Chapter 4 Network Layer v CPSC 335 Data
- Slides: 23
Chapter 4 Network Layer v CPSC 335 Data Communication Systems Readings: 4. 5. 3, 4. 6. 1, 4. 6. 2 v David Nguyen v Computer Networking: A Top Down Approach 6 th edition Jim Kurose, Keith Ross Addison-Wesley March 2012 Adapted from Kurose Ross Transport Layer 3 -1
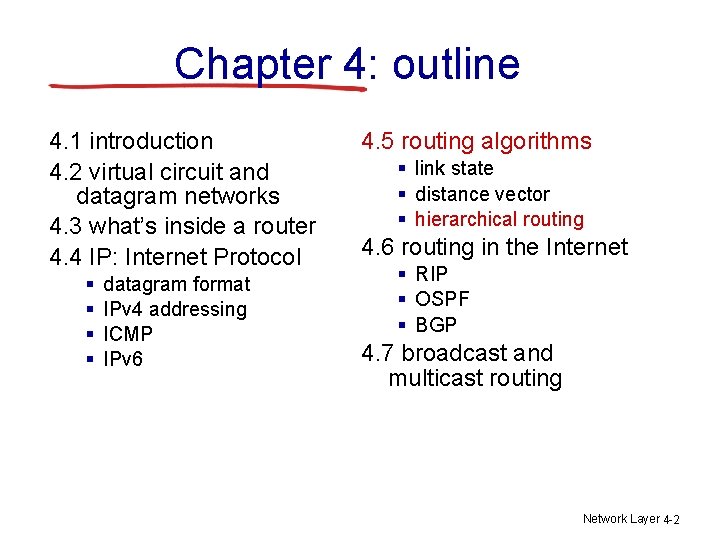
Chapter 4: outline 4. 1 introduction 4. 2 virtual circuit and datagram networks 4. 3 what’s inside a router 4. 4 IP: Internet Protocol § § datagram format IPv 4 addressing ICMP IPv 6 4. 5 routing algorithms § link state § distance vector § hierarchical routing 4. 6 routing in the Internet § RIP § OSPF § BGP 4. 7 broadcast and multicast routing Network Layer 4 -2
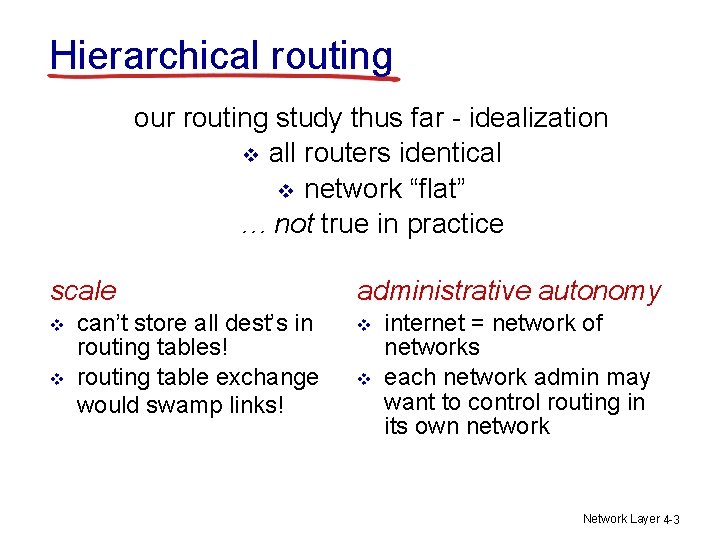
Hierarchical routing our routing study thus far - idealization v all routers identical v network “flat” … not true in practice scale v v can’t store all dest’s in routing tables! routing table exchange would swamp links! administrative autonomy v v internet = network of networks each network admin may want to control routing in its own network Network Layer 4 -3
