CS 5323 Cryptography Basics and Symmetric Cryptography Prof
CS 5323 Cryptography Basics and Symmetric Cryptography Prof. Ravi Sandhu Executive Director and Endowed Chair Lecture 2 ravi. utsa@gmail. com www. profsandhu. com © Ravi Sandhu World-Leading Research with Real-World Impact! 1
Basic Concepts © Ravi Sandhu World-Leading Research with Real-World Impact! 2
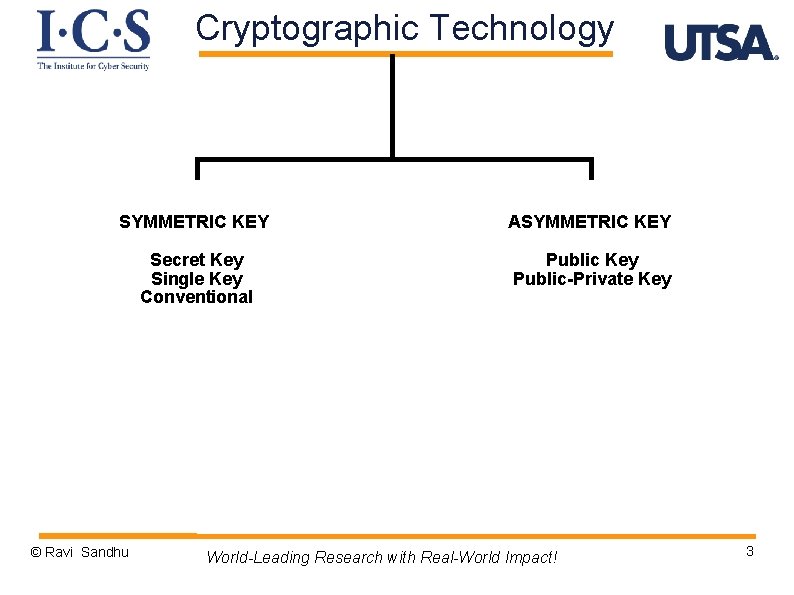
Cryptographic Technology SYMMETRIC KEY ASYMMETRIC KEY Secret Key Single Key Conventional Public Key Public-Private Key © Ravi Sandhu World-Leading Research with Real-World Impact! 3
Cryptographic Technology Ø Ø Ø Ø Symmetric-key encryption Symmetric-key message authentication codes (MACs) Public-key encryption Public-key digital signatures Public-key agreement Message digests (hash functions) Public-key certificates Challenge-response authentication © Ravi Sandhu World-Leading Research with Real-World Impact! 4
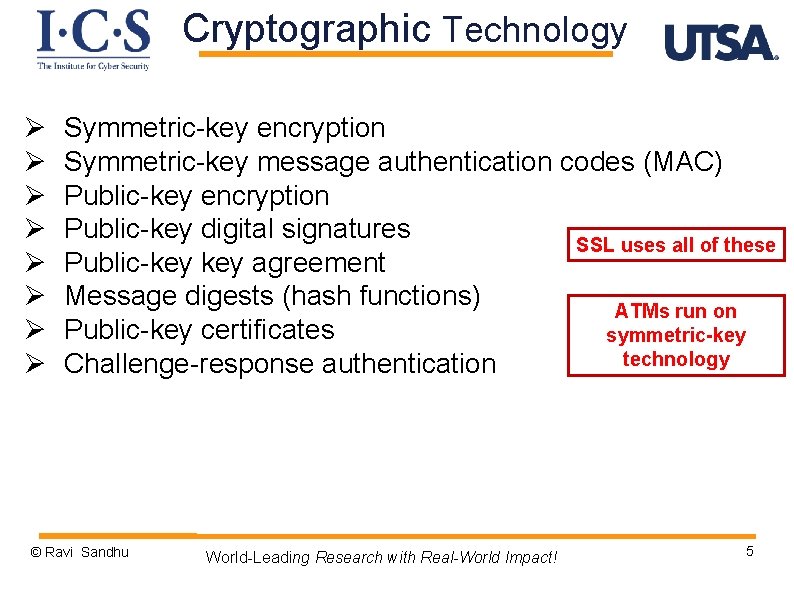
