EHR Action Verbs and Security Operations Tony Weida
EHR Action Verbs and Security Operations Tony Weida HL 7 May WGM May 7, 2014
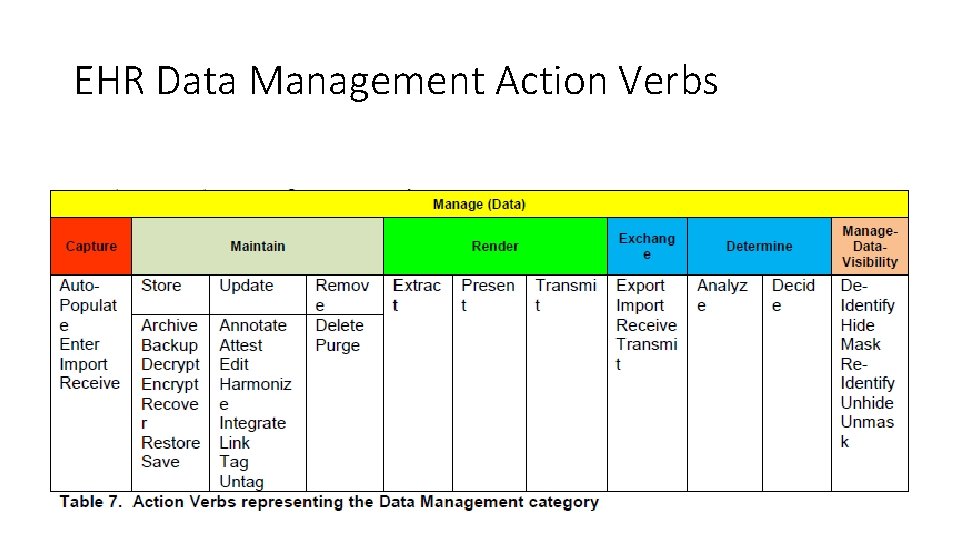
EHR Data Management Action Verbs
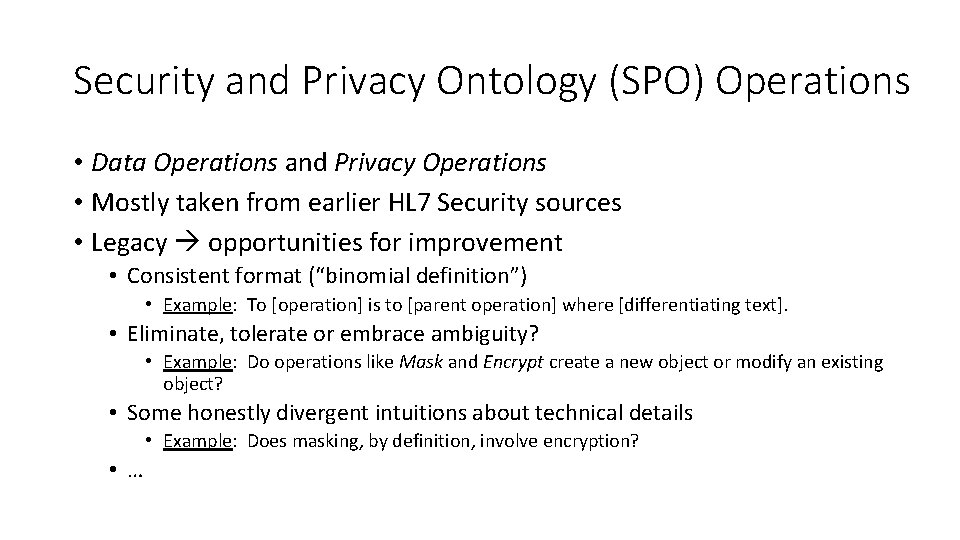
Security and Privacy Ontology (SPO) Operations • Data Operations and Privacy Operations • Mostly taken from earlier HL 7 Security sources • Legacy opportunities for improvement • Consistent format (“binomial definition”) • Example: To [operation] is to [parent operation] where [differentiating text]. • Eliminate, tolerate or embrace ambiguity? • Example: Do operations like Mask and Encrypt create a new object or modify an existing object? • Some honestly divergent intuitions about technical details • Example: Does masking, by definition, involve encryption? • …
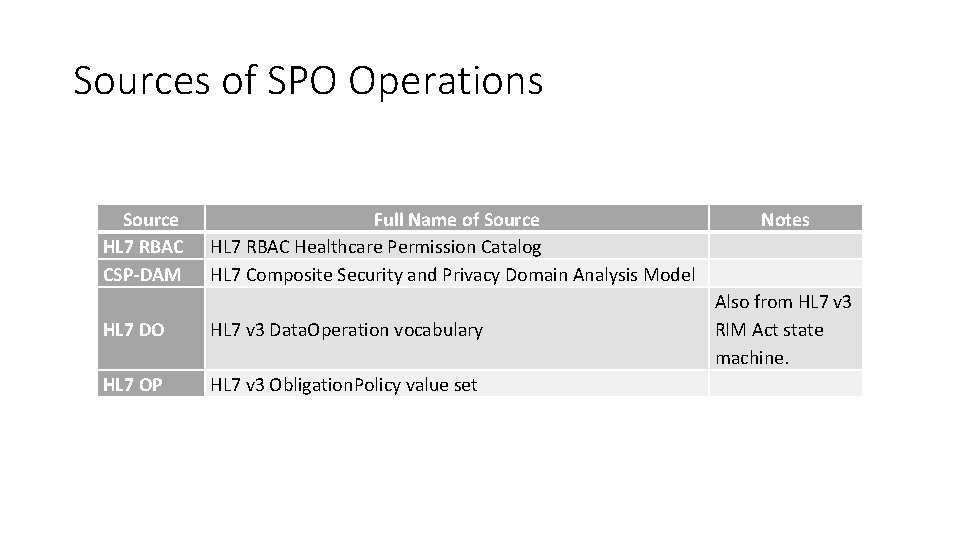
Sources of SPO Operations Source HL 7 RBAC CSP-DAM HL 7 DO HL 7 OP Full Name of Source Notes HL 7 RBAC Healthcare Permission Catalog HL 7 Composite Security and Privacy Domain Analysis Model Also from HL 7 v 3 Data. Operation vocabulary RIM Act state machine. HL 7 v 3 Obligation. Policy value set
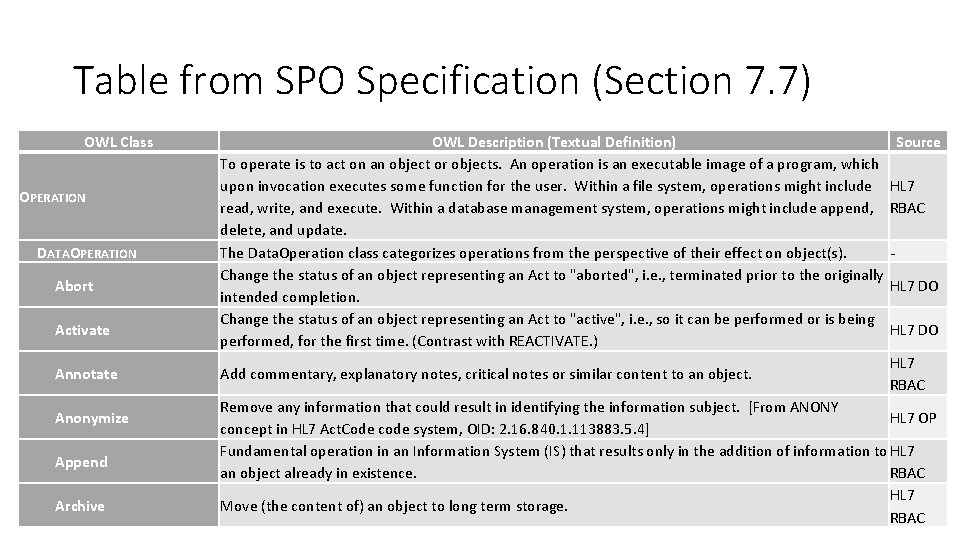
Table from SPO Specification (Section 7. 7) OWL Class OPERATION DATAOPERATION Abort Activate Annotate Anonymize Append Archive OWL Description (Textual Definition) Source To operate is to act on an object or objects. An operation is an executable image of a program, which upon invocation executes some function for the user. Within a file system, operations might include HL 7 read, write, and execute. Within a database management system, operations might include append, RBAC delete, and update. The Data. Operation class categorizes operations from the perspective of their effect on object(s). Change the status of an object representing an Act to "aborted", i. e. , terminated prior to the originally HL 7 DO intended completion. Change the status of an object