pCycles Network Protection with Ringspeed and Meshefficiency 1
![References on p-Cycles • [1] W. D. Grover, D. Stamatelakis, "Cycle-Oriented Distributed Preconfiguration: Ring-like References on p-Cycles • [1] W. D. Grover, D. Stamatelakis, "Cycle-Oriented Distributed Preconfiguration: Ring-like](https://slidetodoc.com/presentation_image/2b6a1a4bcfd159ff605e263ac0e05878/image-39.jpg)
- Slides: 39
p-Cycles: Network Protection with Ring-speed and Mesh-efficiency 1 st COST 270 Workshop on Reliability of Optical Networks, Systems and Components December 13, 2001 - EMPA, Dubendorf, Switzerland Dominic Schupke Claus Gruber Wayne Grover Demetrios Stamatelakis Munich University of Technology Institute of Communication Networks TRLabs, University of Alberta
Outline • • • Motivation Basics p-Cycles in WDM Networks Self-organization of p-Cycles in IP Router Restoration (Overview) Summary
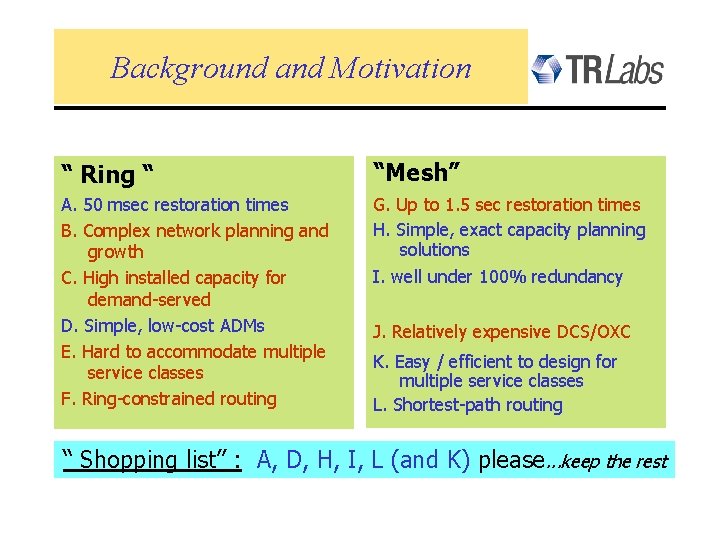
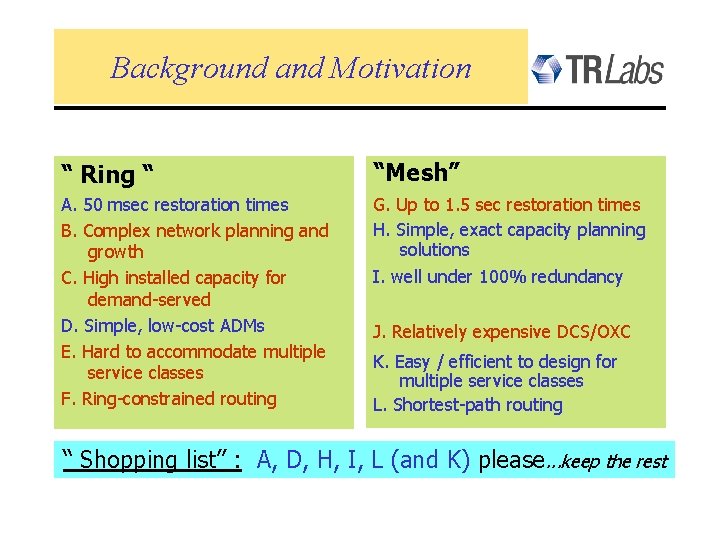
Background and Motivation “ Ring “ “Mesh” A. 50 msec restoration times B. Complex network planning and growth C. High installed capacity for demand-served D. Simple, low-cost ADMs E. Hard to accommodate multiple service classes F. Ring-constrained routing G. Up to 1. 5 sec restoration times H. Simple, exact capacity planning solutions I. well under 100% redundancy J. Relatively expensive DCS/OXC K. Easy / efficient to design for multiple service classes L. Shortest-path routing “ Shopping list” : A, D, H, I, L (and K) please. . . keep the rest
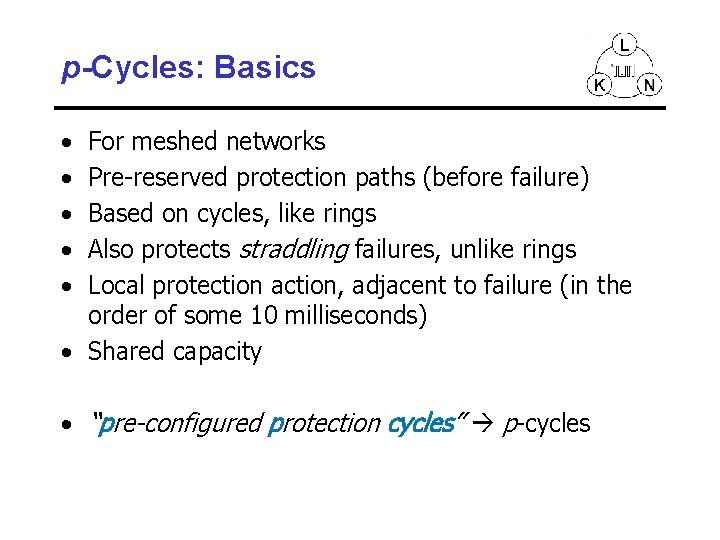
