We are now at Week 10 A DBMS
We are now at Week 10 A DBMS Contains. . Dr. Codd’s 12 Rules for Relational Database Privacy and Ethics Changes in Information Technology Direction CSE 3180 Semester 1 2005 week 10 / 1
Week 10 These items will be addressed – Database Management Systems requirements – Codd’s 12 Rules for Relational Database Systems – Some aspects of Ethics and Privacy – and some thoughts regarding Information Technology and its changing direction CSE 3180 Semester 1 2005 week 10 / 2
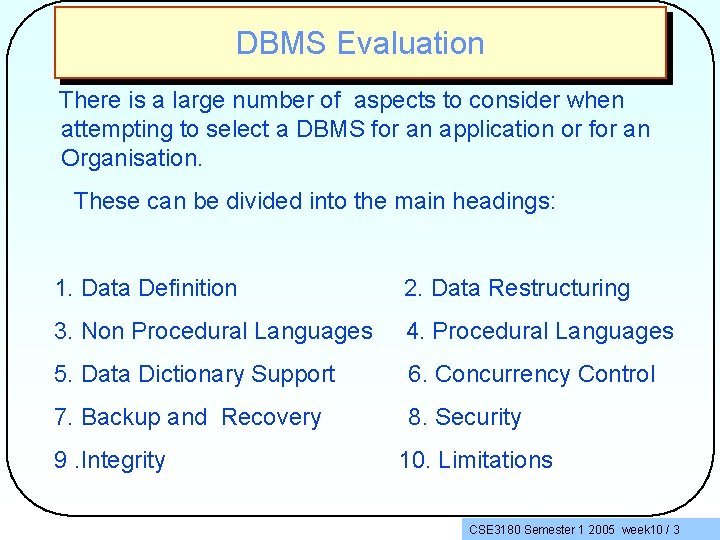
DBMS Evaluation There is a large number of aspects to consider when attempting to select a DBMS for an application or for an Organisation. These can be divided into the main headings: 1. Data Definition 2. Data Restructuring 3. Non Procedural Languages 4. Procedural Languages 5. Data Dictionary Support 6. Concurrency Control 7. Backup and Recovery 8. Security 9. Integrity 10. Limitations CSE 3180 Semester 1 2005 week 10 / 3
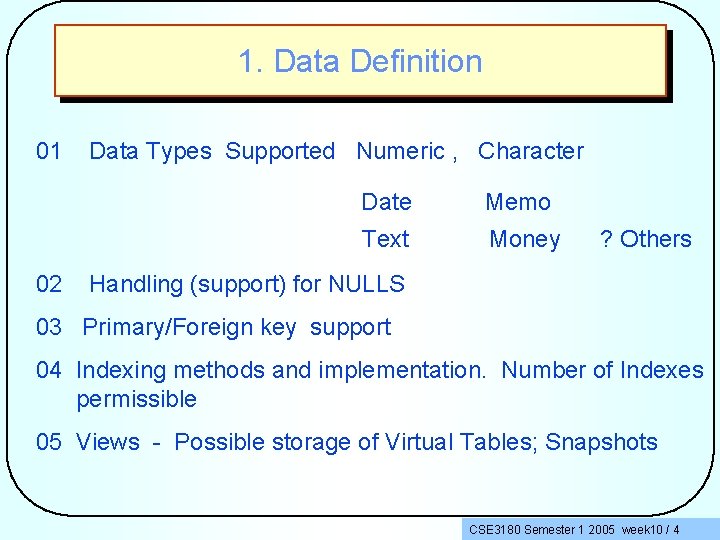
1. Data Definition 01 02 Data Types Supported Numeric , Character Date Memo Text Money ? Others Handling (support) for NULLS 03 Primary/Foreign key support 04 Indexing methods and implementation. Number of Indexes permissible 05 Views - Possible storage of Virtual Tables; Snapshots CSE 3180 Semester 1 2005 week 10 / 4
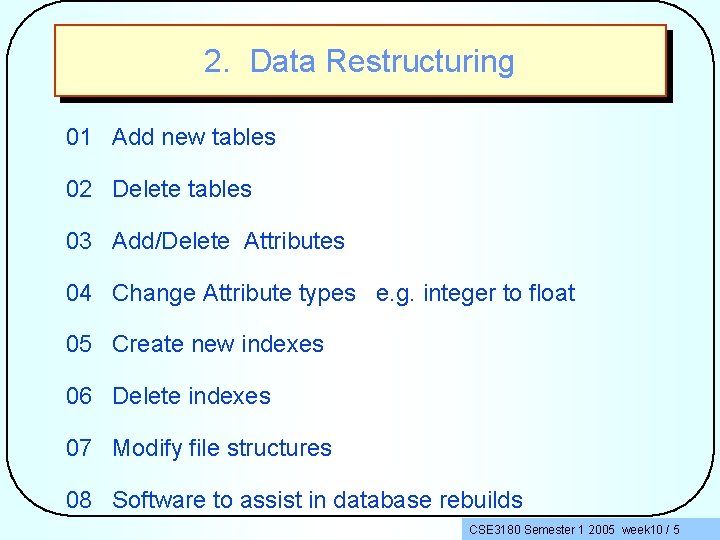
2. Data Restructuring 01 Add new tables 02 Delete tables 03 Add/Delete Attributes 04 Change Attribute types e. g. integer to float 05 Create new indexes 06 Delete indexes 07 Modify file structures 08 Software to assist in database rebuilds CSE 3180 Semester 1 2005 week 10 / 5
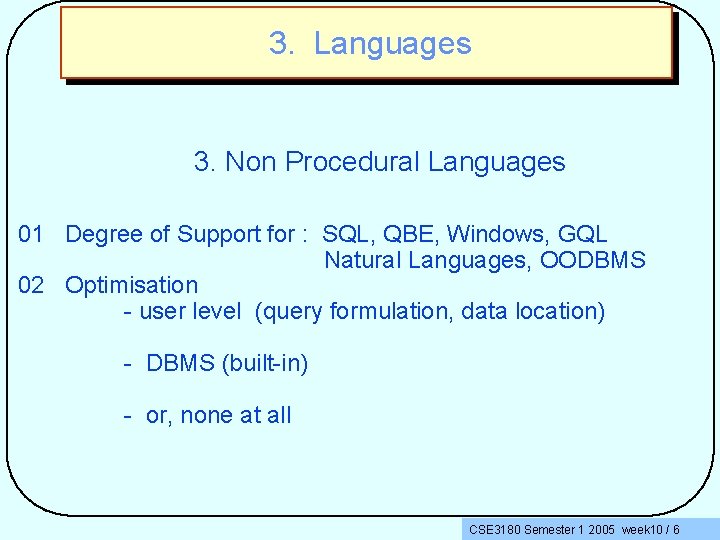
3. Languages 3. Non Procedural Languages 01 Degree of Support for : SQL, QBE, Windows, GQL Natural Languages, OODBMS 02 Optimisation - user level (query formulation, data location) - DBMS (built-in) - or, none at all CSE 3180 Semester 1 2005 week 10 / 6
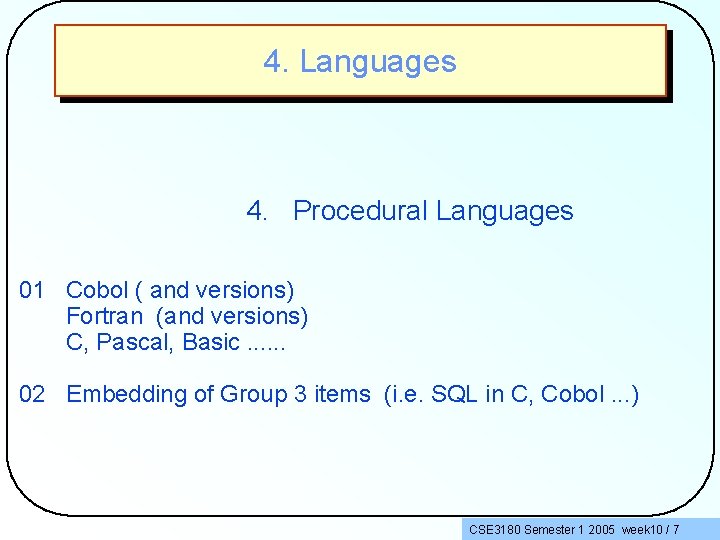
4. Languages 4. Procedural Languages 01 Cobol ( and versions) Fortran (and versions) C, Pascal, Basic. . . 02 Embedding of Group 3 items (i. e. SQL in C, Cobol. . . ) CSE 3180 Semester 1 2005 week 10 / 7
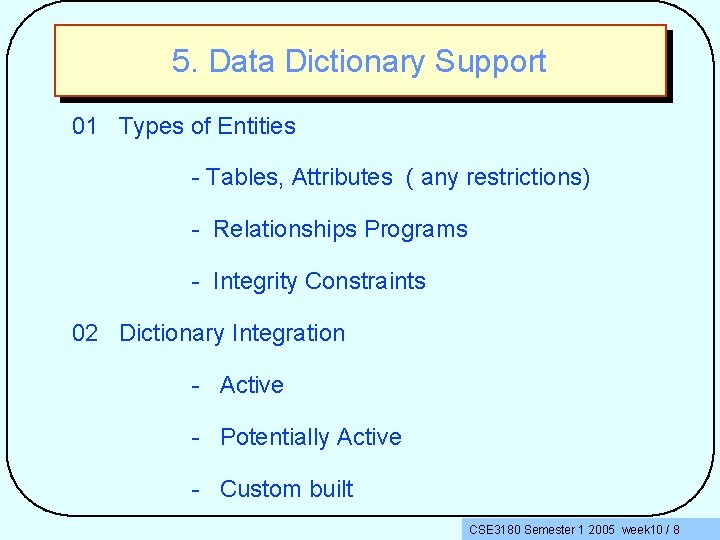
5. Data Dictionary Support 01 Types of Entities - Tables, Attributes ( any restrictions) - Relationships Programs - Integrity Constraints 02 Dictionary Integration - Active - Potentially Active - Custom built CSE 3180 Semester 1 2005 week 10 / 8
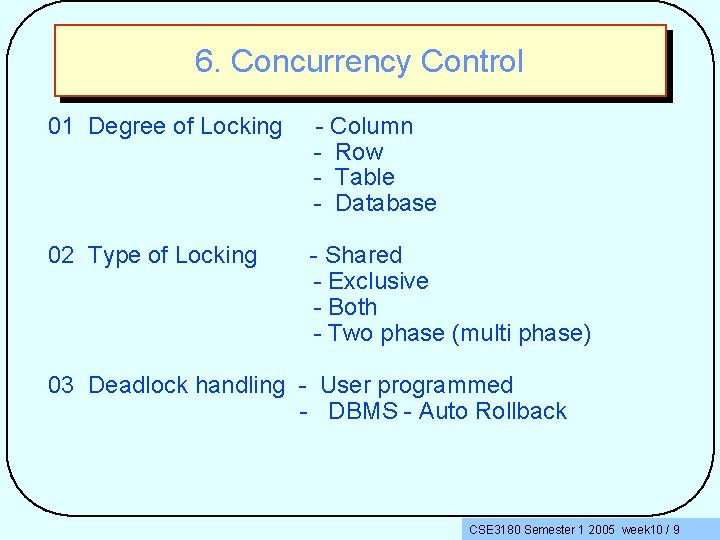
6. Concurrency Control 01 Degree of Locking - Column - Row - Table - Database 02 Type of Locking - Shared - Exclusive - Both - Two phase (multi phase) 03 Deadlock handling - User programmed - DBMS - Auto Rollback CSE 3180 Semester 1 2005 week 10 / 9
