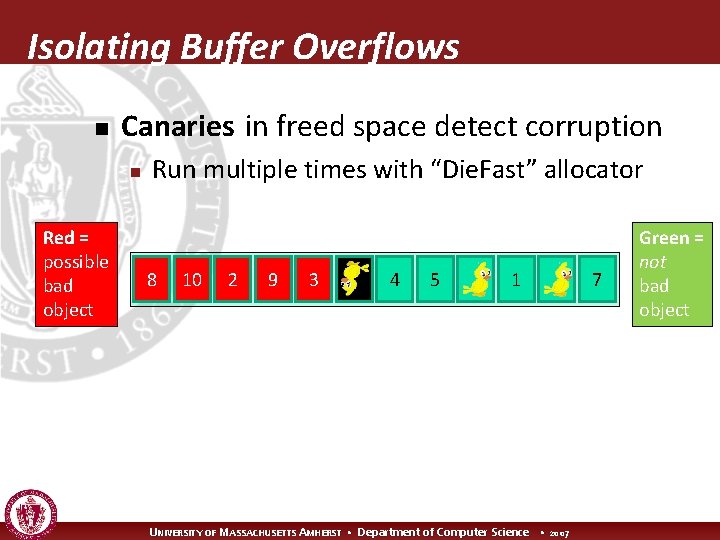
Isolating Buffer Overflows n Canaries in freed space detect corruption n Red = possible bad object Run multiple times with “Die. Fast” allocator 8 10 2 9 3 4 5 1 UNIVERSITY OF MASSACHUSETTS AMHERST • Department of Computer Science • 2007 7 Green = not bad object
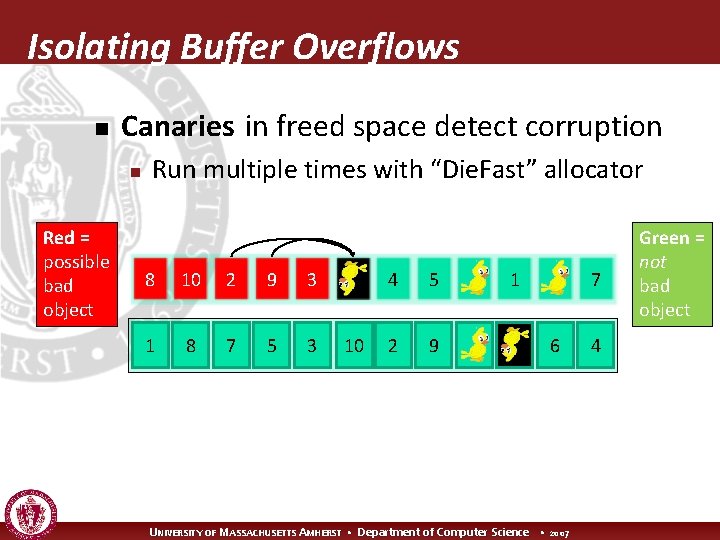
Isolating Buffer Overflows n Canaries in freed space detect corruption n Red = possible bad object Run multiple times with “Die. Fast” allocator 8 10 2 9 3 1 8 7 5 3 10 4 5 2 9 1 7 6 UNIVERSITY OF MASSACHUSETTS AMHERST • Department of Computer Science • 2007 4 Green = not bad object
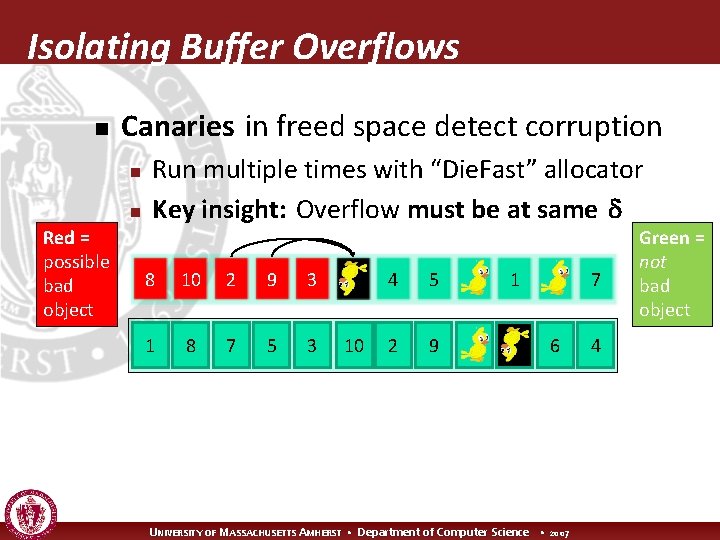
Isolating Buffer Overflows n Canaries in freed space detect corruption n n Red = possible bad object Run multiple times with “Die. Fast” allocator Key insight: Overflow must be at same 8 10 2 9 3 1 8 7 5 3 10 4 5 2 9 1 7 6 UNIVERSITY OF MASSACHUSETTS AMHERST • Department of Computer Science • 2007 4 Green = not bad object
