Linear Cryptanalysis Differential Cryptanalysis of Block Ciphers CSCI
- Linear Cryptanalysis - Differential Cryptanalysis of Block Ciphers CSCI 284 Spring 2009 GWU This slide set almost entirely from: H. M. Heys, "A Tutorial on Linear and Differential Cryptanalysis", Technical Report CORR 2001 -17, Centre for Applied Cryptographic Research, Department of Combinatorics and Optimization, University of Waterloo, Mar. 2001. (Also appears in Cryptologia, vol. XXVI, no. 3, pp. 189 -221, 2002. ) CS 284 -162/Spring 09/GWU/Vora/Block Ciphers: Cryptanalysis. All equations, tables, figures and accompanying text from Heys
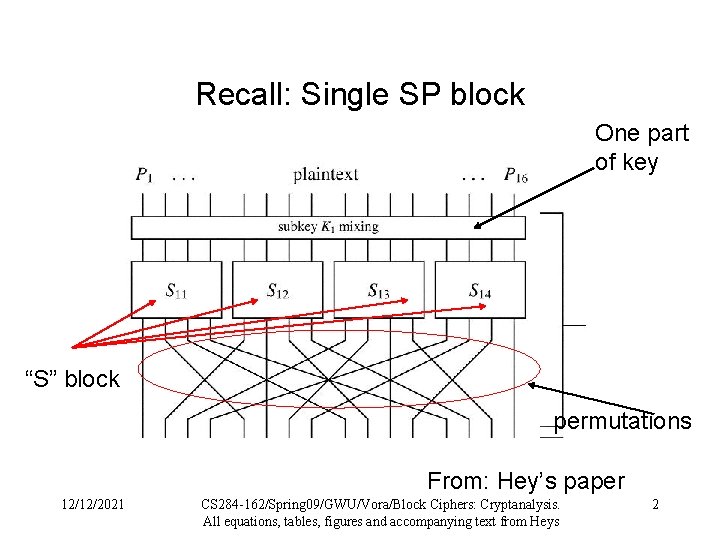
Recall: Single SP block One part of key “S” block permutations From: Hey’s paper 12/12/2021 CS 284 -162/Spring 09/GWU/Vora/Block Ciphers: Cryptanalysis. All equations, tables, figures and accompanying text from Heys 2
