TOR The Onion Routing project By Alex and

TOR The Onion Routing project By Alex and Daniel
What is Tor TOR- The Onion Routing project To protect the personal privacy of its users, freedom and ability to conduct confidential communication by keeping their internet activities unmonitored. Free and open-source software for anonymous communication Difficult to trace the internet activity for Tor users Tor uses Onion routing a technique to encrypt messages Bounces around connections between different routers so it's hard to track and it provides anonymity
A brief history of how TOR came into Existence Idea of Onion Routing began in the mid 1990 s by the U. S. Naval Research Lab for a decentralized network. Lack of security on the internet and its ability to be used for tracking and surveillance was a concern Early 2000 s Roger Dingledine, began working on an an online routing project with Paul Syverson called the project TOR Network operated by entities with diverse interests and trust assumptions and to maximize transparency October 2002 the TOR network was initially deployed
A brief history of how TOR came into Existence In 2005, Tor begins gaining popularity among activists and techsavvy users interested in privacy In 2008 the Tor browser was announced, being a modified version Mozilla Firefox made Tor more accessible to everyday users and activists. By 2018, over 2 million unique users use Tor everyday
Why would anyone use TOR To: ● ● Hide your IP and location Hide your internet traffic from ISP and onlookers Access Onion services Host a Onion service without anyone knowing your location or identity
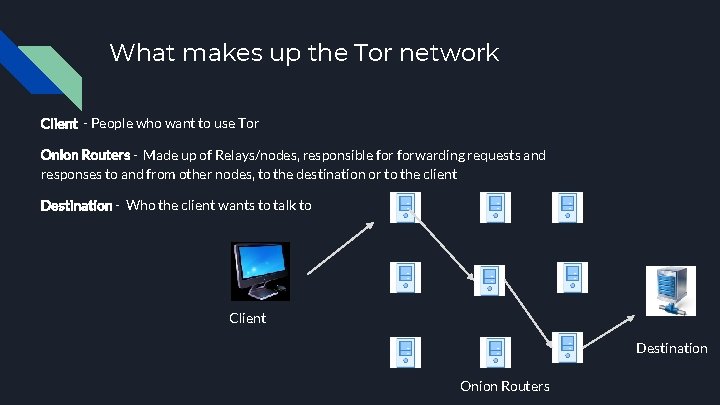
What makes up the Tor network Client - People who want to use Tor Onion Routers - Made up of Relays/nodes, responsible forwarding requests and responses to and from other nodes, to the destination or to the client Destination - Who the client wants to talk to Client Destination Onion Routers
