Physical Media q physical link transmitted data bit
Physical Media q physical link: transmitted data bit propagates across link q guided media: m signals propagate in solid media: copper, fiber q unguided media: m signals propagate freely, e. g. , radio Twisted Pair (TP) q two insulated copper wires m m Category 3: traditional phone wires, 10 Mbps ethernet Category 5 TP: 100 Mbps ethernet 1
Physical Media: coax, fiber Coaxial cable: q wire (signal carrier) within a wire (shield) m m baseband: single channel on cable broadband: multiple channel on cable q bidirectional q common use in 10 Mbs Fiber optic cable: q glass fiber carrying light pulses q high-speed operation: m m 100 Mbps Ethernet high-speed point-to-point transmission (e. g. , 5 Gps) q very low error rate Ethernet 2
Physical media: radio q signal carried in electromagnetic spectrum q no physical “wire” q bidirectional q propagation environment effects: m m m reflection obstruction by objects interference Radio link types: q microwave m e. g. up to 45 Mbps channels q LAN (e. g. , 802. 11 b/g) m 11 Mbps q wide-area (e. g. , cellular) m e. g. CDPD, 10’s Kbps q satellite m up to 50 Mbps channel (or multiple smaller channels) m 270 Msec end-end delay m geosynchronous versus LEOS (low earth orbit) 3
The Data Link Layer Our goals: Overview: q understand principles q link layer services behind data link layer services: m m m error detection, correction sharing a broadcast channel: multiple access link layer addressing q error detection, correction q multiple access protocols and LANs q link layer addressing q specific link layer technologies: m Ethernet q instantiation and implementation of various link layer technologies 4
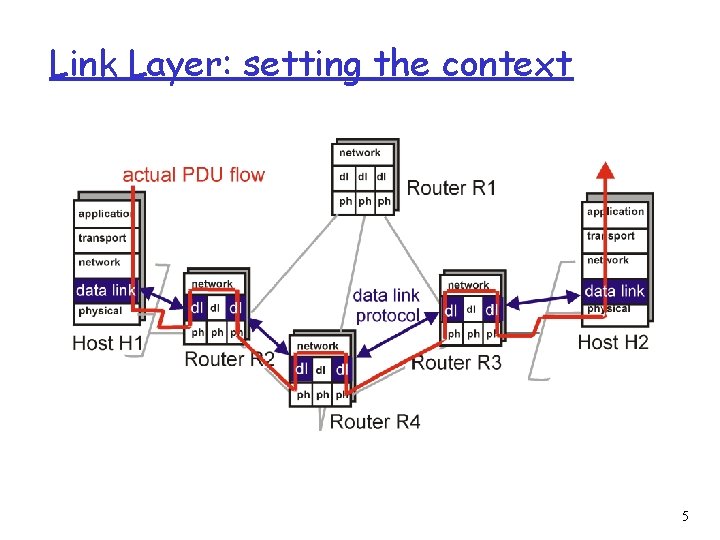
Link Layer: setting the context 5
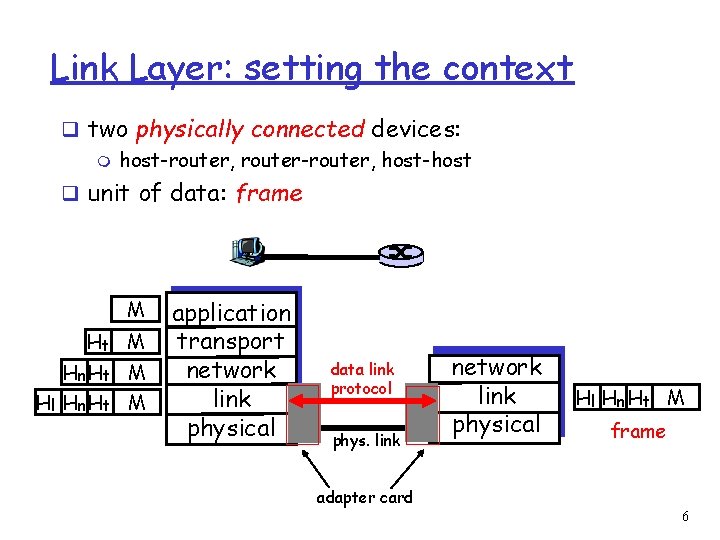
Link Layer: setting the context q two physically connected devices: m host-router, router-router, host-host q unit of data: frame M Ht M Hn Ht M Hl Hn Ht M application transport network link physical data link protocol phys. link network link physical Hl Hn Ht M frame adapter card 6
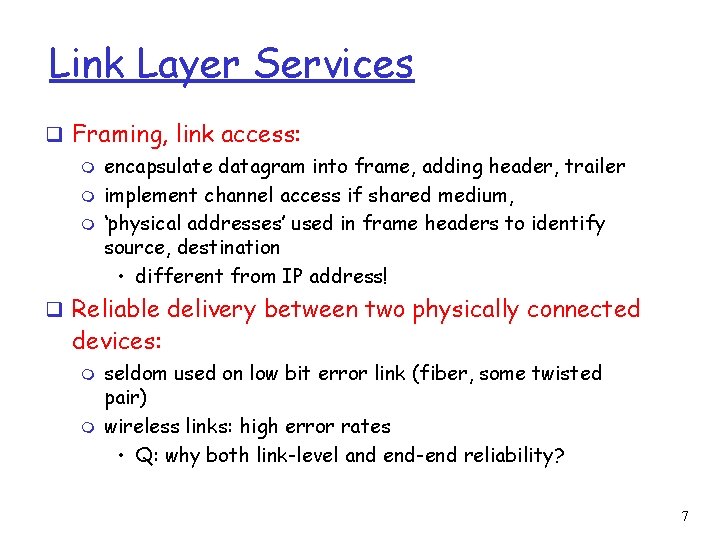
Link Layer Services q Framing, link access: m encapsulate datagram into frame, adding header, trailer m implement channel access if shared medium, m ‘physical addresses’ used in frame headers to identify source, destination • different from IP address! q Reliable delivery between two physically connected devices: m m seldom used on low bit error link (fiber, some twisted pair) wireless links: high error rates • Q: why both link-level and end-end reliability? 7