7. Backup and Recovery Backup Facilities Journalling Facilities Recovery CSE 3180 Semester 1 2005 week 10 / 10
8. Security 01 Passwords 02 Encryption 03 Views 04 Other CSE 3180 Semester 1 2005 week 10 / 11
9. Integrity Support for - Entity Integrity - Referential Integrity - Data Type Integrity - Other Constraints ( how provided ) CSE 3180 Semester 1 2005 week 10 / 12
10. Limitations 01 Number of Tables 02 Number of Attributes (columns) 03 Number of Rows per Table 04 Hardware Platforms 05 LANS, MANS, WANS support CSE 3180 Semester 1 2005 week 10 / 13
Codd’s 12 (+ 1) Rules • Relational Database had its foundations carefully stated by Dr. E. F. Codd. • We will be looking at what these rules are, and also how they determine the various functions of a relational database system. CSE 3180 Semester 1 2005 week 10 / 14
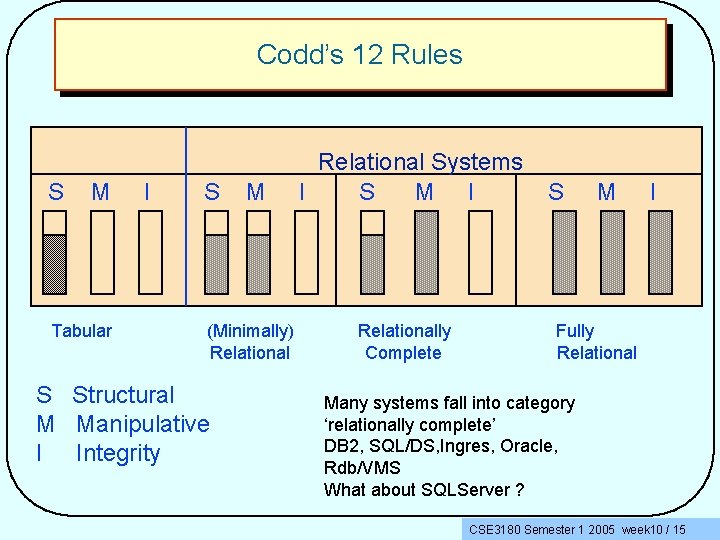
Codd’s 12 Rules S M Tabular I S M (Minimally) Relational S Structural M Manipulative I Integrity Relational Systems I S M I Relationally Complete S M I Fully Relational Many systems fall into category ‘relationally complete’ DB 2, SQL/DS, Ingres, Oracle, Rdb/VMS What about SQLServer ? CSE 3180 Semester 1 2005 week 10 / 15
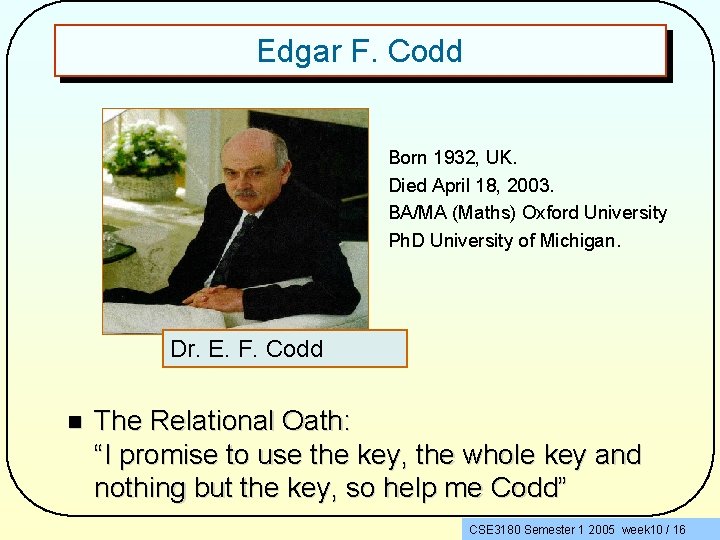
Edgar F. Codd • • Born 1932, UK. Died April 18, 2003. BA/MA (Maths) Oxford University Ph. D University of Michigan. Dr. E. F. Codd n The Relational Oath: “I promise to use the key, the whole key and nothing but the key, so help me Codd” CSE 3180 Semester 1 2005 week 10 / 16
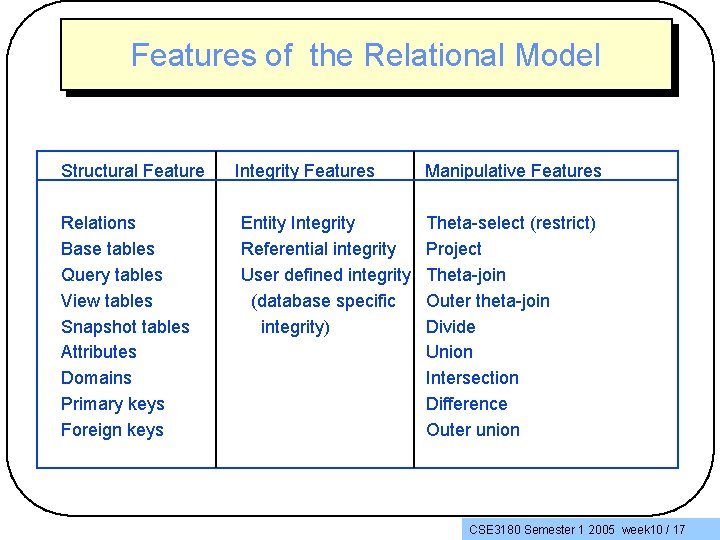
Features of the Relational Model Structural Feature Relations Base tables Query tables View tables Snapshot tables Attributes Domains Primary keys Foreign keys Integrity Features Entity Integrity Referential integrity User defined integrity (database specific integrity) Manipulative Features Theta-select (restrict) Project Theta-join Outer theta-join Divide Union Intersection Difference Outer union CSE 3180 Semester 1 2005 week 10 / 17
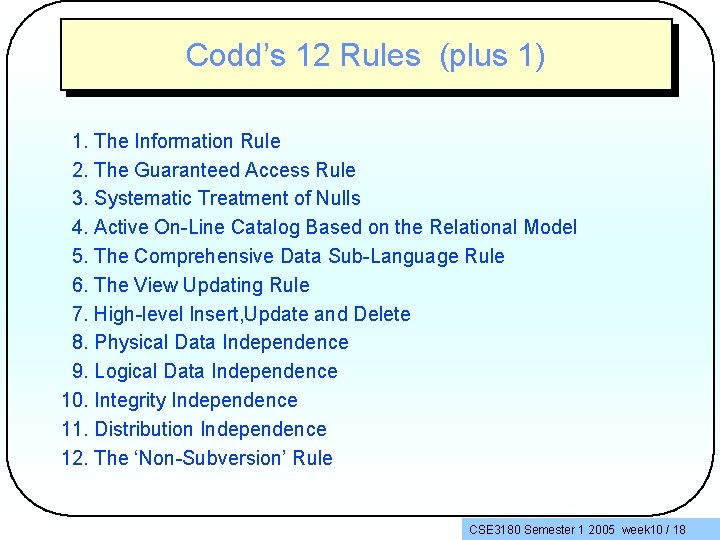
Codd’s 12 Rules (plus 1) 1. The Information Rule 2. The Guaranteed Access Rule 3. Systematic Treatment of Nulls 4. Active On-Line Catalog Based on the Relational Model 5. The Comprehensive Data Sub-Language Rule 6. The View Updating Rule 7. High-level Insert, Update and Delete 8. Physical Data Independence 9. Logical Data Independence 10. Integrity Independence 11. Distribution Independence 12. The ‘Non-Subversion’ Rule CSE 3180 Semester 1 2005 week 10 / 18
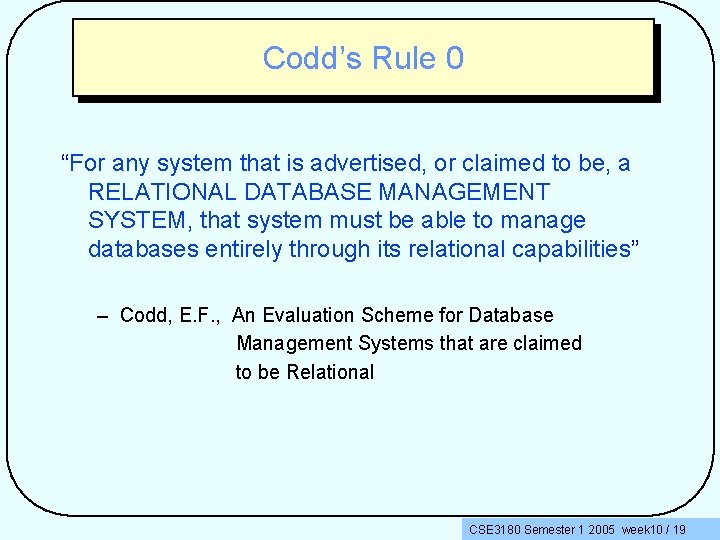
Codd’s Rule 0 “For any system that is advertised, or claimed to be, a RELATIONAL DATABASE MANAGEMENT SYSTEM, that system must be able to manage databases entirely through its relational capabilities” – Codd, E. F. , An Evaluation Scheme for Database Management Systems that are claimed to be Relational CSE 3180 Semester 1 2005 week 10 / 19