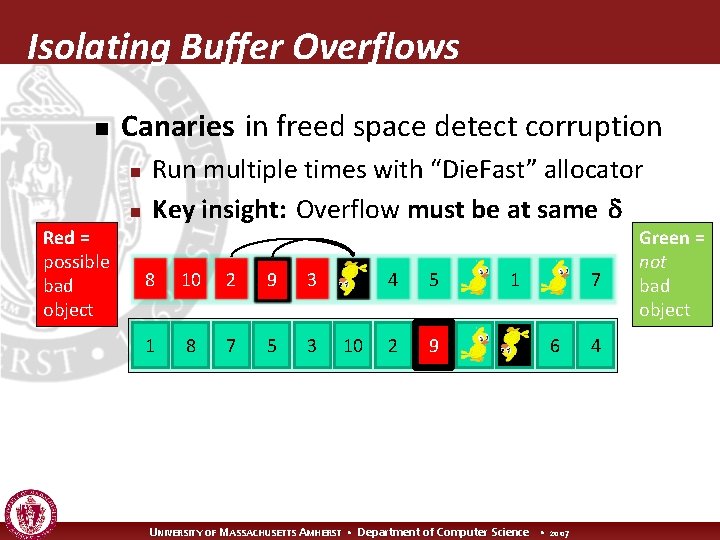
Isolating Buffer Overflows n Canaries in freed space detect corruption n n Red = possible bad object Run multiple times with “Die. Fast” allocator Key insight: Overflow must be at same 8 10 2 9 3 1 8 7 5 3 10 4 5 2 9 1 7 6 UNIVERSITY OF MASSACHUSETTS AMHERST • Department of Computer Science • 2007 4 Green = not bad object
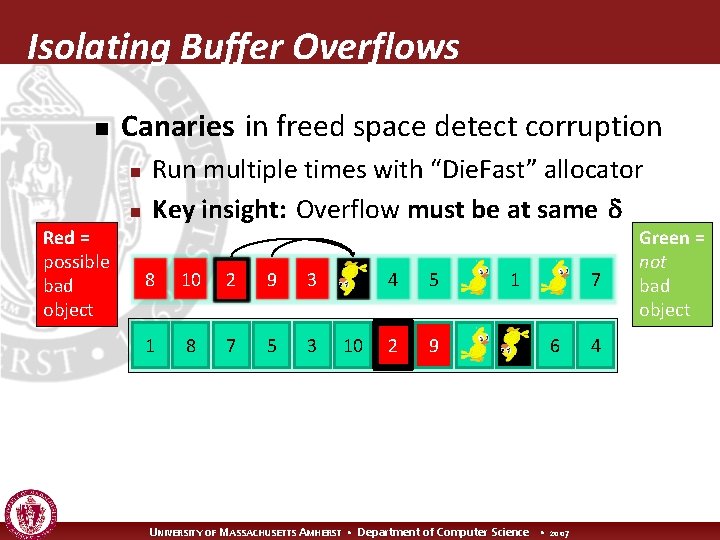
Isolating Buffer Overflows n Canaries in freed space detect corruption n n Red = possible bad object Run multiple times with “Die. Fast” allocator Key insight: Overflow must be at same 8 10 2 9 3 1 8 7 5 3 10 4 5 2 9 1 7 6 UNIVERSITY OF MASSACHUSETTS AMHERST • Department of Computer Science • 2007 4 Green = not bad object
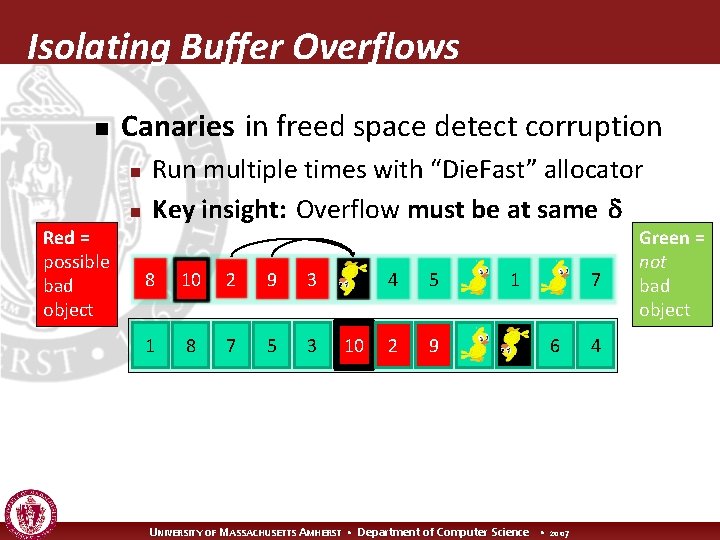
Isolating Buffer Overflows n Canaries in freed space detect corruption n n Red = possible bad object Run multiple times with “Die. Fast” allocator Key insight: Overflow must be