Cybersecurity Risk Lesson 1 Lesson 2 Lesson 3
Cybersecurity Risk Lesson 1: Lesson 2: Lesson 3: Lesson 4: Basic Cybersecurity Risk Concepts Cybersecurity Risk Model=Assessing Risk Cybersecurity Risk Model-Vulnerabilities Cybersecurity Risk Model-Security controls This document is licensed with a Creative Commons Attribution 4. 0 International License © 2017 www. C 5 colleges. org This material is based upon work supported by the National Science Foundation under Grant No. 1548315.
AP CSP Framework CSN-1. D Describe the differences between the Internet and the World Wide Web • CSN-1. D. 1 The World Wide Web is a system of linked pages, programs, and files. • CSN-1. D. 3 The World Wide Web uses the Internet. CSN-1. E For fault-tolerant systems, like the Internet: a. Describe the benefits of fault tolerance. b. Explain how a given system is fault-tolerant. c. Identify vulnerabilities to failure in a system. • CSN-1. E. 2 Redundancy is the inclusion of extra components that can be used to mitigate failure of a system if other components fail. • CSN-1. E. 3 One way to accomplish network redundancy is by having more than one path between any two connected devices. • CSN-1. E. 5 When a system can support failures and still continue to function, it is called fault-tolerant. This is important because elements of complex systems fail at unexpected times, often in groups, and fault tolerance allows users to continue to use the network. This document is licensed with a Creative Commons Attribution 4. 0 International License © 2017 www. C 5 colleges. org This material is based upon work supported by the National Science Foundation under Grant No. 1548315.
AP CSP Framework (cont. 1) IOC-2. A Describe the risks to privacy from collecting and storing personal data on a computer system • IOC-2. A. 1 Personally identifiable information (PII) is information about an individual that identifies, links, relates, or describes them. Examples of PII include: social security number, age, race, phone number(s), medical information, financial information, biometric data. • IOC-2. A. 2 Search engines can record and maintain a history of searches made by users. • IOC-2. A. 3 Websites can record and maintain a history of individuals who have viewed their pages. • IOC-2. A. 4 Devices, websites, and networks can collect information about a user’s location. • IOC-2. A. 5 Technology enables the collection, use, and exploitation of information about, by, and for individuals, groups, and institutions. • IOC-2. A. 6 Search engines can use search history to suggest websites or for targeted marketing. • IOC-2. A. 7: Disparate personal data, such as geolocation, cookies, and browsing history, can be aggregated to create knowledge about an individual. • IOC-2. A. 8 PII and other information placed online can be used to enhance a user’s online experiences. • IOC-2. A. 9 PII stored online can be used to simplify making online purchases. • IOC-2. A. 10 Commercial and governmental curation of information may be exploited if privacy and other protections are ignored. • IOC-2. A. 11: Information placed online can be used in ways that were not intended and in ways that may have a harmful impact. For example, an email message may be forwarded, tweets can be retweeted, social media posts can be viewed by potential employers. • IOC-2. A. 12 PII can be used to stalk or steal the identity of a person or to aid in the planning of other criminal acts. • IOC-2. A. 13 It is difficult to delete information once it has been placed online. • IOC-2. A. 14: Applications can collect your location and record where you have been, how you got there, and how long you have been at a given location. This document is licensed with a Creative Commons Attribution 4. 0 International License © 2017 www. C 5 colleges. org This material is based upon work supported by the National Science Foundation under Grant No. 1548315.
AP CSP Framework (cont. 2) IOC-2. B Explain how computing resources can be protected and can be misused. • IOC-2. B. 1 Authentication measures protect devices and information from unauthorized access. Examples of authentication measures include strong passwords and multifactor authentication. • IOC-2. B. 2 A strong password is something that is easy for a user to remember but would be difficult for someone else to guess based on knowledge of that user. • IOC-2. B. 3 Multifactor authentication is a method of computer access control in which a user is only granted access after successfully presenting several separate pieces of evidence to an authentication mechanism, typically in at least two of the following categories: knowledge, possession, and inheritance. • IOC-2. B. 4 Multifactor authentication requires at least two steps to unlock protected information; each step adds a new layer of security that must be broken to gain unauthorized access. • IOC-2. B. 5 Encryption is the process of encoding data to prevent unauthorized access to information. Decryption is the process of decoding the data. • IOC-2. B. 6 Certificate authorities issue digital certificates that validate the ownership of encryption keys used in secure communications and are based on a trust model. • IOC-2. B. 7 Computer virus and malware scanning software can help protect a computing system against infection. • IOC-2. B. 8 A computer virus is a malicious program that can copy itself and gain access to a computer in an unauthorized way. Computer viruses often attach themselves to legitimate programs and start running independently on a computer. • IOC-2. B. 9 Malware is software intended to damage a computing system or to take partial control over its operation. • IOC-2. B. 10 All real-world systems have errors or design flaws that can be exploited to compromise them. Regular software updates help fix errors that could compromise a computing system. • IOC-2. B. 11 Users can control the permissions programs have for collecting user information. Users should review the permission settings of programs to protect their privacy. This document is licensed with a Creative Commons Attribution 4. 0 International License © 2017 www. C 5 colleges. org This material is based upon work supported by the National Science Foundation under Grant No. 1548315.
AP CSP Framework (cont. 3) IOC-2. C Explain how unauthorized access to computing resources is gained. • IOC-2. C. 1 Phishing is a technique that attempts to trick a user into providing personal information. That personal information can then be used to access sensitive online resources, such as bank accounts and emails. • IOC-2. C. 2 Keylogging is the use of a program to record every keystroke made by a computer user in order to gain fraudulent access to passwords and other confidential information. • IOC-2. C. 3 Data sent over public networks can be intercepted, analyzed, and modified. One way that this can happen is through a rogue access point. • IOC-2. C. 4 A rogue access point is a wireless access point that gives unauthorized access to secure networks. • IOC-2. C. 5 A malicious link can be disguised on a web page or in an email message. • IOC-2. C. 6 Unsolicited emails, attachments, links, and forms in emails can be used to compromise the security of a computing system. These can come from unknown senders or from known senders whose security has been compromised. • IOC-2. C. 7 Untrustworthy (often free) downloads from freeware or shareware sites can contain malware. This document is licensed with a Creative Commons Attribution 4. 0 International License © 2017 www. C 5 colleges. org This material is based upon work supported by the National Science Foundation under Grant No. 1548315.
Learning Objectives • Describe the risks to security and privacy from collecting and storing personal data on a computer system. (IOC-2. A) • Explain how computing resources can be misused. (IOC-2. B) • Differentiate between threats and vulnerabilities. (IOC-2. A) • Explain how unauthorized access to computing resources is gained. (IOC-2. C) • Explain how computing resources are protected. (IOC-2. B) This document is licensed with a Creative Commons Attribution 4. 0 International License © 2017 www. C 5 colleges. org This material is based upon work supported by the National Science Foundation under Grant No. 1548315.
Warm-Up: What is Risk? Can we see, taste, smell, or touch risk like we could a dog? Can you describe a situation involving risk? • What are the risks of leaving your door unlocked? • What are the risks of losing your phone? • What are the risks of sharing a secret? This document is licensed with a Creative Commons Attribution 4. 0 International License © 2017 www. C 5 colleges. org This material is based upon work supported by the National Science Foundation under Grant No. 1548315.
A Formal definition of risk Risk - The potential for an unwanted or adverse outcome resulting from an incident, event, or occurrence, as determined by the likelihood that a particular threat will exploit a particular vulnerability, with the associated consequences. This document is licensed with a Creative Commons Attribution 4. 0 International License © 2017 www. C 5 colleges. org This material is based upon work supported by the National Science Foundation under Grant No. 1548315.
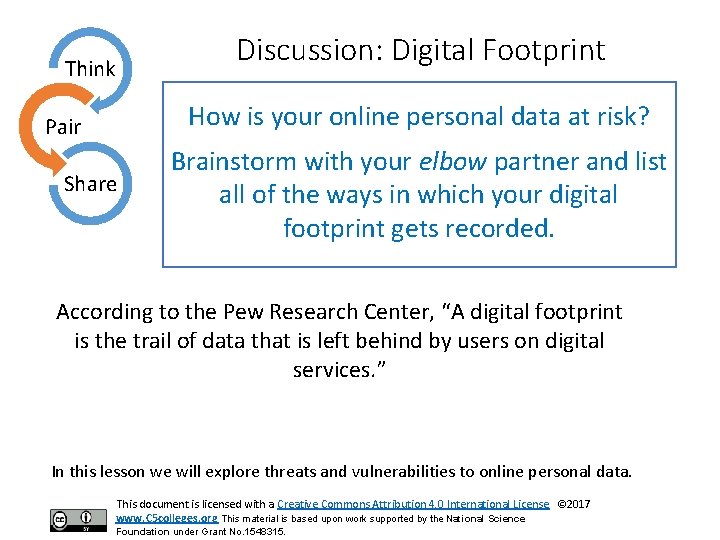
Think Discussion: Digital Footprint How is your online personal data at risk? Pair Share Brainstorm with your elbow partner and list all of the ways in which your digital footprint gets recorded. According to the Pew Research Center, “A digital footprint is the trail of data that is left behind by users on digital services. ” In this lesson we will explore threats and vulnerabilities to online personal data. This document is licensed with a Creative Commons Attribution 4. 0 International License © 2017 www. C 5 colleges. org This material is based upon work supported by the National Science Foundation under Grant No. 1548315.