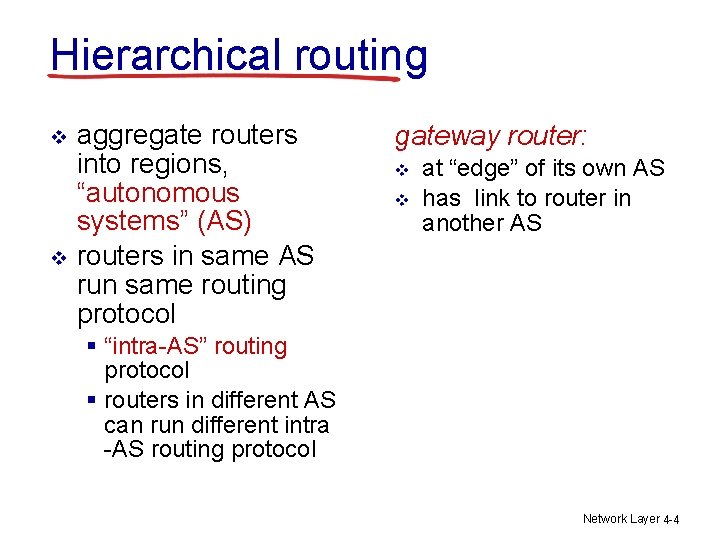
Hierarchical routing v v aggregate routers into regions, “autonomous systems” (AS) routers in same AS run same routing protocol gateway router: v v at “edge” of its own AS has link to router in another AS § “intra-AS” routing protocol § routers in different AS can run different intra -AS routing protocol Network Layer 4 -4
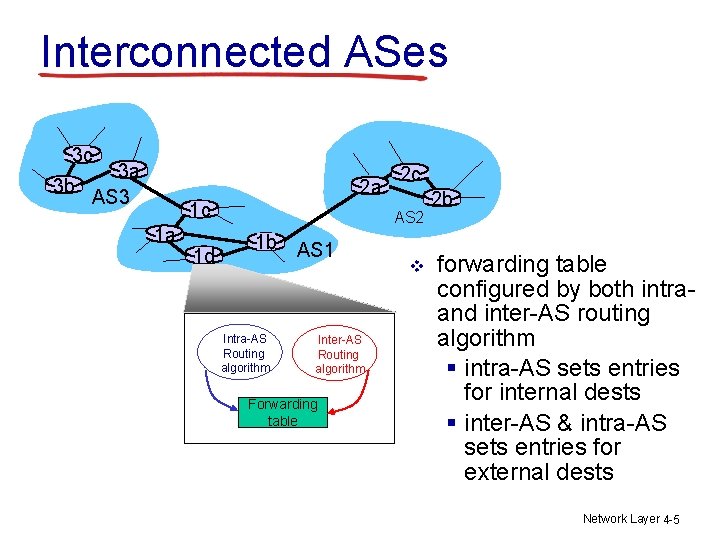
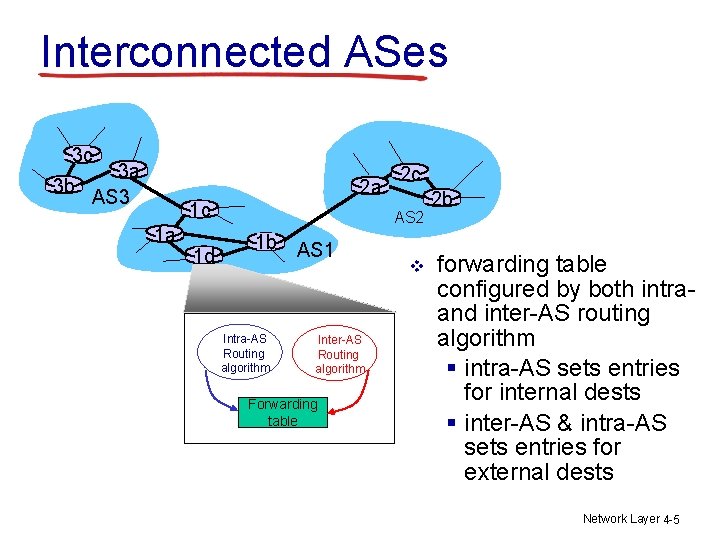
Interconnected ASes 3 c 3 a 3 b AS 3 2 a 1 c 1 a 1 d 2 c AS 2 1 b AS 1 Intra-AS Routing algorithm Inter-AS Routing algorithm Forwarding table v 2 b forwarding table configured by both intraand inter-AS routing algorithm § intra-AS sets entries for internal dests § inter-AS & intra-AS sets entries for external dests Network Layer 4 -5
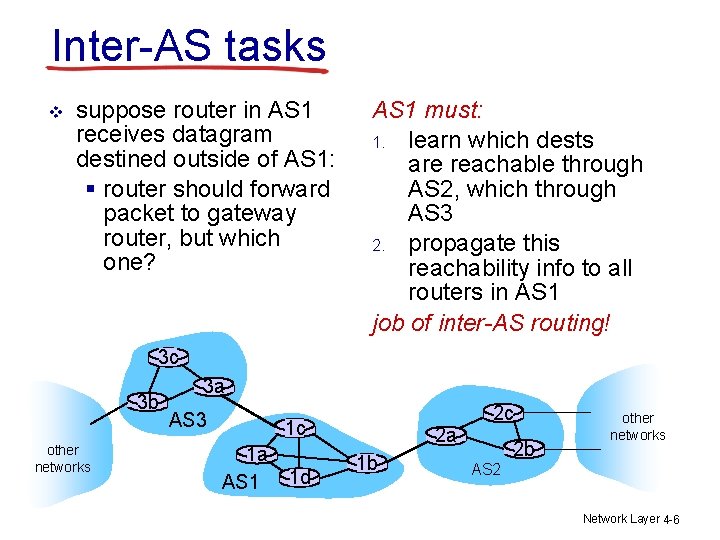
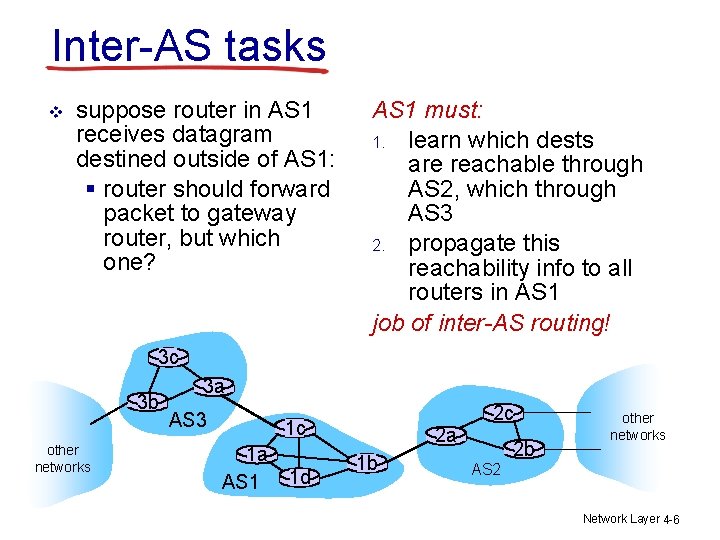