p-Cycles: Basics • • • For meshed networks Pre-reserved protection paths (before failure) Based on cycles, like rings Also protects straddling failures, unlike rings Local protection action, adjacent to failure (in the order of some 10 milliseconds) • Shared capacity • “pre-configured protection cycles” p-cycles
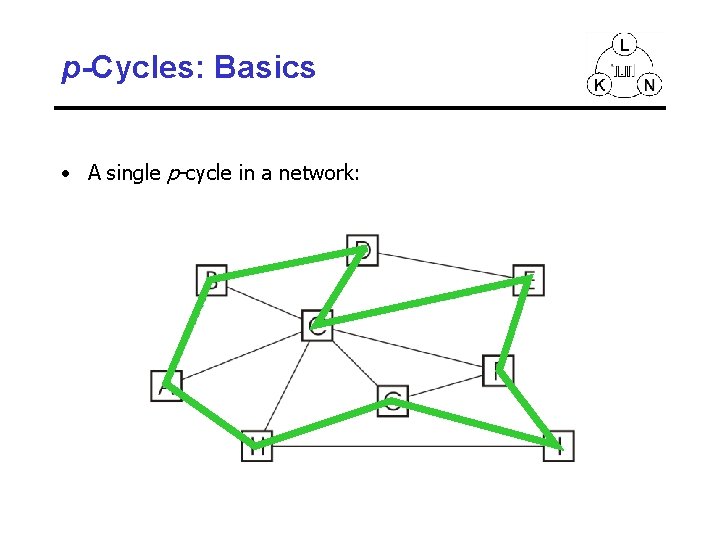
p-Cycles: Basics • A single p-cycle in a network:
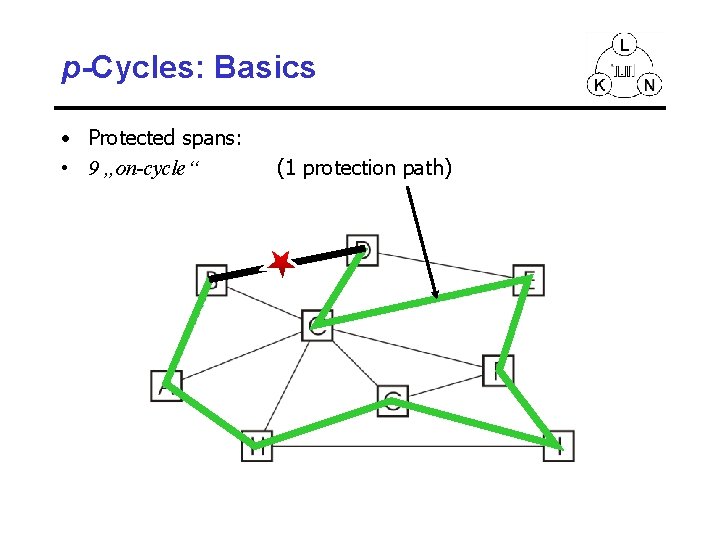
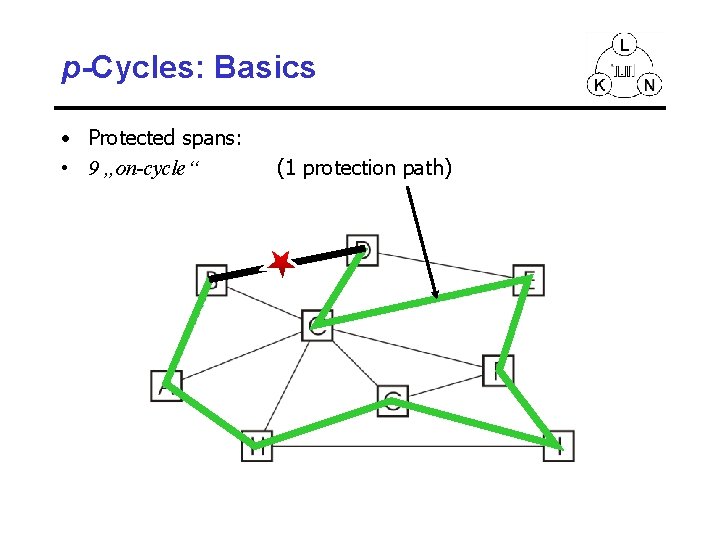
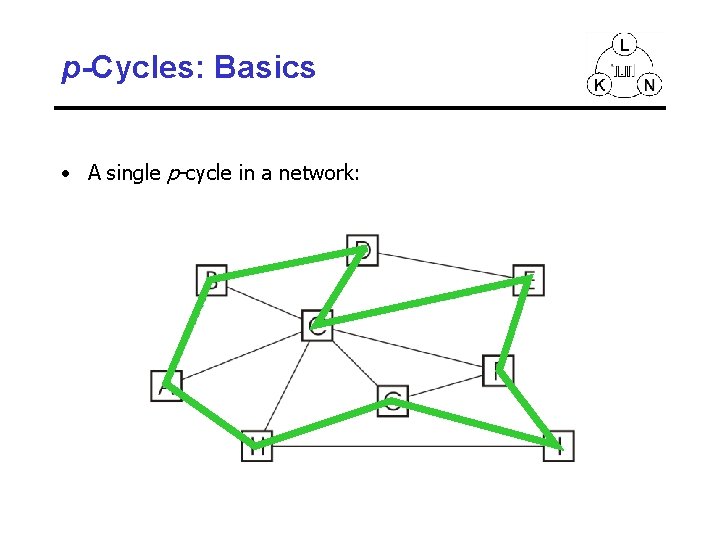
p-Cycles: Basics • Protected spans: • 9 „on-cycle“ (1 protection path)
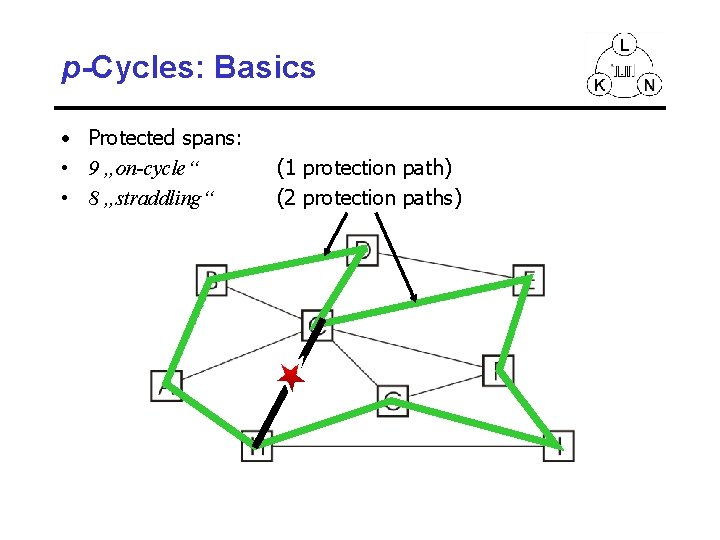
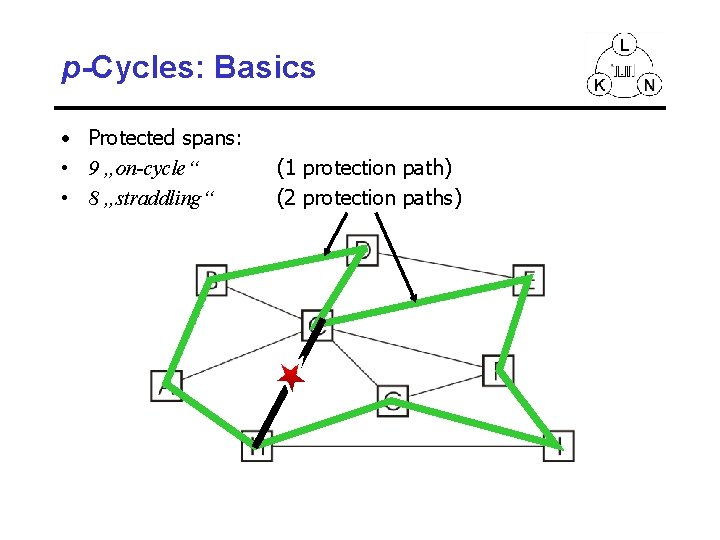
p-Cycles: Basics • Protected spans: • 9 „on-cycle“ • 8 „straddling“ (1 protection path) (2 protection paths)
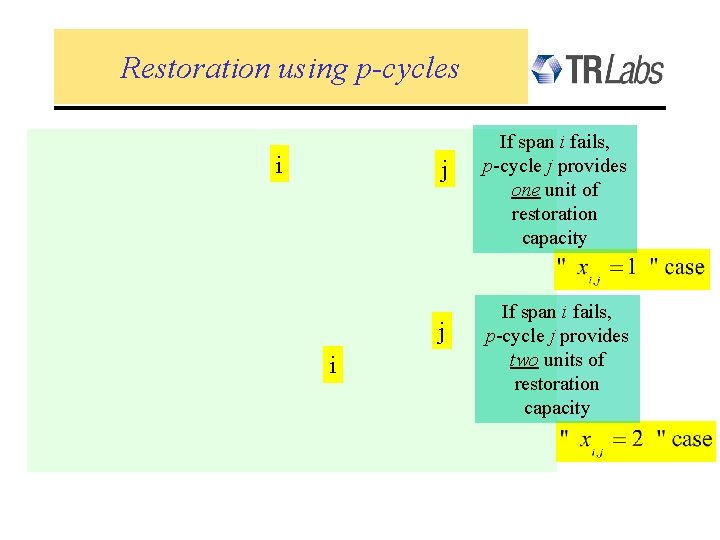
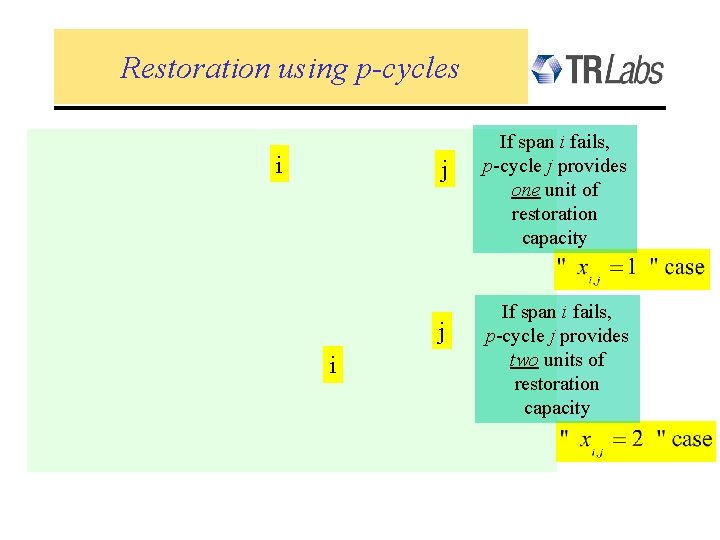
Restoration using p-cycles i j j i If span i fails, p-cycle j provides one unit of restoration capacity If span i fails, p-cycle j provides two units of restoration capacity
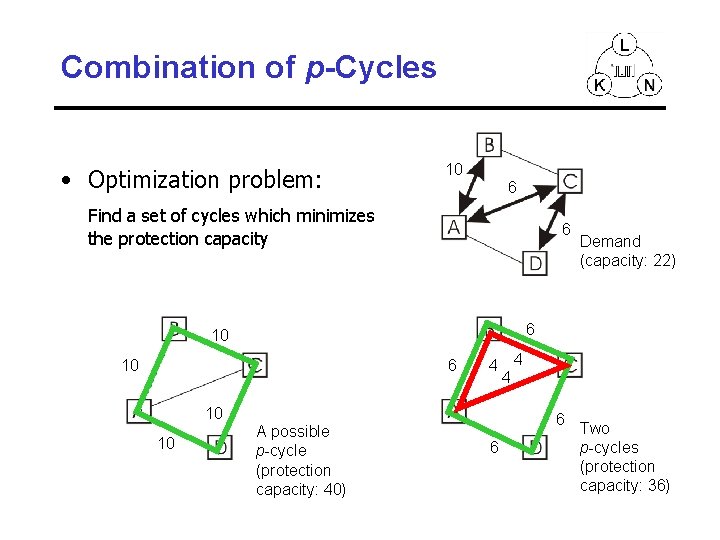
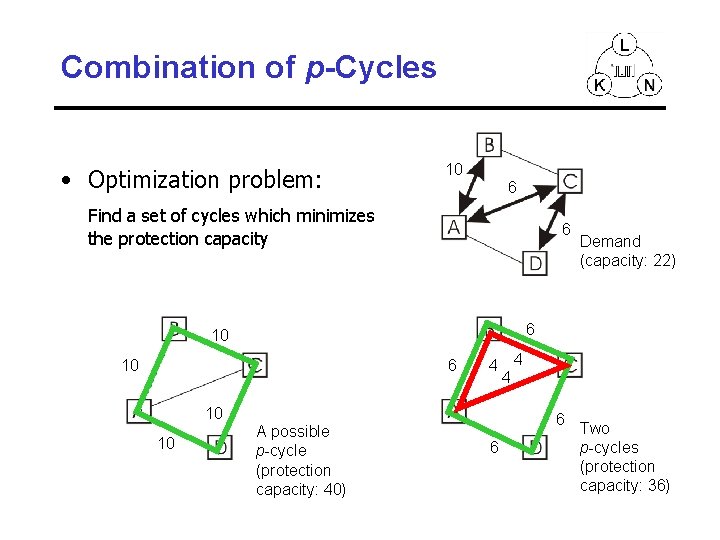
Combination of p-Cycles • Optimization problem: 10 6 Find a set of cycles which minimizes the protection capacity 6 6 10 10 6 4 10 10 Demand (capacity: 22) A possible p-cycle (protection capacity: 40) 4 4 6 6 Two p-cycles (protection capacity: 36)
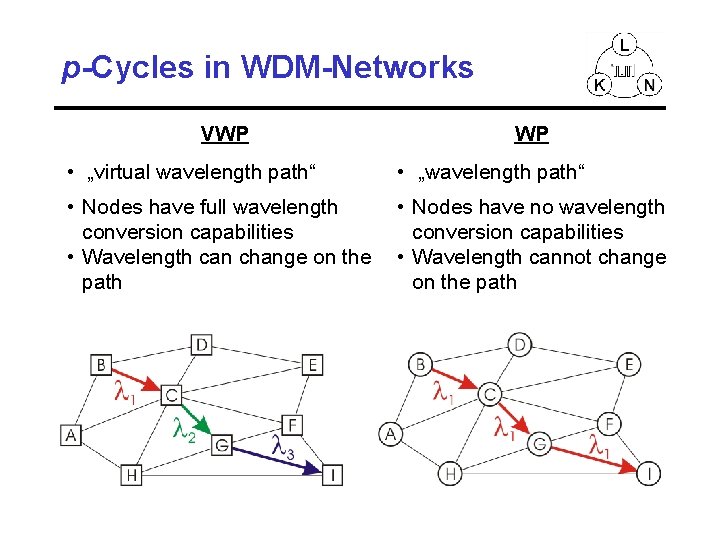
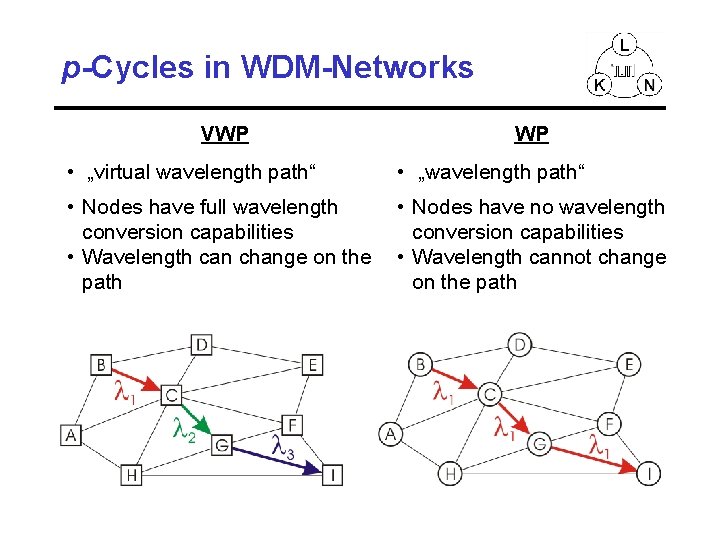
p-Cycles in WDM-Networks VWP • „virtual wavelength path“ WP • „wavelength path“ • Nodes have full wavelength • Nodes have no wavelength conversion capabilities • Wavelength can change on the • Wavelength cannot change path on the path
