Media Access Protocols Organizational Communications and Technologies Prithvi
- Slides: 38
Media Access Protocols Organizational Communications and Technologies Prithvi N. Rao H. John Heinz III School of Public Policy and Management Carnegie Mellon University
Readings High Speed and Wireless LANs(Stallings and van Slyke) Chapters 4, 7, 9
Objectives n Be familiar with the IEEE LAN standards n Recognize various methods of media access n Discuss token passing media access method n Describe broadcast media access n Recognize how information moves between protocol layers
LAN Communication Protocols n Required to define how workstations on LAN interact n Protocols specify rules for successful data movement n Communication protocols define media access methods, addressing and routing information n n Data link to network and transport layers IEEE developed protocols for LAN n Equipment and software
LAN Communication Protocols n Committee formed in 1980 n IEEE 802 LAN specificaiton
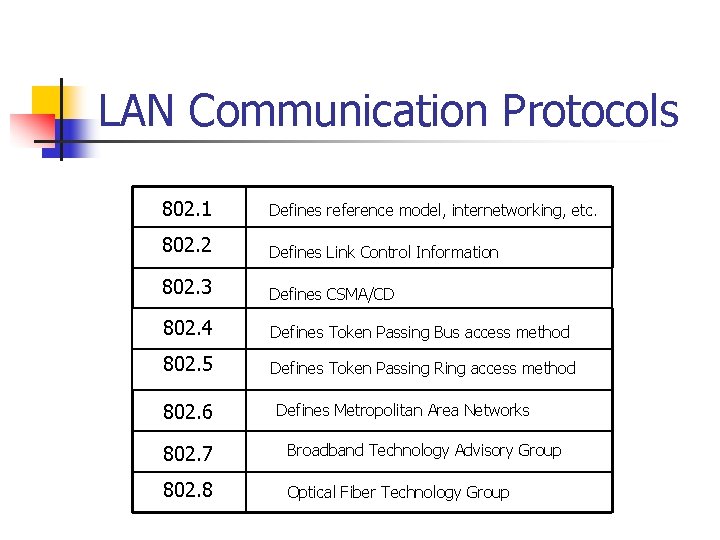
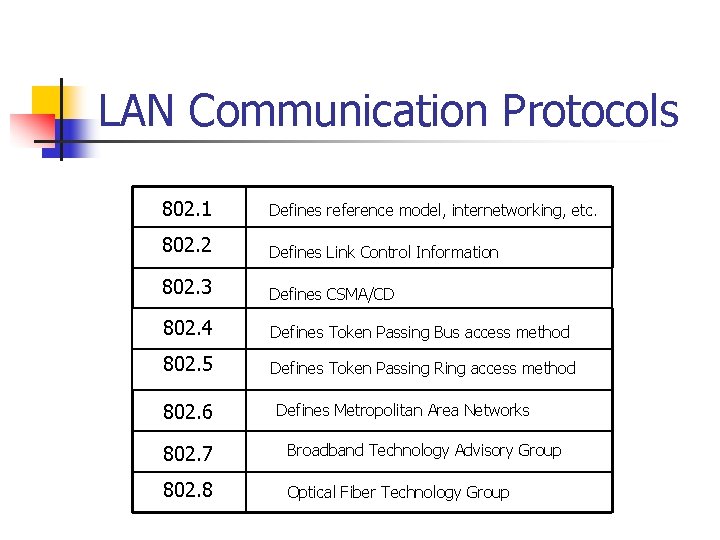
LAN Communication Protocols 802. 1 Defines reference model, internetworking, etc. 802. 2 Defines Link Control Information 802. 3 Defines CSMA/CD 802. 4 Defines Token Passing Bus access method 802. 5 Defines Token Passing Ring access method 802. 6 Defines Metropolitan Area Networks 802. 7 Broadband Technology Advisory Group 802. 8 Optical Fiber Technology Group
