Toward Practical Public Key Anti Counterfeiting for LowCost
Toward Practical Public Key Anti. Counterfeiting for Low-Cost EPC Tags Alex Arbit, Avishai Wool, Yossi Oren, IEEE RFID April 2011 1
Outline Anti-counterfeiting for RFID ¡ Cryptographic anti-counterfeiting ¡ Lab system setup ¡ WIPR protocol flow ¡ Implementation results ¡ Optimizations ¡ Summary & Future work ¡ 2
RFID EPC Supply chain ¡ Counterfeiting is considered one of the greatest treats to the world’s economy ¡ Electronic Product Code (EPC) is designed to guarantee uniqueness of every RFID Tag in Supply Chain ¡ Problem: Ø Standard RFID EPC-based supply chain is generally unprotected and may become an easy target for the adversary 3
RFID Tags Anti-counterfeiting methods ¡ Unique ID (EPC) Ø ¡ A world-wide readers network database to trace compromised tag IDs (track-and-trace) Ø Ø ¡ Unencrypted value – an easy prey for adversary! Essential cooperativeness of all supply chains Loss of information privacy Cryptographic solution Ø Ø Ø Asymmetric solution – Public key on Tag Strong system protection – “breaking” one Tag doesn’t compromise the supply chain Was considered not feasible for RFID chain due to high resource consumption on tag side and long execution times! 4