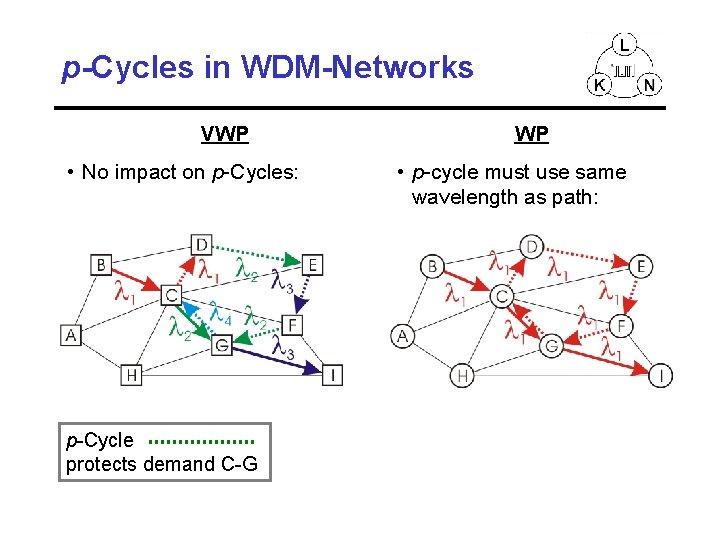
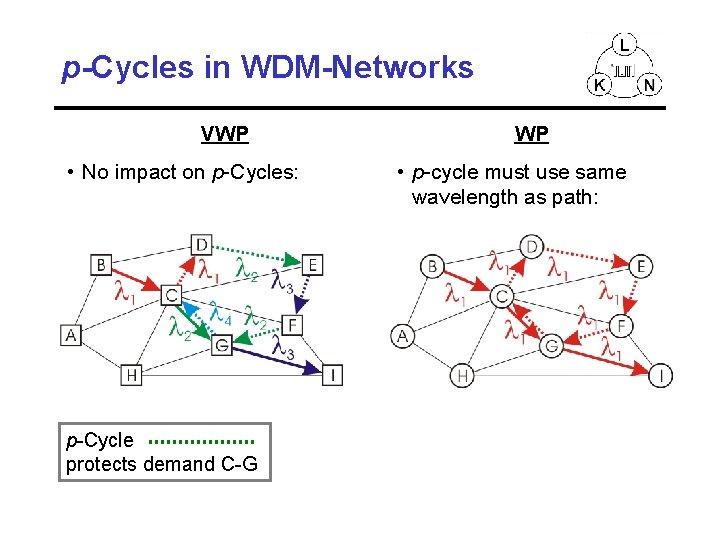
p-Cycles in WDM-Networks VWP • No impact on p-Cycles: p-Cycle protects demand C-G WP • p-cycle must use same wavelength as path:
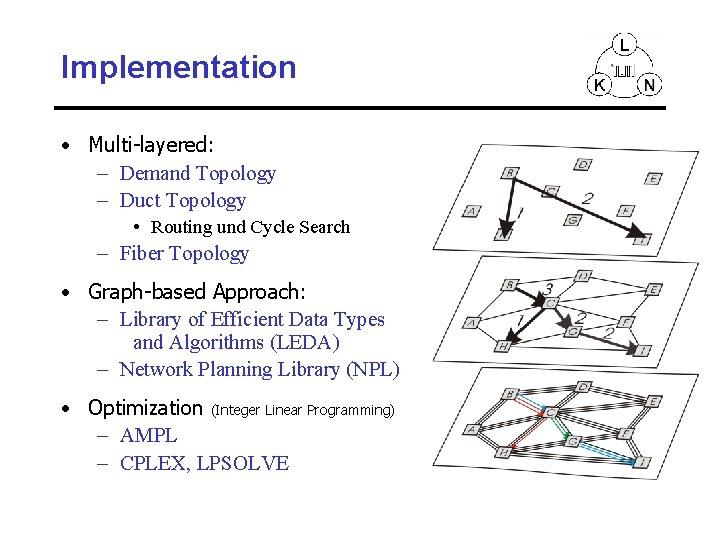
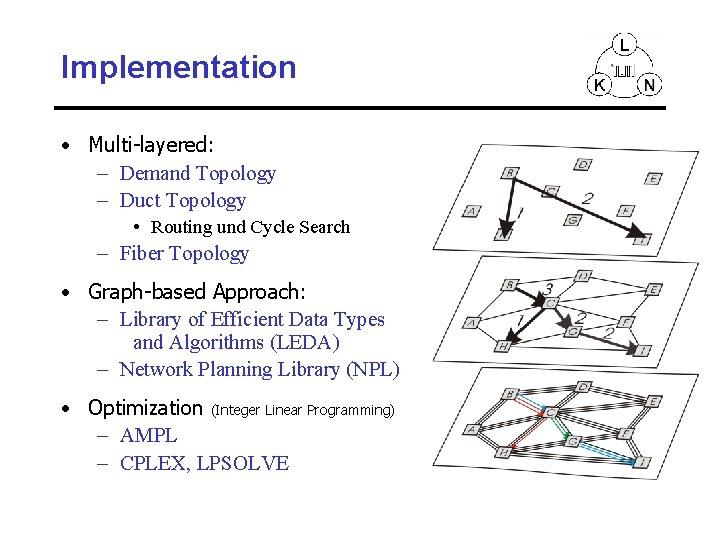
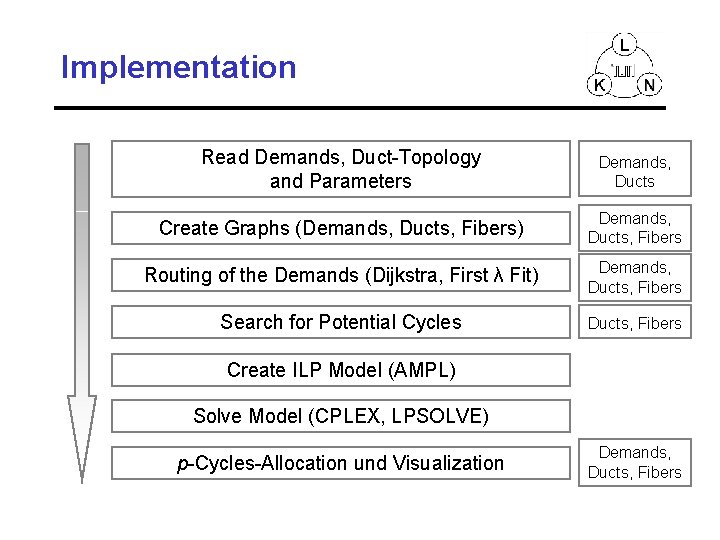
Implementation • Multi-layered: – Demand Topology – Duct Topology • Routing und Cycle Search – Fiber Topology • Graph-based Approach: – Library of Efficient Data Types and Algorithms (LEDA) – Network Planning Library (NPL) • Optimization (Integer Linear Programming) – AMPL – CPLEX, LPSOLVE
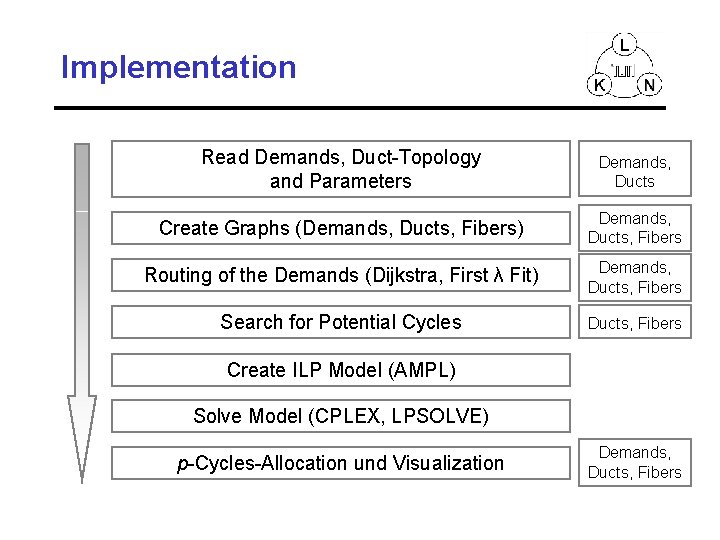
Implementation Read Demands, Duct-Topology and Parameters Demands, Ducts Create Graphs (Demands, Ducts, Fibers) Demands, Ducts, Fibers Routing of the Demands (Dijkstra, First λ Fit) Demands, Ducts, Fibers Search for Potential Cycles Ducts, Fibers Create ILP Model (AMPL) Solve Model (CPLEX, LPSOLVE) p-Cycles-Allocation und Visualization Demands, Ducts, Fibers
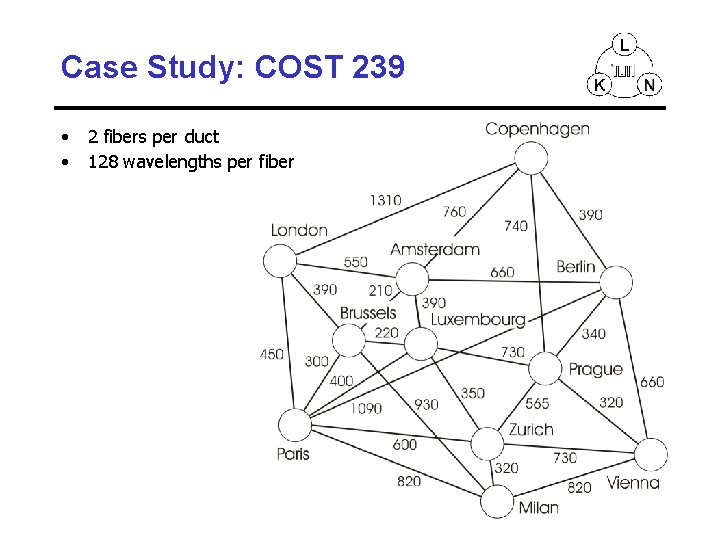
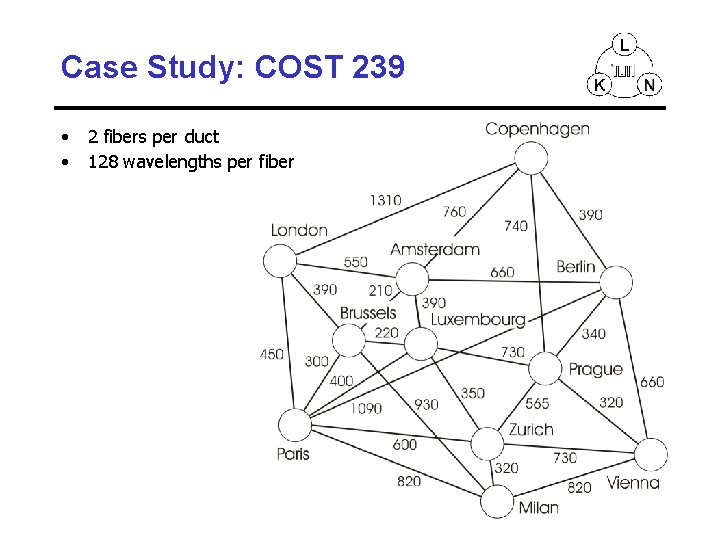
Case Study: COST 239 • • 2 fibers per duct 128 wavelengths per fiber
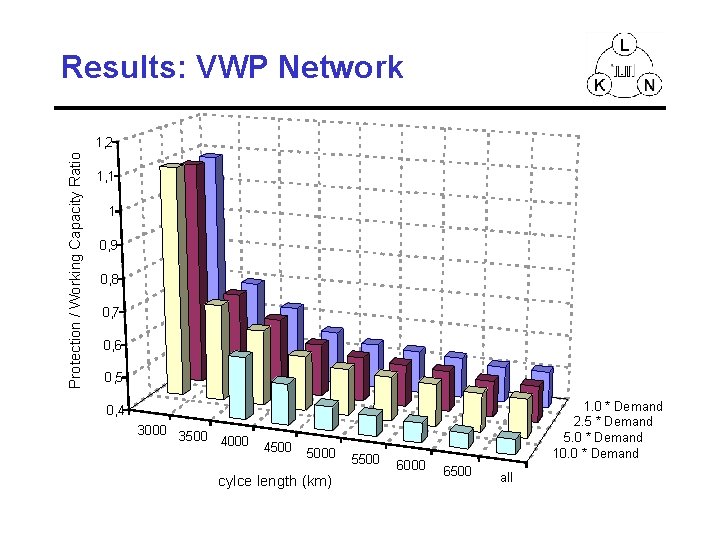
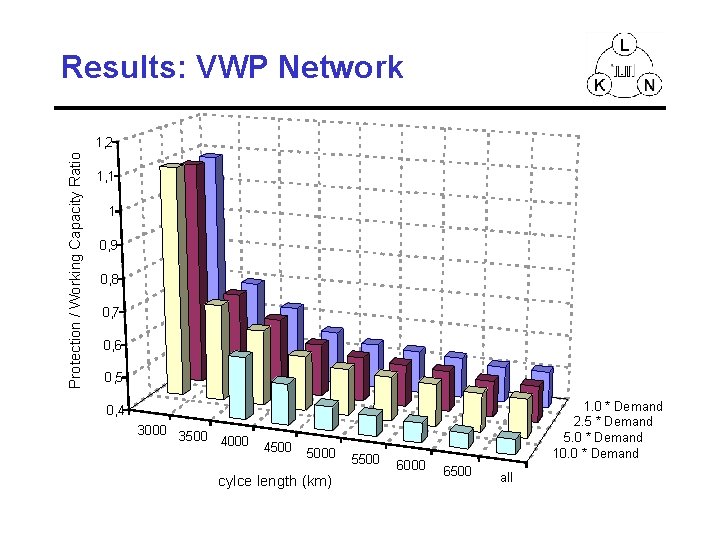
Results: VWP Network Protection / Working Capacity Ratio 1, 2 1, 1 1 0, 9 0, 8 0, 7 0, 6 0, 5 1. 0 * Demand 2. 5 * Demand 5. 0 * Demand 10. 0 * Demand 0, 4 3000 3500 4000 4500 5000 cylce length (km) 5500 6000 6500 all
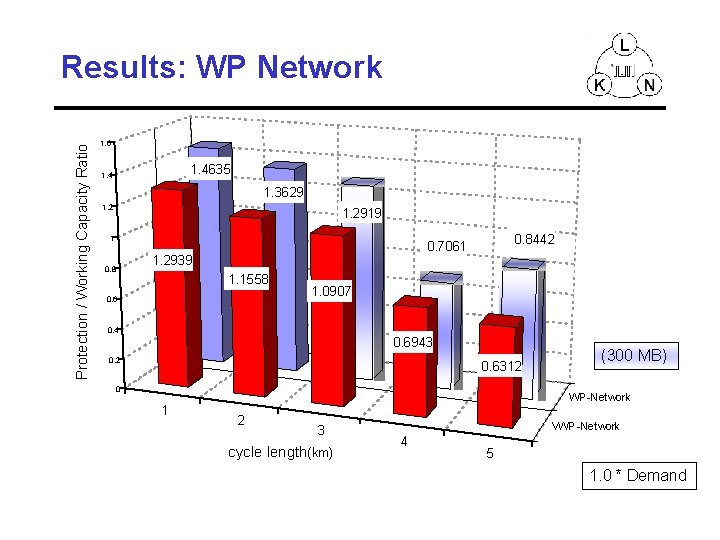
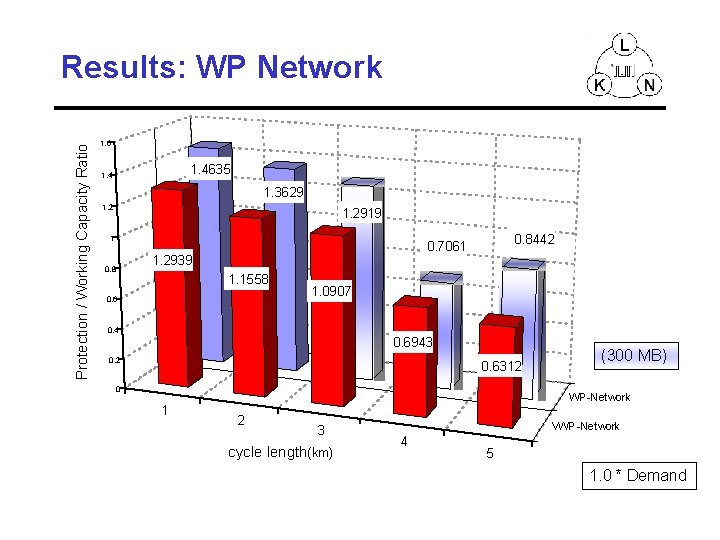