Inter-AS tasks v suppose router in AS 1 receives datagram destined outside of AS 1: § router should forward packet to gateway router, but which one? AS 1 must: 1. learn which dests are reachable through AS 2, which through AS 3 2. propagate this reachability info to all routers in AS 1 job of inter-AS routing! 3 c 3 b other networks 3 a AS 3 1 c 1 a AS 1 1 d 2 a 1 b 2 c 2 b other networks AS 2 Network Layer 4 -6
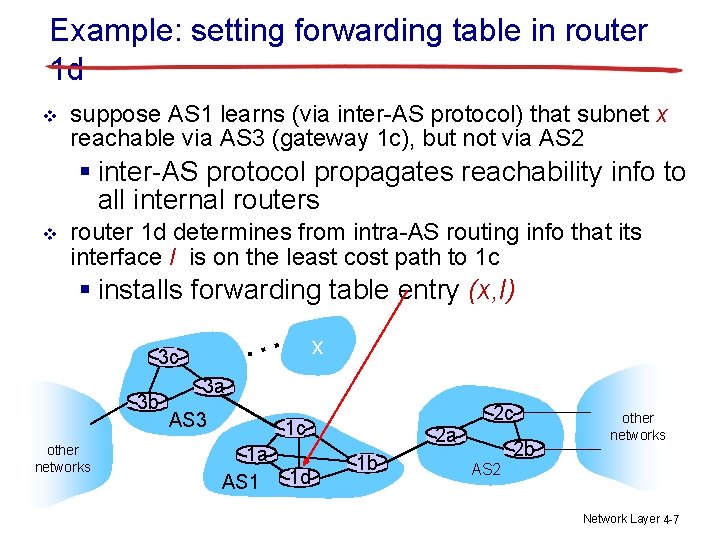
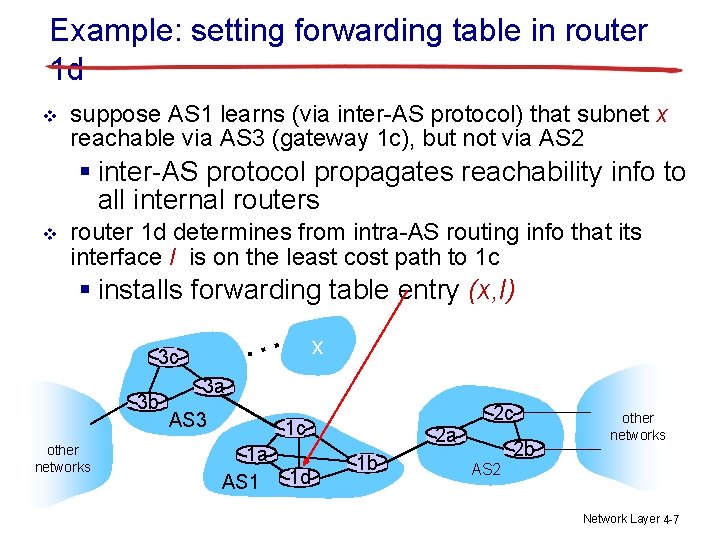
Example: setting forwarding table in router 1 d v suppose AS 1 learns (via inter-AS protocol) that subnet x reachable via AS 3 (gateway 1 c), but not via AS 2 § inter-AS protocol propagates reachability info to all internal routers v router 1 d determines from intra-AS routing info that its interface I is on the least cost path to 1 c § installs forwarding table entry (x, I) … 3 c 3 b other networks x 3 a AS 3 1 c 1 a AS 1 1 d 2 a 1 b 2 c 2 b other networks AS 2 Network Layer 4 -7
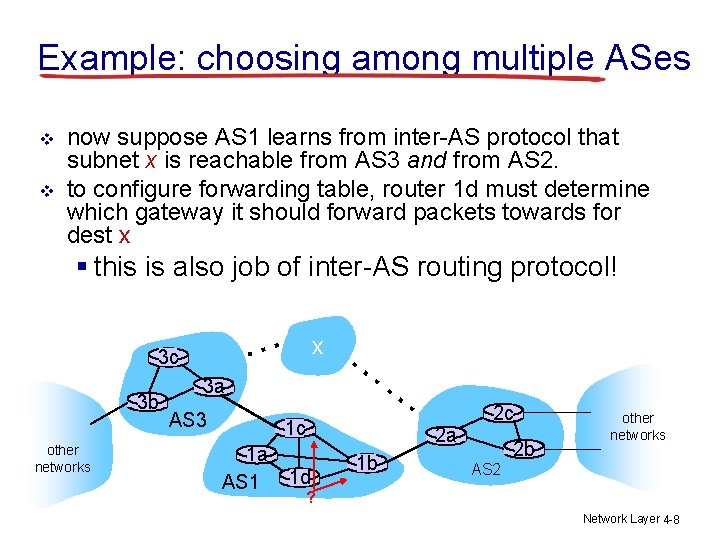
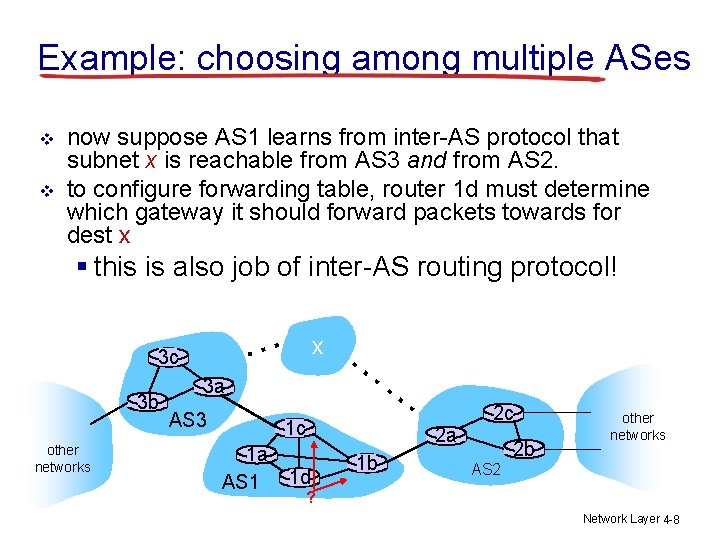
