Anonymity on the Web Onion routing and Crowds
Anonymity on the Web: Onion routing and Crowds
Outline § § § the problem of user privacy basic concepts of anonymous communication MIXes Onion routing Anonymizer Crowds 2
User privacy – the problem § private information is processed and stored extensively by various individuals and organizations – – location of user telecom operators financial situation of user banks, tax authorities wealth of user insurance companies shopping information of user credit card companies, retailers (via usage of fidelity cards) – illnesses of user medical institutions – … § complete and meaningful profiles on people can be created and abused § information technology makes this easier – no compartmentalization of information – cost of storage and processing (data mining) decreases technology is available to everyone 3
“I don’t have anything to hide. ” § think again! – – – – sexuality pregnancy illnesses genetic predisposition sins of youth controversial activities personal interests … 4
User privacy – the goal § private data should be protected from abuse by unauthorized entities – transactional data • e. g. , access/usage logs at telecom operators, buildings, parking, public transport, … – data that reveals personal interests • e. g. , video rentals, credit card purchases, click stream data (WWW), … – data that was disclosed for a well-defined purpose • e. g. , tax data revealed to tax authorities, health related data revealed to doctors, address information revealed in mail orders, … 5
User privacy – existing approaches § data avoidance – – “I don’t tell you, so you can’t abuse it. ” effective but not always applicable often requires anonymity examples: cash transactions, public phones § data protection – – “If ever you abuse it, you will be punished. ” well-established approach difficult to define, enforce, and control requires legislation or voluntary restrictions § multilateral security – cooperation of more than two parties (typically TTPs are involved) – shared responsibilities and partial knowledge § combinations of the above three 6
