INTRODUCTION TO SOFTWARE SECURITY Dr Shahriar Bijani Shahed
INTRODUCTION TO SOFTWARE SECURITY Dr. Shahriar Bijani Shahed University Fall 2016
SLIDE REFERENCES Matt Bishop, Computer Security: Art and Science, the author homepage, 2004. Michael E. Whitman, Principles of Information Security: Chapter 1: Introduction to Information Security, 4/e, 2011. Chris Clifton, CS 526: Information Security course, Purdue university, 2010. 2
WHAT IS SECURITY? Security /sɪˈkjʊərɪti/ noun the state of being free from danger or threat. synonyms: certainty, safe future, assured future, safety, reliability, dependability, solidness, soundness 3
WHAT IS SECURITY? A successful organization should have multiple layers of security in place: � Physical security: to protect the physical items, objects, or areas of an organization from unauthorized access and misuse. � Personal security: to protect the (group of) authorized individual. � Operations security: to protect the details of a particular operation or series of activities. � Communications security: to protect an organization’s communications media, technology, and content. � Network security: to protect networking components, connections, and contents. � Information security 4
BASIC COMPONENTS An Information System is secure if it supports CIA: �Confidentiality Keeping data and resources hidden �Integrity Data integrity (integrity) Origin integrity (authentication) The CIA triangle �Availability Enabling access to data and resources 5
