Identity and Access Management A Focus on Access







- Slides: 28

Identity and Access Management: A Focus on Access Assurance Infinigate IT Security Day Kurt Johnson VP Strategy & Corporate Development Courion Corporation

2

3
Regulation and Compliance 4 Sarbanes-Oxley Act (SOX) ~ PCAOB ~ SAS 94 ~ AICPA/CICA Privacy Framework ~ AICPA Suitable Trust Services Criteria ~ SEC Retention of Records, 17 CFR 210. 2 -06 ~ SEC Controls and Procedures, 17 CFR 240. 15 d-15 ~ SEC Reporting Transactions and Holdings, 17 CFR 240. 16 a-3 ~ Basel II ~ BIS Sound Practices for the Management and Supervision of Operational Risk ~ Gramm-Leach-Bliley Act (GLB) ~ Standards for Safeguarding Customer Info. , FTC 16 CFR 314 ~ Privacy of Consumer Financial Info. Rule ~ Safety and Soundness Standards, Appendix of 12 CFR 30 ~ FFIEC Info. Security ~ FFIEC Development Acquisition ~ FFIEC Business Continuity Planning ~ FFIEC Audit ~ FFIEC Management ~ FFIEC Operations ~ NASD ~ NYSE ~ Recordkeeping rule for securities exchanges, SEC 17 CFR 240. 17 a-1 ~ Records to be made by exchange members, SEC 17 CFR 240. 17 a-3 ~ Records to be preserved by exchange members, SEC 17 CFR 240. 17 a-4 ~ Recordkeeping, SEC 17 CFR 240. 17 Ad-6 ~ Record retention, SEC 17 CFR 240. 17 Ad-7 ~ HIPAA (Health Insurance Portability and Accountability Act) ~ HIPAA HCFA Internet Security Policy ~ NIST Introductory Resource Guide for [HIPAA] (800 -66) ~ CMS Core Security Requirements (CSR) ~ CMS Info. Security Acceptable Risk Safeguards (ARS) ~ CMS Info. Security Certification & Accreditation (C&A) ~ FDA Electronic Records; Electronic Signatures 21 CFR Part 11+D 1 ~ Federal Energy Regulatory Commission (FERC) ~ North American Electric Reliability Council (NERC) ~ VISA CISP (Cardholder Info. Security Program) ~ Mastercard SDP (Site Data Protection) Program ~ American Express DSS (Data Security Standard) ~ PCI DSS (Payment Card Industry Data Security Standard) ~ FTC ESIGN (Electronic Signatures in Global and National Commerce Act) ~ Uniform Electronic Transactions Act (UETA) ~ FISMA (Federal Info. Security Management Act) ~ FISCAM (Federal Info. System Controls Audit Manual) ~ FIPS Security Requirements for Cryptographic Modules 140 -2 ~ FIPS Guideline for the Analysis of LAN Security 191 ~ FIPS Application Profile for GILS 192 ~ Clinger-Cohen Act (Info. Technology Management Reform Act) ~ National Strategy to Secure Cyberspace ~ GAO Financial Audit Manual ~ DOD. . . Standard for Electronic Records Management Software. . . 