Protection / Working Capacity Ratio Results: WP Network 1. 6 1. 4635 1. 4 1. 3629 1. 2919 1 1. 2939 0. 8442 0. 7061 1. 1558 0. 6 1. 0907 0. 4 0. 6943 0. 2 0. 6312 0 1 (300 MB) WP-Network 2 3 cycle length(km) VWP-Network 4 5 1. 0 * Demand
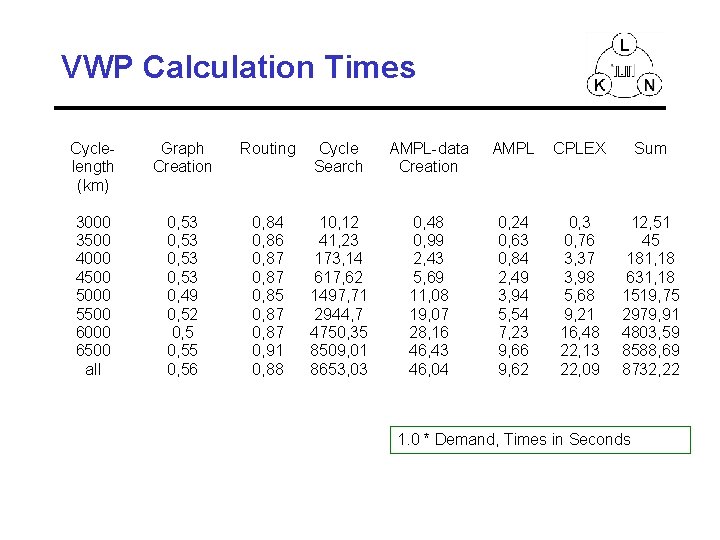
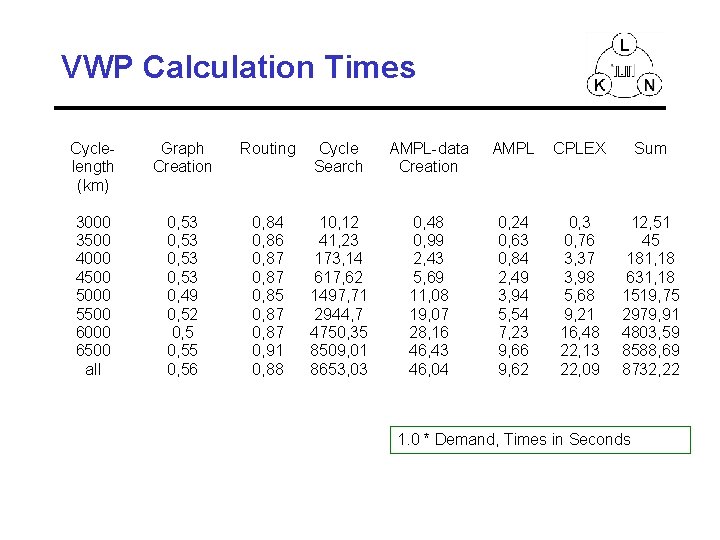
VWP Calculation Times Cyclelength (km) Graph Creation Routing Cycle Search AMPL-data Creation AMPL CPLEX Sum 3000 3500 4000 4500 5000 5500 6000 6500 all 0, 53 0, 49 0, 52 0, 55 0, 56 0, 84 0, 86 0, 87 0, 85 0, 87 0, 91 0, 88 10, 12 41, 23 173, 14 617, 62 1497, 71 2944, 7 4750, 35 8509, 01 8653, 03 0, 48 0, 99 2, 43 5, 69 11, 08 19, 07 28, 16 46, 43 46, 04 0, 24 0, 63 0, 84 2, 49 3, 94 5, 54 7, 23 9, 66 9, 62 0, 3 0, 76 3, 37 3, 98 5, 68 9, 21 16, 48 22, 13 22, 09 12, 51 45 181, 18 631, 18 1519, 75 2979, 91 4803, 59 8588, 69 8732, 22 1. 0 * Demand, Times in Seconds
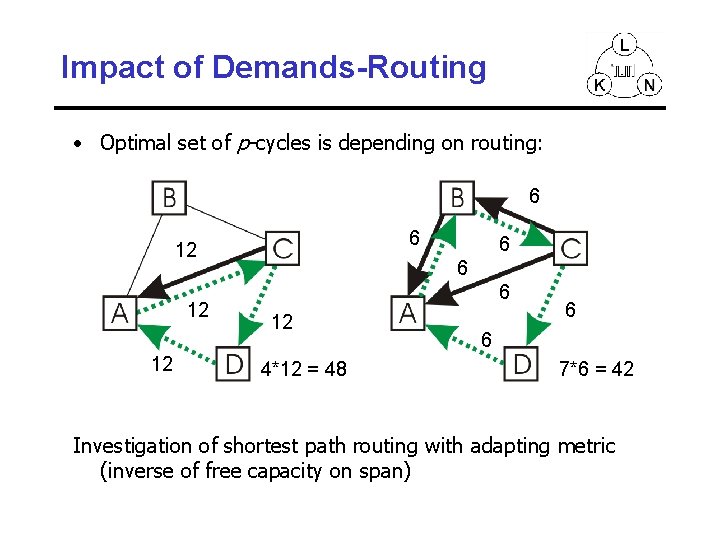
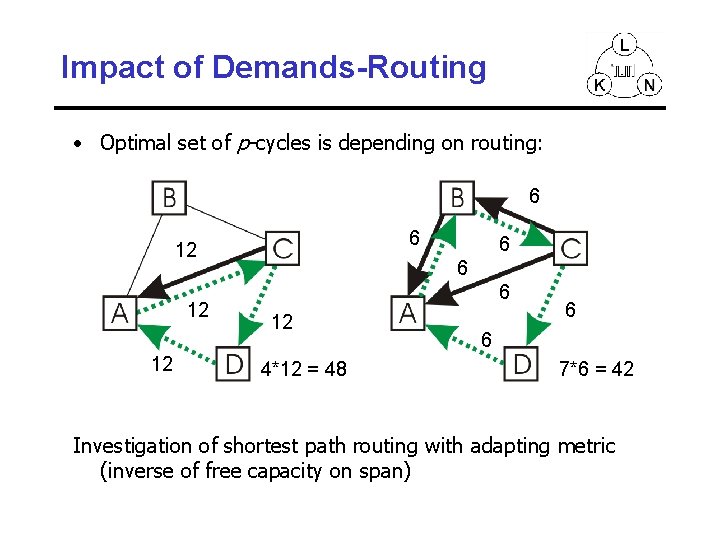
Impact of Demands-Routing • Optimal set of p-cycles is depending on routing: 6 6 12 12 12 6 6 6 12 4*12 = 48 6 6 7*6 = 42 Investigation of shortest path routing with adapting metric (inverse of free capacity on span)
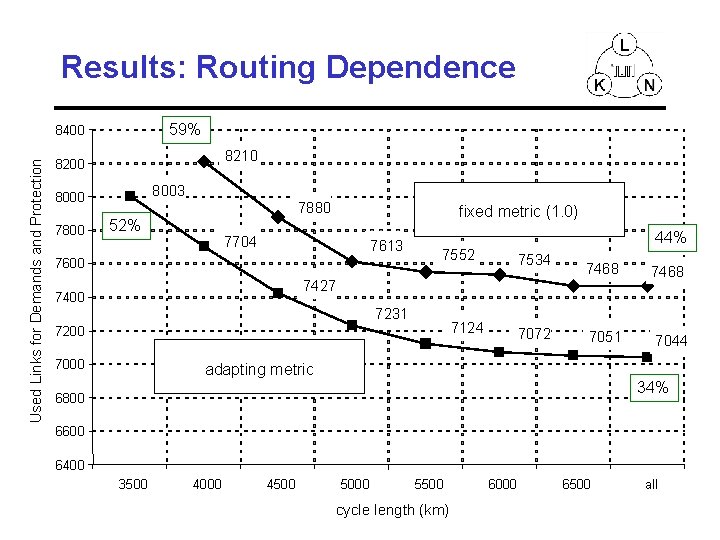
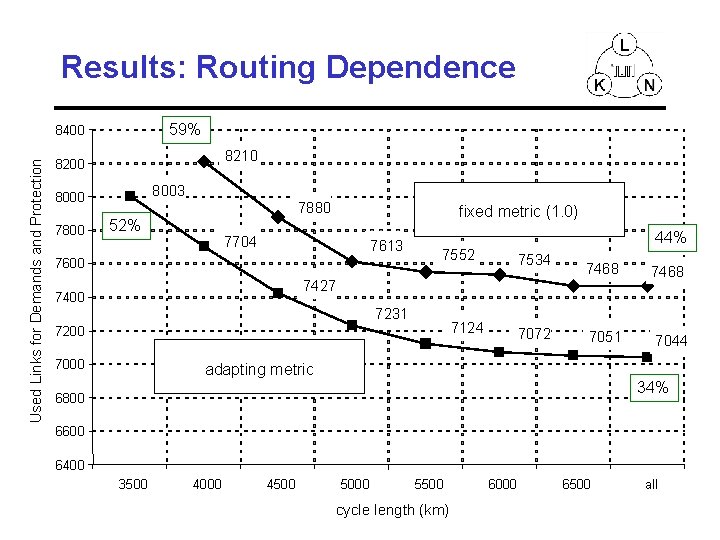
Results: Routing Dependence 59% Used Links for Demands and Protection 8400 8210 8200 8003 8000 7880 52% fixed metric (1. 0) 7704 7613 7600 44% 7552 7534 7468 7051 7044 7427 7400 7231 7124 7200 7072 adapting metric 34% 6800 6600 6400 3500 4000 4500 5000 5500 cycle length (km) 6000 6500 all
Optimal Spare capacity design Typical Results • “Excess Sparing” = Spare Capacity compared to Optimal Span. Restorable Mesh i. e. , “mesh-like” capacity