Media Access Methods n Three methods of media access are: n n n Token passing or the ticket system Broadcast Polling n Each is intended to gain access to the media n Fundamentally there is a message exchange
Media Access Methods: Token Passing n Deterministic access method n n n Node may only transmit when it has token Token is generated and travels throughout network Each node gets chance to transmit Node waiting to transmit grabs token and transmits Token is passed to next node if nothing to transmit Node seizing token changes token bit n n Expands token to add frame to the end Token is transmitted over network to hardware of destination node
Media Access Methods: Token Passing n Destination node does not remove the frame n n n Copies the token Token circles (with data) till it reaches source Source reconstructs token with new data frame Token is released with available bit set to available status Token Ring Summary n n Specification developed and supported by IBM Data rate is 4 or 16 Mbits per second Uses shielded or unshielded twisted pair Built in by-pass capability and a max of 260 stations on ring
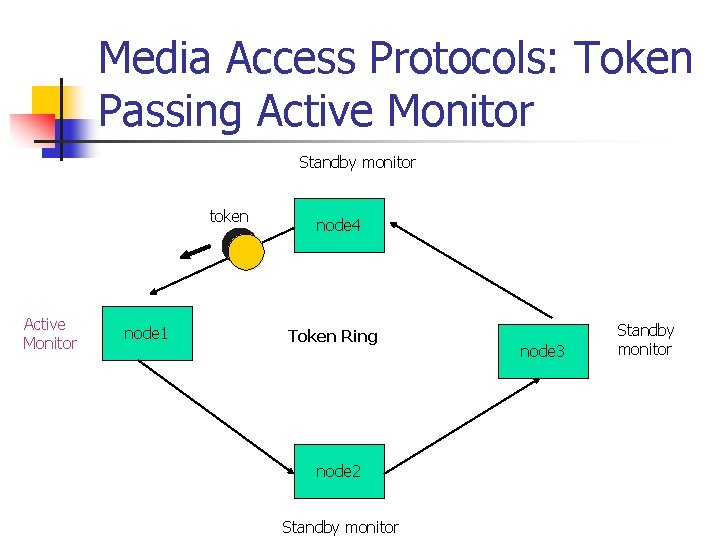
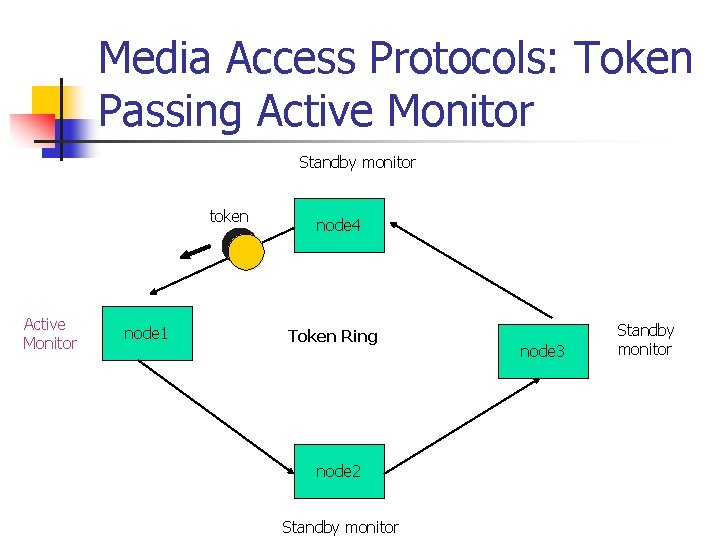
Media Access Protocols: Token Passing Active Monitor Standby monitor token Active Monitor node 1 node 4 Token Ring node 2 Standby monitor node 3 Standby monitor
