Personalized Cybersecurity for Dummies Mehrbod Sharifi Eugene Fink
Personalized Cybersecurity for Dummies Mehrbod Sharifi Eugene Fink Jaime G. Carbonell Application of machine learning and crowdsourcing to adapt cybersecurity tools to the needs of (naïve) individual users.
Individual user differences • Security needs - Data confidentiality - Data-loss tolerance - Recovery costs • Usage patterns • Computer knowledge Different users need different security tools.
Problems • Inflexible engineered solutions with “too much security” - Too high security at high costs - Insufficient customization • “Advanced user” assumption - Complicated customization - Unclear security warnings
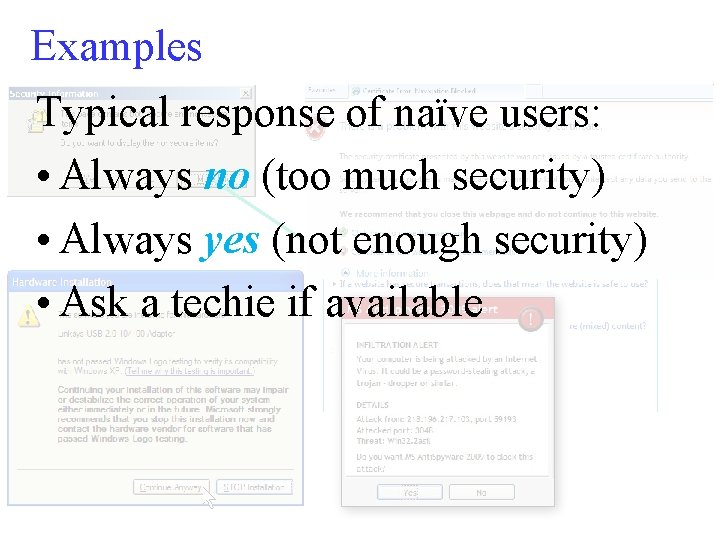
Examples Typical response of naïve users: • Always no (too much security) • Always yes (not enough security) • Ask a techie if available
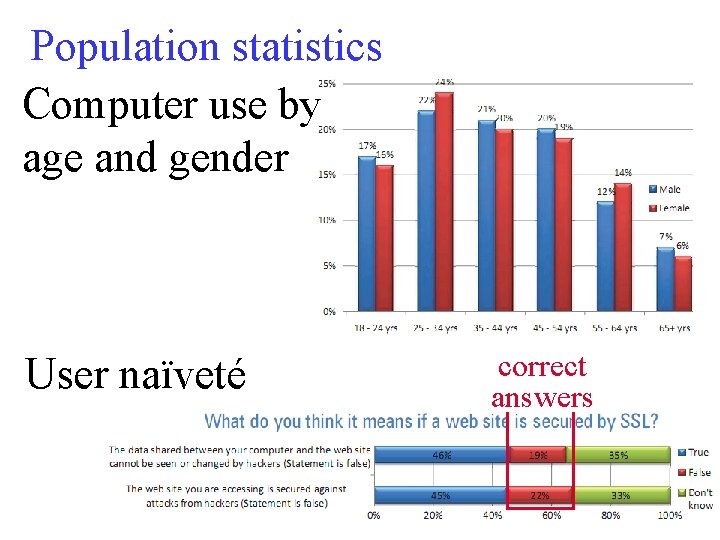
Population statistics Computer use by age and gender User naïveté correct answers

Population statistics • Almost everyone uses a computer • Most users are naïve, with very limited technical knowledge • Many security problems are due to the user naïveté When an average user deals with security issues, she needs basic advice and handholding.

Long-term goal We need an automated security assistant that learns the needs of the individual user and helps the user to apply security tools.
Initial results A security assistant for web browsing, integrated with Internet Explorer.
More problems Automated tools cannot detect “advanced” threats that go beyond software attacks. • Scams (welcome to Nigeria) • Rip-offs (overpricing, low quality) • Bad info (inaccurate, biased) • . . . and so on

Long-term goal Rely on the collective wisdom of the users. Gather Filter Integrate
Initial results A browser plug-in for the gathering of opinions and warnings about web pages.
Future research • Summarization of comments • Analysis of sentiments and biases • Identification of reliable contributors • Synergy with other techniques for analysis of web pages • … and so on
- Slides: 12