representing an Act to "active", i. e. , so it can be performed or is being HL 7 DO performed, for the first time. (Contrast with REACTIVATE. ) HL 7 Add commentary, explanatory notes, critical notes or similar content to an object. RBAC Remove any information that could result in identifying the information subject. [From ANONY HL 7 OP concept in HL 7 Act. Code code system, OID: 2. 16. 840. 1. 113883. 5. 4] Fundamental operation in an Information System (IS) that results only in the addition of information to HL 7 an object already in existence. RBAC HL 7 Move (the content of) an object to long term storage. RBAC
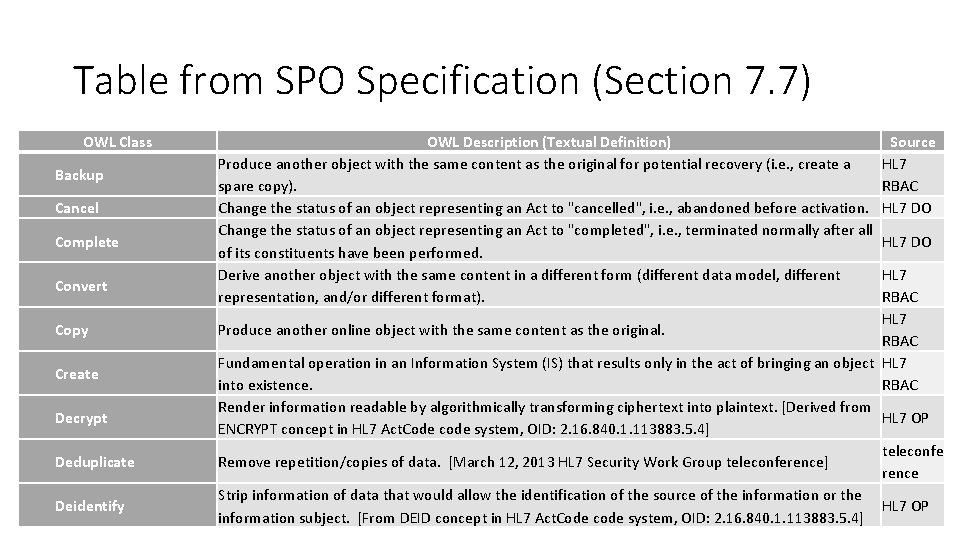
Table from SPO Specification (Section 7. 7) OWL Class Backup Cancel Complete Convert Copy Create Decrypt Deduplicate Deidentify OWL Description (Textual Definition) Produce another object with the same content as the original for potential recovery (i. e. , create a spare copy). Change the status of an object representing an Act to "cancelled", i. e. , abandoned before activation. Change the status of an object representing an Act to "completed", i. e. , terminated normally after all of its constituents have been performed. Derive another object with the same content in a different form (different data model, different representation, and/or different format). Source HL 7 RBAC HL 7 DO HL 7 RBAC HL 7 Produce another online object with the same content as the original. RBAC Fundamental operation in an Information System (IS) that results only in the act of bringing an object HL 7 into existence. RBAC Render information readable by algorithmically transforming ciphertext into plaintext. [Derived from HL 7 OP ENCRYPT concept in HL 7 Act. Code code system, OID: 2. 16. 840. 1. 113883. 5. 4] teleconfe Remove repetition/copies of data. [March 12, 2013 HL 7 Security Work Group teleconference] rence Strip information of data that would allow the identification of the source of the information or the HL 7 OP information subject. [From DEID concept in HL 7 Act. Code code system, OID: 2. 16. 840. 1. 113883. 5. 4]