Cryptographic Technology Ø Ø Ø Ø Symmetric-key encryption Symmetric-key message authentication codes (MAC) Public-key encryption Public-key digital signatures SSL uses all of these Public-key agreement Message digests (hash functions) ATMs run on Public-key certificates symmetric-key technology Challenge-response authentication © Ravi Sandhu World-Leading Research with Real-World Impact! 5
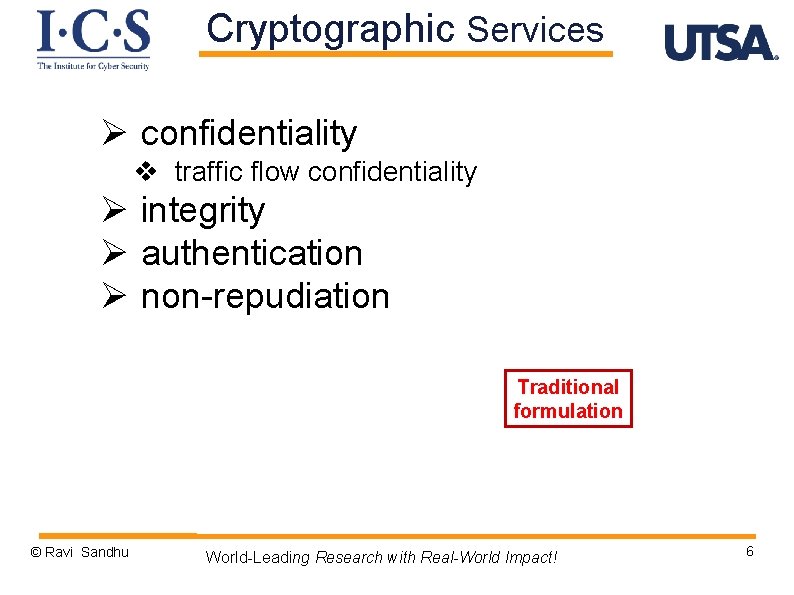
Cryptographic Services Ø confidentiality v traffic flow confidentiality Ø integrity Ø authentication Ø non-repudiation Traditional formulation © Ravi Sandhu World-Leading Research with Real-World Impact! 6
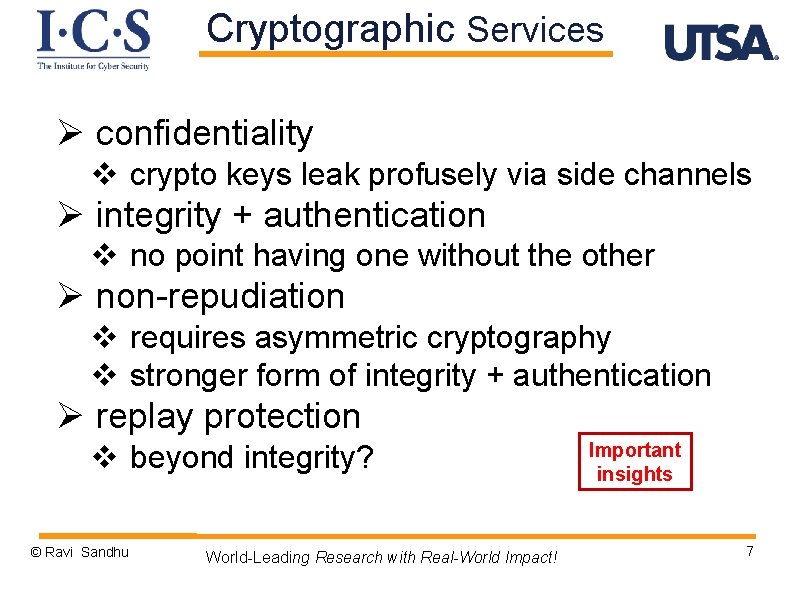
Cryptographic Services Ø confidentiality v crypto keys leak profusely via side channels Ø integrity + authentication v no point having one without the other Ø non-repudiation v requires asymmetric cryptography v stronger form of integrity + authentication Ø replay protection v beyond integrity? © Ravi Sandhu World-Leading Research with Real-World Impact! Important insights 7
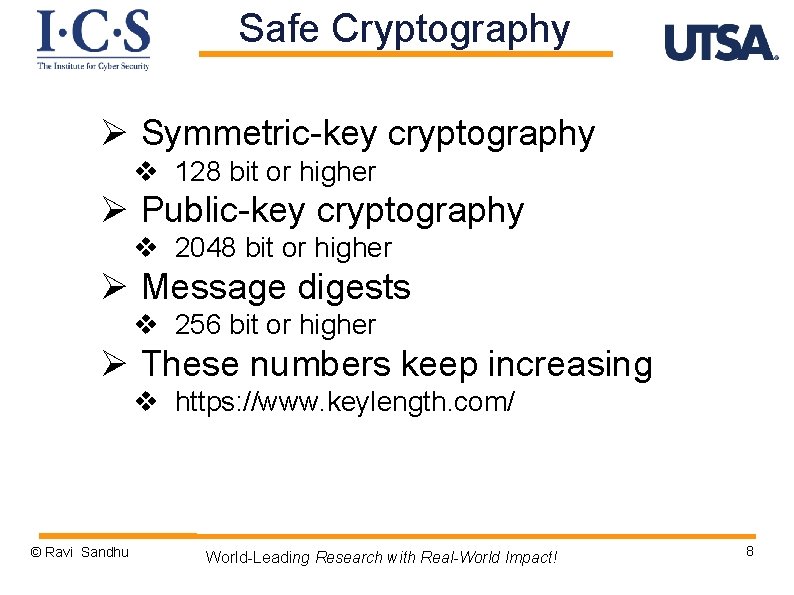