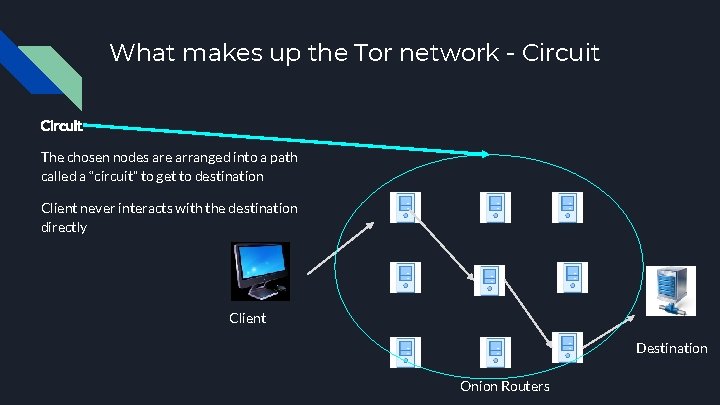
What makes up the Tor network - Circuit The chosen nodes are arranged into a path called a “circuit” to get to destination Client never interacts with the destination directly Client Destination Onion Routers
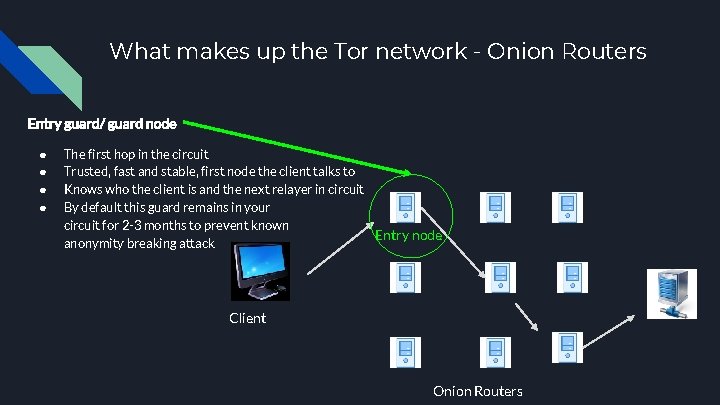
What makes up the Tor network - Onion Routers Entry guard/ guard node ● ● The first hop in the circuit Trusted, fast and stable, first node the client talks to Knows who the client is and the next relayer in circuit By default this guard remains in your circuit for 2 -3 months to prevent known Entry node anonymity breaking attack Client Onion Routers
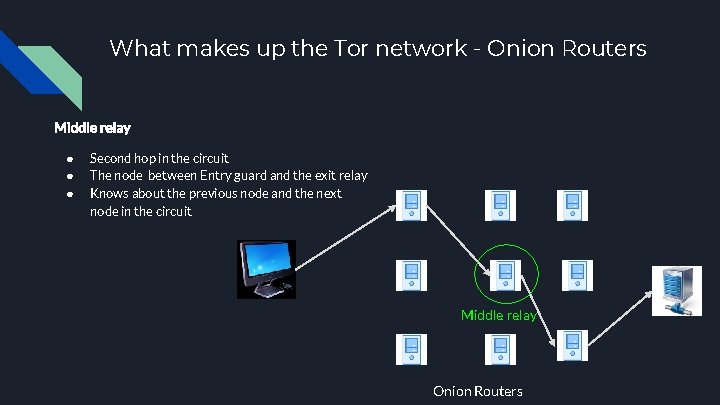
What makes up the Tor network - Onion Routers Middle relay ● ● ● Second hop in the circuit The node between Entry guard and the exit relay Knows about the previous node and the next node in the circuit Middle relay Onion Routers
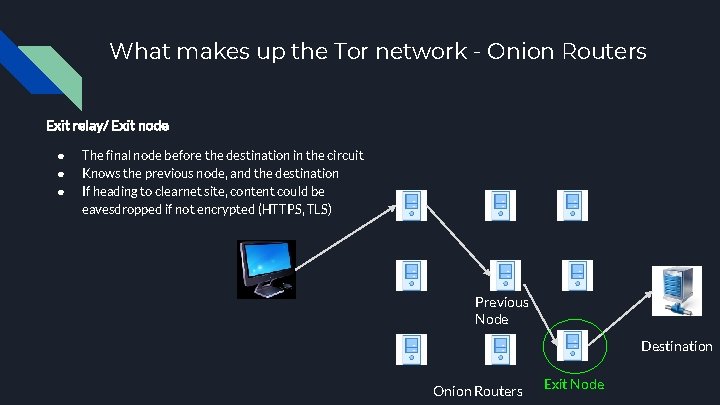
What makes up the Tor network - Onion Routers Exit relay/ Exit node ● ● ● The final node before the destination in the circuit Knows the previous node, and the destination If heading to clearnet site, content could be eavesdropped if not encrypted (HTTPS, TLS) Previous Node Destination Onion Routers Exit Node
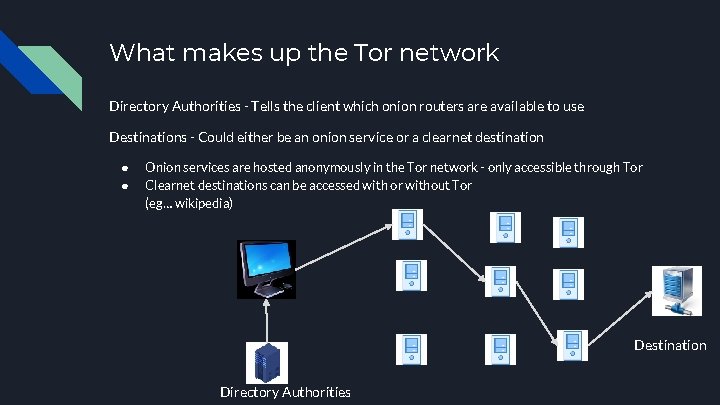
What makes up the Tor network Directory Authorities - Tells the client which onion routers are available to use Destinations - Could either be an onion service or a clearnet destination ● ● Onion services are hosted anonymously in the Tor network - only accessible through Tor Clearnet destinations can be accessed with or without Tor (eg… wikipedia) Destination Directory Authorities