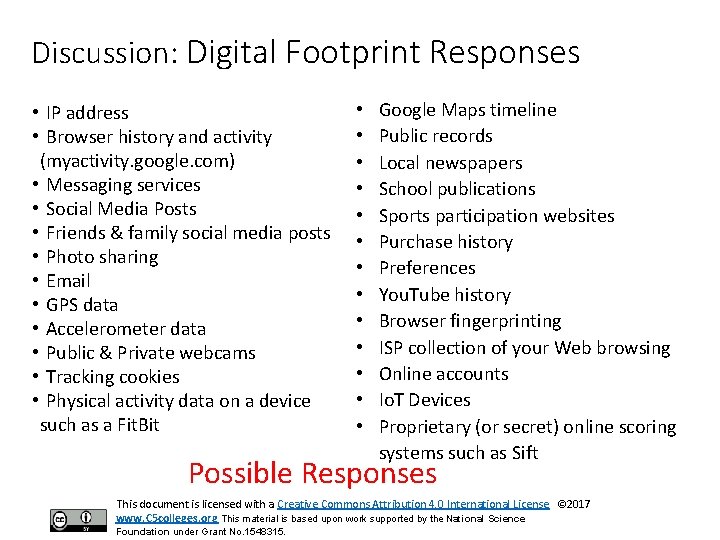
Discussion: Digital Footprint Responses • IP address • Browser history and activity (myactivity. google. com) • Messaging services • Social Media Posts • Friends & family social media posts • Photo sharing • Email • GPS data • Accelerometer data • Public & Private webcams • Tracking cookies • Physical activity data on a device such as a Fit. Bit • • • • Google Maps timeline Public records Local newspapers School publications Sports participation websites Purchase history Preferences You. Tube history Browser fingerprinting ISP collection of your Web browsing Online accounts Io. T Devices Proprietary (or secret) online scoring systems such as Sift Possible Responses This document is licensed with a Creative Commons Attribution 4. 0 International License © 2017 www. C 5 colleges. org This material is based upon work supported by the National Science Foundation under Grant No. 1548315.
Beneficial and Harmful Impacts What is Personally Identifiable Information? • How do we benefit from the collection of personal data when visiting websites? • How does the collection and aggregation of personal data cause harm? Benefit Harm This document is licensed with a Creative Commons Attribution 4. 0 International License © 2017 www. C 5 colleges. org This material is based upon work supported by the National Science Foundation under Grant No. 1548315.
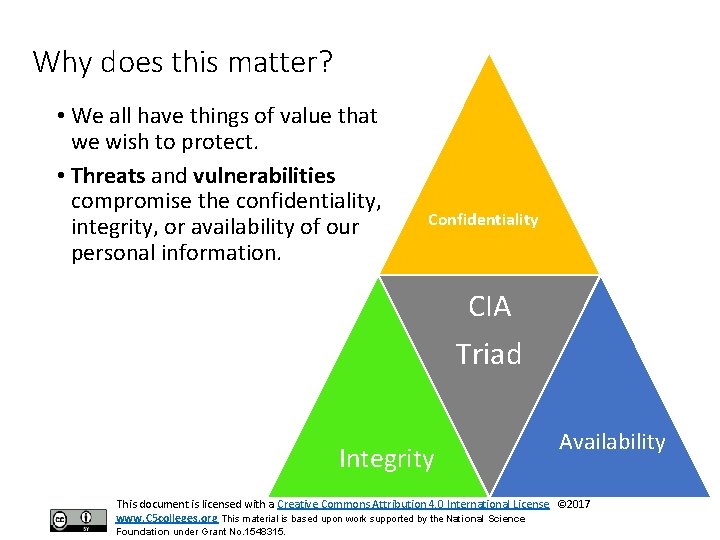
Why does this matter? • We all have things of value that we wish to protect. • Threats and vulnerabilities compromise the confidentiality, integrity, or availability of our personal information. Confidentiality CIA Triad Integrity Availability This document is licensed with a Creative Commons Attribution 4. 0 International License © 2017 www. C 5 colleges. org This material is based upon work supported by the National Science Foundation under Grant No. 1548315.
Identity Theft Threat • Identity theft is a crime that involves using another person’s personal information to take malicious actions, such as conducting fraud or stealing funds. • Criminals use a variety of methods to obtain Personally Identifiable Information (PII), which can be leveraged to carry out malicious actions. • According to a 2017 report from the US Department of Justice, 17. 6 million Americans or 7% of 16 years or older were victims of identity theft, and 86% experienced misuse of an existing credit card or bank account. • The threat actors include hacktivist (hackers for a social/political cause), disgruntled employees, cyber criminals, and nation-state actors. This document is licensed with a Creative Commons Attribution 4. 0 International License © 2017 www. C 5 colleges. org This material is based upon work supported by the National Science Foundation under Grant No. 1548315.
Phishing Attack • Phishing is the use of emails and websites that falsely purport to be associated with legitimate banks, financial institutions, or companies, but that manipulate Internet users into disclosing personal and financial data. • Phishing is a type of social engineering attack. The attackers research their targets and mimic actual emails and websites. The attacker attempts to create a sense of urgency and take advantage of human error. The very nature of the Web, a system of linked pages, programs, and files, creates vulnerabilities which can be exploited through phishing. This document is licensed with a Creative Commons Attribution 4. 0 International License © 2017 www. C 5 colleges. org This material is based upon work supported by the National Science Foundation under Grant No. 1548315.
How big is this problem? In its 2018 Internet Crime Report, the FBI reported that Phishing/Vishing/Smishing/Pharming caused: • Victim Loss of $48, 241, 748 • Victim Count of 26, 379 Phishing/Vishing/Smishing/Pharming is defined as unsolicited email, text messages, and telephone calls purportedly from a legitimate company requesting personal, financial, and/or login credentials. Source: https: //pdf. ic 3. gov/2018_IC 3 Report. pdf This document is licensed with a Creative Commons Attribution 4. 0 International License © 2017 www. C 5 colleges. org This material is based upon work supported by the National Science Foundation under Grant No. 1548315.
Threat and Vulnerability Defined • Threat - A circumstance or event that has or indicates the potential to exploit vulnerabilities and to adversely impact (create adverse consequences for) organizational operations, organizational assets (including information and information systems), individuals, other organizations, or society. 1 • Vulnerability - A characteristic or specific weakness that renders an organization or asset (such as information or an information system) open to exploitation by a given threat or susceptible to a given hazard. 1 This document is licensed with a Creative Commons Attribution 4. 0 International License © 2017 www. C 5 colleges. org This material is based upon work supported by the National Science Foundation under Grant No. 1548315.
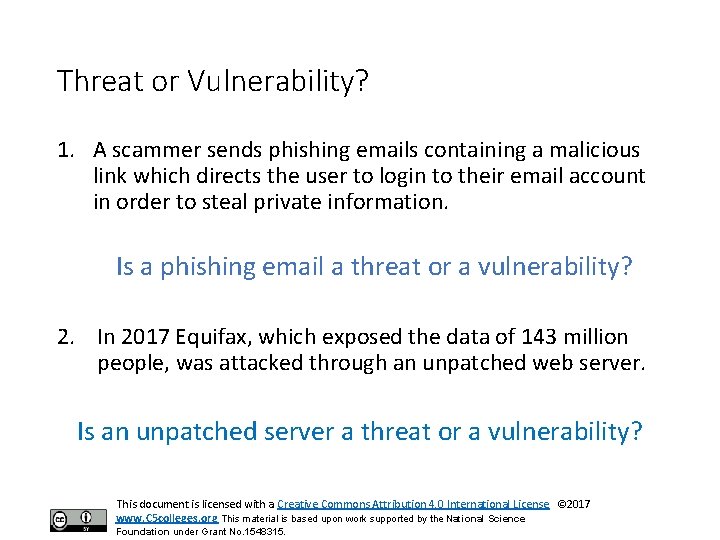
Threat or Vulnerability? 1. A scammer sends phishing emails containing a malicious link which directs the user to login to their email account in order to steal private information. Is a phishing email a threat or a vulnerability? 2. In 2017 Equifax, which exposed the data of 143 million people, was attacked through an unpatched web server. Is an unpatched server a threat or a vulnerability? This document is licensed with a Creative Commons Attribution 4. 0 International License © 2017 www. C 5 colleges. org This material is based upon work supported by the National Science Foundation under Grant No. 1548315.
Threat Vocabulary terms • Threat actor - An individual or a group posing a threat. • Threat agent/source – Either (i) intent and method targeted at the intentional exploitation of a vulnerability; or (ii) a situation and method that may accidentally trigger a vulnerability. • Threat assessment/analysis - Assessment to evaluate the actual or potential effect of a threat to a system. Note: The threat assessment may include identifying and describing the nature of the threat. This document is licensed with a Creative Commons Attribution 4. 0 International License © 2017 www. C 5 colleges. org This material is based upon work supported by the National Science Foundation under Grant No. 1548315.
Think Pair Share Brainstorm: Personal Data Threat Sources Brainstorm with your elbow partner and describe threat environment to your online personal data. Which items are threat actors or sources? Which items are vulnerabilities? Can you justify your responses? This document is licensed with a Creative Commons Attribution 4. 0 International License © 2017 www. C 5 colleges. org This material is based upon work supported by the National Science Foundation under Grant No. 1548315.
Threat landscape (actors, sources, events) • Cyberthreats (Ransomware, Malware, Phishing, Data breaches, Man in the Middle Attack, DDo. S) • Human error vulnerability • Hardware or software failure vulnerability • Misuse by authorized entities vulnerability • Misuse by unauthorized entity/insider attack • Cyber criminal threat • Hacktivist threat • Nation-state actor threat • Threat of natural disasters (fire, weather events). Your physical location may make you vulnerable to a specific threat event. Possible Responses This document is licensed with a Creative Commons Attribution 4. 0 International License © 2017 www. C 5 colleges. org This material is based upon work supported by the National Science Foundation under Grant No. 1548315.
What are vulnerabilities? • Posting on social networks and giving away hints or personal information. For example, using your pet’s name as a password and then posting photos and the name of your pet on your social media pages. • Personal data stored by your school, your healthcare provider, your bank, or retailers can be vulnerable to a data breach. All types of companies routinely collect data from Web surfing and use of apps. • Connecting to an open Wi-Fi access point can make you vulnerable to an attack. • Failing to update or patch your device can make you vulnerable to software exploits. Personal Data Breach: A leak or spill of personal data that is released from a secure location to an untrusted environment. It may also refer to a security incident in which an individual's sensitive, protected, or confidential data is copied, transmitted, viewed, stolen or used by an unauthorized individual. This document is licensed with a Creative Commons Attribution 4. 0 International License © 2017 www. C 5 colleges. org This material is based upon work supported by the National Science Foundation under Grant No. 1548315.