Safe Cryptography Ø Symmetric-key cryptography v 128 bit or higher Ø Public-key cryptography v 2048 bit or higher Ø Message digests v 256 bit or higher Ø These numbers keep increasing v https: //www. keylength. com/ © Ravi Sandhu World-Leading Research with Real-World Impact! 8
Symmetric Encryption © Ravi Sandhu World-Leading Research with Real-World Impact! 9
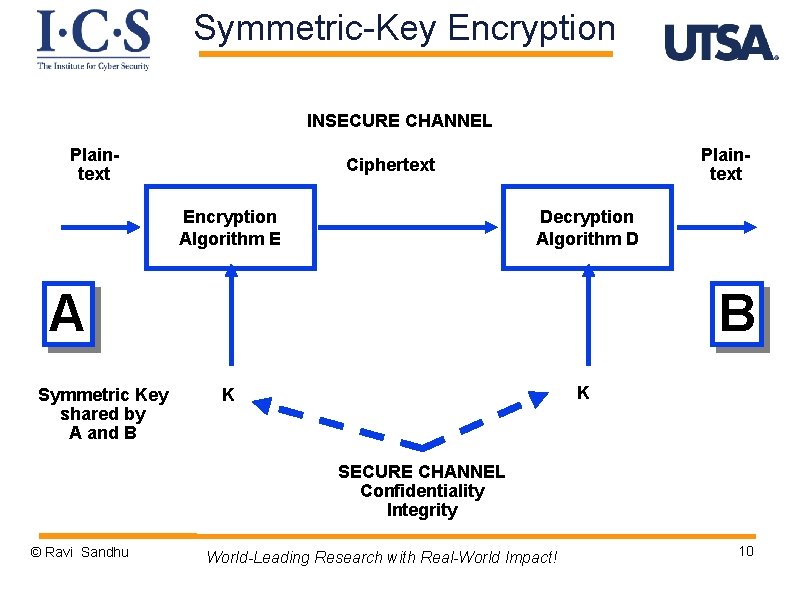
Symmetric-Key Encryption INSECURE CHANNEL Plaintext Ciphertext Encryption Algorithm E Decryption Algorithm D A Symmetric Key shared by A and B B K K SECURE CHANNEL Confidentiality Integrity © Ravi Sandhu World-Leading Research with Real-World Impact! 10
Symmetric-Key Encryption Ø confidentiality depends only on secrecy of the key v size of key is critical Ø Symmetric key systems do not scale well v with N parties we need to generate and distribute N*(N -1)/2 keys Ø A and B can be people or computers © Ravi Sandhu World-Leading Research with Real-World Impact! 11
Master Keys and Session Keys Ø master keys, long lifetime v prolonged use increases exposure Ø session keys v short-term keys communicated by means of § § © Ravi Sandhu master symmetric keys public key technology World-Leading Research with Real-World Impact! 12