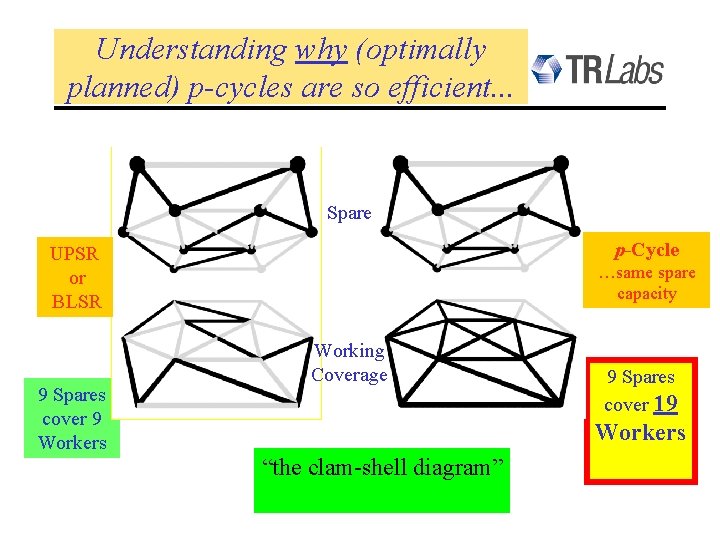
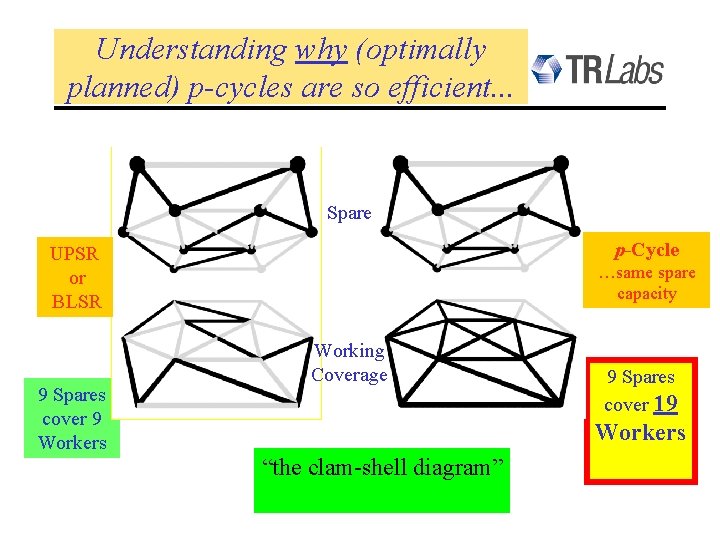
Understanding why (optimally planned) p-cycles are so efficient. . . Spare p-Cycle UPSR or BLSR 9 Spares cover 9 Workers …same spare capacity Working Coverage 9 Spares cover 19 Workers “the clam-shell diagram”
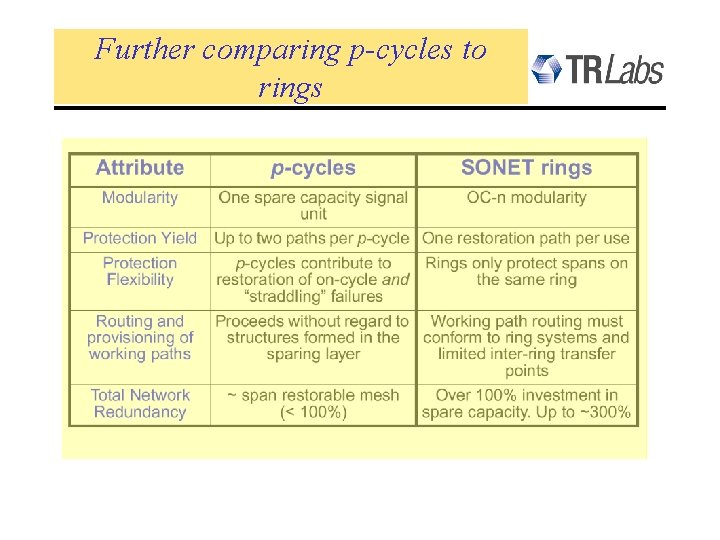
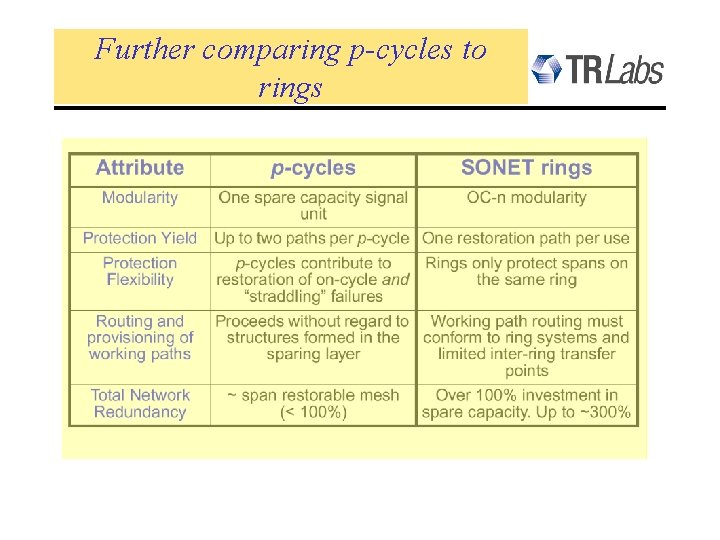
Further comparing p-cycles to rings
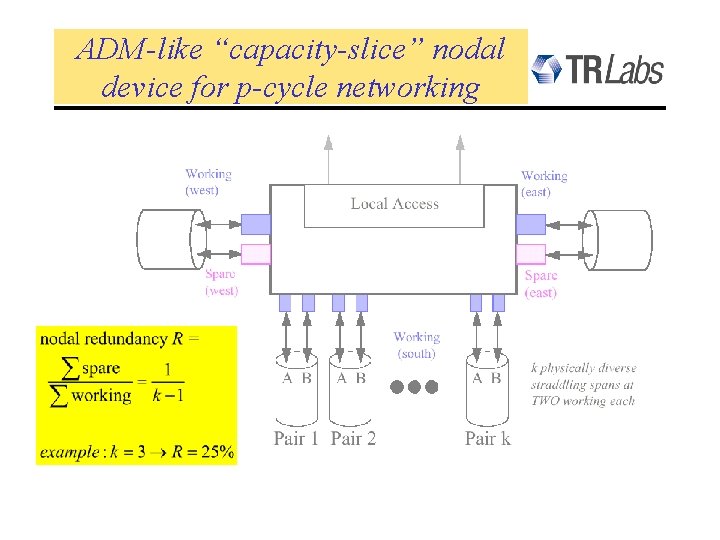
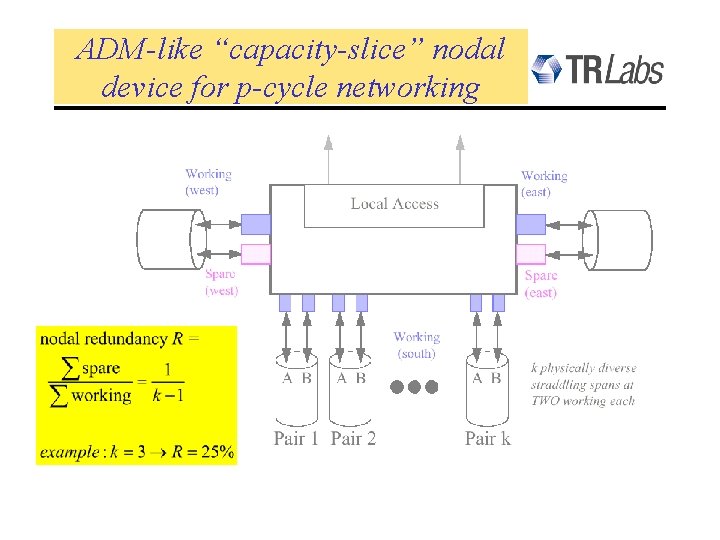
ADM-like “capacity-slice” nodal device for p-cycle networking
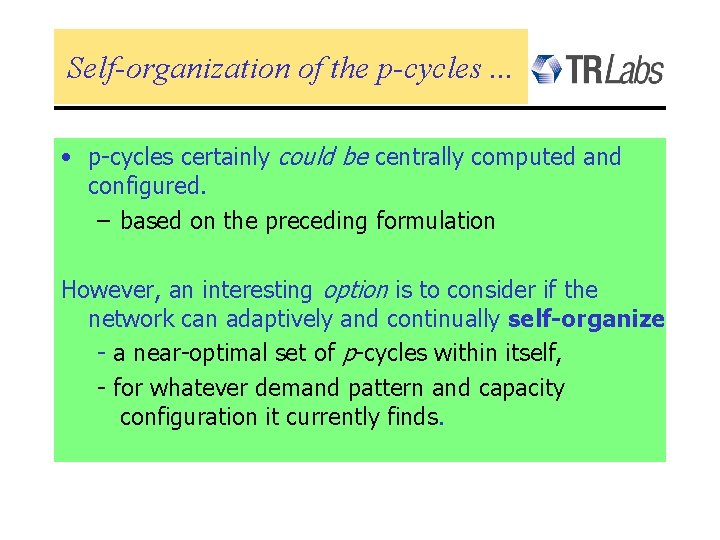
Self-organization of the p-cycles. . . • p-cycles certainly could be centrally computed and configured. – based on the preceding formulation However, an interesting option is to consider if the network can adaptively and continually self-organize - a near-optimal set of p-cycles within itself, - for whatever demand pattern and capacity configuration it currently finds.
Self-organization of the p-cycles • Based on an extension / adaptation of SHN™ distributed mesh restoration algorithm – “DCPC” = distributed cycle pre-configuration protocol • Operates continually in background – Non-real time phase self-organizes p-cycles – Real time phase is essentially BLSR switching – p-cycles in continual self-test while in “storage” • Centralized “oversight” but not low-level control – Method is autonomous, adaptive • Networks actual state on the ground is the database
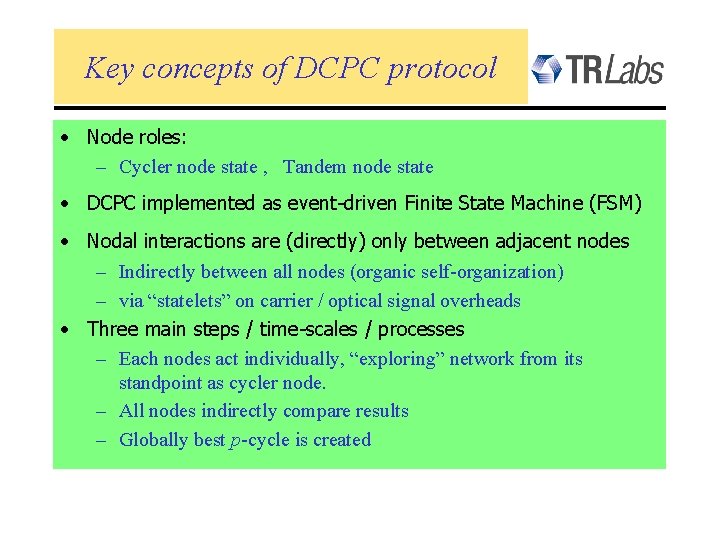
