Public Key Infrastructure Symmetric vs Public key systems
Public Key Infrastructure Symmetric vs. Public key systems PKI added value
Teaching Points n n n n Symmetric vs. Public key systems Message Digests Key Management Man-in-the-middle Certificates Cross certification Timestamps
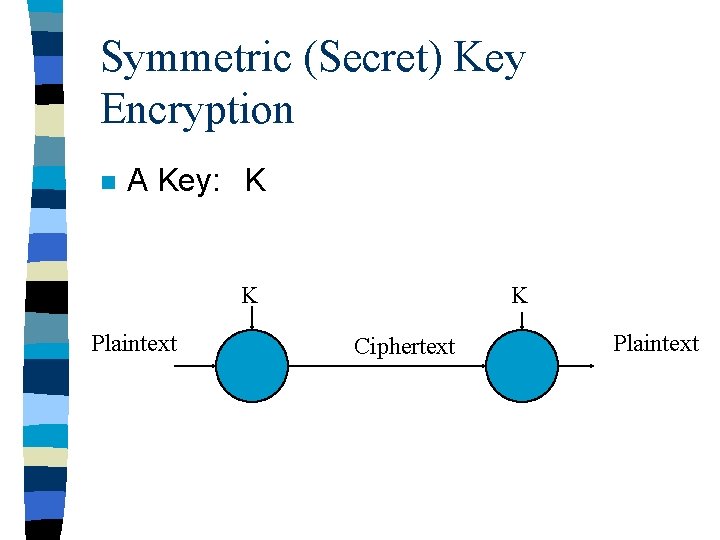
Symmetric (Secret) Key Encryption n A Key: K K Plaintext K Ciphertext Plaintext
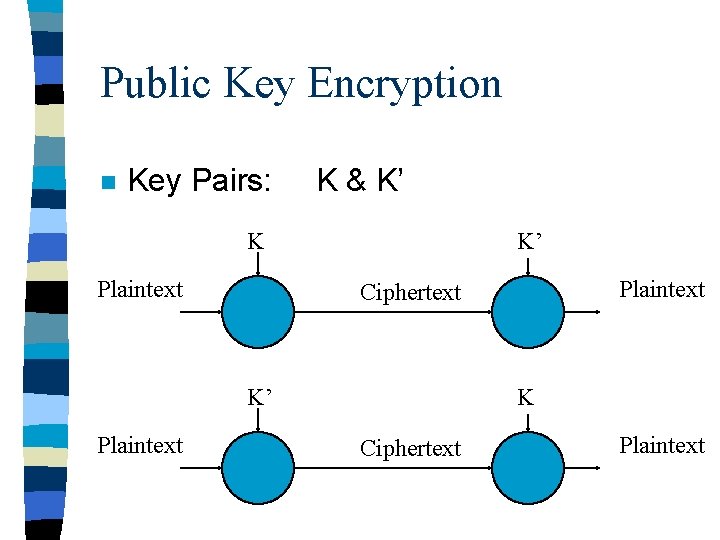
Public Key Encryption n Key Pairs: K & K’ K Plaintext K’ K’ Plaintext Ciphertext K Ciphertext Plaintext
Secure Hash/Message Digest (digital fingerprint) n A hash function with the properties: – Arbitrary sized input produces a fixed size (small) output – it is computationally infeasible to find two messages that hash to the same value – the hash/digest does not reveal anything about the input – small changes in input produce large changes in output
Secrecy vs. Signature n n n Symmetric or public schemes can be used for both Both rely on uncompromised keys Symmetric: – if you know one party did not sign the other party must have signed n Pubic: – the party with the private key must have signed
What to sign? n n n Public key cryptography is generally more expensive in effort If we sign the whole document then it is unreadable without PKI software to decrypt it. So, we sign the message digest – cheaper – leaves the document readable
What to Encrypt for Secrecy? n n Public key cryptography is generally more expensive in effort So: – Generate a symmetric key – encrypt the document using the symmetric key – encrypt the symmetric key using the private key – include the encrypted key with the document
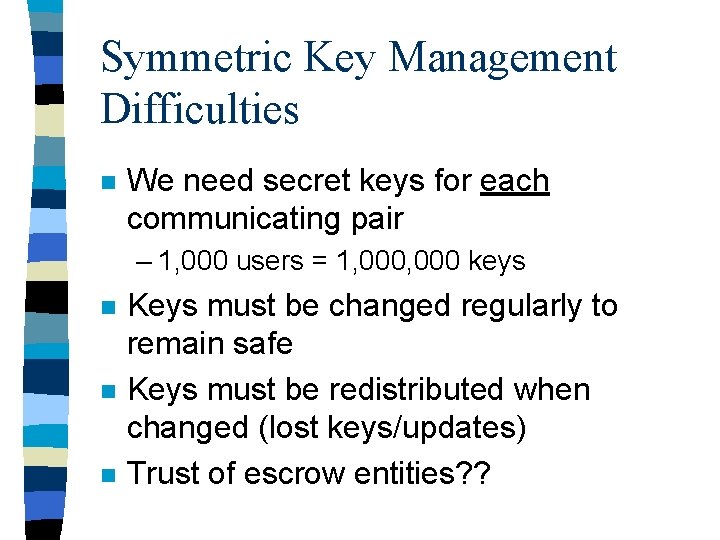
Symmetric Key Management Difficulties n We need secret keys for each communicating pair – 1, 000 users = 1, 000 keys n n n Keys must be changed regularly to remain safe Keys must be redistributed when changed (lost keys/updates) Trust of escrow entities? ?