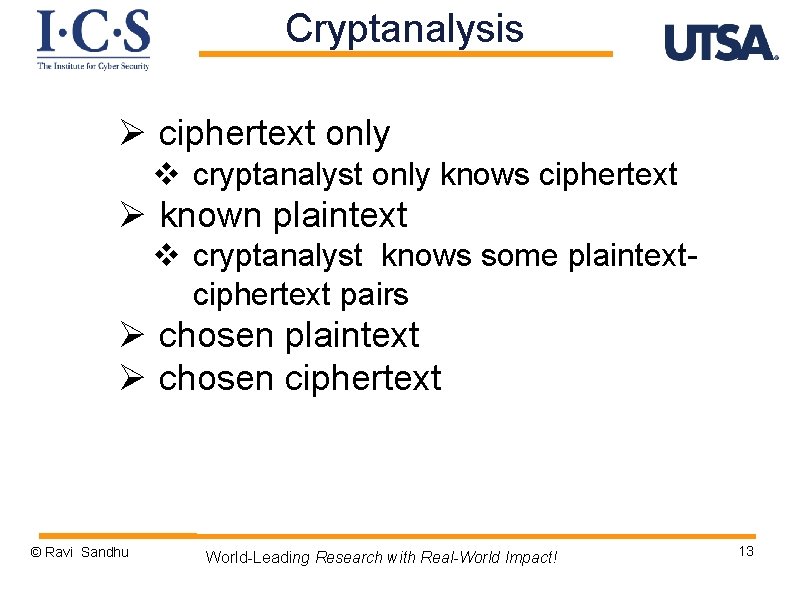
Cryptanalysis Ø ciphertext only v cryptanalyst only knows ciphertext Ø known plaintext v cryptanalyst knows some plaintextciphertext pairs Ø chosen plaintext Ø chosen ciphertext © Ravi Sandhu World-Leading Research with Real-World Impact! 13
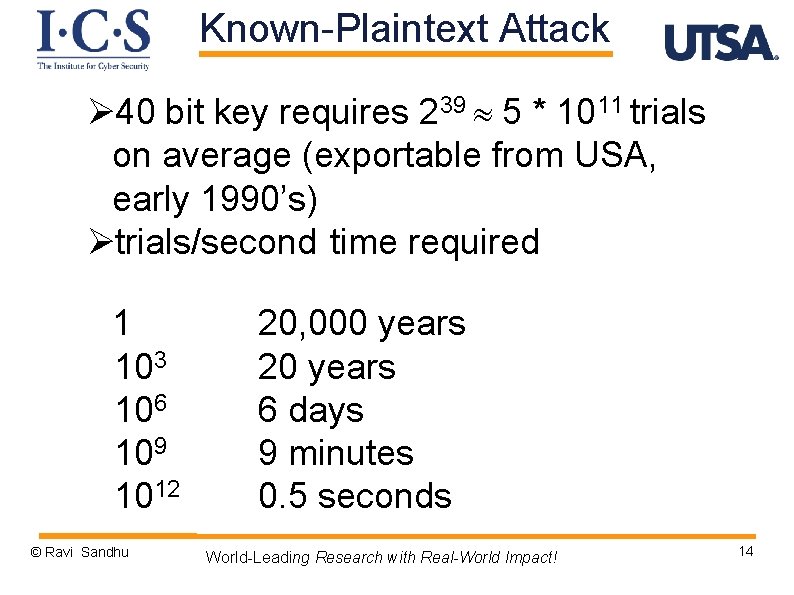
Known-Plaintext Attack Ø 40 bit key requires 239 5 * 1011 trials on average (exportable from USA, early 1990’s) Øtrials/second time required 1 103 106 109 1012 © Ravi Sandhu 20, 000 years 20 years 6 days 9 minutes 0. 5 seconds World-Leading Research with Real-World Impact! 14
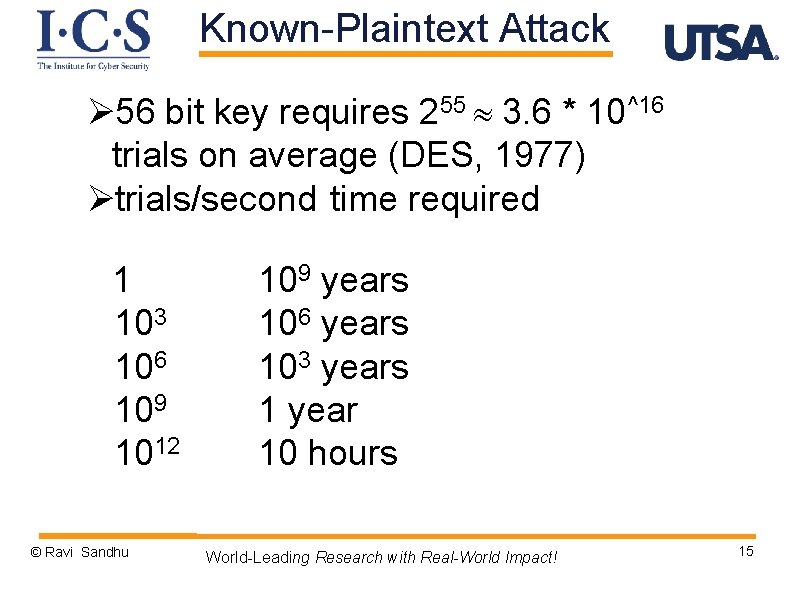
Known-Plaintext Attack Ø 56 bit key requires 255 3. 6 * 10^16 trials on average (DES, 1977) Øtrials/second time required 1 103 106 109 1012 © Ravi Sandhu 109 years 106 years 103 years 1 year 10 hours World-Leading Research with Real-World Impact! 15
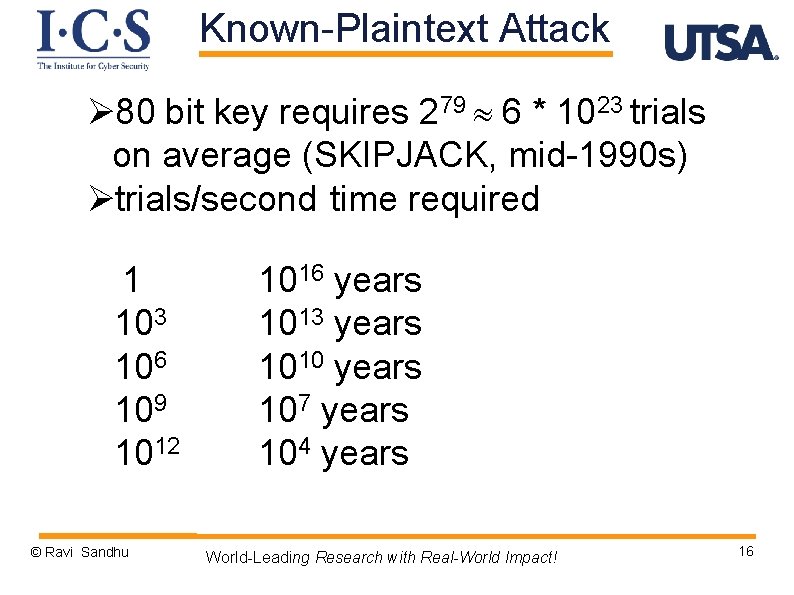