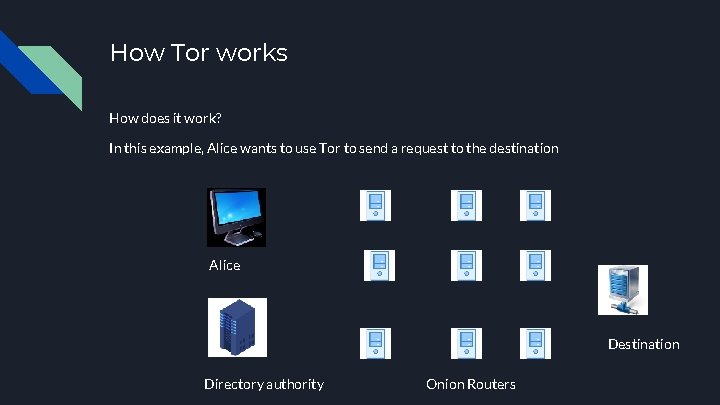
How Tor works How does it work? In this example, Alice wants to use Tor to send a request to the destination Alice Destination Directory authority Onion Routers
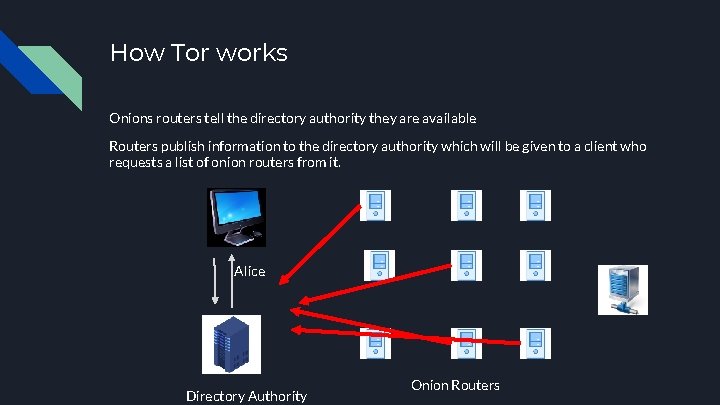
How Tor works Onions routers tell the directory authority they are available Routers publish information to the directory authority which will be given to a client who requests a list of onion routers from it. Alice Directory Authority Onion Routers
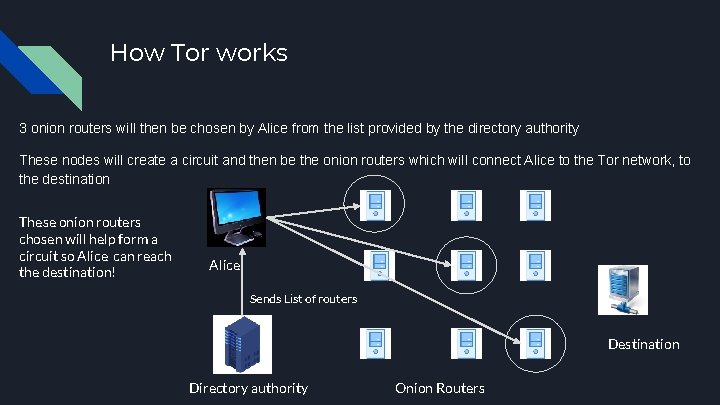
How Tor works 3 onion routers will then be chosen by Alice from the list provided by the directory authority These nodes will create a circuit and then be the onion routers which will connect Alice to the Tor network, to the destination These onion routers chosen will help form a circuit so Alice can reach the destination! Alice Sends List of routers Destination Directory authority Onion Routers
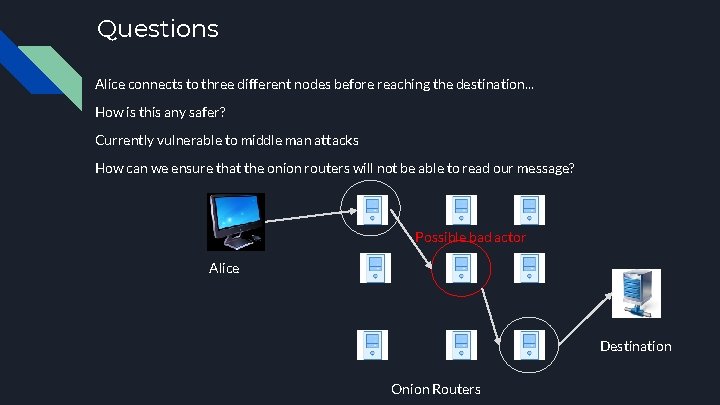
Questions Alice connects to three different nodes before reaching the destination. . . How is this any safer? Currently vulnerable to middle man attacks How can we ensure that the onion routers will not be able to read our message? Possible bad actor Alice Destination Onion Routers
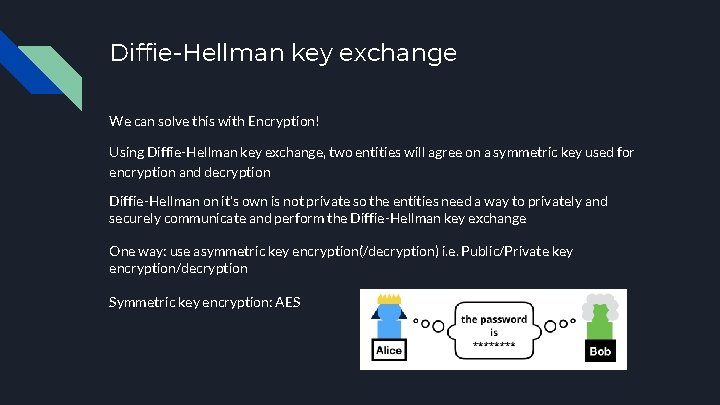
Diffie-Hellman key exchange We can solve this with Encryption! Using Diffie-Hellman key exchange, two entities will agree on a symmetric key used for encryption and decryption Diffie-Hellman on it’s own is not private so the entities need a way to privately and securely communicate and perform the Diffie-Hellman key exchange One way: use asymmetric key encryption(/decryption) i. e. Public/Private key encryption/decryption Symmetric key encryption: AES
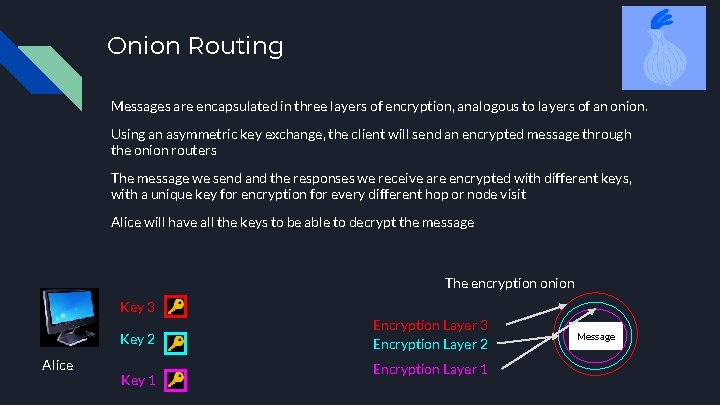