THE HISTORY OF INFORMATION SECURITY Began immediately following development first mainframes � Developed for code-breaking computations � During World War II � Multiple levels of security were implemented Physical controls Elementary � Mainly composed of simple document classification � Defending against physical theft, espionage, and sabotage 6
THE 1960 S Original communication by mailing tapes Advanced Research Project Agency (ARPA) � Examined feasibility of networked communications Larry Roberts developed ARPANET Plan � Link computers � Resource sharing � Link 17 Computer Research Centers � Cost 3. 4 M $ ARPANET is predecessor to the Internet 7
THE 1970 S AND 80 S ARPANET grew in popularity Potential for misuse grew Fundamental problems with ARPANET security � Individual remote sites were not secure from unauthorized users � Vulnerability of password structure and formats � No safety procedures for dial-up connections to ARPANET � Non-existent user identification and authorization to system 8
THE 1970 S AND 80… S Rand Report R-609 � Paper that started the study of computer security � Information Security as we know it began Scope of computer security grew from physical security to include: � Safety of data � Limiting unauthorized access to data � Involvement of personnel from multiple levels of an organization 9
THE 1990 S Networks of computers became more common Need to interconnect networks grew Internet became first demonstration of a global network of networks Initially based on de facto standards In early Internet deployments, security was treated as a low priority 10