Media Access Methods: Token Passing n All nodes are one of two types n n n Active monitor – responsible for the high integrity of the token Standby monitors – waiting to become an active monitor Active monitor is in charge of token n n Releases token and manages token passing protocol Active monitor is first station on the ring Standby monitors bid to become active monitors by sending a claim token command Node with highest hardware address becomes new active monitor
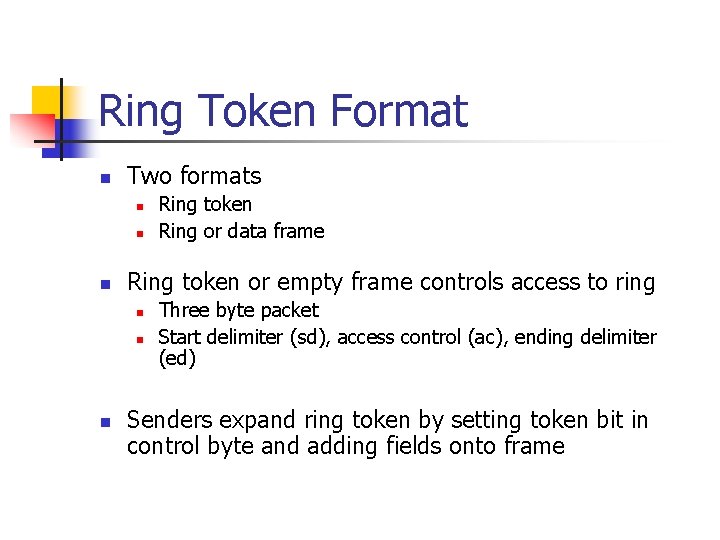
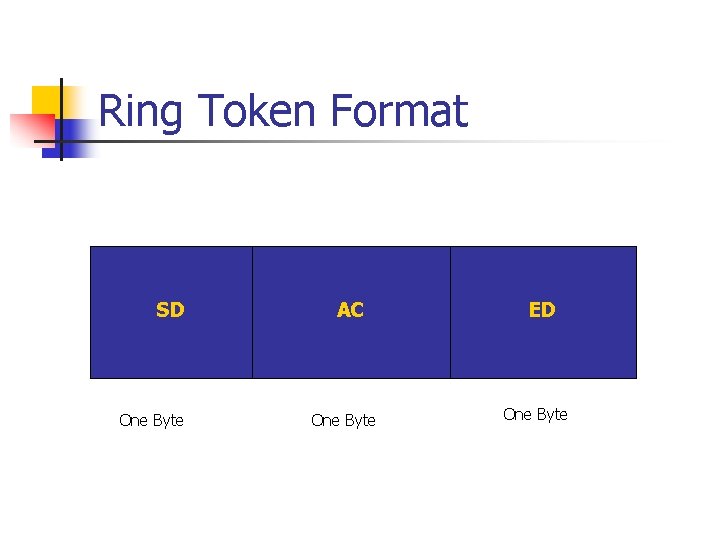
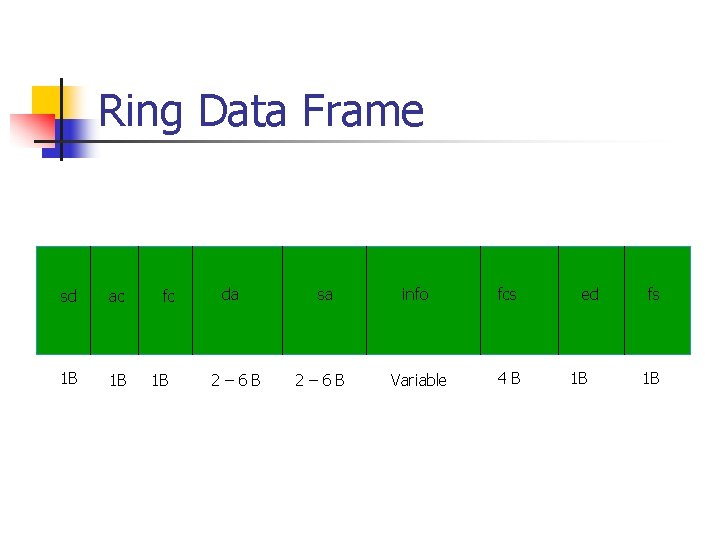
Ring Token Format n Two formats n n n Ring token or empty frame controls access to ring n n n Ring token Ring or data frame Three byte packet Start delimiter (sd), access control (ac), ending delimiter (ed) Senders expand ring token by setting token bit in control byte and adding fields onto frame
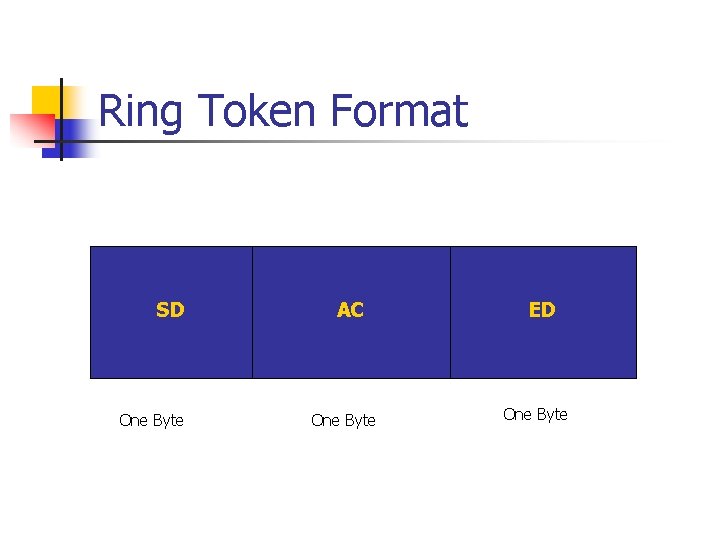
Ring Token Format SD One Byte AC One Byte ED One Byte
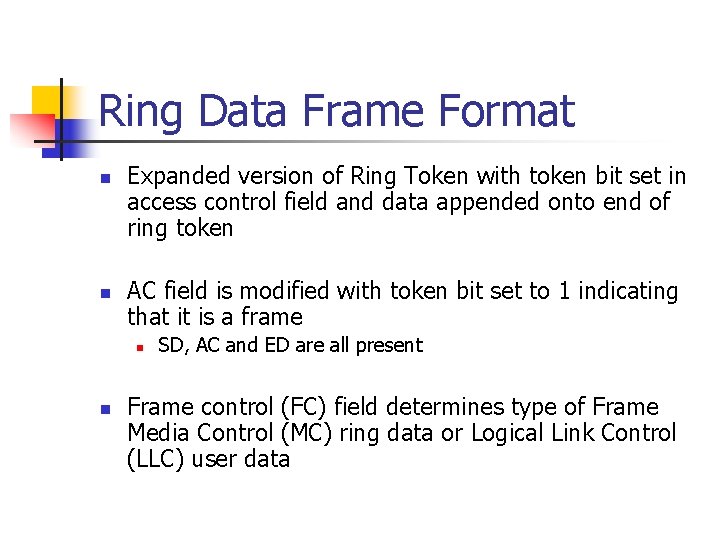
Ring Data Frame Format n n Expanded version of Ring Token with token bit set in access control field and data appended onto end of ring token AC field is modified with token bit set to 1 indicating that it is a frame n n SD, AC and ED are all present Frame control (FC) field determines type of Frame Media Control (MC) ring data or Logical Link Control (LLC) user data