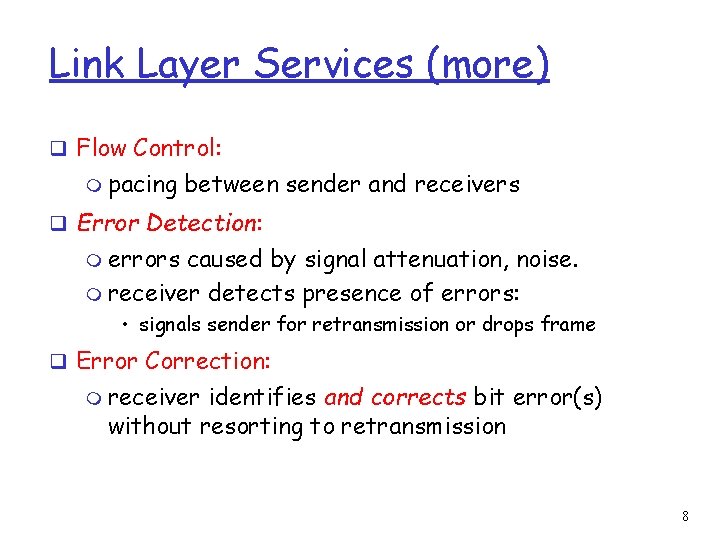
Link Layer Services (more) q Flow Control: m pacing between sender and receivers q Error Detection: m errors caused by signal attenuation, noise. m receiver detects presence of errors: • signals sender for retransmission or drops frame q Error Correction: m receiver identifies and corrects bit error(s) without resorting to retransmission 8
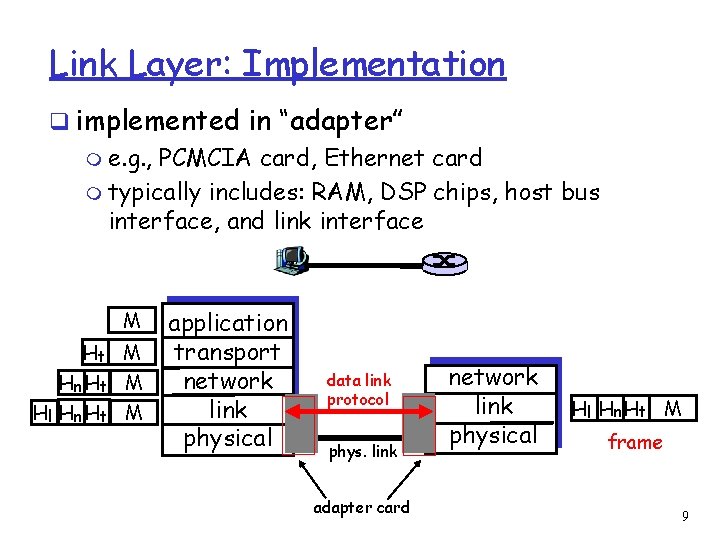
Link Layer: Implementation q implemented in “adapter” m e. g. , PCMCIA card, Ethernet card m typically includes: RAM, DSP chips, host bus interface, and link interface M Ht M Hn Ht M Hl Hn Ht M application transport network link physical data link protocol phys. link adapter card network link physical Hl Hn Ht M frame 9
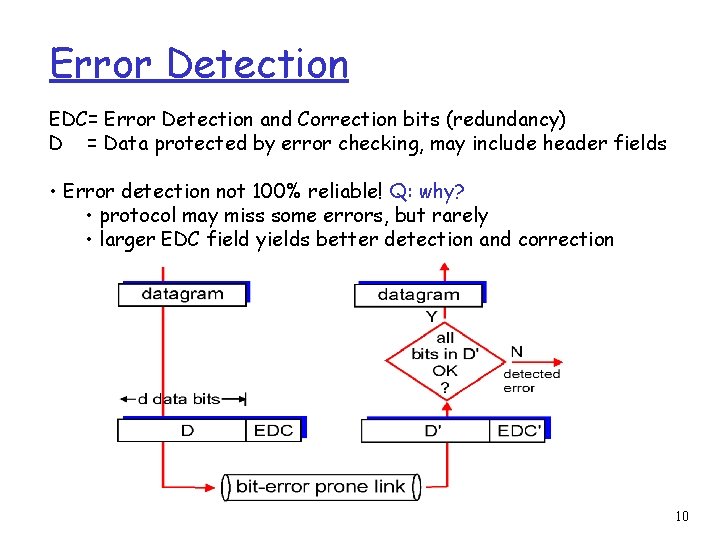
Error Detection EDC= Error Detection and Correction bits (redundancy) D = Data protected by error checking, may include header fields • Error detection not 100% reliable! Q: why? • protocol may miss some errors, but rarely • larger EDC field yields better detection and correction 10
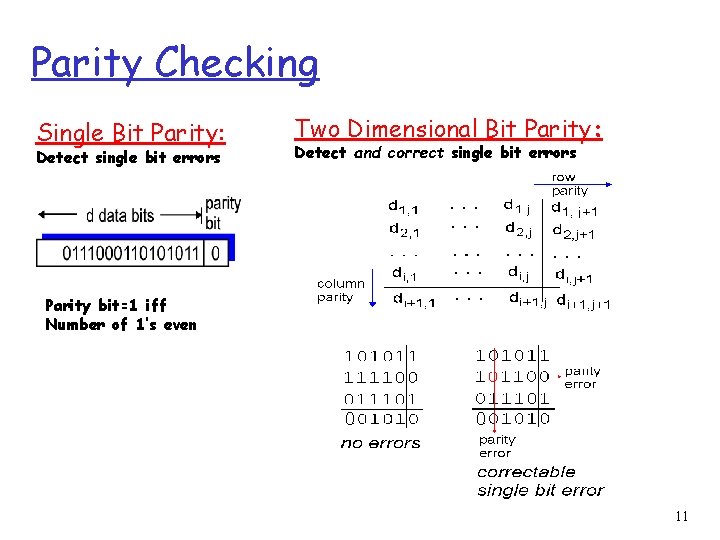
Parity Checking Single Bit Parity: Detect single bit errors Two Dimensional Bit Parity: Detect and correct single bit errors Parity bit=1 iff Number of 1’s even 0 0 11
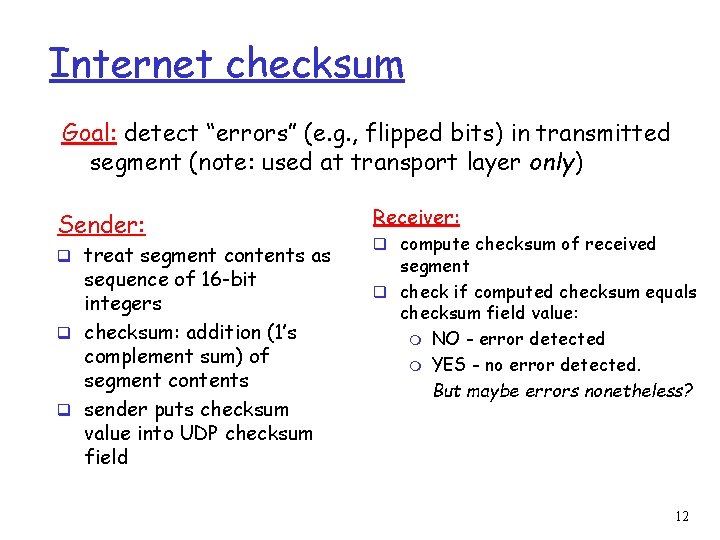
Internet checksum Goal: detect “errors” (e. g. , flipped bits) in transmitted segment (note: used at transport layer only) Sender: q treat segment contents as sequence of 16 -bit integers q checksum: addition (1’s complement sum) of segment contents q sender puts checksum value into UDP checksum field Receiver: q compute checksum of received segment q check if computed checksum equals checksum field value: m NO - error detected m YES - no error detected. But maybe errors nonetheless? 12
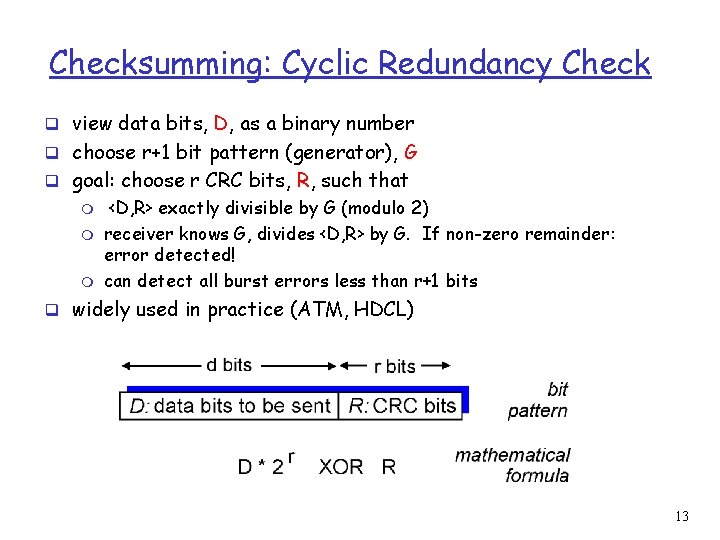
Checksumming: Cyclic Redundancy Check q view data bits, D, as a binary number q choose r+1 bit pattern (generator), G q goal: choose r CRC bits, R, such that m m m <D, R> exactly divisible by G (modulo 2) receiver knows G, divides <D, R> by G. If non-zero remainder: error detected! can detect all burst errors less than r+1 bits q widely used in practice (ATM, HDCL) 13
