Know Your Cyber Security Trivia Game Brought to

Know Your Cyber Security Trivia Game Brought to you by the National Cyber Security Alliance (NCSA), the Cybersecurity and Critical Infrastructure Security Agency (CISA), and Do. IT.

Know Your Cyber Security Trivia Game #Be. Cyber. Smart: Online Safety Device Security Types of Cyber Attacks Cyber History Cyber Stats 100 100 100 200 200 200 300 300 300 400 400 400 500 500 500 Final Round 2
#Be. Cyber. Smart: Online Safety - 100 You post a picture of you and your best friend to your favorite social media platform. She doesn’t feel comfortable with the image, so you agree to take it down. Will this ensure that no one else sees the picture? Answer: No. Once an image (or any information) is posted on the internet, it is virtually impossible to remove it from circulation. Taking it off of your social media page will help, but there is no guarantee that others have not already seen it and/or downloaded it to their own machines. After. Click each anywhere answer appears, please to Game Board. on slide toreturn display answer Back to game board 3
#Be. Cyber. Smart: Online Safety - 200 You receive an email from an online shopping site claiming that you were incorrectly charged for your last purchase and are due a refund. The email asks you to click a link where you will submit the necessary information. What should you do? Answer: Do NOT click the link! Check the sender’s address and search the document for spelling/grammar mistakes. If you notice anything suspicious, the email is likely a scam. Even if it seems legitimate, navigate to the site yourself rather than clicking any links. After. Click each answer appears, pleasetoreturn to Game Board. anywhere on slide display answer Back to game board 4
#Be. Cyber. Smart: Online Safety - 300 You’ve just settled into your hotel room when you realize you need to transfer some funds from your savings account to your checking account. In order to do this, you will need to use your laptop. Should you connect to the hotel’s public Wi-Fi and log in to your online bank? Answer: It depends. In general, it is never safe to transmit PII (Personally Identifiable Information), especially financial information, over a public network. If you find yourself in a situation where you may need to do so, first consider all your options, including using your mobile data or a VPN (Virtual Private Network) to help protect your browsing. After. Click each answer appears, pleasetoreturn to Game Board. anywhere on slide display answer Back to game board 5
#Be. Cyber. Smart: Online Safety - 400 You have a long commute. Thankfully, your train just installed public Wi-Fi. Now you can listen to your favorite music or podcast. However, when you check for social media updates around lunch, you find that your account has been hacked. What steps could you take to prevent your mobile device or laptop data from being compromised in the future? Answer(s): • Turn off Wi-Fi and Bluetooth when not using them. These leave you open to remote attacks. • Make sure the network is legitimate. Hackers love creating fake Wi-Fi networks that mimic real ones, enticing unsuspecting users to log on. • Don’t connect. Though perhaps drastic, one near-certain way to circumvent the dangers of public Wi-Fi is simply to avoid using it whenever possible. After. Click each answer appears, pleasetoreturn to Game Board. anywhere on slide display answer Back to game board 6
#Be. Cyber. Smart: Online Safety - 500 Passwords often have complex requirements, and most people will need to remember numerous different passwords to access their internet services. What is a way to help you keep track of all these different passwords? Answer: Use a password manager. These are apps, devices, or cloud services that store your passwords in an encrypted vault that can only be unlocked with a single master password. After. Click each answer appears, pleasetoreturn to Game Board. anywhere on slide display answer Back to game board 7
Device Security - 100 Which of the following are strong password practices? (Choose all that apply. ) 1. Passwords should contain a mixture of upper and lower case letters, numbers, and special characters. 2. Passwords should have personal meaning to you (e. g. a relative’s birthday) so that you can remember them more easily. 3. You should immediately change your password in the case of a known data breach. 4. You should store your passwords on paper or in a text document, giving you a backup in the event that you forget them. Answer: 1 & 3. While it is helpful for passwords to have some level of personal relevance, anything concrete or publicly-available can be easily researched and guessed by an attacker. Storing your passwords physically or in a text-document is also ill-advised, as someone could gain access to the copy. After. Click each answer appears, pleasetoreturn to Game Board. anywhere on slide display answer Back to game board 8