at same 8 10 2 9 3 1 8 7 5 3 10 4 5 2 9 1 7 6 UNIVERSITY OF MASSACHUSETTS AMHERST • Department of Computer Science • 2007 4 Green = not bad object
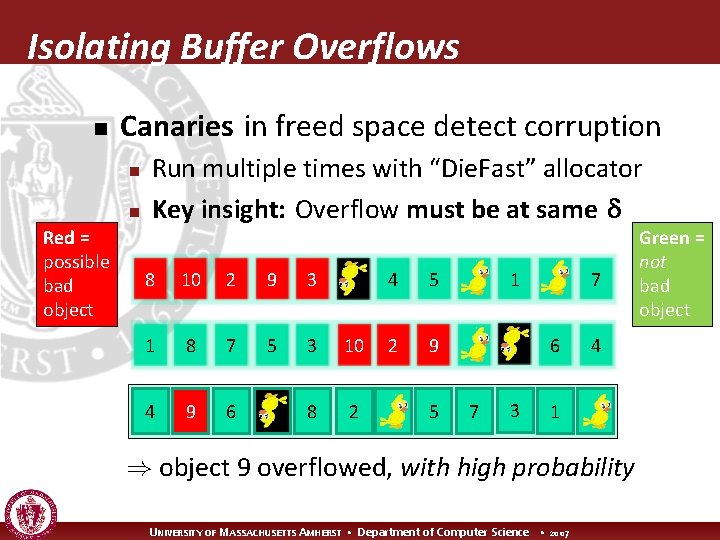
Isolating Buffer Overflows n Canaries in freed space detect corruption n n Red = possible bad object Run multiple times with “Die. Fast” allocator Key insight: Overflow must be at same 8 10 2 9 3 1 8 7 5 3 10 4 9 6 8 2 4 5 2 9 5 1 7 6 7 3 4 1 ) object 9 overflowed, with high probability UNIVERSITY OF MASSACHUSETTS AMHERST • Department of Computer Science • 2007 Green = not bad object
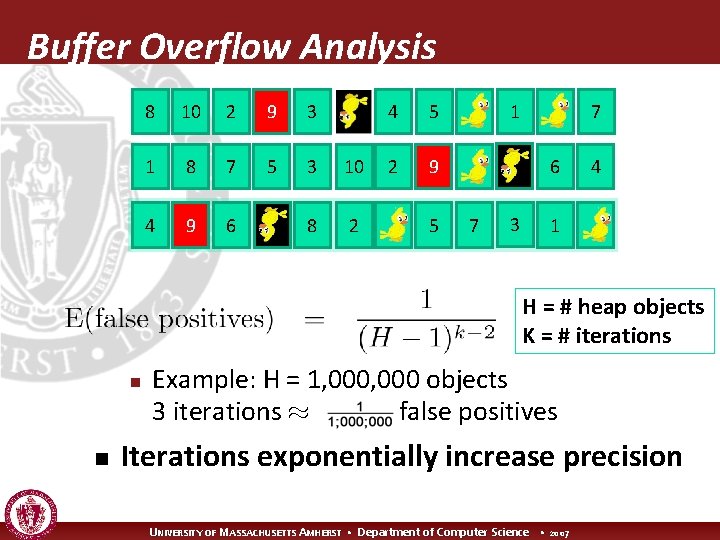
Buffer Overflow Analysis 8 10 2 9 3 1 8 7 5 3 10 4 9 6 8 2 4 5 2 9 5 1 7 6 7 3 4 1 H = # heap objects K = # iterations n n Example: H = 1, 000 objects 3 iterations ¼ false positives Iterations exponentially increase precision UNIVERSITY OF MASSACHUSETTS AMHERST • Department of Computer Science • 2007
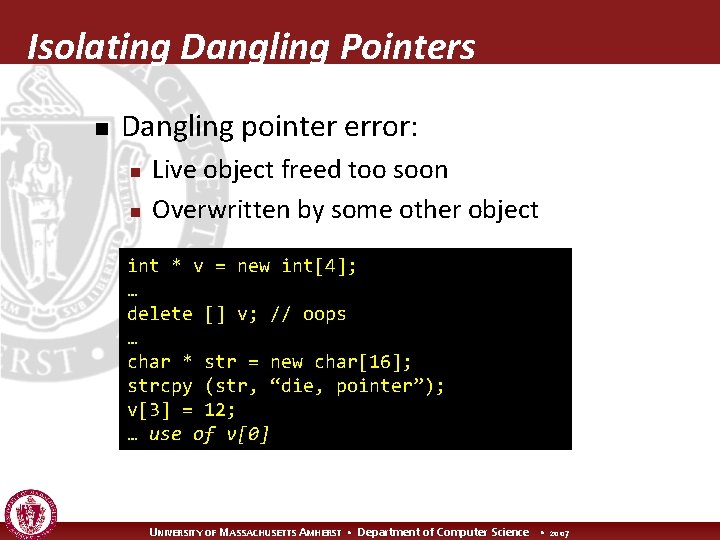
