Optimizing Password Composition Policies Jeremiah Blocki CMU Saranga
Optimizing Password Composition Policies Jeremiah Blocki (CMU) Saranga Komanduri (CMU) Ariel Procaccia (CMU) Or Sheffet (CMU) EC 2013

1
Valuable Resources Protected by Weak Passwords 12345 password 12345 Guess Limit: k-strikes policy 2
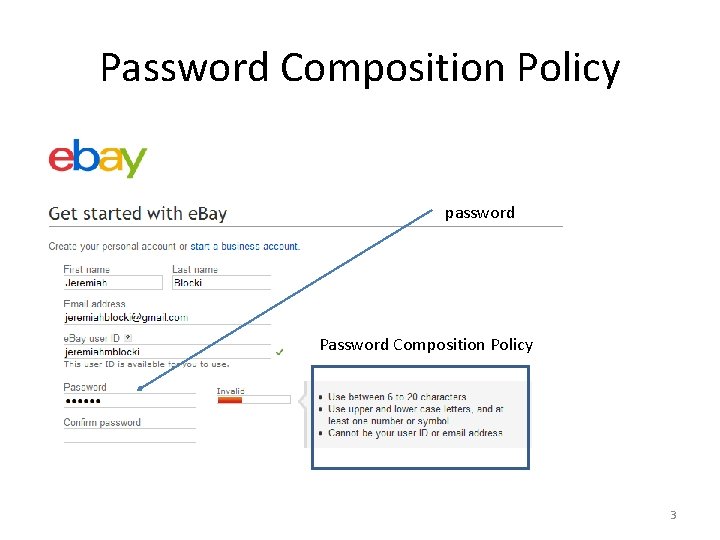
Password Composition Policy password Password Composition Policy 3
How Do Users Respond? Password 1 4
Predictable Responses 1. password 2. 123456 3. 12345678 4. abc 123 5. qwerty 6. monkey 7. letmein 8. dragon 9. 111111 …. 25. password 1 5
![Previous Work • Initial password composition policies designed without empirical data [BDP, 2006]. • Previous Work • Initial password composition policies designed without empirical data [BDP, 2006]. •](http://slidetodoc.com/presentation_image_h2/7441c6d3ffacbf7346ec6f3fda3cc3e8/image-7.jpg)
Previous Work • Initial password composition policies designed without empirical data [BDP, 2006]. • User’s respond to password composition policies in predictable ways [KSKMBCCE, 2011] • Trivial password choices vary widely across contexts [BX, 2012]. • No theoretical models of password composition policies. 6
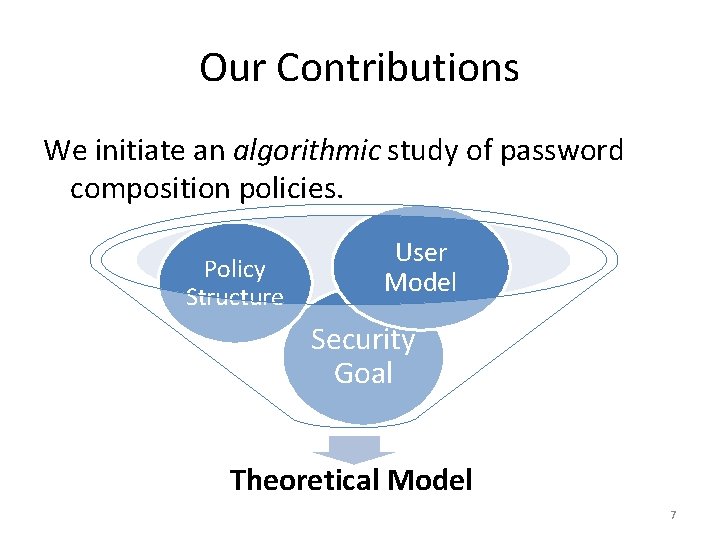