5015 -2 ~ CISWG Report on the Best Practices Subgroup ~ CISWG Info. Security Program Elements ~ NCUA Guidelines for Safeguarding Member Info. 12 CFR 748 ~ IRS Revenue Procedure: Retention of books and records 97 -22 ~ IRS Revenue Procedure: Record retention: automatic data processing… 98 -25 ~ IRS Internal Revenue Code Section 501(c)(3) ~ Federal Rules of Civil Procedure ~ Uniform Rules of Civil Procedure ~ ISO 15489 -1 Info. and Documentation: Records mgmt. : General ~ ISO 15489 -2 Info. and Documentation: Records management: Guidelines ~ DIRKS: A Strategic Approach to Managing Business Info. ~ Sedona Principles Addressing Elec. Document Production ~ NIST. . . Principles and Practices for Securing IT Systems 800 -14 ~ NIST. . . Developing Security Plans for Federal Info. Systems 800 -18 ~ NIST Security Self-Assessment Guide. . . 800 -26 ~ NIST Risk Management Guide. . . 800 -30 ~ NIST Contingency Planning Guide. . . 800 -34 ~ NIST. . . Patch and Vulnerability Management Program 800 -40 ~ NIST Guidelines on Firewalls and Firewall Policy 800 -41 ~ NIST Security Controls for Federal Info. Sys 800 -53 ~ NIST. . . Mapping. . . Info. and. . . Systems to Security Categories 800 -60 ~ NIST Computer Security Incident Handling Guide 800 -61 ~ NIST Security Considerations in. . . Info. Sys Development 800 -64 ~ ISO 73: 2002 Risk management -- Vocabulary ~ ISO 1335 Info. technology – Guidelines for management of IT Security ~ ISO 17799: 2000 Code of Practice for Info. Security Management ~ ISO 27001: 2005. . . Info. Security Management Systems -- Requirements ~ IT Info. Library (ITIL) Planning to Implement Service Management ~ IT Info. Library (ITIL) ICT Infrastructure Management ~ IT Info. Library (ITIL) Service Delivery ~ IT Info. Library (ITIL) Service Support ~ IT Info. Library (ITIL) App. Management ~ IT Info. Library (ITIL) Security Management ~ COSO Enterprise Risk Management (ERM) Framework ~ Cobi. T 3 rd Edition ~ Cobi. T 4 th Edition ~ ISACA IS Standards, Guidelines, and Procedures for Auditing and Control. . . ~ NFPA 1600. . . Disaster/Emergency Management and Business Continuity. . . ~ Info. Security Forum (ISF) Standard of Good Practice ~ Info. Security Forum (ISF) Security Audit of Networks ~ A Risk Management Standard, jointly issued by AIRMIC, ALARM, and IRM ~ Business Continuity Institute (BCI) Good Practice Guidelines ~ IIA Global Technology Audit Guide - Info. Technology Controls ~ ISSA Generally Accepted Info. Security Principles (GAISP) ~ CERT Operationally Critical Threat, Asset & Vulnerability Evaluation (OCTAVE) ~ Cable Communications Privacy Act Title 47 § 551 ~ Telemarketing Sales Rule (TSR) amendment 16 CFR 310. 