Privacy Policy Management October 11 2007 Privacy Policy
Privacy Policy Management October 11, 2007 Privacy Policy, Law and Technology • Carnegie Mellon University • Fall 2007 • Lorrie Cranor • http: //cups. cmu. edu/courses/privpolawtech-fa 07/ 1
Privacy & security policy management n http: //projects. cerias. purdue. edu/ocrproj/ n Today many organizations have ad hoc policies • Difficult to enforce reliably n Policy management frameworks promote consistent policy enforcement n Components • • • Policy authoring Policy conflict/gap detection/resolution Policy enforcement Policy communication Policy composition and comparison (combining multiple policies) Privacy Policy, Law and Technology • Carnegie Mellon University • Fall 2007 • Lorrie Cranor • http: //cups. cmu. edu/courses/privpolawtech-fa 07/ 2
Privacy languages serve many roles n Specify organization’s privacy policy to end users and their agents n Specify users’ privacy preferences to users’ agent n Specify organization’s privacy policy to gatekeeper server that can approve or deny requests to access database n Specify policy associated with particular data elements to parties that buy or rent data Privacy Policy, Law and Technology • Carnegie Mellon University • Fall 2007 • Lorrie Cranor • http: //cups. cmu. edu/courses/privpolawtech-fa 07/ 3
Can one privacy language do it all? n Maybe… n But so far none have emerged n We’ve found over a dozen privacy languages (including several access control and rule languages used for privacy applications) n Languages have different audiences, specify policies at different levels of granularity, and have different strengths and weaknesses Privacy Policy, Law and Technology • Carnegie Mellon University • Fall 2007 • Lorrie Cranor • http: //cups. cmu. edu/courses/privpolawtech-fa 07/ 4