Example: choosing among multiple ASes v v now suppose AS 1 learns from inter-AS protocol that subnet x is reachable from AS 3 and from AS 2. to configure forwarding table, router 1 d must determine which gateway it should forward packets towards for dest x § this is also job of inter-AS routing protocol! … 3 c 3 b other networks x … … 3 a AS 3 1 c 1 a AS 1 2 a 1 d 1 b 2 c 2 b other networks AS 2 ? Network Layer 4 -8
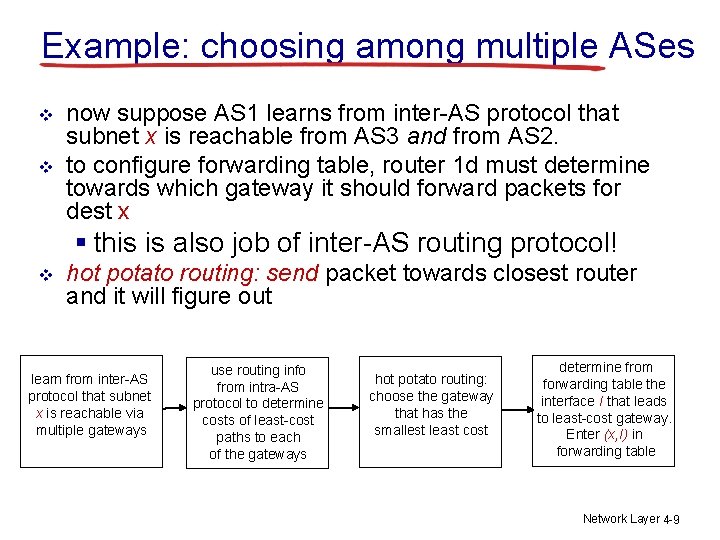
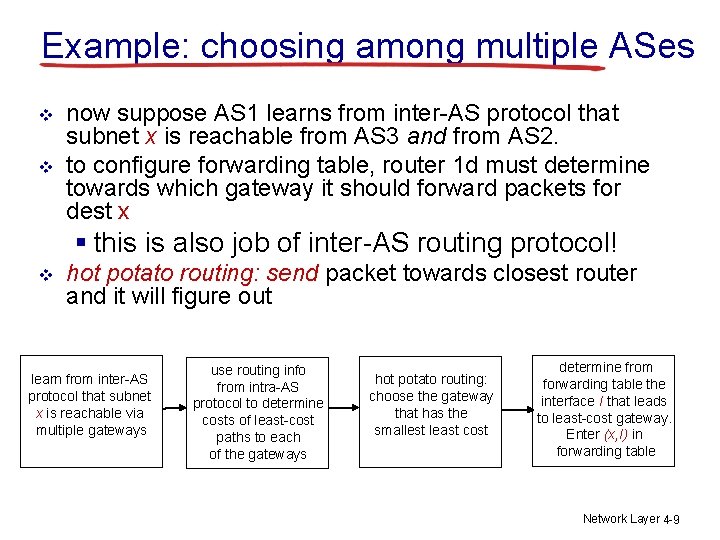
Example: choosing among multiple ASes v v now suppose AS 1 learns from inter-AS protocol that subnet x is reachable from AS 3 and from AS 2. to configure forwarding table, router 1 d must determine towards which gateway it should forward packets for dest x § this is also job of inter-AS routing protocol! v hot potato routing: send packet towards closest router and it will figure out learn from inter-AS protocol that subnet x is reachable via multiple gateways use routing info from intra-AS protocol to determine costs of least-cost paths to each of the gateways hot potato routing: choose the gateway that has the smallest least cost determine from forwarding table the interface I that leads to least-cost gateway. Enter (x, I) in forwarding table Network Layer 4 -9