Known-Plaintext Attack Ø 80 bit key requires 279 6 * 1023 trials on average (SKIPJACK, mid-1990 s) Øtrials/second time required 1 103 106 109 1012 © Ravi Sandhu 1016 years 1013 years 1010 years 107 years 104 years World-Leading Research with Real-World Impact! 16
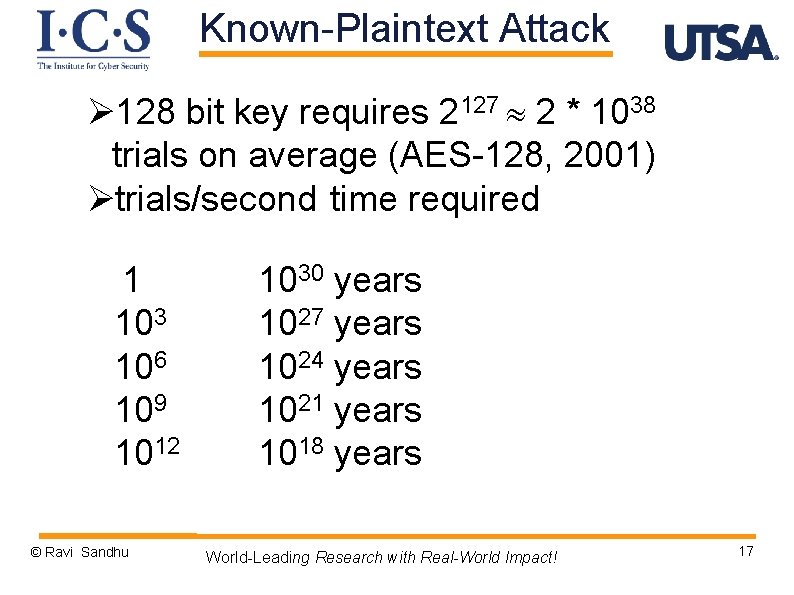
Known-Plaintext Attack Ø 128 bit key requires 2127 2 * 1038 trials on average (AES-128, 2001) Øtrials/second time required 1 103 106 109 1012 © Ravi Sandhu 1030 years 1027 years 1024 years 1021 years 1018 years World-Leading Research with Real-World Impact! 17
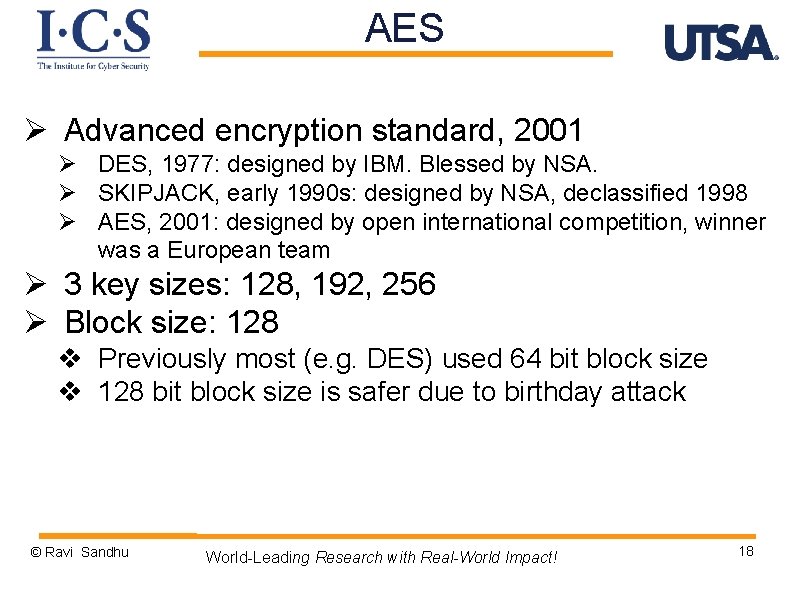
AES Ø Advanced encryption standard, 2001 Ø DES, 1977: designed by IBM. Blessed by NSA. Ø SKIPJACK, early 1990 s: designed by NSA, declassified 1998 Ø AES, 2001: designed by open international competition, winner was a European team Ø 3 key sizes: 128, 192, 256 Ø Block size: 128 v Previously most (e. g. DES) used 64 bit block size v 128 bit block size is safer due to birthday attack © Ravi Sandhu World-Leading Research with Real-World Impact! 18