Basic concepts of anonymous communication § What do we want to hide? – sender anonymity • attacker cannot determine who the sender of a particular message is – receiver anonymity • attacker cannot determine who the intended receiver of a particular message is – unlinkability • attacker may determine senders and receivers but not the associations between them (attacker doesn’t know who communicates with whom) § From whom do we want to hide this? – communication partner (sender anonymity) – external attackers • local eavesdropper (sniffing on a particular link (e. g. , LAN)) • global eavesdropper (observing traffic in the whole network) – internal attackers 7
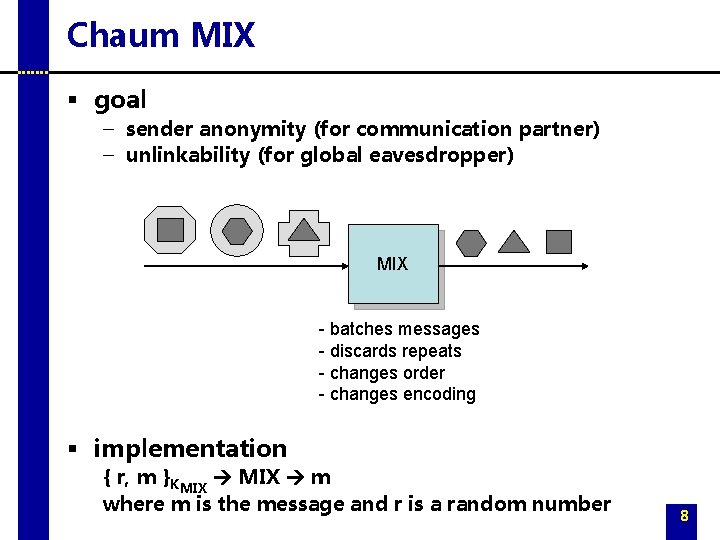
Chaum MIX § goal – sender anonymity (for communication partner) – unlinkability (for global eavesdropper) MIX - batches messages - discards repeats - changes order - changes encoding § implementation { r, m }KMIX m where m is the message and r is a random number 8
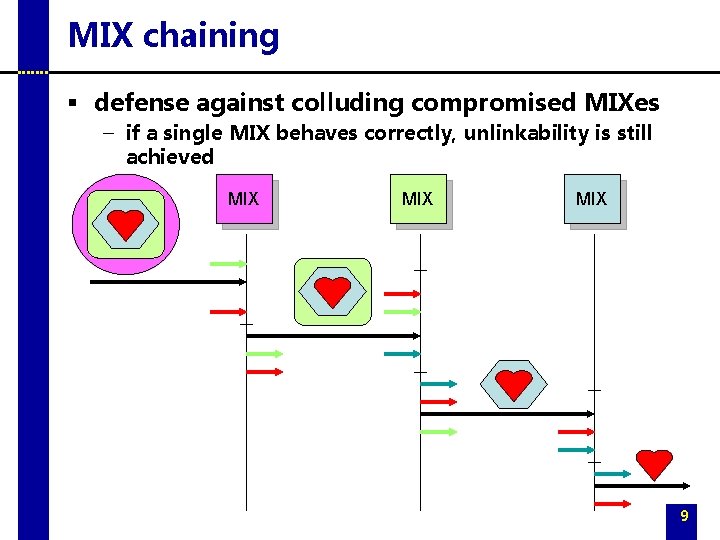
MIX chaining § defense against colluding compromised MIXes – if a single MIX behaves correctly, unlinkability is still achieved MIX MIX 9
A real-time MIX network – Onion routing § general purpose infrastructure for anonymous communications over a public network (e. g. , Internet) § supports several types of applications (HTTP, FTP, SMTP, rlogin, telnet, …) through the use of application specific proxies § operates over a (logical) network of onion routers – onion routers are real-time Chaum MIXes (messages are passed on nearly in real-time this may limit mixing and weaken the protection!) – onion routers are under the control of different administrative domains makes collusion less probable § anonymous connections through onion routers 10
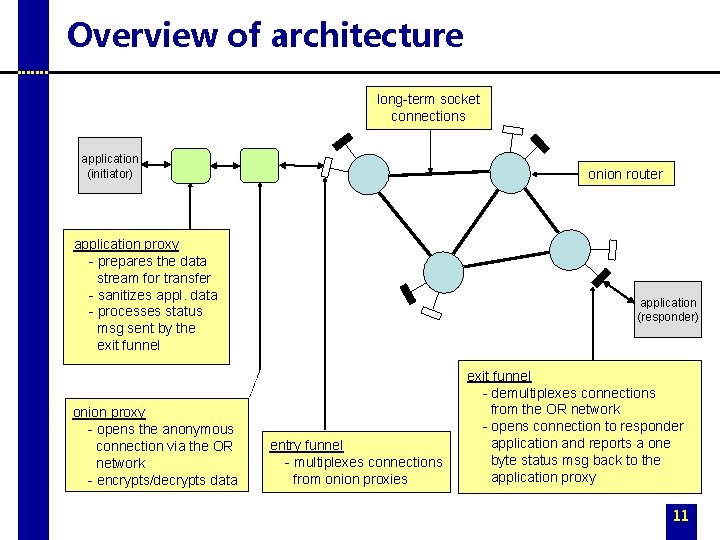