Onion Routing Messages are encapsulated in three layers of encryption, analogous to layers of an onion. Using an asymmetric key exchange, the client will send an encrypted message through the onion routers The message we send and the responses we receive are encrypted with different keys, with a unique key for encryption for every different hop or node visit Alice will have all the keys to be able to decrypt the message The encryption onion Key 3 Key 2 Alice Key 1 Encryption Layer 3 Encryption Layer 2 Encryption Layer 1 Message
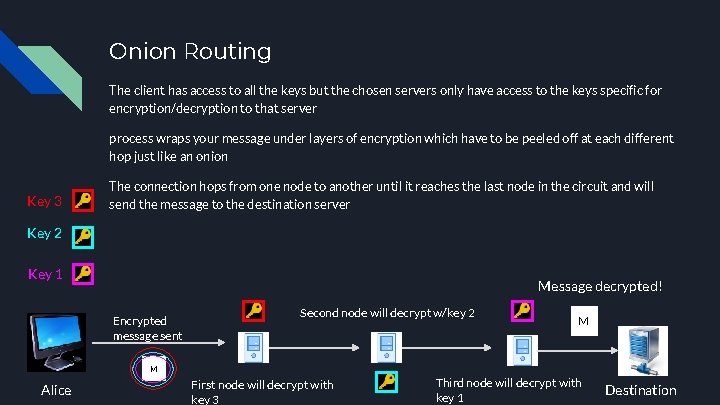
Onion Routing The client has access to all the keys but the chosen servers only have access to the keys specific for encryption/decryption to that server process wraps your message under layers of encryption which have to be peeled off at each different hop just like an onion Key 3 The connection hops from one node to another until it reaches the last node in the circuit and will send the message to the destination server Key 2 Key 1 Message decrypted! Encrypted message sent Second node will decrypt w/key 2 M M Alice First node will decrypt with key 3 Third node will decrypt with key 1 Destination
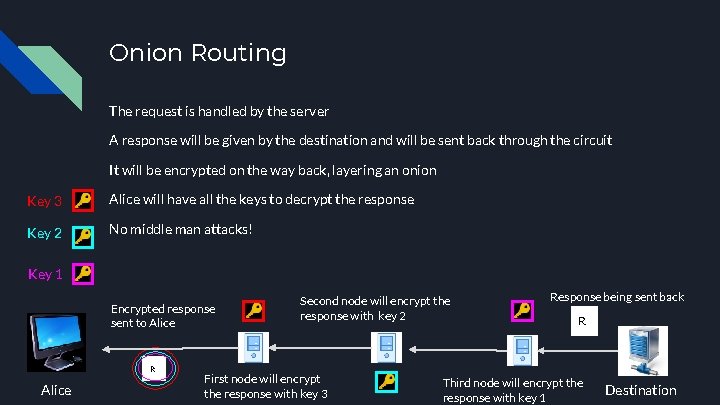
Onion Routing The request is handled by the server A response will be given by the destination and will be sent back through the circuit It will be encrypted on the way back, layering an onion Key 3 Alice will have all the keys to decrypt the response Key 2 No middle man attacks! Key 1 Encrypted response sent to Alice R Alice Second node will encrypt the response with key 2 First node will encrypt the response with key 3 Response being sent back R Third node will encrypt the response with key 1 Destination
Onion routing in detail If you are interested in onion routing, Awesome computerphile video on it: https: //www. youtube. com/watch? v=QRYzre 4 bf 7 I
