Robust Mesh Watermarking Emil Praun Hugues Hoppe Adam
Robust Mesh Watermarking Emil Praun Hugues Hoppe Adam Finkelstein Princeton University Microsoft Research Princeton University
Watermarking Applications • Authentication / localization of changes Fragile watermarks • Ownership protection Robust watermarks • Tracing of distribution channels Fingerprints
Watermarking Applications • Authentication / localization of changes Fragile watermarks • Ownership protection Robust watermarks • Tracing of distribution channels Fingerprints
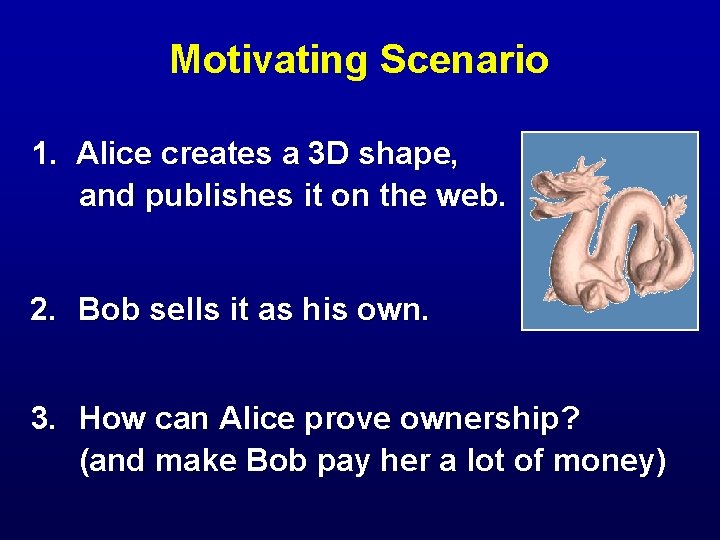
Motivating Scenario 1. Alice creates a 3 D shape, and publishes it on the web. 2. Bob sells it as his own. 3. How can Alice prove ownership? (and make Bob pay her a lot of money)
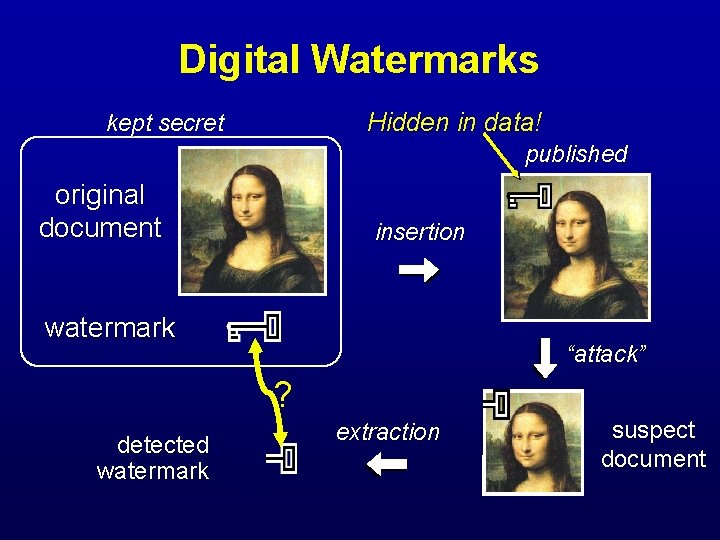
Digital Watermarks Hidden in data! kept secret published original document insertion watermark “attack” ? detected watermark extraction suspect document