Overview of architecture long-term socket connections application (initiator) onion router application proxy - prepares the data stream for transfer - sanitizes appl. data - processes status msg sent by the exit funnel onion proxy - opens the anonymous connection via the OR network - encrypts/decrypts data application (responder) entry funnel - multiplexes connections from onion proxies exit funnel - demultiplexes connections from the OR network - opens connection to responder application and reports a one byte status msg back to the application proxy 11
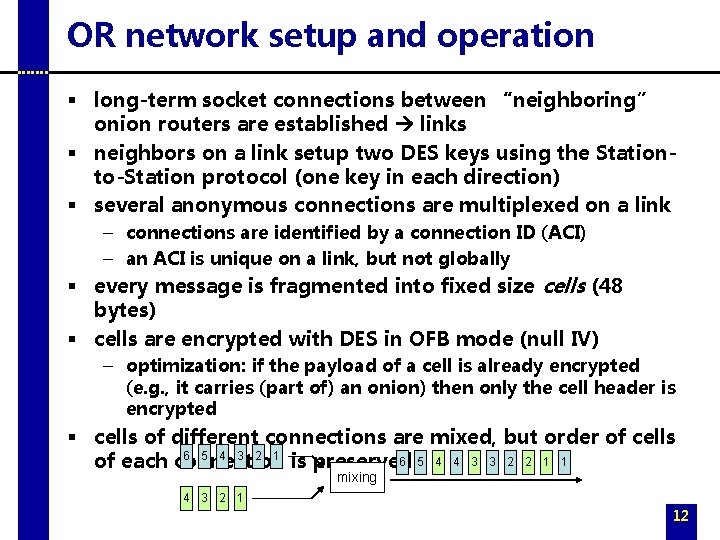
OR network setup and operation § long-term socket connections between “neighboring” onion routers are established links § neighbors on a link setup two DES keys using the Stationto-Station protocol (one key in each direction) § several anonymous connections are multiplexed on a link – connections are identified by a connection ID (ACI) – an ACI is unique on a link, but not globally § every message is fragmented into fixed size cells (48 bytes) § cells are encrypted with DES in OFB mode (null IV) – optimization: if the payload of a cell is already encrypted (e. g. , it carries (part of) an onion) then only the cell header is encrypted § cells of different connections are mixed, but order of cells 6 5 4 3 2 1 6 5 4 4 3 3 2 2 1 1 of each connection is preserved mixing 4 3 2 1 12
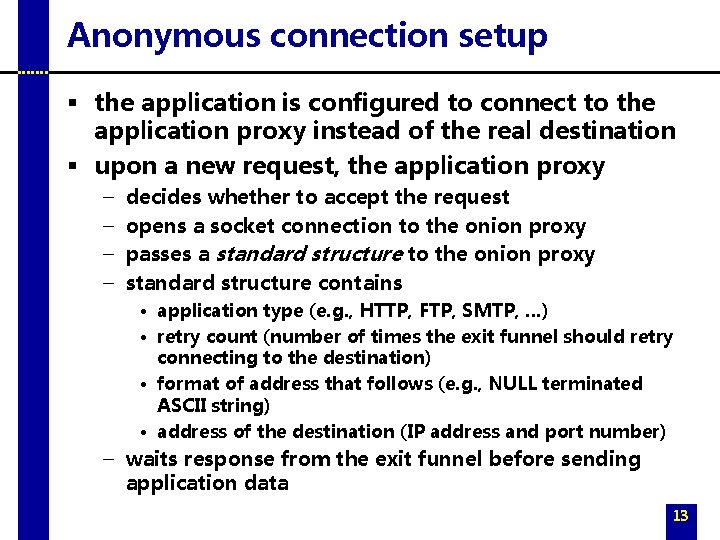
Anonymous connection setup § the application is configured to connect to the application proxy instead of the real destination § upon a new request, the application proxy – – decides whether to accept the request opens a socket connection to the onion proxy passes a standard structure to the onion proxy standard structure contains • application type (e. g. , HTTP, FTP, SMTP, …) • retry count (number of times the exit funnel should retry connecting to the destination) • format of address that follows (e. g. , NULL terminated ASCII string) • address of the destination (IP address and port number) – waits response from the exit funnel before sending application data 13