ONION Services (hidden services) Conceptually similar to regular web services, but hosted and only accessible within the TOR network. Added security benefits: ● ● ● Host’s identity is hidden Traffic already encrypted, no need for HTTPS Various methods of authenticating services Hosting might even be easier than regular web hosting! AWS ONION
ONION Services; how they look ● ● ● No IP or domain name; ONION addresses instead Randomly generated string containing identity public key of an ONION service 16 or 56 characters depending if V 2 or V 3 Clients use this address to find more a way to connect to this service
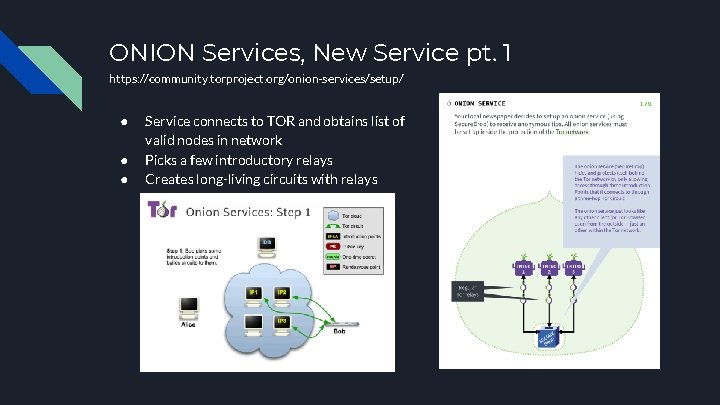
ONION Services, New Service pt. 1 https: //community. torproject. org/onion-services/setup/ ● ● ● Service connects to TOR and obtains list of valid nodes in network Picks a few introductory relays Creates long-living circuits with relays
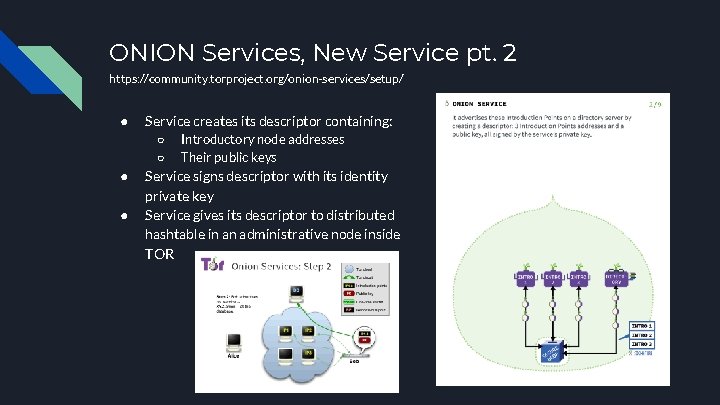
ONION Services, New Service pt. 2 https: //community. torproject. org/onion-services/setup/ ● Service creates its descriptor containing: ○ ○ ● ● Introductory node addresses Their public keys Service signs descriptor with its identity private key Service gives its descriptor to distributed hashtable in an administrative node inside TOR

ONION Services, New Service DONE! https: //community. torproject. org/onion-services/setup/
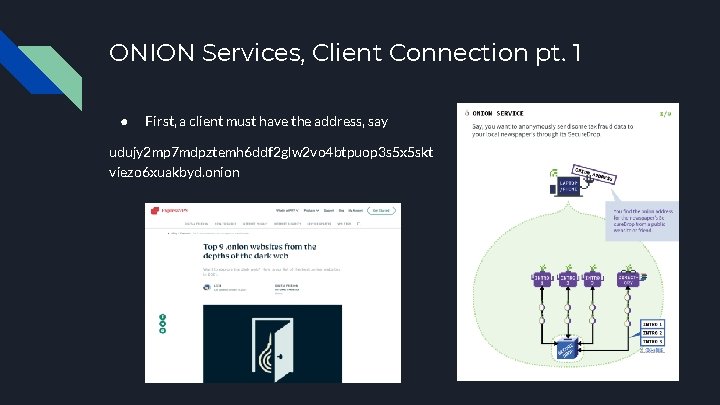
ONION Services, Client Connection pt. 1 ● First, a client must have the address, say udujy 2 mp 7 mdpztemh 6 ddf 2 glw 2 vo 4 btpuop 3 s 5 x 5 skt viezo 6 xuakbyd. onion
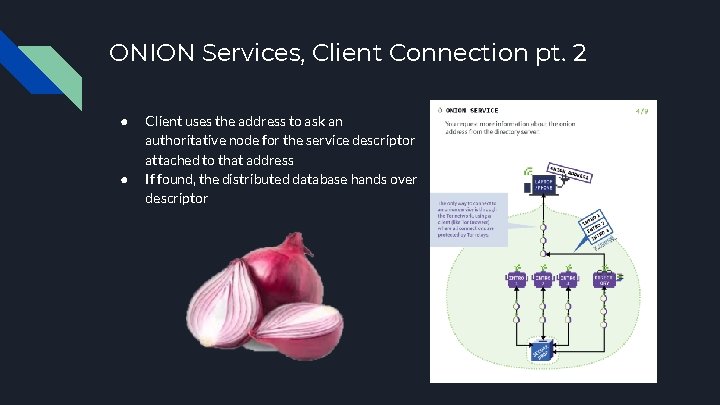
ONION Services, Client Connection pt. 2 ● ● Client uses the address to ask an authoritative node for the service descriptor attached to that address If found, the distributed database hands over descriptor