Chapter 4: outline 4. 1 introduction 4. 2 virtual circuit and datagram networks 4. 3 what’s inside a router 4. 4 IP: Internet Protocol § § datagram format IPv 4 addressing ICMP IPv 6 4. 5 routing algorithms § link state § distance vector § hierarchical routing 4. 6 routing in the Internet § RIP § OSPF § BGP 4. 7 broadcast and multicast routing Network Layer 4 -10
Intra-AS Routing v most common intra-AS routing protocols: § RIP: Routing Information Protocol § OSPF: Open Shortest Path First Network Layer 4 -11
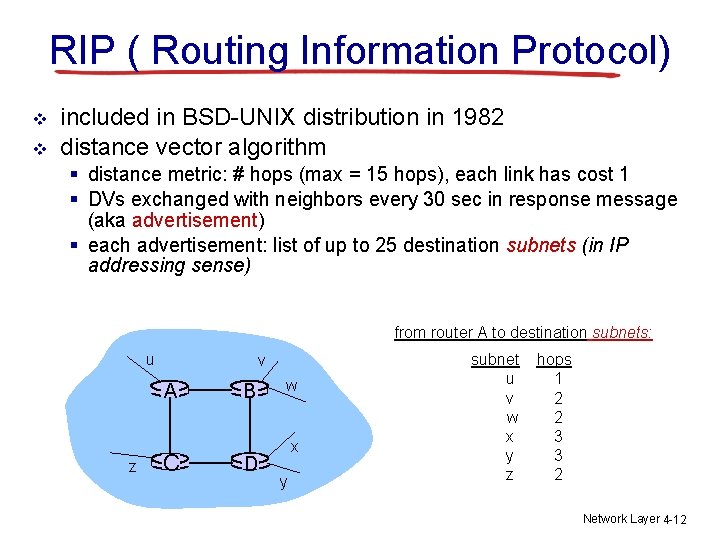
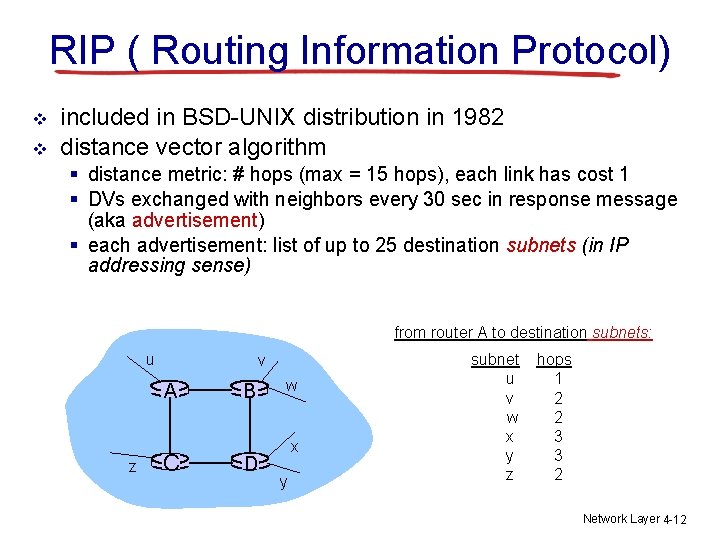
RIP ( Routing Information Protocol) v v included in BSD-UNIX distribution in 1982 distance vector algorithm § distance metric: # hops (max = 15 hops), each link has cost 1 § DVs exchanged with neighbors every 30 sec in response message (aka advertisement) § each advertisement: list of up to 25 destination subnets (in IP addressing sense) from router A to destination subnets: u v A z C B D w x y subnet u v w x y z hops 1 2 2 3 3 2 Network Layer 4 -12