Ring Data Frame Format n Address fields contain six byte source n n n Contains destination hardware or MAC addresses of transmitting and receiving nodes Route information field contains ring or bridge number Data field length determined by token holding timer n n n Longer timer means more data can be carried in data field before it expires 4 k for 4 mega-bit-per-second (MBPS) 17. 8 k for a 16 MBPS
Ring Data Frame n n Frame Check Sequence (FCS) field holds a CRC validation number Frame Status (FS) field contains address recognized
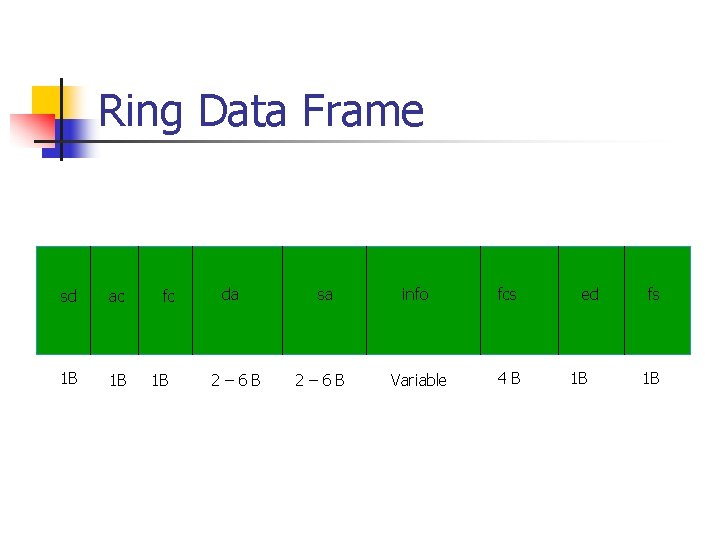
Ring Data Frame sd ac 1 B 1 B fc 1 B da 2– 6 B sa 2– 6 B info fcs Variable 4 B ed 1 B fs 1 B
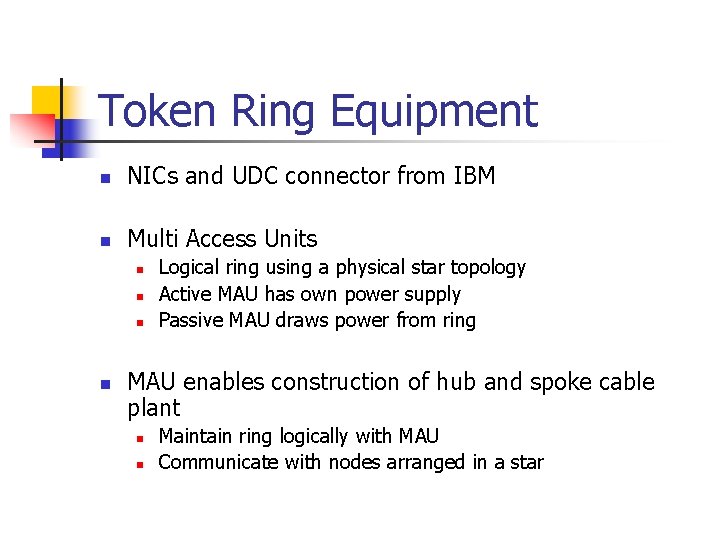
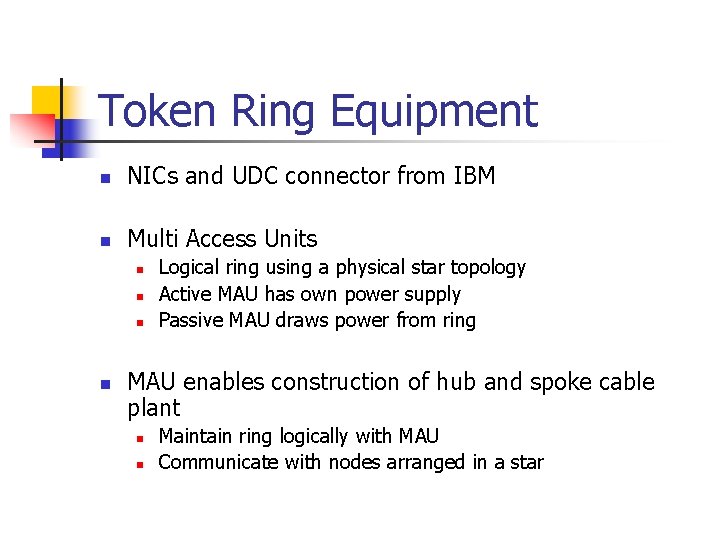
Token Ring Equipment n NICs and UDC connector from IBM n Multi Access Units n n Logical ring using a physical star topology Active MAU has own power supply Passive MAU draws power from ring MAU enables construction of hub and spoke cable plant n n Maintain ring logically with MAU Communicate with nodes arranged in a star
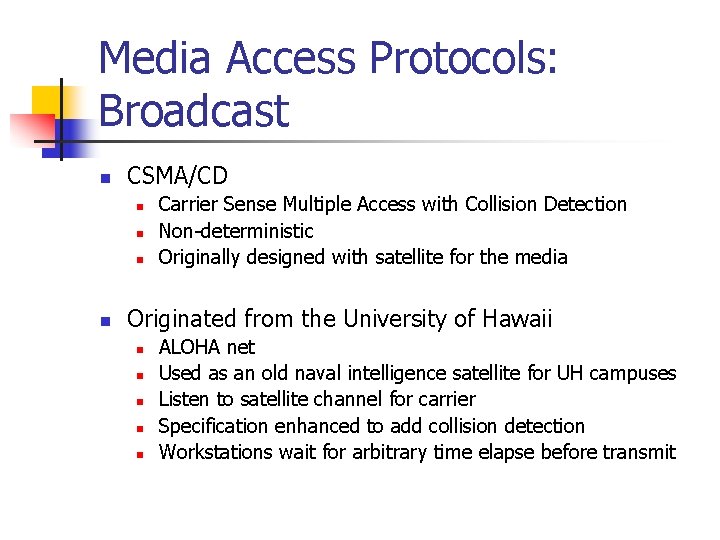
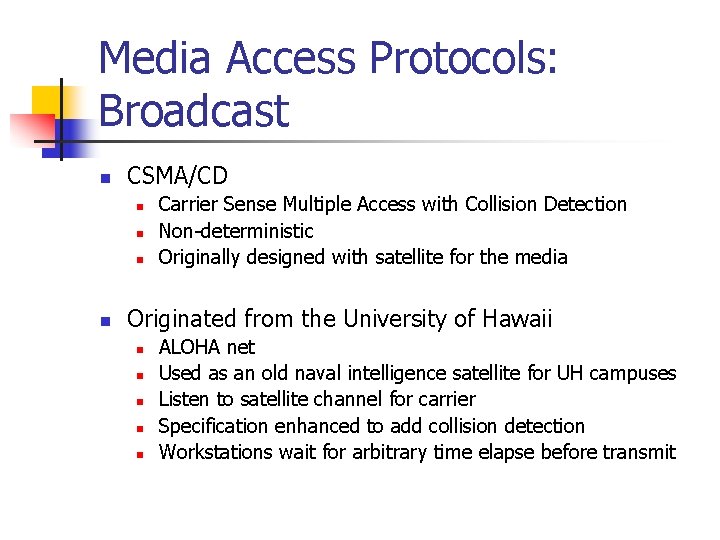