Isolating Dangling Pointers n Dangling pointer error: n n Live object freed too soon Overwritten by some other object int * v = new int[4]; … delete [] v; // oops … char * str = new char[16]; strcpy (str, “die, pointer”); v[3] = 12; … use of v[0] UNIVERSITY OF MASSACHUSETTS AMHERST • Department of Computer Science • 2007
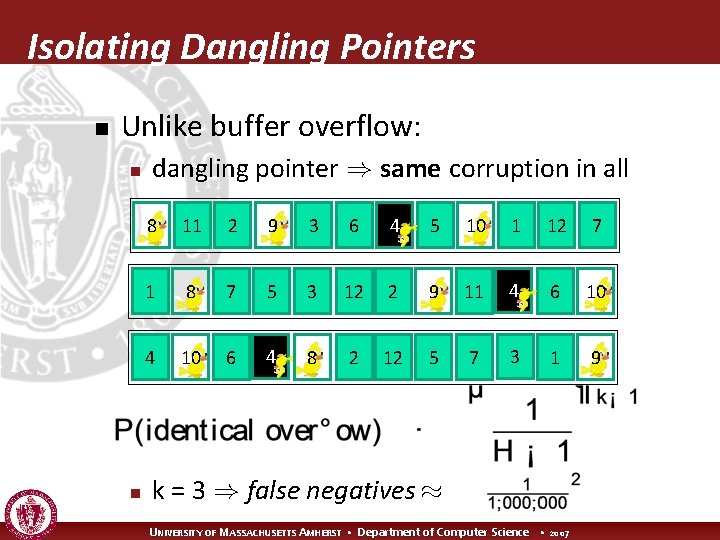
Isolating Dangling Pointers n Unlike buffer overflow: n n dangling pointer ) same corruption in all 8 11 2 9 3 6 4 5 10 1 12 7 1 8 7 5 3 12 2 9 11 4 6 10 4 10 6 4 8 2 12 5 7 3 1 9 k = 3 ) false negatives ¼ UNIVERSITY OF MASSACHUSETTS AMHERST • Department of Computer Science • 2007
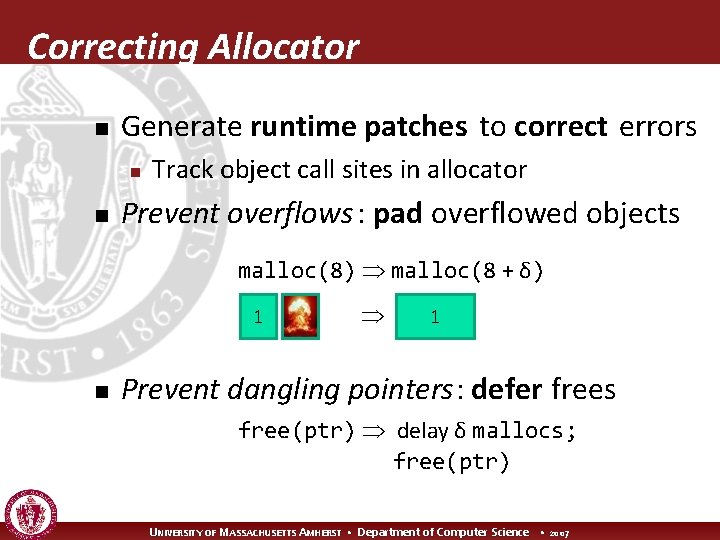
Correcting Allocator n Generate runtime patches to correct errors n n Track object call sites in allocator Prevent overflows : pad overflowed objects malloc(8) malloc(8 + δ) 1 n 1 Prevent dangling pointers: defer frees free(ptr) delay δ mallocs; free(ptr) UNIVERSITY OF MASSACHUSETTS AMHERST • Department of Computer Science • 2007