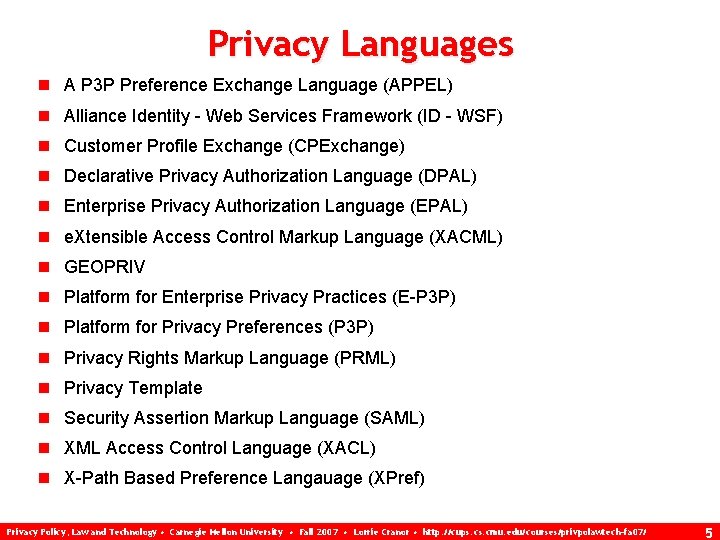
Privacy Languages n A P 3 P Preference Exchange Language (APPEL) n Alliance Identity - Web Services Framework (ID - WSF) n Customer Profile Exchange (CPExchange) n Declarative Privacy Authorization Language (DPAL) n Enterprise Privacy Authorization Language (EPAL) n e. Xtensible Access Control Markup Language (XACML) n GEOPRIV n Platform for Enterprise Privacy Practices (E-P 3 P) n Platform for Privacy Preferences (P 3 P) n Privacy Rights Markup Language (PRML) n Privacy Template n Security Assertion Markup Language (SAML) n XML Access Control Language (XACL) n X-Path Based Preference Langauage (XPref) Privacy Policy, Law and Technology • Carnegie Mellon University • Fall 2007 • Lorrie Cranor • http: //cups. cmu. edu/courses/privpolawtech-fa 07/ 5
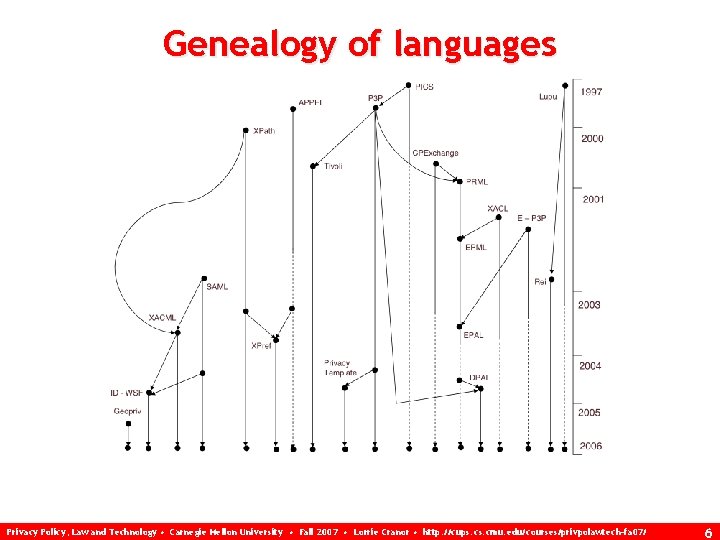
Genealogy of languages Privacy Policy, Law and Technology • Carnegie Mellon University • Fall 2007 • Lorrie Cranor • http: //cups. cmu. edu/courses/privpolawtech-fa 07/ 6
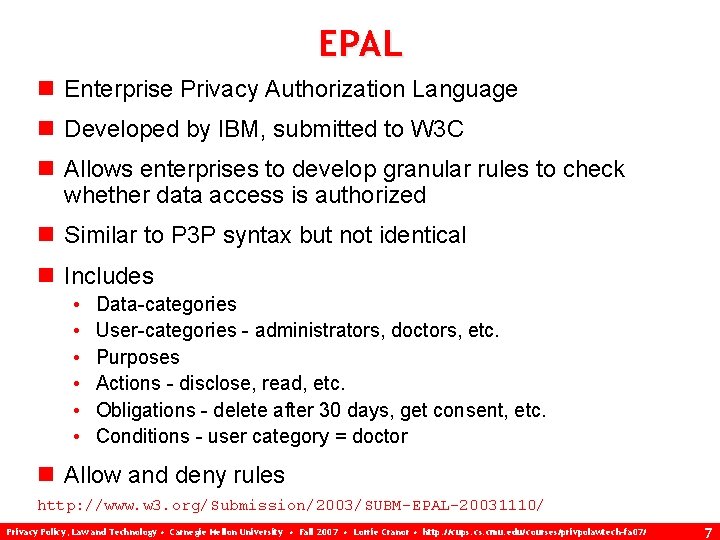
EPAL n Enterprise Privacy Authorization Language n Developed by IBM, submitted to W 3 C n Allows enterprises to develop granular rules to check whether data access is authorized n Similar to P 3 P syntax but not identical n Includes • • • Data-categories User-categories - administrators, doctors, etc. Purposes Actions - disclose, read, etc. Obligations - delete after 30 days, get consent, etc. Conditions - user category = doctor n Allow and deny rules http: //www. w 3. org/Submission/2003/SUBM-EPAL-20031110/ Privacy Policy, Law and Technology • Carnegie Mellon University • Fall 2007 • Lorrie Cranor • http: //cups. cmu. edu/courses/privpolawtech-fa 07/ 7