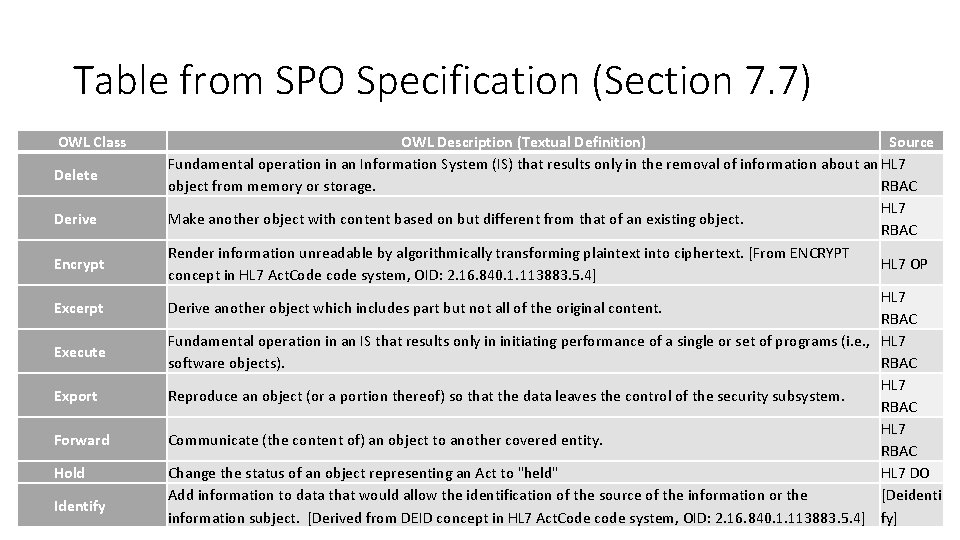
Table from SPO Specification (Section 7. 7) OWL Class Delete Derive Encrypt Excerpt Execute Export Forward Hold Identify OWL Description (Textual Definition) Source Fundamental operation in an Information System (IS) that results only in the removal of information about an HL 7 object from memory or storage. RBAC HL 7 Make another object with content based on but different from that of an existing object. RBAC Render information unreadable by algorithmically transforming plaintext into ciphertext. [From ENCRYPT HL 7 OP concept in HL 7 Act. Code code system, OID: 2. 16. 840. 1. 113883. 5. 4] HL 7 Derive another object which includes part but not all of the original content. RBAC Fundamental operation in an IS that results only in initiating performance of a single or set of programs (i. e. , HL 7 software objects). RBAC HL 7 Reproduce an object (or a portion thereof) so that the data leaves the control of the security subsystem. RBAC HL 7 Communicate (the content of) an object to another covered entity. RBAC Change the status of an object representing an Act to "held" HL 7 DO Add information to data that would allow the identification of the source of the information or the [Deidenti information subject. [Derived from DEID concept in HL 7 Act. Code code system, OID: 2. 16. 840. 1. 113883. 5. 4] fy]
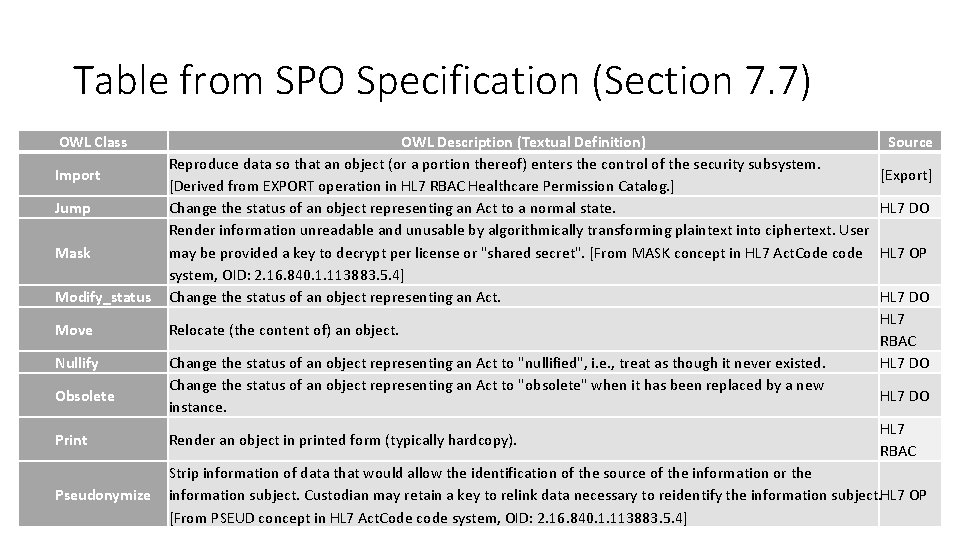
Table from SPO Specification (Section 7. 7) OWL Class Modify_status OWL Description (Textual Definition) Reproduce data so that an object (or a portion thereof) enters the control of the security subsystem. [Derived from EXPORT operation in HL 7 RBAC Healthcare Permission Catalog. ] Change the status of an object representing an Act to a normal state. Render information unreadable and unusable by algorithmically transforming plaintext into ciphertext. User may be provided a key to decrypt per license or "shared secret". [From MASK concept in HL 7 Act. Code code system, OID: 2. 