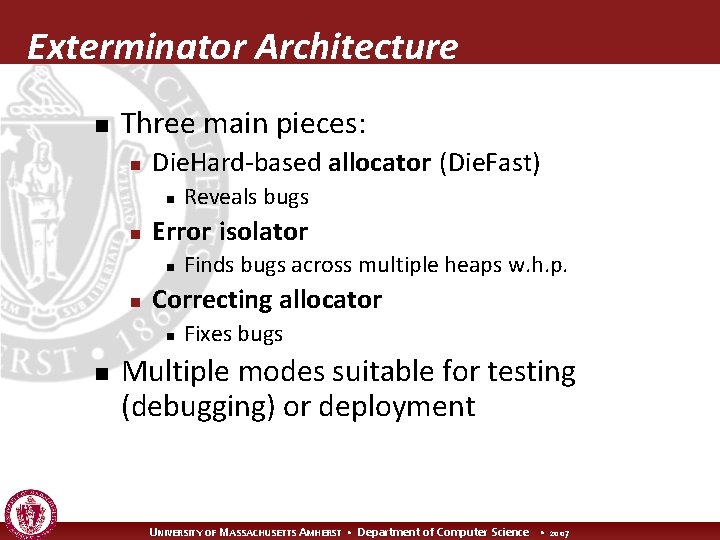
Exterminator Architecture n Three main pieces: n Die. Hard-based allocator (Die. Fast) n n Error isolator n n Finds bugs across multiple heaps w. h. p. Correcting allocator n n Reveals bugs Fixes bugs Multiple modes suitable for testing (debugging) or deployment UNIVERSITY OF MASSACHUSETTS AMHERST • Department of Computer Science • 2007
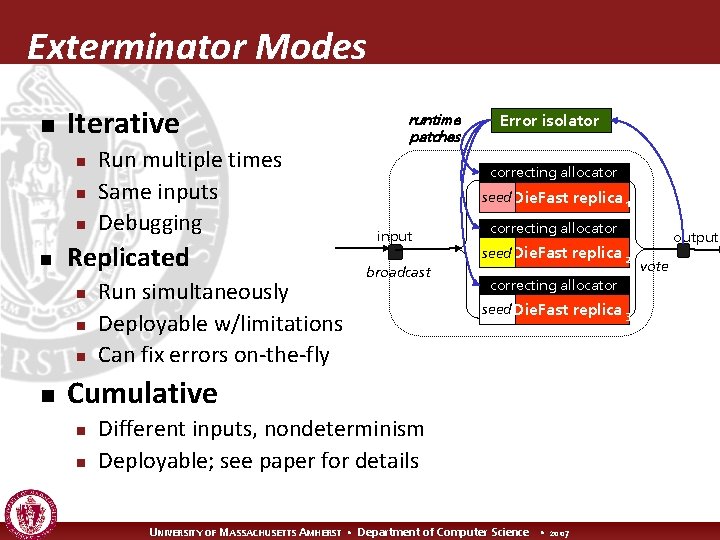
Exterminator Modes n Iterative n n Replicated n n Run multiple times Same inputs Debugging Run simultaneously Deployable w/limitations Can fix errors on-the-fly runtime patches Error isolator correcting allocator seed Die. Fast replica 1 input broadcast correcting allocator seed Die. Fast replica 2 correcting allocator seed Die. Fast replica 3 Cumulative n n Different inputs, nondeterminism Deployable; see paper for details UNIVERSITY OF MASSACHUSETTS AMHERST • Department of Computer Science • 2007 output vote