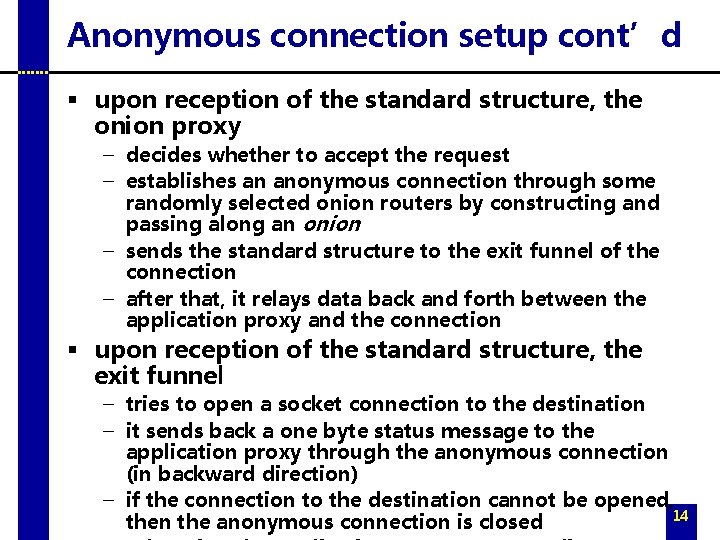
Anonymous connection setup cont’d § upon reception of the standard structure, the onion proxy – decides whether to accept the request – establishes an anonymous connection through some randomly selected onion routers by constructing and passing along an onion – sends the standard structure to the exit funnel of the connection – after that, it relays data back and forth between the application proxy and the connection § upon reception of the standard structure, the exit funnel – tries to open a socket connection to the destination – it sends back a one byte status message to the application proxy through the anonymous connection (in backward direction) – if the connection to the destination cannot be opened, 14 then the anonymous connection is closed
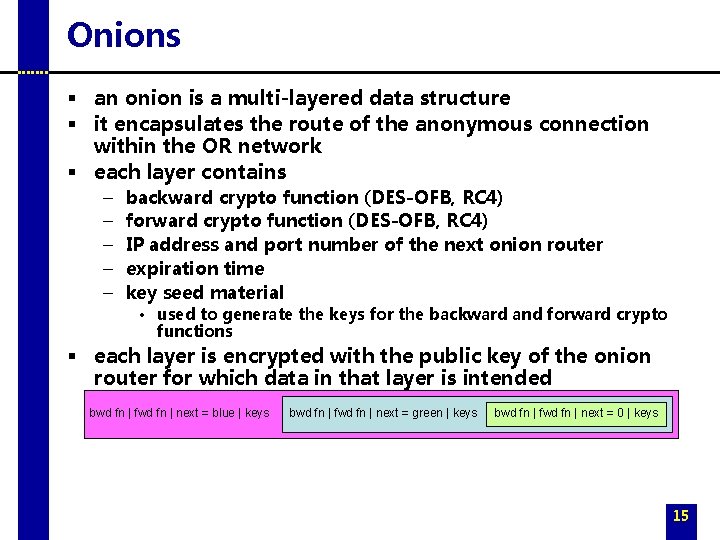
Onions § an onion is a multi-layered data structure § it encapsulates the route of the anonymous connection within the OR network § each layer contains – – – backward crypto function (DES-OFB, RC 4) forward crypto function (DES-OFB, RC 4) IP address and port number of the next onion router expiration time key seed material • used to generate the keys for the backward and forward crypto functions § each layer is encrypted with the public key of the onion router for which data in that layer is intended bwd fn | fwd fn | next = blue | keys bwd fn | fwd fn | next = green | keys bwd fn | fwd fn | next = 0 | keys 15
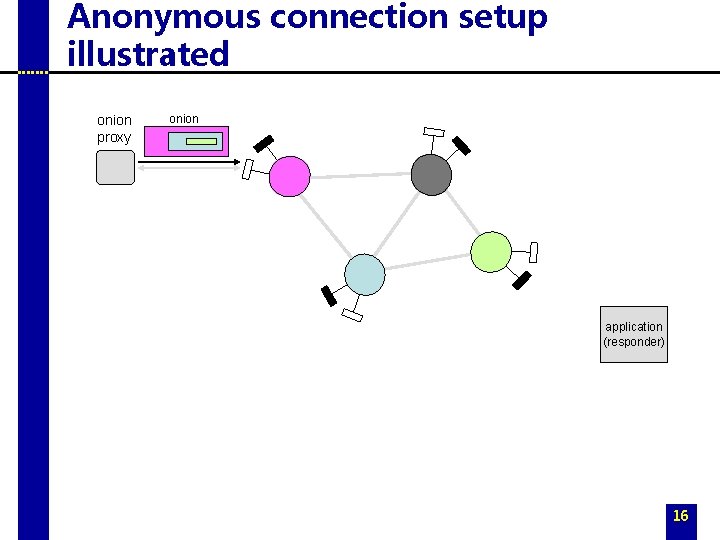
Anonymous connection setup illustrated onion proxy onion application (responder) 16
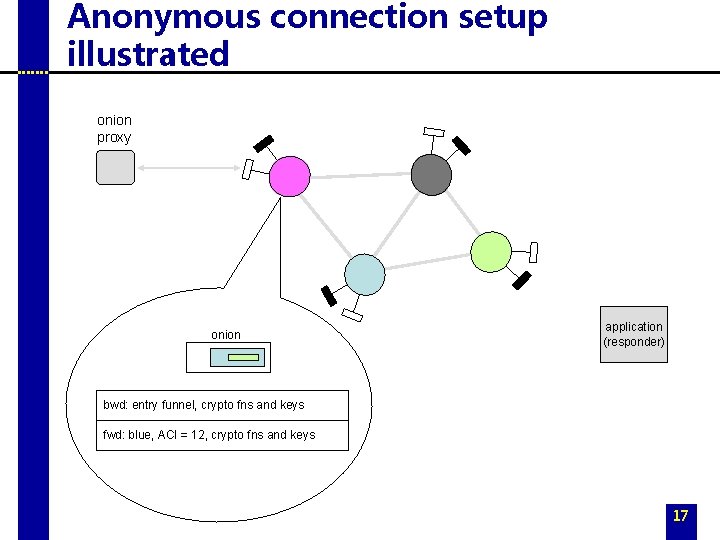
Anonymous connection setup illustrated onion proxy onion application (responder) bwd: entry funnel, crypto fns and keys fwd: blue, ACI = 12, crypto fns and keys 17
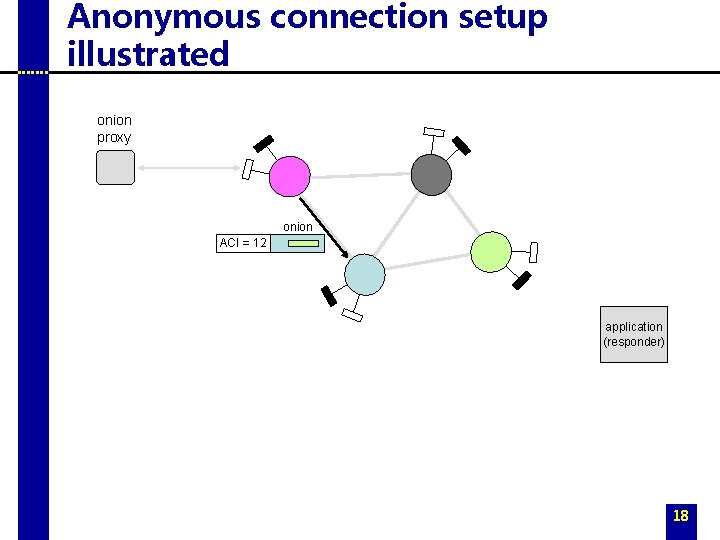