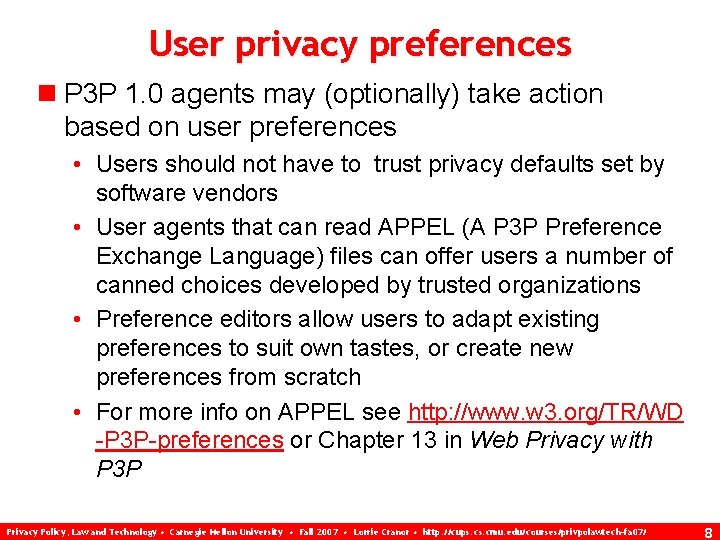
User privacy preferences n P 3 P 1. 0 agents may (optionally) take action based on user preferences • Users should not have to trust privacy defaults set by software vendors • User agents that can read APPEL (A P 3 P Preference Exchange Language) files can offer users a number of canned choices developed by trusted organizations • Preference editors allow users to adapt existing preferences to suit own tastes, or create new preferences from scratch • For more info on APPEL see http: //www. w 3. org/TR/WD -P 3 P-preferences or Chapter 13 in Web Privacy with P 3 P Privacy Policy, Law and Technology • Carnegie Mellon University • Fall 2007 • Lorrie Cranor • http: //cups. cmu. edu/courses/privpolawtech-fa 07/ 8
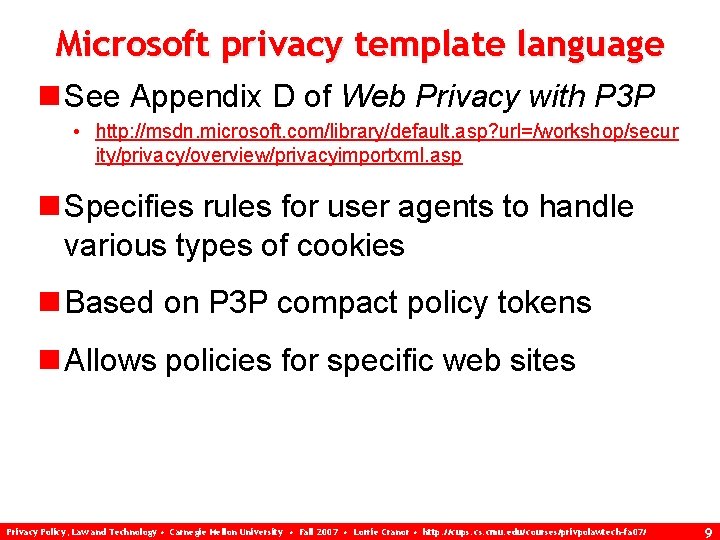
Microsoft privacy template language n See Appendix D of Web Privacy with P 3 P • http: //msdn. microsoft. com/library/default. asp? url=/workshop/secur ity/privacy/overview/privacyimportxml. asp n Specifies rules for user agents to handle various types of cookies n Based on P 3 P compact policy tokens n Allows policies for specific web sites Privacy Policy, Law and Technology • Carnegie Mellon University • Fall 2007 • Lorrie Cranor • http: //cups. cmu. edu/courses/privpolawtech-fa 07/ 9
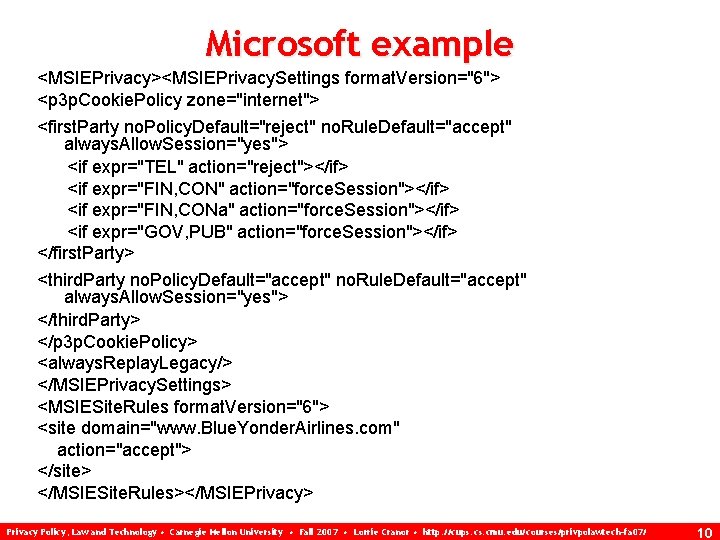