Media Access Protocols: Broadcast n CSMA/CD n n Carrier Sense Multiple Access with Collision Detection Non-deterministic Originally designed with satellite for the media Originated from the University of Hawaii n n n ALOHA net Used as an old naval intelligence satellite for UH campuses Listen to satellite channel for carrier Specification enhanced to add collision detection Workstations wait for arbitrary time elapse before transmit
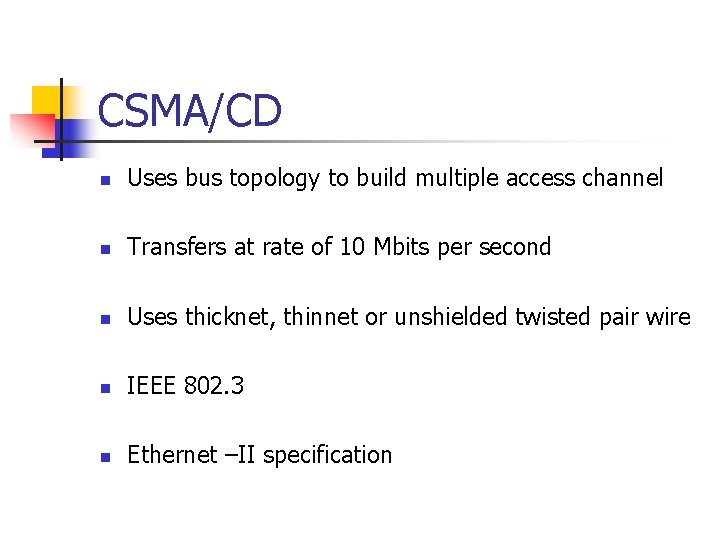
CSMA/CD n Uses bus topology to build multiple access channel n Transfers at rate of 10 Mbits per second n Uses thicknet, thinnet or unshielded twisted pair wire n IEEE 802. 3 n Ethernet –II specification
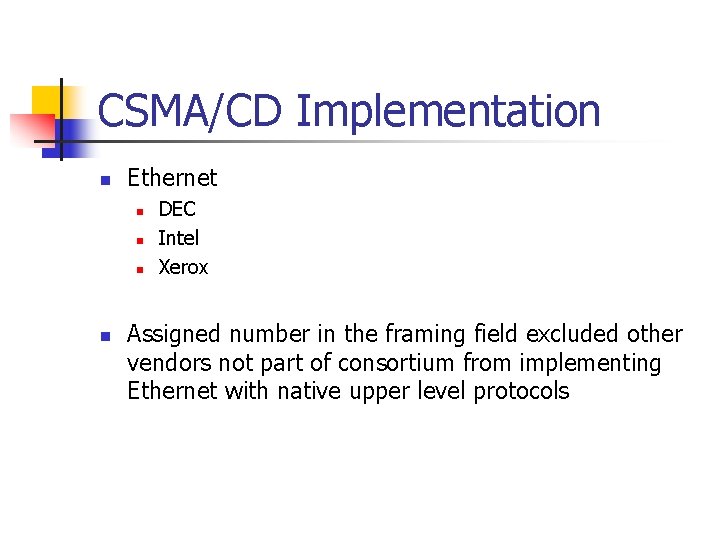
CSMA/CD Implementation n Ethernet n n DEC Intel Xerox Assigned number in the framing field excluded other vendors not part of consortium from implementing Ethernet with native upper level protocols
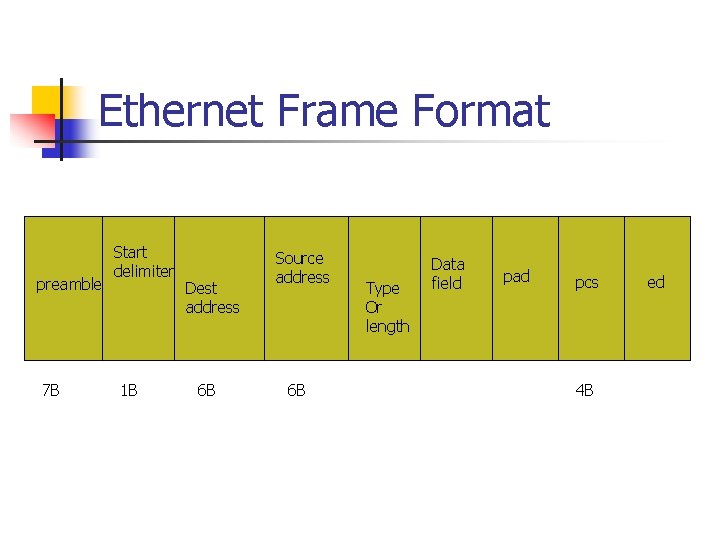
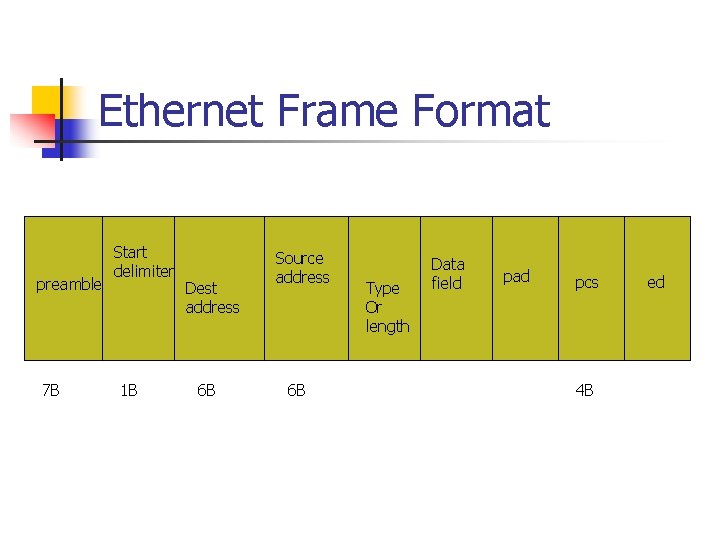
Ethernet Frame Format preamble 7 B Start delimiter 1 B Dest address 6 B Source address 6 B Type Or length Data field pad pcs 4 B ed
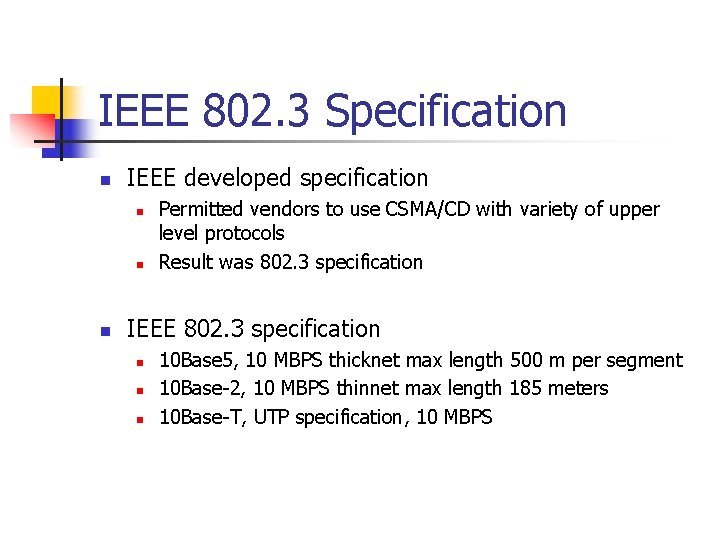
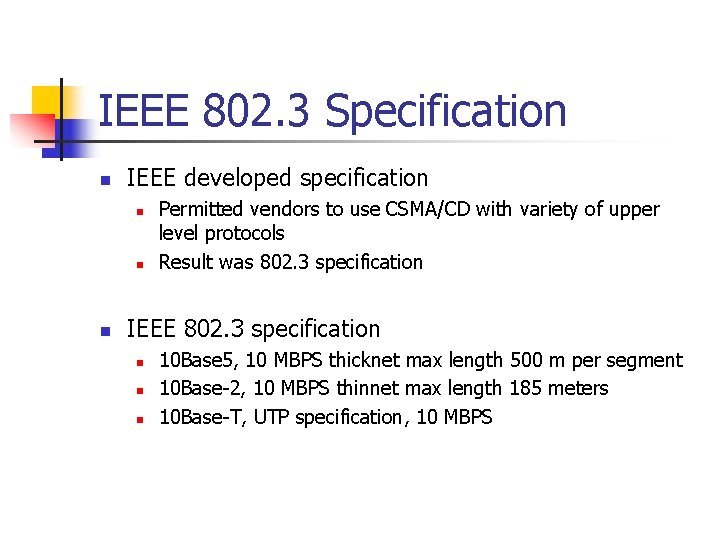
IEEE 802. 3 Specification n IEEE developed specification n Permitted vendors to use CSMA/CD with variety of upper level protocols Result was 802. 3 specification IEEE 802. 3 specification n 10 Base 5, 10 MBPS thicknet max length 500 m per segment 10 Base-2, 10 MBPS thinnet max length 185 meters 10 Base-T, UTP specification, 10 MBPS