Device Security - 200 True or false: Automatically updating your machine poses a significant security concern, as it could install unwanted programs/features that disrupt your network or harm your computer. Answer: False. Although updates can occasionally cause problems, they also contain vital patches to help protect your machine against attackers. Keep your machine up-to-date and install new patches as soon as possible. Don’t click, “Remind me later, ” twelve times. After. Click each answer appears, pleasetoreturn to Game Board. anywhere on slide display answer Back to game board 9
Device Security - 300 True or false: Although they operate similarly to computers, most mobile devices (cell phones, tablets, etc. ) are not full computers and do not require software, such as anti-virus, to be secure. Answer: False. Almost all consumer devices, especially cell phones and tablets, are simply miniature computers. They contain important data (contacts, financial information, calendars) and require protection like any other device. After. Click each answer appears, pleasetoreturn to Game Board. anywhere on slide display answer Back to game board 10
Device Security - 400 Which of the following devices could potentially be exploited by an attacker? • • • Desktop computer Laptop computer Cell phone Television Remote-controlled keys • • • Tablet Security camera Pacemaker Baby monitor Thermostat • Refrigerator • GPS • Digital Assistant • Toaster Answer: All of them. Yes, even the toaster – possibly. After each answer appears, please return to Game Board. Click anywhere on slide to display answer Back to game board 11
Device Security - 500 What is the method of access control by which users must present multiple, separate pieces of identification, such as a password and keycard, in order to access a system? Answer: Multi-Factor Authentication (MFA). MFA greatly increases the security of access control. Even if a password is learned or an ID is stolen, it will not be enough to compromise a system. Many online services allow MFA options, such as requiring a one-time login code as well as a password. After. Click each answer appears, pleasetoreturn to Game Board. anywhere on slide display answer Back to game board 12
Types of Cyber Attacks - 100 A scammer creates a fake email and sends it to thousands of people, hoping some of them will click on a link and give up their personal information. What is this type of attack called? Answer: Phishing is a type of social engineering that often manipulates human impulses, such as greed, fear, or the desire to help others. After. Click each answer appears, pleasetoreturn to Game Board. anywhere on slide display answer Back to game board 13
Types of Cyber Attacks - 200 What is the term for harmful software that seeks to damage or exploit the machines that run it? Answer: Malware. This stands for “malicious software, ” and refers to a large variety of software-based attacks. After. Click each answer appears, pleasetoreturn to Game Board. anywhere on slide display answer Back to game board 14
Types of Cyber Attacks - 300 An attacker goes to a local coffee shop and creates a wireless network using the shop’s name, hoping unsuspecting customers will log on. What is this type of attack called? Answer: Spoofing. This kind of attack can come in many forms (email, GPS, caller ID), but is most commonly known with regards to fake and malicious wireless networks. Before logging onto a public network, be sure it is the correct one. After. Click each answer appears, pleasetoreturn to Game Board. anywhere on slide display answer Back to game board 15
Types of Cyber Attacks - 400 You bring your laptop to a local restaurant. Without your knowledge, the customer at the table behind you watches you log in to your email, thereby learning your username and password. What is this type of attack called? Answer: Shoulder surfing. It is important to remember that not all cyber attacks require the direct manipulation of technology. Attackers can often obtain important information by simply observing people, asking questions, or piecing together dissociated facts to learn or guess something private. After. Click each answer appears, pleasetoreturn to Game Board. anywhere on slide display answer Back to game board 16
Types of Cyber Attacks - 500 After clicking an advertisement on an unsecure website, your computer freezes. A message appears, demanding you pay a certain amount of money to unlock your computer. What is this type of attack called? Answer: Ransomware. This type of attack has grown more common in recent years, especially againstitutions that need to recover their data as soon as possible, such as medical facilities and local government agencies. After. Click each answer appears, pleasetoreturn to Game Board. anywhere on slide display answer Back to game board 17
