Data Hiding system Cover image Stego image 10101
- Slides: 33
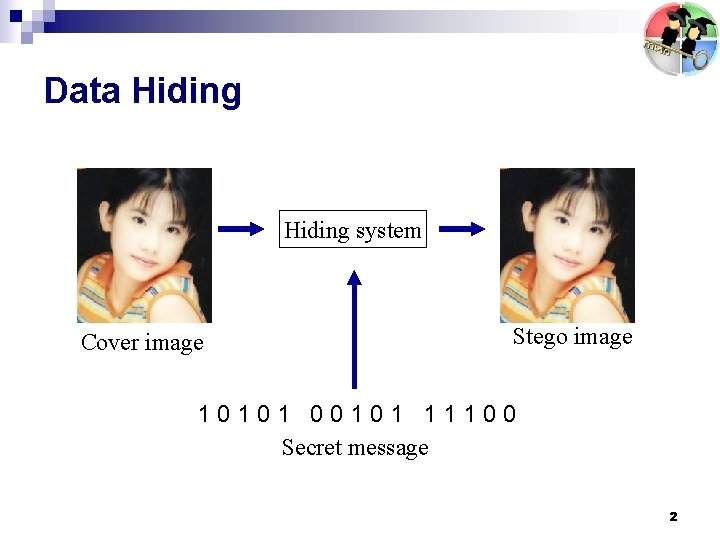
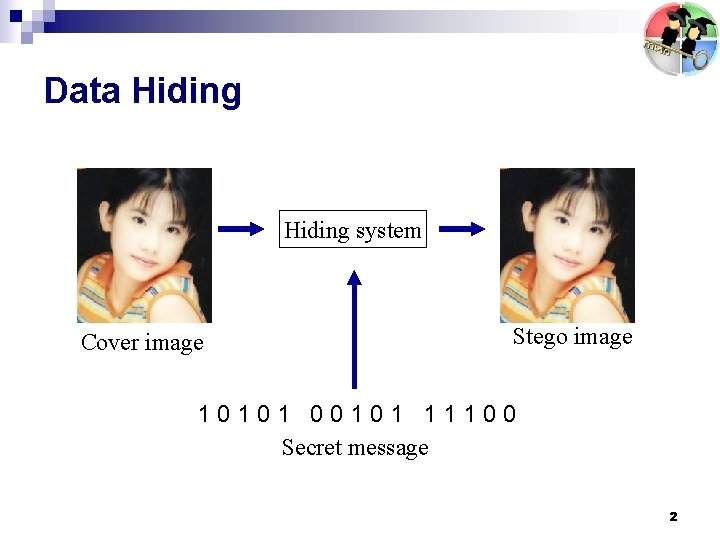
Data Hiding system Cover image Stego image 10101 00101 11100 Secret message 2
Cover Carriers Image n Video n Sound n Text n 3
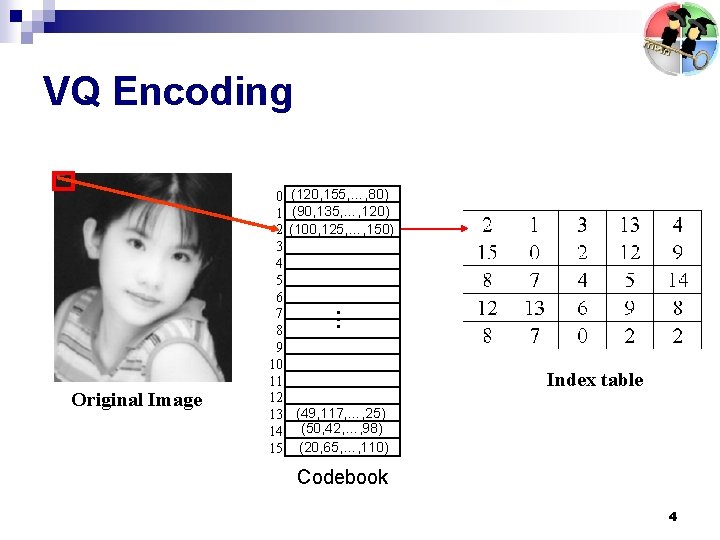
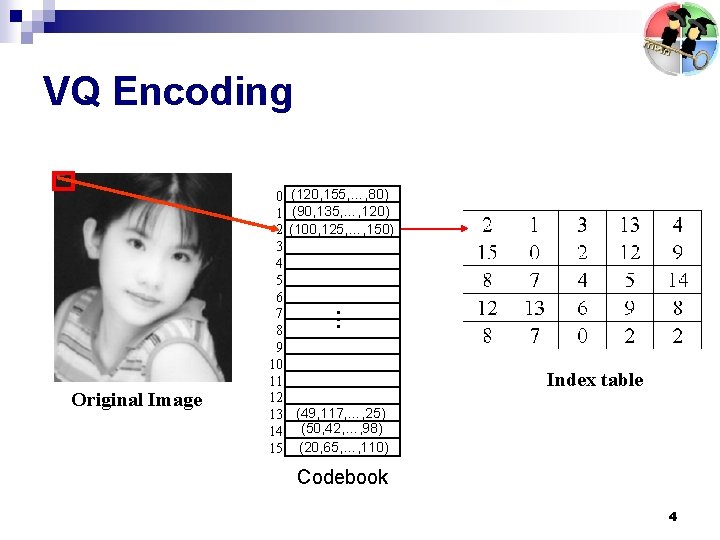
VQ Encoding (120, 155, …, 80) (90, 135, …, 120) (100, 125, …, 150) … Original Image 0 1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 Index table (49, 117, …, 25) (50, 42, …, 98) (20, 65, …, 110) Codebook 4
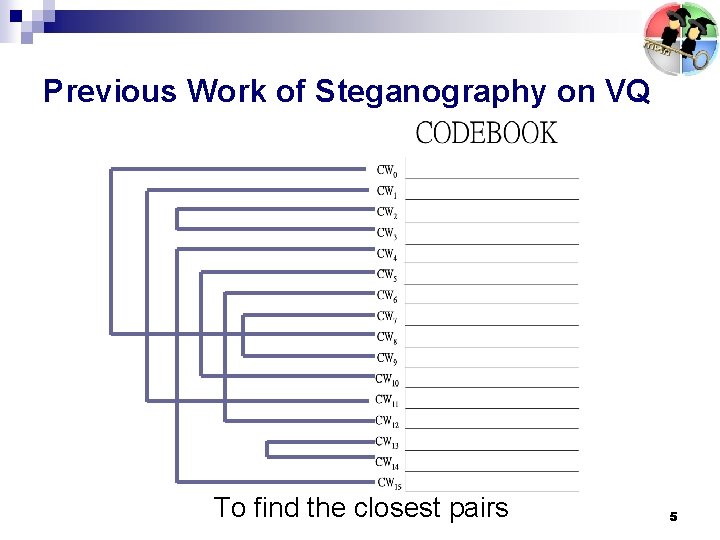
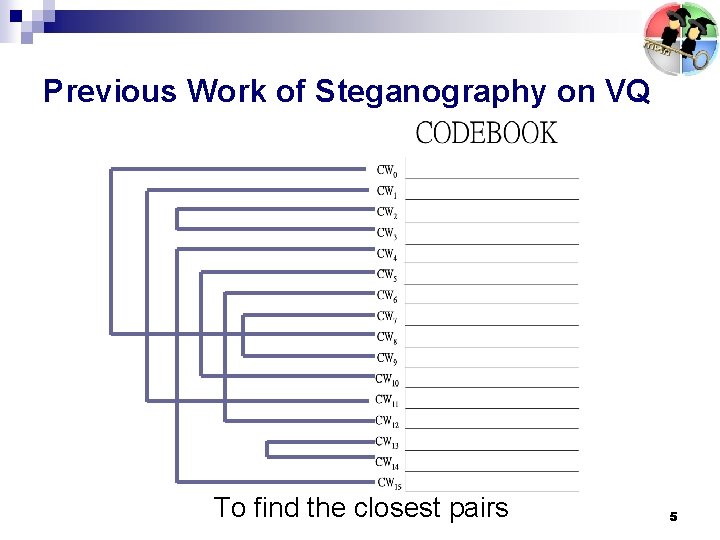
Previous Work of Steganography on VQ To find the closest pairs 5
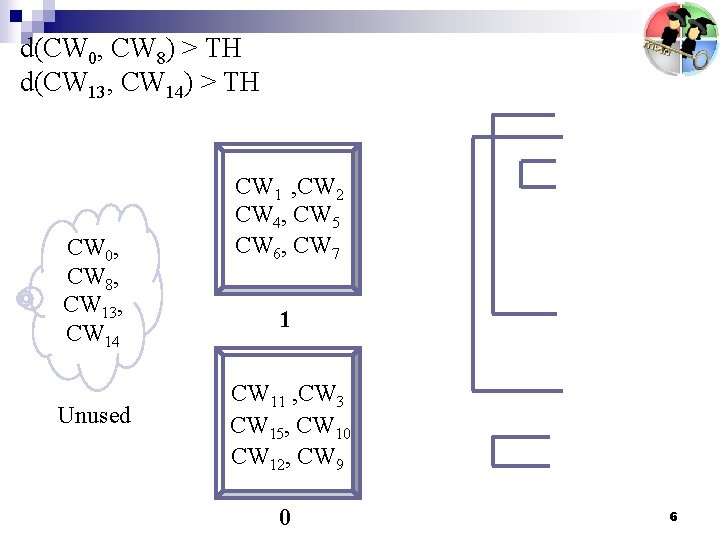
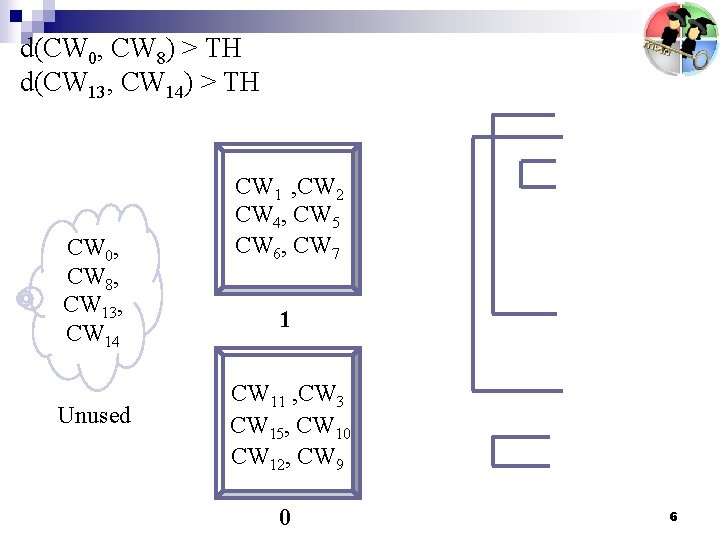