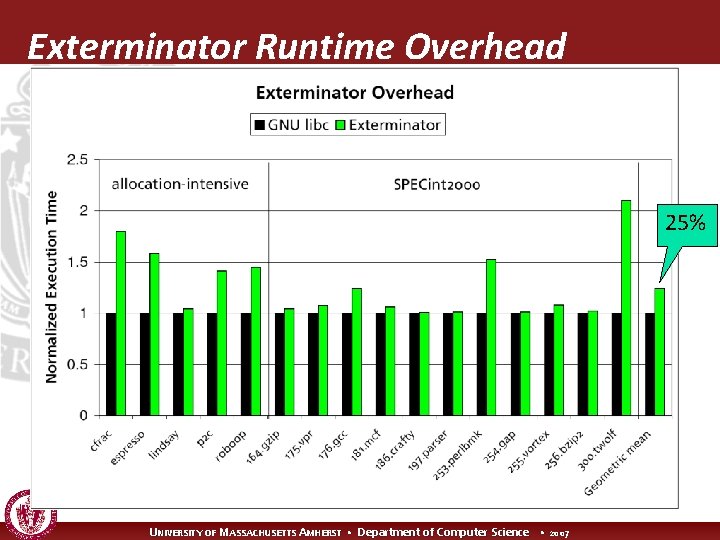
Exterminator Runtime Overhead 25% UNIVERSITY OF MASSACHUSETTS AMHERST • Department of Computer Science • 2007
Empirical Results: Real Faults n Squid heap overflow n n Crashes glibc 2. 8. 0 and BDW collector 3 iterations to fix ) 6 byte pad n Prevents overflow for all subsequent executions UNIVERSITY OF MASSACHUSETTS AMHERST • Department of Computer Science • 2007
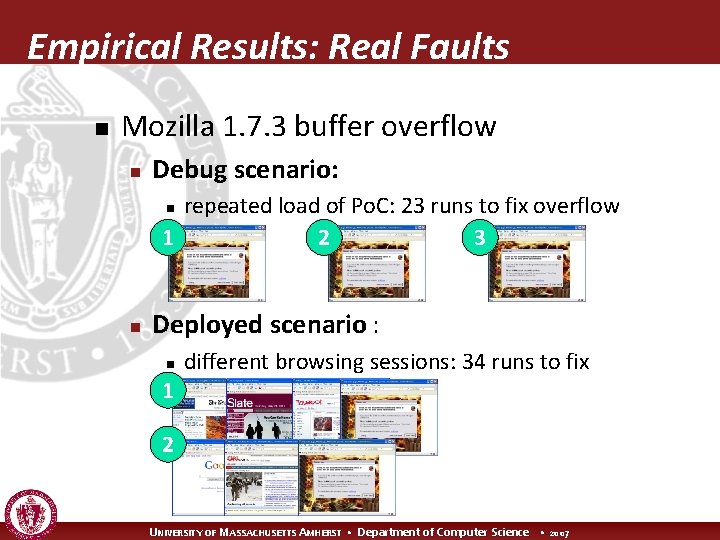
Empirical Results: Real Faults n Mozilla 1. 7. 3 buffer overflow n Debug scenario: repeated load of Po. C: 23 runs to fix overflow 1 2 3 n n Deployed scenario : n 1 different browsing sessions: 34 runs to fix 2 UNIVERSITY OF MASSACHUSETTS AMHERST • Department of Computer Science • 2007
Exterminator Conclusion n Exterminator: automatic error correction w. h. p. n n n Randomization bugs have different effects Statistical analysis combines information from multiple runs to isolate error Correcting allocator eliminates bugs at runtime http: //www. cs. umass. edu/~gnovark/ UNIVERSITY OF MASSACHUSETTS AMHERST • Department of Computer Science • 2007