4(b)(3)(iv) ~ CAN SPAM Act ~ Children's Online Privacy Protection Act (COPPA) 16 CFR 312 ~ Driver's Privacy Protection Act (DPPA) 18 USC 2721 ~ Family Education Rights Privacy Act (FERPA) 20 USC 1232 ~ Privacy Act of 1974 5 USC 552 a ~ Telemarketing Sales Rule (TSR) 16 CFR 310 ~ Video Privacy Protection Act (VPPA) 18 USC 2710 ~ Specter. Leahy Personal Data Privacy and Security Act ~ AR Personal Info. Protection Act SB 1167 ~ AZ Amendment to Arizona Revised Statutes 13 -2001 HB 2116 ~ CA Info. Practice Act SB 1386 ~ CA General Security Standard for Businesses AB 1950 ~ CA Public Records Military Veteran Discharge Documents AB 1798 ~ CA OPP Recommended Practices on Notification of Security Breach ~ CO Prohibition against Using Identity Info. for Unlawful Purpose HB 1134 ~ CO Consumer Credit Solicitation Protection HB 1274 ~ CO Prohibiting Inclusion of Social Security Number HB 1311 ~ CT Requiring Consumer Credit Bureaus to Offer Security Freezes SB 650 ~ CT Concerning Nondisclosure of Private Tenant Info. HB 5184 ~ DE Computer Security Breaches HB 116 ~ FL Personal Identification Info. /Unlawful Use HB 481 ~ GA Consumer Reporting Agencies SB 230 ~ GA Public employees; Fraud, Waste, and Abuse HB 656 ~ HI Exempting disclosure of Social Security numbers HB 2674 ~ IL Personal Info. Protection Act HB 1633 ~ IN Release of Social Security Number, Notice of Security Breach SB 503 ~ LADatabase Security Breach Notification Law SB 205 Act 499 ~ ME To Protect ME Citizens from Identity Theft LD 1671 ~ MN Data Warehouses; Notice Required for Certain Disclosures HF 2121 ~ MO HB 957 ~ MT To Implement Individual Privacy and to Prevent Identity Theft HB 732 ~ NJ Identity Theft Prevention Act A 4001/S 1914 ~ NY A 4254, A 3492 [no title] ~ NV SB 347 [no title] ~ NC Security Breach Notification Law (Identity Theft Protection Act) SB 1048 ~ ND Personal Info. protection act SB 2251 ~ OH Personal Info. -- contact if unauthorized access HB 104 ~ RI Security Breach Notification Law H 6191 ~ TN Security Breach Notification SB 2220 ~ TX Identity Theft Enforcement and Protection Act SB 122 ~ VT Relating to Identity Theft HB 327 ~ VA Identity theft; penalty; restitution; victim assistance HB 872 ~ WA Notice of a breach of the security SB 6043 ~ EU Directive on Privacy and Electronic Communications 2002/58/EC ~ EU Directive on Data Protection 95/46/EC ~ US Department of Commerce EU Safe Harbor Privacy Principles ~. . . Consumer Interests in the Telecommunications Market Act No. 661 ~ Directive On Privacy And Electronic Communications 2002. 