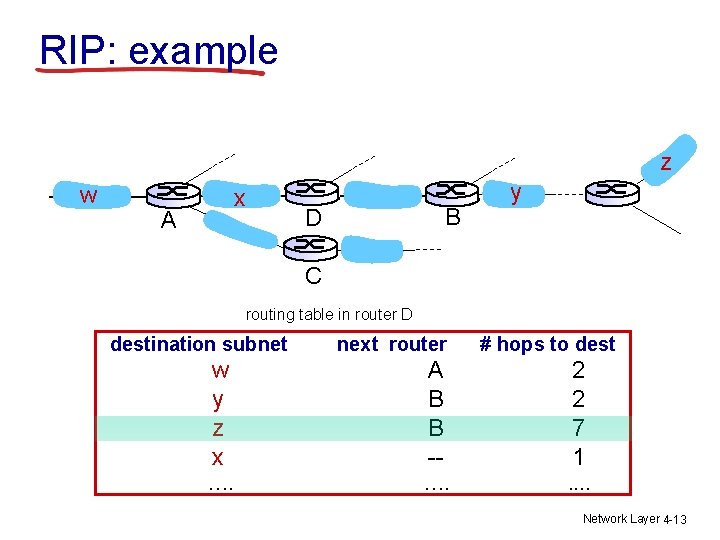
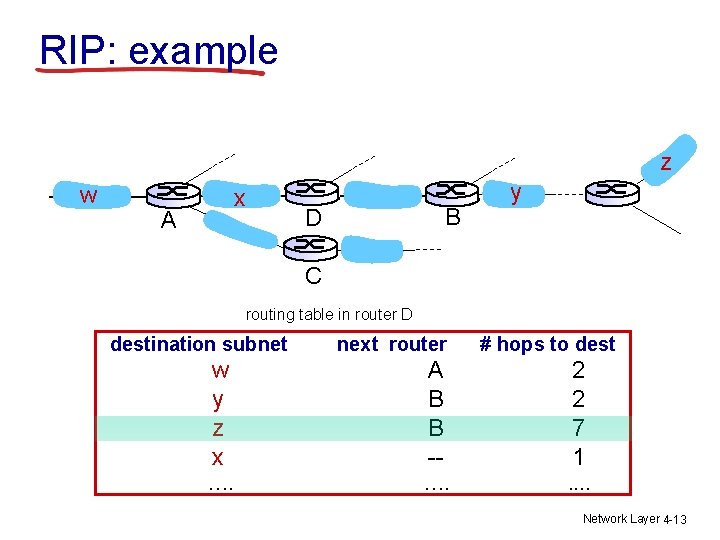
RIP: example z w x A B D y C routing table in router D destination subnet next router # hops to dest w y z x A B B -- 2 2 7 1 …. . . Network Layer 4 -13
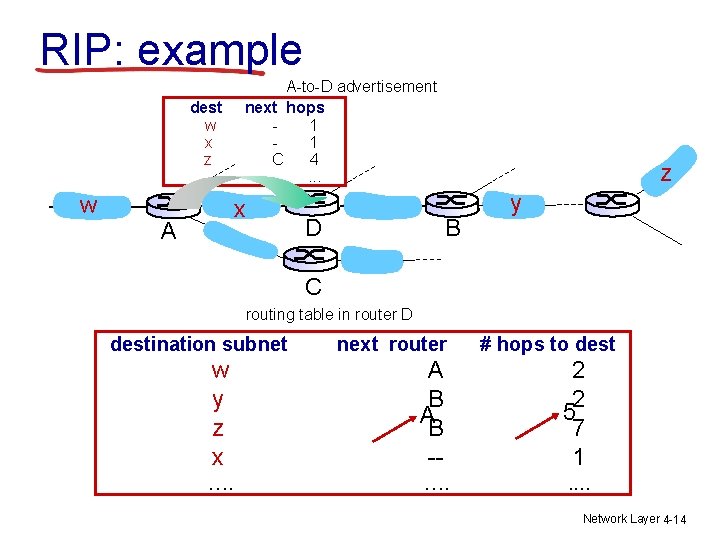
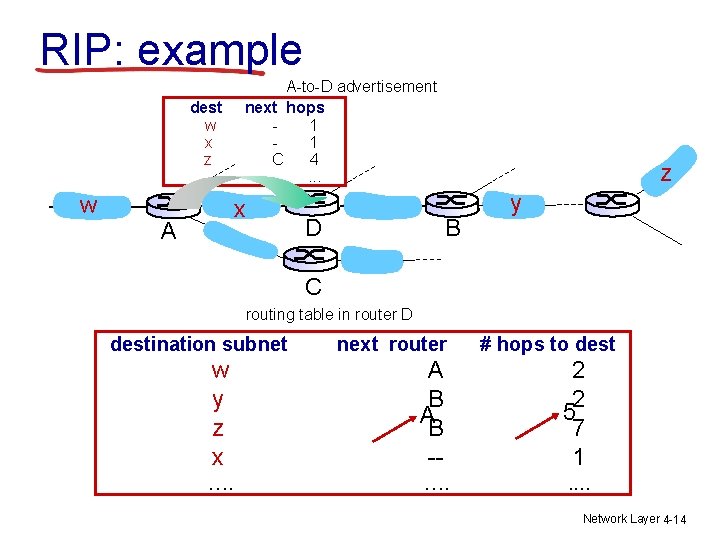
RIP: example dest w x z …. w A-to-D advertisement next hops 1 1 C 4 …. . . x A z B D y C routing table in router D destination subnet next router # hops to dest w y z x A B -- 2 2 5 7 1 …. . . Network Layer 4 -14
RIP: link failure, recovery if no advertisement heard after 180 sec --> neighbor/link declared dead § routes via neighbor invalidated § new advertisements sent to neighbors § neighbors in turn send out new advertisements (if tables changed) § link failure info propagates to entire net Network Layer 4 -15
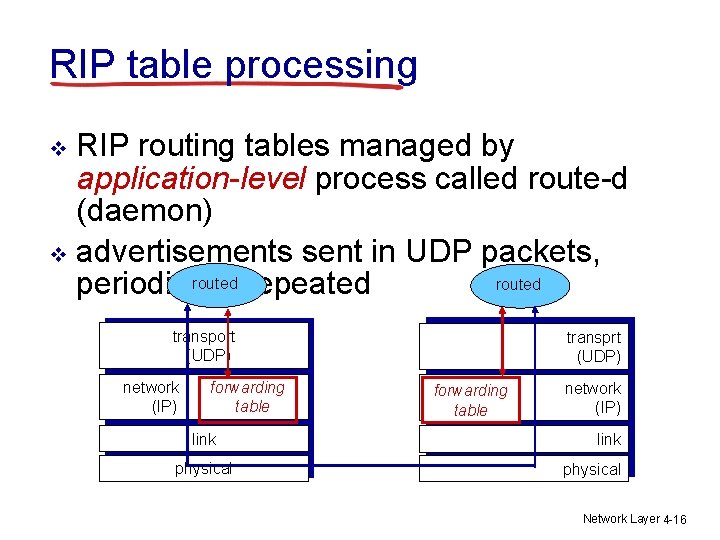
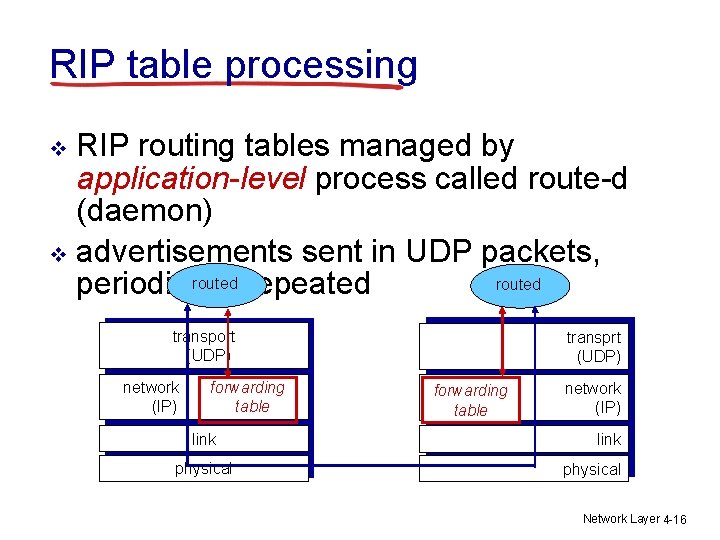
