Critical Infrastructure Cybersecurity Module 11 Trends Except where
Critical Infrastructure Cybersecurity Module 11 Trends Except where otherwise noted, this presentation is licensed under a Creative Commons Attribution 4. 0 International License. © 2017 Cyber. Watch West, Whatcom Community College.
Lesson Objectives • Identify emerging trends and demonstrate an understanding of emerging technologies. • Understand the Internet of Things (Io. T) and how it expands the cyber “attack surface. ” • Be able to make educated predictions of what the future might look like for the cybersecurity critical infrastructure framework. • Discuss ethical issues that can arise in relation to new technology and new defense strategies. Except where otherwise noted, this presentation is licensed under a Creative Commons Attribution 4. 0 International License. © 2017 Cyber. Watch West, Whatcom Community College.
Critical Infrastructure Threat Trends Attacks on critical infrastructure systems continue to evolve and multiply. These include: ◦ Increased number of data integrity attacks ◦ Multiple Advanced Persistent Threat (APT) actors on the system ◦ Compromised infrastructure ◦ Many are covertly communicating data to embargoed countries ◦ Increased use of social engineering ◦ Growing attack surface with the Internet of Things (Io. T) Except where otherwise noted, this presentation is licensed under a Creative Commons Attribution 4. 0 International License. © 2017 Cyber. Watch West, Whatcom Community College.
Data Integrity Attacks "If you take a controlled system like the power grid or water system that involves machinery that's operated by computers and make some change in the operational instructions for that equipment, that can lead to some catastrophic results — power outages or changes in chemical balance. “ —Eddie Schwartz, international vice president, ISACA Rather than be satisfied with denial-of-service attacks that make the system unavailable, attackers will increasingly launch attacks that include modification of machine instructions or data sets that cause equipment to act on skewed data. Except where otherwise noted, this presentation is licensed under a Creative Commons Attribution 4. 0 International License. © 2017 Cyber. Watch West, Whatcom Community College.
Multiple Advanced Persistent Threats • An advanced persistent threat (APT) is a network attack in which an attacker gains unauthorized access and remains for a long period of time, undetected. • Agencies are seeing multiple attackers on networks, sometimes warring with each other for dominance over the compromised system. • This has given rise to research efforts to develop operating systems that can securely continue to operate, even with the presence of APTs on the network. Except where otherwise noted, this presentation is licensed under a Creative Commons Attribution 4. 0 International License. © 2017 Cyber. Watch West, Whatcom Community College.
Compromised Infrastructure • Critical infrastructure systems will be compromised and used to launch attacks against other systems. • This is facilitated, in part, by the lack of security hardening on sensors and devices. In many cases, these devices and systems have been found to have default passwords or vulnerable legacy software in use. • In some cases, systems are covertly communicating data, some of which is even encrypted, to embargoed countries. Except where otherwise noted, this presentation is licensed under a Creative Commons Attribution 4. 0 International License. © 2017 Cyber. Watch West, Whatcom Community College.
Increased Use of Social Engineering • People will continue to be “the weak link” in the security chain. Historically, as systems become hardened, making them more difficult to hack into through system vulnerabilities, attacks against personnel in the workforce increase. • Spear-phishing attacks contributed to a significant number of attacks against the manufacturing sector in 2015, according to ICS-CERT. Except where otherwise noted, this presentation is licensed under a Creative Commons Attribution 4. 0 International License. © 2017 Cyber. Watch West, Whatcom Community College.
Growing Attack Surface with the “Internet of Things” Io. T expands the attack surface and diversifies threat types with billions of connected devices. ◦ Secure and insecure locations ◦ Security may or may not be built in ◦ Not IT – but usually connected to the network ◦ New bleeding-edge protocols and technologies in use ◦ The small nature of the devices leave many vulnerable to attack Except where otherwise noted, this presentation is licensed under a Creative Commons Attribution 4. 0 International License. © 2017 Cyber. Watch West, Whatcom Community College.