d(CW 0, CW 8) > TH d(CW 13, CW 14) > TH CW 0, CW 8, CW 13, CW 14 Unused CW 1 , CW 2 CW 4, CW 5 CW 6, CW 7 1 CW 11 , CW 3 CW 15, CW 10 CW 12, CW 9 0 6
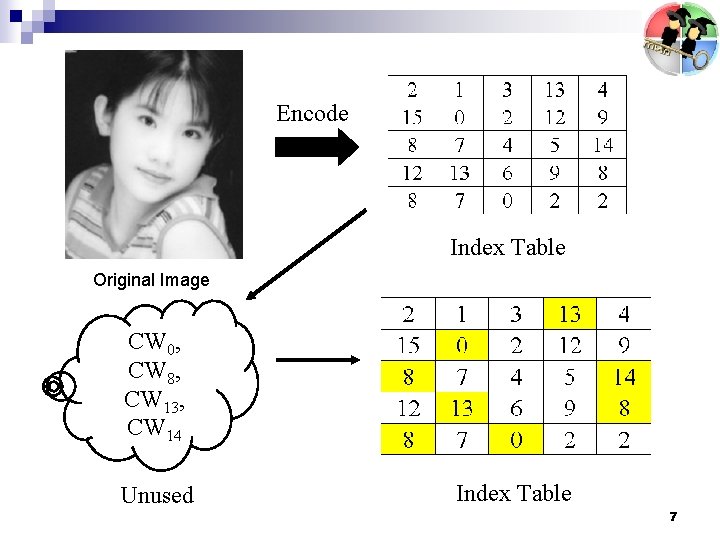
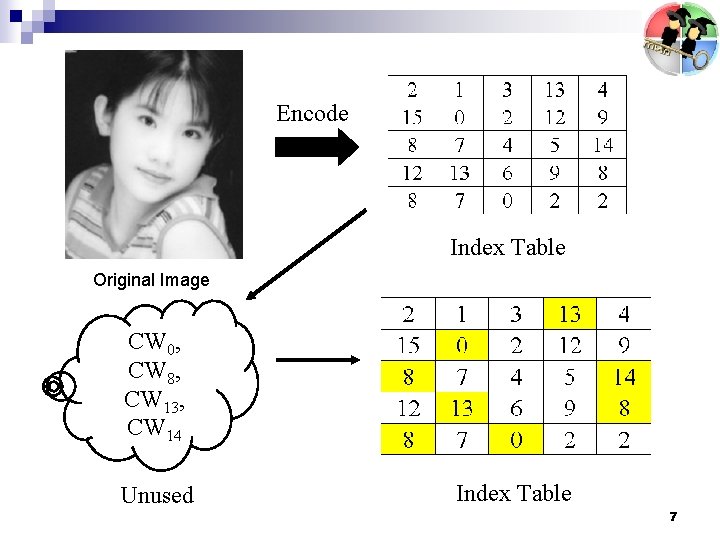
Encode Index Table Original Image CW 0, CW 8, CW 13, CW 14 Unused Index Table 7
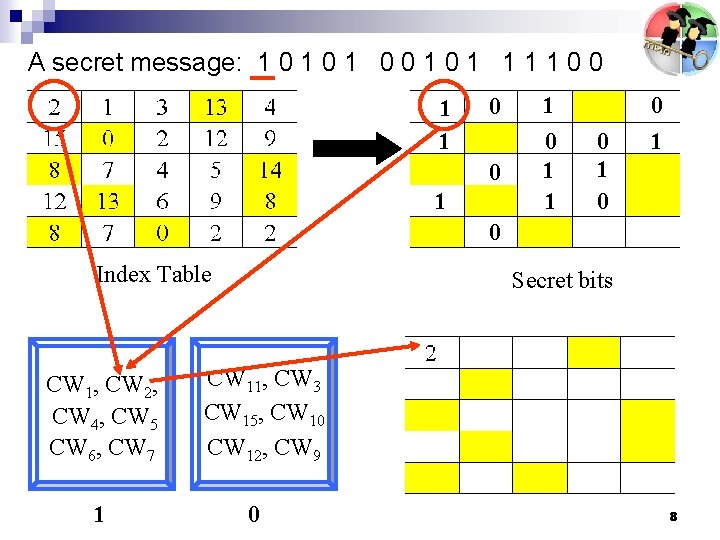
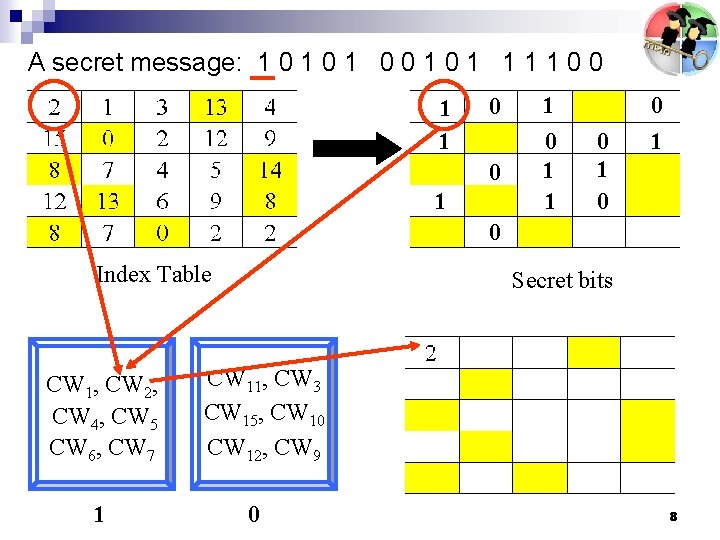
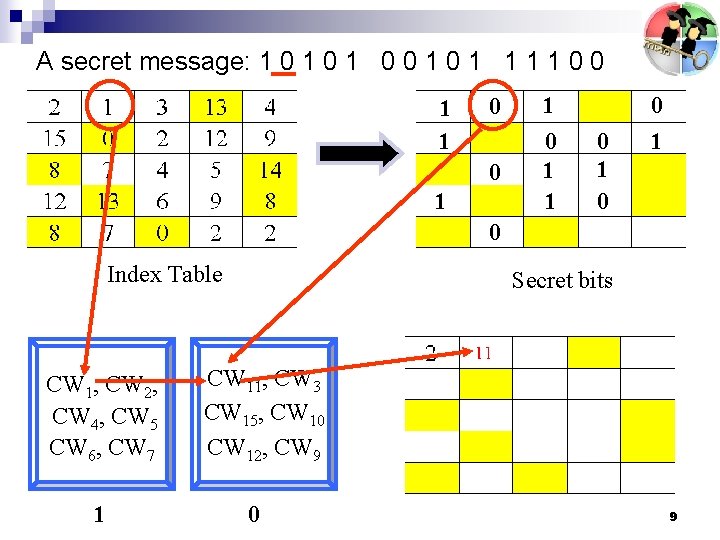
A secret message: 1 0 1 0 0 1 1 1 1 0 0 1 1 0 1 0 Index Table CW 1, CW 2, CW 4, CW 5 CW 6, CW 7 1 Secret bits CW 11, CW 3 CW 15, CW 10 CW 12, CW 9 0 8
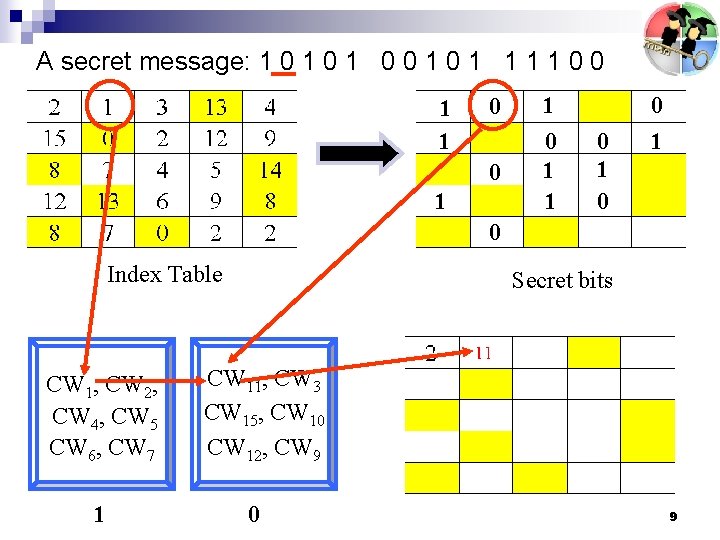
A secret message: 1 0 1 0 0 1 1 1 1 0 0 1 1 0 1 0 Index Table CW 1, CW 2, CW 4, CW 5 CW 6, CW 7 1 Secret bits CW 11, CW 3 CW 15, CW 10 CW 12, CW 9 0 9
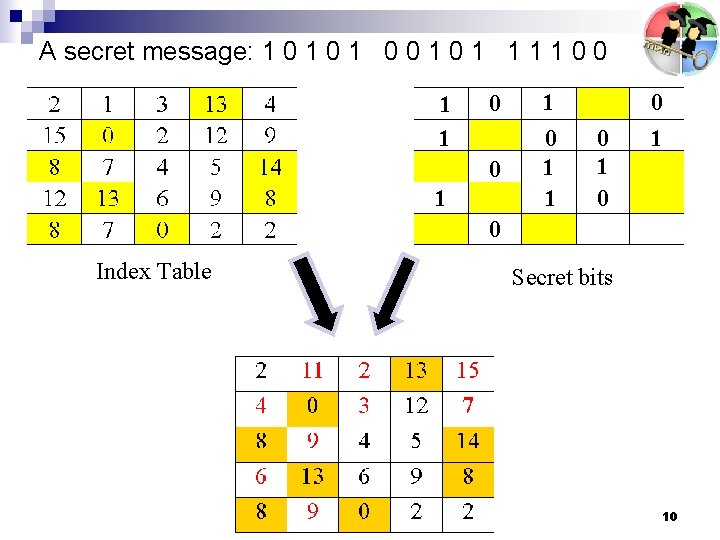
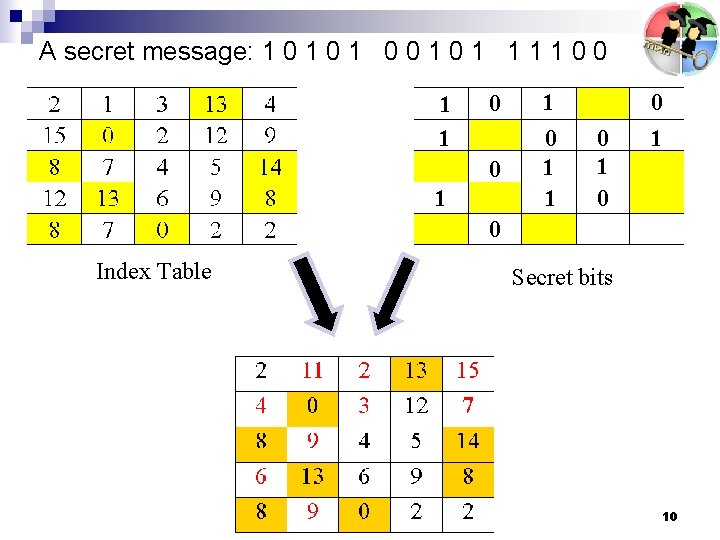
A secret message: 1 0 1 0 0 1 1 1 1 0 0 1 1 0 1 0 Index Table Secret bits 10