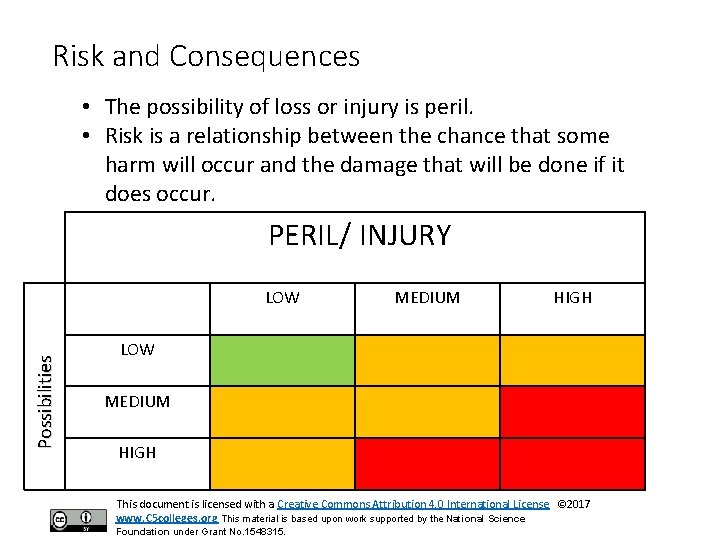
Risk and Consequences • The possibility of loss or injury is peril. • Risk is a relationship between the chance that some harm will occur and the damage that will be done if it does occur. PERIL/ INJURY Possibilities LOW MEDIUM HIGH This document is licensed with a Creative Commons Attribution 4. 0 International License © 2017 www. C 5 colleges. org This material is based upon work supported by the National Science Foundation under Grant No. 1548315.
Risk and Consequences (cont. 1) • Select a celebrity (athlete, actor, artist, etc). • How much personal information can you find about this person online? • You have 15 minutes to record as much information as you can find. Fill in the first two columns only. • Pair up with a classmate, list and discuss potential harm in the third column. This document is licensed with a Creative Commons Attribution 4. 0 International License © 2017 www. C 5 colleges. org This material is based upon work supported by the National Science Foundation under Grant No. 1548315.
Consequences or Damages $ • Financial loss • Ransomware • Disruption to business operations • Downtime (lack of availability) • Online vandalism • Physical or psychological harm from cyberstalking • Damage to reputation • Embarrassment or stigma from social media posts • Potential for discrimination by the release of data • Individual and Societal harm from disinformation and lack of trust This document is licensed with a Creative Commons Attribution 4. 0 International License © 2017 www. C 5 colleges. org This material is based upon work supported by the National Science Foundation under Grant No. 1548315.
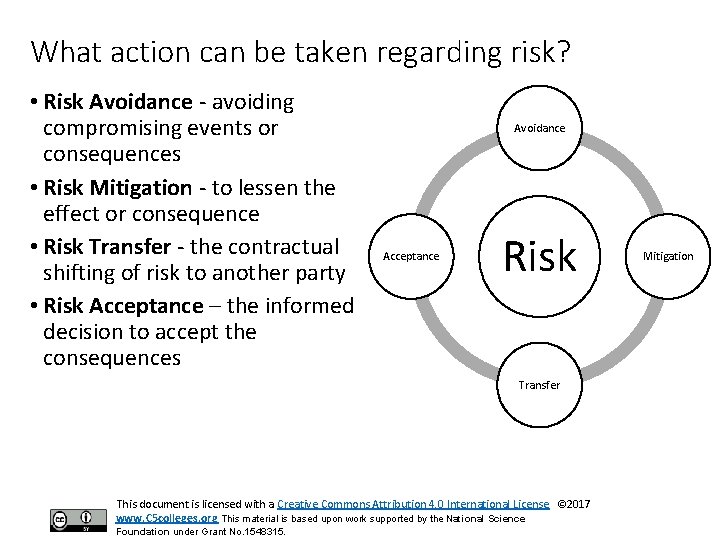
What action can be taken regarding risk? • Risk Avoidance - avoiding compromising events or consequences • Risk Mitigation - to lessen the effect or consequence • Risk Transfer - the contractual shifting of risk to another party • Risk Acceptance – the informed decision to accept the consequences Avoidance Acceptance Risk Transfer This document is licensed with a Creative Commons Attribution 4. 0 International License © 2017 www. C 5 colleges. org This material is based upon work supported by the National Science Foundation under Grant No. 1548315. Mitigation
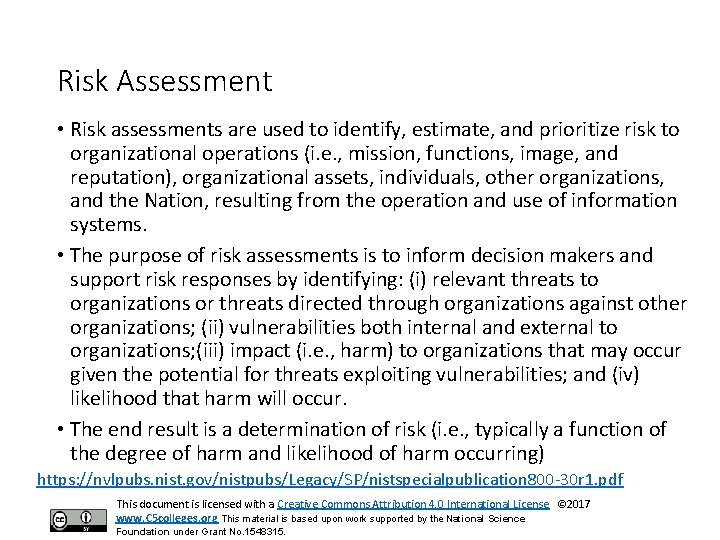
Risk Assessment • Risk assessments are used to identify, estimate, and prioritize risk to organizational operations (i. e. , mission, functions, image, and reputation), organizational assets, individuals, other organizations, and the Nation, resulting from the operation and use of information systems. • The purpose of risk assessments is to inform decision makers and support risk responses by identifying: (i) relevant threats to organizations or threats directed through organizations against other organizations; (ii) vulnerabilities both internal and external to organizations; (iii) impact (i. e. , harm) to organizations that may occur given the potential for threats exploiting vulnerabilities; and (iv) likelihood that harm will occur. • The end result is a determination of risk (i. e. , typically a function of the degree of harm and likelihood of harm occurring) https: //nvlpubs. nist. gov/nistpubs/Legacy/SP/nistspecialpublication 800 -30 r 1. pdf This document is licensed with a Creative Commons Attribution 4. 0 International License © 2017 www. C 5 colleges. org This material is based upon work supported by the National Science Foundation under Grant No. 1548315.
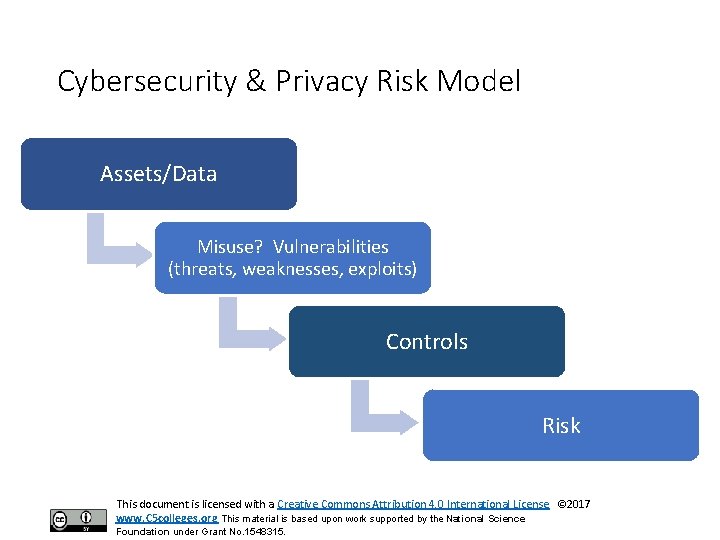
Cybersecurity & Privacy Risk Model Assets/Data Misuse? Vulnerabilities (threats, weaknesses, exploits) Controls Risk This document is licensed with a Creative Commons Attribution 4. 0 International License © 2017 www. C 5 colleges. org This material is based upon work supported by the National Science Foundation under Grant No. 1548315.
Summary Basic Cybersecurity Concepts • Risk is the potential for an unwanted or adverse outcome resulting from an incident, event, or occurrence, as determined by the likelihood that a particular threat will exploit a particular vulnerability, with the associated consequences. • Threats and vulnerabilities compromise the confidentiality, integrity, or availability of our personal information. • Threats are an event or condition that has the potential for causing loss and the undesirable consequences or impact from such loss. • Vulnerabilities are flaws or weaknesses in an information system. This document is licensed with a Creative Commons Attribution 4. 0 International License © 2017 www. C 5 colleges. org This material is based upon work supported by the National Science Foundation under Grant No. 1548315.
Warm-up Activity: Your Data Risk Do the potential risks to your data (collected by businesses) outweigh the benefits? What do you get in return for the data that is collected about you? This document is licensed with a Creative Commons Attribution 4. 0 International License © 2017 www. C 5 colleges. org This material is based upon work supported by the National Science Foundation under Grant No. 1548315.
Warm-up Activity: Survey Results A recent Pew Research Center survey reported the following: • over 70% of respondents believe that most or all of what we do online is tracked • 2/3 of respondents believe that surveillance is an inevitable consequence of modern existence • Over 80% of respondents believe that they have very little or no control over the data being collected • 81% of respondents believe that the potential risks of data collection by companies outweigh the benefits • 79% of Americans say they are not too or not at all confident that companies will admit mistakes and take responsibility if they misuse or compromise personal information • 70% of adults say their personal data is less secure today than it was five years ago This document is licensed with a Creative Commons Attribution 4. 0 International License © 2017 www. C 5 colleges. org This material is based upon work supported by the National Science Foundation under Grant No. 1548315.
Introduction In this lesson, we will explore risk assessment. A Cybersecurity Risk Model is presented as the framework for understanding what is at risk (assets), and what are threats and vulnerabilities, The model is based upon the NIST Framework. The NIST Framework integrates industry standards and best practices to help organizations manage their cybersecurity risks. This document is licensed with a Creative Commons Attribution 4. 0 International License © 2017 www. C 5 colleges. org This material is based upon work supported by the National Science Foundation under Grant No. 1548315.