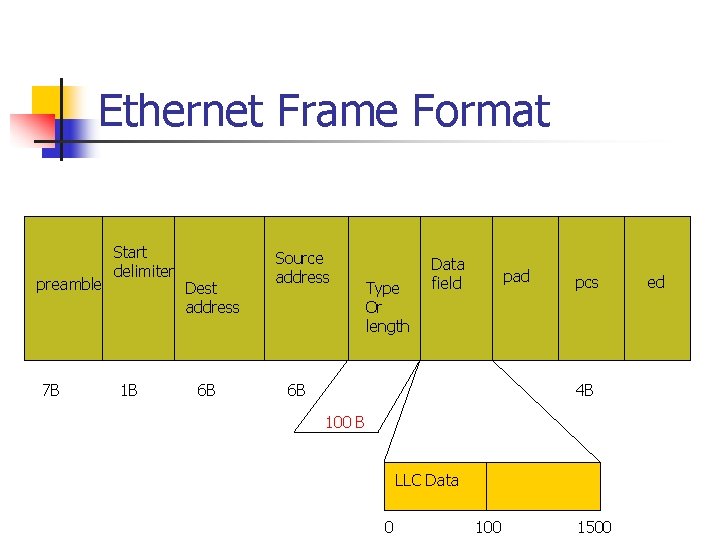
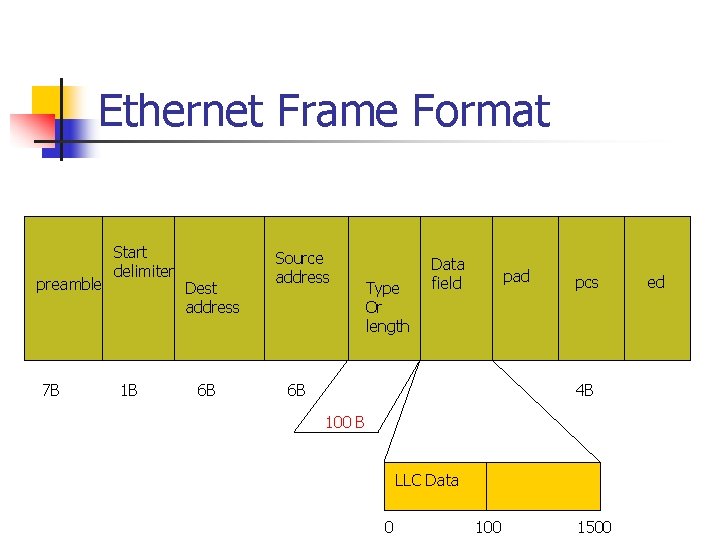
Ethernet Frame Format preamble 7 B Start delimiter 1 B Dest address 6 B Source address Type Or length Data field pad 6 B pcs 4 B 100 B LLC Data 0 100 1500 ed
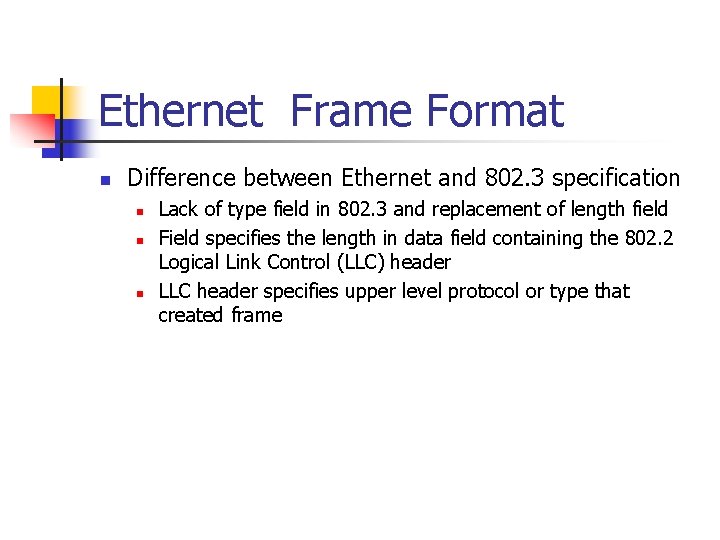
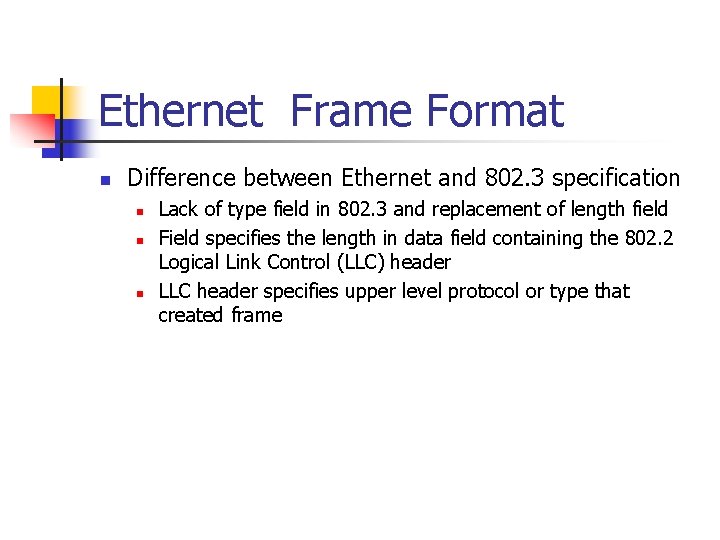
Ethernet Frame Format n Difference between Ethernet and 802. 3 specification n Lack of type field in 802. 3 and replacement of length field Field specifies the length in data field containing the 802. 2 Logical Link Control (LLC) header LLC header specifies upper level protocol or type that created frame
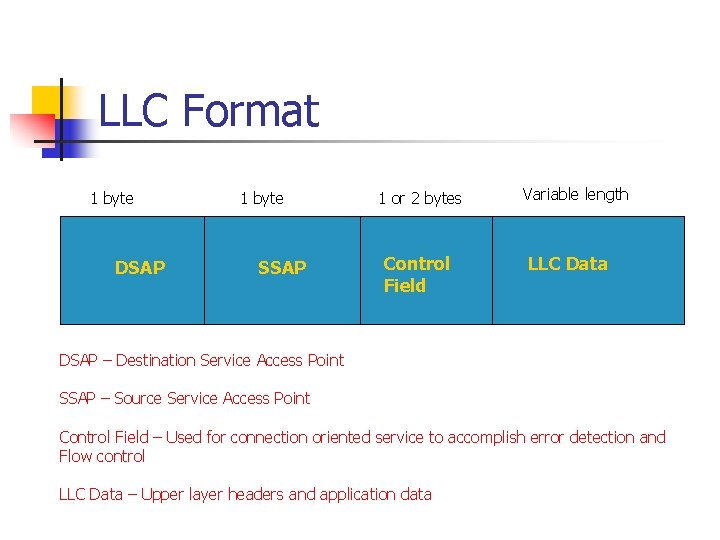
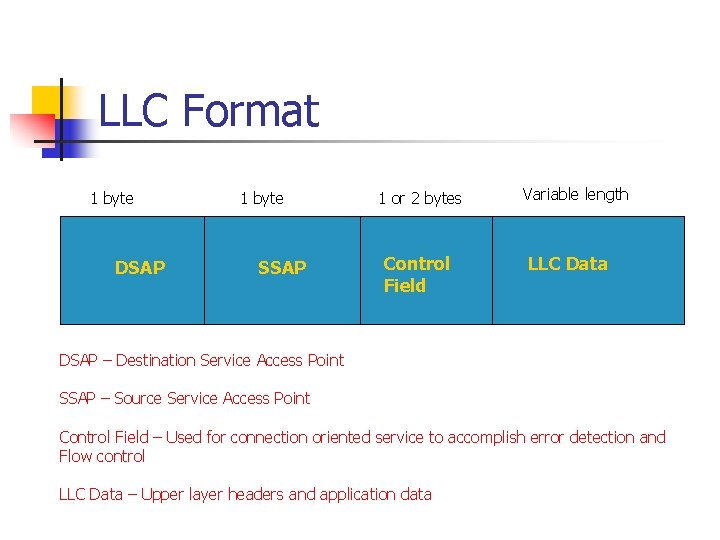
LLC Format 1 byte DSAP 1 byte SSAP 1 or 2 bytes Control Field Variable length LLC Data DSAP – Destination Service Access Point SSAP – Source Service Access Point Control Field – Used for connection oriented service to accomplish error detection and Flow control LLC Data – Upper layer headers and application data
Media Access Polling n Token passing and broadcast media access methods rely on network to permit access to media n Rules are built into the protocol n Token passing is more equitable n n Each node has equal chance to use media Rely on bursty nature of network usage n Permits access to media whenever node wishes to transmit