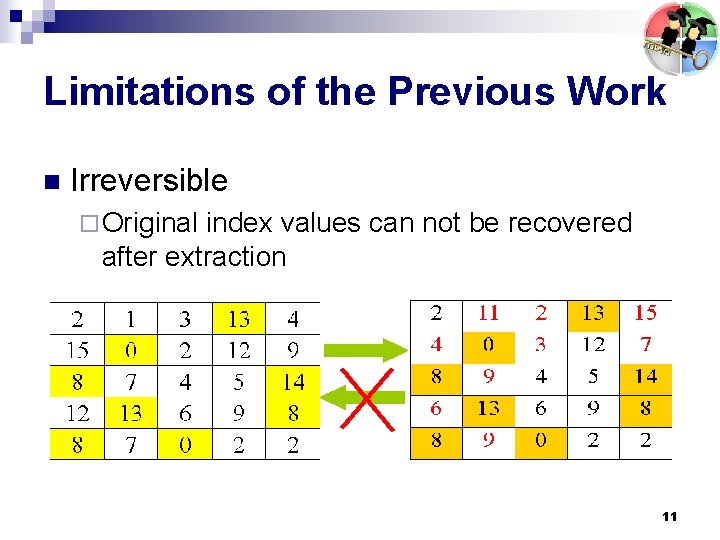
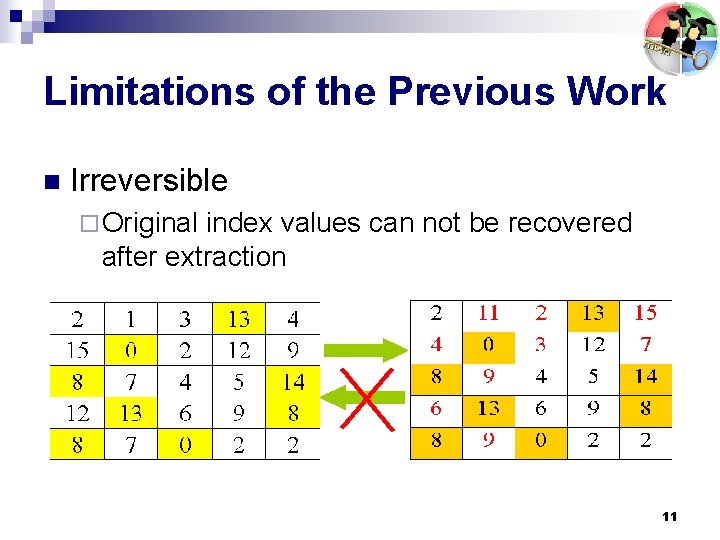
Limitations of the Previous Work n Irreversible ¨ Original index values can not be recovered after extraction 11
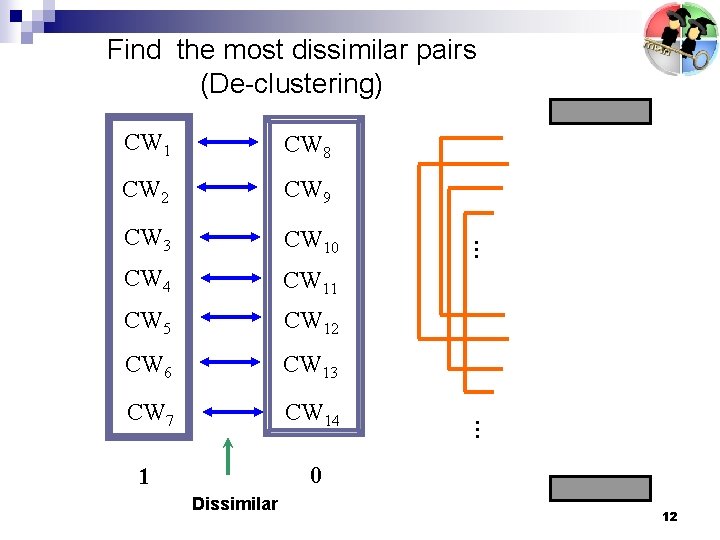
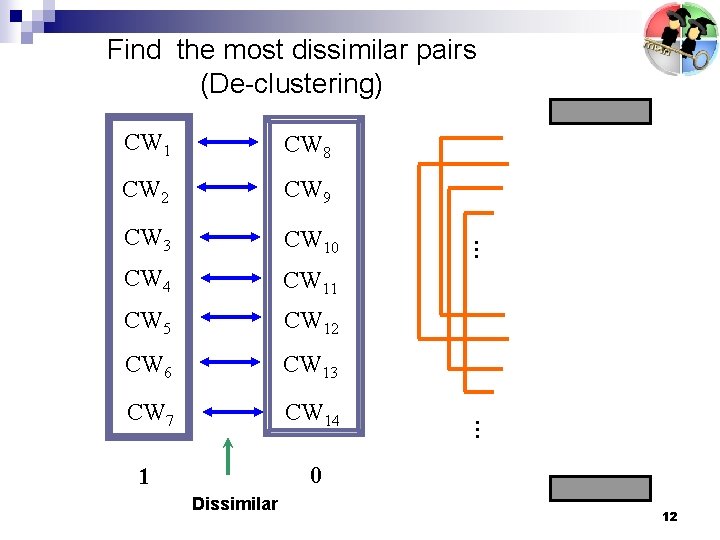
Find the most dissimilar pairs (De-clustering) CW 2 CW 9 CW 3 CW 10 CW 4 CW 11 CW 5 CW 12 CW 6 CW 13 CW 7 CW 14 1 0 Dissimilar … CW 8 … CW 1 12
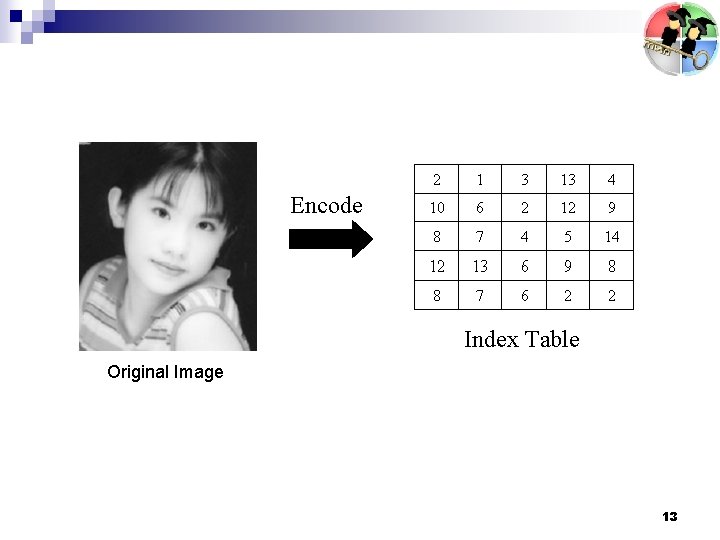
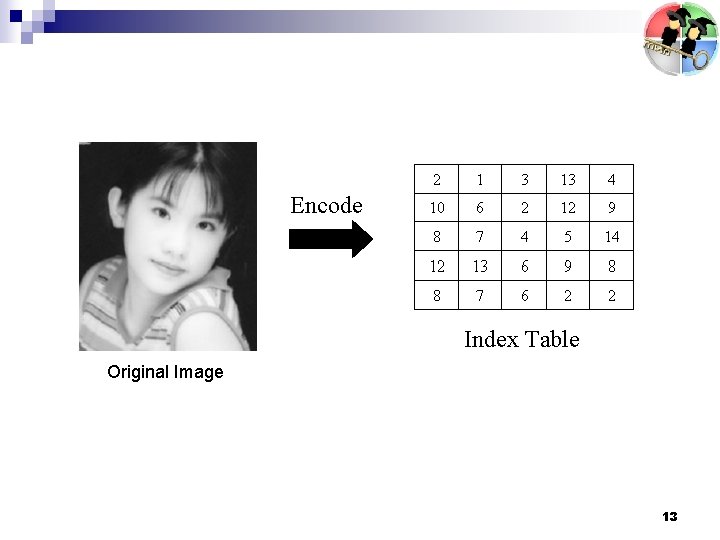
Encode Index Table Original Image 13
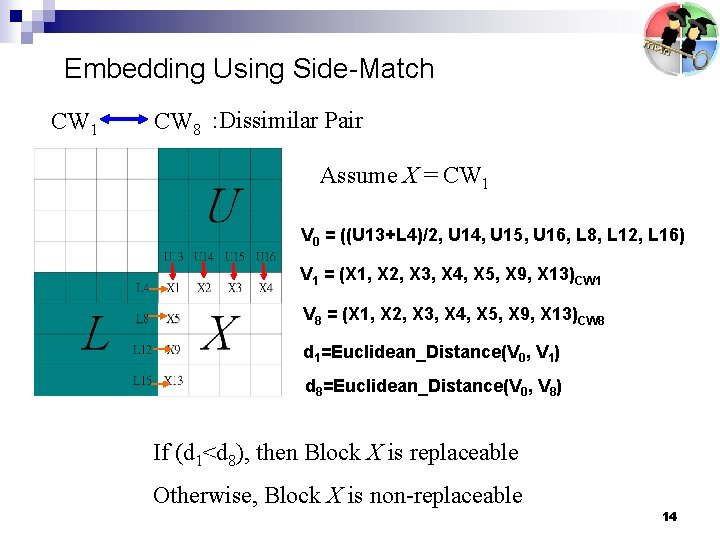
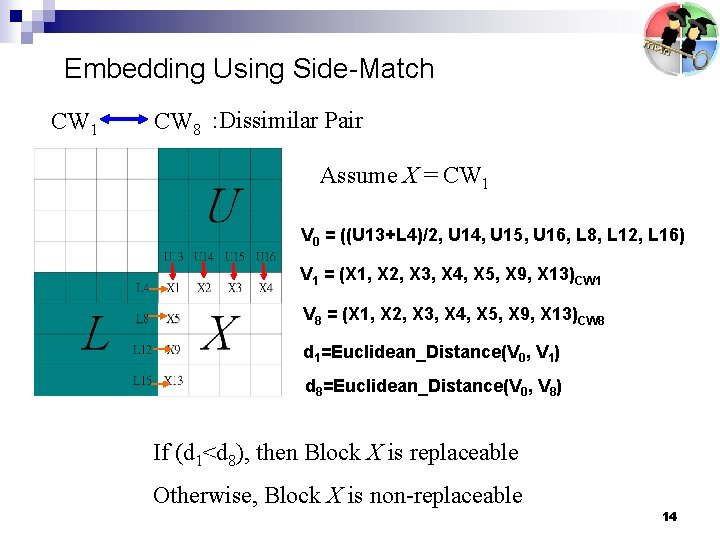
Embedding Using Side-Match CW 1 CW 8 : Dissimilar Pair Assume X = CW 1 V 0 = ((U 13+L 4)/2, U 14, U 15, U 16, L 8, L 12, L 16) V 1 = (X 1, X 2, X 3, X 4, X 5, X 9, X 13)CW 1 V 8 = (X 1, X 2, X 3, X 4, X 5, X 9, X 13)CW 8 d 1=Euclidean_Distance(V 0, V 1) d 8=Euclidean_Distance(V 0, V 8) If (d 1<d 8), then Block X is replaceable Otherwise, Block X is non-replaceable 14