16. 840. 1. 113883. 5. 4] Change the status of an object representing an Act. Move Relocate (the content of) an object. Nullify Change the status of an object representing an Act to "nullified", i. e. , treat as though it never existed. Change the status of an object representing an Act to "obsolete" when it has been replaced by a new instance. Import Jump Mask Obsolete Source [Export] HL 7 DO HL 7 OP HL 7 DO HL 7 RBAC Print Render an object in printed form (typically hardcopy). Pseudonymize Strip information of data that would allow the identification of the source of the information or the information subject. Custodian may retain a key to relink data necessary to reidentify the information subject. HL 7 OP [From PSEUD concept in HL 7 Act. Code code system, OID: 2. 16. 840. 1. 113883. 5. 4]
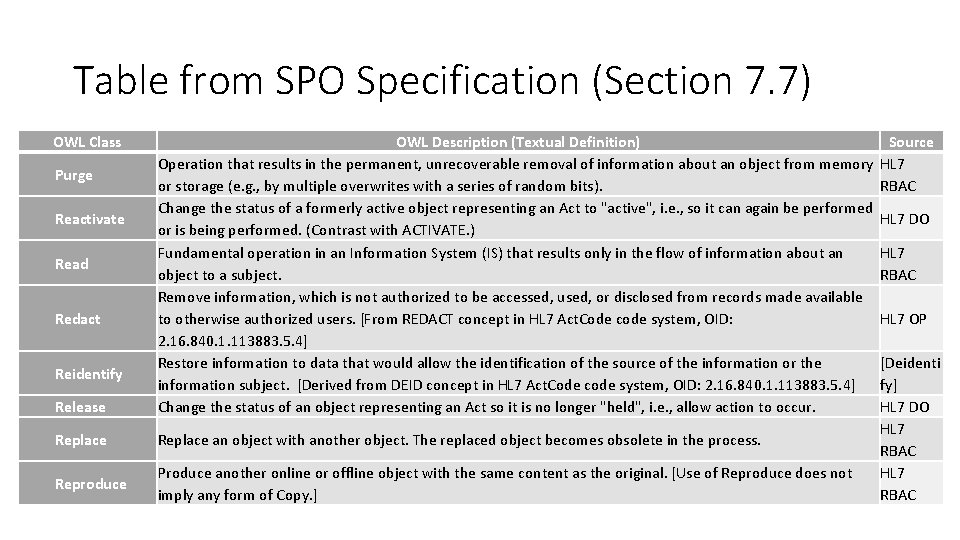
Table from SPO Specification (Section 7. 7) OWL Class Purge Reactivate Read Redact Reidentify Release Replace Reproduce OWL Description (Textual Definition) Source Operation that results in the permanent, unrecoverable removal of information about an object from memory HL 7 or storage (e. g. , by multiple overwrites with a series of random bits). RBAC Change the status of a formerly active object representing an Act to "active", i. e. , so it can again be performed HL 7 DO or is being performed. (Contrast with ACTIVATE. ) Fundamental operation in an Information System (IS) that results only in the flow of information about an HL 7 object to a subject. RBAC Remove information, which is not authorized to be accessed, used, or disclosed from records made available to otherwise authorized users. [From REDACT concept in HL 7 Act. Code code system, OID: HL 7 OP 2. 16. 840. 1. 113883. 5. 