Risk Assessment Defined The process of identifying the risks to system security and determining the probability of occurrence, the resulting impact, and the additional safeguards that mitigate this impact. This document is licensed with a Creative Commons Attribution 4. 0 International License © 2017 www. C 5 colleges. org This material is based upon work supported by the National Science Foundation under Grant No. 1548315.
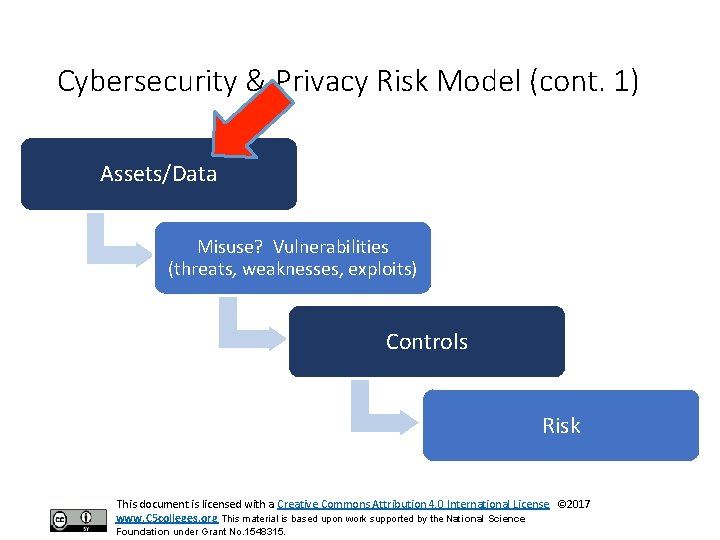
Cybersecurity & Privacy Risk Model (cont. 1) Assets/Data Misuse? Vulnerabilities (threats, weaknesses, exploits) Controls Risk This document is licensed with a Creative Commons Attribution 4. 0 International License © 2017 www. C 5 colleges. org This material is based upon work supported by the National Science Foundation under Grant No. 1548315.
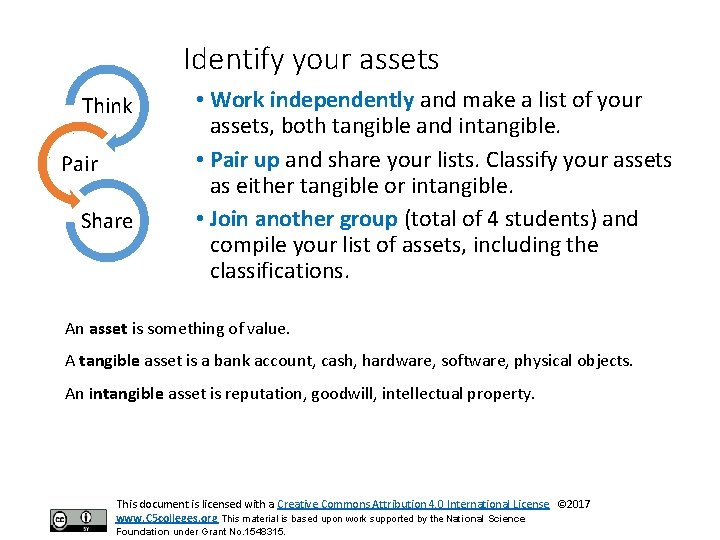
Identify your assets Think Pair Share • Work independently and make a list of your assets, both tangible and intangible. • Pair up and share your lists. Classify your assets as either tangible or intangible. • Join another group (total of 4 students) and compile your list of assets, including the classifications. An asset is something of value. A tangible asset is a bank account, cash, hardware, software, physical objects. An intangible asset is reputation, goodwill, intellectual property. This document is licensed with a Creative Commons Attribution 4. 0 International License © 2017 www. C 5 colleges. org This material is based upon work supported by the National Science Foundation under Grant No. 1548315.
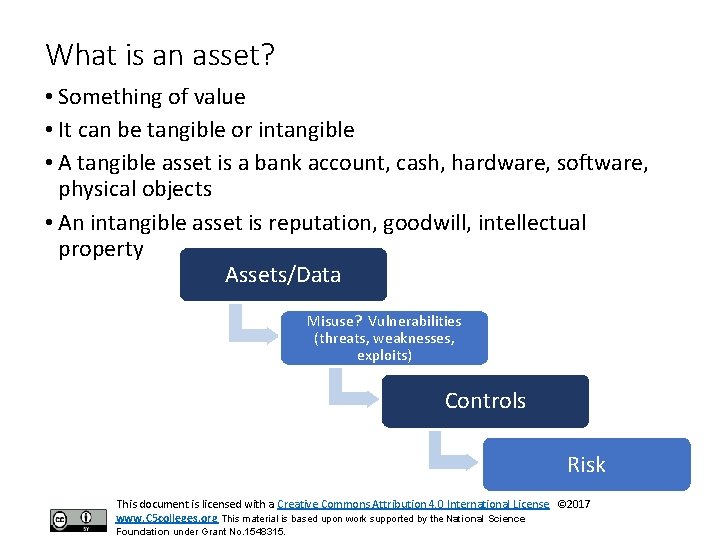
What is an asset? • Something of value • It can be tangible or intangible • A tangible asset is a bank account, cash, hardware, software, physical objects • An intangible asset is reputation, goodwill, intellectual property Assets/Data Misuse? Vulnerabilities (threats, weaknesses, exploits) Controls Risk This document is licensed with a Creative Commons Attribution 4. 0 International License © 2017 www. C 5 colleges. org This material is based upon work supported by the National Science Foundation under Grant No. 1548315.
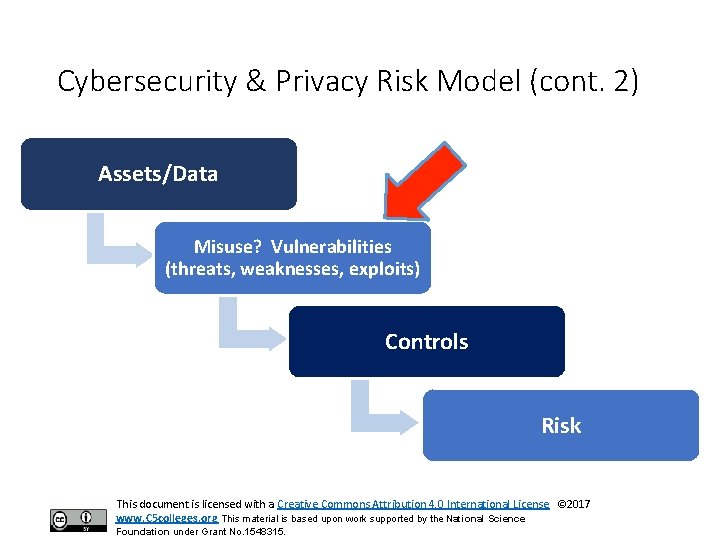
Cybersecurity & Privacy Risk Model (cont. 2) Assets/Data Misuse? Vulnerabilities (threats, weaknesses, exploits) Controls Risk This document is licensed with a Creative Commons Attribution 4. 0 International License © 2017 www. C 5 colleges. org This material is based upon work supported by the National Science Foundation under Grant No. 1548315.
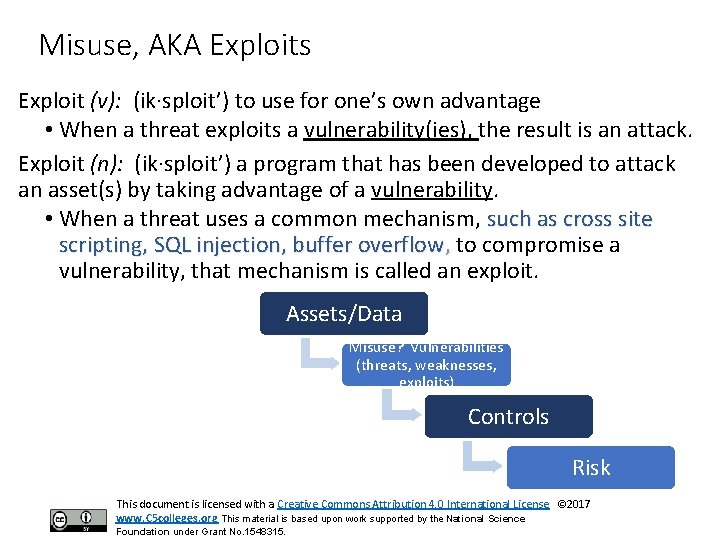
Misuse, AKA Exploits Exploit (v): (ik∙sploit’) to use for one’s own advantage • When a threat exploits a vulnerability(ies), the result is an attack. Exploit (n): (ik∙sploit’) a program that has been developed to attack an asset(s) by taking advantage of a vulnerability. • When a threat uses a common mechanism, such as cross site scripting, SQL injection, buffer overflow, to compromise a vulnerability, that mechanism is called an exploit. Assets/Data Misuse? Vulnerabilities (threats, weaknesses, exploits) Controls Risk This document is licensed with a Creative Commons Attribution 4. 0 International License © 2017 www. C 5 colleges. org This material is based upon work supported by the National Science Foundation under Grant No. 1548315.
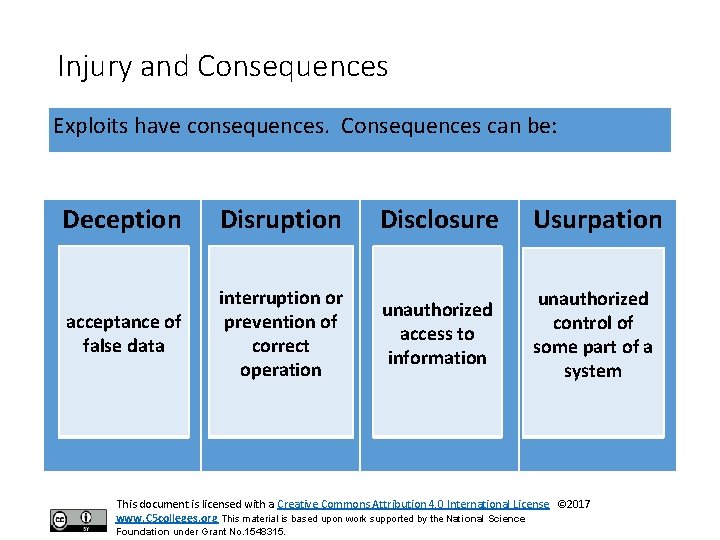
Injury and Consequences Exploits have consequences. Consequences can be: Deception Disruption Disclosure Usurpation acceptance of false data interruption or prevention of correct operation unauthorized access to information unauthorized control of some part of a system This document is licensed with a Creative Commons Attribution 4. 0 International License © 2017 www. C 5 colleges. org This material is based upon work supported by the National Science Foundation under Grant No. 1548315.