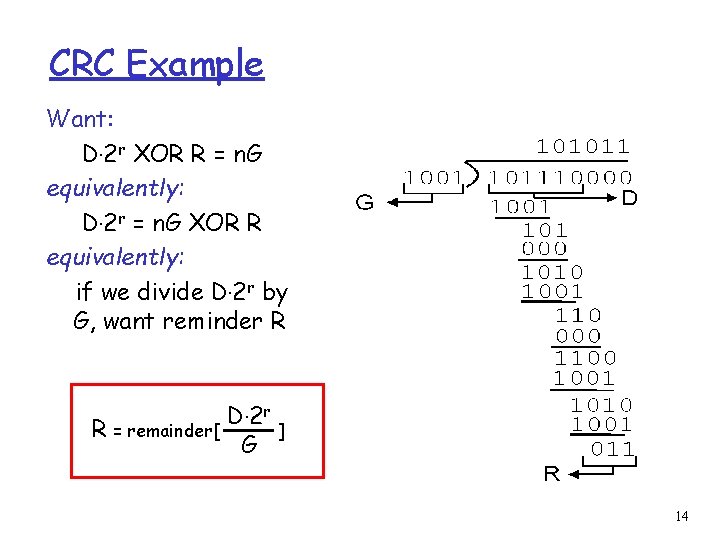
CRC Example Want: D. 2 r XOR R = n. G equivalently: D. 2 r = n. G XOR R equivalently: if we divide D. 2 r by G, want reminder R R = remainder[ D. 2 r G ] 14
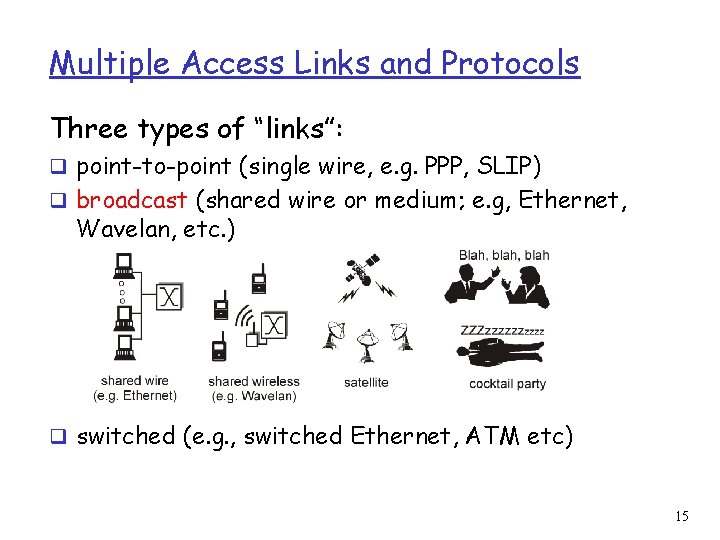
Multiple Access Links and Protocols Three types of “links”: q point-to-point (single wire, e. g. PPP, SLIP) q broadcast (shared wire or medium; e. g, Ethernet, Wavelan, etc. ) q switched (e. g. , switched Ethernet, ATM etc) 15
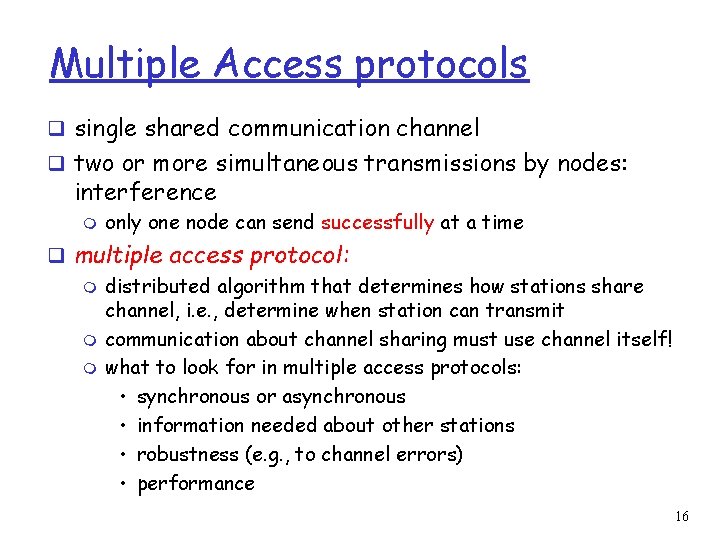
Multiple Access protocols q single shared communication channel q two or more simultaneous transmissions by nodes: interference m only one node can send successfully at a time q multiple access protocol: m distributed algorithm that determines how stations share channel, i. e. , determine when station can transmit m communication about channel sharing must use channel itself! m what to look for in multiple access protocols: • synchronous or asynchronous • information needed about other stations • robustness (e. g. , to channel errors) • performance 16
Multiple Access protocols q claim: humans use multiple access protocols all the time q class can "guess" multiple access protocols m multiaccess protocol 1: m multiaccess protocol 2: m multiaccess protocol 3: m multiaccess protocol 4: 17
MAC Protocols: a taxonomy Three broad classes: q Channel Partitioning m m divide channel into smaller “pieces” (time slots, frequency) allocate piece to node for exclusive use q Random Access m allow collisions m “recover” from collisions q “Taking turns” m tightly coordinate shared access to avoid collisions Goal: efficient, fair, simple, decentralized 18
MAC Protocols: Measures q Channel Rate = R bps q Efficient: m Single user: Throughput R q Fairness m. N users m Min. user throughput R/N q Decentralized m Fault tolerance q Simple 19
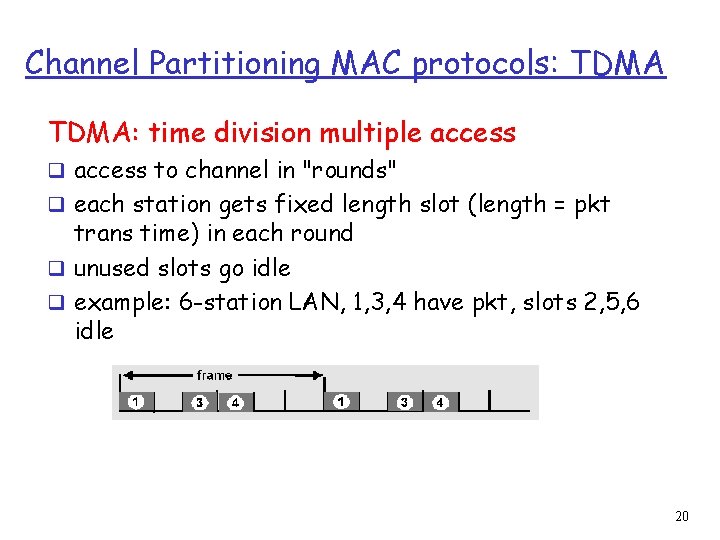
Channel Partitioning MAC protocols: TDMA: time division multiple access q access to channel in "rounds" q each station gets fixed length slot (length = pkt trans time) in each round q unused slots go idle q example: 6 -station LAN, 1, 3, 4 have pkt, slots 2, 5, 6 idle 20
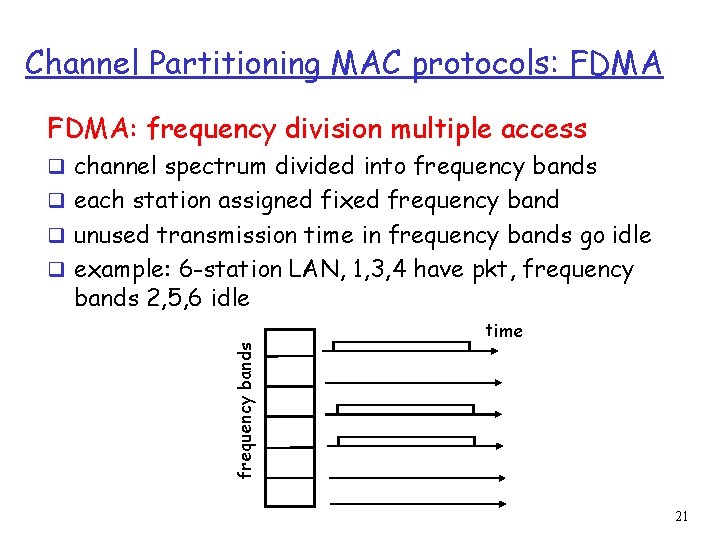
Channel Partitioning MAC protocols: FDMA: frequency division multiple access q channel spectrum divided into frequency bands q each station assigned fixed frequency band q unused transmission time in frequency bands go idle q example: 6 -station LAN, 1, 3, 4 have pkt, frequency bands 2, 5, 6 idle frequency bands time 21