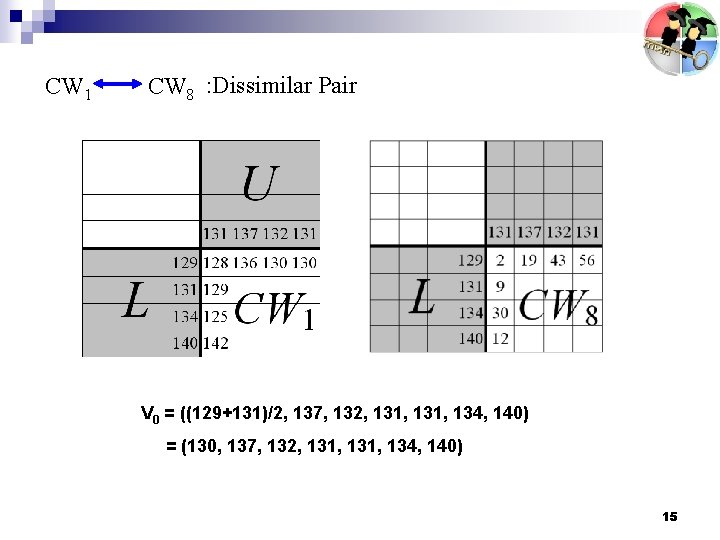
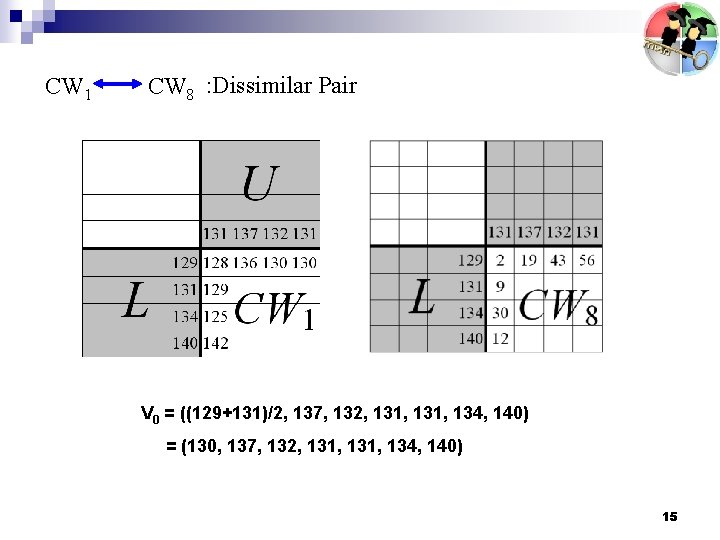
CW 1 CW 8 : Dissimilar Pair V 0 = ((129+131)/2, 137, 132, 131, 134, 140) = (130, 137, 132, 131, 134, 140) 15
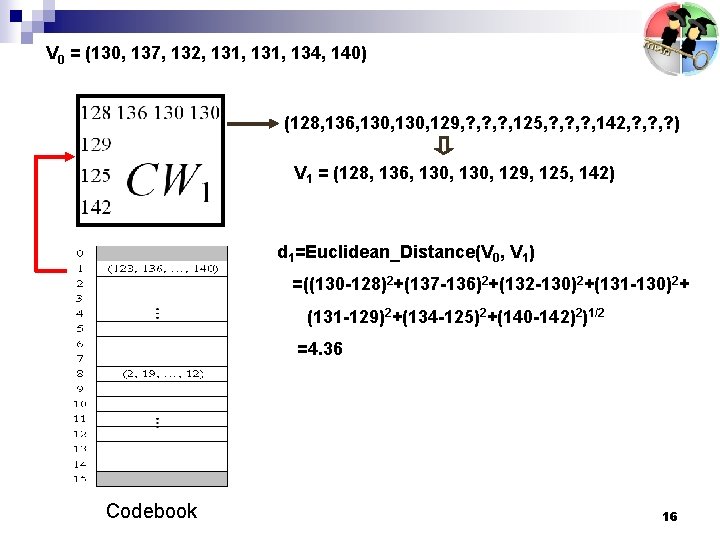
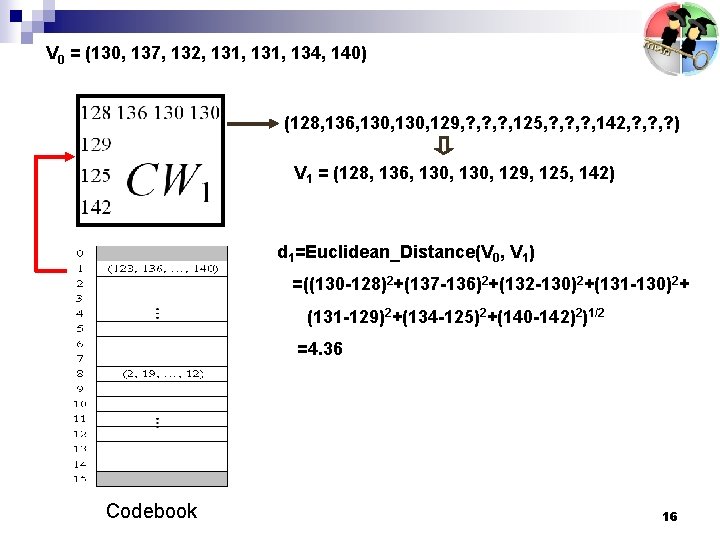
V 0 = (130, 137, 132, 131, 134, 140) (128, 136, 130, 129, ? , ? , 125, ? , ? , 142, ? , ? ) V 1 = (128, 136, 130, 129, 125, 142) d 1=Euclidean_Distance(V 0, V 1) =((130 -128)2+(137 -136)2+(132 -130)2+(131 -130)2+ (131 -129)2+(134 -125)2+(140 -142)2)1/2 =4. 36 Codebook 16
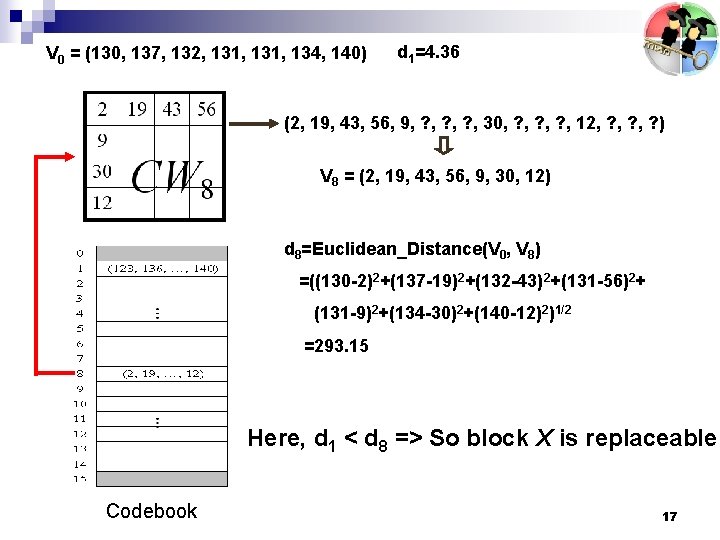
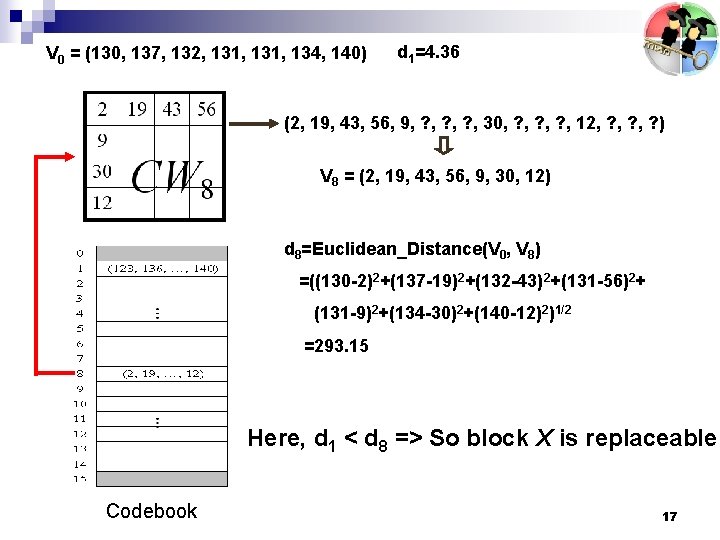