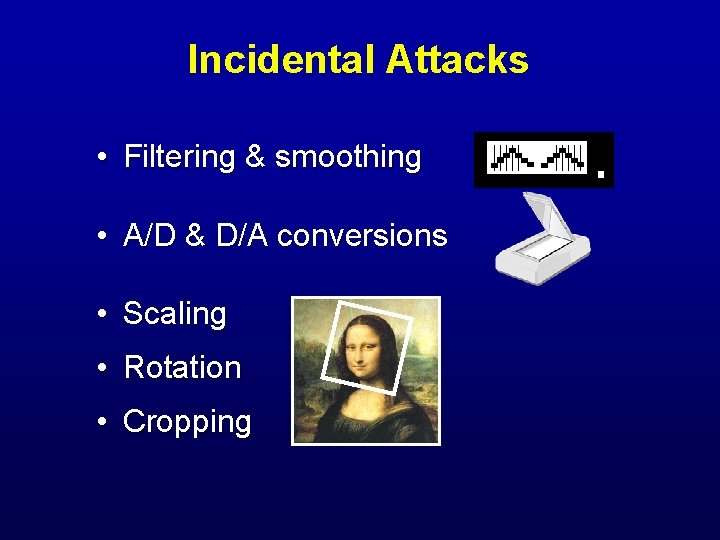
Incidental Attacks • Filtering & smoothing • A/D & D/A conversions • Scaling • Rotation • Cropping
Malicious Attacks • Adding noise • Adding another watermark • Resampling • Statistical analysis

Our Goal Watermarking scheme for 3 D models: • Robust against attacks • Works on arbitrary meshes • Preserves original connectivity • Imperceptible
![Previous Watermarking [Cox et al. ’ 97] Introduce spread-spectrum for images [Ohbuchi et al. Previous Watermarking [Cox et al. ’ 97] Introduce spread-spectrum for images [Ohbuchi et al.](http://slidetodoc.com/presentation_image_h2/958483978f4831d99740a7584b8e33e9/image-9.jpg)
Previous Watermarking [Cox et al. ’ 97] Introduce spread-spectrum for images [Ohbuchi et al. ’ 98] 3 schemes fragile under resampling [Kanai et al. ’ 98] Requires subdivision connectivity meshes [Benedens ’ 99] Redistributes face normals by moving vertices