Our Contributions We initiate an algorithmic study of password composition policies. Policy Structure User Model Security Goal Theoretical Model 7
Outline • • • Goal User Model Policy Structure Algorithms and Reductions Experiments 8
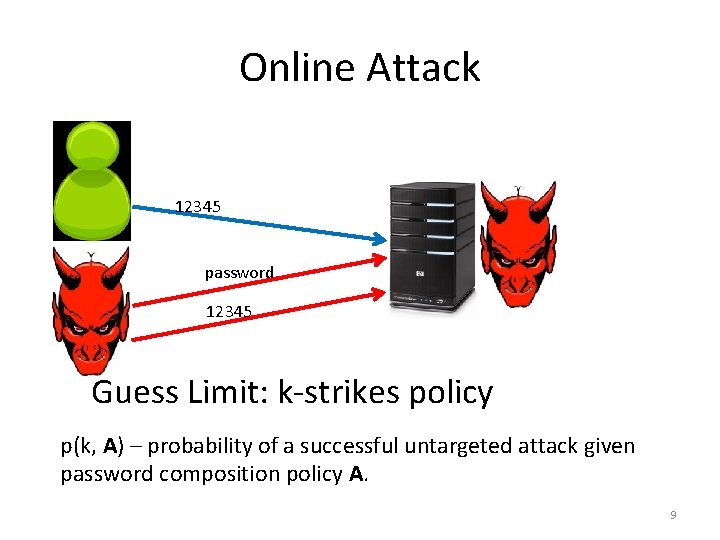
Online Attack 12345 password 12345 Guess Limit: k-strikes policy p(k, A) – probability of a successful untargeted attack given password composition policy A. 9
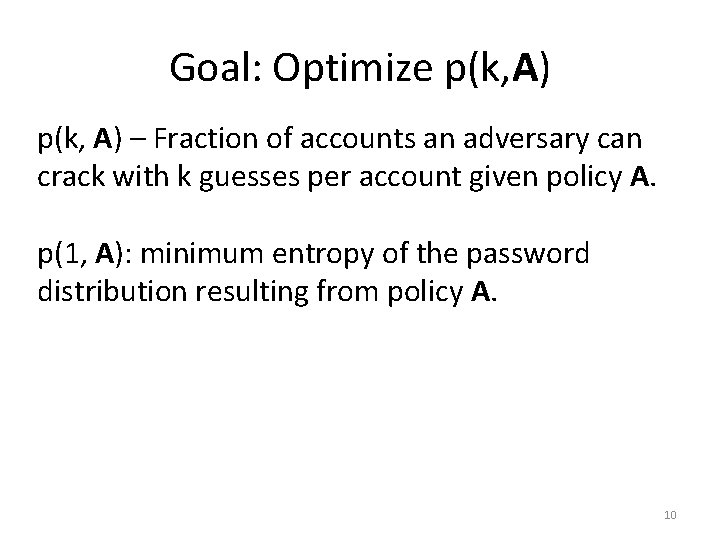
Goal: Optimize p(k, A) – Fraction of accounts an adversary can crack with k guesses per account given policy A. p(1, A): minimum entropy of the password distribution resulting from policy A. 10
Outline • • • Goal User Model Policy Structure Algorithms and Reductions Experiments 11
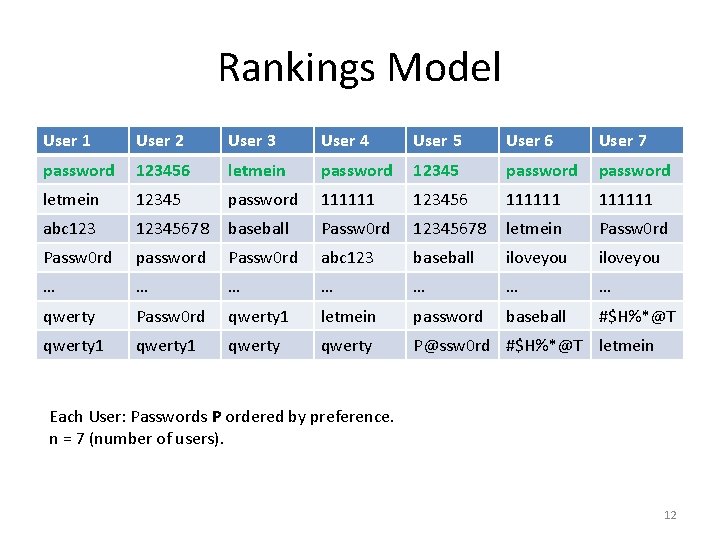
Rankings Model User 1 User 2 User 3 User 4 User 5 User 6 User 7 password 123456 letmein password 12345 password letmein 12345 password 111111 123456 111111 abc 12345678 baseball Passw 0 rd 12345678 letmein Passw 0 rd password Passw 0 rd abc 123 baseball iloveyou … … … … qwerty Passw 0 rd qwerty 1 letmein password baseball #$H%*@T qwerty 1 qwerty P@ssw 0 rd #$H%*@T letmein Each User: Passwords P ordered by preference. n = 7 (number of users). 12
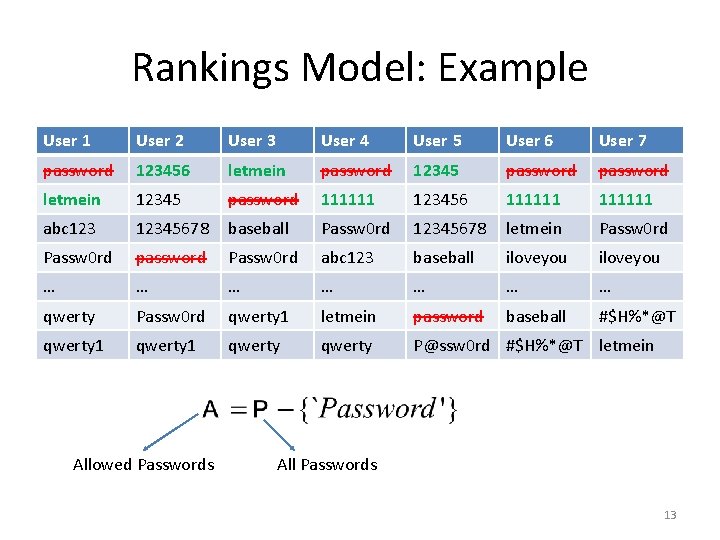