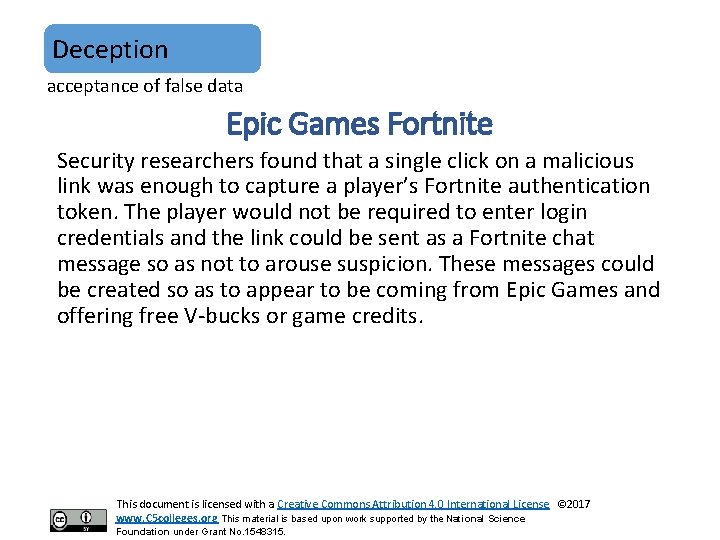
Deception acceptance of false data Epic Games Fortnite Security researchers found that a single click on a malicious link was enough to capture a player’s Fortnite authentication token. The player would not be required to enter login credentials and the link could be sent as a Fortnite chat message so as not to arouse suspicion. These messages could be created so as to appear to be coming from Epic Games and offering free V-bucks or game credits. This document is licensed with a Creative Commons Attribution 4. 0 International License © 2017 www. C 5 colleges. org This material is based upon work supported by the National Science Foundation under Grant No. 1548315.
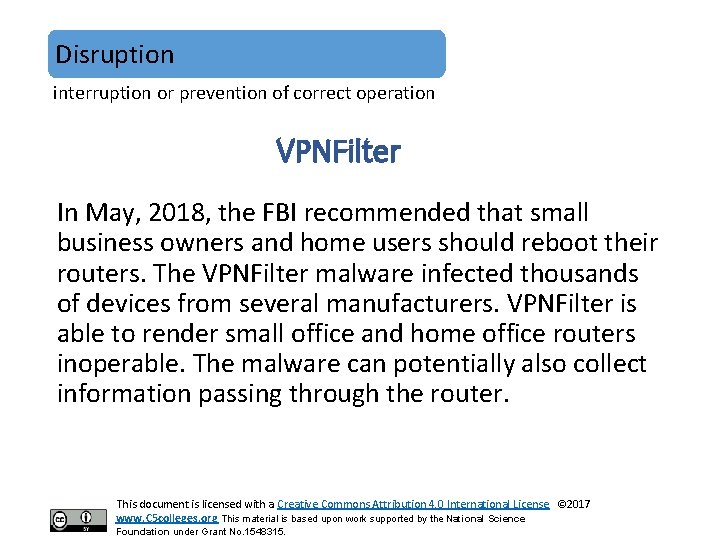
Disruption interruption or prevention of correct operation VPNFilter In May, 2018, the FBI recommended that small business owners and home users should reboot their routers. The VPNFilter malware infected thousands of devices from several manufacturers. VPNFilter is able to render small office and home office routers inoperable. The malware can potentially also collect information passing through the router. This document is licensed with a Creative Commons Attribution 4. 0 International License © 2017 www. C 5 colleges. org This material is based upon work supported by the National Science Foundation under Grant No. 1548315.
Disclosure unauthorized access to information Marriott breach In 2018, Marriott reported that a breach of its Starwood guest reservation database exposed the personal information of up to 500 million people. According to Marriott, the hackers accessed people’s names, addresses, phone numbers, email addresses, passport numbers, dates of birth, gender, Starwood loyalty program account information, and reservation information. For some, they also stole payment card numbers and expiration dates. Marriott says the payment card numbers were encrypted, but it does not yet know if the hackers also stole the information needed to decrypt them. This document is licensed with a Creative Commons Attribution 4. 0 International License © 2017 www. C 5 colleges. org This material is based upon work supported by the National Science Foundation under Grant No. 1548315.
Usurpation unauthorized control of some part of a system Ransomware The Cryptowall Trojan is mainly distributed through spam campaigns, compromised websites, malicious ads, or other malware. Once installed, it encrypts the files on the compromised computer. It then attempts to convince the user to pay a ransom to decrypt the files. It is designed to prevent the user from accessing their files. This document is licensed with a Creative Commons Attribution 4. 0 International License © 2017 www. C 5 colleges. org This material is based upon work supported by the National Science Foundation under Grant No. 1548315.
Risk Scenarios Activity • Read each of the Four Risk Scenarios provided in the handout. For each scenario, write down if you think: 1) it has a low/medium/or high possibility of happening and 2) the resulting peril or injury would be low/medium/or high. • Then on the handout given to you, write the scenario number in the corresponding cell. • In the table, write your reasons for the rating for possibility and the rating for injury. This document is licensed with a Creative Commons Attribution 4. 0 International License © 2017 www. C 5 colleges. org This material is based upon work supported by the National Science Foundation under Grant No. 1548315.
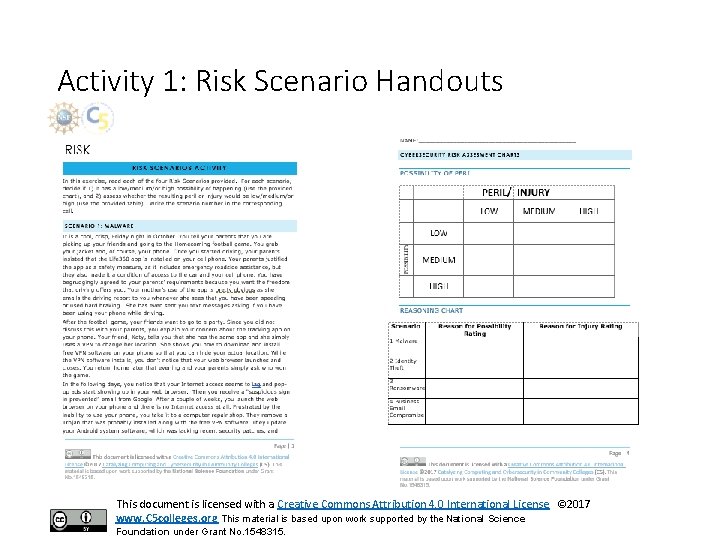
Activity 1: Risk Scenario Handouts This document is licensed with a Creative Commons Attribution 4. 0 International License © 2017 www. C 5 colleges. org This material is based upon work supported by the National Science Foundation under Grant No. 1548315.
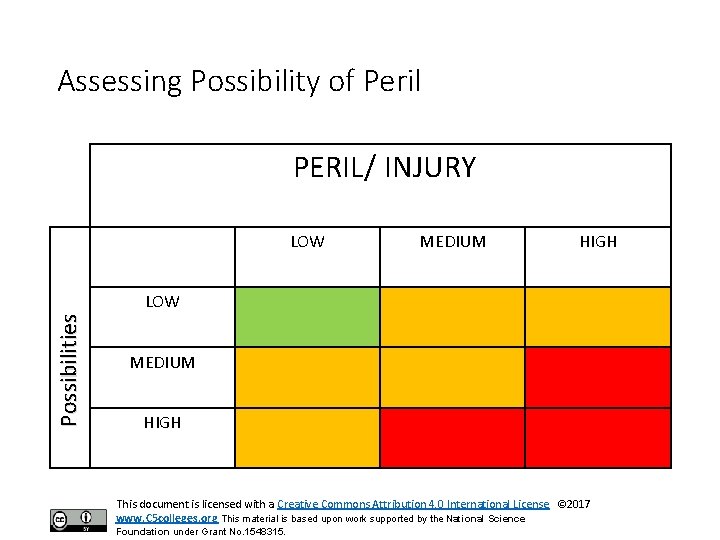
Assessing Possibility of Peril PERIL/ INJURY LOW MEDIUM HIGH Possibilities LOW MEDIUM HIGH This document is licensed with a Creative Commons Attribution 4. 0 International License © 2017 www. C 5 colleges. org This material is based upon work supported by the National Science Foundation under Grant No. 1548315.
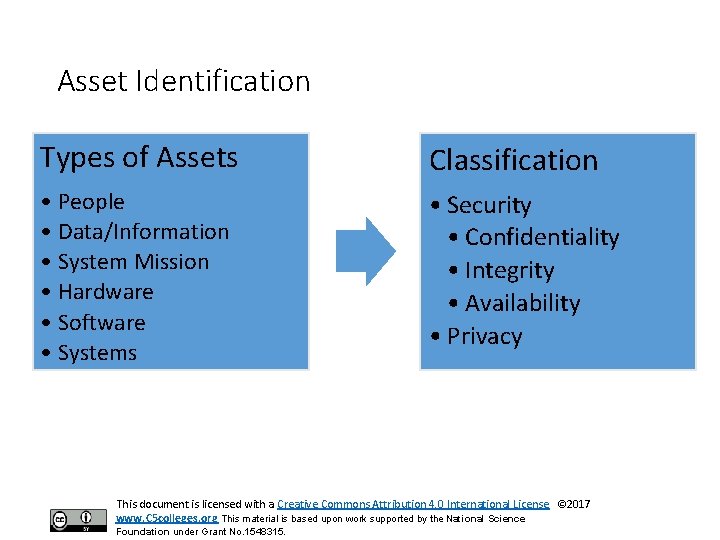
Asset Identification Types of Assets Classification • People • Data/Information • System Mission • Hardware • Software • Systems • Security • Confidentiality • Integrity • Availability • Privacy This document is licensed with a Creative Commons Attribution 4. 0 International License © 2017 www. C 5 colleges. org This material is based upon work supported by the National Science Foundation under Grant No. 1548315.