Ethics and Privacy Some common uses of data about people: CSE 3180 Semester 1 2005 week 10 / 20
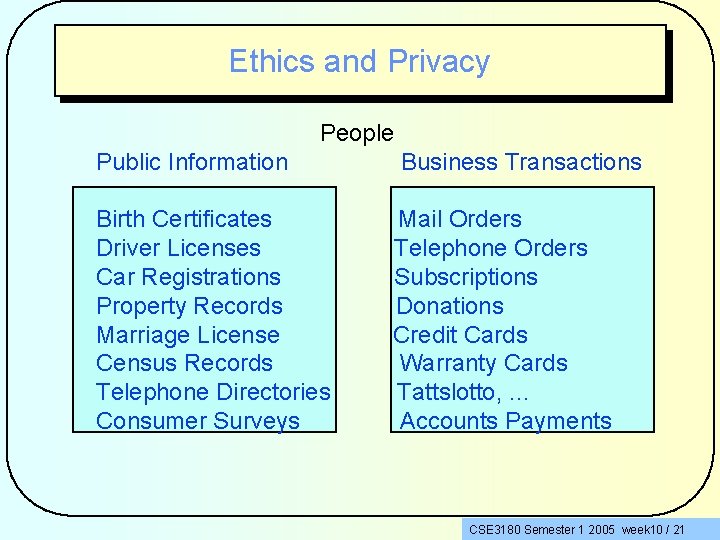
Ethics and Privacy People Public Information Birth Certificates Driver Licenses Car Registrations Property Records Marriage License Census Records Telephone Directories Consumer Surveys Business Transactions Mail Orders Telephone Orders Subscriptions Donations Credit Cards Warranty Cards Tattslotto, . . . Accounts Payments CSE 3180 Semester 1 2005 week 10 / 21
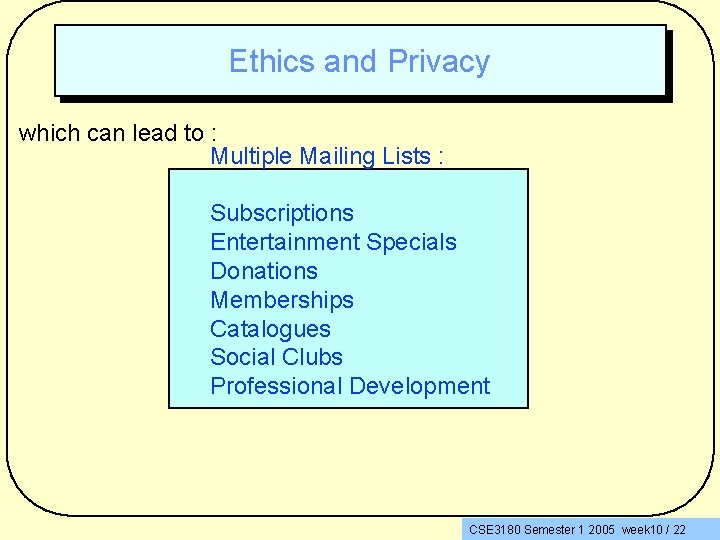
Ethics and Privacy which can lead to : Multiple Mailing Lists : Subscriptions Entertainment Specials Donations Memberships Catalogues Social Clubs Professional Development CSE 3180 Semester 1 2005 week 10 / 22
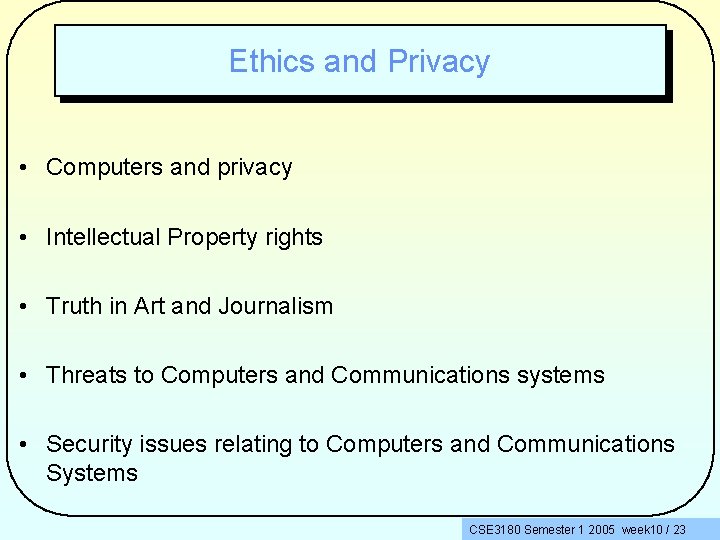
Ethics and Privacy • Computers and privacy • Intellectual Property rights • Truth in Art and Journalism • Threats to Computers and Communications systems • Security issues relating to Computers and Communications Systems CSE 3180 Semester 1 2005 week 10 / 23
Ethics and Privacy • Ethics: A set of principles which govern the conduct of an individual or group • Privacy: The right of people not to reveal information about themselves, the right to keep personal information from being misused • Electronic invasion of personal data has become a serious ethical issue CSE 3180 Semester 1 2005 week 10 / 24
Ethics and Privacy • Invasion of Privacy : Would you agree to : Your personal shopping habits, your income, to be available to any number of businesses ? Your medical records being used by your employer as one of the means of making decision regarding promotions, hiring, redundancy ? CSE 3180 Semester 1 2005 week 10 / 25
Ethics, How do. Privacy you feeland about Security this ? • Draw 98 is a Microsoft product • It is available from the Microsoft Web site (so is other software) • It is part of the progression to server based software • Downloading Draw 98 initiates a scan of the user’s hard disk for components of the Office suite so that ‘the installer (software) knows what you need to make Draw 98 run correctly” • Full marks to Microsoft for innovation ? ? CSE 3180 Semester 1 2005 week 10 / 26
Ethics • Ethics, noun – pertaining to right or wrong in conduct • Ethical, adj – in accordance with the rules or standards for right conduct or practice, especially the standards of a profession – the rules of conduct recognised in a particular class of human actions CSE 3180 Semester 1 2005 week 10 / 27
Ethics – The overriding principles are • fairness • integrity • openness • responsibility • commitment to accuracy and truth CSE 3180 Semester 1 2005 week 10 / 28