V 0 = (130, 137, 132, 131, 134, 140) d 1=4. 36 (2, 19, 43, 56, 9, ? , ? , 30, ? , ? , 12, ? , ? ) V 8 = (2, 19, 43, 56, 9, 30, 12) d 8=Euclidean_Distance(V 0, V 8) =((130 -2)2+(137 -19)2+(132 -43)2+(131 -56)2+ (131 -9)2+(134 -30)2+(140 -12)2)1/2 =293. 15 Here, d 1 < d 8 => So block X is replaceable Codebook 17
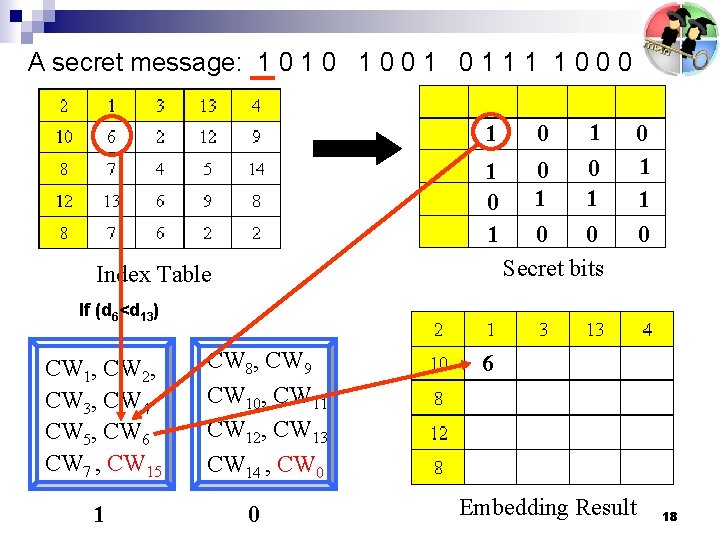
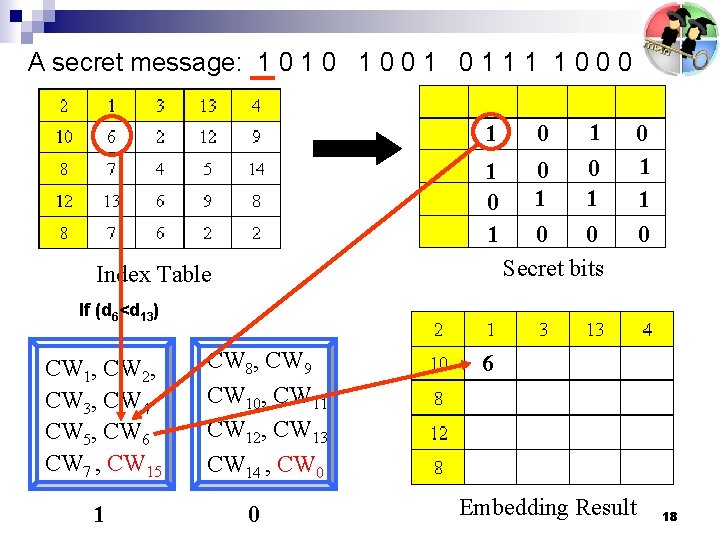
A secret message: 1 0 1 0 0 1 1 1 1 0 0 0 1 1 0 1 Index Table 0 1 0 0 Secret bits 0 1 1 0 If (d 6<d 13) CW 1, CW 2, CW 3, CW 4 CW 5, CW 6 CW 7 , CW 15 1 CW 8, CW 9 CW 10, CW 11 CW 12, CW 13 CW 14 , CW 0 0 6 Embedding Result 18
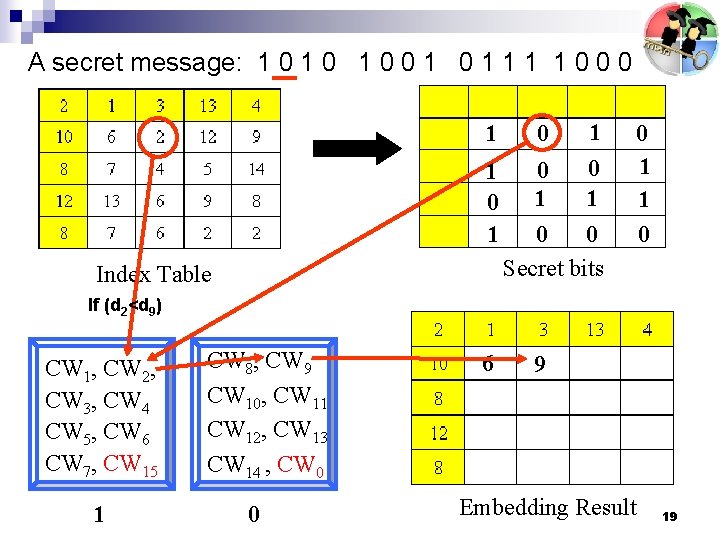
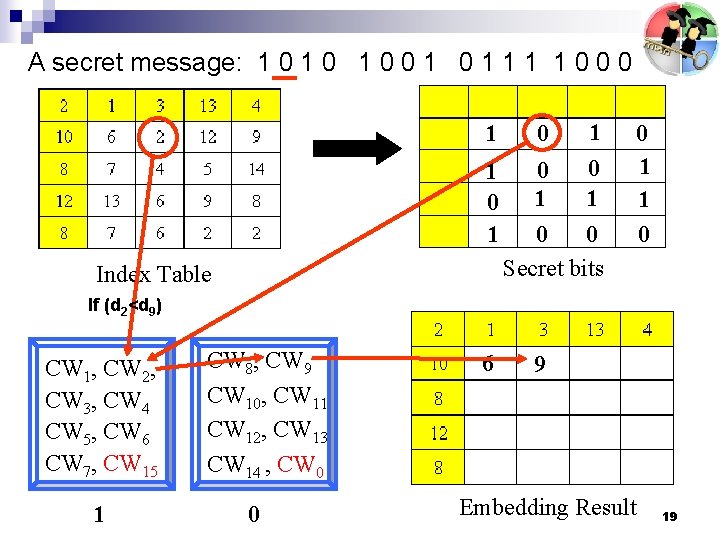
A secret message: 1 0 1 0 0 1 1 1 1 0 0 0 1 1 0 1 Index Table 0 1 0 0 Secret bits 0 1 1 0 If (d 2<d 9) CW 1, CW 2, CW 3, CW 4 CW 5, CW 6 CW 7, CW 15 1 CW 8, CW 9 CW 10, CW 11 CW 12, CW 13 CW 14 , CW 0 0 6 9 Embedding Result 19
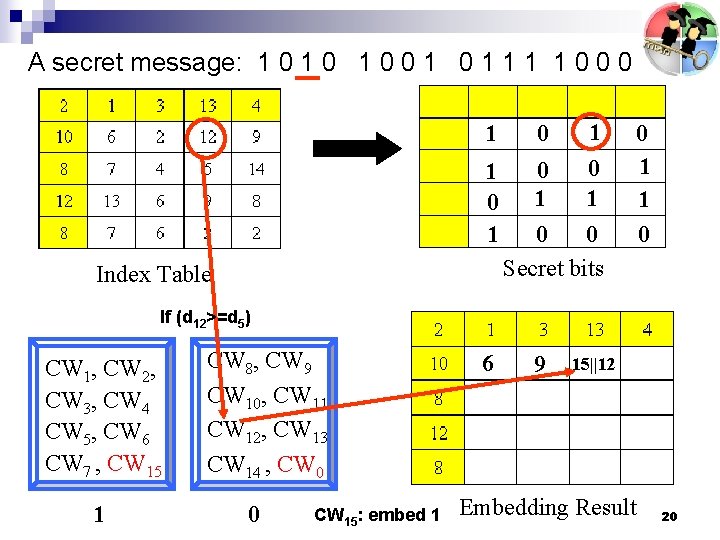