2000 TO PRESENT Millions of computer networks communicate Many of the communication unsecured Ability to secure a computer’s data influenced by the security of every computer to which it is connected Growing threat of cyber attacks has increased the need for improved security 11
KEY INFORMATION SECURITY CONCEPTS Subjects / Objects Access Asset Control, Safeguard, or Countermeasure Exploit Exposure Hack Loss • • • Risk Vulnerability Threat Attack Compromise Security Blueprint 12
ATTACK An attack occurs when someone attempts to exploit a vulnerability Type of attacks � Passive (e. g. , eavesdropping) � Active (e. g. , password guessing, Do. S) A compromise occurs when an attack is successful 13
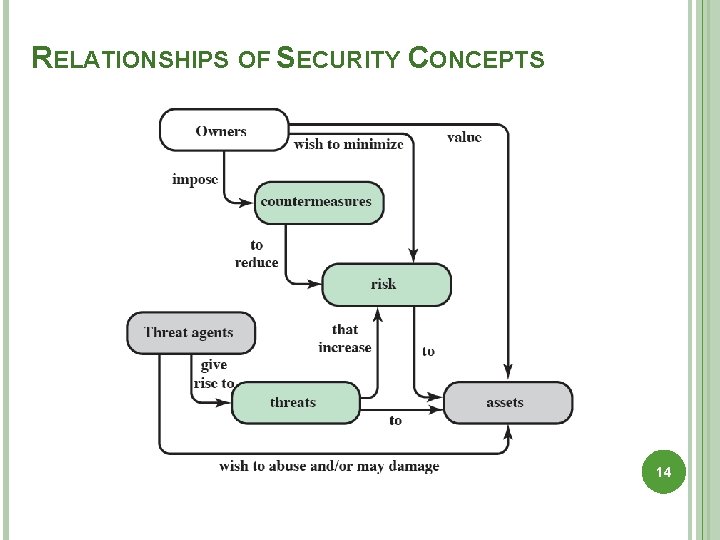
RELATIONSHIPS OF SECURITY CONCEPTS 14
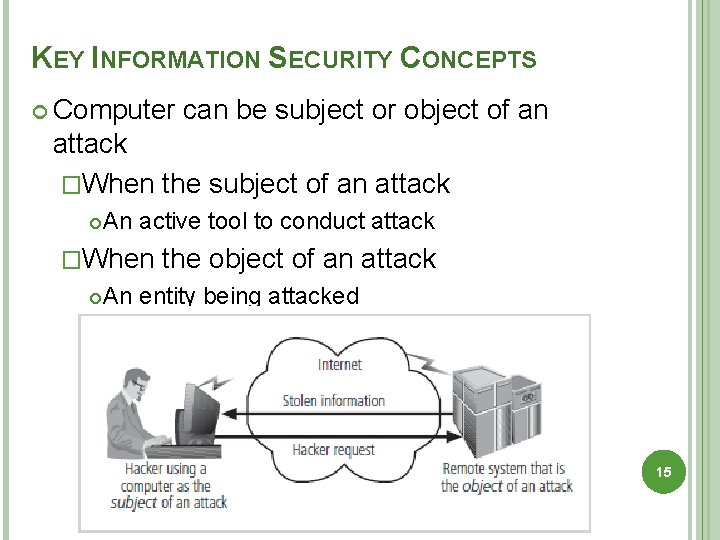
KEY INFORMATION SECURITY CONCEPTS Computer can be subject or object of an attack �When the subject of an attack An active tool to conduct attack �When the object of an attack An entity being attacked 15
INFORMATION SECURITY VS. ACCESS Perfect security is impossible Security is a process Security should be considered balance between protection and availability Must allow reasonable access, yet protect against threats 16
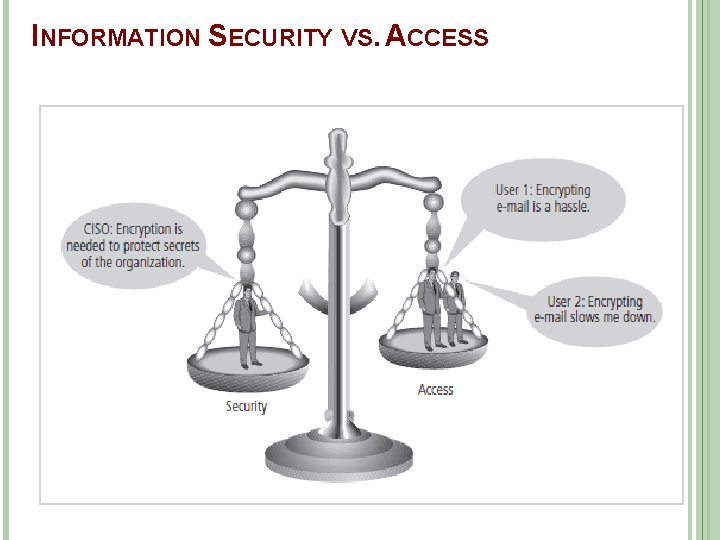
INFORMATION SECURITY VS. ACCESS 17
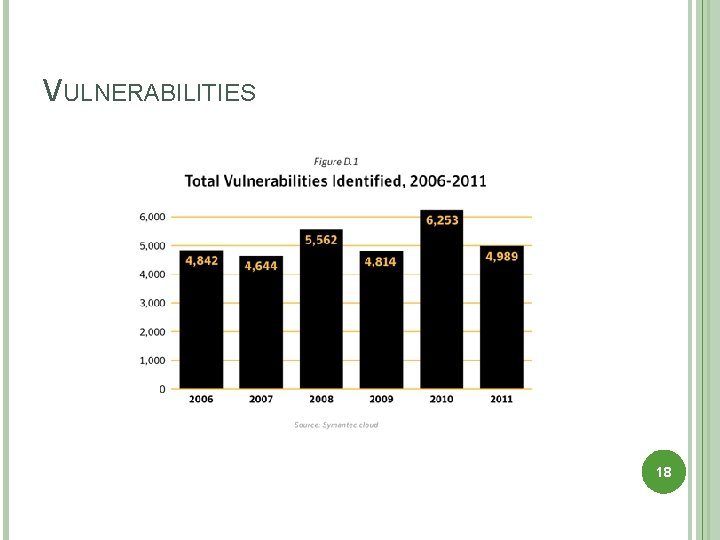
VULNERABILITIES 18