Ethics – Members of a profession should act always for the maintenance for the community, rather than for sectional interests – This includes the exposure of hypocrisy, falsehoods or double standards – Members should seek to present fair, balanced and accurate material – Confidentiality must be protected at all costs CSE 3180 Semester 1 2005 week 10 / 29
Ethics – Fair and honest means should be used to obtain material, including information. Misrepresentations and the user of concealed equipment or surveillance devices should be avoided – Members of an organisation should have equal opportunity to develop their skills – The employer organisation is obliged to provide a healthy and safe working environment CSE 3180 Semester 1 2005 week 10 / 30
Ethics – Activities outside workhours may be seen to have an impact on the individual’s or the employer organisation – No person should be harassed or discriminated against on grounds of gender, colour, race, nationality, religious belief, impairment, age, height, weight, marital status, appearance or sexual preference – Managers or others with access to personal information relating to other members are required to treat such information as confidential, and not to disclose such information except in the course of discharging formal responsibilities CSE 3180 Semester 1 2005 week 10 / 31
Ethics • Members should not use their position to obtain private benefit for themselves or others • Members should not be influenced by family or other personal relationships • Members should be alert to conflict of interests which may arise and declare to a senior person or officer any real or perceived conflict of interest which arises or is foreseen CSE 3180 Semester 1 2005 week 10 / 32
Ethics • Members engaged in the development of software or hardware or communications or other Information Technology facility and who believe they have a interest on such development, maintenance, or installation should acknowledge such interest • Members in doubt as to whether a conflict of interest exists should consult a senior officer • No payment, gift or other advantage which may be seen to undermine accuracy, fairness or independence is to be accepted. CSE 3180 Semester 1 2005 week 10 / 33
Ethics • Other people’s material is not to be reproduced without reference and acknowledgement • The source of material obtained form another organisation should be acknowledged CSE 3180 Semester 1 2005 week 10 / 34
Ethics The Australian Computer Society has this to say : • An essential characteristic of a profession is the need for its members to abide by a Code of Ethics. The Society requires its members to subscribe to a set of values and ideals which uphold and advance the honour, dignity and effectiveness of the profession of information technology CSE 3180 Semester 1 2005 week 10 / 35