4] Restore information to data that would allow the identification of the source of the information or the [Deidenti information subject. [Derived from DEID concept in HL 7 Act. Code code system, OID: 2. 16. 840. 1. 113883. 5. 4] fy] Change the status of an object representing an Act so it is no longer "held", i. e. , allow action to occur. HL 7 DO HL 7 Replace an object with another object. The replaced object becomes obsolete in the process. RBAC Produce another online or offline object with the same content as the original. [Use of Reproduce does not HL 7 imply any form of Copy. ] RBAC
Table from SPO Specification (Section 7. 7) OWL Class Restore Resume Sign Suspend Transfer Translate Update Verify OWL Description (Textual Definition) Produce another object with the same content as one previously backed up (i. e. , recreates a readily usable copy). Change the status of a suspended object representing an Act to "active", i. e. , so it can be performed or is being performed. Affix authentication information (i. e. An electronic signature) to an object so that its origin and integrity can be verified. Change the status of an object representing an Act to "suspended", i. e. , so it is temporarily not in service. Source HL 7 RBAC HL 7 DO HL 7 RBAC HL 7 Derive another object in a different natural language (e. g. , from English to Spanish). RBAC Fundamental operation in an Information System (IS) that results only in the revision or alteration of HL 7 an object. RBAC Determine whether an object has been altered and whether its signature was affixed by the claimed HL 7 signer. RBAC Communicate (the content of) an object to an external clearinghouse without examining the content.
Privacy Operations • Collect • Access • Use • Disclose
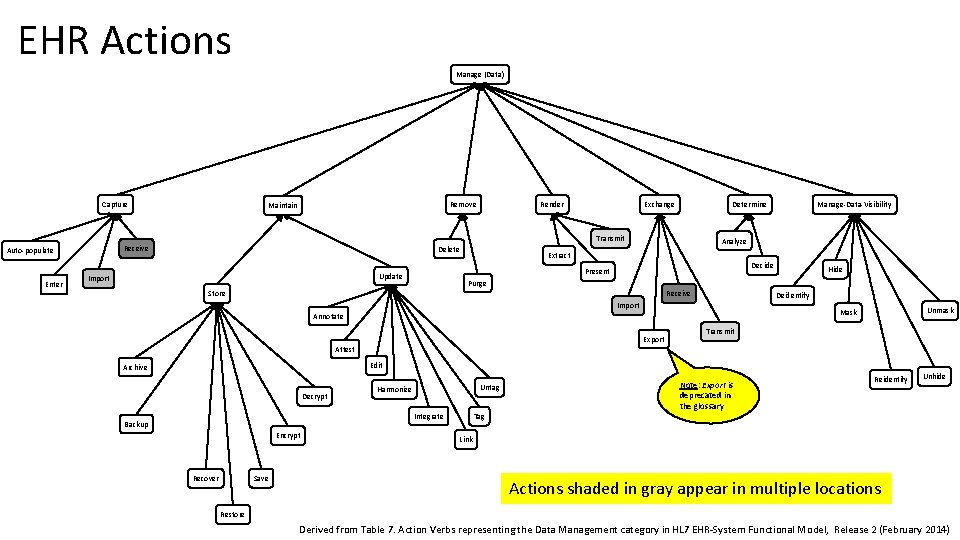
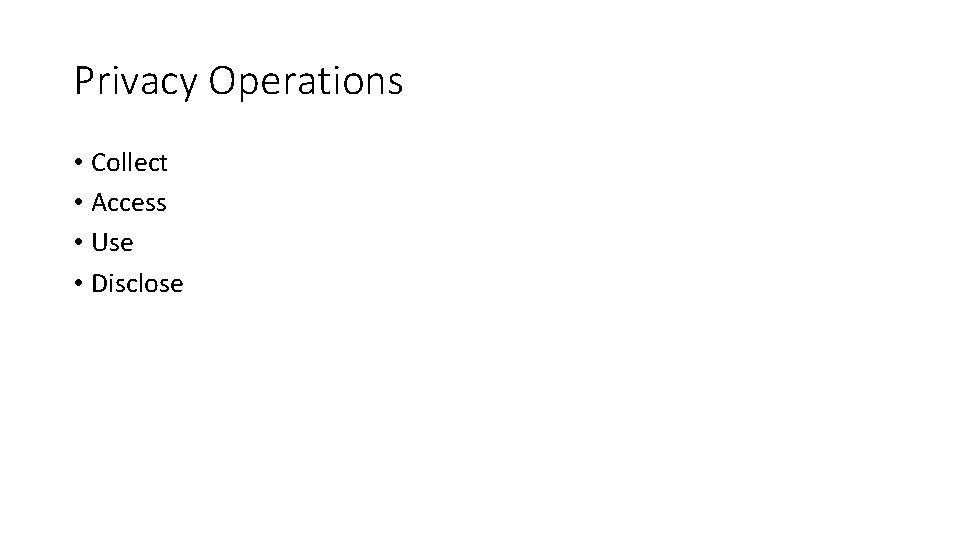