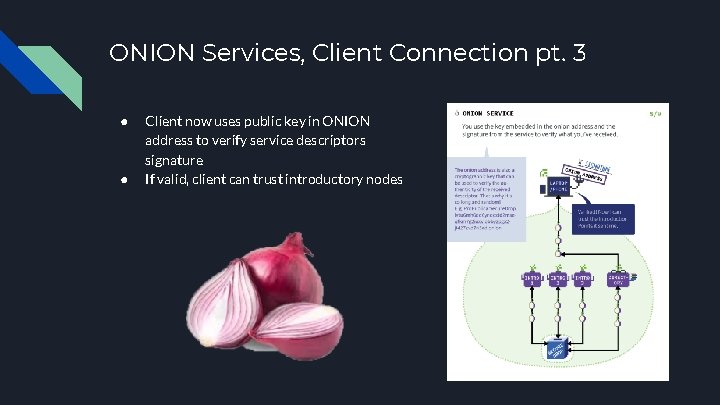
ONION Services, Client Connection pt. 3 ● ● Client now uses public key in ONION address to verify service descriptors signature If valid, client can trust introductory nodes
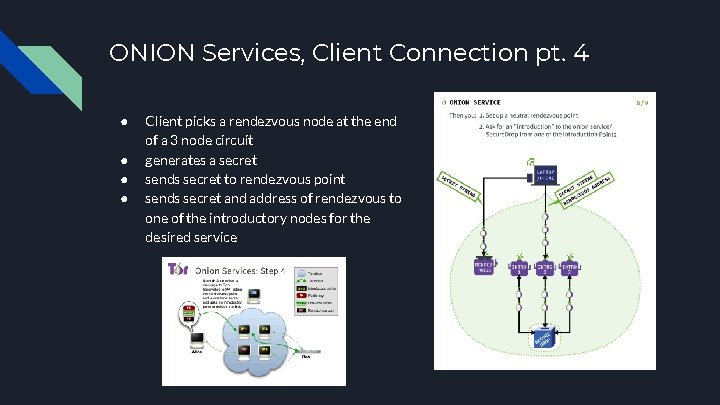
ONION Services, Client Connection pt. 4 ● ● Client picks a rendezvous node at the end of a 3 node circuit generates a secret sends secret to rendezvous point sends secret and address of rendezvous to one of the introductory nodes for the desired service
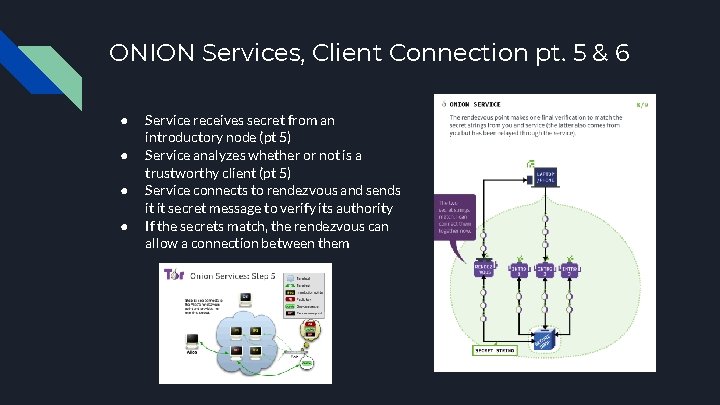
ONION Services, Client Connection pt. 5 & 6 ● ● Service receives secret from an introductory node (pt 5) Service analyzes whether or not is a trustworthy client (pt 5) Service connects to rendezvous and sends it it secret message to verify its authority If the secrets match, the rendezvous can allow a connection between them
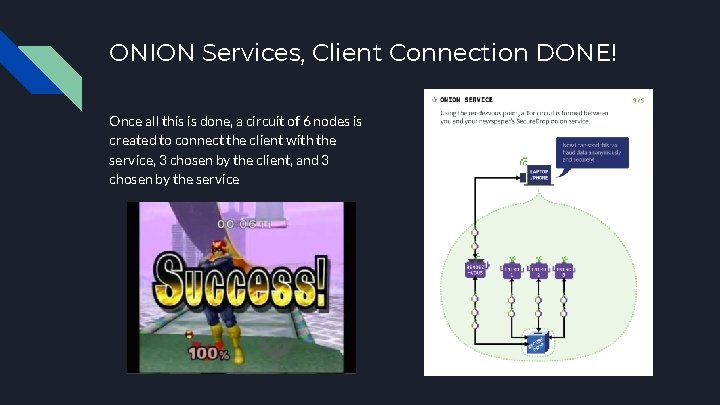
ONION Services, Client Connection DONE! Once all this is done, a circuit of 6 nodes is created to connect the client with the service, 3 chosen by the client, and 3 chosen by the service
Vulnerabilities TOR is NOT bulletproof! Fairly secure but there a few noticeable weaknesses in the TOR network: ● ● Eavesdropping: First and Last node in circuit containing info about user and host Attacking Authoritative Nodes: Puts the network in a stale state, possible crashing parts of it Careless users can also fall prey to other attacks or exploits like unsafe protocols, or fingerprinting ��
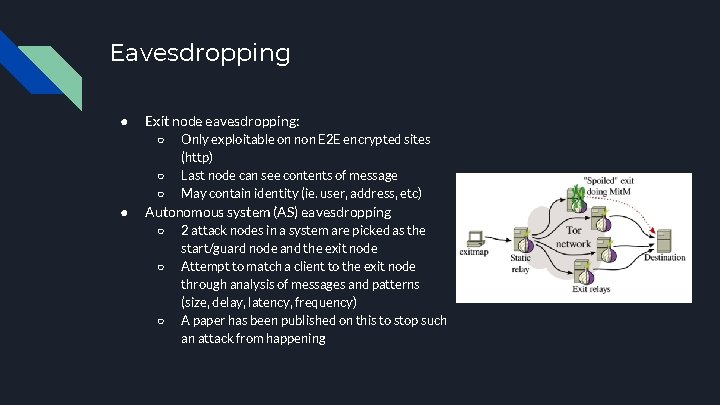