Ethics • In keeping with this statement, a member must – be honest, forthright and impartial – serve the community – strive to increase the competency and prestige of the profession – use special knowledge and skill for the advancement of human welfare CSE 3180 Semester 1 2005 week 10 / 36
Ethics - ACS • Competence (part only of the Standards of Conduct) – A member must endeavour to provide products and services which match the operational and financial needs of my clients and employers – A member must give value for money in the services and products I supply – A member must respect and protect the clients’ and employers’ proprietary interests CSE 3180 Semester 1 2005 week 10 / 37
Ethics - ACS • Social Implications – A member must protect and promote the health and safety of those affected by her/his work – A member must consider and respect people’s privacy which might be affected by a member’s work – A member must respect employees and refrain from treating them unfairly The full statement of the code of ethics is available at www. acs. org. au/national/pospaper/acs 131. htm CSE 3180 Semester 1 2005 week 10 / 38
Ethics Acknowledgements to The Age Code of Conduct The Australian Computer Society CSE 3180 Semester 1 2005 week 10 / 39
Ethics and Privacy Rules and Laws on Privacy: Privacy Act 1974, amended 2001 Freedom of Information Act Fair Credit Reporting Act Right to Financial Privacy Act Computer Fraud and Abuse Act Federal Data-Matching Program (Assistance and Tax Act) CSE 3180 Semester 1 2005 week 10 / 40
Ethics and Privacy Intellectual Property Rights: Products of the human mind and includes tangible (i. e. ‘real products’) and intangible property (i. e. ‘ideas’) 3 common methods of ‘protection’ : Patents (inventions) Trade Secrets (formal or method of conducting business) Copyright ( Laws which prohibit copying of intellectual property without the permission of the copyright holder) CSE 3180 Semester 1 2005 week 10 / 41
Ethics and Privacy Piracy: Theft or unauthorised distribution or use Software Piracy: Unauthorised copying of copyright software Network Piracy: The use of electronic networks to distribute unauthorised copyright materials in digitised form Plagiarism: Is the use of another’s text, findings, interpretations and presenting it as one’s own original work Also involved here is the ownership of images and sounds : for example Walt Disney animations and ‘speech/sound’ CSE 3180 Semester 1 2005 week 10 / 42