4 Rounds 12/12/2021 CS 284 -162/Spring 09/GWU/Vora/Block Ciphers: Cryptanalysis. All equations, tables, figures and accompanying text from Heys 3
An attack: linear cryptanalysis First concentrate on breaking a single S-box: Model S-box in terms of probabilities of linear relationships between input and output bits E. g. : x 1 x 4 = y 2 y 4 is true with what probability? If Sbox were truly random, what would be the probability of that equation being true? Difference is the bias – the higher it is, the easier an attack 12/12/2021 CS 284 -162/Spring 09/GWU/Vora/Block Ciphers: Cryptanalysis. All equations, tables, figures and accompanying text from Heys 4
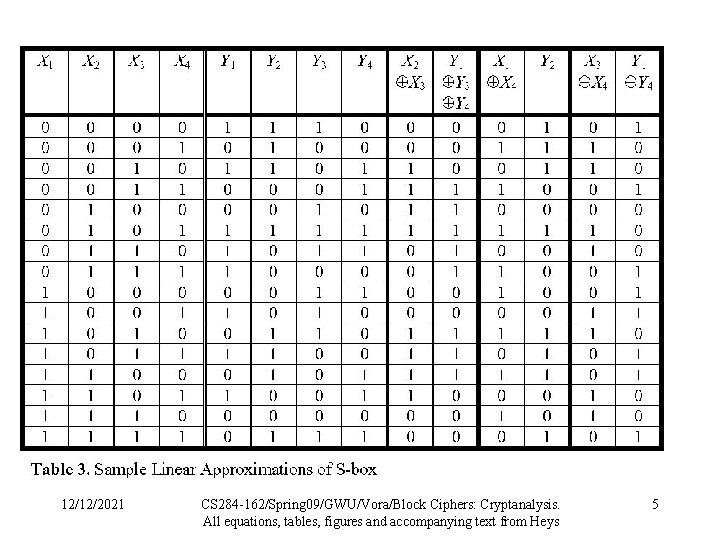
12/12/2021 CS 284 -162/Spring 09/GWU/Vora/Block Ciphers: Cryptanalysis. All equations, tables, figures and accompanying text from Heys 5
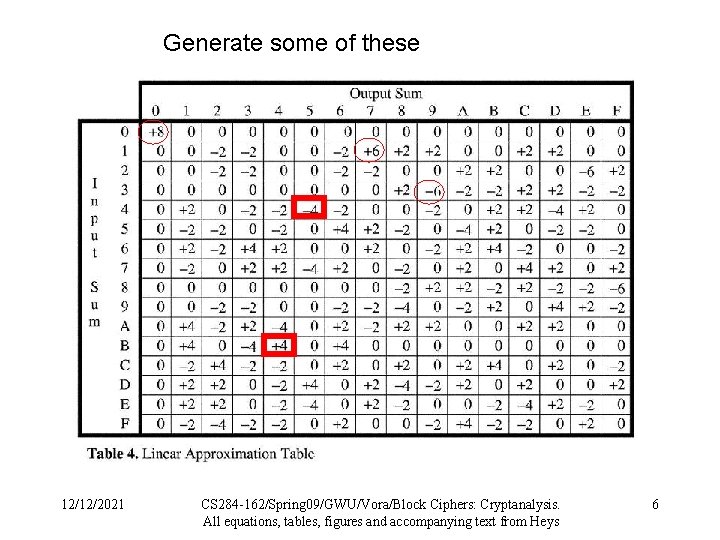