Eavesdropping ● Exit node eavesdropping: ○ ○ ○ ● Only exploitable on non E 2 E encrypted sites (http) Last node can see contents of message May contain identity (ie. user, address, etc) Autonomous system (AS) eavesdropping ○ ○ ○ 2 attack nodes in a system are picked as the start/guard node and the exit node Attempt to match a client to the exit node through analysis of messages and patterns (size, delay, latency, frequency) A paper has been published on this to stop such an attack from happening
Consensus Blocking Authoritative nodes are very important to network, they vote on things like: ● ● Good exit/entry nodes ONION service descriptors validity (directories) When compromised, this authoritative nodes won’t be able to hold a consensus they, usually held hourly. Leaves network in a non-live or invalid state. Recent DDOS attack to these authoritative nodes caused the V 3 service descriptors to be labeled invalid; made most V 3 services in network unreachable. https: //www. youtube. com/watch? v=4 L 8 Svvdxn 08&ab_channel=Mental. Outlaw A patch has been added to alpha build to allow non-live state for service descriptors to be used (possible issues with security? )
Other weaknesses/exploits ● Mouse Fingerprinting ○ ○ ● Unsafe protocols ○ ○ ● Requires non-onion version of service Statistically matches mouse movements in both versions to match identity Bit. Torrent Connection to obtain network nodes is not made through TOR Relay early traffic confirmation attack (2014) ○ ○ ○ Network of nodes added as relays Entry nodes would change headers to encrypt extra info, Exit node could deduce identity of origin by checking this data Various arrests attributed to this exploit Patched soon after discovery

What TOR CAN do Makes tracing you and your info harder Hides your location and IP from host Makes tracing your internet traffic much more difficult for ISPs or other onlookers Allow access to ISP or government censored content Hide hosts location and public IP via ONION Services Increases your anonymity!!!