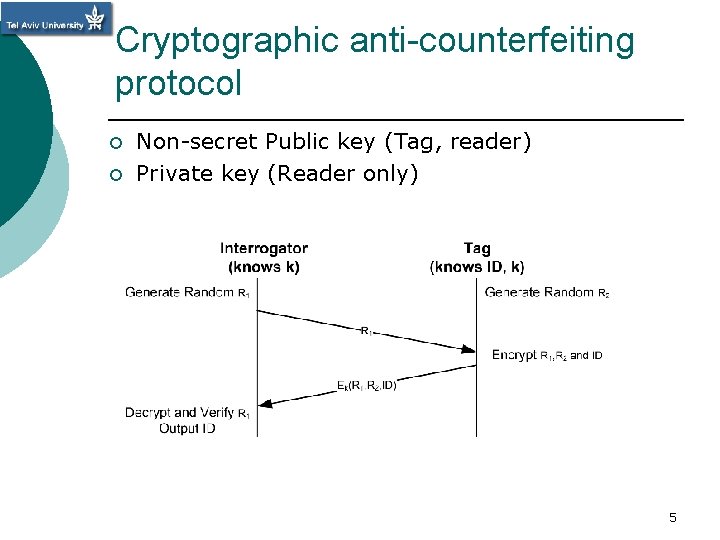
Cryptographic anti-counterfeiting protocol ¡ ¡ Non-secret Public key (Tag, reader) Private key (Reader only) 5
Asymmetric cryptographic approach ¡ Tag bears only a partial (public) key -> can only encrypt messages Ø ¡ System not compromised even if a certain tag is Reader possesses both key parts -> can encrypt and decrypt Ø Ø Only one private key is required for entire chain No need for a constant link to a central server 6
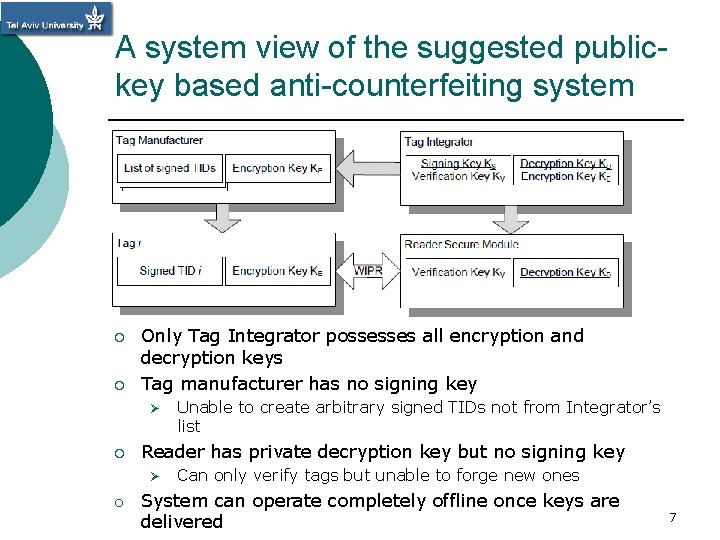
A system view of the suggested publickey based anti-counterfeiting system ¡ ¡ Only Tag Integrator possesses all encryption and decryption keys Tag manufacturer has no signing key Ø ¡ Unable to create arbitrary signed TIDs not from Integrator’s list Reader has private decryption key but no signing key Ø Can only verify tags but unable to forge new ones o System can operate completely offline once keys are delivered 7
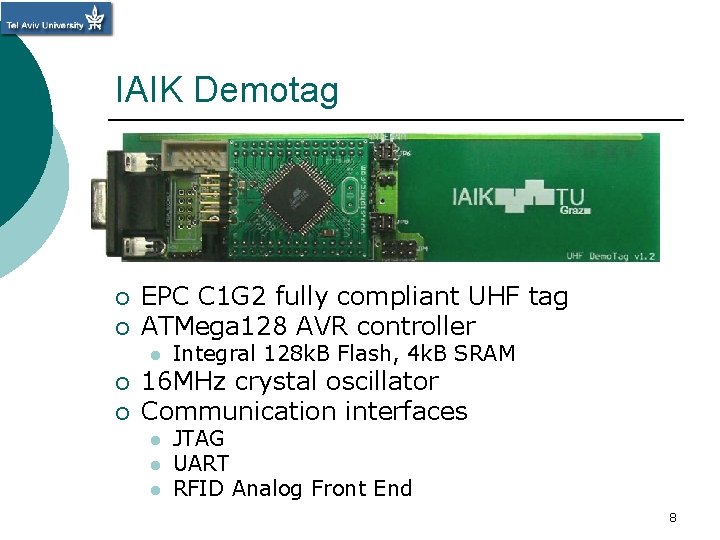
IAIK Demotag ¡ ¡ EPC C 1 G 2 fully compliant UHF tag ATMega 128 AVR controller l ¡ ¡ Integral 128 k. B Flash, 4 k. B SRAM 16 MHz crystal oscillator Communication interfaces l l l JTAG UART RFID Analog Front End 8