RIP table processing RIP routing tables managed by application-level process called route-d (daemon) v advertisements sent in UDP packets, routed repeated routed periodically v transport (UDP) network (IP) forwarding table link physical transprt (UDP) forwarding table network (IP) link physical Network Layer 4 -16
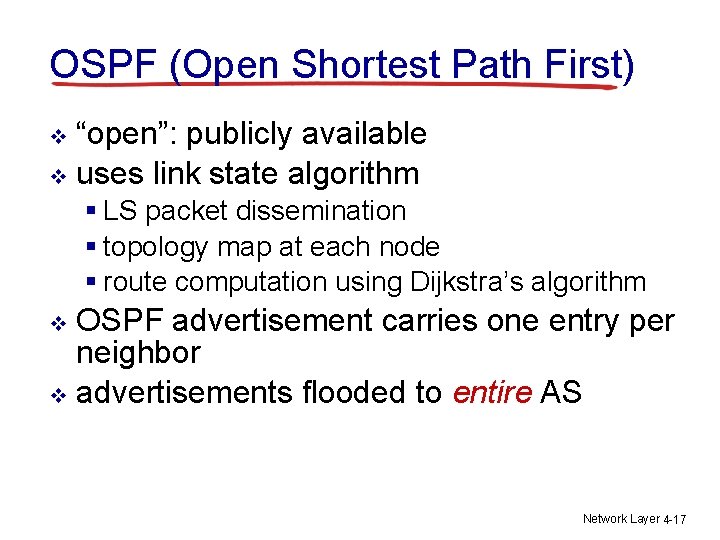
OSPF (Open Shortest Path First) “open”: publicly available v uses link state algorithm v § LS packet dissemination § topology map at each node § route computation using Dijkstra’s algorithm OSPF advertisement carries one entry per neighbor v advertisements flooded to entire AS v Network Layer 4 -17
OSPF “advanced” features (not in RIP) security: all OSPF messages authenticated (to prevent malicious intrusion) v multiple same-cost paths allowed (only one path in RIP) v hierarchical OSPF in large domains. v Network Layer 4 -18
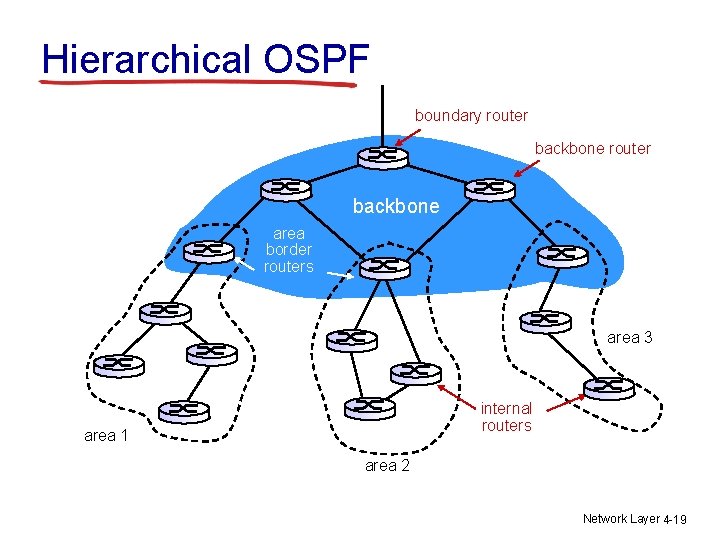
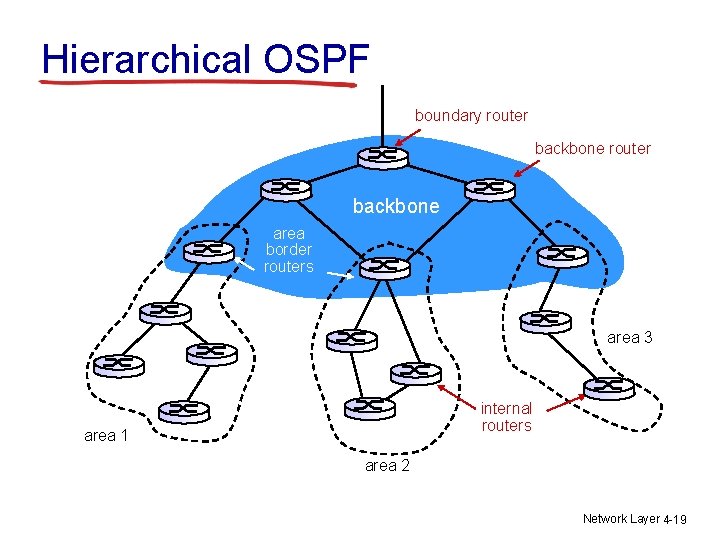
Hierarchical OSPF boundary router backbone area border routers area 3 internal routers area 1 area 2 Network Layer 4 -19
How to get a dream job at big IT companies? Tips based on personal experience and “Cracking the Coding Interview” GOOGLE AND AMAZON INTERVIEW TIPS! Transport Layer 3 -20