Microsoft example <MSIEPrivacy><MSIEPrivacy. Settings format. Version="6"> <p 3 p. Cookie. Policy zone="internet"> <first. Party no. Policy. Default="reject" no. Rule. Default="accept" always. Allow. Session="yes"> <if expr="TEL" action="reject"></if> <if expr="FIN, CON" action="force. Session"></if> <if expr="FIN, CONa" action="force. Session"></if> <if expr="GOV, PUB" action="force. Session"></if> </first. Party> <third. Party no. Policy. Default="accept" no. Rule. Default="accept" always. Allow. Session="yes"> </third. Party> </p 3 p. Cookie. Policy> <always. Replay. Legacy/> </MSIEPrivacy. Settings> <MSIESite. Rules format. Version="6"> <site domain="www. Blue. Yonder. Airlines. com" action="accept"> </site> </MSIESite. Rules></MSIEPrivacy> Privacy Policy, Law and Technology • Carnegie Mellon University • Fall 2007 • Lorrie Cranor • http: //cups. cmu. edu/courses/privpolawtech-fa 07/ 10
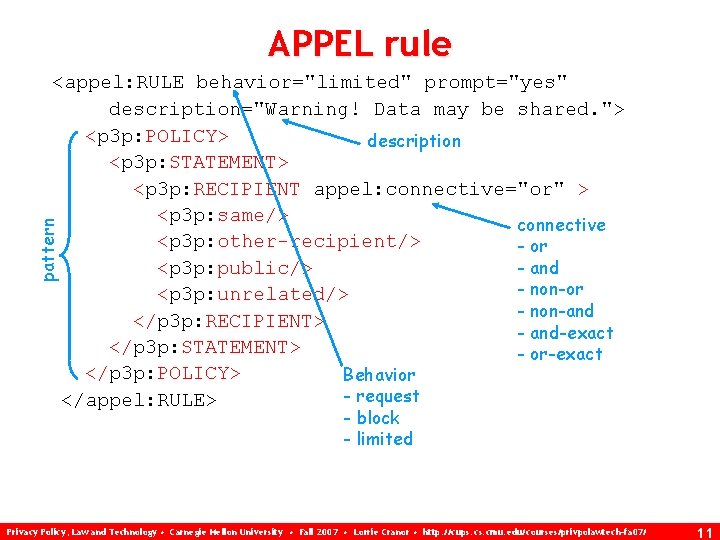
APPEL rule pattern <appel: RULE behavior="limited" prompt="yes" description="Warning! Data may be shared. "> <p 3 p: POLICY> description <p 3 p: STATEMENT> <p 3 p: RECIPIENT appel: connective="or" > <p 3 p: same/> connective <p 3 p: other-recipient/> - or <p 3 p: public/> - and - non-or <p 3 p: unrelated/> - non-and </p 3 p: RECIPIENT> - and-exact </p 3 p: STATEMENT> - or-exact </p 3 p: POLICY> Behavior - request </appel: RULE> - block - limited Privacy Policy, Law and Technology • Carnegie Mellon University • Fall 2007 • Lorrie Cranor • http: //cups. cmu. edu/courses/privpolawtech-fa 07/ 11
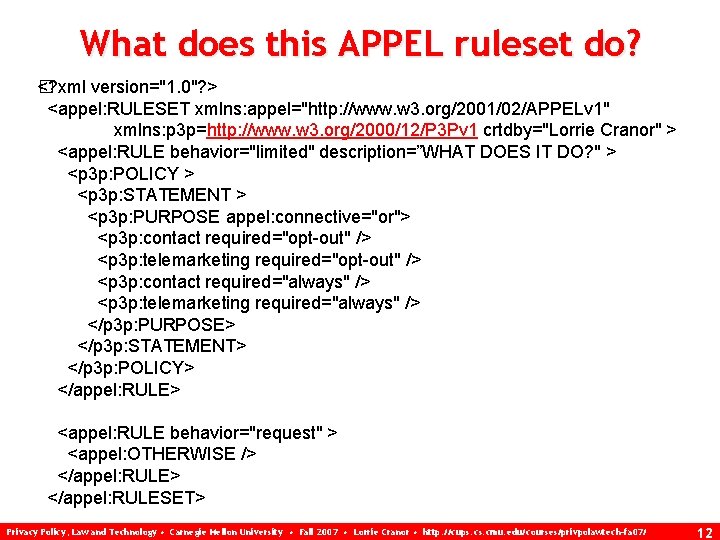