What TOR can’t do NOT a silver bullet! If used carelessly or improperly, clients or services may still be exposing their identities Various attacks exist which can compromise user’s identities The first and last node have the ip of sender and the ip of the target respectively, which could be exploited TOR does not implement E 2 E encryption natively, so make sure to use SSL for sensitive uses (HTTPS) Hosts can see when a connection is made through TOR, and thus can choose to block such connections TOR != Automatic Hackerman
How is TOR different from a VPN TOR can be used like a VPN in some sense, it: ● ● Changes/hides your ip Can put you in a different country (although randomly decided) VPNs SHOULD NOT be used as a solution for anonymity. TOR is decentralized and encrypts traffic at each node VPNs can potentially see all the traffic made by an user. VPNs are also a single point of failure, if compromised info about their users or their users’ network traffic is accessible. Proxychains are also less secure, since they’re not encrypted and could easily be snooped on
Bad publicity in Tor draws a lot of negative publicity by traditional media and is often associated with the Dark Web Popular media depict Tor as a gateway to hacking or making purchases with cryptocurrencies for illegal products and services (Drugs, hitmen, illegal pornography, malware distribution) About 6. 7% of Tor network users connect to Onion/Hidden services used for illicit purposes
How people use it today (Tor in popular culture) Tor is used by populations who have massive censorship and want to be able to use the internet freely allowing users to surf the internet and chat anonymously such as Iran, China…
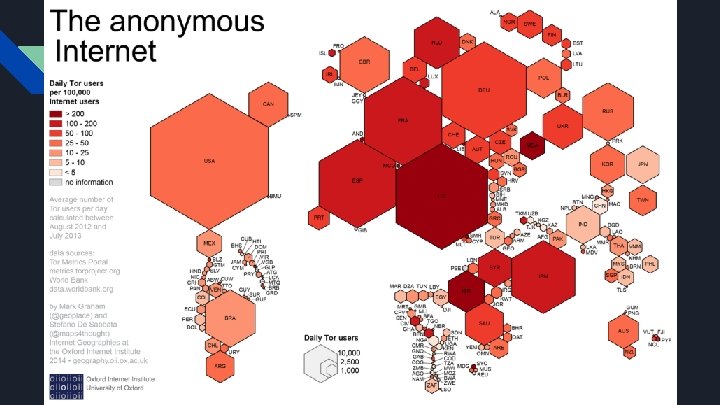
How people use it today (Tor in popular culture) Tor is used by populations who have massive censorship and want to be able to use the internet freely allowing users to surf the internet and chat anonymously such as Iran, China… As well, criminal enterprises can use services anonymously through Onion services to access Darknet Markets (Silk Road), Hacking group and services, Financing, Fraud services, Hoaxes and unverified content, Illegal pornography and terrorism
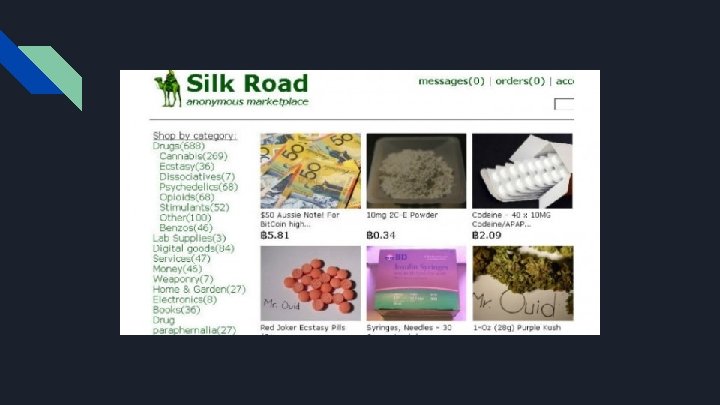

How people use it today (Tor in popular culture) Tor is used by populations who have massive censorship and want to be able to use the internet freely allowing users to surf the internet and chat anonymously such as Iran, China… As well, criminal enterprises can use services anonymously through Onion services to access Darknet Markets (Silk Road), Hacking group and services, Financing, Fraud services, Hoaxes and unverified content, Illegal pornography and terrorism Law enforcement monitor illegal activity and illicit Onion services in the case of criminal activity
How to access the TOR Browser (and network) https: //linuxize. com/post/how-to-install-tor-browser-on-ubuntu-1804/#: ~: text=You%20 can%20 start%20 the%20 Tor, Browser%20 and%20 all%20 other%20 dependencies. https: //www. torproject. org/download/ https: //2019. www. torproject. org/docs/debian. html. en
The end Comment like and subscribe : ) Any questions?
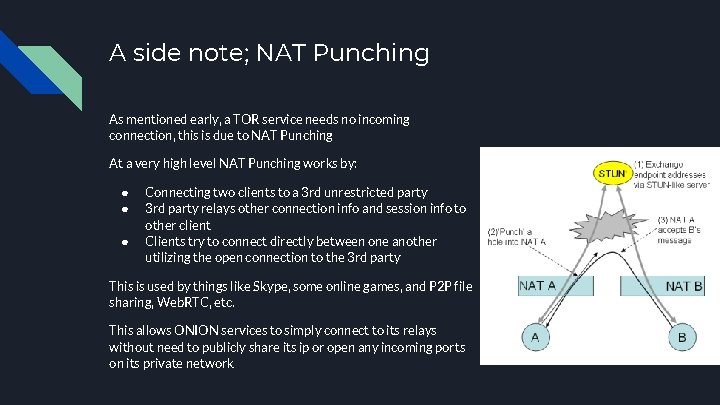
A side note; NAT Punching As mentioned early, a TOR service needs no incoming connection, this is due to NAT Punching At a very high level NAT Punching works by: ● ● ● Connecting two clients to a 3 rd unrestricted party 3 rd party relays other connection info and session info to other client Clients try to connect directly between one another utilizing the open connection to the 3 rd party This is used by things like Skype, some online games, and P 2 P file sharing, Web. RTC, etc. This allows ONION services to simply connect to its relays without need to publicly share its ip or open any incoming ports on its private network
- Slides: 47