Cyber History - 100 This entrepreneur is widely-known for his contributions to the personal computer industry. He founded the Microsoft Corporation in 1975, with his business partner Paul Allen. Answer: Bill Gates. After. Click each answer appears, pleasetoreturn to Game Board. anywhere on slide display answer Back to game board 18
Cyber History - 200 Which United States federal agency has been tasked with improving national cybersecurity and protecting the nation’s critical infrastructure? Answer: The Department of Homeland Security. Specifically, the Cybersecurity and Infrastructure Security Agency (CISA), which is responsible for protecting the Nation’s critical infrastructure from physical and cyber threats. After. Click each answer appears, pleasetoreturn to Game Board. anywhere on slide display answer Back to game board 19
Cyber History - 300 This English cryptanalyst is famous for deciphering encoded messages during World War II and creating standards for artificial intelligence. He is considered by many to be the father of theoretical computing. (Hint: There was a 2014 movie based on his biography. ) Answer: Alan Turing helped the Allies by cracking intercepted messages from the German forces, gleaning information that was crucial to an Allied victory. He also created the “Turing test, ” which examines a machine’s ability to display human behavior à la artificial intelligence. After. Click each answer appears, pleasetoreturn to Game Board. anywhere on slide display answer Back to game board 20
Cyber History - 400 This English writer and mathematician is known for her work on the Analytical Engine and is considered to be one of the first computer programmers. Answer(s): Ada Lovelace Ada worked alongside Charles Babbage in the 1840 s to publish the first computer-based algorithm. After. Click each answer appears, pleasetoreturn to Game Board. anywhere on slide display answer Back to game board 21
Cyber History - 500 In May 2017, this worldwide cyber attack used ransomware to exploit approximately 200, 000 unpatched machines, resulting in damages totaling to over $4, 000, 000 (4 billion USD). Answer: Wanna. Cry. This ransomware attack propagated through an exploit called Eternal. Blue, which took advantage of older Windows systems. Targeted machines had their data involuntarily encrypted, with a demand of Bitcoin payment for the decryption key needed to get the data back. After. Click each answer appears, pleasetoreturn to Game Board. anywhere on slide display answer Back to game board 22
Cyber Stats - 100 Approximately how many attempted cyber attacks are reported to the Pentagon every day? (Closest answer wins. ) Answer: Over 10 million. After. Click each answer appears, pleasetoreturn to Game Board. anywhere on slide display answer Back to game board 23
Cyber Stats - 200 How many unfilled cybersecurity jobs are there in the United States alone? (Closest answer wins. ) Answer: 313, 735 Drill into the data by Cyber. Seek at https: //www. cyberseek. org/heatmap. html. After. Click each answer appears, pleasetoreturn to Game Board. anywhere on slide display answer Back to game board 24
Cyber Stats - 300 Globally, how many unfilled cybersecurity positions are there estimated to be by 2022? (Closest answer wins. ) Answer: 1. 8 Million Read the report by the International Information Systems Security Certification Consortium, Inc. (ISC 2) at https: //www. isc 2. org/News-and-Events/Press-Room/Posts/2017/02/13/Cybersecurity. Workforce-Shortage-Continues-to-Grow-Worldwide After. Click each answer appears, pleasetoreturn to Game Board. anywhere on slide display answer Back to game board 25

Cyber Stats - 400 What is the estimated cost of a successful phishing attack on a single small or medium-sized business? (Closest answer wins. ) Answer: $1. 6 Million USD. After. Click each answer appears, pleasetoreturn to Game Board. anywhere on slide display answer Back to game board 26
Cyber Stats - 500 What is the estimated global cost of cybercrime by the end of 2019? (Closest answer wins). Answer: $2 Trillion USD. After. Click each answer appears, pleasetoreturn to Game Board. anywhere on slide display answer Back to game board 27
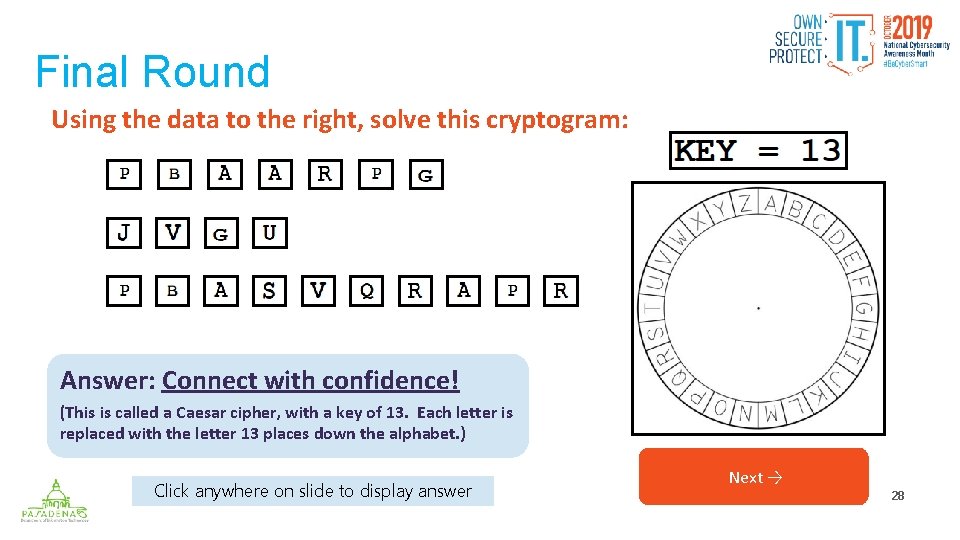
Final Round Using the data to the right, solve this cryptogram: Answer: Connect with confidence! (This is called a Caesar cipher, with a key of 13. Each letter is replaced with the letter 13 places down the alphabet. ) Click anywhere on slide to display answer Next → 28
Thanks for playing! Visit https: //niccs. us-cert. gov/national-cybersecurity-awareness-month-2019 to learn more about NCSAM 2019 and how you can get involved. Back to game board
- Slides: 29