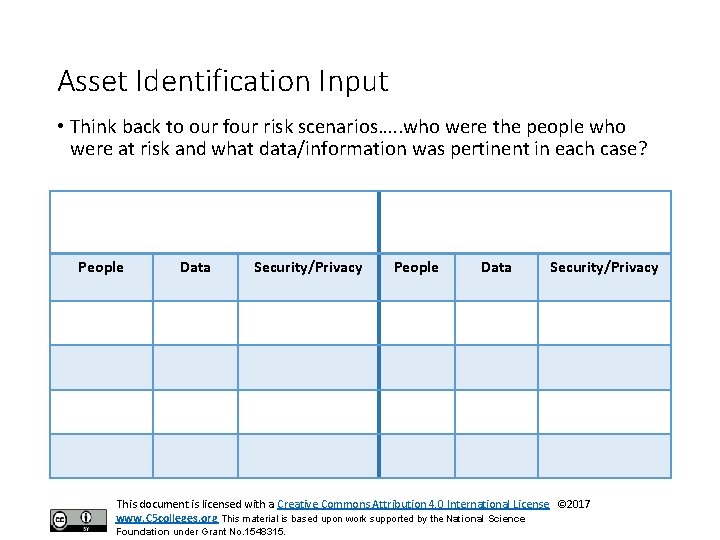
Asset Identification Input • Think back to our four risk scenarios…. . who were the people who were at risk and what data/information was pertinent in each case? People Data Security/Privacy This document is licensed with a Creative Commons Attribution 4. 0 International License © 2017 www. C 5 colleges. org This material is based upon work supported by the National Science Foundation under Grant No. 1548315.
Asset Identification Activity The goal of this activity is to identify all of the assets that you rely on daily using Risk Scenario #1. This document is licensed with a Creative Commons Attribution 4. 0 International License © 2017 www. C 5 colleges. org This material is based upon work supported by the National Science Foundation under Grant No. 1548315.
Summary of Cybersecurity Risk Model. Assessing Risk • The consequences of exploits can be deception, disruption, disclosure, or usurpation. • The process of identifying the risks to system security and determining the probability of occurrence, the resulting impact, and the additional safeguards that mitigate this impact. • An asset is something of value. This document is licensed with a Creative Commons Attribution 4. 0 International License © 2017 www. C 5 colleges. org This material is based upon work supported by the National Science Foundation under Grant No. 1548315.
Warm Up Activity: Student Poll 1. Do you regularly update your phone’s OS? 2. Have you ever connected to a public Wi. Fi access point? 3. Have you ever suspected the authenticity of an email? This document is licensed with a Creative Commons Attribution 4. 0 International License © 2017 www. C 5 colleges. org This material is based upon work supported by the National Science Foundation under Grant No. 1548315.
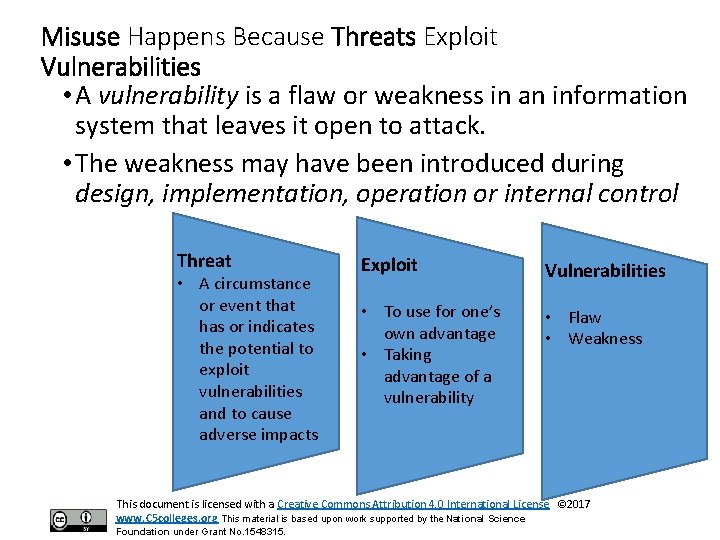
Misuse Happens Because Threats Exploit Vulnerabilities • A vulnerability is a flaw or weakness in an information system that leaves it open to attack. • The weakness may have been introduced during design, implementation, operation or internal control Threat • A circumstance or event that has or indicates the potential to exploit vulnerabilities and to cause adverse impacts Exploit Vulnerabilities • To use for one’s own advantage • Taking advantage of a vulnerability • Flaw • Weakness This document is licensed with a Creative Commons Attribution 4. 0 International License © 2017 www. C 5 colleges. org This material is based upon work supported by the National Science Foundation under Grant No. 1548315.
Vulnerability Identification Activity • How do you identify vulnerabilities? • Vulnerability Databases • There are databases that collect, maintain and disseminate information vulnerabilities targeting real computer systems that have been discovered. • These database will usually describe the vulnerability, assess the potential infliction on computer systems and the workaround required to desist a hacker. This document is licensed with a Creative Commons Attribution 4. 0 International License © 2017 www. C 5 colleges. org This material is based upon work supported by the National Science Foundation under Grant No. 1548315.
National Vulnerability Database • The NVD is the U. S. government repository of standards based vulnerability management data represented using the Security Content Automation Protocol (SCAP). • The NVD is a product of the NIST Computer Security Division, Information Technology Laboratory and is sponsored by the Department of Homeland Security’s National Cyber Security Division. • National Institute of Standards and Technology (NIST) promotes U. S. innovation and industrial competitiveness by advancing measurement science, standards and technology in ways that enhance economic security and improve our quality of life. NIST is a nonregulatory agency of the U. S. Department of Commerce. This document is licensed with a Creative Commons Attribution 4. 0 International License © 2017 www. C 5 colleges. org This material is based upon work supported by the National Science Foundation under Grant No. 1548315.
Example Search: Pulse SSL • What is the base vulnerability severity score? • What is the impact score? • What is the exploitability score? • What is the attack vector? • Does the vulnerability impact confidentiality? • Does the vulnerability impact integrity? • Does the vulnerability impact availability? This document is licensed with a Creative Commons Attribution 4. 0 International License © 2017 www. C 5 colleges. org This material is based upon work supported by the National Science Foundation under Grant No. 1548315.
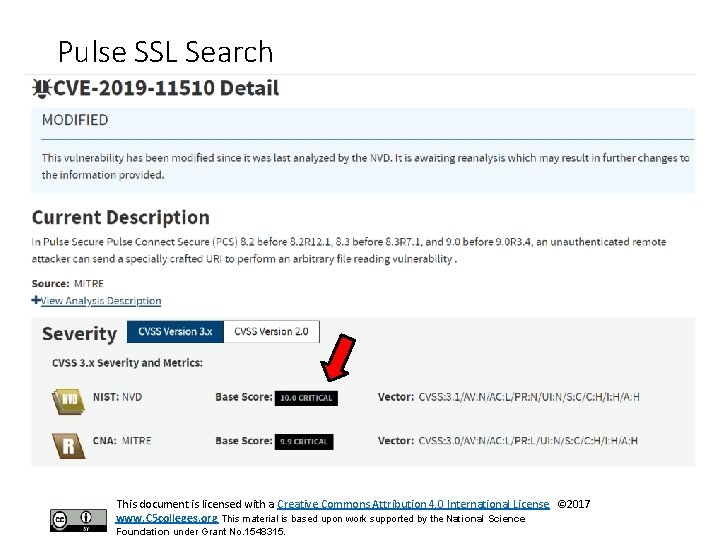
Pulse SSL Search This document is licensed with a Creative Commons Attribution 4. 0 International License © 2017 www. C 5 colleges. org This material is based upon work supported by the National Science Foundation under Grant No. 1548315.
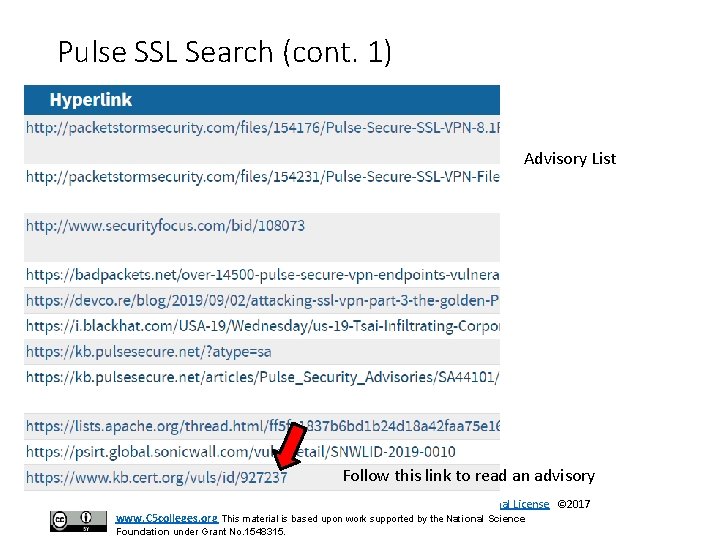
Pulse SSL Search (cont. 1) Advisory List Follow this link to read an advisory This document is licensed with a Creative Commons Attribution 4. 0 International License © 2017 www. C 5 colleges. org This material is based upon work supported by the National Science Foundation under Grant No. 1548315.
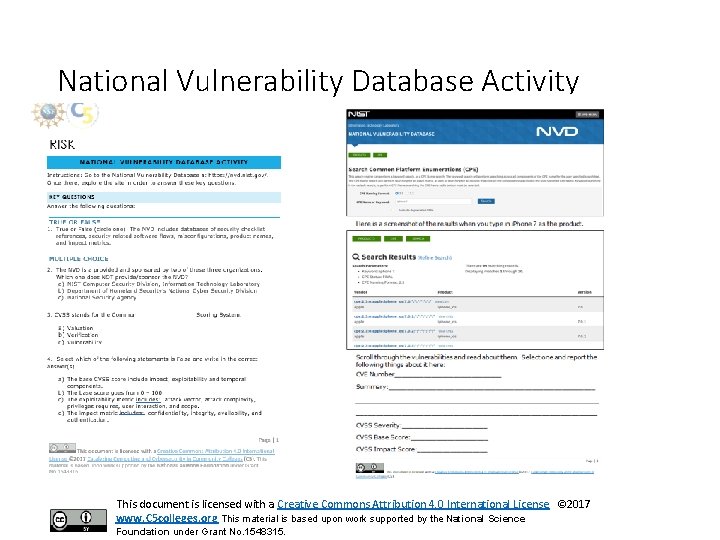
National Vulnerability Database Activity This document is licensed with a Creative Commons Attribution 4. 0 International License © 2017 www. C 5 colleges. org This material is based upon work supported by the National Science Foundation under Grant No. 1548315.