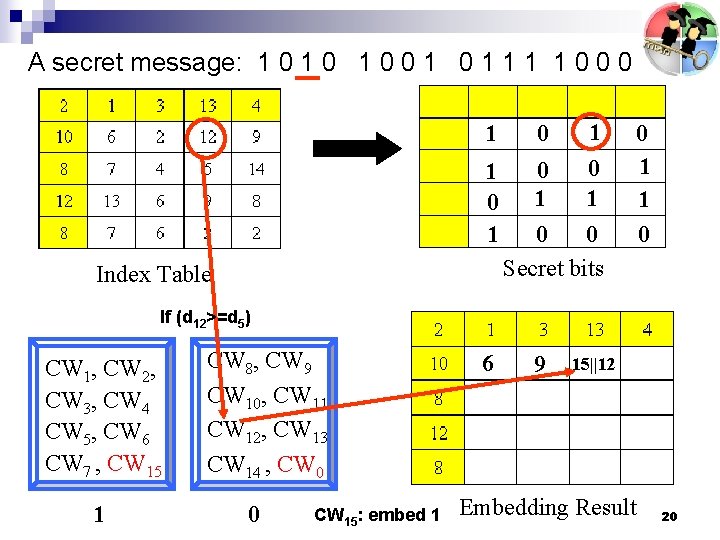
A secret message: 1 0 1 0 0 1 1 1 1 0 0 0 1 1 0 1 Index Table 0 1 0 0 Secret bits 0 1 1 0 If (d 12>=d 5) CW 1, CW 2, CW 3, CW 4 CW 5, CW 6 CW 7 , CW 15 1 CW 8, CW 9 CW 10, CW 11 CW 12, CW 13 CW 14 , CW 0 0 CW 15: embed 1 6 9 15||12 Embedding Result 20
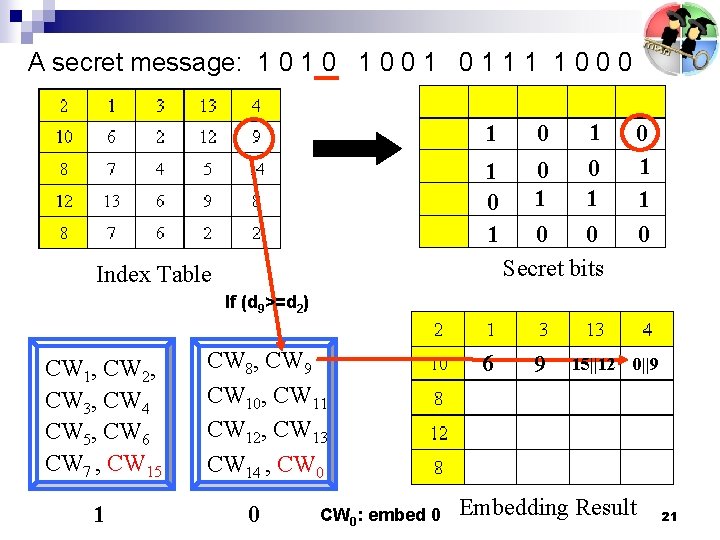
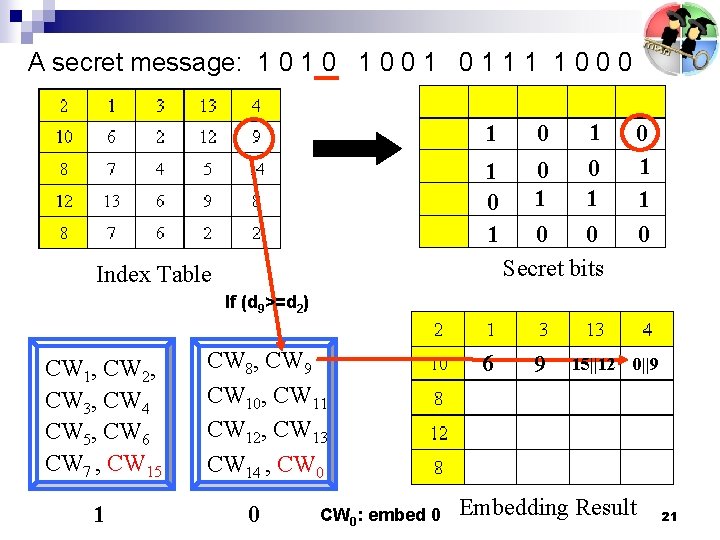
A secret message: 1 0 1 0 0 1 1 1 1 0 0 0 1 1 0 1 Index Table 0 1 0 0 Secret bits 0 1 1 0 If (d 9>=d 2) CW 1, CW 2, CW 3, CW 4 CW 5, CW 6 CW 7 , CW 15 1 CW 8, CW 9 CW 10, CW 11 CW 12, CW 13 CW 14 , CW 0 0 CW 0: embed 0 6 9 15||12 0||9 Embedding Result 21
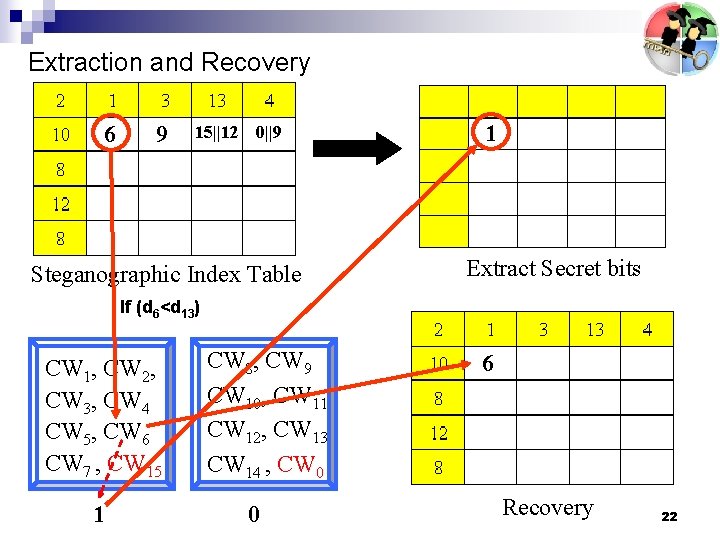
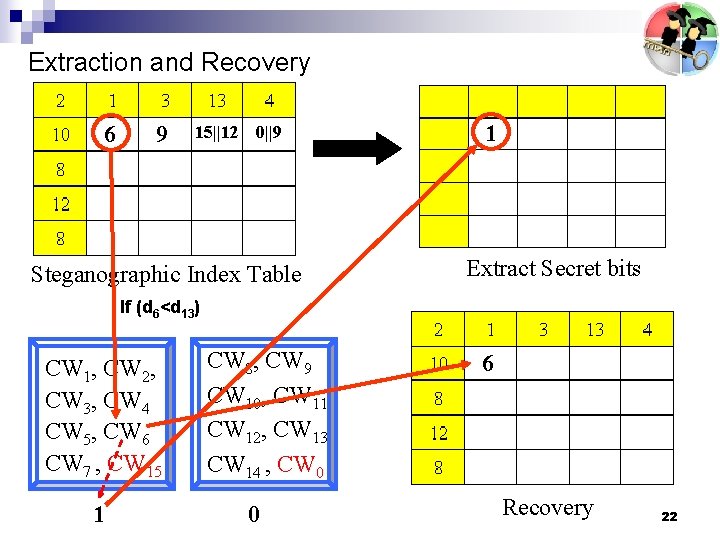
Extraction and Recovery 6 9 15||12 0||9 Steganographic Index Table 1 Extract Secret bits If (d 6<d 13) CW 1, CW 2, CW 3, CW 4 CW 5, CW 6 CW 7 , CW 15 1 CW 8, CW 9 CW 10, CW 11 CW 12, CW 13 CW 14 , CW 0 0 6 Recovery 22