Generate some of these 12/12/2021 CS 284 -162/Spring 09/GWU/Vora/Block Ciphers: Cryptanalysis. All equations, tables, figures and accompanying text from Heys 6
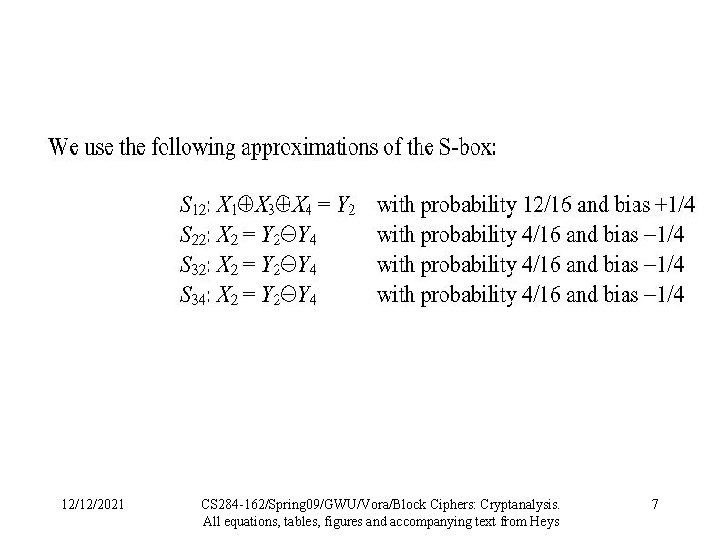
12/12/2021 CS 284 -162/Spring 09/GWU/Vora/Block Ciphers: Cryptanalysis. All equations, tables, figures and accompanying text from Heys 7
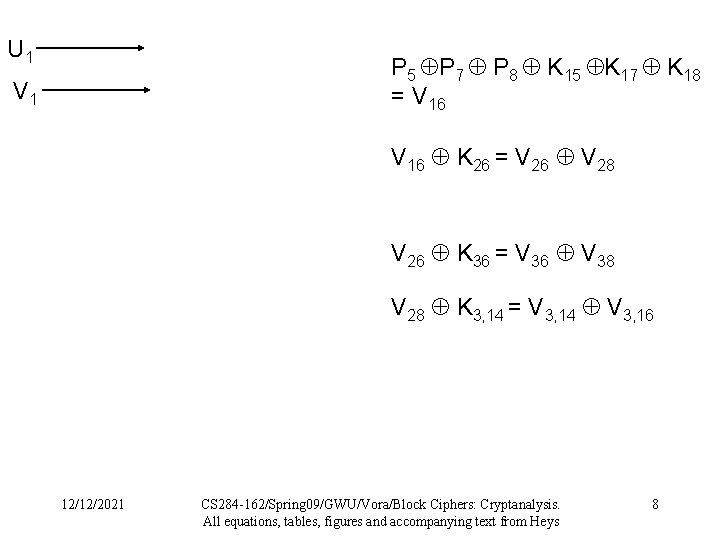
U 1 P 5 P 7 P 8 K 15 K 17 K 18 = V 16 K 26 = V 26 V 28 V 26 K 36 = V 36 V 38 V 28 K 3, 14 = V 3, 14 V 3, 16 12/12/2021 CS 284 -162/Spring 09/GWU/Vora/Block Ciphers: Cryptanalysis. All equations, tables, figures and accompanying text from Heys 8
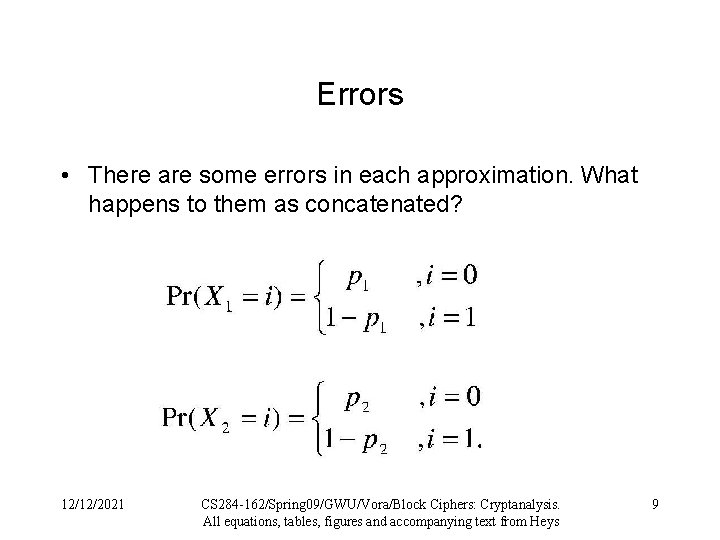
Errors • There are some errors in each approximation. What happens to them as concatenated? 12/12/2021 CS 284 -162/Spring 09/GWU/Vora/Block Ciphers: Cryptanalysis. All equations, tables, figures and accompanying text from Heys 9
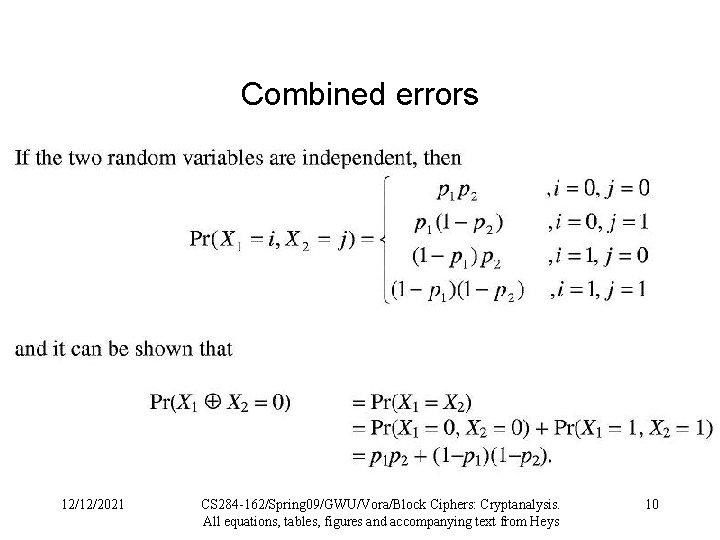