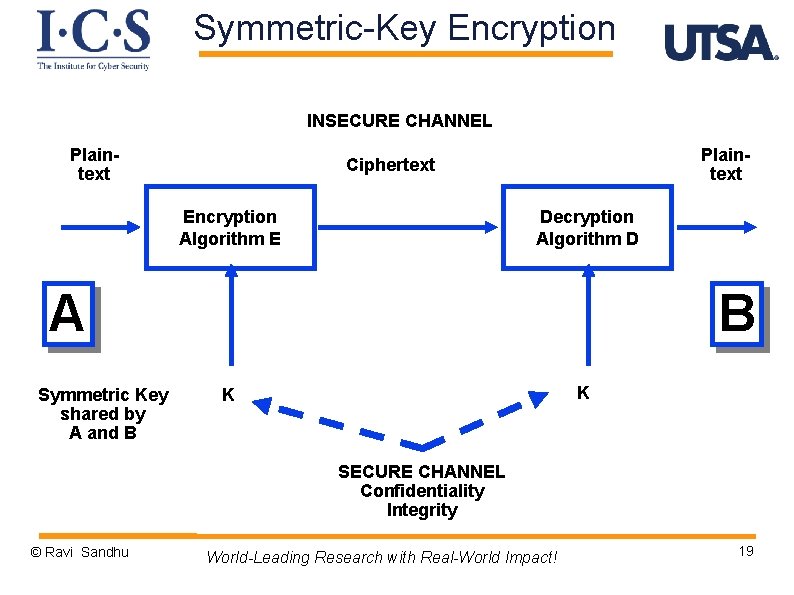
Symmetric-Key Encryption INSECURE CHANNEL Plaintext Ciphertext Encryption Algorithm E Decryption Algorithm D A Symmetric Key shared by A and B B K K SECURE CHANNEL Confidentiality Integrity © Ravi Sandhu World-Leading Research with Real-World Impact! 19
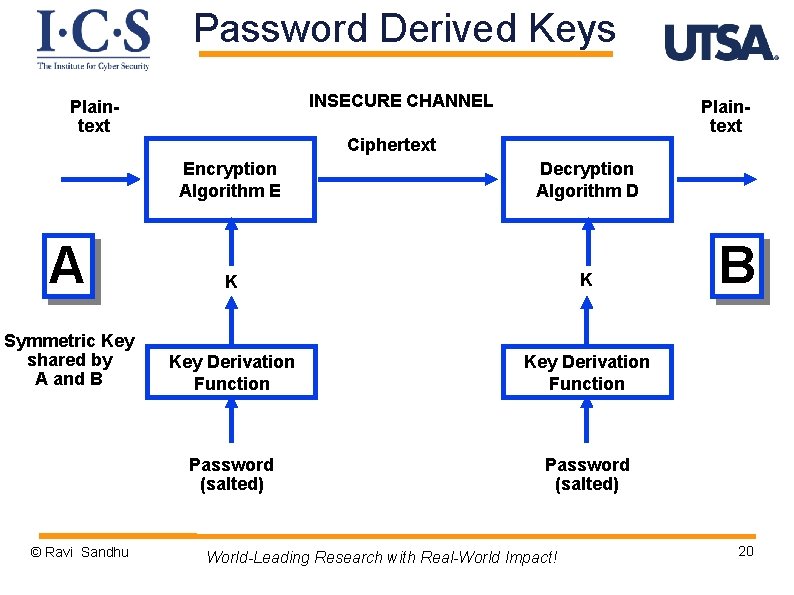
Password Derived Keys INSECURE CHANNEL Plaintext Ciphertext Encryption Algorithm E Decryption Algorithm D A K K Symmetric Key shared by A and B Key Derivation Function Password (salted) © Ravi Sandhu World-Leading Research with Real-World Impact! B 20
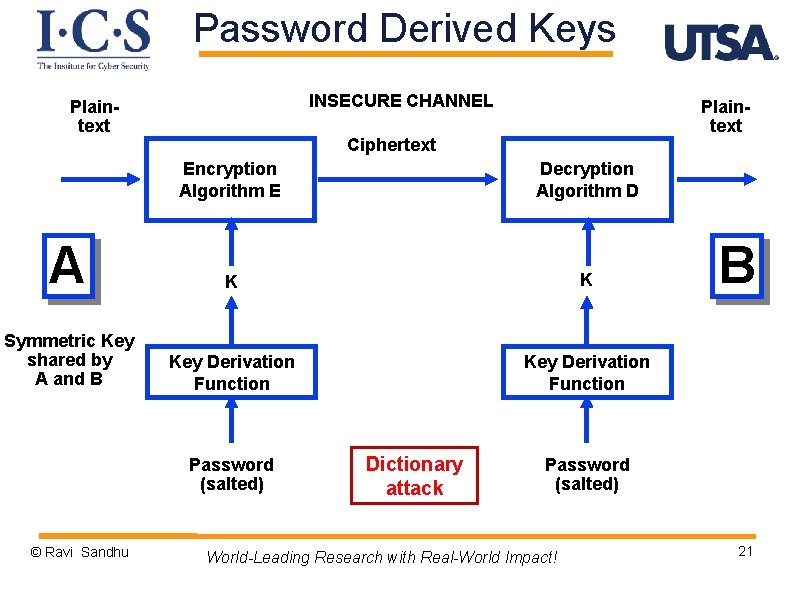
Password Derived Keys INSECURE CHANNEL Plaintext Ciphertext Encryption Algorithm E Decryption Algorithm D A K K Symmetric Key shared by A and B Key Derivation Function Password (salted) © Ravi Sandhu Dictionary attack B Password (salted) World-Leading Research with Real-World Impact! 21
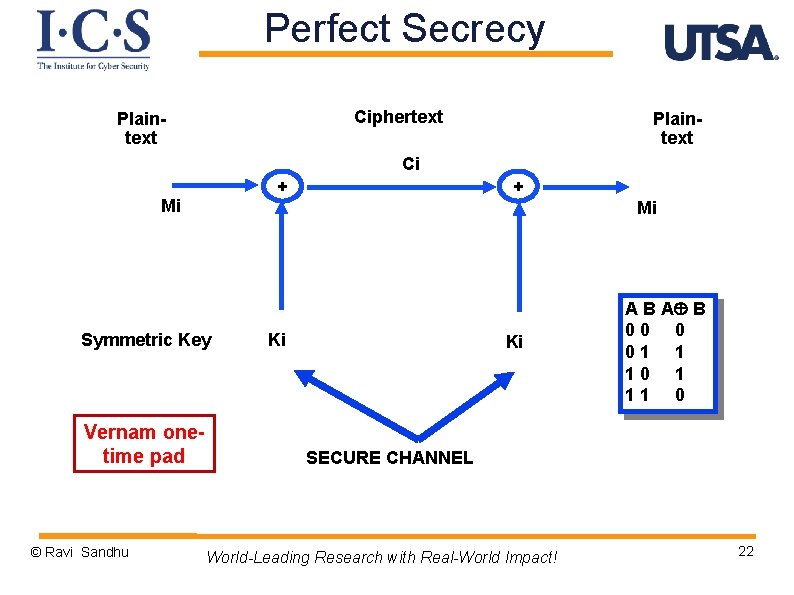
Perfect Secrecy Ciphertext Plaintext Ci + Mi Mi Symmetric Key Vernam onetime pad © Ravi Sandhu + Ki Ki A B 00 0 01 1 10 1 11 0 SECURE CHANNEL World-Leading Research with Real-World Impact! 22