Summary of Cybersecurity Risk Model. Vulnerabilities • Misuse happens because threats exploit vulnerabilities. • A vulnerability is a flaw or weakness in an information system that leaves it open to attack. • The weakness may have been introduced during design, implementation, operation or internal control. • An exploit is to take advantage of a vulnerability. • Threats are an event or condition that has the potential for causing loss and the undesirable consequences or impact from such loss. This document is licensed with a Creative Commons Attribution 4. 0 International License © 2017 www. C 5 colleges. org This material is based upon work supported by the National Science Foundation under Grant No. 1548315.
Warm Up Activity: Do you have any Io. T devices in your home? If so, what do you know about the security of these devices? Examples of Io. T include: • • • Google Home, Amazon Alexa Smart bulbs Ring doorbell Keyless entry or smartlock Garage door and window blinds automation Webcams or surveillance cameras Fitbit or Smart watches Nest thermostat Smart television Smart kitchen appliances Medical devices This document is licensed with a Creative Commons Attribution 4. 0 International License © 2017 www. C 5 colleges. org This material is based upon work supported by the National Science Foundation under Grant No. 1548315.
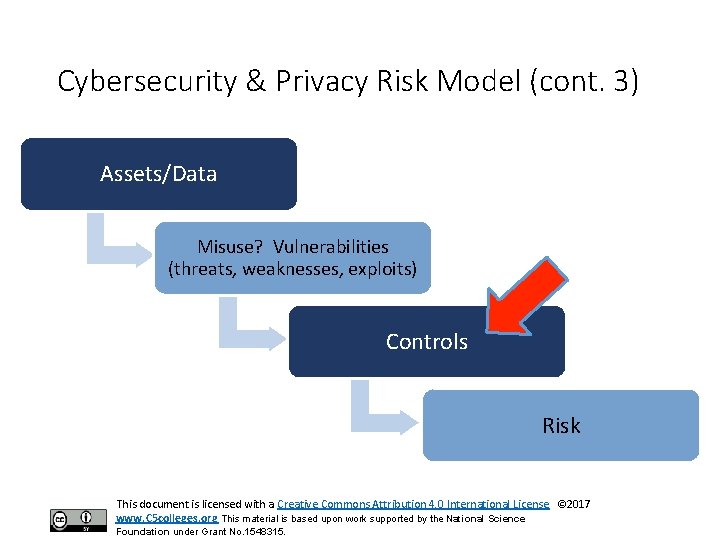
Cybersecurity & Privacy Risk Model (cont. 3) Assets/Data Misuse? Vulnerabilities (threats, weaknesses, exploits) Controls Risk This document is licensed with a Creative Commons Attribution 4. 0 International License © 2017 www. C 5 colleges. org This material is based upon work supported by the National Science Foundation under Grant No. 1548315.

NIST Io. T Security Video NIST Video, “What is the Internet of Things (Io. T) and how can we secure it? ” URL https: //youtu. be/H_X 6 IP 1 -NDc This document is licensed with a Creative Commons Attribution 4. 0 International License © 2017 www. C 5 colleges. org This material is based upon work supported by the National Science Foundation under Grant No. 1548315.
Controls • Privacy is the right of a party to maintain control over and confidentiality of information about itself. It is freedom from intrusion into the private life or affairs of an individual when that intrusion results from undue or illegal gathering and use of data about that individual. (NIST Glossary) • Security can be defined as “the quality or state of being secure: such as freedom from danger: safety” or as “something that secures: protection. ” (Merriam-Webster) • In order to protect our information assets (information and information systems), we can provide security and privacy controls where needed. This document is licensed with a Creative Commons Attribution 4. 0 International License © 2017 www. C 5 colleges. org This material is based upon work supported by the National Science Foundation under Grant No. 1548315.
What security controls are used in a home? This document is licensed with a Creative Commons Attribution 4. 0 International License © 2017 www. C 5 colleges. org This material is based upon work supported by the National Science Foundation under Grant No. 1548315.
Putting Controls Together • The concept of “defense in depth” is of military strategy origins, where multiple controls at different layers are implemented to keep the asset secure/private. • When one layer fails, other controls are still in effect to mitigate the risk. • These controls are generally implemented in hardware, software, and people. Organization personnel must understand the threats, risks, and vulnerabilities associated with their job function. This document is licensed with a Creative Commons Attribution 4. 0 International License © 2017 www. C 5 colleges. org This material is based upon work supported by the National Science Foundation under Grant No. 1548315.
Defense in Depth or a Layered Defense • An organization may install anti-virus software at the network perimeter, on email servers, web servers, notebook computers, and workstations to maximize the number of safeguards that adversaries must penetrate before compromising the information system. • Redundant security mechanisms requires an attacker to circumvent each mechanism to gain access to a digital asset. This document is licensed with a Creative Commons Attribution 4. 0 International License © 2017 www. C 5 colleges. org This material is based upon work supported by the National Science Foundation under Grant No. 1548315.
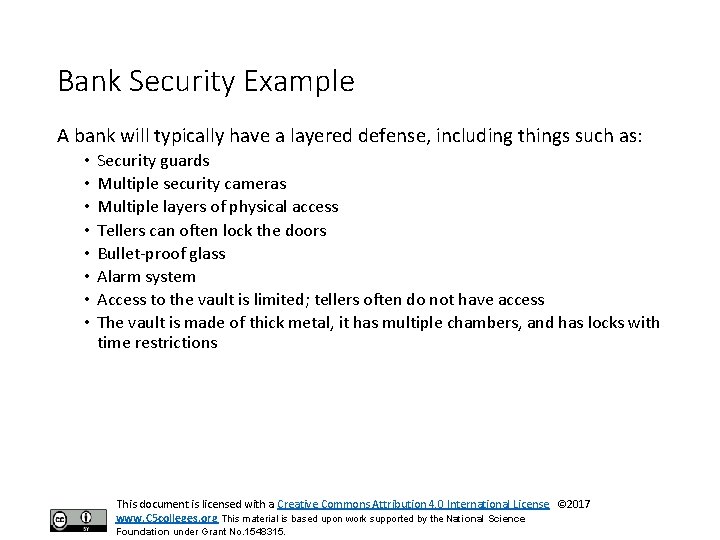
Bank Security Example A bank will typically have a layered defense, including things such as: • • Security guards Multiple security cameras Multiple layers of physical access Tellers can often lock the doors Bullet-proof glass Alarm system Access to the vault is limited; tellers often do not have access The vault is made of thick metal, it has multiple chambers, and has locks with time restrictions This document is licensed with a Creative Commons Attribution 4. 0 International License © 2017 www. C 5 colleges. org This material is based upon work supported by the National Science Foundation under Grant No. 1548315.
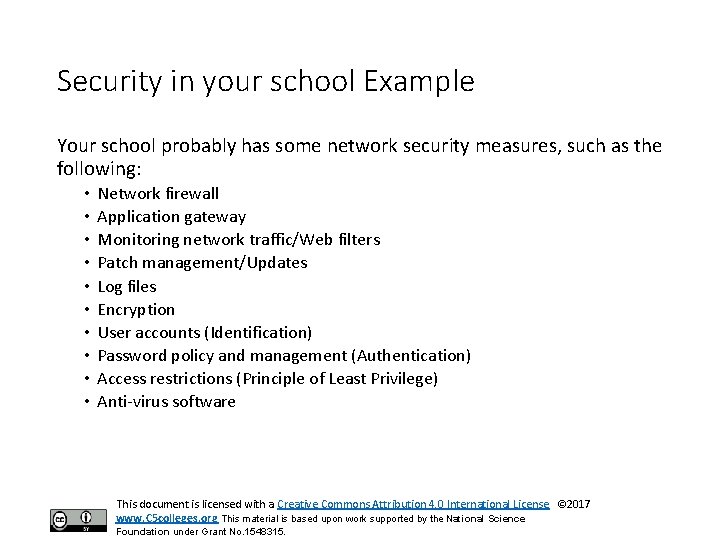
Security in your school Example Your school probably has some network security measures, such as the following: • • • Network firewall Application gateway Monitoring network traffic/Web filters Patch management/Updates Log files Encryption User accounts (Identification) Password policy and management (Authentication) Access restrictions (Principle of Least Privilege) Anti-virus software This document is licensed with a Creative Commons Attribution 4. 0 International License © 2017 www. C 5 colleges. org This material is based upon work supported by the National Science Foundation under Grant No. 1548315.
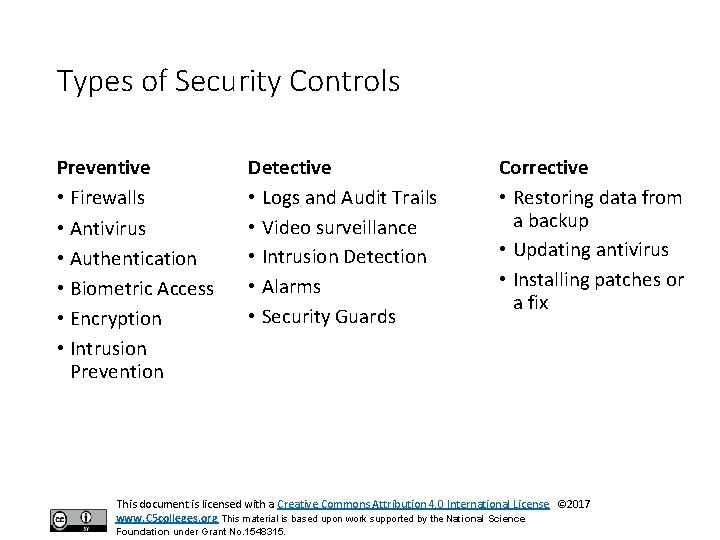
Types of Security Controls Preventive • Firewalls • Antivirus • Authentication • Biometric Access • Encryption • Intrusion Prevention Detective • Logs and Audit Trails • Video surveillance • Intrusion Detection • Alarms • Security Guards Corrective • Restoring data from a backup • Updating antivirus • Installing patches or a fix This document is licensed with a Creative Commons Attribution 4. 0 International License © 2017 www. C 5 colleges. org This material is based upon work supported by the National Science Foundation under Grant No. 1548315.