Combined errors 12/12/2021 CS 284 -162/Spring 09/GWU/Vora/Block Ciphers: Cryptanalysis. All equations, tables, figures and accompanying text from Heys 10
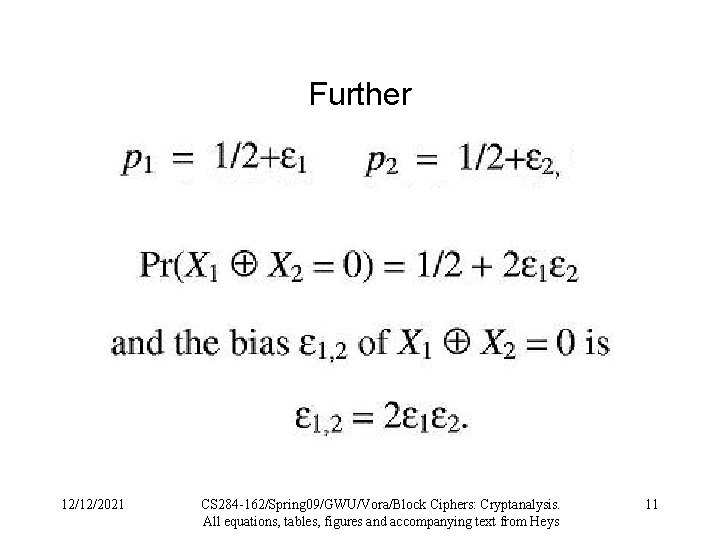
Further 12/12/2021 CS 284 -162/Spring 09/GWU/Vora/Block Ciphers: Cryptanalysis. All equations, tables, figures and accompanying text from Heys 11
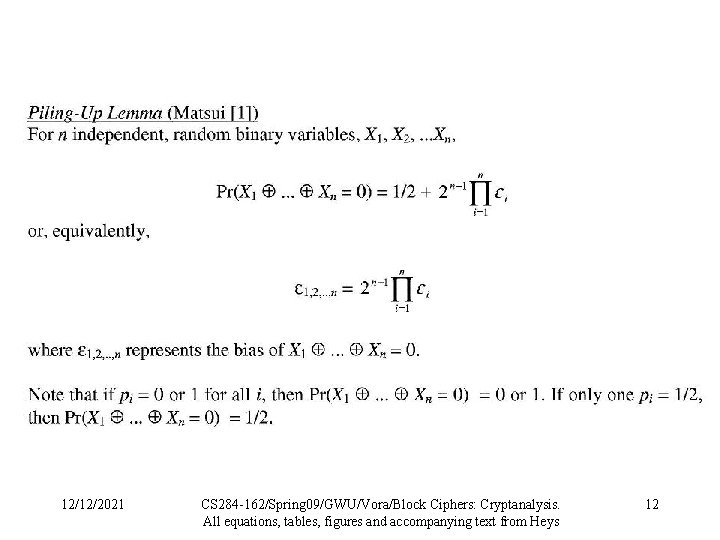
12/12/2021 CS 284 -162/Spring 09/GWU/Vora/Block Ciphers: Cryptanalysis. All equations, tables, figures and accompanying text from Heys 12
Complexity of linear cryptanalysis Need known plaintext-ciphertext pairs O(1 / 2) 12/12/2021 CS 284 -162/Spring 09/GWU/Vora/Block Ciphers: Cryptanalysis. All equations, tables, figures and accompanying text from Heys 13
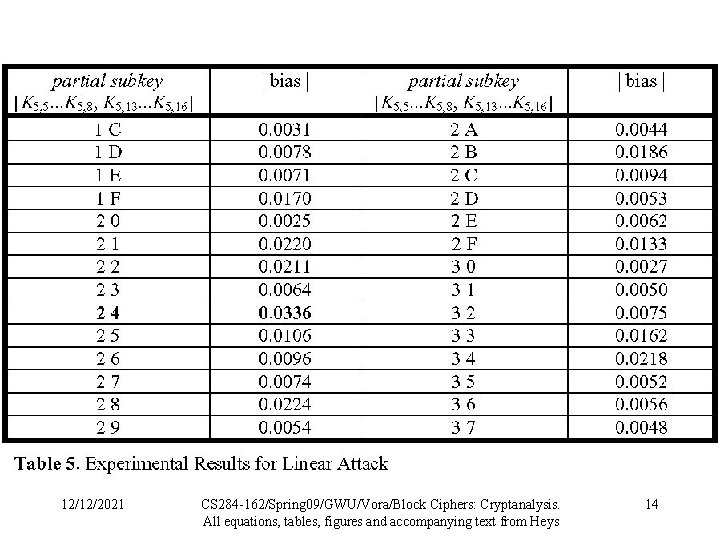
12/12/2021 CS 284 -162/Spring 09/GWU/Vora/Block Ciphers: Cryptanalysis. All equations, tables, figures and accompanying text from Heys 14