TDMA & FDMA: Performance q Channel Rate = R bps q Single user m Throughput R/N q Fairness m Each user gets the same allocation m Depends on maximum number of users q Decentralized m Requires division q Simple 22
Channel Partitioning (CDMA) CDMA (Code Division Multiple Access) q unique “code” assigned to each user; ie, code set partitioning q used mostly in wireless broadcast channels (cellular, q q satellite, etc) all users share same frequency, but each user has own “chipping” sequence (ie, code) to encode data encoded signal = (original data) X (chipping sequence) decoding: inner-product of encoded signal and chipping sequence allows multiple users to “coexist” and transmit simultaneously with minimal interference (if codes are “orthogonal”) 23
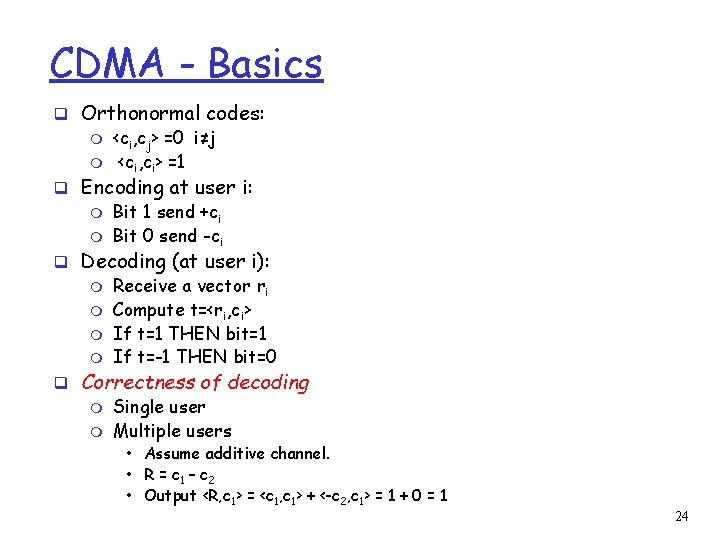
CDMA - Basics q Orthonormal codes: m <ci, cj> =0 i≠j m <ci, ci> =1 q Encoding at user i: m Bit 1 send +ci m Bit 0 send -ci q Decoding (at user i): m Receive a vector ri m Compute t=<ri, ci> m If t=1 THEN bit=1 m If t=-1 THEN bit=0 q Correctness of decoding m Single user m Multiple users • Assume additive channel. • R = c 1 – c 2 • Output <R, c 1> = <c 1, c 1> + <-c 2, c 1> = 1 + 0 = 1 24
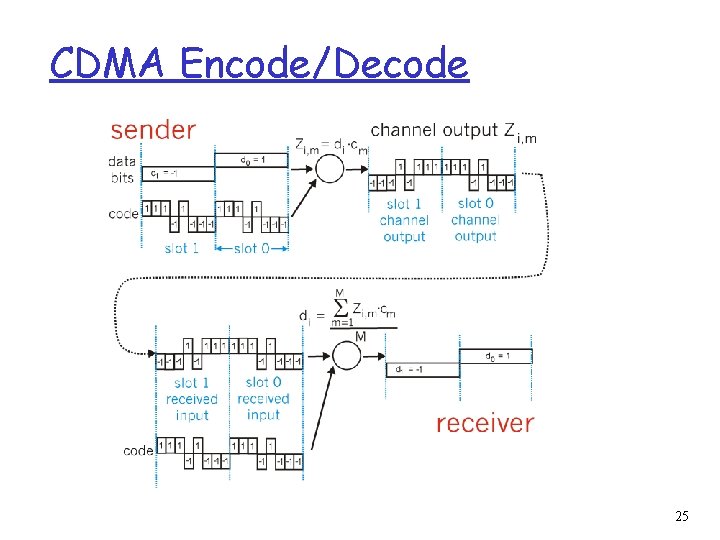
CDMA Encode/Decode 25
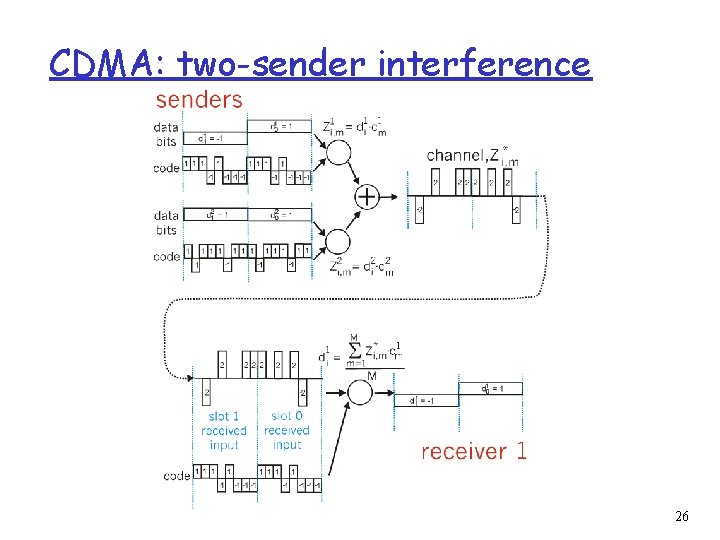
CDMA: two-sender interference 26
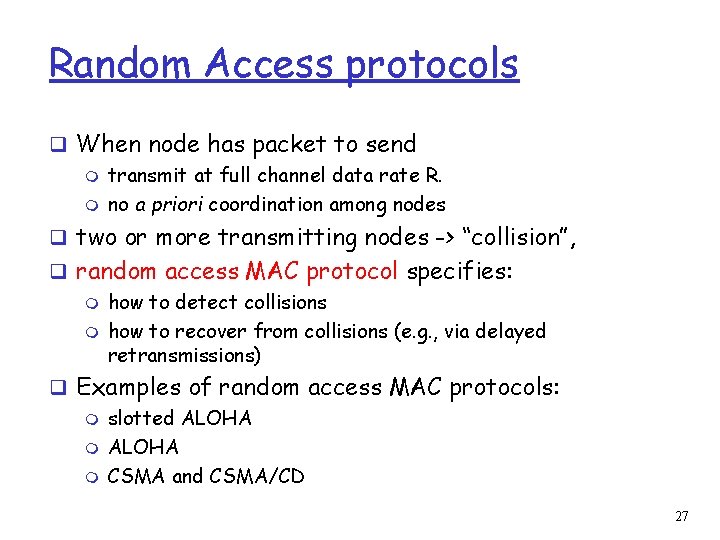
Random Access protocols q When node has packet to send m transmit at full channel data rate R. m no a priori coordination among nodes q two or more transmitting nodes -> “collision”, q random access MAC protocol specifies: m how to detect collisions m how to recover from collisions (e. g. , via delayed retransmissions) q Examples of random access MAC protocols: m slotted ALOHA m CSMA and CSMA/CD 27
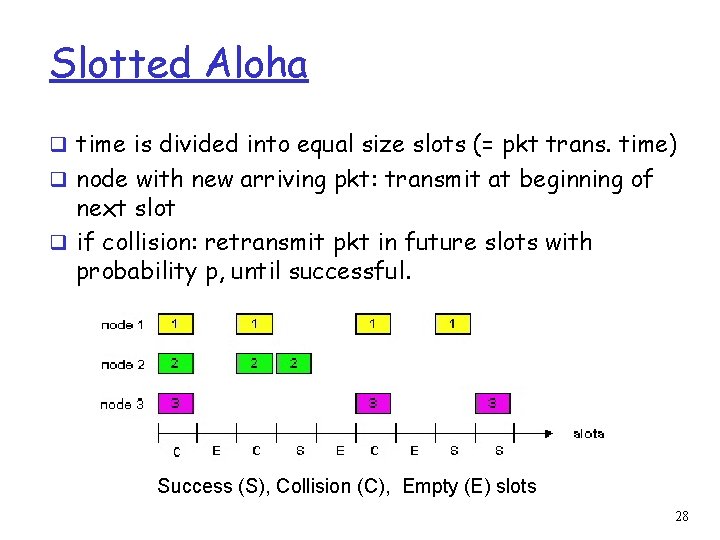
Slotted Aloha q time is divided into equal size slots (= pkt trans. time) q node with new arriving pkt: transmit at beginning of next slot q if collision: retransmit pkt in future slots with probability p, until successful. Success (S), Collision (C), Empty (E) slots 28
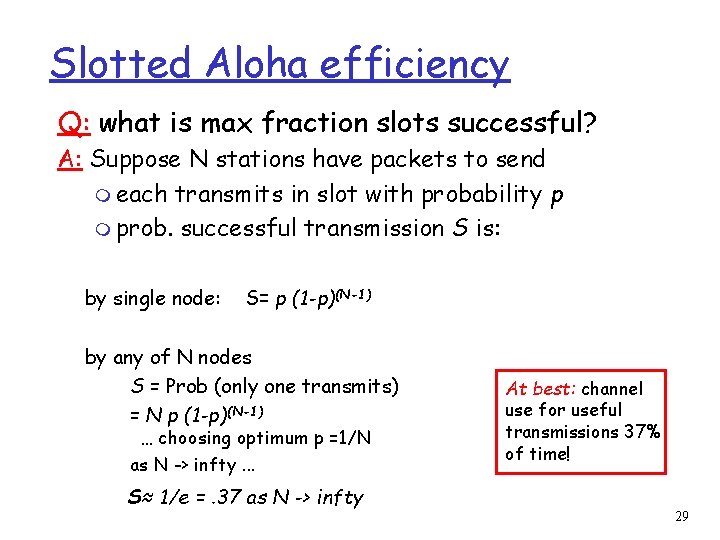