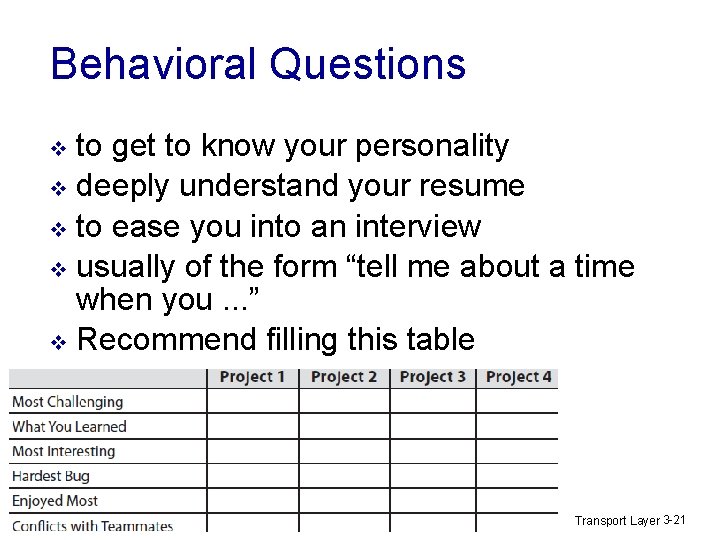
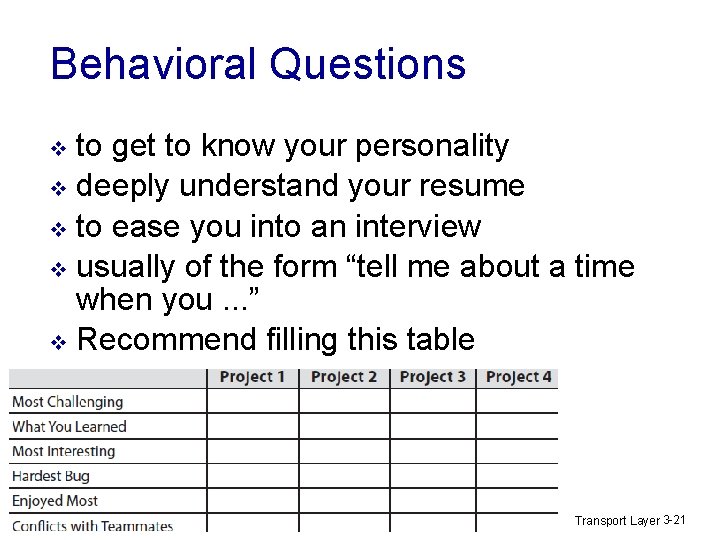
Behavioral Questions to get to know your personality v deeply understand your resume v to ease you into an interview v usually of the form “tell me about a time when you. . . ” v Recommend filling this table v Transport Layer 3 -21
Behavioral Questions Do the similar table with major aspects of your resume (jobs, …) v Study the tables before the interview v Additional advice v § When asked about your weaknesses, give a real weakness! (I work too hard / am a perfectionist - arrogant) § When asked what the most challenging part was, don’t say “I had to learn a lot of new languages and technologies. ” (means nothing was really that hard) Transport Layer 3 -22
Sample theory questions (Google) What are the differences between TCP and UDP? (should be easy for you now : ) v Explain what happens, step by step, after you type a URL into a browser. Use as much detail as possible. (piece of cake again) v Transport Layer 3 -23