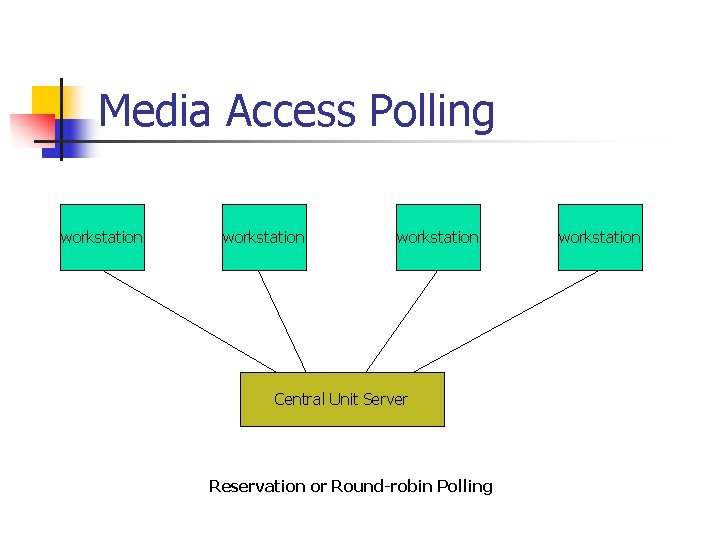
Media Access Polling n Polling is combination of design of two methods n Polling protocol defines central intelligent device n n n Pre-determined order Node requesting network service accomplished when node is queried or polled Node begins to use network n n Node completes transmission Central device can interrupt node in favor of higher priority node
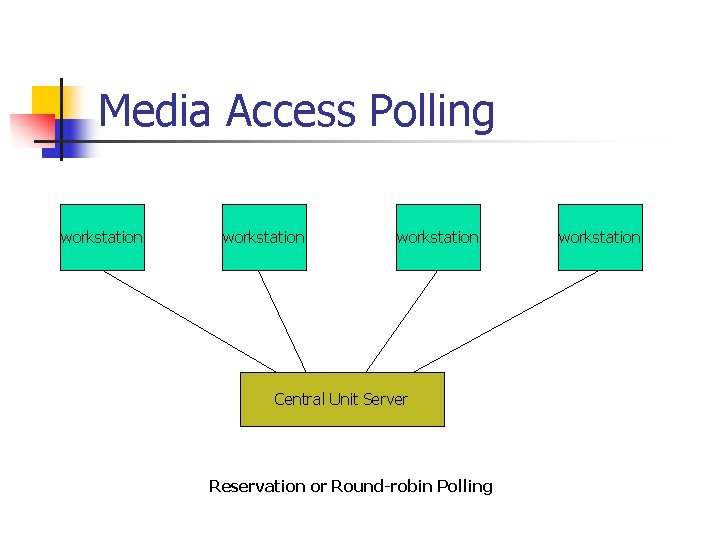
Media Access Polling workstation Central Unit Server Reservation or Round-robin Polling workstation
Media Access Polling not as popular as token passing or broadcast methods n n AKA round robin used in mainframe or mini-computer mulltiuser networks Polling could come back into vogue n High-speed multi-channel media getting popular
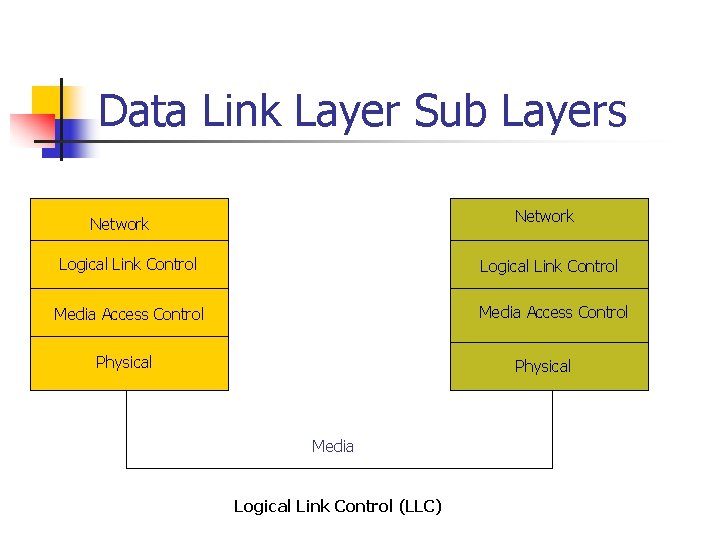
Data Link Layer Sub Layers n Subdivided into two parts n n Media Access Control (MAC) Logical Link Control (LLC) Important to understand LLC before moving up the OSI model Key is that each layer must know what to do with data it is handed
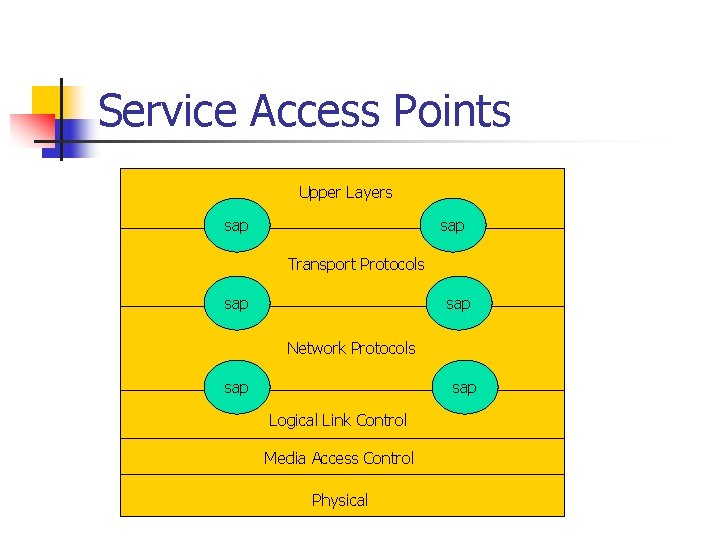
Data Link Layer Sub Layers n LLC sub-layer indicates service access point (sac) used to move transmission unit up to next level n n SAC is address of next protocol to which transmission should be sent SAC are interface between layers n N + 1 and N – 1 for layer N
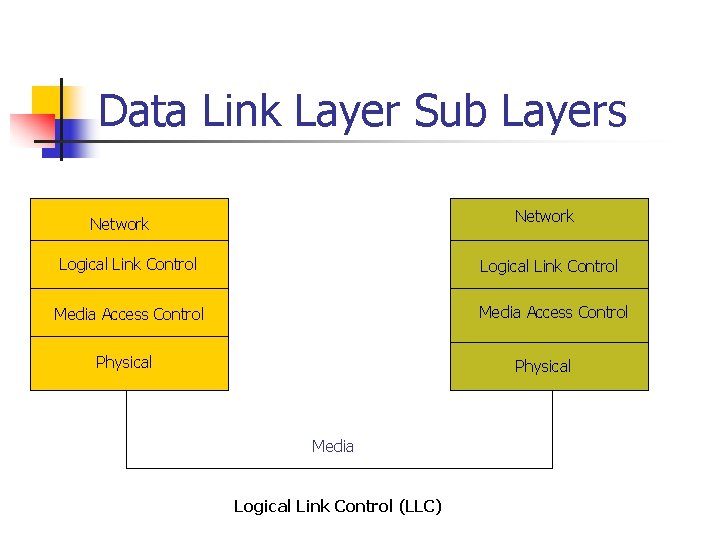