Differential Cryptanalysis • Like linear cryptanalysis, concentrate on breaking a single S-box: – Model S-box in terms of probabilities of output differences given input differences • E. g. : x = 1011 y = 0010 is true with what probability? If S-box were truly random, what would be the probability? • Difference is the bias – the higher the bias, the easier an attack 12/12/2021 CS 284 -162/Spring 09/GWU/Vora/Block Ciphers: Cryptanalysis. All equations, tables, figures and accompanying text from Heys 15
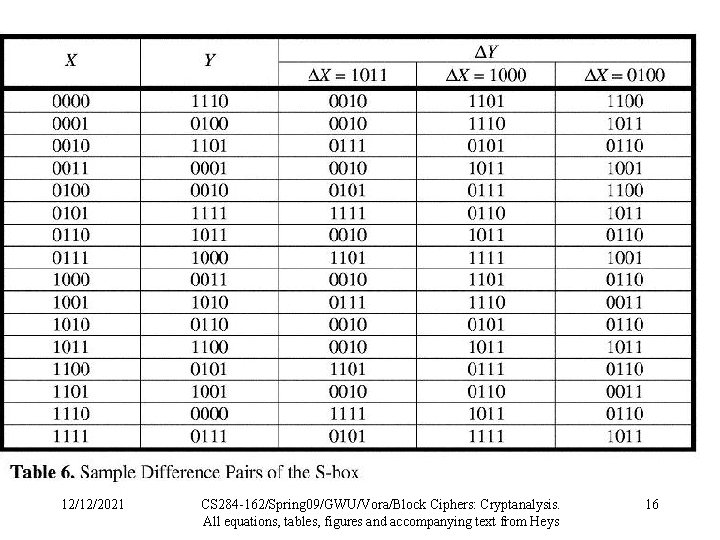
12/12/2021 CS 284 -162/Spring 09/GWU/Vora/Block Ciphers: Cryptanalysis. All equations, tables, figures and accompanying text from Heys 16
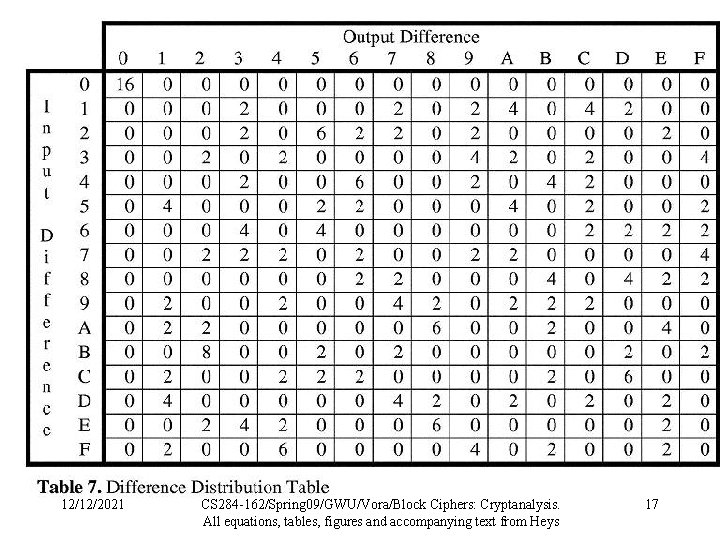
12/12/2021 CS 284 -162/Spring 09/GWU/Vora/Block Ciphers: Cryptanalysis. All equations, tables, figures and accompanying text from Heys 17