Anonymous connection setup illustrated onion proxy onion ACI = 12 application (responder) 18
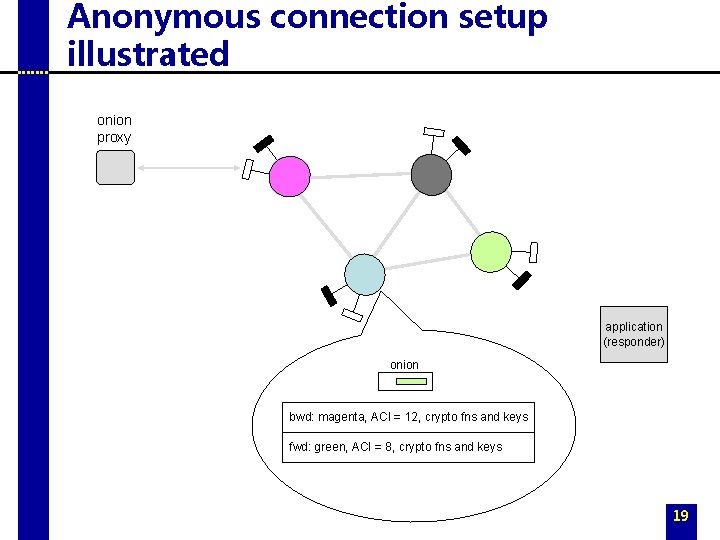
Anonymous connection setup illustrated onion proxy application (responder) onion bwd: magenta, ACI = 12, crypto fns and keys fwd: green, ACI = 8, crypto fns and keys 19
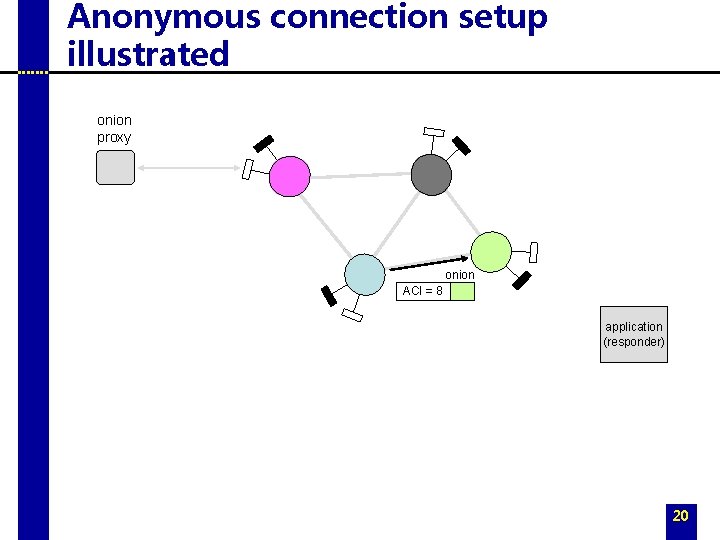
Anonymous connection setup illustrated onion proxy onion ACI = 8 application (responder) 20
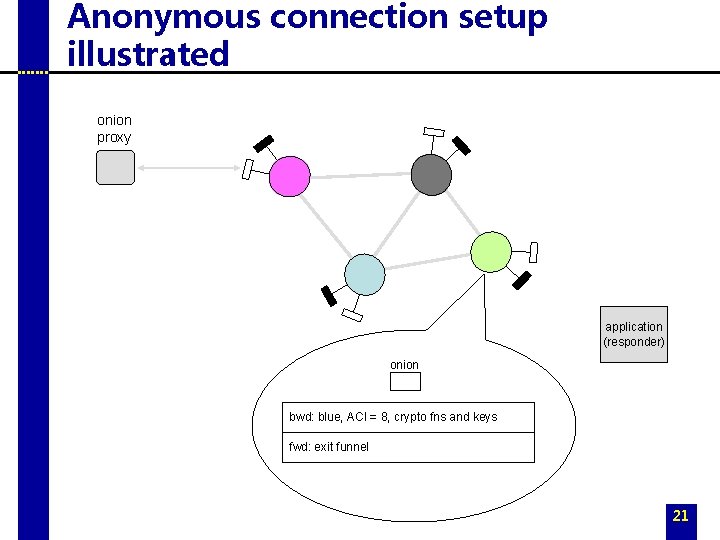
Anonymous connection setup illustrated onion proxy application (responder) onion bwd: blue, ACI = 8, crypto fns and keys fwd: exit funnel 21
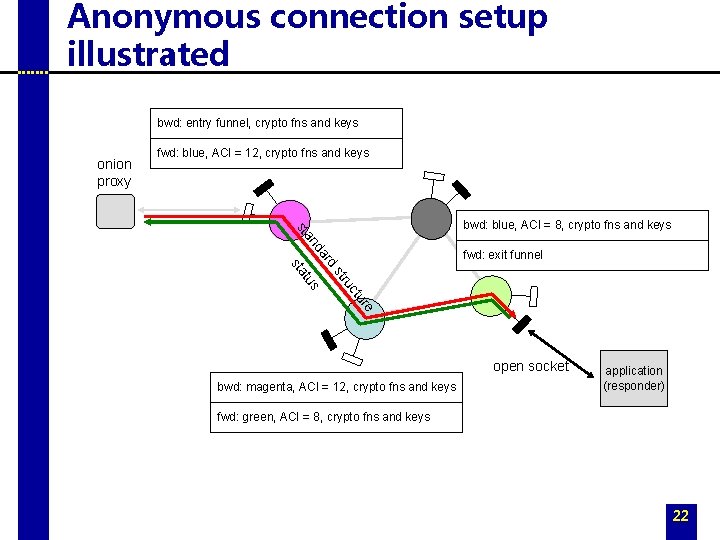
Anonymous connection setup illustrated bwd: entry funnel, crypto fns and keys onion proxy fwd: blue, ACI = 12, crypto fns and keys a nd sta bwd: blue, ACI = 8, crypto fns and keys uc str s tu sta rd fwd: exit funnel re tu open socket bwd: magenta, ACI = 12, crypto fns and keys application (responder) fwd: green, ACI = 8, crypto fns and keys 22
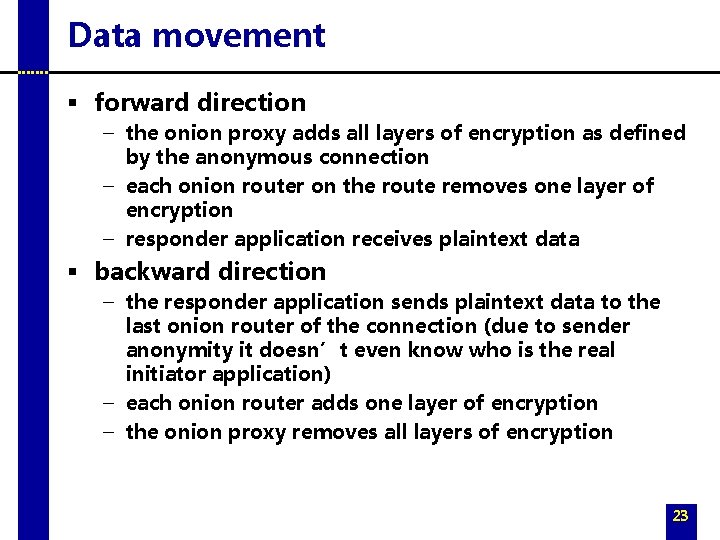
Data movement § forward direction – the onion proxy adds all layers of encryption as defined by the anonymous connection – each onion router on the route removes one layer of encryption – responder application receives plaintext data § backward direction – the responder application sends plaintext data to the last onion router of the connection (due to sender anonymity it doesn’t even know who is the real initiator application) – each onion router adds one layer of encryption – the onion proxy removes all layers of encryption 23
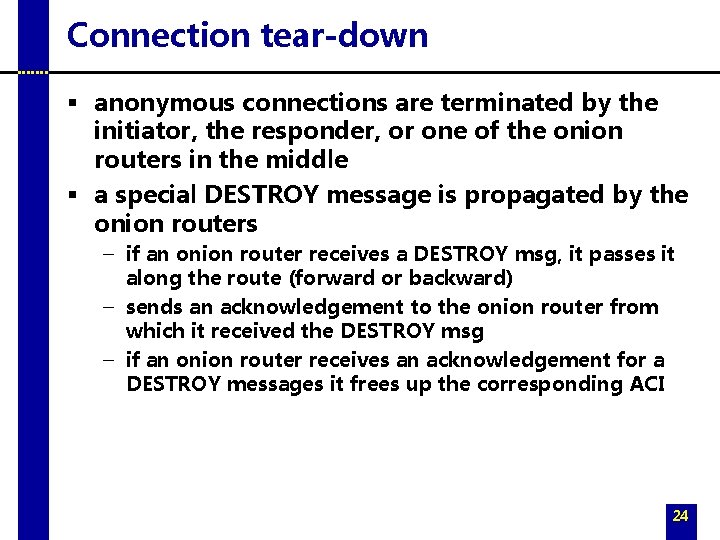
Connection tear-down § anonymous connections are terminated by the initiator, the responder, or one of the onion routers in the middle § a special DESTROY message is propagated by the onion routers – if an onion router receives a DESTROY msg, it passes it along the route (forward or backward) – sends an acknowledgement to the onion router from which it received the DESTROY msg – if an onion router receives an acknowledgement for a DESTROY messages it frees up the corresponding ACI 24