UNIVERSITY OF MASSACHUSETTS AMHERST • Department of Computer Science • 2007
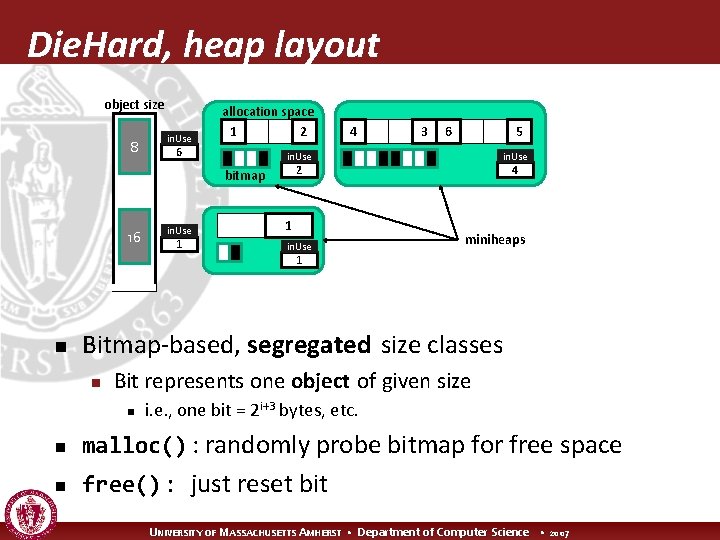
Die. Hard, heap layout object size 8 in. Use allocation space 1 2 6 in. Use 1 3 6 5 in. Use 4 2 bitmap 16 4 1 in. Use miniheaps 1 n Bitmap-based, segregated size classes n Bit represents one object of given size n i. e. , one bit = 2 i+3 bytes, etc. n malloc() : randomly probe bitmap for free space n free() : just reset bit UNIVERSITY OF MASSACHUSETTS AMHERST • Department of Computer Science • 2007
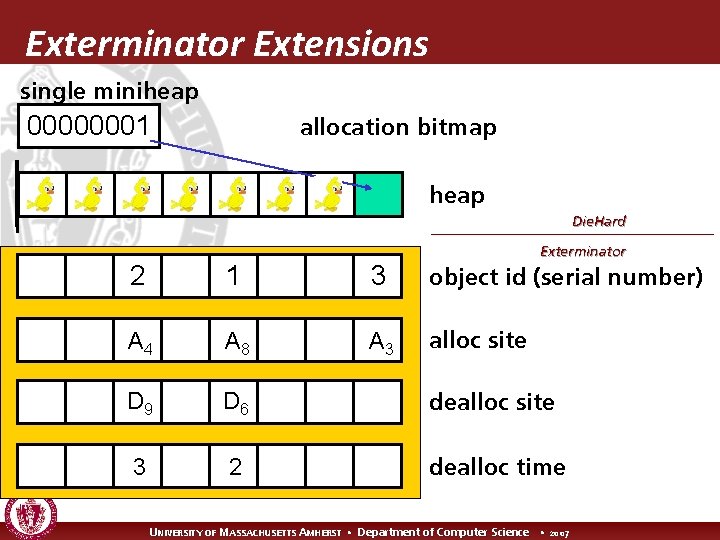
Exterminator Extensions single miniheap 00000001 allocation bitmap heap Die. Hard Exterminator 2 1 3 object id (serial number) A 4 A 8 A 3 alloc site D 9 D 6 dealloc site 3 2 dealloc time UNIVERSITY OF MASSACHUSETTS AMHERST • Department of Computer Science • 2007
- Slides: 36