Ethics and Privacy Art and Journalism: Manipulation of Sound - mixing, overlays, reductions, deletions, substitution Manipulation of phonographs and video recordings - ‘touch ups’, overlays, repositioning, insertions, deletions, enhancing, minimising Morphing - construction of an image (at pixel level) to superimpose, enhance, overlay, redirect, recolour, animate, animation with voice commentary, disjoint morphing ( a person’s head which is rotated - change of facial attitude) CSE 3180 Semester 1 2005 week 10 / 43
Ethics and Privacy Questions : What is ‘REAL’ Which values are ‘ACCURATE’ Which data can MANIPULATE people ? CSE 3180 Semester 1 2005 week 10 / 44
Public Safety Aspects – Factory / Production Processes and Controls – Dangerous Materials – Power Generation and Distribution - Power Surges – Weaponry – Transport - Road, Rail, Sea, Air – Computer Controlled Communications CSE 3180 Semester 1 2005 week 10 / 45
A Mind Bender The following exercise is based on advanced mathematics and mental gymnastics 1. Write down the number of times per week night that you eat out (if you don’t, write down 0) 2. Multiply this value by 2 3. Add 5 4. Multiply the result of (3) by 50 5. If you have already had your birthday this year add 1750 If not, add 1749 6. Subtract your year of birth 7. You should have a 3 digit number. The first digit should be the same as in (1) above, and the other 2 are your age. CSE 3180 Semester 1 2005 week 10 / 46
CSE 3180 Semester 1 2005 week 10 / 47
Information Technology A few comments about this discipline In the Business environment, the use of Information Technology is the primary means to express and execute business strategy Information Technology executives who don’t understand IT will place their companies at risk of failure Building and sustaining competitive advantage is tightly linked to the intelligent use of Information Technology CSE 3180 Semester 1 2005 week 10 / 48
The Information Age Some characteristics: The computer is the dominant technology Computing intelligence is dispersed into all aspects which can be improved by being ‘smart’. Computerisation is called mechatronics (mechanical electronics) Technology gives products the capability to be customised and made responsive to each user CSE 3180 Semester 1 2005 week 10 / 49
The Information Age The output of the current period is knowledge Products which are ‘information rich’ produces products which have a high level of attraction to users The basis of wealth is information. Information drives the creation of knowledge > which drives strategic actions > which create temporary competitive advantage for businesses. CSE 3180 Semester 1 2005 week 10 / 50
The Information Age The ‘knowledge worker’ is the key to information A large part of the workforce is involved in collecting, processing and communication information The means of ‘moving things’ is communications networks Logistics is concerned with moving bits representing data and information as opposed to moving physical products CSE 3180 Semester 1 2005 week 10 / 51