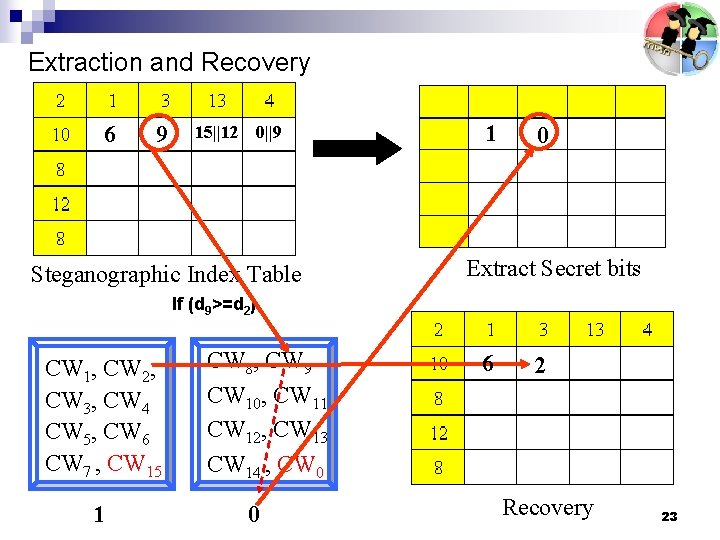
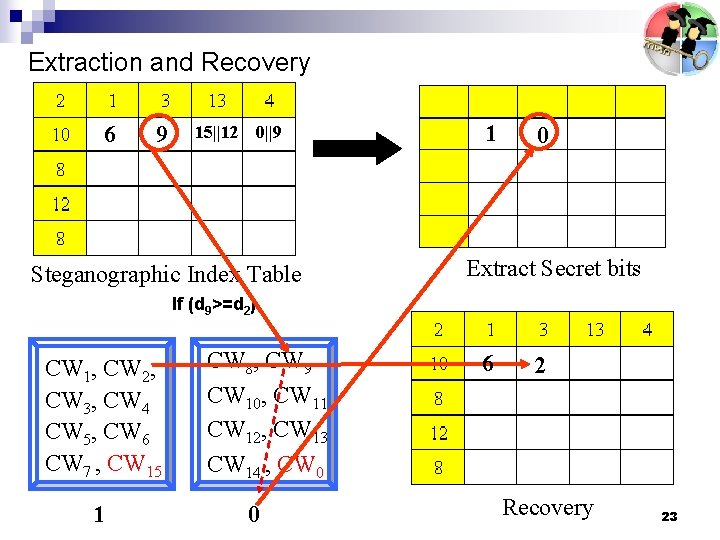
Extraction and Recovery 6 9 15||12 0||9 Steganographic Index Table 1 0 Extract Secret bits If (d 9>=d 2) CW 1, CW 2, CW 3, CW 4 CW 5, CW 6 CW 7 , CW 15 1 CW 8, CW 9 CW 10, CW 11 CW 12, CW 13 CW 14 , CW 0 0 6 2 Recovery 23
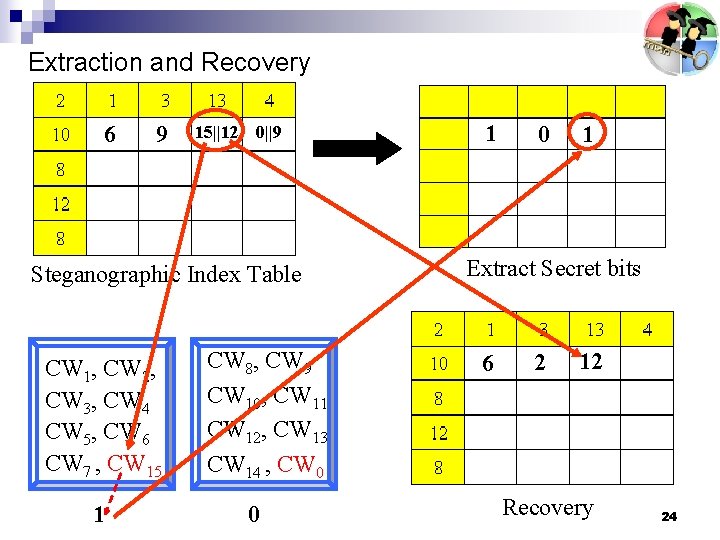
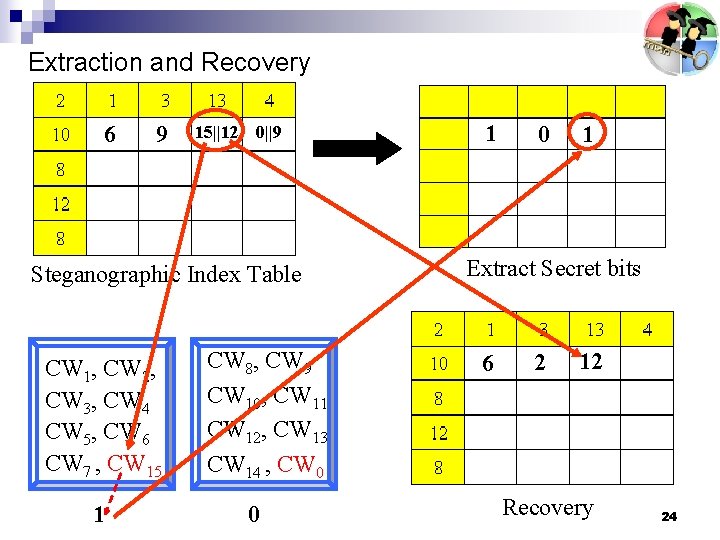
Extraction and Recovery 6 9 15||12 0||9 Steganographic Index Table CW 1, CW 2, CW 3, CW 4 CW 5, CW 6 CW 7 , CW 15 1 CW 8, CW 9 CW 10, CW 11 CW 12, CW 13 CW 14 , CW 0 0 1 Extract Secret bits 6 2 12 Recovery 24
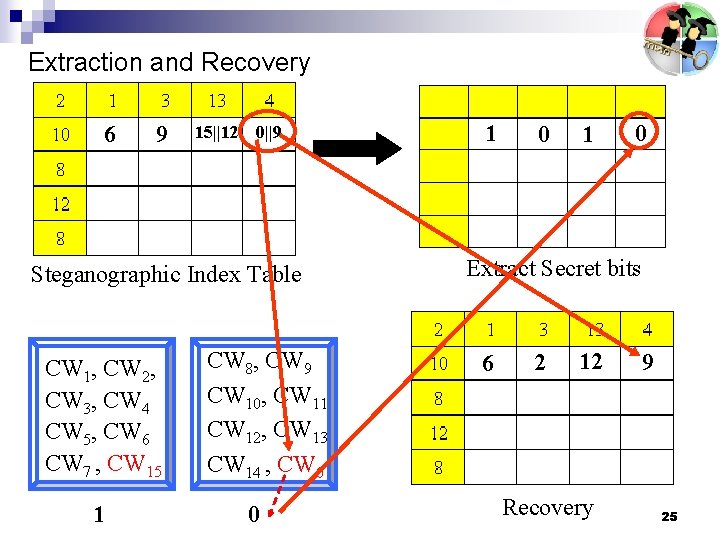
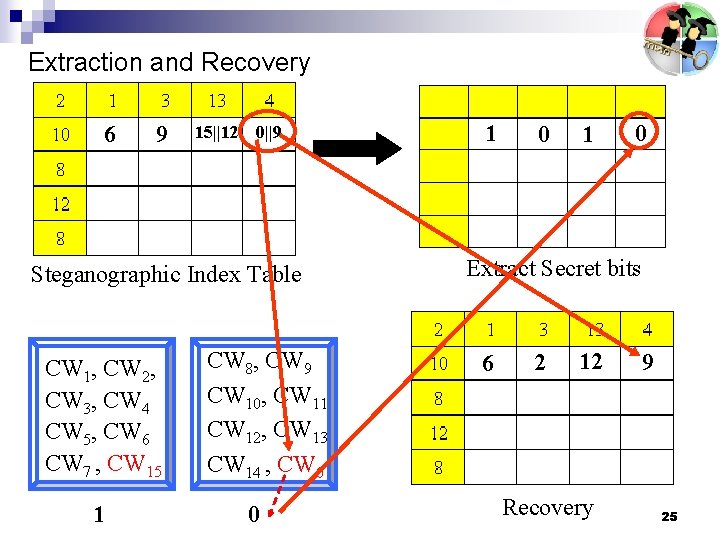
Extraction and Recovery 6 9 15||12 0||9 Steganographic Index Table CW 1, CW 2, CW 3, CW 4 CW 5, CW 6 CW 7 , CW 15 1 CW 8, CW 9 CW 10, CW 11 CW 12, CW 13 CW 14 , CW 0 0 1 0 Extract Secret bits 6 2 12 Recovery 9 25