Key concepts of DCPC protocol • Node roles: – Cycler node state , Tandem node state • DCPC implemented as event-driven Finite State Machine (FSM) • Nodal interactions are (directly) only between adjacent nodes – Indirectly between all nodes (organic self-organization) – via “statelets” on carrier / optical signal overheads • Three main steps / time-scales / processes – Each nodes act individually, “exploring” network from its standpoint as cycler node. – All nodes indirectly compare results – Globally best p-cycle is created
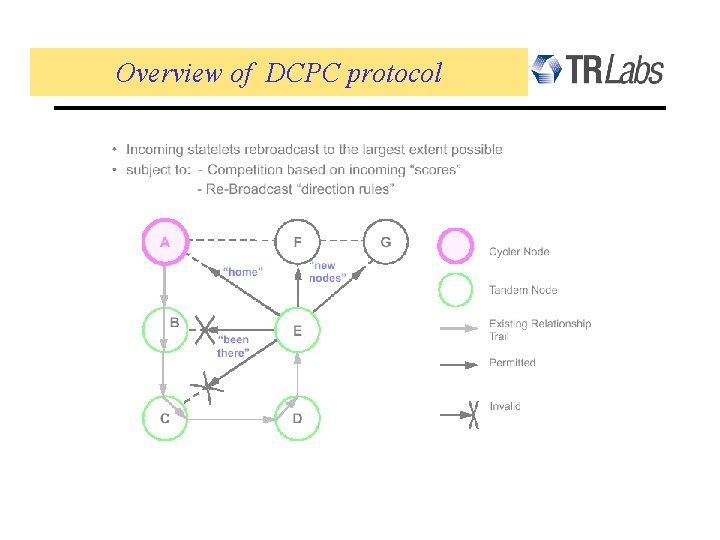
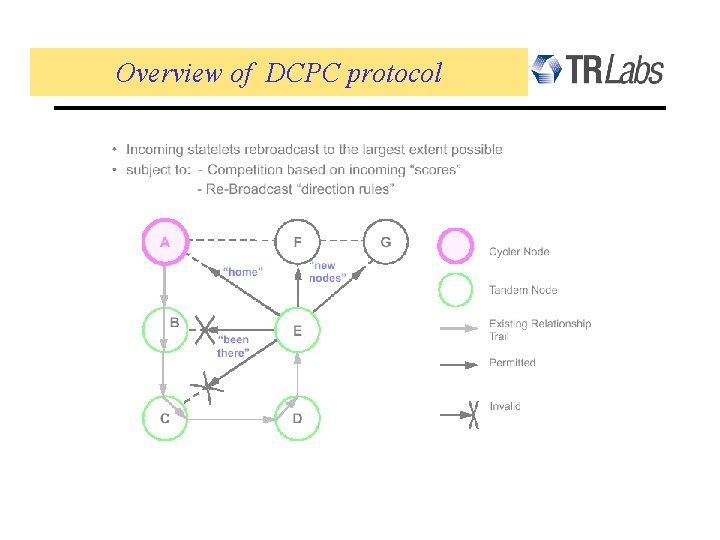
Overview of DCPC protocol
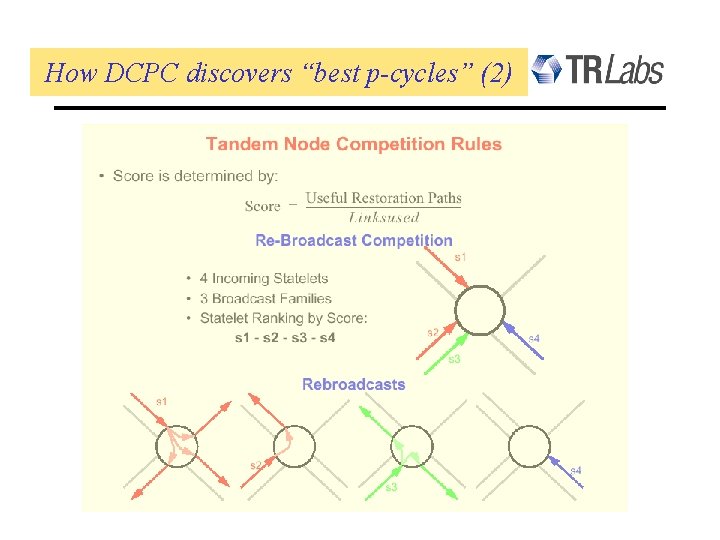
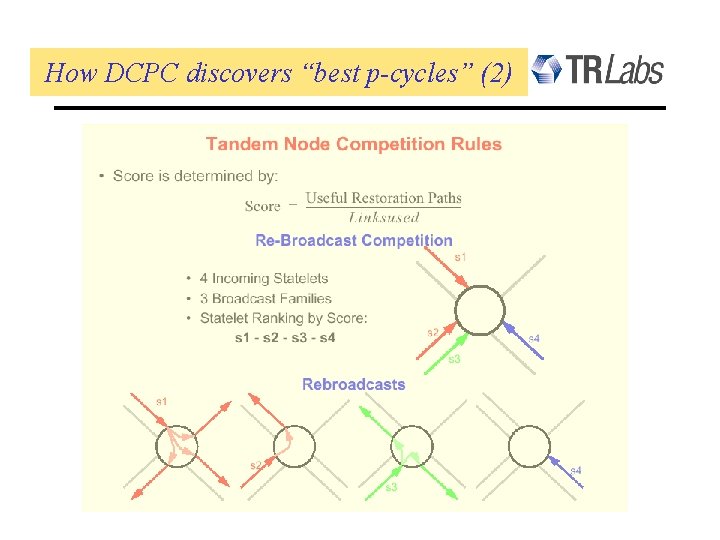
How DCPC discovers “best p-cycles” (2)
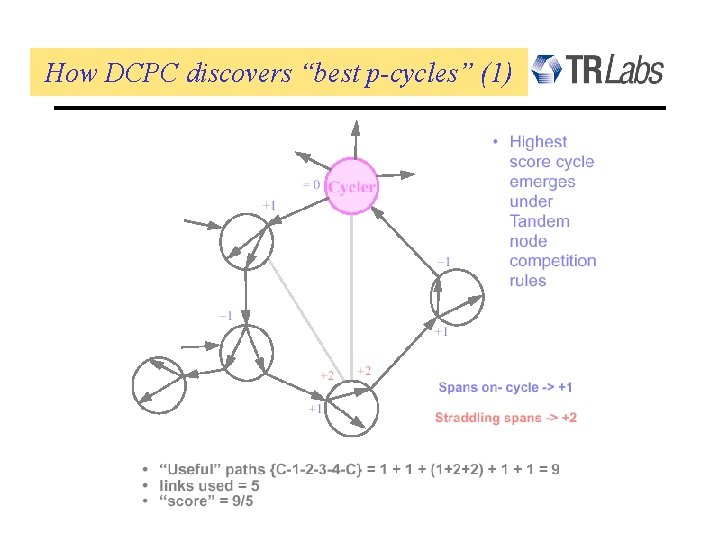
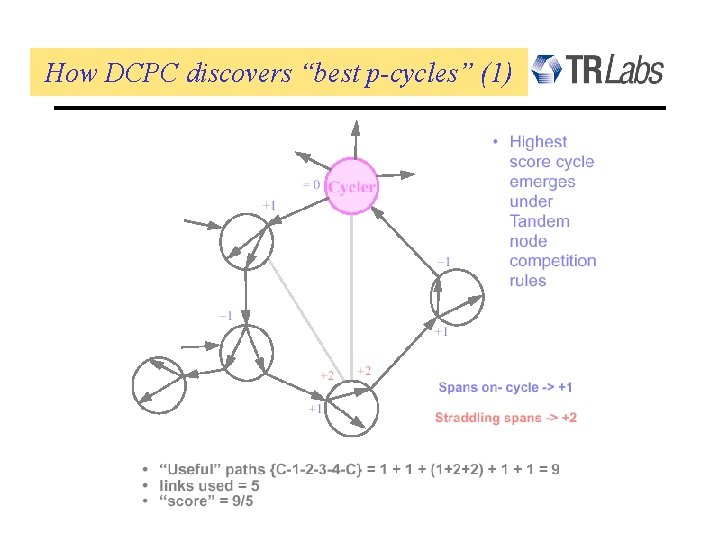
How DCPC discovers “best p-cycles” (1)
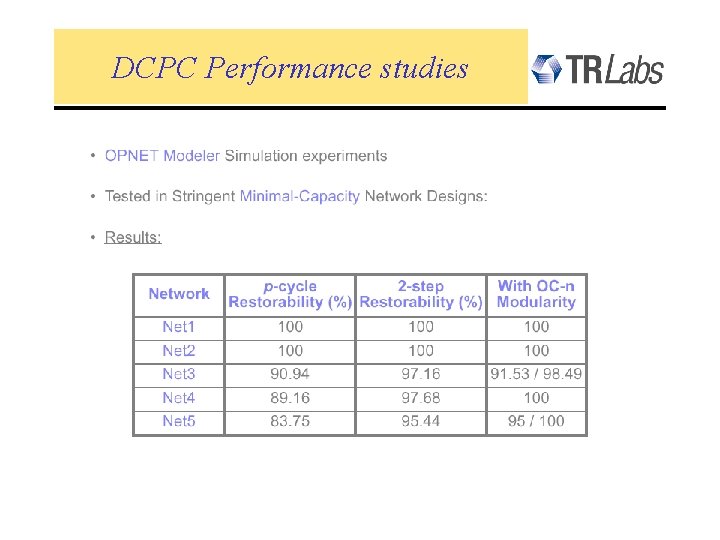
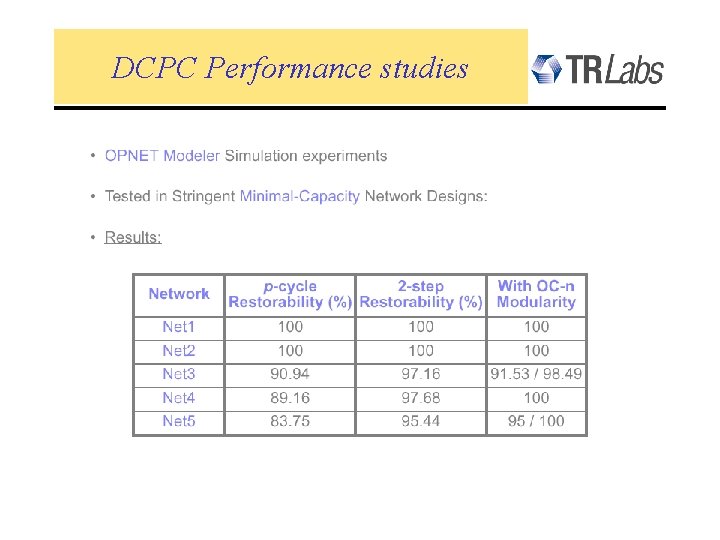
DCPC Performance studies
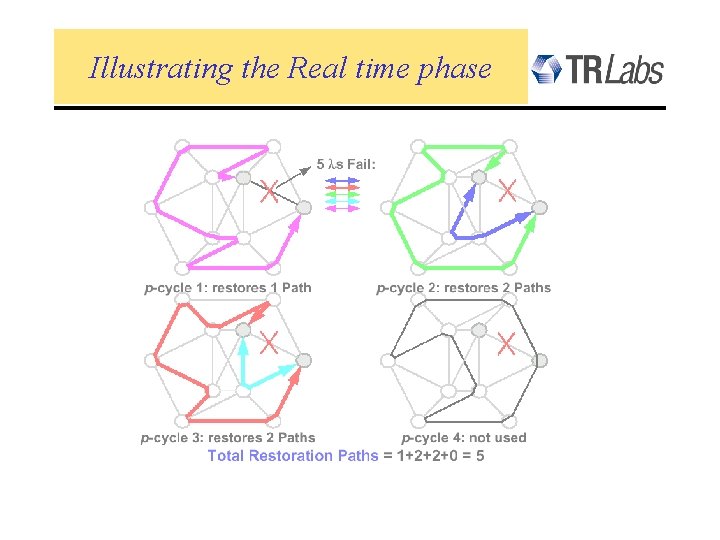
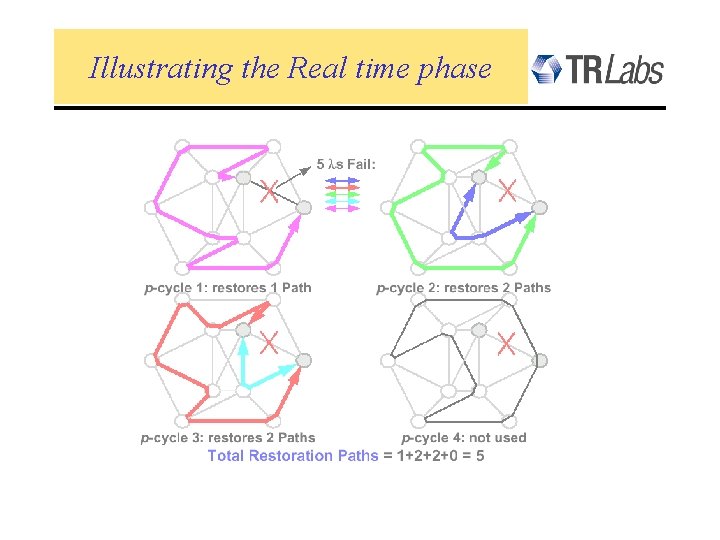
Illustrating the Real time phase
Adapting p-cycles to the IP-layer …
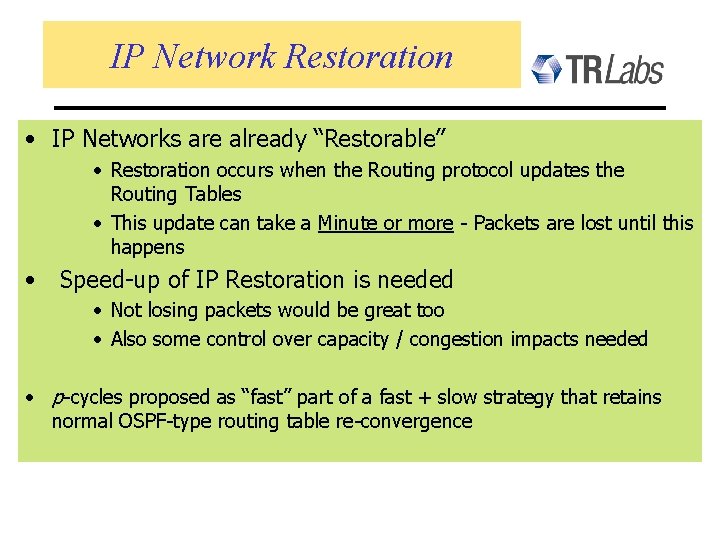
IP Network Restoration • IP Networks are already “Restorable” • Restoration occurs when the Routing protocol updates the Routing Tables • This update can take a Minute or more - Packets are lost until this happens • Speed-up of IP Restoration is needed • Not losing packets would be great too • Also some control over capacity / congestion impacts needed • p-cycles proposed as “fast” part of a fast + slow strategy that retains normal OSPF-type routing table re-convergence
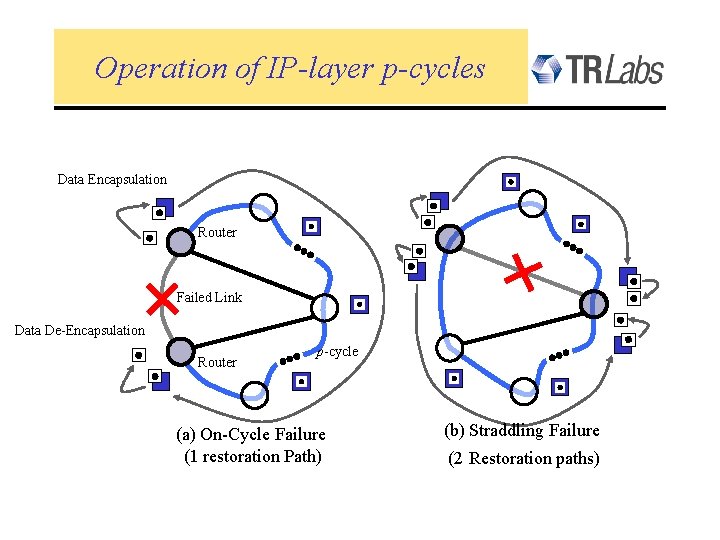
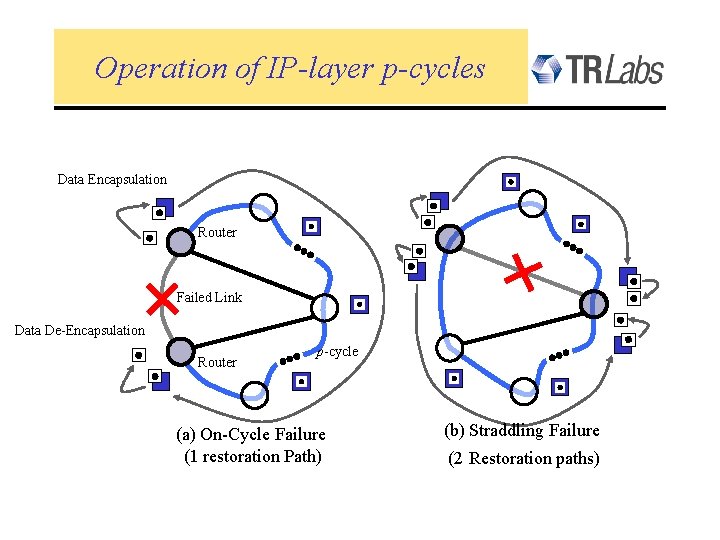