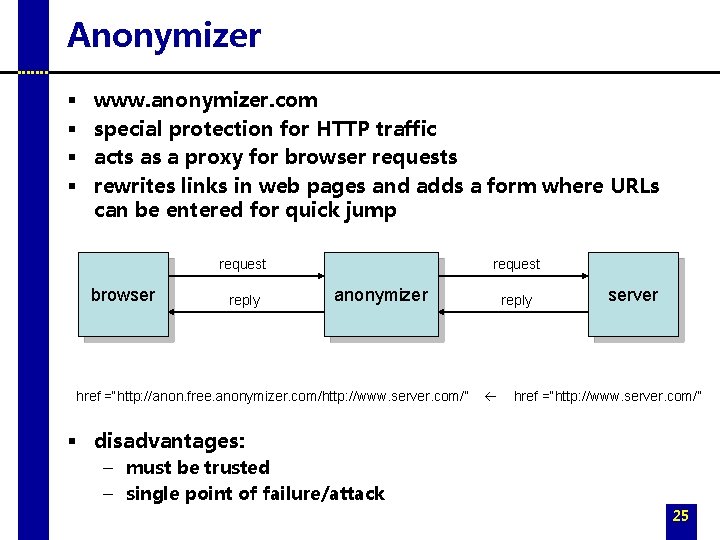
Anonymizer § § www. anonymizer. com special protection for HTTP traffic acts as a proxy for browser requests rewrites links in web pages and adds a form where URLs can be entered for quick jump request browser reply request anonymizer href =“http: //anon. free. anonymizer. com/http: //www. server. com/” reply server href =“http: //www. server. com/” § disadvantages: – must be trusted – single point of failure/attack 25
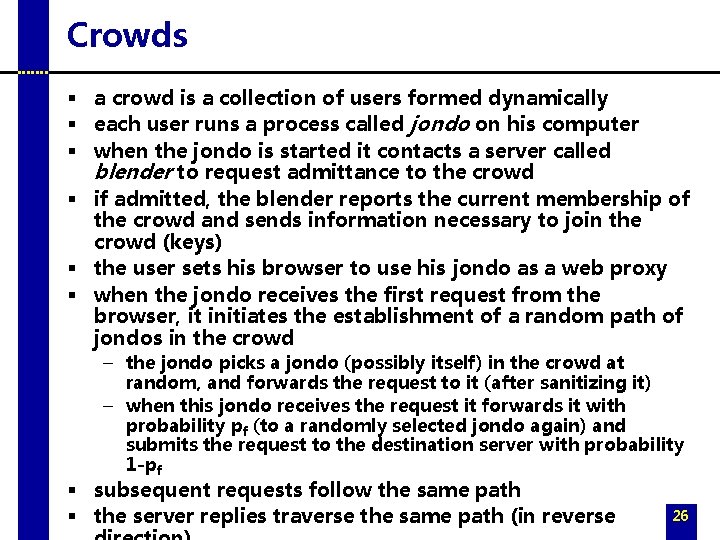
Crowds § a crowd is a collection of users formed dynamically § each user runs a process called jondo on his computer § when the jondo is started it contacts a server called blender to request admittance to the crowd § if admitted, the blender reports the current membership of the crowd and sends information necessary to join the crowd (keys) § the user sets his browser to use his jondo as a web proxy § when the jondo receives the first request from the browser, it initiates the establishment of a random path of jondos in the crowd – the jondo picks a jondo (possibly itself) in the crowd at random, and forwards the request to it (after sanitizing it) – when this jondo receives the request it forwards it with probability pf (to a randomly selected jondo again) and submits the request to the destination server with probability 1 -pf § subsequent requests follow the same path § the server replies traverse the same path (in reverse 26
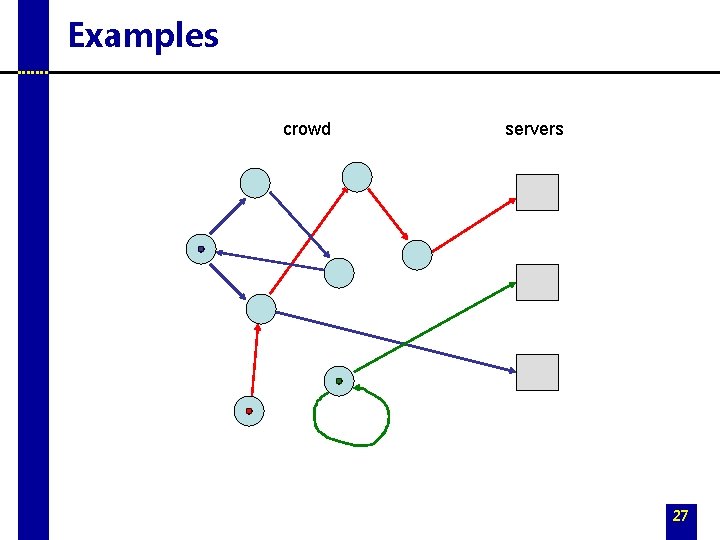
Examples crowd servers 27
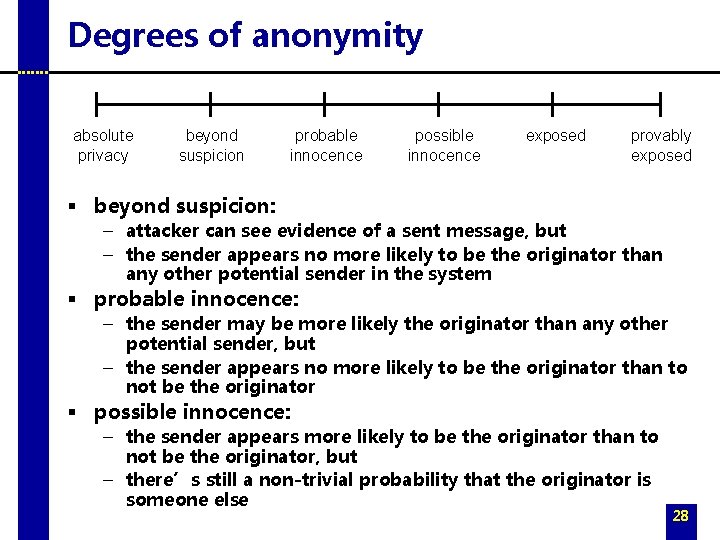