The Information Age The market place (where people gather to buy and sell products and services) has shifted from the physical marketplace to the marketspace - which is an electronic market place in cyberspace) Information based improvements become the main method of creating new products and services The value of existing goods and services is enhanced by information enhancement CSE 3180 Semester 1 2005 week 10 / 52
And the Customers ? Customers are marketed, sold and serviced as individuals, not as statistical averages An accessible information highway, the Internet, permits global and interactive access to multimedia information CSE 3180 Semester 1 2005 week 10 / 53
And People ? Convergence of information forms leads to ‘new’ ways of working and living Time and space constraints of markets collapse People live where they please They work with remote employers They purchase products from local or distant providers as required CSE 3180 Semester 1 2005 week 10 / 54
Anything Else ? Yes. The Information Age has introduced radical shifts in the basis of wealth. Industrial Age products were physical Information Age products are virtual Industrial Age focus was the automation of labour Information Age focus is the creation and exploitation of knowledge CSE 3180 Semester 1 2005 week 10 / 55
The Industrial vs the Information Age Industrial Age : Information flow was physical and paper based Information Age : Information flow is virtual and digitised The result is the movement from manufacturing to knowledge as the key to societal wealth The end result is the global economy becoming merged and information-centric = globalisation ? CSE 3180 Semester 1 2005 week 10 / 56
The Information Age 5 Primary Perspectives: 1. Technology Continued innovation in information technologies results in information technology addressing all forms of life 2. Economics The economy becomes information-centered. The creation of wealth is tied to the ability to create new information-based products and amend existing products with information 3. Employment There is a shift in numbers to knowledge workers. People make their living in creating, moving, analysing, interpreting or distributing information CSE 3180 Semester 1 2005 week 10 / 57
The Information Age 4. Spatial World networking of computers leads to the collapse of the traditional market constraints of time and space. The world becomes a global marketspace 5. Cultural Society becomes media-laden. Information is readily available in multimedia formats, it can be customised easily and accurately, and it is interactive We expect information in forms which are readily accessible and convenient CSE 3180 Semester 1 2005 week 10 / 58