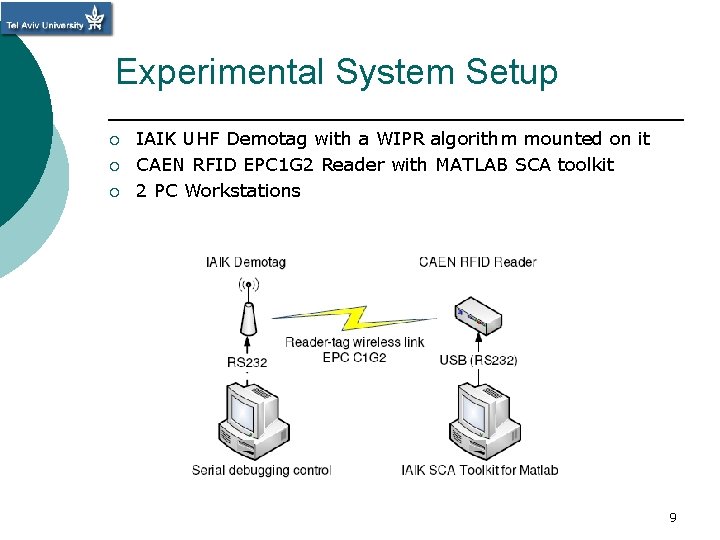
Experimental System Setup ¡ ¡ ¡ IAIK UHF Demotag with a WIPR algorithm mounted on it CAEN RFID EPC 1 G 2 Reader with MATLAB SCA toolkit 2 PC Workstations 9
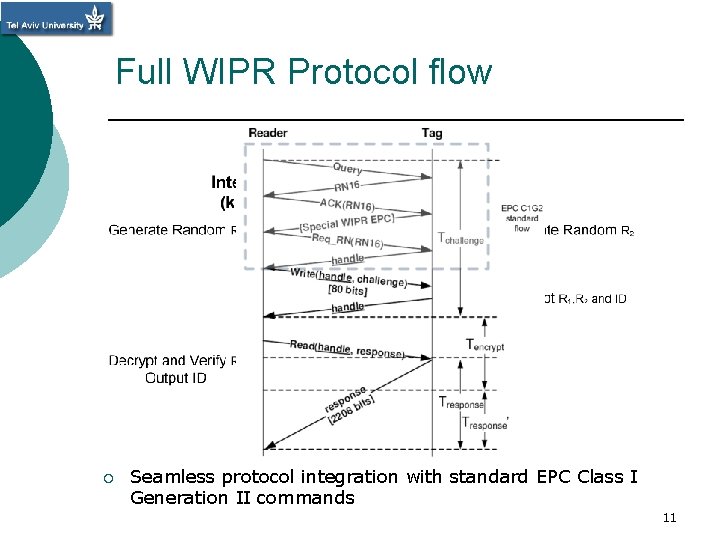
Full WIPR Protocol flow ¡ Seamless protocol integration with standard EPC Class I Generation II commands 11
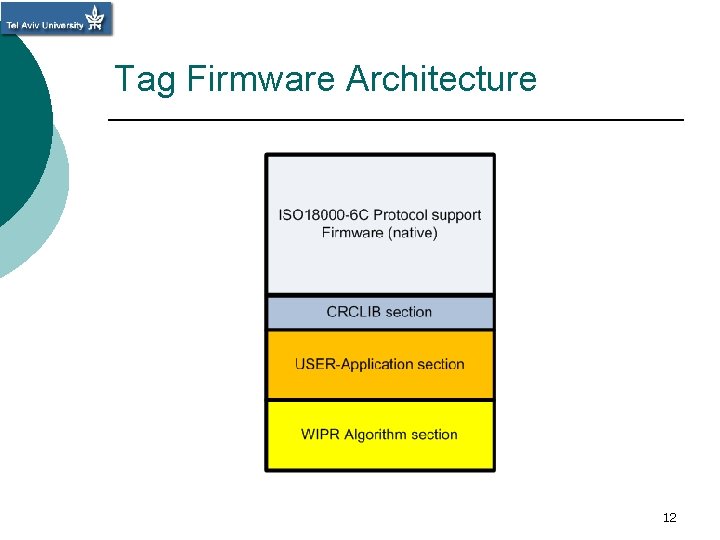
Tag Firmware Architecture 12
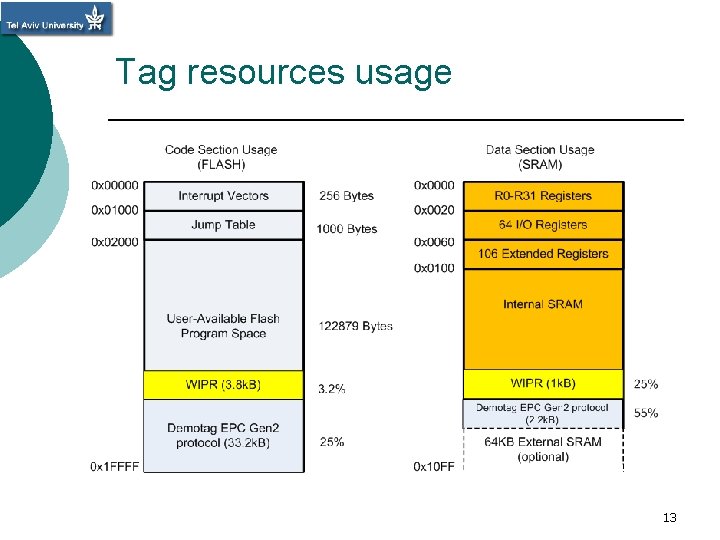
Tag resources usage 13
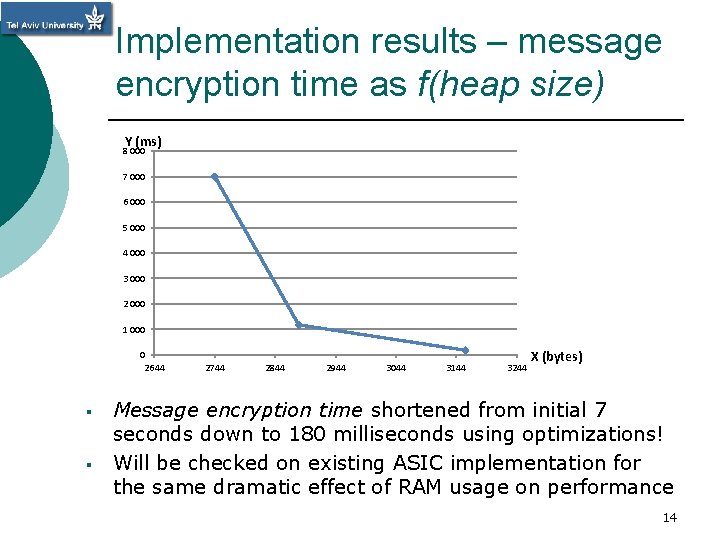
Implementation results – message encryption time as f(heap size) Y (ms) 8 000 7 000 6 000 5 000 4 000 3 000 2 000 1 000 0 2644 § § 2744 2844 2944 3044 3144 3244 X (bytes) Message encryption time shortened from initial 7 seconds down to 180 milliseconds using optimizations! Will be checked on existing ASIC implementation for the same dramatic effect of RAM usage on performance 14
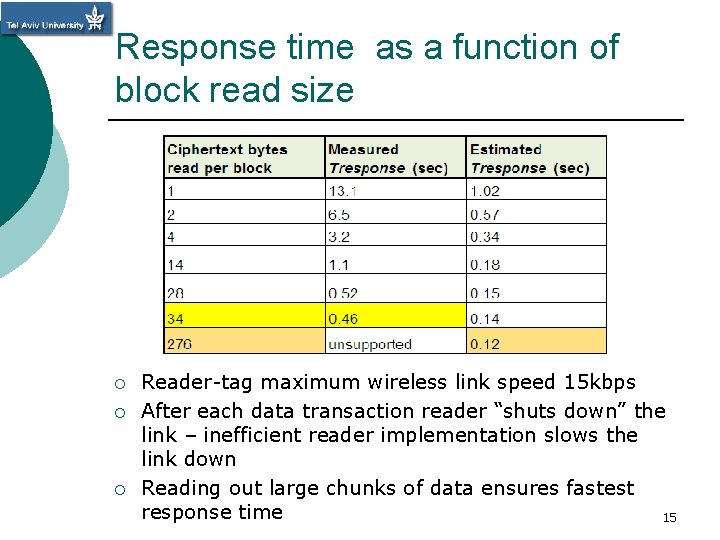
Response time as a function of block read size ¡ ¡ ¡ Reader-tag maximum wireless link speed 15 kbps After each data transaction reader “shuts down” the link – inefficient reader implementation slows the link down Reading out large chunks of data ensures fastest response time 15