Degrees of anonymity absolute privacy beyond suspicion probable innocence possible innocence exposed provably exposed § beyond suspicion: – attacker can see evidence of a sent message, but – the sender appears no more likely to be the originator than any other potential sender in the system § probable innocence: – the sender may be more likely the originator than any other potential sender, but – the sender appears no more likely to be the originator than to not be the originator § possible innocence: – the sender appears more likely to be the originator than to not be the originator, but – there’s still a non-trivial probability that the originator is someone else 28
Types of attackers § local eavesdropper – can observe communication to and from the users computer § collaborating crowd members – crowd members that can pool their information and deviate from the protocol § end server – the web server to which the transaction is directed 29
Security analysis – local eavesdropper § a local eavesdropper can see that the user originated a request – sender is exposed § however, he typically cannot see the target of the request – requests are encrypted unless they are submitted to the target server – if request is encrypted, each end-server appears for the attacker equally likely to be the target of the request beyond suspicion anonymity – if the user’s own jondo submits the request, then the target is exposed; the probability of this is 1/n where n is the size of the crowd – P( receiver / beyond suspicion ) 1 as n infinity 30
Security analysis – end server § end-server is the target of the request – receiver anonymity is not possible § anonymity for the originator is strong – user’s jondo always forwards the request to a random member of the crowd (~ hides user identity with a onetime pad) the end-server is equally likely to receive the request from any crowd member – from the end-server perspective, each user is equally likely to be the originator sender / beyond suspicion anonymity guaranteed 31
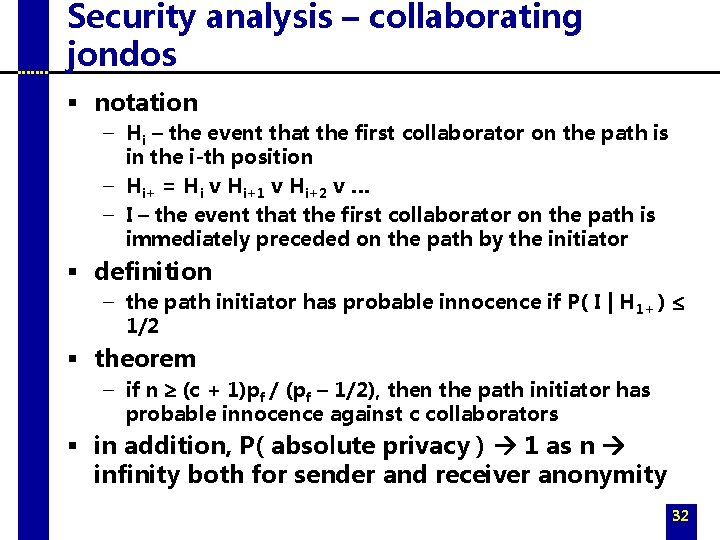