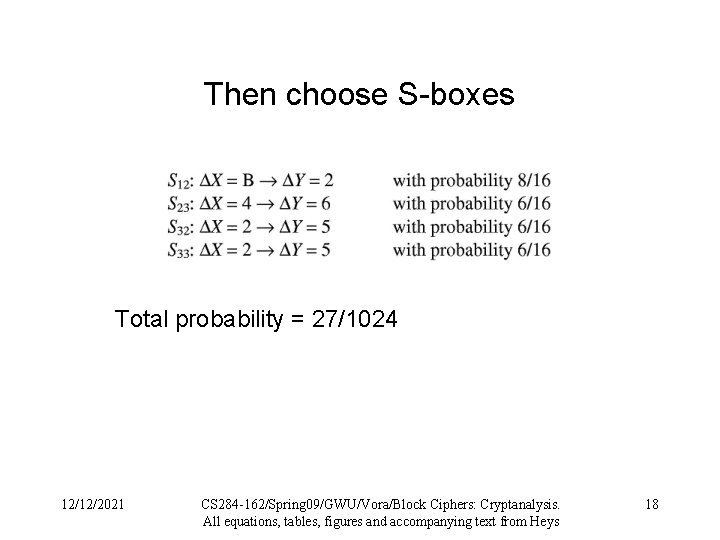
Then choose S-boxes Total probability = 27/1024 12/12/2021 CS 284 -162/Spring 09/GWU/Vora/Block Ciphers: Cryptanalysis. All equations, tables, figures and accompanying text from Heys 18
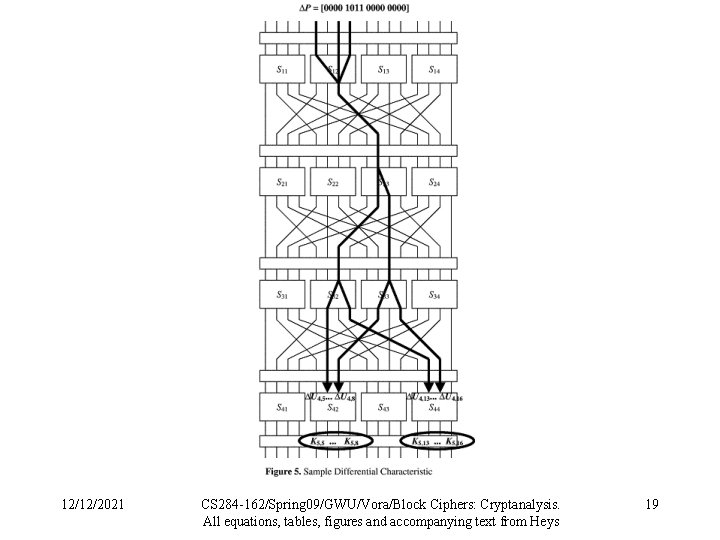
12/12/2021 CS 284 -162/Spring 09/GWU/Vora/Block Ciphers: Cryptanalysis. All equations, tables, figures and accompanying text from Heys 19
Try all target sub-keys • Try all sub-keys and see which one gives the correct input to the last round most often. • That’s the most likely sub-key. 12/12/2021 CS 284 -162/Spring 09/GWU/Vora/Block Ciphers: Cryptanalysis. All equations, tables, figures and accompanying text from Heys 20
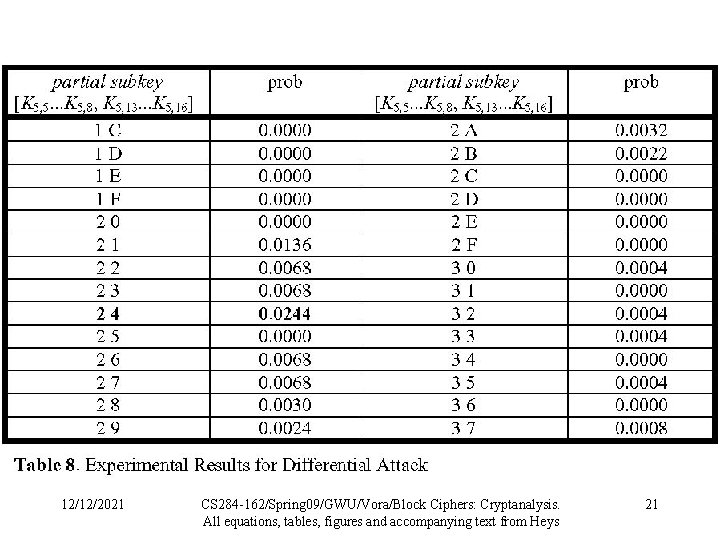
12/12/2021 CS 284 -162/Spring 09/GWU/Vora/Block Ciphers: Cryptanalysis. All equations, tables, figures and accompanying text from Heys 21
- Slides: 21