What does this APPEL ruleset do? �? xml version="1. 0"? > < <appel: RULESET xmlns: appel="http: //www. w 3. org/2001/02/APPELv 1" xmlns: p 3 p=http: //www. w 3. org/2000/12/P 3 Pv 1 crtdby="Lorrie Cranor" > <appel: RULE behavior="limited" description=”WHAT DOES IT DO? " > <p 3 p: POLICY > <p 3 p: STATEMENT > <p 3 p: PURPOSE appel: connective="or"> <p 3 p: contact required="opt-out" /> <p 3 p: telemarketing required="opt-out" /> <p 3 p: contact required="always" /> <p 3 p: telemarketing required="always" /> </p 3 p: PURPOSE> </p 3 p: STATEMENT> </p 3 p: POLICY> </appel: RULE> <appel: RULE behavior="request" > <appel: OTHERWISE /> </appel: RULESET> Privacy Policy, Law and Technology • Carnegie Mellon University • Fall 2007 • Lorrie Cranor • http: //cups. cmu. edu/courses/privpolawtech-fa 07/ 12
Creating APPEL rule sets n Express your personal privacy preferences in English • Example: "I don't want companies to share my data. " n Translate your rules into P 3 P vocabulary elements • Example: "RECIPIENT=ours" n Create an APPEL ruleset that represents your privacy preference rules (plus a catchall rule) Privacy Policy, Law and Technology • Carnegie Mellon University • Fall 2007 • Lorrie Cranor • http: //cups. cmu. edu/courses/privpolawtech-fa 07/ 13
Using APPEL to analyze P 3 P policies n Toolkit for Automated Privacy Policy Analysis (TAPPA) n http: //cups. cmu. edu/tappa/ Privacy Policy, Law and Technology • Carnegie Mellon University • Fall 2007 • Lorrie Cranor • http: //cups. cmu. edu/courses/privpolawtech-fa 07/ 14
Homework 3 Discussion n http: //cups. cmu. edu/courses/privpolawte ch-fa 07/hw/hw 3. html n Web bugs - What are they used for? Do these uses raise privacy concerns? n P 3 P user agent critiques Privacy Policy, Law and Technology • Carnegie Mellon University • Fall 2007 • Lorrie Cranor • http: //cups. cmu. edu/courses/privpolawtech-fa 07/ 15
- Slides: 15