EHR Actions Manage (Data) Capture Remove Maintain Render Exchange Determine Transmit Receive Auto-populate Enter Delete Analyze Extract Decide Present Update Import Manage-Data-Visibility Hide Purge Store Receive Deidentify Import Unmask Mask Annotate Export Transmit Attest Edit Archive Decrypt Untag Harmonize Integrate Backup Encrypt Save Recover Tag Note: Export is deprecated in the glossary Reidentify Unhide Link Actions shaded in gray appear in multiple locations Restore Derived from Table 7. Action Verbs representing the Data Management category in HL 7 EHR-System Functional Model, Release 2 (February 2014)
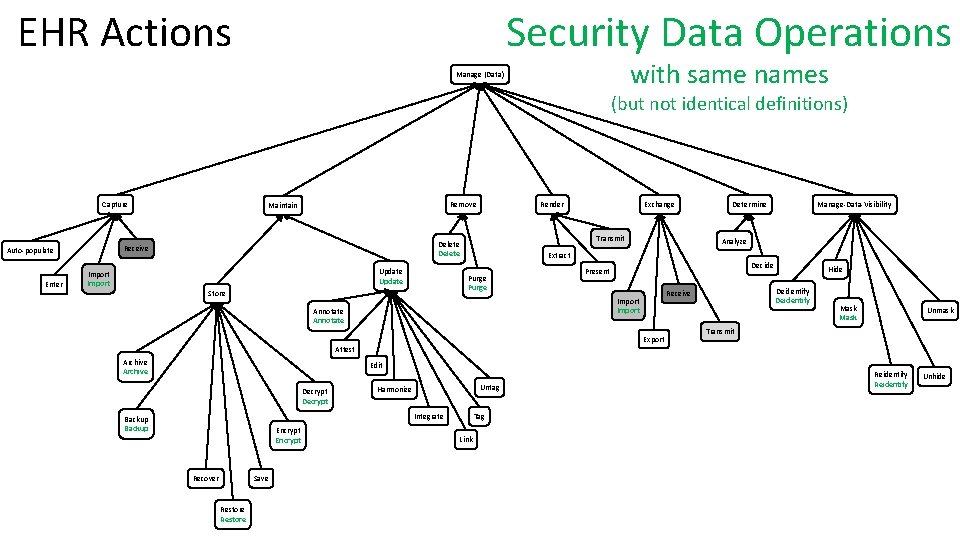
Security Data Operations EHR Actions with same names Manage (Data) (but not identical definitions) Capture Render Update Import Determine Manage-Data-Visibility Analyze Extract Purge Store Exchange Transmit Delete Receive Auto-populate Enter Remove Maintain Decide Present Annotate Deidentify Receive Import Export Hide Mask Unmask Transmit Attest Archive Edit Decrypt Untag Harmonize Integrate Backup Encrypt Save Recover Restore Tag Link Reidentify Unhide
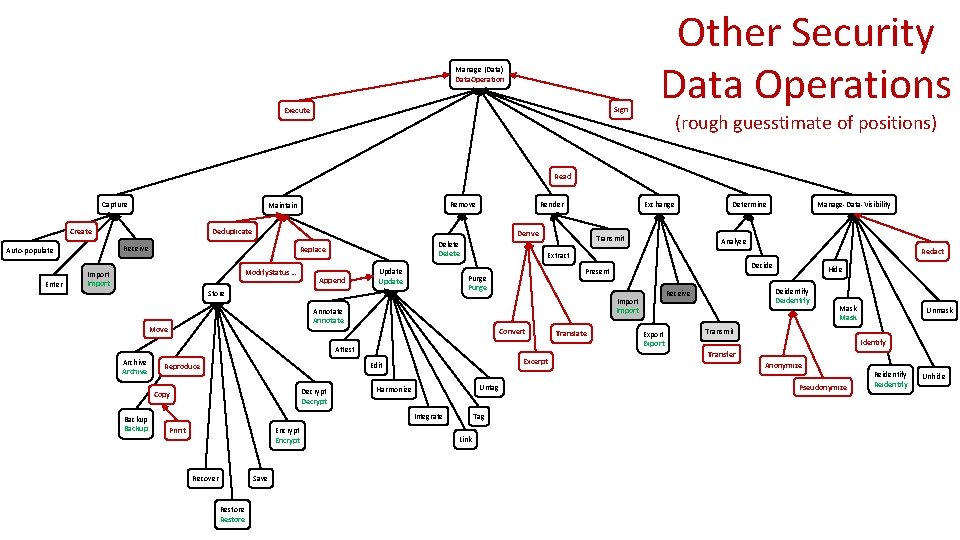
Manage (Data) Data. Operation Sign Execute Other Security Data Operations (rough guesstimate of positions) Read Capture Create Enter Render Deduplicate Delete Replace Modify. Status … Import Append Update Transmit Backup Excerpt Edit Decrypt Untag Harmonize Integrate Print Encrypt Save Recover Restore Decide Tag Link Translate Export Hide Deidentify Receive Import Attest Copy Analyze Present Convert Reproduce Manage-Data-Visibility Redact Annotate Move Determine Extract Purge Store Archive Exchange Derive Receive Auto-populate Remove Maintain Mask Unmask Transmit Identify Transfer Anonymize Pseudonymize Reidentify Unhide
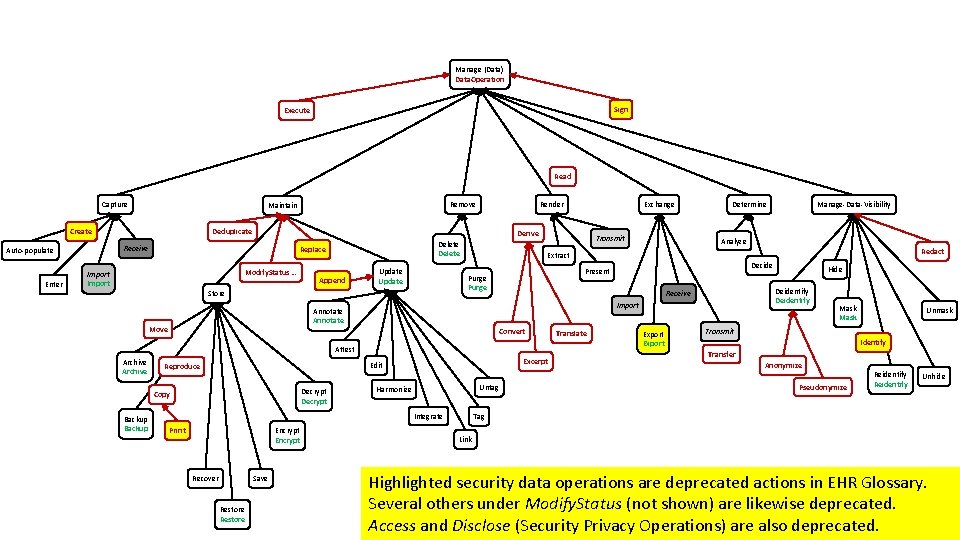
Manage (Data) Data. Operation Sign Execute Read Capture Create Enter Render Deduplicate Delete Replace Modify. Status … Import Append Update Transmit Backup Excerpt Untag Harmonize Integrate Print Encrypt Save Recover Restore Translate Export Hide Deidentify Import Edit Decrypt Decide Receive Attest Copy Analyze Present Convert Reproduce