Rankings Model: Example User 1 User 2 User 3 User 4 User 5 User 6 User 7 password 123456 letmein password 12345 password letmein 12345 password 111111 123456 111111 abc 12345678 baseball Passw 0 rd 12345678 letmein Passw 0 rd password Passw 0 rd abc 123 baseball iloveyou … … … … qwerty Passw 0 rd qwerty 1 letmein password baseball #$H%*@T qwerty 1 qwerty P@ssw 0 rd #$H%*@T letmein Allowed Passwords All Passwords 13
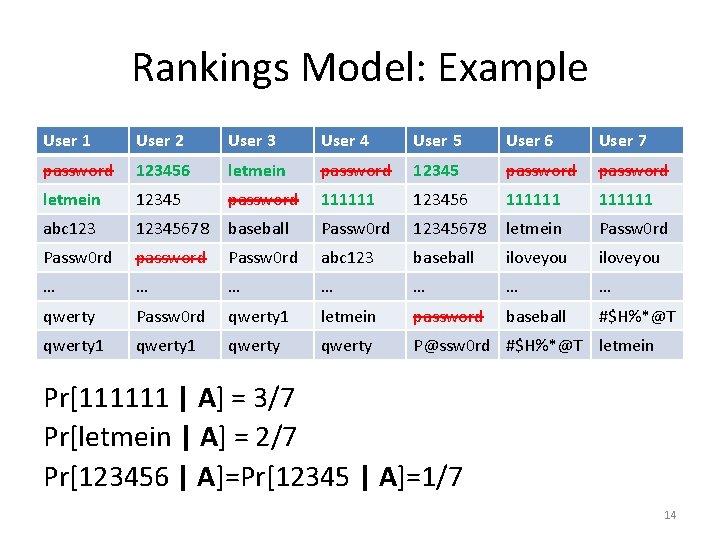
Rankings Model: Example User 1 User 2 User 3 User 4 User 5 User 6 User 7 password 123456 letmein password 12345 password letmein 12345 password 111111 123456 111111 abc 12345678 baseball Passw 0 rd 12345678 letmein Passw 0 rd password Passw 0 rd abc 123 baseball iloveyou … … … … qwerty Passw 0 rd qwerty 1 letmein password baseball #$H%*@T qwerty 1 qwerty P@ssw 0 rd #$H%*@T letmein Pr[111111 | A] = 3/7 Pr[letmein | A] = 2/7 Pr[123456 | A]=Pr[12345 | A]=1/7 14
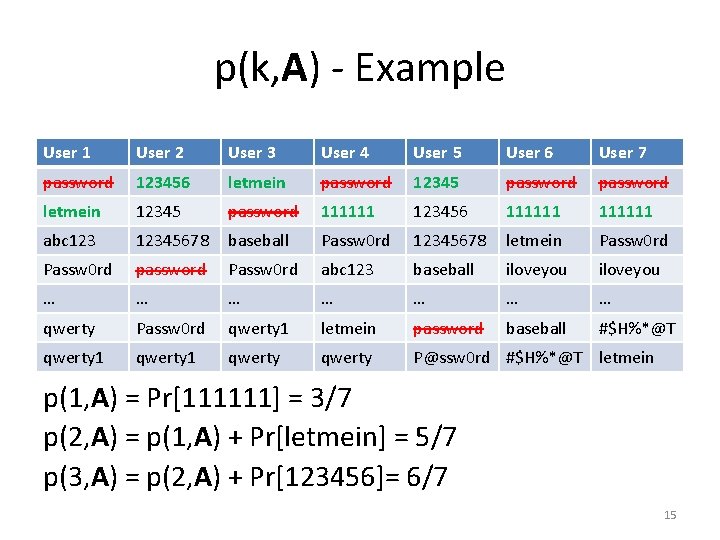
p(k, A) - Example User 1 User 2 User 3 User 4 User 5 User 6 User 7 password 123456 letmein password 12345 password letmein 12345 password 111111 123456 111111 abc 12345678 baseball Passw 0 rd 12345678 letmein Passw 0 rd password Passw 0 rd abc 123 baseball iloveyou … … … … qwerty Passw 0 rd qwerty 1 letmein password baseball #$H%*@T qwerty 1 qwerty P@ssw 0 rd #$H%*@T letmein p(1, A) = Pr[111111] = 3/7 p(2, A) = p(1, A) + Pr[letmein] = 5/7 p(3, A) = p(2, A) + Pr[123456]= 6/7 15