58. EC ~ OECD Technology Risk Checklist ~ OECD Guidelines on. . . Privacy and Transborder Flows of Personal Data ~ UN Guidelines for the Regulation of Computerized Personal Data Files (1990) ~ ISACA Cross-border Privacy Impact Assessment ~ The Combined Code on Corporate Governance ~ Turnbull Guidance on Internal Control, UK FRC ~ Smith Guidance on Audit Comm. Combined Code, UK FRC ~ UK Data Protection Act of 1998 ~ BS 15000 -1 IT Service Management Standard ~ BS 15000 -2 IT Service Management Standard - Code of Practice ~ Canada Keeping the Promise for a Strong Economy Act Bill 198 ~ Canada Personal Info. Protection and Electronic Documents Act ~ Canada Privacy Policy and Principles ~ Argentina Personal Data Protection Act ~ Mexico Federal Personal Data Protection Law ~ Austria Data Protection Act ~ Austria Telecommunications Act ~ Bosnia Law on Protection of Personal Data ~ Czech Republic Personal Data Protection Act ~ Denmark Act on Competitive Conditions and Consumer Interests ~ Finland Personal Data Protection Act ~ Finland Amendment of the Personal Data Act ~ France Data Protection Act ~ German Federal Data Protection Act ~ Greece Law on Personal Data Protection ~ Hungary Protection of Personal Data and Disclosure of Data of Public Interest ~ Iceland Protection of Privacy as regards the Processing of Personal Data ~ Ireland Data Protection Act ~ Ireland Data Protection Amendment 2003 ~ Italy Personal Data Protection Code ~ Italy Protection of Individuals with Regard to. . . Processing of Personal Data ~ Lithuania Law on Legal Protection of Personal Data ~ Luxembourg Data Protection Law ~ Netherlands Personal Data Protection Act ~ Poland Protection of Personal Data Act ~ Slovak Republic Protection of Personal Data in Info. Systems ~ Slovenia Personal Data Protection Act ~ South Africa Promotion of Access to Info. Act ~ Spain Organic law on the Protection of Personal Data ~ Sweden Personal Data Act ~ Swiss Federal Act on Data Protection ~ Australian Business Continuity Management Guide ~ Australia Spam Act of 2003 ~ Australia Privacy Amendment Act ~ Australia Telecommunications Act ~ Australia Spam Act 2003: A Practical Guide for Business ~ Hong Kong Personal Data (Privacy) Ordinance ~ India Info. Privacy Act ~ Japan Guidelines for Personal Data Protection in Electronic Commerce, ECOM ~ Japan Handbook Concerning Protection of Intl’Data, MITI ~ Japan Personal Info. Protection Act ~ Korea Act on the Promotion of Info. . Protection ~ Korea Act on the Protection of Personal Info. . by Public Agencies ~ Korea Use and Protection of Credit Info. Act ~ New Zealand Privacy Act ~ Taiwan Computer-Processed Personal Data Protection Law