THREATS A threat is a potential violation of security. 19
CLASSES OF THREATS Interruption (Disruption) � interruption or prevention of correct operation � DOS attack: Denial of Service Interception / Disclosure � Unauthorized access to information � Snooping: the unauthorized interception of information Modification � An unauthorized party not only gains access to but modify an asset. � Masquerading or spoofing: an impersonation of one entity by another. Fabrication � An 20 unauthorized party inserts fake objects into the system.
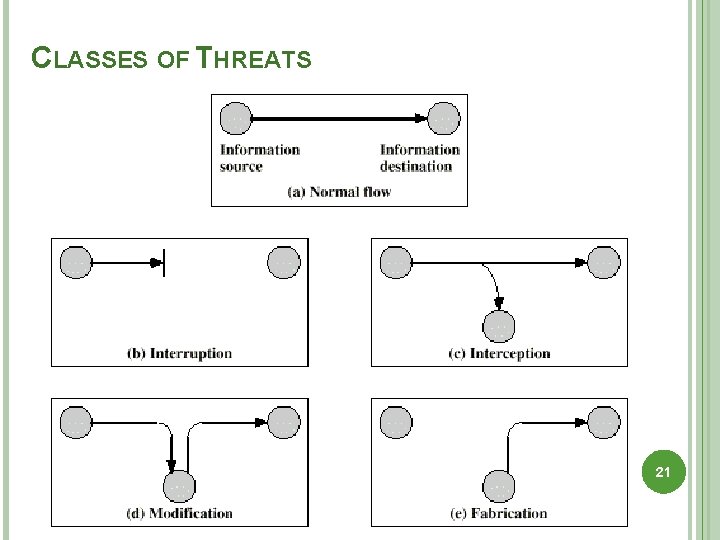
CLASSES OF THREATS 21
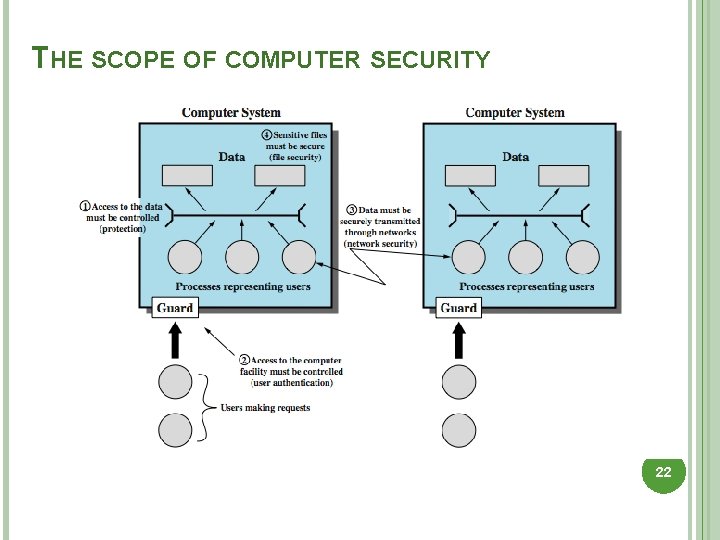
THE SCOPE OF COMPUTER SECURITY 22
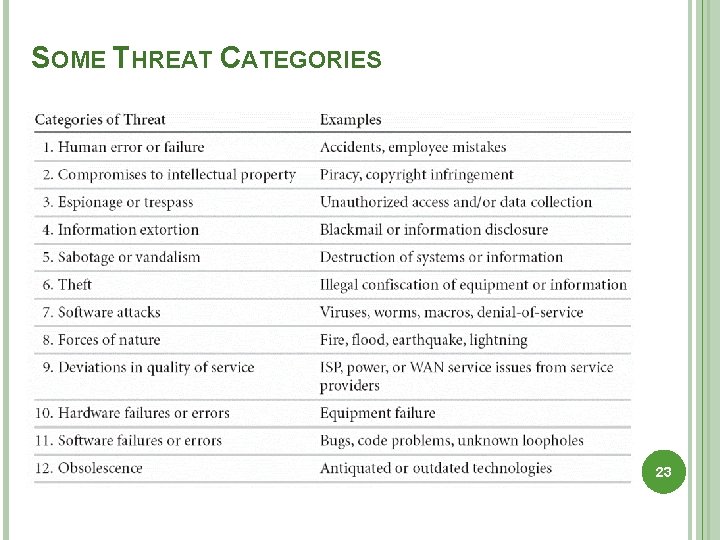
SOME THREAT CATEGORIES 23
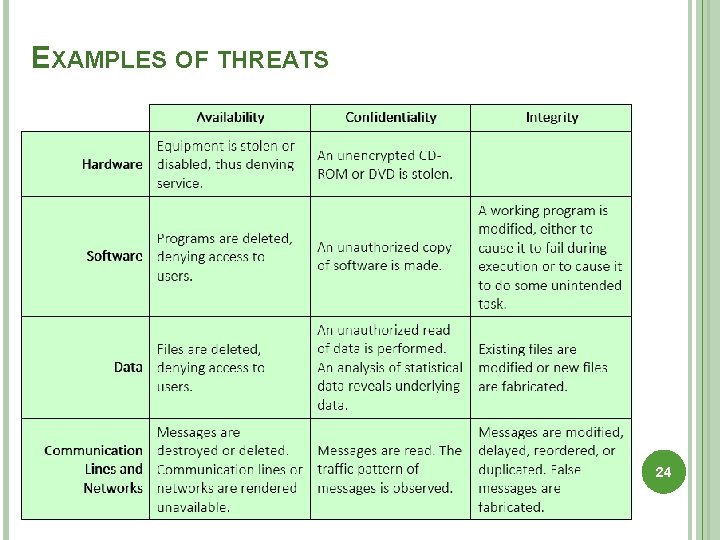
EXAMPLES OF THREATS 24
CHALLENGES OF COMPUTER SECURITY 1. 2. 3. 4. 5. 6. 7. 8. 9. Computer security is not simple One must consider potential (unexpected) attacks Must decide where to deploy mechanisms Involve algorithms and secret info (keys) A battle between attacker / admin It is not perceived on benefit until fails Requires constant monitoring Too often incorporated after the design is complete (not integral) Regarded as a barrier to using system 25
POLICIES AND MECHANISMS Policy says what is, and is not, allowed � This defines “security” for the site/system/etc. Mechanisms enforce policies Composition of policies � If policies conflict, inconsistencies may create security vulnerabilities 26