Slotted Aloha efficiency Q: what is max fraction slots successful? A: Suppose N stations have packets to send m each transmits in slot with probability p m prob. successful transmission S is: by single node: S= p (1 -p)(N-1) by any of N nodes S = Prob (only one transmits) = N p (1 -p)(N-1) … choosing optimum p =1/N as N -> infty. . . S≈ 1/e =. 37 as N -> infty At best: channel use for useful transmissions 37% of time! 29
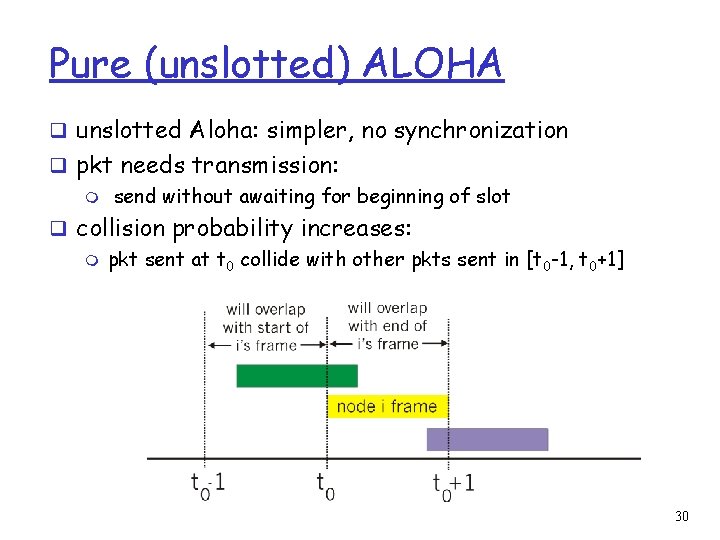
Pure (unslotted) ALOHA q unslotted Aloha: simpler, no synchronization q pkt needs transmission: m send without awaiting for beginning of slot q collision probability increases: m pkt sent at t 0 collide with other pkts sent in [t 0 -1, t 0+1] 30
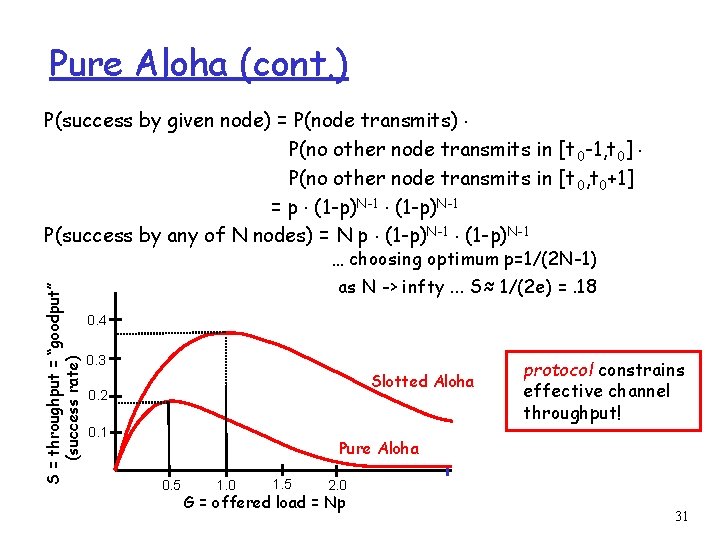
Pure Aloha (cont. ) P(success by given node) = P(node transmits). P(no other node transmits in [t 0 -1, t 0]. P(no other node transmits in [t 0, t 0+1] = p. (1 -p)N-1 P(success by any of N nodes) = N p. (1 -p)N-1 S = throughput = “goodput” (success rate) … choosing optimum p=1/(2 N-1) as N -> infty. . . S≈ 1/(2 e) =. 18 0. 4 0. 3 Slotted Aloha 0. 2 0. 1 protocol constrains effective channel throughput! Pure Aloha 0. 5 1. 0 1. 5 2. 0 G = offered load = Np 31
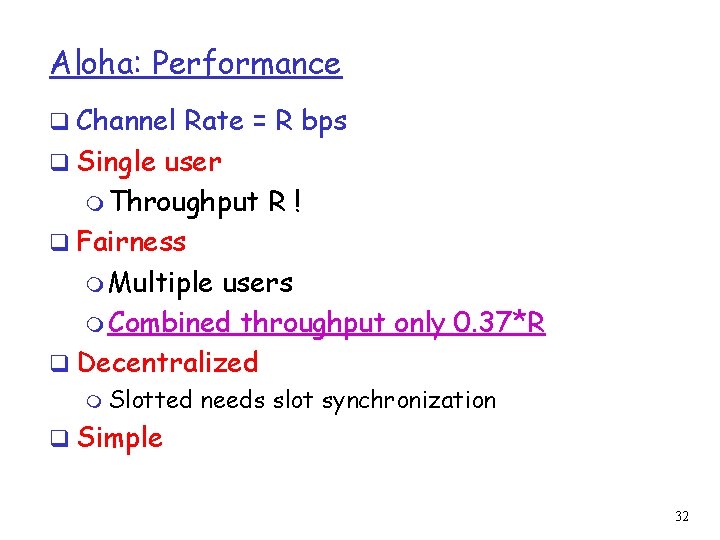
Aloha: Performance q Channel Rate = R bps q Single user m Throughput R! q Fairness m Multiple users m Combined throughput only 0. 37*R q Decentralized m Slotted needs slot synchronization q Simple 32
CSMA: Carrier Sense Multiple Access) CSMA: listen before transmit: q If channel sensed idle: transmit entire pkt q If channel sensed busy, defer transmission m Persistent CSMA: retry immediately with probability p when channel becomes idle m Non-persistent CSMA: retry after random interval q human analogy: don’t interrupt others! 33
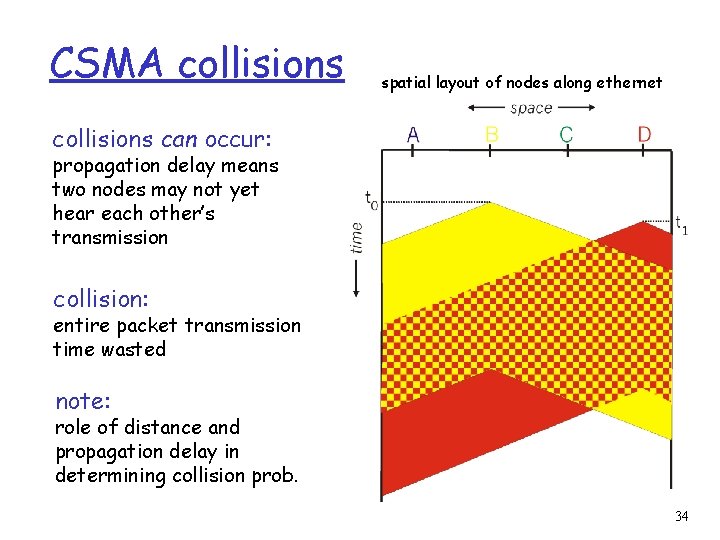
CSMA collisions spatial layout of nodes along ethernet collisions can occur: propagation delay means two nodes may not yet hear each other’s transmission collision: entire packet transmission time wasted note: role of distance and propagation delay in determining collision prob. 34
CSMA/CD (Collision Detection) CSMA/CD: carrier sensing, deferral as in CSMA m collisions detected within short time m colliding transmissions aborted, reducing channel wastage m persistent or non-persistent retransmission q collision detection: m easy in wired LANs: measure signal strengths, compare transmitted, received signals m difficult in wireless LANs: receiver shut off while transmitting q human analogy: the polite conversationalist 35