The Public Key Solution n Publish one half of each key pair – private/pubic keys n Distribution is now cheap The number of keys required is now in the order of n instead of n 2 n But… keys are big n
Where to keep your secret key? n n n n n Keys are to long to remember @Private. Key=m 19 w. I 2 IYyze. Dx. AEf 3 JG 0 e 2 p. VJUbk. OALFs 4 y. XCPLj. Zt. YF 4 njh. DTF 1 CB 31 v 9 s. Y _continue_=w. K/ru. ERO 1 Cnu/1 idw. JNPYHA/KSs 8 a. T+Xd. AIN 6+uiiaq. Tx. La. Px 2 l. TQl 03 t. O 3 f. D _continue_=Xq. QQ 15 VP 2 I 2 Ju 5 vtx 3 m. Lbl. FGkyt/6 SWh. ZUKbbie. UGMPgi. MFM 99 L 3 VTav. Nn 1 x 5 _continue_=km. Dg. OMra/7 h 4 VYSy+Oa 27 c. MENJR/+j. D 0 WMQZ 2 f. Wclugw/Bj. Ohp+R 6+qbhf 8 P K _continue_=5 H+jy 43 XKnq 057 Bhim. ROr. Quhv. WNJ 3 Hcznda. R 0 P 2 dm 1 h. NWc. O 5 T 8 OEKPUnly PMV _continue_=Misq. Nvi 59 Irrp. Kym. Ey. VQSCVs. Lf. HPl. RVmuma 71 j. Sn. Pfbk. N 3 S 5 Q 1 EExk 6 Xj 6/4 Z _continue_=h 2 RXd. Lnqlr 69 qmti 2 S+S/Ci. Lurk. Xw 69 TIzqjliks. Ty. Ll/Fdz. A 6 VQPDu. PZ 1 n. DO _continue_=Xkj. RDQcbqj. K 8 f. OIEkhrs. Ysy. Ztn 1 bkd 0 Ldn/40 ZGf/j. Gb. TRz. Kj+l 49 f. VS 5 Qz/V _continue_=IRZ 9 jjtv. QSIEQ 9 w==
Password Protect Keys n n n But now they are only as safe as the password Where to keep password protected keys? a special file on the disk/network a floppy a smart card a really smart card
Where to Keep Public Keys? n A Public directory service – well known directory – DNS – X. 500 n BUT. . .
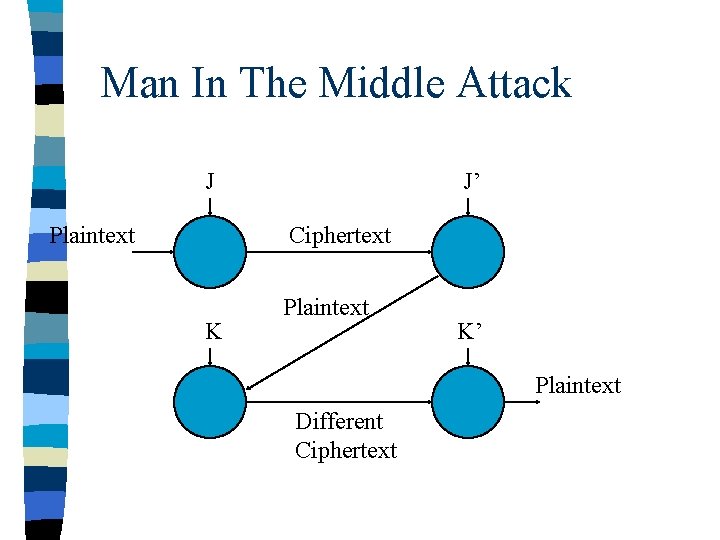
Man In The Middle Attack J Plaintext J’ Ciphertext K Plaintext K’ Plaintext Different Ciphertext
Certificates n We need to trust at least one public key n That key can be used to certify others
What is a Certificate? n A certificate is information (usually a public key) signed by another entity – I. e. certified by another entity n Other information can be included: – subject identified with the information – certificate tracking information
Public Key Infrastructure (PKI) n n Management for certificates/certificate revocation lists Management for key updates/replacement – normally two key pairs issued • confidentiality keys • signing keys n Should be transparent to users
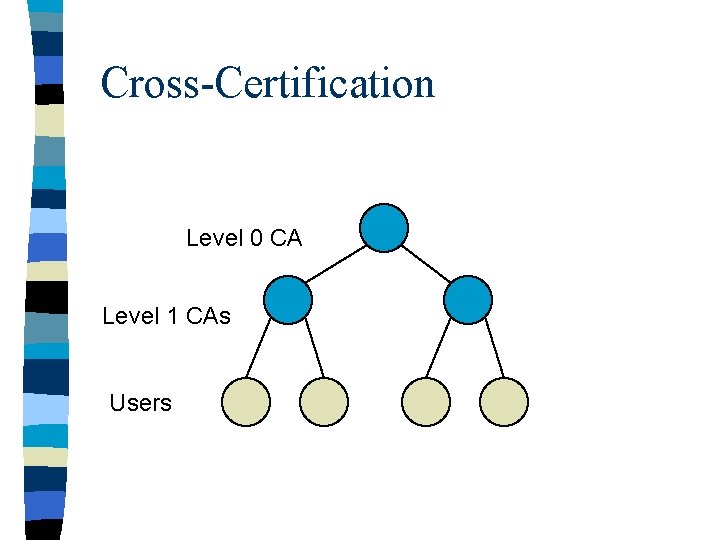
Cross-Certification Level 0 CA Level 1 CAs Users
Time-Stamping n Non-repudiation – The inability of an entity to deny having signed something n What happens if credentials are lost? ?
Teaching Points n n n n Symmetric vs. Public key systems Message Digests Key Management Man-in-the-middle Certificates Cross certification Timestamps
- Slides: 20