Security analysis – collaborating jondos § notation – Hi – the event that the first collaborator on the path is in the i-th position – Hi+ = Hi v Hi+1 v Hi+2 v … – I – the event that the first collaborator on the path is immediately preceded on the path by the initiator § definition – the path initiator has probable innocence if P( I | H 1+ ) £ 1/2 § theorem – if n ³ (c + 1)pf / (pf – 1/2), then the path initiator has probable innocence against c collaborators § in addition, P( absolute privacy ) 1 as n infinity both for sender and receiver anonymity 32
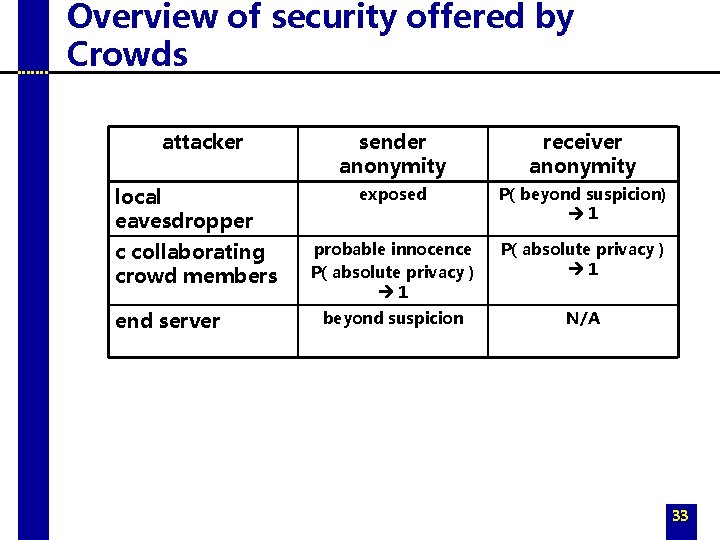
Overview of security offered by Crowds attacker local eavesdropper c collaborating crowd members end server sender anonymity receiver anonymity exposed P( beyond suspicion) 1 probable innocence P( absolute privacy ) 1 beyond suspicion N/A 33
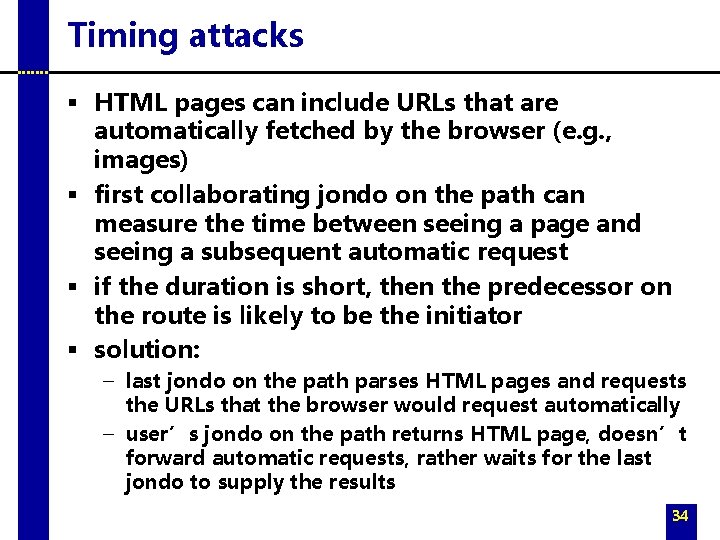
Timing attacks § HTML pages can include URLs that are automatically fetched by the browser (e. g. , images) § first collaborating jondo on the path can measure the time between seeing a page and seeing a subsequent automatic request § if the duration is short, then the predecessor on the route is likely to be the initiator § solution: – last jondo on the path parses HTML pages and requests the URLs that the browser would request automatically – user’s jondo on the path returns HTML page, doesn’t forward automatic requests, rather waits for the last jondo to supply the results 34
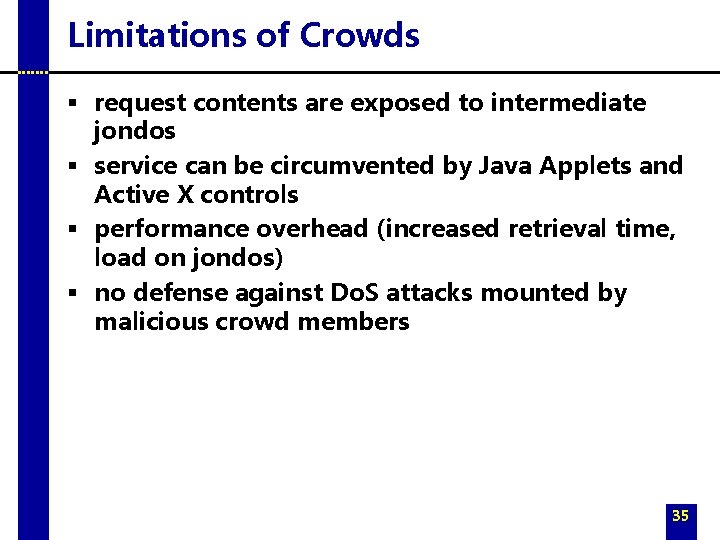
Limitations of Crowds § request contents are exposed to intermediate jondos § service can be circumvented by Java Applets and Active X controls § performance overhead (increased retrieval time, load on jondos) § no defense against Do. S attacks mounted by malicious crowd members 35
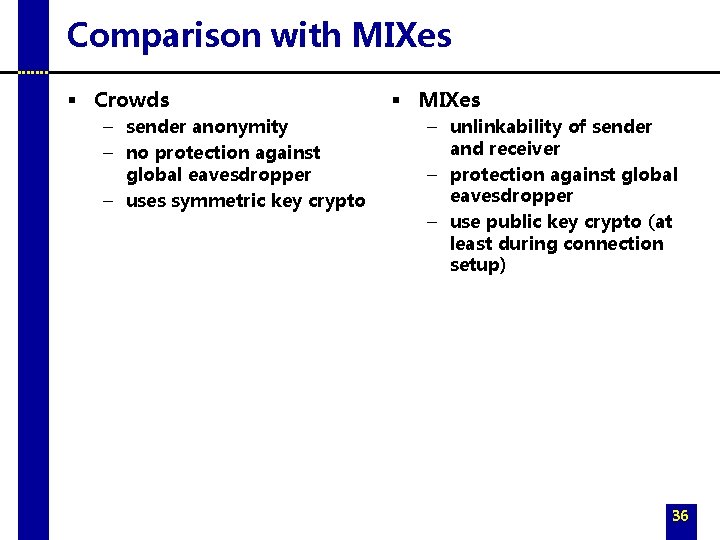
Comparison with MIXes § Crowds – sender anonymity – no protection against global eavesdropper – uses symmetric key crypto § MIXes – unlinkability of sender and receiver – protection against global eavesdropper – use public key crypto (at least during connection setup) 36
- Slides: 36