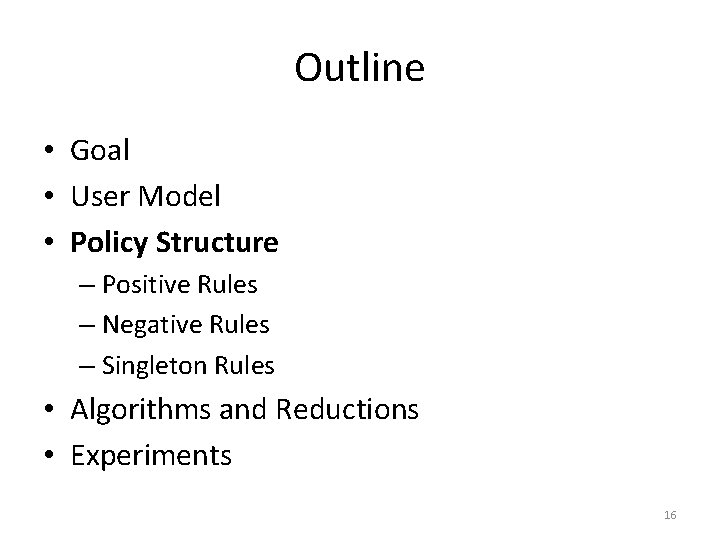
Outline • Goal • User Model • Policy Structure – Positive Rules – Negative Rules – Singleton Rules • Algorithms and Reductions • Experiments 16
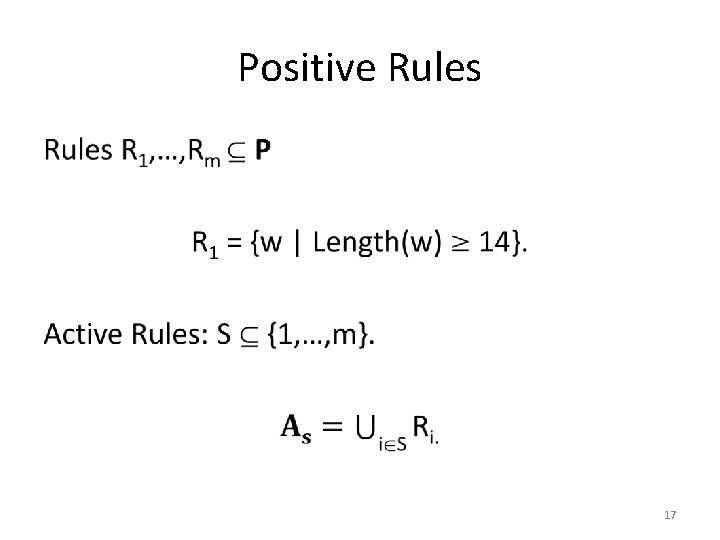
Positive Rules • 17
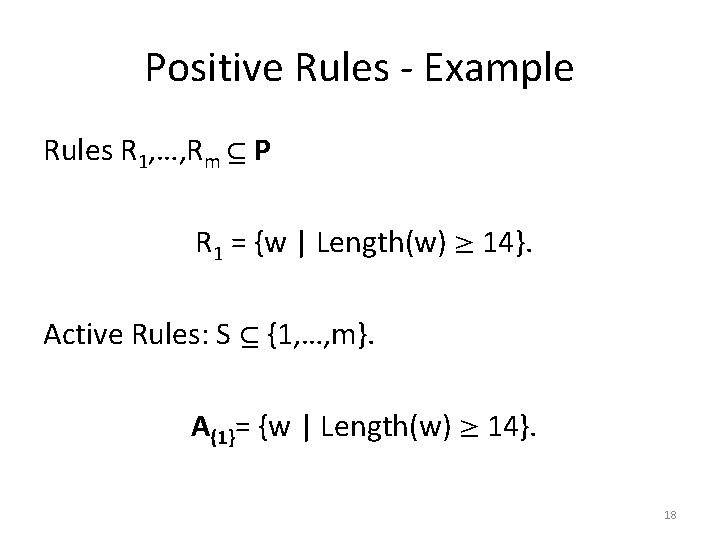
Positive Rules - Example Rules R 1, …, Rm P R 1 = {w | Length(w) 14}. Active Rules: S {1, …, m}. A{1}= {w | Length(w) 14}. 18
Negative Rules • 19
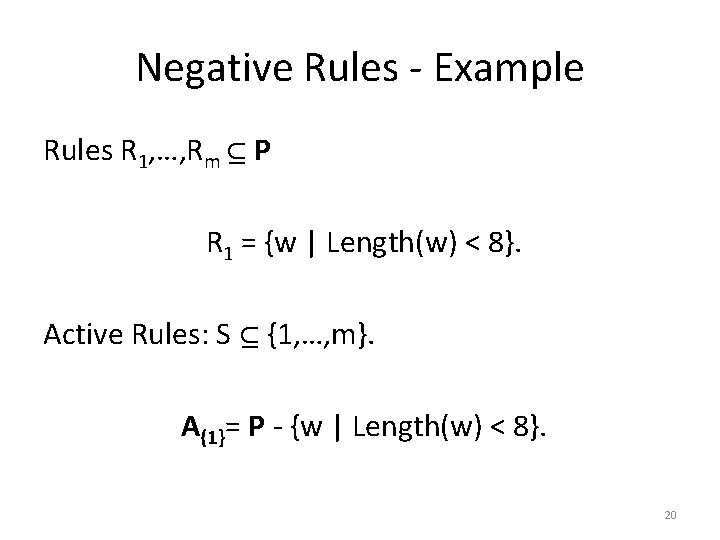
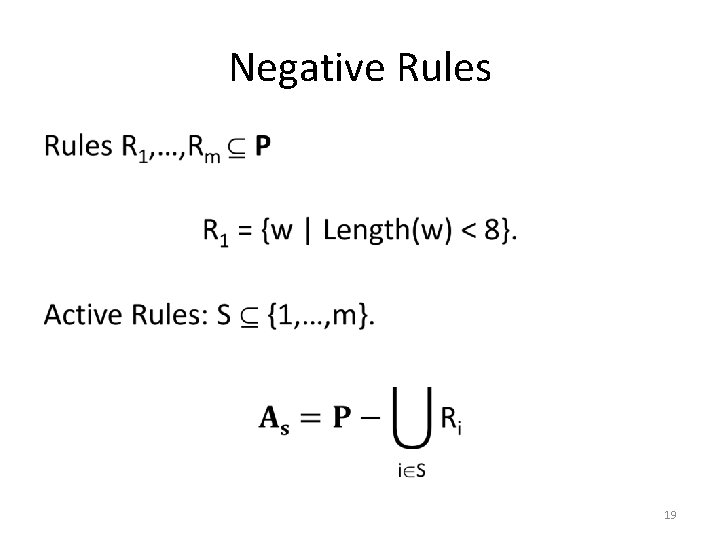
Negative Rules - Example Rules R 1, …, Rm P R 1 = {w | Length(w) < 8}. Active Rules: S {1, …, m}. A{1}= P - {w | Length(w) < 8}. 20
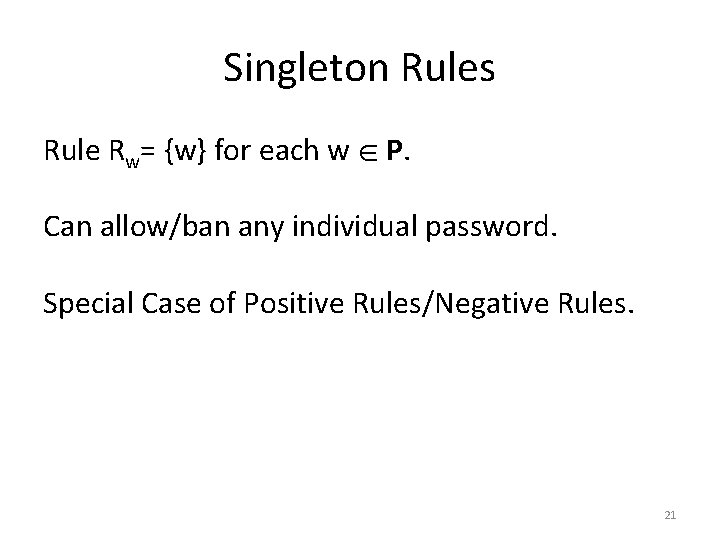
Singleton Rules Rule Rw= {w} for each w P. Can allow/ban any individual password. Special Case of Positive Rules/Negative Rules. 21
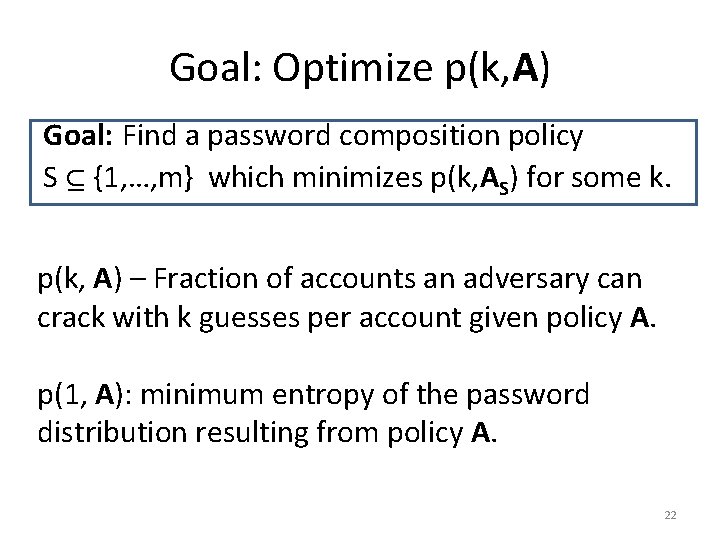
Goal: Optimize p(k, A) Goal: Find a password composition policy S {1, …, m} which minimizes p(k, AS) for some k. p(k, A) – Fraction of accounts an adversary can crack with k guesses per account given policy A. p(1, A): minimum entropy of the password distribution resulting from policy A. 22
Outline • • • Goal User Model Policy Structure Algorithms and Reductions Experiments 23