Operation of IP-layer p-cycles Data Encapsulation Router Failed Link Data De-Encapsulation Router p-cycle (a) On-Cycle Failure (1 restoration Path) (b) Straddling Failure (2 Restoration paths)
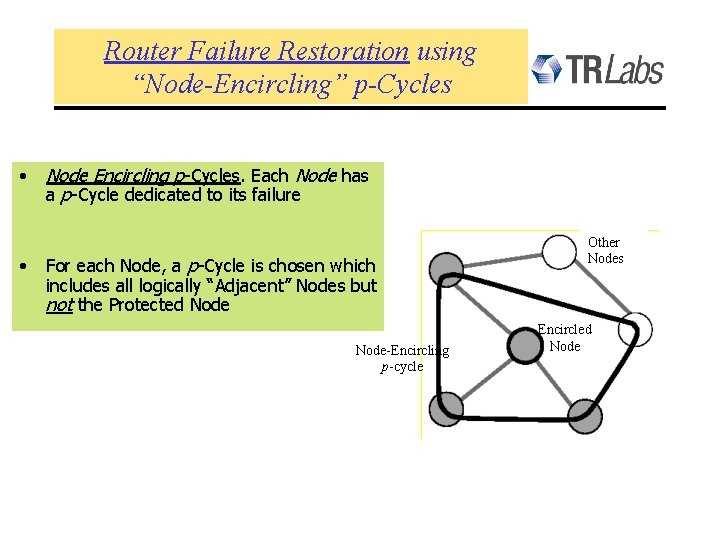
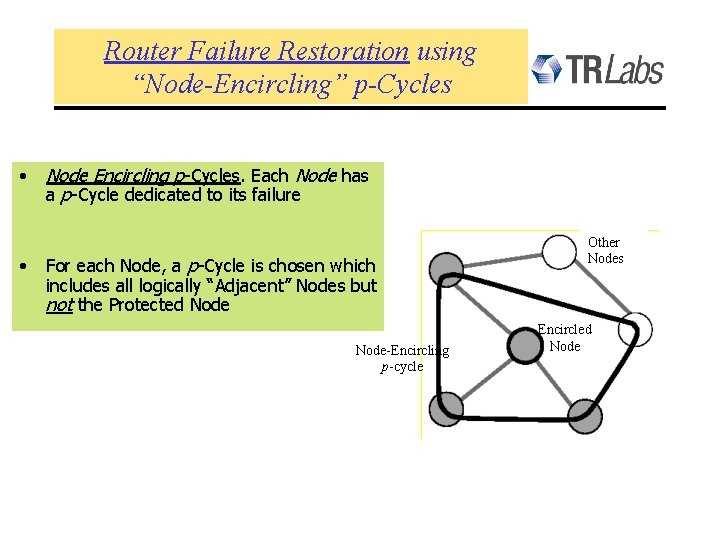
Router Failure Restoration using “Node-Encircling” p-Cycles • • Node Encircling p-Cycles. Each Node has a p-Cycle dedicated to its failure For each Node, a p-Cycle is chosen which includes all logically “Adjacent” Nodes but not the Protected Node-Encircling p-cycle Other Nodes Encircled Node
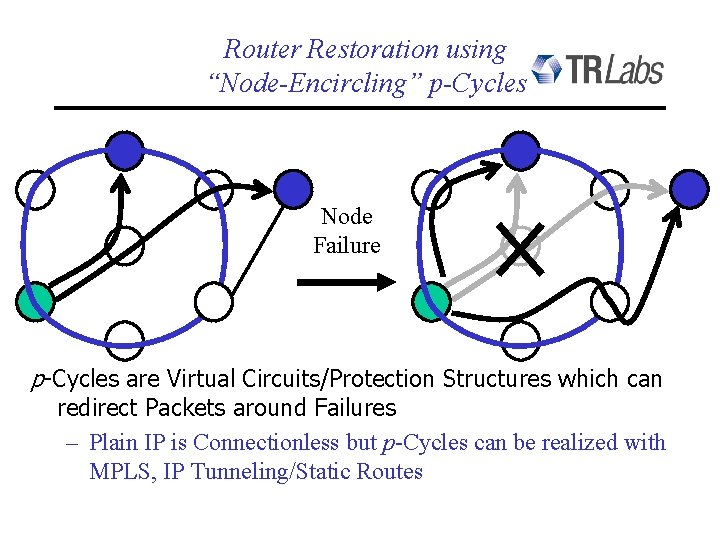
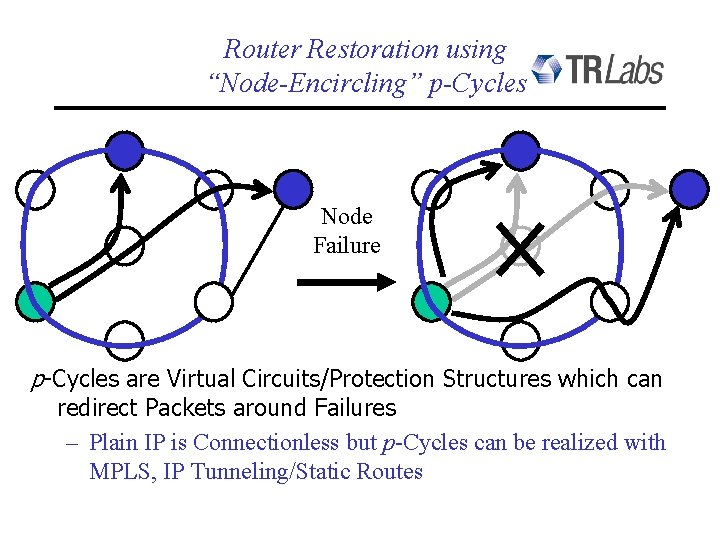
Router Restoration using “Node-Encircling” p-Cycles Node Failure p-Cycles are Virtual Circuits/Protection Structures which can redirect Packets around Failures – Plain IP is Connectionless but p-Cycles can be realized with MPLS, IP Tunneling/Static Routes
Concluding Comments Investigation on WDM-networks: • p-cycles are suitable and efficient for converting and non-converting WDM-networks • Short off-line calculation times for fully converting networks • Results are depending on demands routing • Only some improvement by non-simple cycles Outlook: • Partial wavelength conversion • Multiple failures
Concluding Comments • p-cycles offer new approaches to both WDM and IP-layer transport – “ mesh-like efficiency with ring-like speed ” • Capacity-planning theory – for 100% span restoration in WDM / Sonet with mesh sparing – for controlled worst-case over-subscription in IP-layer • “Node-encircling” p-cycles – fast integrated restoration against either router or link-failures • Nortel has implemented span-restoration via IP p-cycles – ~ 10 msec restoration time, no packet loss in their experiments • Ongoing studies: • Integrated planning of composite node / link restoration p-cycles • Availability analysis of p-cycles
![References on pCycles 1 W D Grover D Stamatelakis CycleOriented Distributed Preconfiguration Ringlike References on p-Cycles • [1] W. D. Grover, D. Stamatelakis, "Cycle-Oriented Distributed Preconfiguration: Ring-like](https://slidetodoc.com/presentation_image/2b6a1a4bcfd159ff605e263ac0e05878/image-39.jpg)
References on p-Cycles • [1] W. D. Grover, D. Stamatelakis, "Cycle-Oriented Distributed Preconfiguration: Ring-like Speed with Mesh-like Capacity for Self-planning Network Restoration, " Proc. IEEE International Conf. Commun. (ICC'98), Atlanta, June 8 -11, 1998. pp. 537 -543. • [2] D. Stamatelakis, W. D. Grover, "Theoretical Underpinnings for the Efficiency of Restorable Networks Using Pre-configured Cycles ("p-cycles")", to appear in IEEE Transactions on Communications, accepted December 1999 (contact TRLabs for an advance copy) • [3] W. D. Grover, D Stamatelakis, "Bridging the ring-mesh dichotomy with p-cycles", Proc. Design of Reliable Communication Networks (DRCN 2000), Technical University of Munich, April 2000, pp. 92 -104. • [4] D. Stamatelakis, W. D. Grover, "Rapid Restoration of Internet Protocol Networks using Pre-configured Protection Cycles, " Proc. 3 rd Can. Conf. On Broadband Research (CCBR'99), Nov. 7, 9, Ottawa, 1999 • [5] D. A. Schupke, C. G. Gruber, A. Autenrieth, “Optimal Configuration of p-Cycles in WDM Networks, ” submitted to ICC 2002