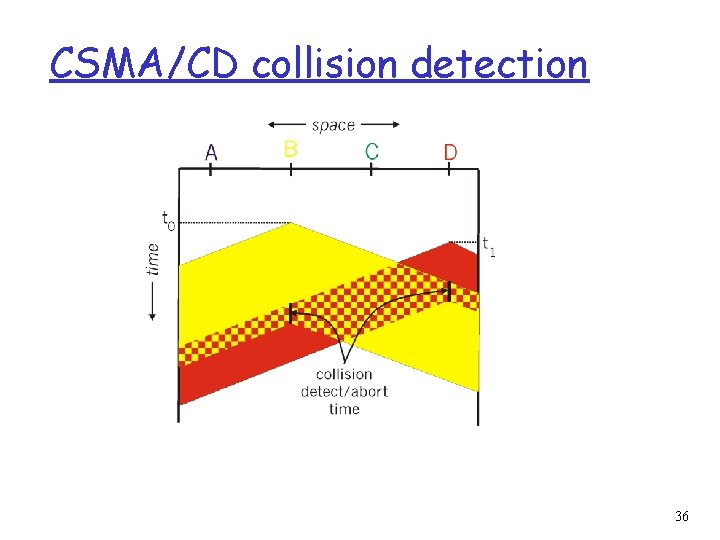
CSMA/CD collision detection 36
CDMA/CD q Channel Rate = R bps q Single user m Throughput q Fairness R m Multiple users m Depends on Detection Time q Decentralized m Completely q Simple m Needs collision detection hardware 37
“Taking Turns” MAC protocols channel partitioning MAC protocols: m share channel efficiently at high load m inefficient at low load: delay in channel access, 1/N bandwidth allocated even if only 1 active node! Random access MAC protocols m efficient at low load: single node can fully utilize channel m high load: collision overhead “taking turns” protocols look for best of both worlds! 38
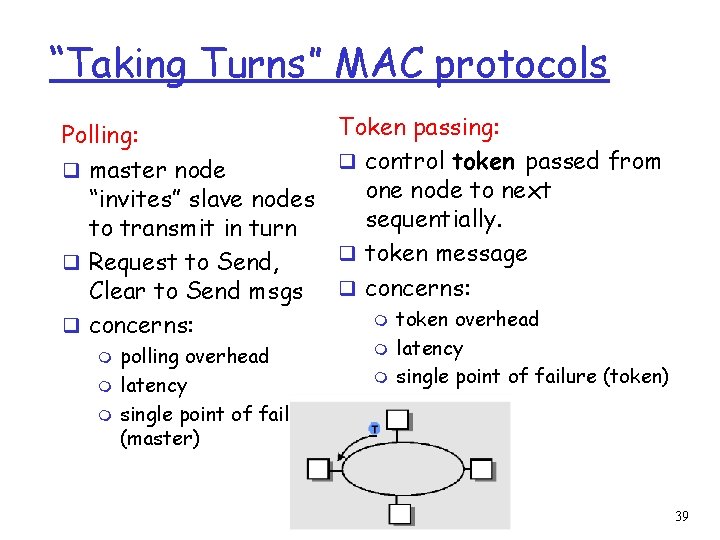
“Taking Turns” MAC protocols Polling: q master node “invites” slave nodes to transmit in turn q Request to Send, Clear to Send msgs q concerns: m m m polling overhead latency single point of failure (master) Token passing: q control token passed from one node to next sequentially. q token message q concerns: m m m token overhead latency single point of failure (token) 39
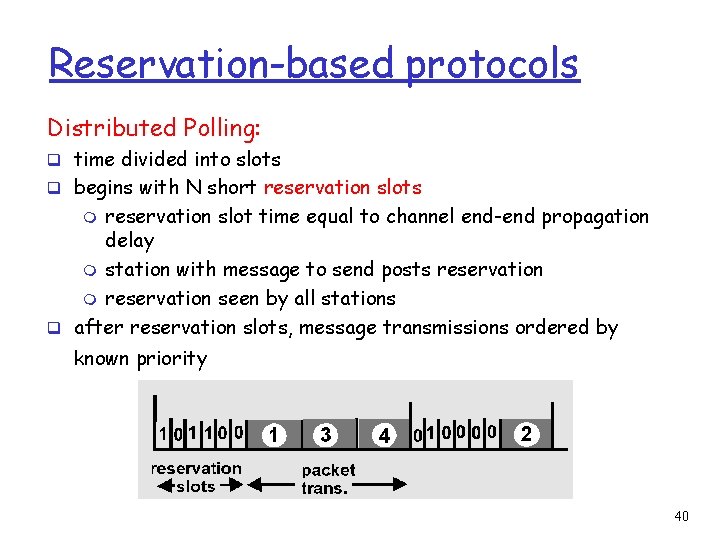
Reservation-based protocols Distributed Polling: q time divided into slots q begins with N short reservation slots reservation slot time equal to channel end-end propagation delay m station with message to send posts reservation m reservation seen by all stations q after reservation slots, message transmissions ordered by m known priority 40
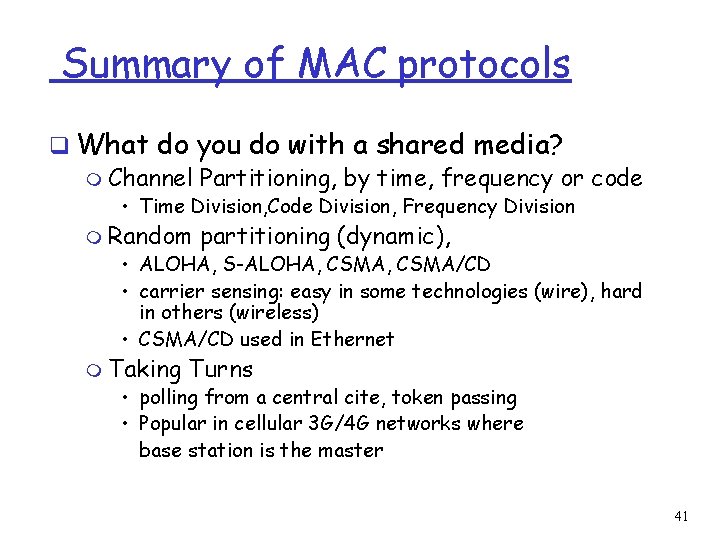
Summary of MAC protocols q What do you do with a shared media? m Channel Partitioning, by time, frequency or code • Time Division, Code Division, Frequency Division m Random partitioning (dynamic), • ALOHA, S-ALOHA, CSMA/CD • carrier sensing: easy in some technologies (wire), hard in others (wireless) • CSMA/CD used in Ethernet m Taking Turns • polling from a central cite, token passing • Popular in cellular 3 G/4 G networks where base station is the master 41
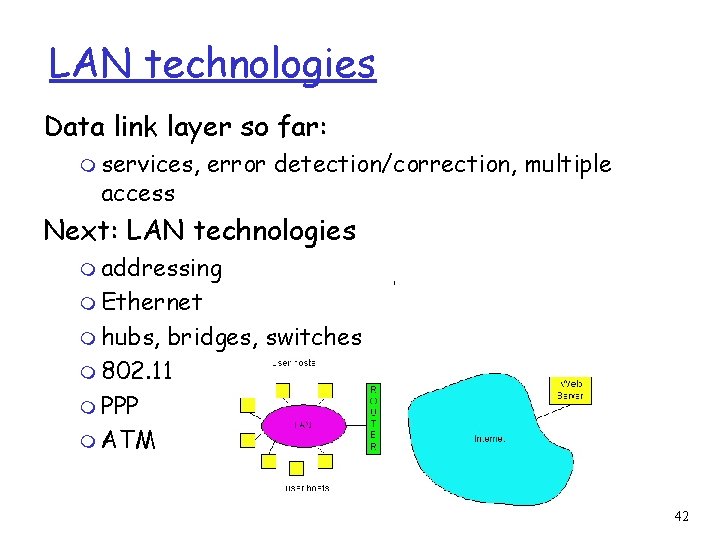
LAN technologies Data link layer so far: m services, access error detection/correction, multiple Next: LAN technologies m addressing m Ethernet m hubs, bridges, switches m 802. 11 m PPP m ATM 42
LAN Addresses 32 -bit IP address: q network-layer address q used to get datagram to destination network LAN (or MAC or physical) address: q used to get datagram from one interface to another physically-connected interface (same network) q 48 bit MAC address (for most LANs) burned in the adapter ROM 43