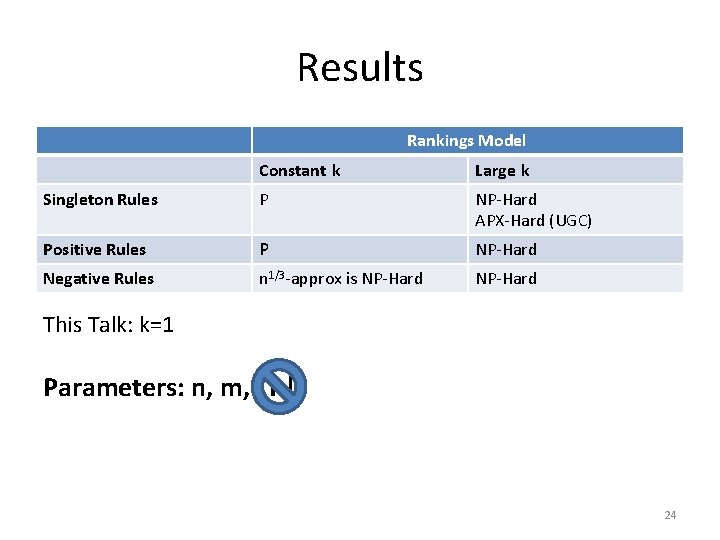
Results Rankings Model Constant k Large k Singleton Rules P NP-Hard APX-Hard (UGC) Positive Rules P NP-Hard Negative Rules n 1/3 -approx is NP-Hard This Talk: k=1 Parameters: n, m, |P| 24
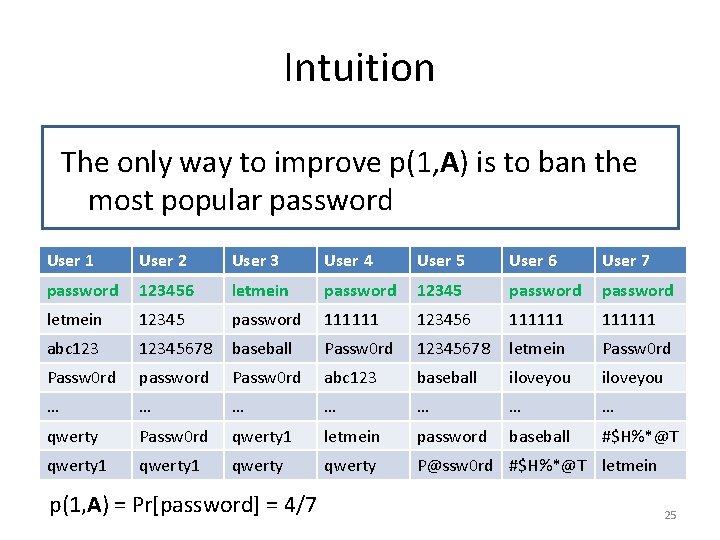
Intuition The only way to improve p(1, A) is to ban the most popular password User 1 User 2 User 3 User 4 User 5 User 6 User 7 password 123456 letmein password 12345 password letmein 12345 password 111111 123456 111111 abc 12345678 baseball Passw 0 rd 12345678 letmein Passw 0 rd password Passw 0 rd abc 123 baseball iloveyou … … … … qwerty Passw 0 rd qwerty 1 letmein password baseball #$H%*@T qwerty 1 qwerty P@ssw 0 rd #$H%*@T letmein p(1, A) = Pr[password] = 4/7 25
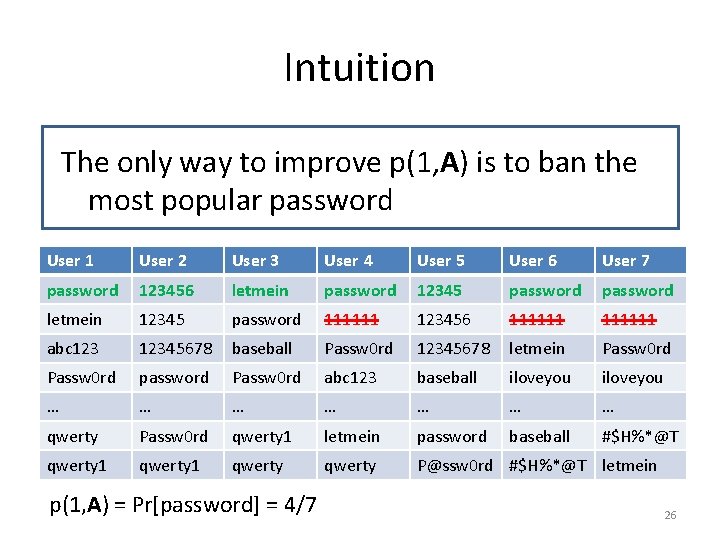
Intuition The only way to improve p(1, A) is to ban the most popular password User 1 User 2 User 3 User 4 User 5 User 6 User 7 password 123456 letmein password 12345 password letmein 12345 password 111111 123456 111111 abc 12345678 baseball Passw 0 rd 12345678 letmein Passw 0 rd password Passw 0 rd abc 123 baseball iloveyou … … … … qwerty Passw 0 rd qwerty 1 letmein password baseball #$H%*@T qwerty 1 qwerty P@ssw 0 rd #$H%*@T letmein p(1, A) = Pr[password] = 4/7 26