Data Link Layer Sub Layers Network Logical Link Control Media Access Control Physical Media Logical Link Control (LLC)
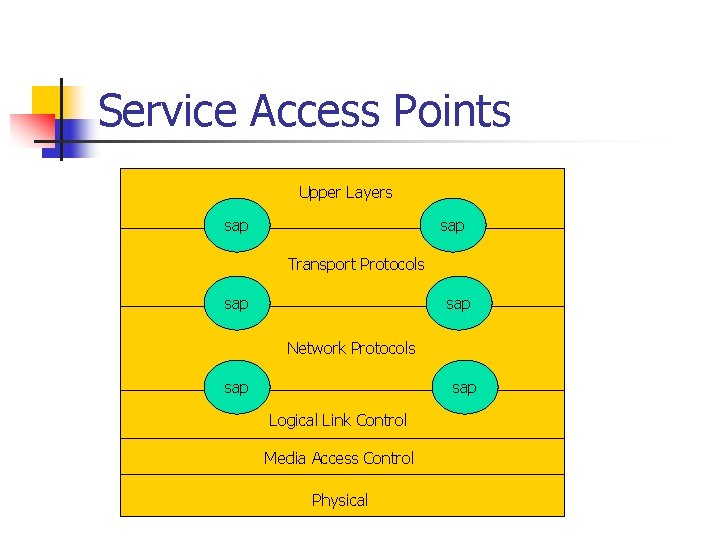
Service Access Points Upper Layers sap Transport Protocols sap Network Protocols sap Logical Link Control Media Access Control Physical
Service Access Points n n Modular design of OSI model enables variety of protocols to be available at each level Given layer knows about layer to send transmission using the source and destination SAP header
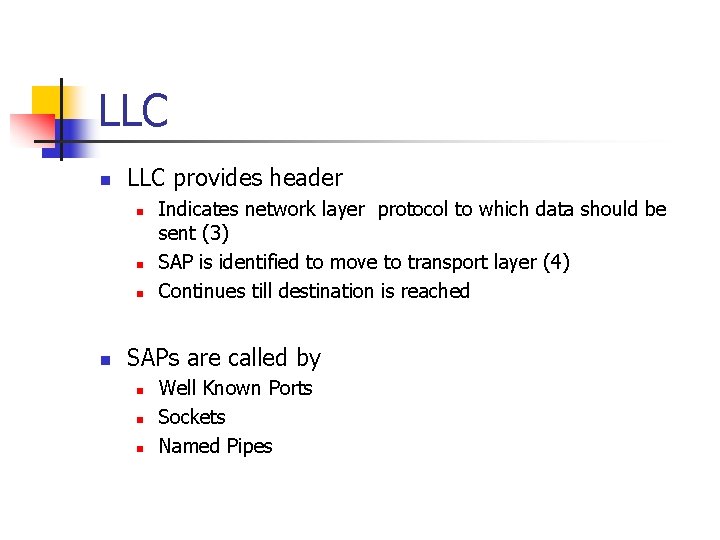
LLC n LLC provides header n n Indicates network layer protocol to which data should be sent (3) SAP is identified to move to transport layer (4) Continues till destination is reached SAPs are called by n n n Well Known Ports Sockets Named Pipes
Summary n Three prevalent forms of media access n n Token passing Broadcast Polling Token passing defined in IEEE 802. 3 n n Several implementations of non-deterministic Ethernet protocol Ethernet LANs provide access to the LAN on a first-comefirst serve or most persistent basis
Summary n Polling is controlled by central monitor n n Future LANs may benefit from this Information moves between layers of communication architecture through addressing n Service access points are specific address locations that enable information to move through a layered architecture