![Spread-Spectrum Watermarking Transform to frequency space [Cox et al. ’ 97] DCT image frequency Spread-Spectrum Watermarking Transform to frequency space [Cox et al. ’ 97] DCT image frequency](http://slidetodoc.com/presentation_image_h2/958483978f4831d99740a7584b8e33e9/image-10.jpg)
Spread-Spectrum Watermarking Transform to frequency space [Cox et al. ’ 97] DCT image frequency domain
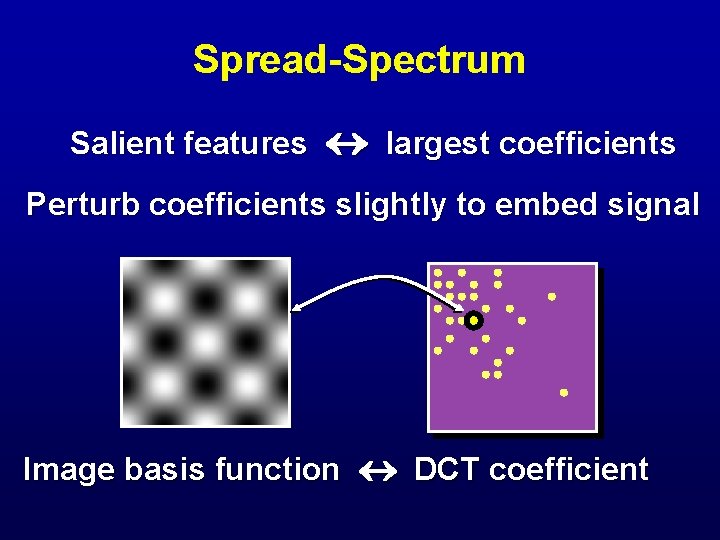
Spread-Spectrum Salient features largest coefficients Perturb coefficients slightly to embed signal Image basis function DCT coefficient
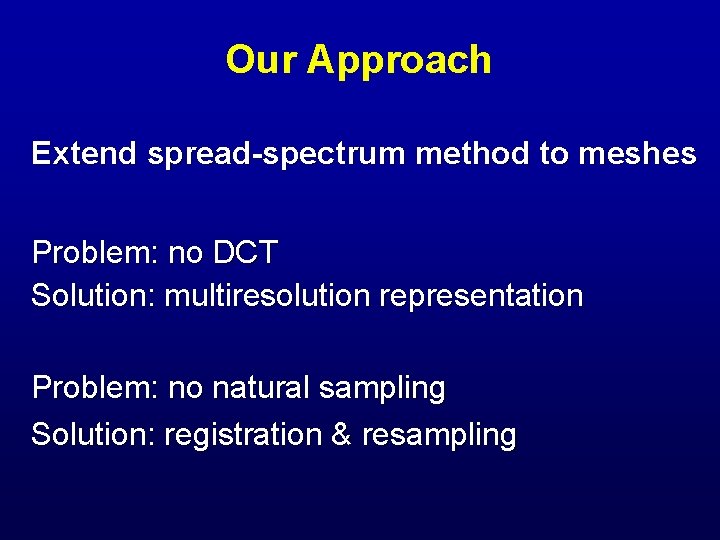
Our Approach Extend spread-spectrum method to meshes Problem: no DCT Solution: multiresolution representation Problem: no natural sampling Solution: registration & resampling
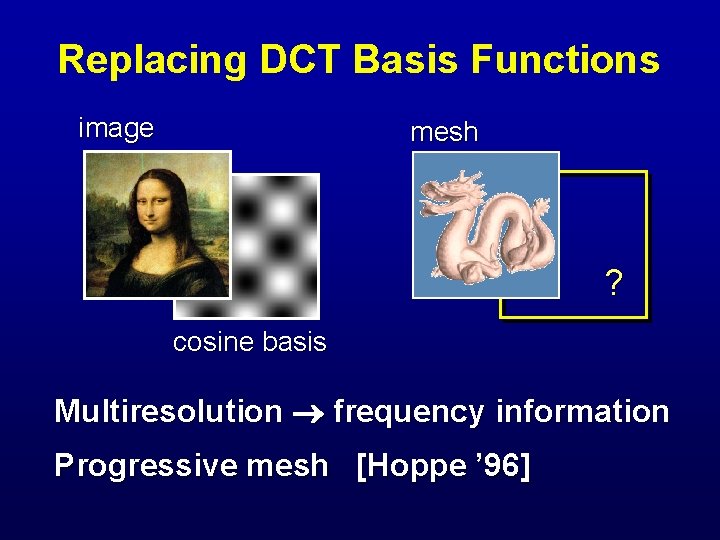