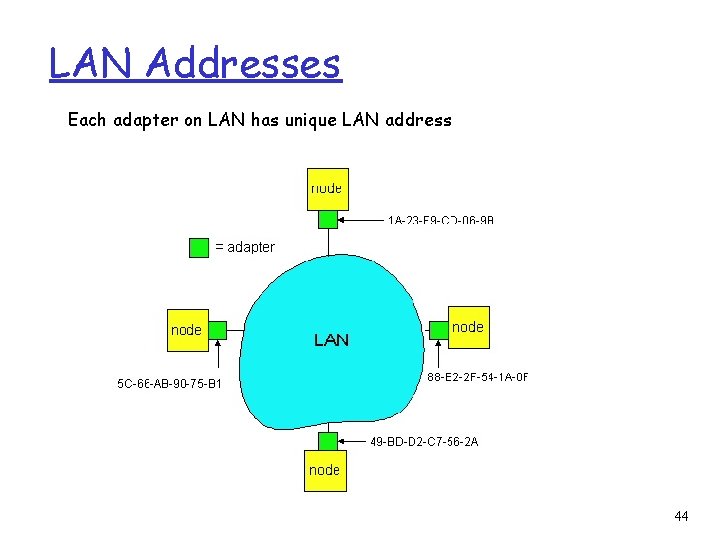
LAN Addresses Each adapter on LAN has unique LAN address 44
LAN Address (more) q MAC address allocation administered by IEEE q manufacturer buys portion of MAC address space (to assure uniqueness) q Analogy: (a) MAC address: like Social Security Number (b) IP address: like postal address q MAC flat address => portability m can move LAN card from one LAN to another q IP hierarchical address NOT portable m depends on network to which one attaches q ARP protocol translates IP address to MAC address 45
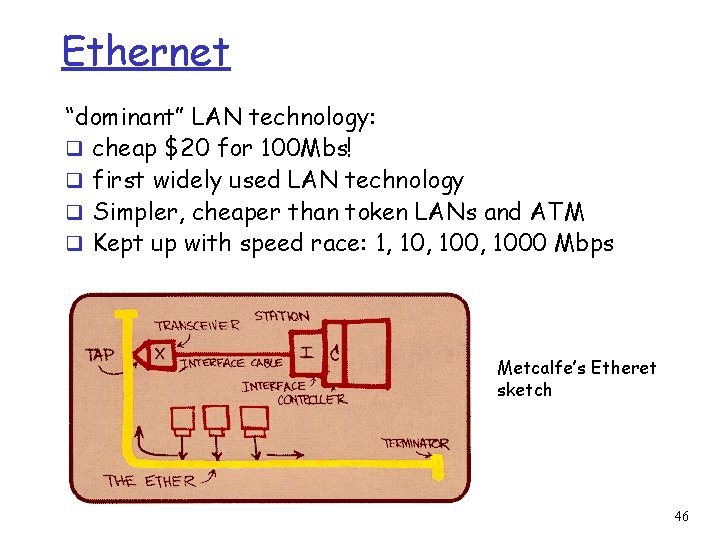
Ethernet “dominant” LAN technology: q cheap $20 for 100 Mbs! q first widely used LAN technology q Simpler, cheaper than token LANs and ATM q Kept up with speed race: 1, 100, 1000 Mbps Metcalfe’s Etheret sketch 46
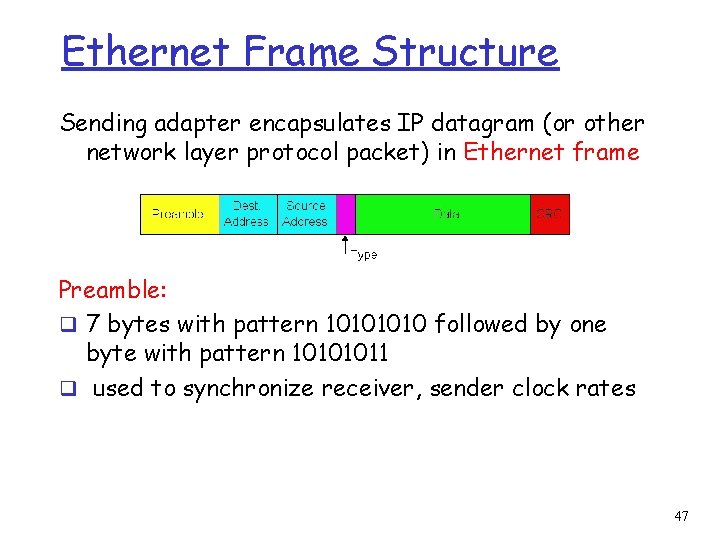
Ethernet Frame Structure Sending adapter encapsulates IP datagram (or other network layer protocol packet) in Ethernet frame Preamble: q 7 bytes with pattern 1010 followed by one byte with pattern 10101011 q used to synchronize receiver, sender clock rates 47
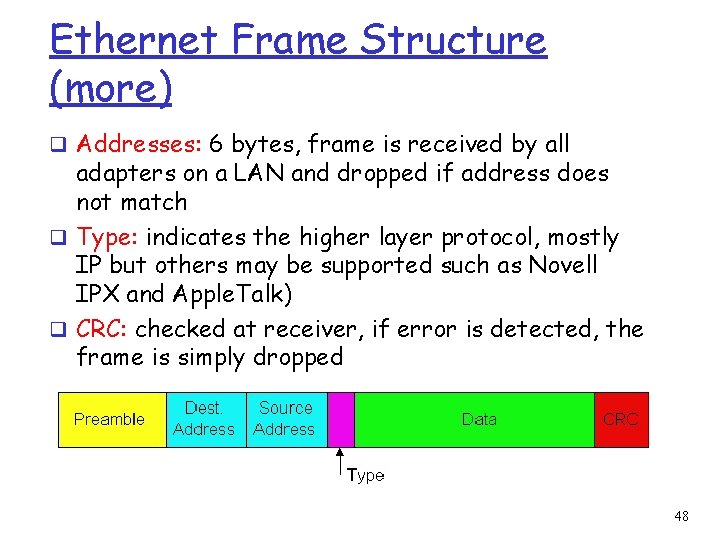
Ethernet Frame Structure (more) q Addresses: 6 bytes, frame is received by all adapters on a LAN and dropped if address does not match q Type: indicates the higher layer protocol, mostly IP but others may be supported such as Novell IPX and Apple. Talk) q CRC: checked at receiver, if error is detected, the frame is simply dropped 48
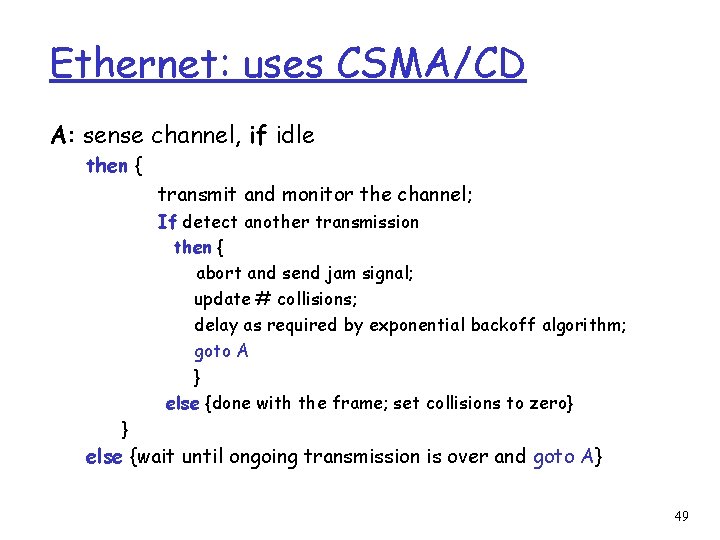
Ethernet: uses CSMA/CD A: sense channel, if idle then { transmit and monitor the channel; If detect another transmission then { abort and send jam signal; update # collisions; delay as required by exponential backoff algorithm; goto A } else {done with the frame; set collisions to zero} } else {wait until ongoing transmission is over and goto A} 49
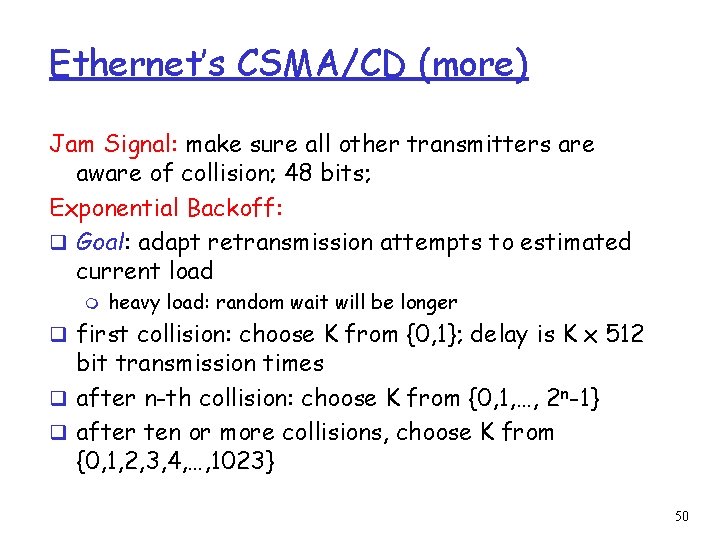
Ethernet’s CSMA/CD (more) Jam Signal: make sure all other transmitters are aware of collision; 48 bits; Exponential Backoff: q Goal: adapt retransmission attempts to estimated current load m heavy load: random wait will be longer q first collision: choose K from {0, 1}; delay is K x 512 bit transmission times q after n-th collision: choose K from {0, 1, …, 2 n-1} q after ten or more collisions, choose K from {0, 1, 2, 3, 4, …, 1023} 50