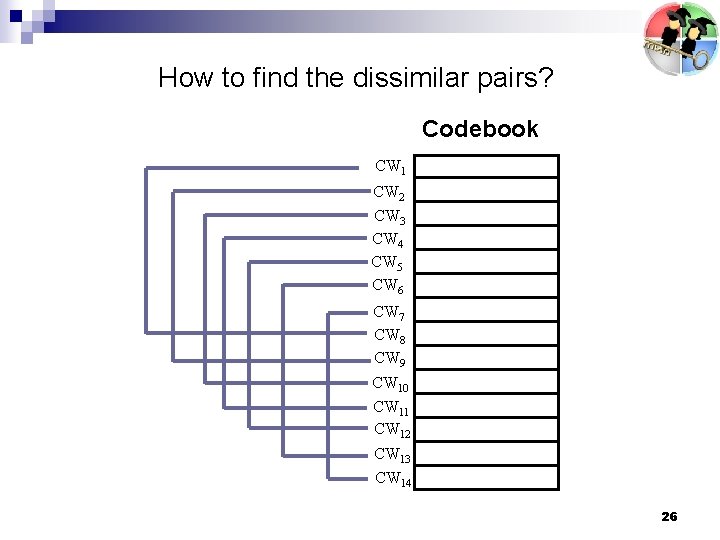
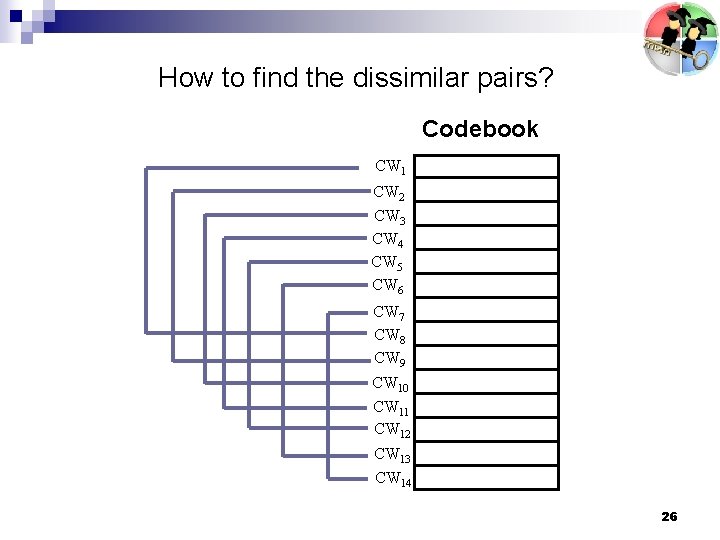
How to find the dissimilar pairs? Codebook CW 1 CW 2 CW 3 CW 4 CW 5 CW 6 CW 7 CW 8 CW 9 CW 10 CW 11 CW 12 CW 13 CW 14 26
Codeword Distribution 27
Codeword Projection by PCA (Principle Component Analysis) 28
Find the Dissimilar Pairs 29
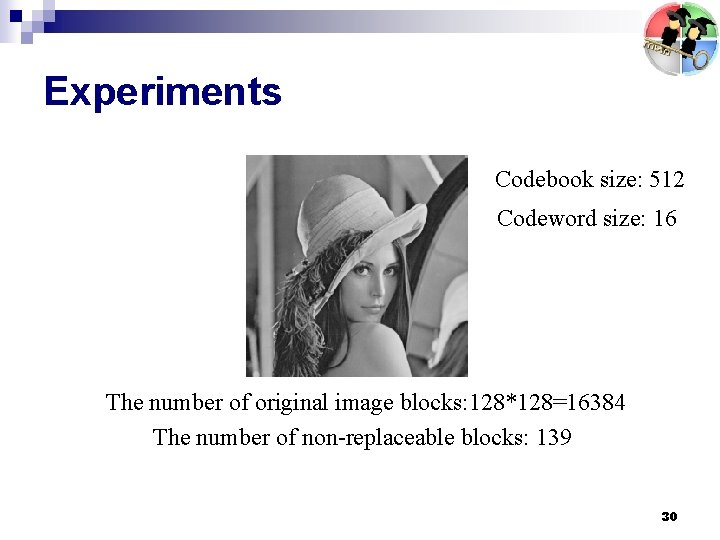
Experiments Codebook size: 512 Codeword size: 16 The number of original image blocks: 128*128=16384 The number of non-replaceable blocks: 139 30
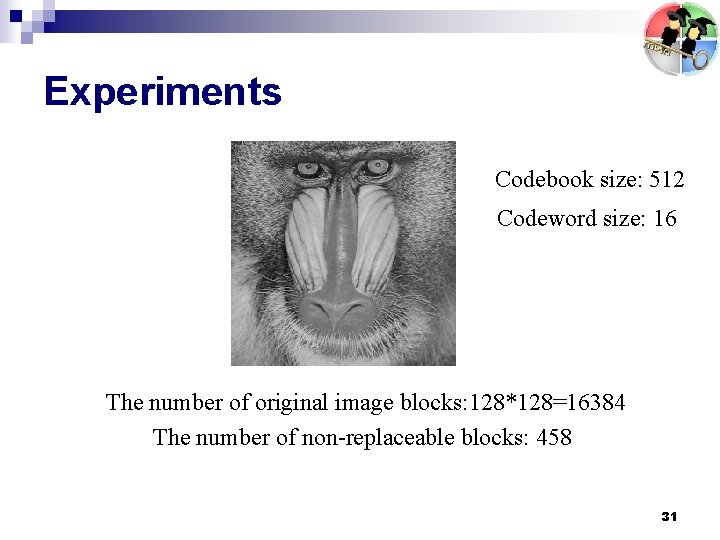
Experiments Codebook size: 512 Codeword size: 16 The number of original image blocks: 128*128=16384 The number of non-replaceable blocks: 458 31
Conclusions n A reversible VQ steganographic mehtod is proposed 32
Thank you very much for your attention !! 33