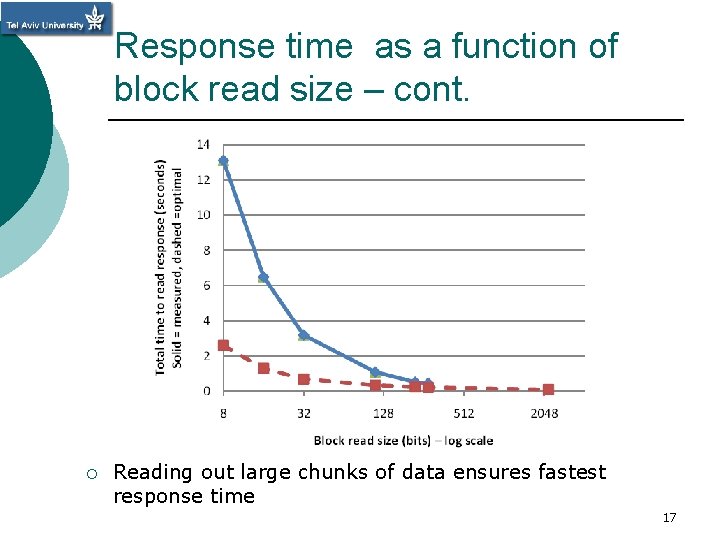
Response time as a function of block read size – cont. ¡ Reading out large chunks of data ensures fastest response time 17
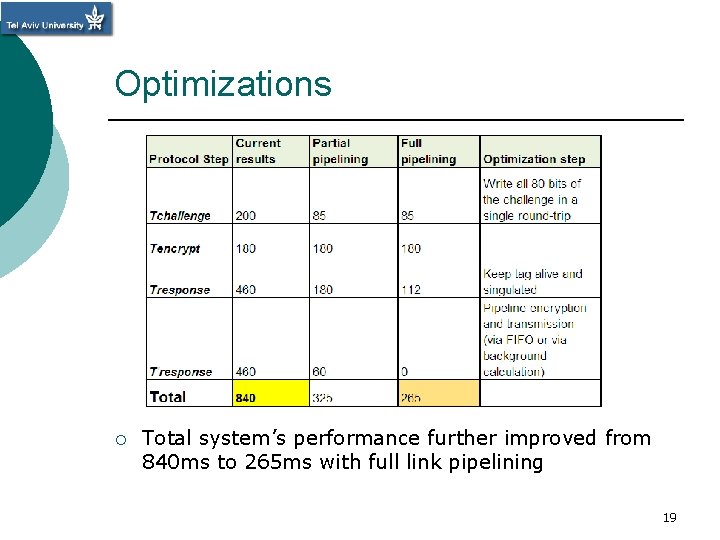
Optimizations Total link time 900 800 700 600 T response T encrypt Tchallenge 500 400 300 200 100 0 1 ¡ 2 3 Total system’s performance further improved from 840 ms to 265 ms with full link pipelining 19
Summary ¡ A full strength Public key Crypto system is implemented on standard EPC C 1 G 2 Tag for RFID supply chain! ¡ RAM usage presents a resource vs. message encrypt time latency trade-off. ¡ A better use of air interface by the reader side squeeze the total execution time down to 0. 265 s for full pipelining. ¡ System designed for fully off-line operation can be further strengthened by use of standard reader track-and-trace with no additional cost on Tag side. 20
Future Work ¡ Adding a small amount of RAM to existing ASIC implementation to compare performances and benchmarking ¡ Integrate suggested anti-counterfeiting solution with current EPC C 1 G 2 tag chips ¡ Work with other reader vendors to see if they handle a standard EPC Class I Generation II more efficiently 21
Thank You! ! תודה רבה 22
- Slides: 19