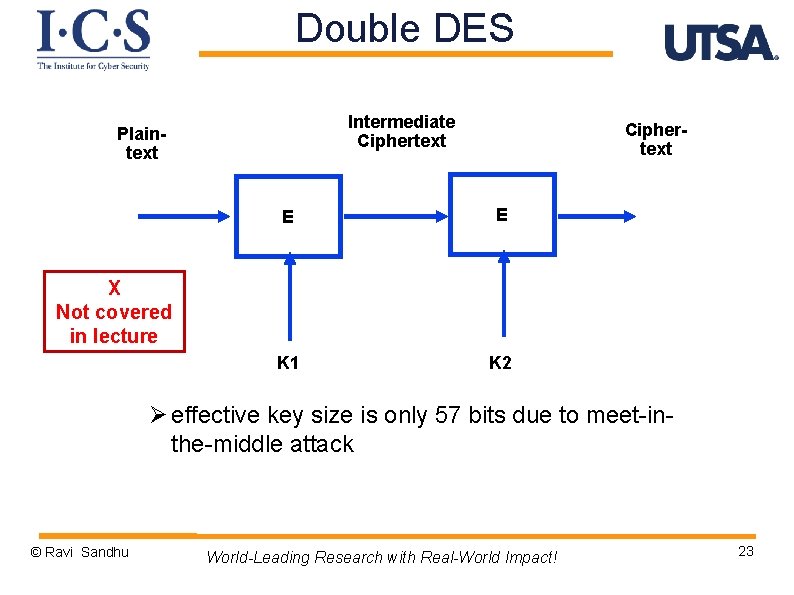
Double DES Intermediate Ciphertext Plaintext Ciphertext E E K 1 K 2 X Not covered in lecture Ø effective key size is only 57 bits due to meet-inthe-middle attack © Ravi Sandhu World-Leading Research with Real-World Impact! 23
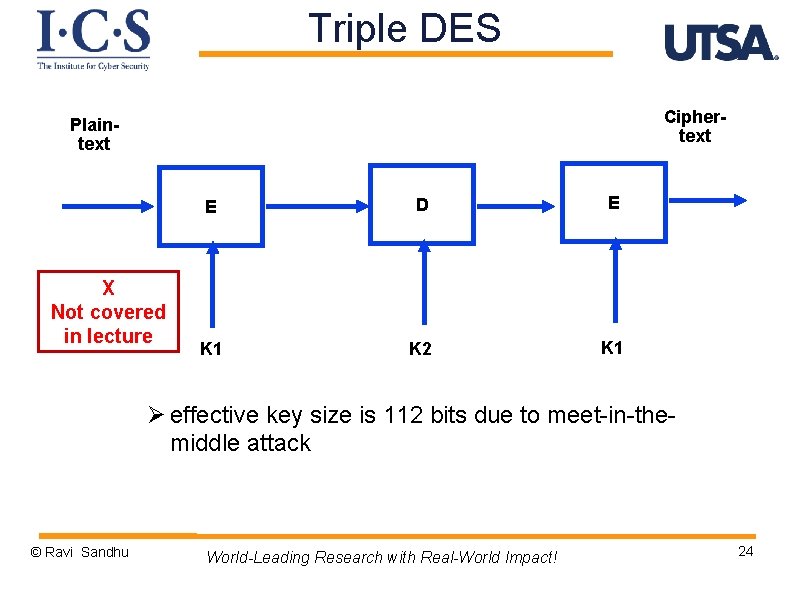
Triple DES Ciphertext Plaintext X Not covered in lecture E D E K 1 K 2 K 1 Ø effective key size is 112 bits due to meet-in-themiddle attack © Ravi Sandhu World-Leading Research with Real-World Impact! 24
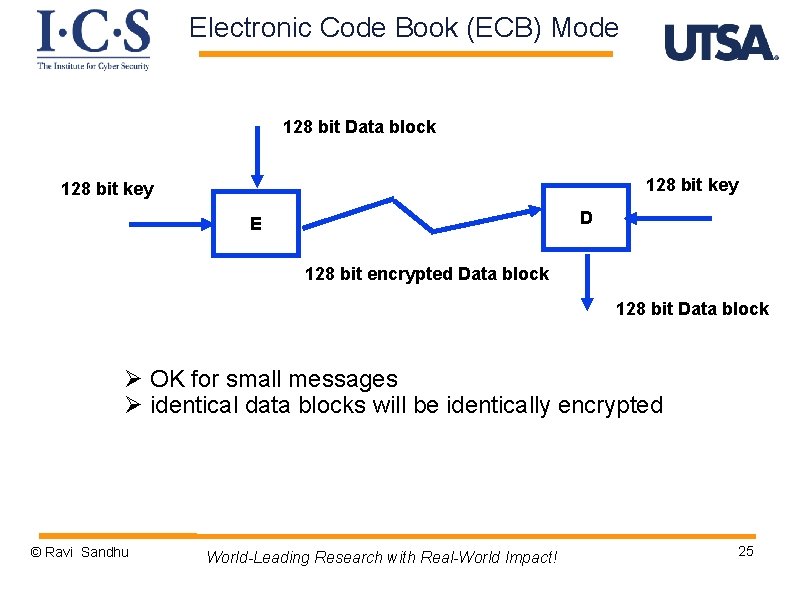
Electronic Code Book (ECB) Mode 128 bit Data block 128 bit key D E 128 bit encrypted Data block 128 bit Data block Ø OK for small messages Ø identical data blocks will be identically encrypted © Ravi Sandhu World-Leading Research with Real-World Impact! 25
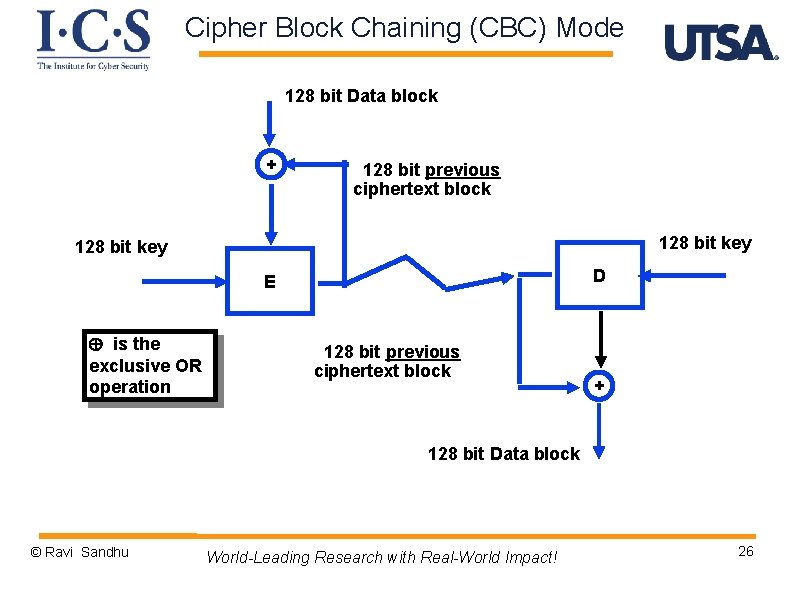
Cipher Block Chaining (CBC) Mode 128 bit Data block + 128 bit previous ciphertext block 128 bit key D E is the exclusive OR operation 128 bit previous ciphertext block + 128 bit Data block © Ravi Sandhu World-Leading Research with Real-World Impact! 26