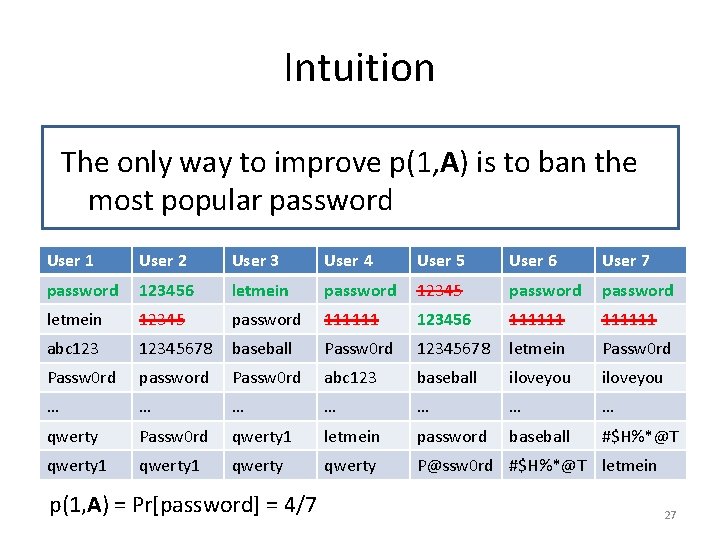
Intuition The only way to improve p(1, A) is to ban the most popular password User 1 User 2 User 3 User 4 User 5 User 6 User 7 password 123456 letmein password 12345 password letmein 12345 password 111111 123456 111111 abc 12345678 baseball Passw 0 rd 12345678 letmein Passw 0 rd password Passw 0 rd abc 123 baseball iloveyou … … … … qwerty Passw 0 rd qwerty 1 letmein password baseball #$H%*@T qwerty 1 qwerty P@ssw 0 rd #$H%*@T letmein p(1, A) = Pr[password] = 4/7 27
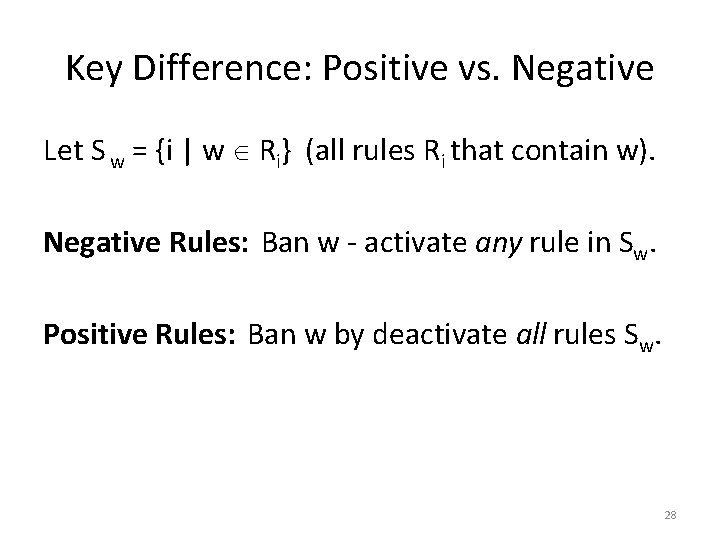
Key Difference: Positive vs. Negative Let S w = {i | w Ri} (all rules Ri that contain w). Negative Rules: Ban w - activate any rule in Sw. Positive Rules: Ban w by deactivate all rules Sw. 28
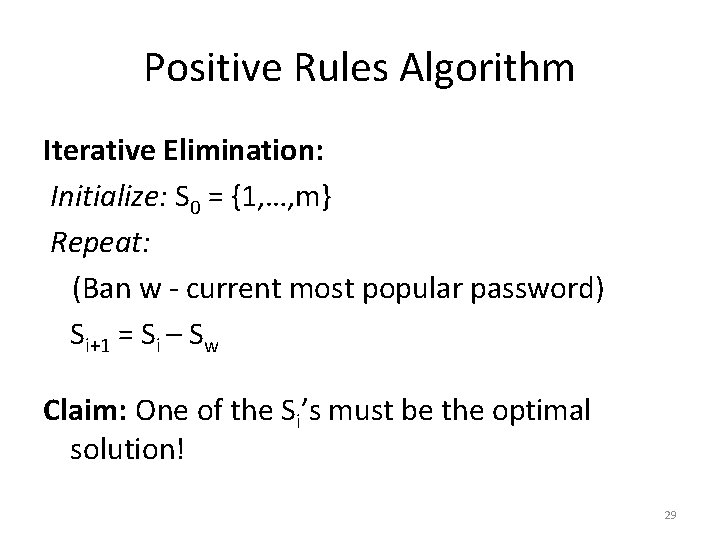
Positive Rules Algorithm Iterative Elimination: Initialize: S 0 = {1, …, m} Repeat: (Ban w - current most popular password) Si+1 = Si – Sw Claim: One of the Si’s must be the optimal solution! 29
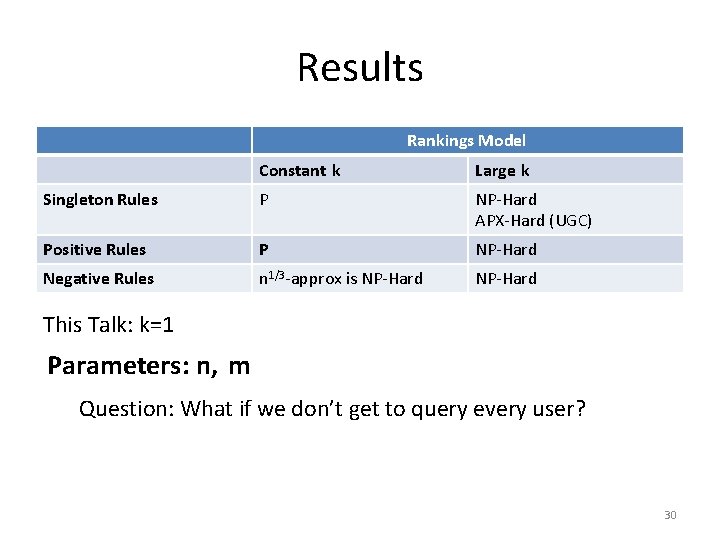
Results Rankings Model Constant k Large k Singleton Rules P NP-Hard APX-Hard (UGC) Positive Rules P NP-Hard Negative Rules n 1/3 -approx is NP-Hard This Talk: k=1 Parameters: n, m Question: What if we don’t get to query every user? 30
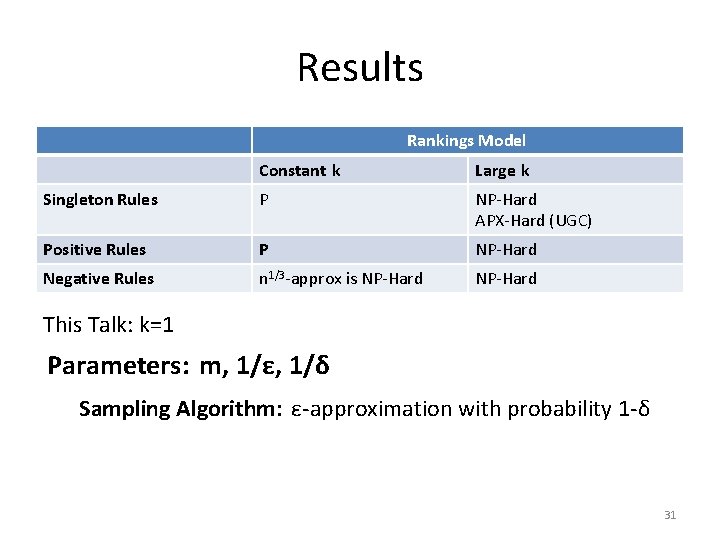