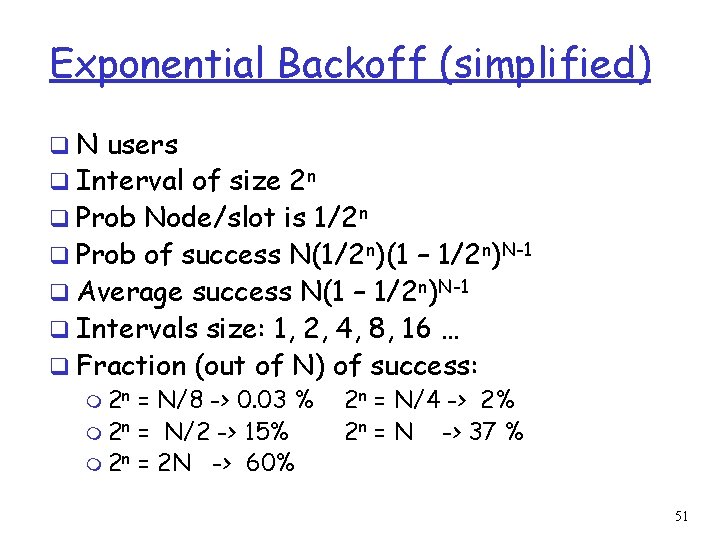
Exponential Backoff (simplified) q N users q Interval of size 2 n q Prob Node/slot is 1/2 n q Prob of success N(1/2 n)(1 – 1/2 n)N-1 q Average success N(1 – 1/2 n)N-1 q Intervals size: 1, 2, 4, 8, 16 … q Fraction (out of N) of success: m 2 n = N/8 -> 0. 03 % 2 n = N/4 -> 2% m 2 n = N/2 -> 15% 2 n = N -> 37 % m 2 n = 2 N -> 60% 51
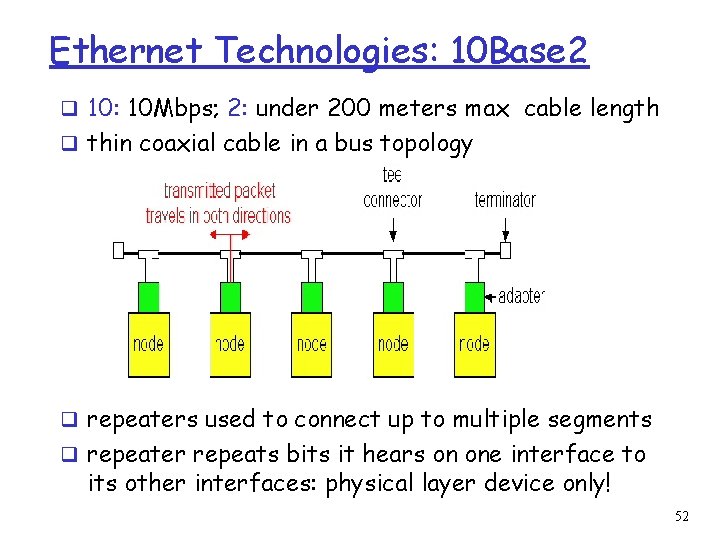
Ethernet Technologies: 10 Base 2 q 10: 10 Mbps; 2: under 200 meters max cable length q thin coaxial cable in a bus topology q repeaters used to connect up to multiple segments q repeater repeats bits it hears on one interface to its other interfaces: physical layer device only! 52
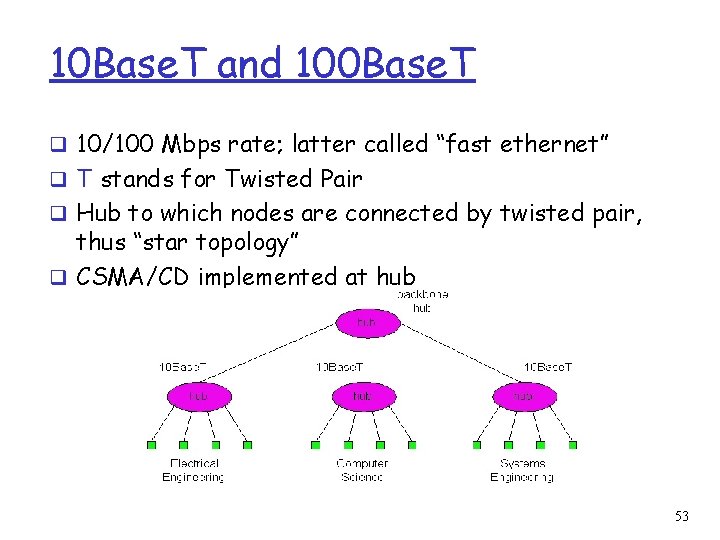
10 Base. T and 100 Base. T q 10/100 Mbps rate; latter called “fast ethernet” q T stands for Twisted Pair q Hub to which nodes are connected by twisted pair, thus “star topology” q CSMA/CD implemented at hub 53
10 Base. T and 100 Base. T (more) q Max distance from node to Hub is 100 meters q Hub can disconnect “jabbering adapter q Hub can gather monitoring information, statistics for display to LAN administrators 54
Gbit Ethernet q use standard Ethernet frame format q allows for point-to-point links and shared broadcast channels q in shared mode, CSMA/CD is used; short distances between nodes to be efficient q uses hubs, called here “Buffered Distributors” q Full-Duplex at 1 Gbps for point-to-point links 55
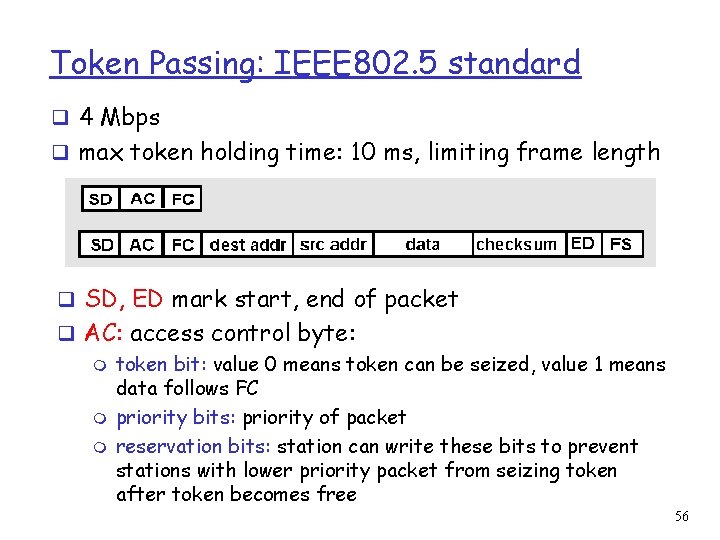
Token Passing: IEEE 802. 5 standard q 4 Mbps q max token holding time: 10 ms, limiting frame length q SD, ED mark start, end of packet q AC: access control byte: m token bit: value 0 means token can be seized, value 1 means data follows FC m priority bits: priority of packet m reservation bits: station can write these bits to prevent stations with lower priority packet from seizing token after token becomes free 56
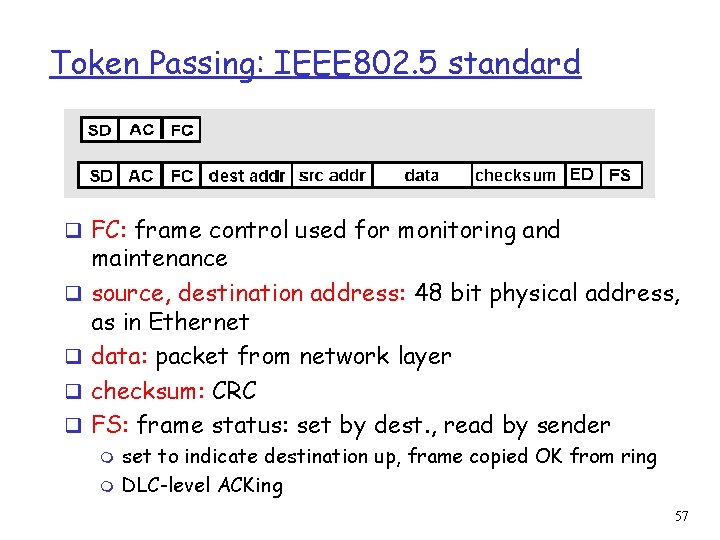
Token Passing: IEEE 802. 5 standard q FC: frame control used for monitoring and q q maintenance source, destination address: 48 bit physical address, as in Ethernet data: packet from network layer checksum: CRC FS: frame status: set by dest. , read by sender m m set to indicate destination up, frame copied OK from ring DLC-level ACKing 57
- Slides: 57