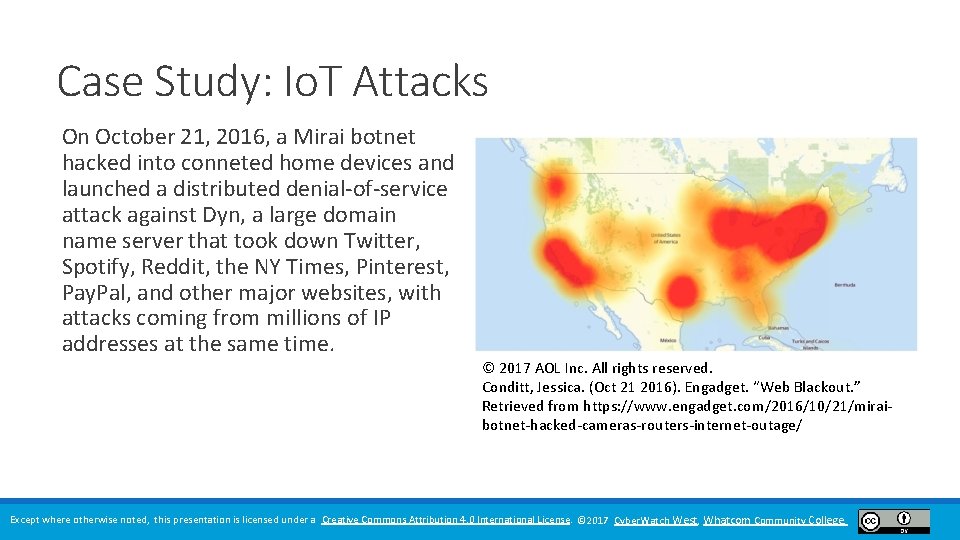
Case Study: Io. T Attacks On October 21, 2016, a Mirai botnet hacked into conneted home devices and launched a distributed denial-of-service attack against Dyn, a large domain name server that took down Twitter, Spotify, Reddit, the NY Times, Pinterest, Pay. Pal, and other major websites, with attacks coming from millions of IP addresses at the same time. © 2017 AOL Inc. All rights reserved. Conditt, Jessica. (Oct 21 2016). Engadget. “Web Blackout. ” Retrieved from https: //www. engadget. com/2016/10/21/miraibotnet-hacked-cameras-routers-internet-outage/ Except where otherwise noted, this presentation is licensed under a Creative Commons Attribution 4. 0 International License. © 2017 Cyber. Watch West, Whatcom Community College.
Case Study 2: Io. T Attacks Mirai is a malicious worm that spreads to connected Internet devices, such as cameras, insecure routers, digital video recorders, etc. , by continuously scanning the Internet for these systems, looking for devices that have not changed their factory default passwords. Once compromised, these devices are turned into “bots” that allow an attacker to control them to attack other systems. In September 2016, a massive Mirai attack took down security site Krebson. Security, peaking at nearly 620 Gbps. In that case, more than 145, 000 devices were compromised and used in the attack. Except where otherwise noted, this presentation is licensed under a Creative Commons Attribution 4. 0 International License. © 2017 Cyber. Watch West, Whatcom Community College.
Move to “Active Defense” • Traditional incident response processes, while a significant part of an organization’s security program, are reactive in nature. • In response to the increase of highly sophisticated attacks and vulnerable attack surfaces, and the rapidity of attacks, organizations and agencies are adopting more proactive measures, known as “active defense. ” • Active defense takes into consideration threat intelligence information (information about threats that is collected, analyzed, and shared among communities) to rapidly act on threat information. Except where otherwise noted, this presentation is licensed under a Creative Commons Attribution 4. 0 International License. © 2017 Cyber. Watch West, Whatcom Community College.
Active Defense Components An active defense relies on the following components: ◦ Identification of mission-critical assets and systems that will be targets of attack ◦ Identification of “threat actors, ” or those who would be most likely to attack these assets ◦ Knowledge of attacker tactics, techniques, and procedures (TTPs), identifying the methods that would be used by the attacker to attack the asset Using this knowledge, the organization can take steps to fortify (harden) the assets, increasing monitoring for anomalous events at vulnerable assets, installing additional security devices, such as firewalls, Intrusion Prevention Systems, or honeypots (the installation of fake servers designed to deceive or redirect attacker activities). Except where otherwise noted, this presentation is licensed under a Creative Commons Attribution 4. 0 International License. © 2017 Cyber. Watch West, Whatcom Community College.
Ethical Issues Ethical and privacy issues are arising on a daily basis with critical infrastructure protection. Some of these issues include: ◦ The use of unmanned aerial vehicles (UAVs, or drones) to monitor critical infrastructure assets, such as oil pipelines, bridges, or power lines. This technology could be abused to spy on individuals, collecting unauthorized data. (Infosec Institute, 2014) ◦ Existing data privacy standards do not translate well into Io. T. A Hewlett-Packard study performed in 2014 found that “more than 90 percent of all Io. T devices examined collected at least one piece of personal information. ” Of these devices, over 70% lacked sufficient authentication to the data on the device, as well as lacked encryption. (NSTAC, 2014) Can you think of other ethical issues associated with different sectors, such as the Financial Services Sector or the Healthcare and Public Health Sector? Except where otherwise noted, this presentation is licensed under a Creative Commons Attribution 4. 0 International License. © 2017 Cyber. Watch West, Whatcom Community College.
Privacy-by-Design Implement privacy-by-design at project initiation. Privacy-by-design provides standards for: ◦ Privatizing, or anonymizing, data at collection so that it is collected anonymously but data can still be aggregated for analysis. ◦ NIST has begun a privacy engineering initiative, integrating the Fair Information Practice Principles (FIPPS) to risk management frameworks. This provides an excellent example of government and private sector collaboration to arrive at a solution. (NSTAC, 2014) Except where otherwise noted, this presentation is licensed under a Creative Commons Attribution 4. 0 International License. © 2017 Cyber. Watch West, Whatcom Community College.
Cyber. Watch West Is funded by a National Science Foundation Advanced Technology Education Grant and is located at Whatcom Community College 237 West Kellogg Road Bellingham, WA 98226 T: 360. 383. 3176 www. cyberwatchwest. org Except where otherwise noted, this presentation is licensed under a Creative Commons Attribution 4. 0 International License. © 2017 Cyber. Watch West, Whatcom Community College.
- Slides: 15