Results Rankings Model Constant k Large k Singleton Rules P NP-Hard APX-Hard (UGC) Positive Rules P NP-Hard Negative Rules n 1/3 -approx is NP-Hard This Talk: k=1 Parameters: m, 1/ε, 1/δ Sampling Algorithm: ε-approximation with probability 1 -δ 31
![Sampling Algorithm Sample: q(A) returns w with probability P[w|A]. • Idea: Run iterative elimination. Sampling Algorithm Sample: q(A) returns w with probability P[w|A]. • Idea: Run iterative elimination.](http://slidetodoc.com/presentation_image_h2/7441c6d3ffacbf7346ec6f3fda3cc3e8/image-33.jpg)
Sampling Algorithm Sample: q(A) returns w with probability P[w|A]. • Idea: Run iterative elimination. In each round use sampling to estimate the probability of the most popular word. 32
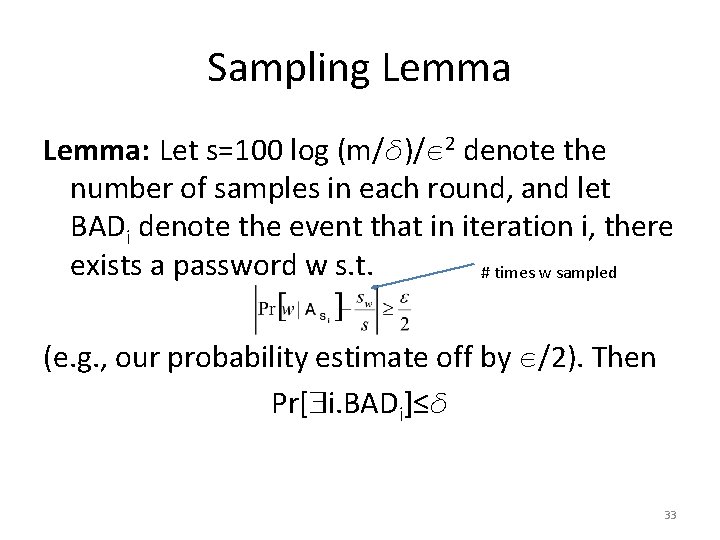
Sampling Lemma: Let s=100 log (m/ )/ 2 denote the number of samples in each round, and let BADi denote the event that in iteration i, there exists a password w s. t. # times w sampled (e. g. , our probability estimate off by /2). Then Pr[ i. BADi]≤ 33

Outline • • • Goal User Model Policy Structure Algorithms and Reductions Experiments – Normalized Probabilities Assumption – Rules – Results 34
![Rock. You Dataset • Rock. You password leak: 32 million plaintext passwords. • Pr[“password”] Rock. You Dataset • Rock. You password leak: 32 million plaintext passwords. • Pr[“password”]](http://slidetodoc.com/presentation_image_h2/7441c6d3ffacbf7346ec6f3fda3cc3e8/image-36.jpg)