Manage-Data-Visibility Redact Annotate Move Determine Extract Purge Store Archive Exchange Derive Receive Auto-populate Remove Maintain Mask Unmask Transmit Identify Transfer Anonymize Pseudonymize Reidentify Unhide Tag Link Highlighted security data operations are deprecated actions in EHR Glossary. Several others under Modify. Status (not shown) are likewise deprecated. Access and Disclose (Security Privacy Operations) are also deprecated.
Comparison of EHR / Security Definitions • Good news: those with the same name have reasonably compatible definitions • So we might start with 14 cases involving active EHR actions (additional cases involve deprecated EHR actions) …
Steps to Consensus • Agree on • Inclusion criteria • Text definitions • Structured description (consistent with text definitions) • Hierarchy • Further logical description (eventually) • Consider internal consistency vs. consistency with disparate sources • Defined work process
Annotate EHR Security • To UPDATE data by attaching comments • Add commentary, explanatory notes, or notes to the data without editing the critical notes or similar content to an data. For example, an Attending physician object. may ANNOTATE the information entered by the Resident physician before signing the report.
Archive EHR • To STORE data by moving the data to long -term storage media and deleting or purging data on the original online storage, according to scope of practice, organizational policy, and/or jurisdictional law. For example, the system at the Oak Street Hospital automatically ARCHIVES patient-related data that is older than eight years by encrypting and compressing it, moving it to long-term storage, purging it, identifying the data by month and year, and creating a pointer to the archived data. Another example is that a system may automatically ARCHIVE outpatient clinic schedules that are being replaced. Security • Move (the content of) an object to long term storage.