GOALS OF SECURITY Prevention( )پیﺸگیﺮی � Prevent Detection ( )ﺗﺸﺨیﺺ � Detect attackers from violating security policy attackers’ violation of security policy Recovery ( )ﺗﺮﻣیﻢ � Stop attack, assess and repair damage � Continue to function correctly even if attack succeeds 27
TRUST AND ASSUMPTIONS Underlie all aspects of security Policies � Unambiguously partition system states � Correctly capture security requirements Mechanisms � Assumed to enforce policy � Support mechanisms work correctly 28
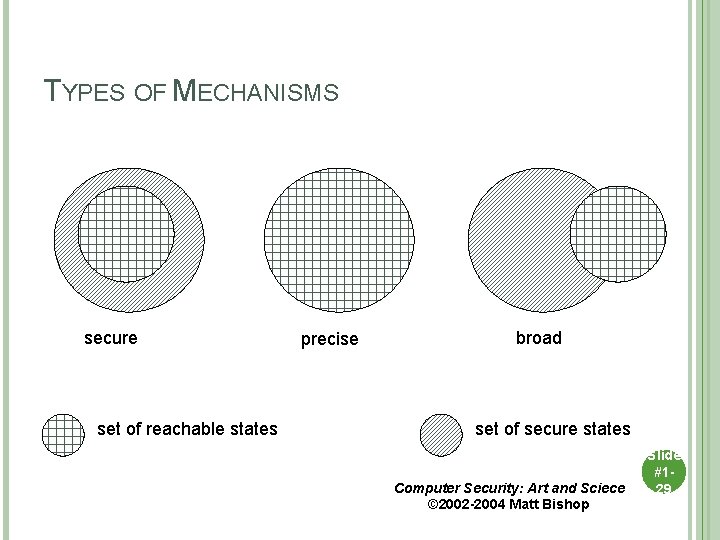
TYPES OF MECHANISMS secure set of reachable states precise broad set of secure states Computer Security: Art and Sciece © 2002 -2004 Matt Bishop Slide #129
ASSURANCE ( )ﺍﻃﻤیﻨﺎﻥ Assurance is a measure of how well the system meets its requirements Specification � Requirements analysis � Statement of desired functionality Design � How system will meet specification Implementation � Programs/systems that carry out design 30
OPERATIONAL ISSUES Cost-Benefit Analysis � Is it cheaper to prevent or recover? Risk Analysis � Should we protect something? � How much should we protect this thing? Laws and Customs � Are desired security measures illegal? � Will people do them? 31
HUMAN ISSUES Organizational Problems � Power and responsibility � Financial benefits People problems � Outsiders and insiders � Social engineering 32
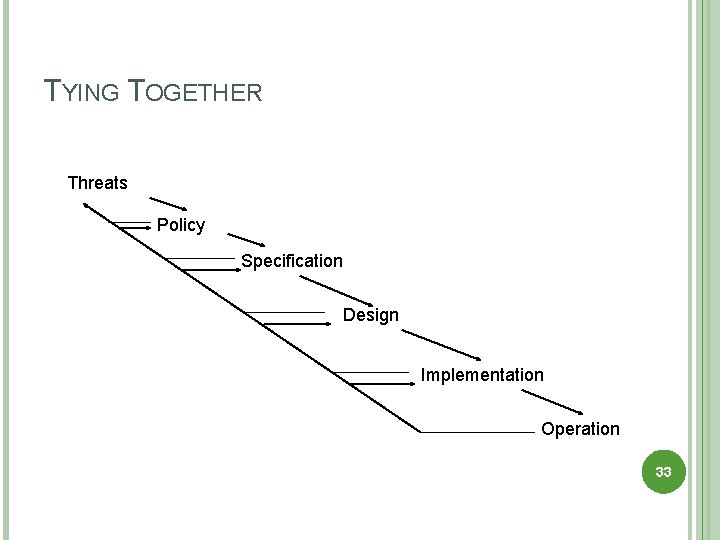
TYING TOGETHER Threats Policy Specification Design Implementation Operation 33
- Slides: 33