Defense in Depth Activity Step 1: Select one of the cybersecurity risk scenarios. Identify 5 controls from the list that could be used in a layered or “defense in depth” strategy. Refer to the activity handout This document is licensed with a Creative Commons Attribution 4. 0 International License © 2017 www. C 5 colleges. org This material is based upon work supported by the National Science Foundation under Grant No. 1548315.
Defense in Depth Activity (cont. 1) Step 2: Define each of the 5 controls that you selected in Step 1. Identify whether the control is preventive, detective, or corrective. Preventive measures are meant to deter. Detective measures identify so that corrective measures can be implemented. Corrective measures help mitigate damage. Refer to the activity handout This document is licensed with a Creative Commons Attribution 4. 0 International License © 2017 www. C 5 colleges. org This material is based upon work supported by the National Science Foundation under Grant No. 1548315.
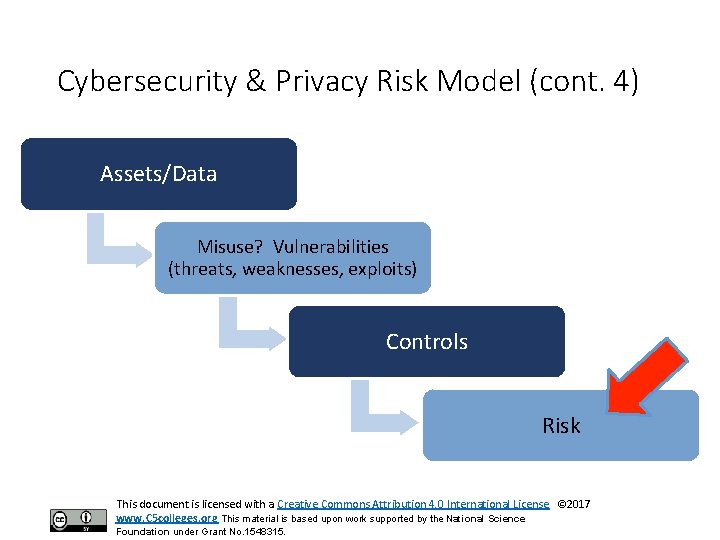
Cybersecurity & Privacy Risk Model (cont. 4) Assets/Data Misuse? Vulnerabilities (threats, weaknesses, exploits) Controls Risk This document is licensed with a Creative Commons Attribution 4. 0 International License © 2017 www. C 5 colleges. org This material is based upon work supported by the National Science Foundation under Grant No. 1548315.
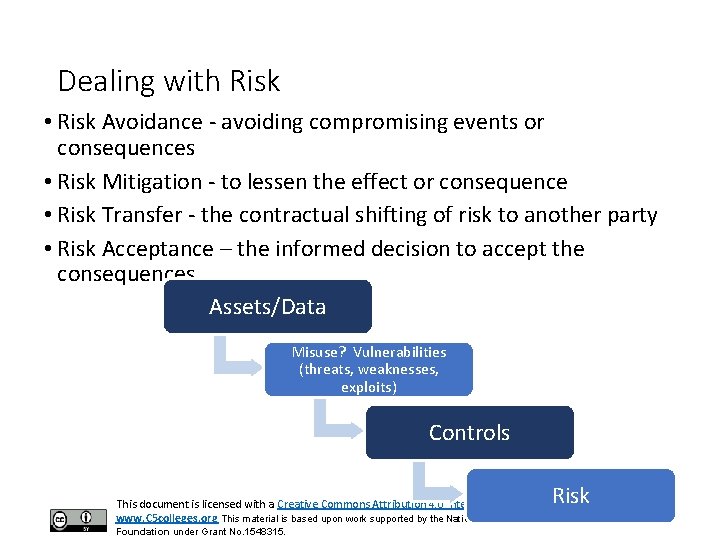
Dealing with Risk • Risk Avoidance - avoiding compromising events or consequences • Risk Mitigation - to lessen the effect or consequence • Risk Transfer - the contractual shifting of risk to another party • Risk Acceptance – the informed decision to accept the consequences Assets/Data Misuse? Vulnerabilities (threats, weaknesses, exploits) Controls Risk This document is licensed with a Creative Commons Attribution 4. 0 International License © 2017 www. C 5 colleges. org This material is based upon work supported by the National Science Foundation under Grant No. 1548315.
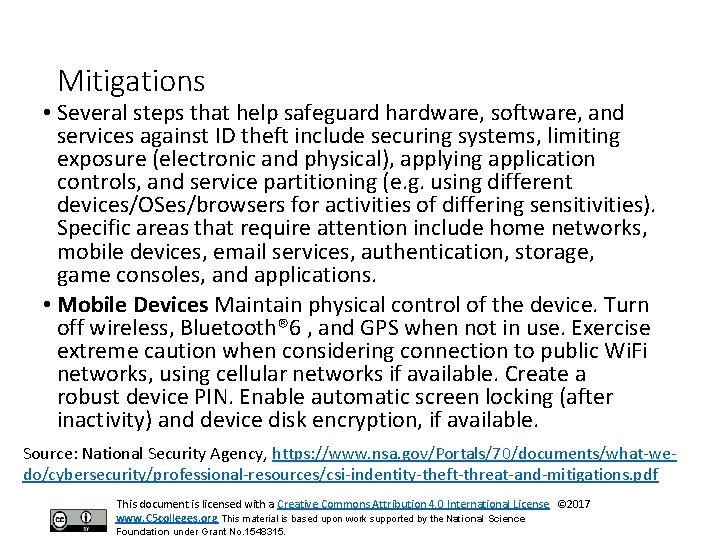
Mitigations • Several steps that help safeguard hardware, software, and services against ID theft include securing systems, limiting exposure (electronic and physical), applying application controls, and service partitioning (e. g. using different devices/OSes/browsers for activities of differing sensitivities). Specific areas that require attention include home networks, mobile devices, email services, authentication, storage, game consoles, and applications. • Mobile Devices Maintain physical control of the device. Turn off wireless, Bluetooth® 6 , and GPS when not in use. Exercise extreme caution when considering connection to public Wi. Fi networks, using cellular networks if available. Create a robust device PIN. Enable automatic screen locking (after inactivity) and device disk encryption, if available. Source: National Security Agency, https: //www. nsa. gov/Portals/70/documents/what-wedo/cybersecurity/professional-resources/csi-indentity-theft-threat-and-mitigations. pdf This document is licensed with a Creative Commons Attribution 4. 0 International License © 2017 www. C 5 colleges. org This material is based upon work supported by the National Science Foundation under Grant No. 1548315.
Mitigations (cont. 1) • Home Network Keep home network devices (e. g. Wi. Fi routers) patched and updated to help deal with the latest attacks and to protect against website drive-by infection. Use anti-virus and anti-malware software to help eliminate threats. Keep browsers and browser plug-ins up-to-date, enable automatic updates if possible, and disable Java™ 7 in the browser. Limit privileges (e. g. “guest” or “user” privileges) for accounts used by guests, children, and other daily accesses. Periodically change passwords and keep a higher level of complexity. Make sure wireless access points and domain name servers are secure using the most up-to-date methods. Source: National Security Agency, https: //www. nsa. gov/Portals/70/documents/what-wedo/cybersecurity/professional-resources/csi-indentity-theft-threat-and-mitigations. pdf This document is licensed with a Creative Commons Attribution 4. 0 International License © 2017 www. C 5 colleges. org This material is based upon work supported by the National Science Foundation under Grant No. 1548315.
Risk and ethical considerations • Read https: //www. darkreading. com /threat-intelligence/artificialintelligence-experts-talk-ethical -security-concerns/d/did/1330081 • Then watch https: //www. ted. com/talks/ja nelle_shane_the_danger_of_ai _is_weirder_than_you_think? l anguage=en#t-57175 • Discussion Questions: • What risk does AI bring? • Who are the stakeholders? • Where is accountability assigned? This document is licensed with a Creative Commons Attribution 4. 0 International License © 2017 www. C 5 colleges. org This material is based upon work supported by the National Science Foundation under Grant No. 1548315.
Cybersecurity Risk Challenges • It is difficult to know the capabilities and resources of adversaries. • The effectiveness of control measures varies. • It is difficult to determine the scope of damages after a successful attack. • The cost of security controls can be measured, but there is no reward for preventing attacks. This document is licensed with a Creative Commons Attribution 4. 0 International License © 2017 www. C 5 colleges. org This material is based upon work supported by the National Science Foundation under Grant No. 1548315.
Summary of Cybersecurity Risk Model-Security Controls • Cybersecurity risk is the possibility of injury, loss, or peril. • Misuse occurs when threats exploit vulnerabilities. • Vulnerabilities are flaws or weaknesses in an information system. • Controls mitigate the risk of a vulnerability being exploited. • Risk management is a fundamental principle of cybersecurity. This document is licensed with a Creative Commons Attribution 4. 0 International License © 2017 www. C 5 colleges. org This material is based upon work supported by the National Science Foundation under Grant No. 1548315.
References • https: //niccs. us-cert. gov/about-niccs/glossary#R. National Initiative for Cybersecurity Careers and Studies. • https: //nvlpubs. nist. gov/nistpubs/Legacy/SP/nistspecialpublication 8 00 -30 r 1. pdf • https: //csrc. nist. gov/projects/risk-managementframework-(RMF)-Overview • https: //www. nist. gov/cyberframework This document is licensed with a Creative Commons Attribution 4. 0 International License © 2017 www. C 5 colleges. org This material is based upon work supported by the National Science Foundation under Grant No. 1548315.
Catalyzing Computing and Cybersecurity in Community Colleges www. ncyte. net This material is based upon work supported by the National Science Foundation under Grant No. 1548315.
- Slides: 79