Rock. You Dataset • Rock. You password leak: 32 million plaintext passwords. • Pr[“password”] 0. 01 • No Preference Lists: Insufficient for our sampling algorithm. • We test our algorithm under an additional assumption… 35
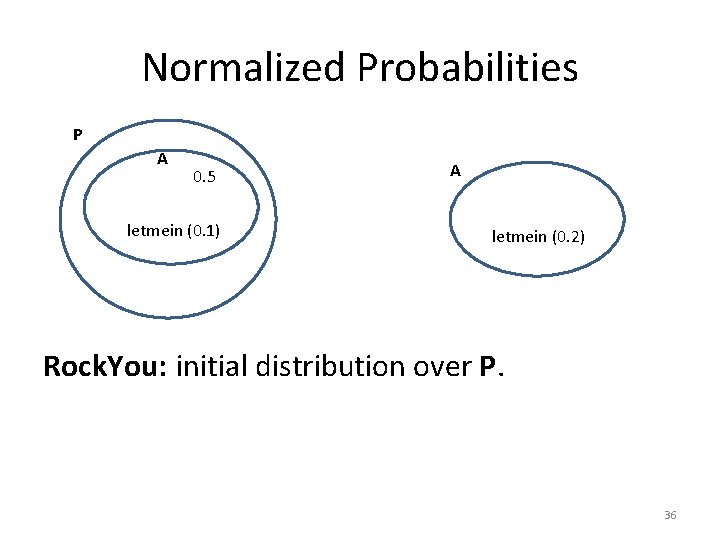
Normalized Probabilities P A 0. 5 1 0. 5 letmein (0. 1) A 1 letmein (0. 2) Rock. You: initial distribution over P. 36
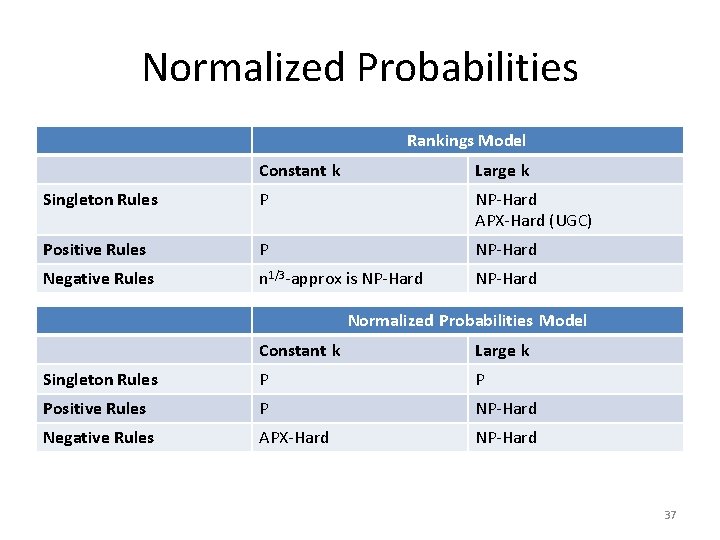
Normalized Probabilities Rankings Model Constant k Large k Singleton Rules P NP-Hard APX-Hard (UGC) Positive Rules P NP-Hard Negative Rules n 1/3 -approx is NP-Hard Normalized Probabilities Model Constant k Large k Singleton Rules P P Positive Rules P NP-Hard Negative Rules APX-Hard NP-Hard 37
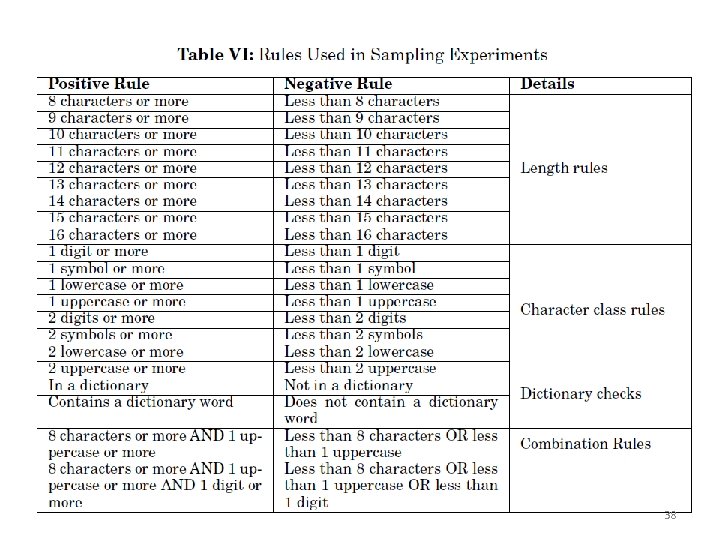
38
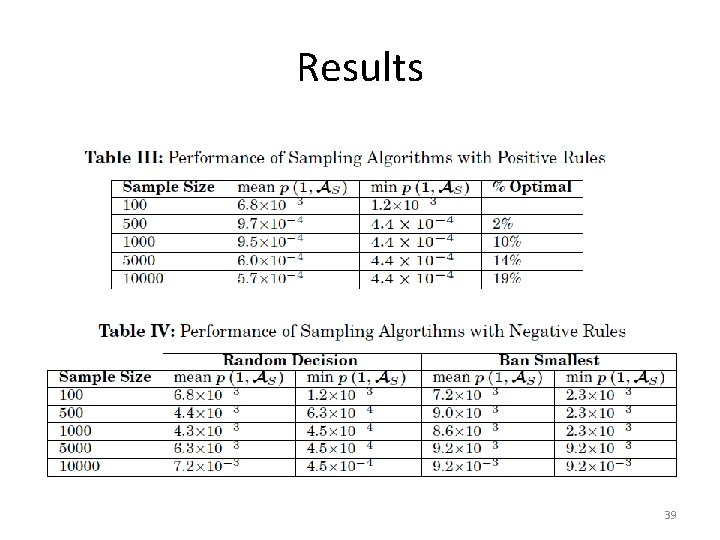
Results 39
Future Work • Open Questions – Approximation algorithm in negative rules setting with normalized probabilities assumption? • Interesting Directions: – Usability Costs? – Additional Rules? – Adversary with limited background knowledge (e. g. , age, gender). – General experiment in preference list model? Thanks for Listening! 40
- Slides: 41