Symmetric-Key Message Authentication Code (MAC) © Ravi Sandhu World-Leading Research with Real-World Impact! 27
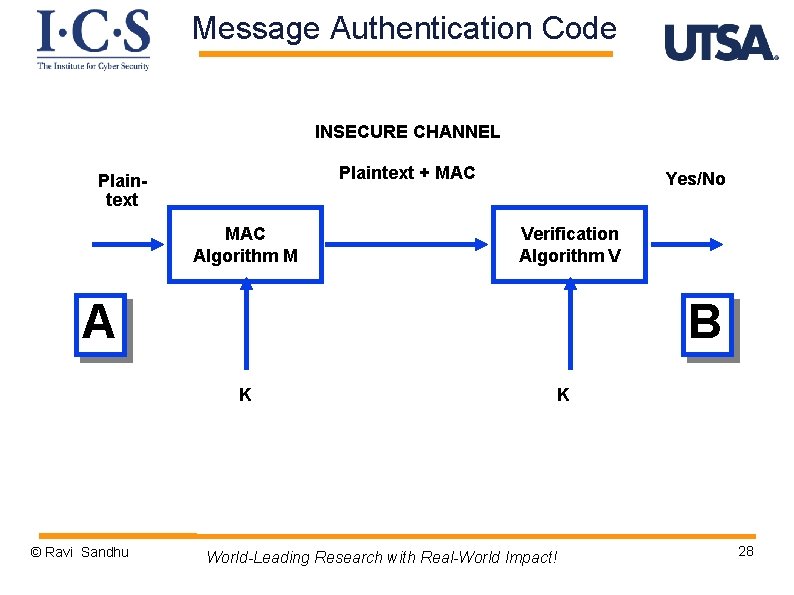
Message Authentication Code INSECURE CHANNEL Plaintext + MAC Plaintext MAC Algorithm M Yes/No Verification Algorithm V A B K © Ravi Sandhu K World-Leading Research with Real-World Impact! 28
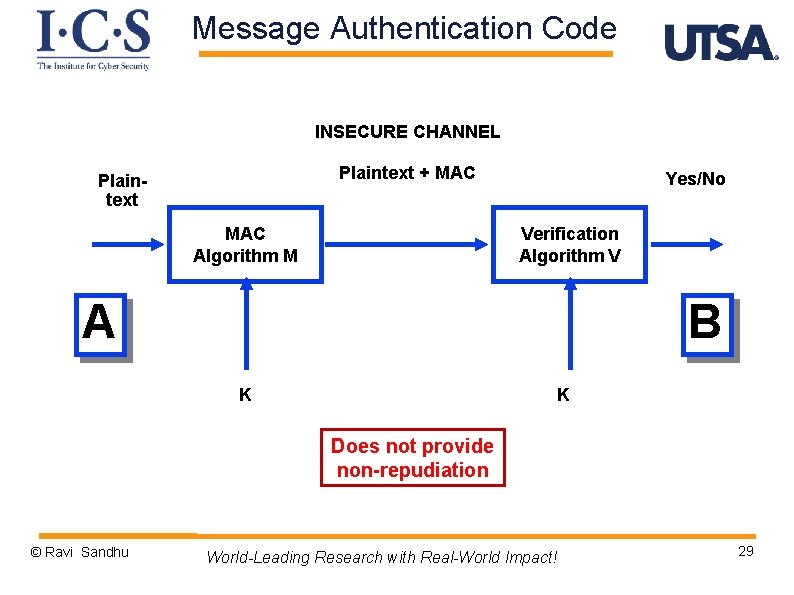
Message Authentication Code INSECURE CHANNEL Plaintext + MAC Plaintext MAC Algorithm M Yes/No Verification Algorithm V A B K K Does not provide non-repudiation © Ravi Sandhu World-Leading Research with Real-World Impact! 29
Message Authentication Code Symmetric Encryption Based © Ravi Sandhu Message-Digest Based World-Leading Research with Real-World Impact! 30
Message Authentication Code Symmetric Encryption Based Message-Digest Based Will revisit after discussing message digests © Ravi Sandhu World-Leading Research with Real-World Impact! 31
- Slides: 31