The Information Age 3 associated technology changes drive the information age 1. Digitisation of information - regardless of form (audio, data, image, video) All information shares the same basis of construction It becomes • transportable • interoperable • subject to interactive manipulation by the user CSE 3180 Semester 1 2005 week 10 / 59
The Information Age 2. Rapidly decreasing cost of computing This ensures that computing will become available everywhere (ubiquitous) cost attractive 3. Broadband Communications Multimedia is storage intensive and time sensitive Gigabit communications (lecture 9) will give rise to efficiency and effectiveness of work CSE 3180 Semester 1 2005 week 10 / 60
The Information Age The Implications ? Companies will engage in IT based high levels of competition and aggressiveness. The use of IT will be the primary expression of business strategy Business will need highly flexible information systems The objective will be to attract and/or retain customers AND to deter competitors CSE 3180 Semester 1 2005 week 10 / 61
The Information Age Business is highly competitive Success is the objective Success can be achieved by advantage Advantage is expressed through the power and agility of information technology I. T. is now not seen as an expense - it is the means of attracting customers adding value to products improving productivity beating the competition CSE 3180 Semester 1 2005 week 10 / 62
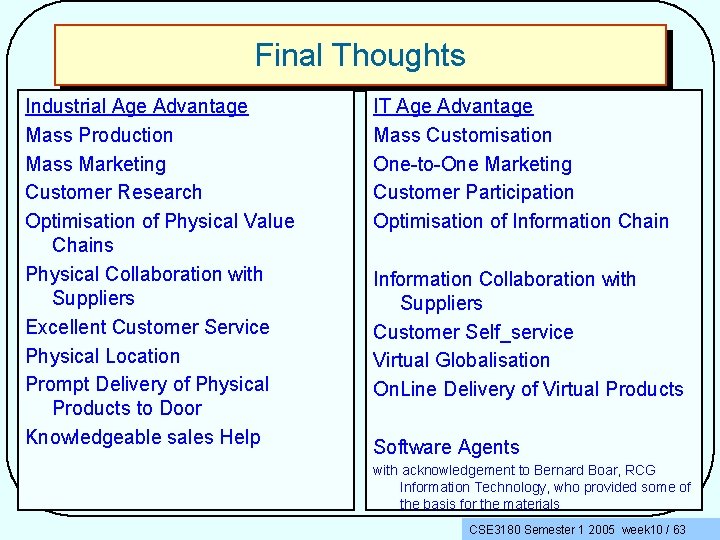
Final Thoughts Industrial Age Advantage Mass Production Mass Marketing Customer Research Optimisation of Physical Value Chains Physical Collaboration with Suppliers Excellent Customer Service Physical Location Prompt Delivery of Physical Products to Door Knowledgeable sales Help IT Age Advantage Mass Customisation One-to-One Marketing Customer Participation Optimisation of Information Chain Information Collaboration with Suppliers Customer Self_service Virtual Globalisation On. Line Delivery of Virtual Products Software Agents with acknowledgement to Bernard Boar, RCG Information Technology, who provided some of the basis for the materials CSE 3180 Semester 1 2005 week 10 / 63
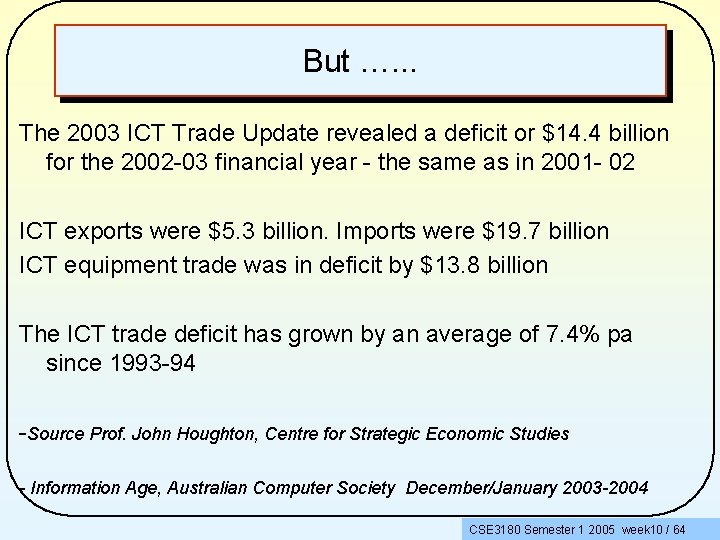
But …. . . The 2003 ICT Trade Update revealed a deficit or $14. 4 billion for the 2002 -03 financial year - the same as in 2001 - 02 ICT exports were $5. 3 billion. Imports were $19. 7 billion ICT equipment trade was in deficit by $13. 8 billion The ICT trade deficit has grown by an average of 7. 4% pa since 1993 -94 -Source Prof. John Houghton, Centre for Strategic Economic Studies - Information Age, Australian Computer Society December/January 2003 -2004 CSE 3180 Semester 1 2005 week 10 / 64
- Slides: 64