Backup EHR Security • To STORE data by placing a copy of the • Produce another object with the same data onto an electronically-accessible content as the original for potential device for preservation in case the recovery (i. e. , create a spare copy). original is lost, corrupted, or destroyed. For example, a system may BACK UP the incremental changes made to a patient’s record by storing it locally on a daily basis. Another example is that an administrator may BACK UP a complete copy of certain data by storing it at an offsite facility.
Decrypt EHR Security • To STORE data by converting encrypted data back into its original form, so it can be understood. For example, the system may DECRYPT clinical data received from an authenticated external laboratory system. • Render information readable by algorithmically transforming ciphertext into plaintext. [Derived from ENCRYPT concept in HL 7 Act. Code code system, OID: 2. 16. 840. 1. 113883. 5. 4]
Deidentify EHR Security • To MANAGE-DATA-VISIBILITY by removing identifiers from data in such a way that the risk of identifying an individual is very small under the circumstances, as specified by scope of practice, organizational policy, and/or jurisdictional law. For example, a system may DE-IDENTIFY data for a researcher who wants to perform an analysis of drug effectiveness on diabetic patients. Another example is where a hospital may DE-IDENTIFY data for a set of patients to transmit to a university professor looking for illustrative cases for educational work. • Strip information of data that would allow the identification of the source of the information or the information subject. [From DEID concept in HL 7 Act. Code code system, OID: 2. 16. 840. 1. 113883. 5. 4]
Delete EHR Security • To REMOVE data by making it inaccessible to the application. For example, a user may DELETE an existing patient-appointment at the request of the patient. Note: In the case where the data becomes invalid but needs to remain in the system, the word “TAG” is preferred over the word “DELETE” or the word “Nullify”. This type of action is considered a data “Tagging” process and not a data deletion process. For example, a health information management professional may desire to TAG a certain clinical term as obsolete, but the term needs to remain in the system for backward compatibility purposes. • Fundamental operation in an Information System (IS) that results only in the removal of information about an object from memory or storage.
Encrypt EHR Security • To STORE data by transforming the data into a form that is difficult to understand by unauthorized people or systems. For example, the system may ENCRYPT sensitive information such as the patient’s financial information. • Render information unreadable by algorithmically transforming plaintext into ciphertext. [From ENCRYPT concept in HL 7 Act. Code code system, OID: 2. 16. 840. 1. 113883. 5. 4]
Export EHR Security • Use RENDER instead. • Reproduce an object (or a portion thereof) so that the data leaves the control of the security subsystem.
Import EHR Security • To CAPTURE data into a local system by proactively accessing data from an external source and then downloading and integrating the data into the local system. For example, the system may IMPORT the latest drug trial data every Friday evening. Another example is that the user may IMPORT various sets of best practices related to juvenile diabetes. • Reproduce data so that an object (or a portion thereof) enters the control of the security subsystem.
Mask EHR Security • To MANAGE-DATA-VISIBILITY by obscuring (masking) specific data elements in order that this information is not available except to authorized users; viewers of the patient record can see that the data exists but cannot see actual contents. For example, the administrator may MASK the pregnancy status of all patients who are below the age of eighteen except for the obstetric unit staff. Note: the verb “unmask” is an acceptable verb to reverse the action of masking. • Render information unreadable and unusable by algorithmically transforming plaintext into ciphertext. User may be provided a key to decrypt per license or "shared secret". [From MASK concept in HL 7 Act. Code code system, OID: 2. 16. 840. 1. 113883. 5. 4]
Purge EHR Security • To REMOVE data by making it unrecoverable at the storage and/or media-level. For example, the system may PURGE the patient record for John Smith according to a rule that targets all records that are older than seven years. (Note: Destroy and Purge are synonyms; PURGE is the preferred term. ) • Operation that results in the permanent, unrecoverable removal of information about an object from memory or storage (e. g. , by multiple overwrites with a series of random bits).
Reidentify EHR Security • To MANAGE-DATA-VISIBILITY by combining data in such a way that the patient’s identity is re-established according to scope of practice, organizational policy, and/or jurisdictional law. For example, the system may RE-IDENTIFY de-identified data by providing a key that allows authorized users to re-establish the link between a given patient and that patient’s de-identified data. • Restore information to data that would allow the identification of the source of the information or the information subject
Restore EHR Security • To STORE data to the production system by using previously archived data. For example, the system may RESTORE patient-encounter data for a returning patient whose data had been archived due to inactivity. Another example is that the system may RESTORE, for evidentiary support, patient data that had been archived after the patient expired. (See ARCHIVE. ) • Produce another object with the same content as one previously backed up (i. e. , recreates a readily usable copy).
Update EHR Security • To MAINTAIN data by annotating, editing, harmonizing, integrating, linking and tagging the data. For example, a clinician may UPDATE a patient’s medication dosage. Another example is that the system may UPDATE a patient’s record. • Fundamental operation in an Information System (IS) that results only in the revision or alteration of an object.
Discussion
- Slides: 32