Replacing DCT Basis Functions image mesh ? cosine basis Multiresolution frequency information Progressive mesh [Hoppe ’ 96]
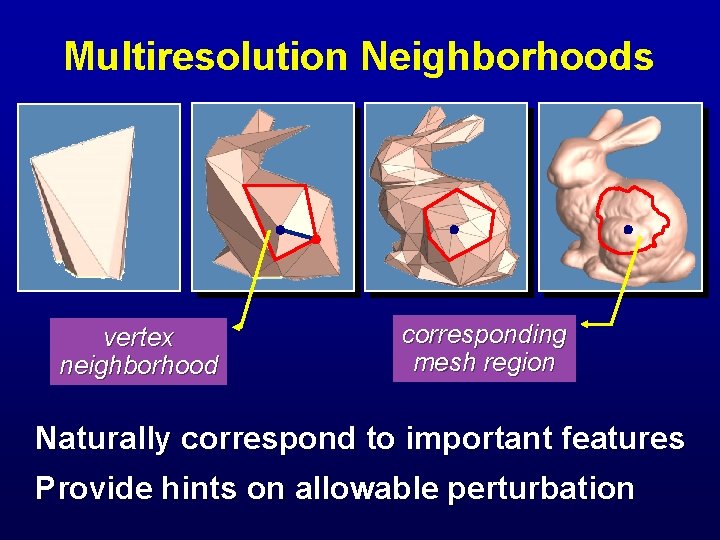
Multiresolution Neighborhoods vertex neighborhood corresponding mesh region Naturally correspond to important features Provide hints on allowable perturbation
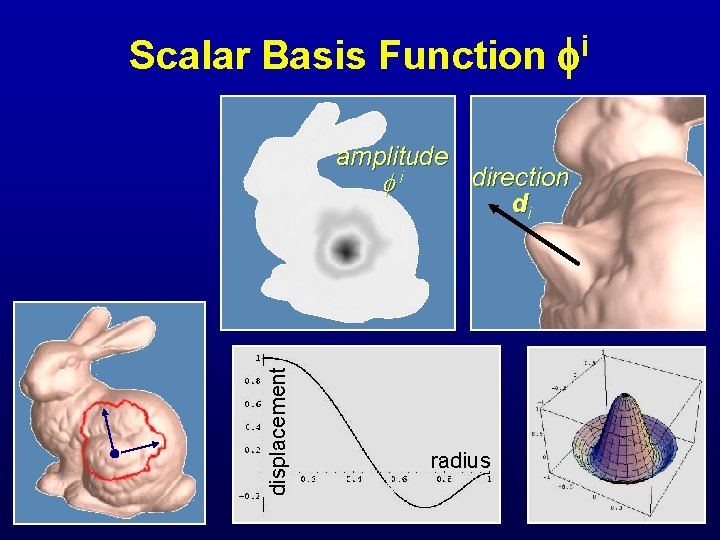
Scalar Basis Function amplitude displacement i i direction di radius
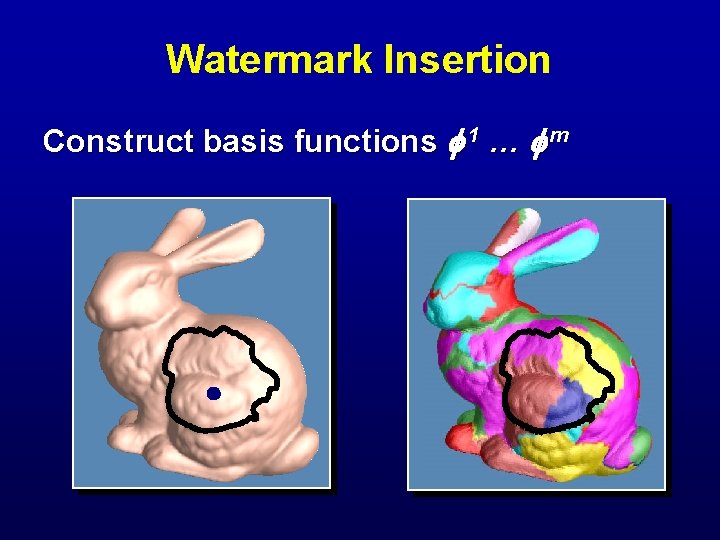
Watermark Insertion Construct basis functions 1 … m
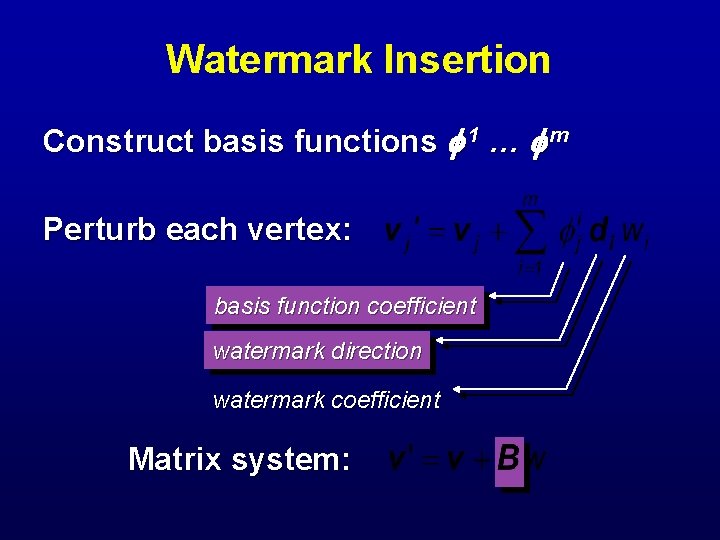
Watermark Insertion Construct basis functions 1 … m Perturb each vertex: basis function coefficient watermark direction watermark coefficient Matrix system:
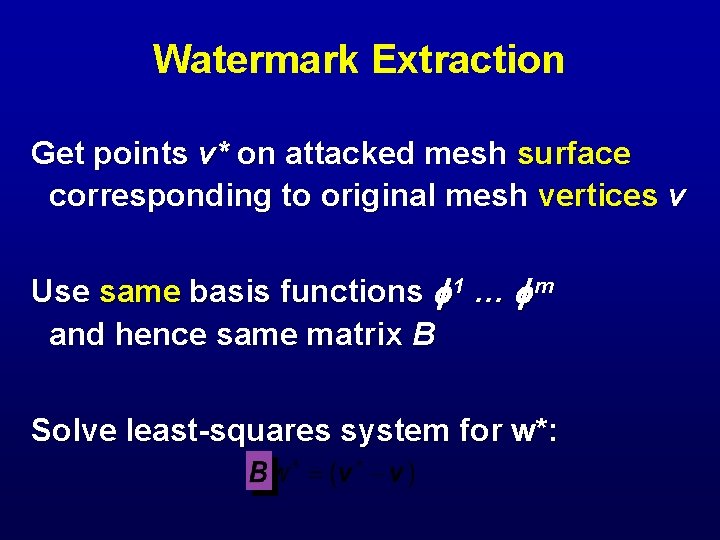
Watermark Extraction Get points v* on attacked mesh surface corresponding to original mesh vertices v Use same basis functions 1 … m and hence same matrix B Solve least-squares system for w*:
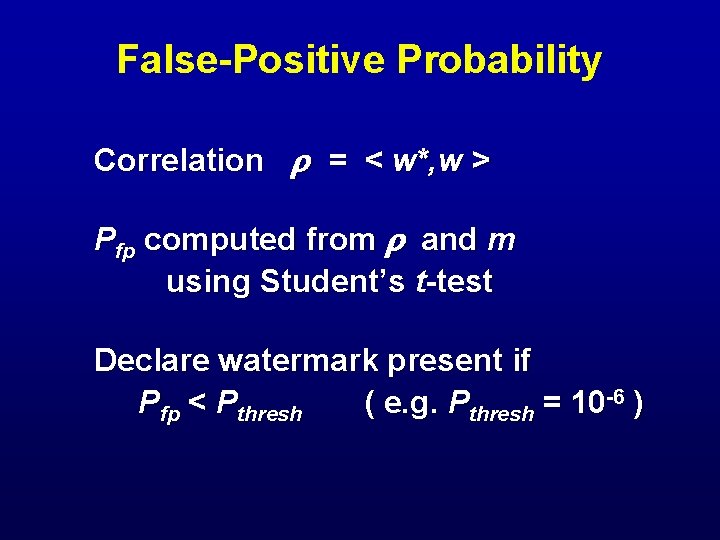
False-Positive Probability Correlation = < w*, w > Pfp computed from and m using Student’s t-test Declare watermark present if Pfp < Pthresh ( e. g. Pthresh = 10 -6 )
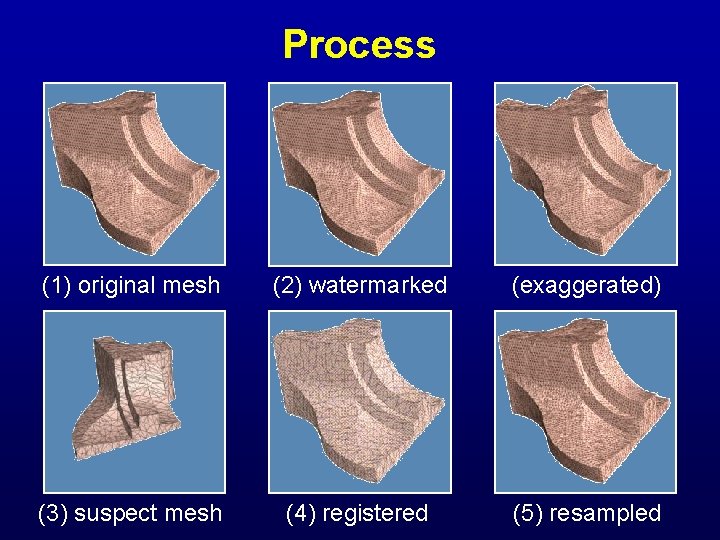
Process (1) original mesh (2) watermarked (exaggerated) (3) suspect mesh (4) registered (5) resampled
![Registration & Resampling Registration: • [Chen & Medioni ’ 92] Resampling choices: • Closest Registration & Resampling Registration: • [Chen & Medioni ’ 92] Resampling choices: • Closest](http://slidetodoc.com/presentation_image_h2/958483978f4831d99740a7584b8e33e9/image-21.jpg)
Registration & Resampling Registration: • [Chen & Medioni ’ 92] Resampling choices: • Closest point projection • Ray-casting along local normal • Global deformation of original
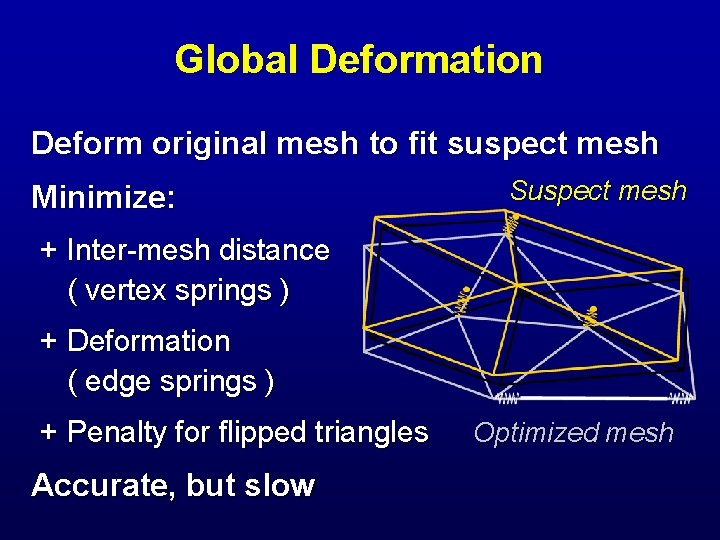
Global Deformation Deform original mesh to fit suspect mesh Minimize: Suspect mesh + Inter-mesh distance ( vertex springs ) + Deformation ( edge springs ) + Penalty for flipped triangles Accurate, but slow Optimized mesh
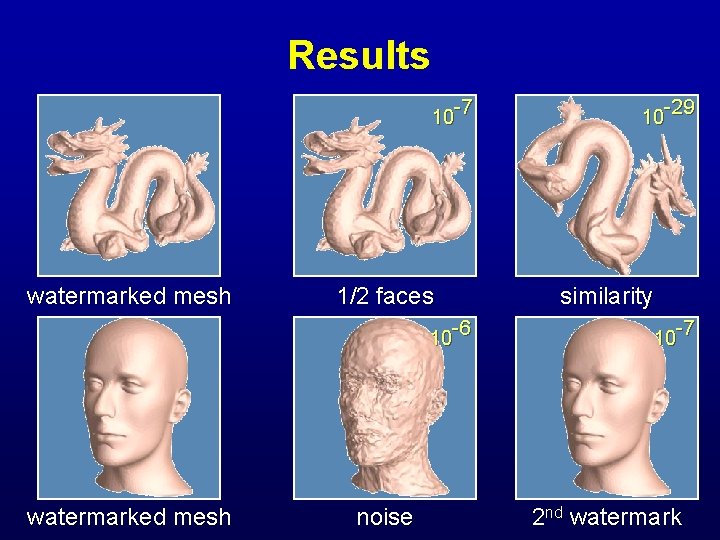
Results 10 -7 watermarked mesh 1/2 faces 10 -6 watermarked mesh noise 10 -29 similarity 10 -7 2 nd watermark
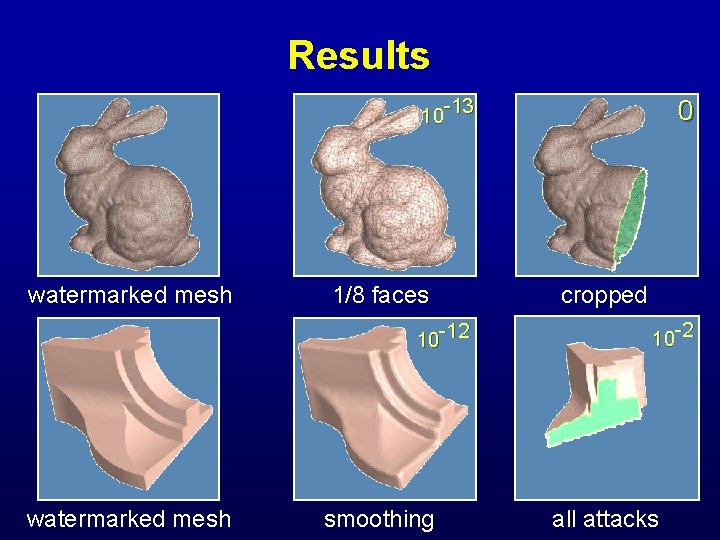
Results 10 -13 watermarked mesh 1/8 faces 10 -12 watermarked mesh smoothing 0 cropped 10 -2 all attacks
Summary Robust watermarking for 3 D meshes • Spread-spectrum • Basis functions from multiresolution analysis • Resampling as global optimization Resilient to a variety of attacks
Future Work Consider other attacks: • General affine and projective transforms • Free-form deformations! [Stir. Mark by Petitcolas] Explore other basis functions • e. g. [Guskov et al. ’ 99] Fast mesh recognition web crawler
- Slides: 26