5
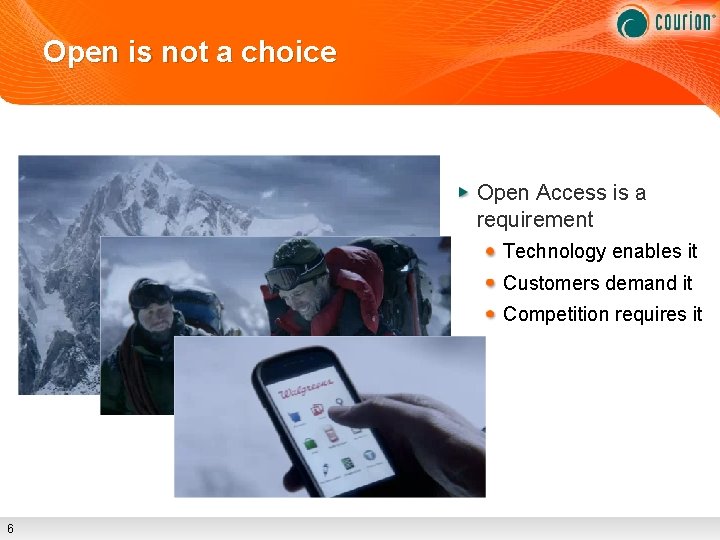
Open is not a choice Open Access is a requirement Technology enables it Customers demand it Competition requires it 6
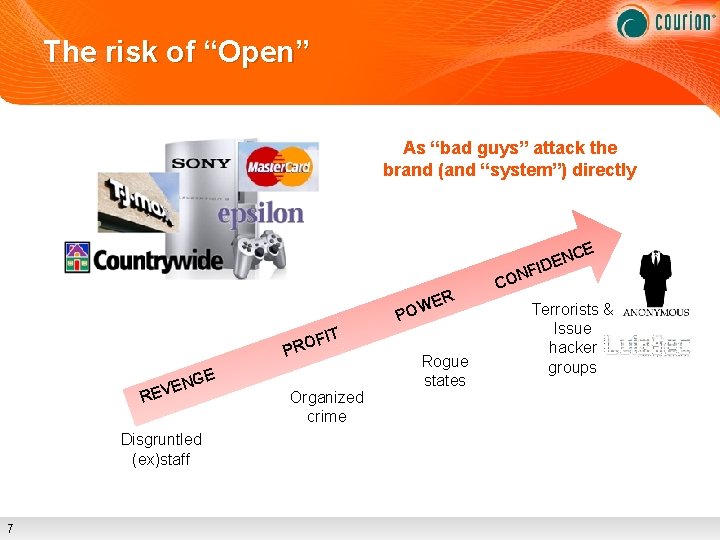
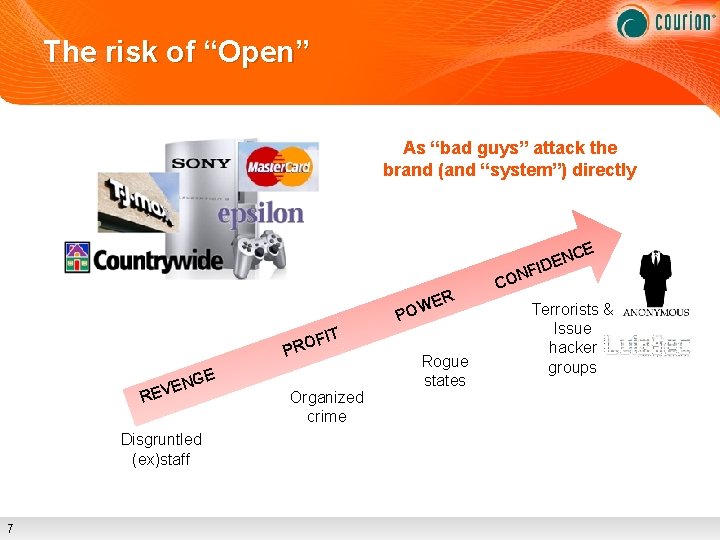
The risk of “Open” As “bad guys” attack the brand (and “system”) directly R WE O P T FI O R P GE N E EV R Disgruntled (ex)staff 7 Organized crime Rogue states CO CE N IDE NF Terrorists & Issue hacker groups
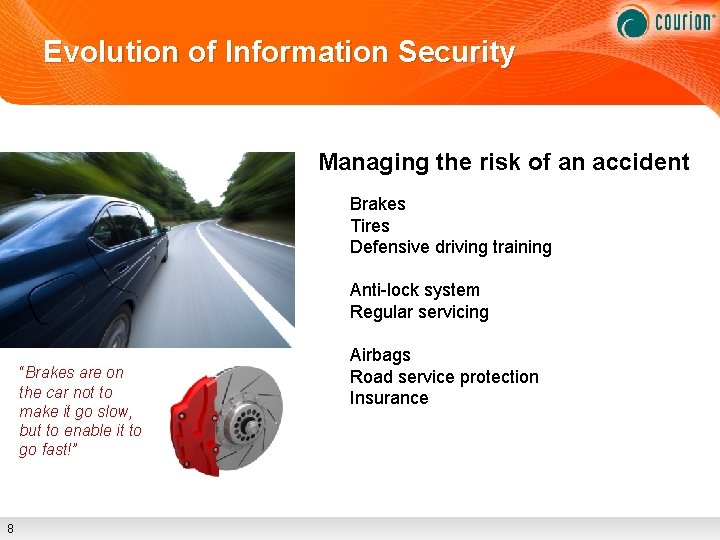
Evolution of Information Security Managing the risk of an accident Brakes Tires Defensive driving training Anti-lock system Regular servicing “Brakes are on the car not to make it go slow, but to enable it to go fast!” 8 Airbags Road service protection Insurance
Moving from security management to risk management Need to evolve beyond security management only First stage focused on identifying and managing risk There is an increasing need to not only identify and manage risk, but to… Understand risk Communicate risk effectively to the business Even as the risk factors are constantly changing First step is education of the business In partnership with the business Identity and access is critical part of this strategy 9
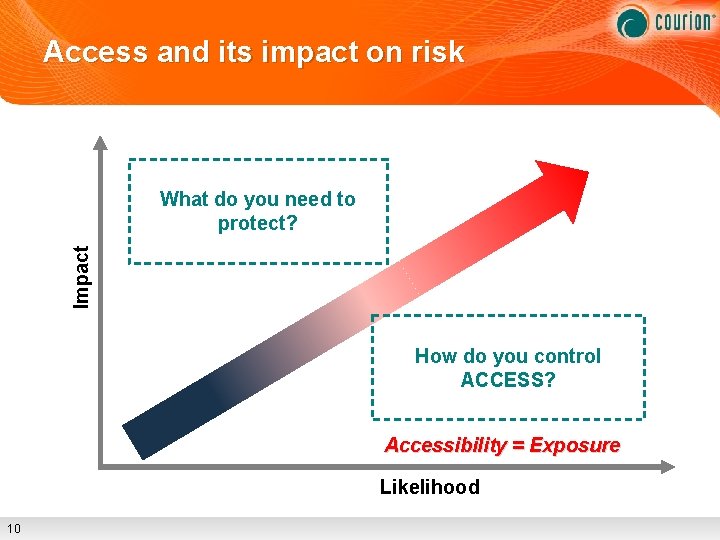
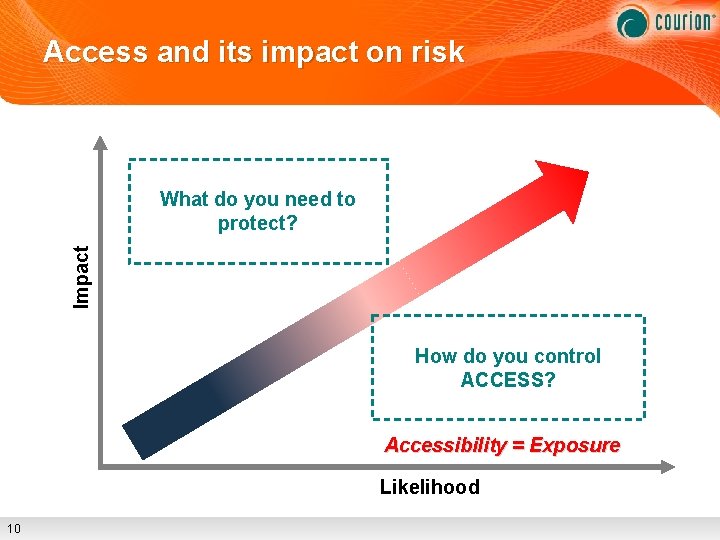
Access and its impact on risk Impact What do you need to protect? How do you control ACCESS? Accessibility = Exposure Likelihood 10
Is Your Critical Data at Risk? Excessive account privileges Exposure to fraud and misuse Employees and non-employees Misuse of the data Downloads, distribution, copying Zombie accounts Disgruntled ex-employees, back-door access Segregation of duties Toxic combinations Developer access to production data The most sensitive data sitting on public shares Share. Point sites, file shares, peer-to-peer networks Privileged access Administrative privileges with access to most sensitive data 11
Your Data in the Cloud Amazon Cloud Services License Agreement 10. Disclaimers THE SERVICE OFFERINGS ARE PROVIDED “AS IS. ” WE … MAKE NO REPRESENTATIONS OR WARRANTIES OF ANY KIND … THAT THE SERVICE OFFERINGS OR THIRD PARTY CONTENT WILL BE UNINTERRUPTED, ERROR FREE OF HARMFUL COMPONENTS, OR THAT ANY CONTENT, INCLUDING YOUR CONTENT …. WILL BE SECURE OR NOT OTHERWISE LOST OR DAMAGED… 12
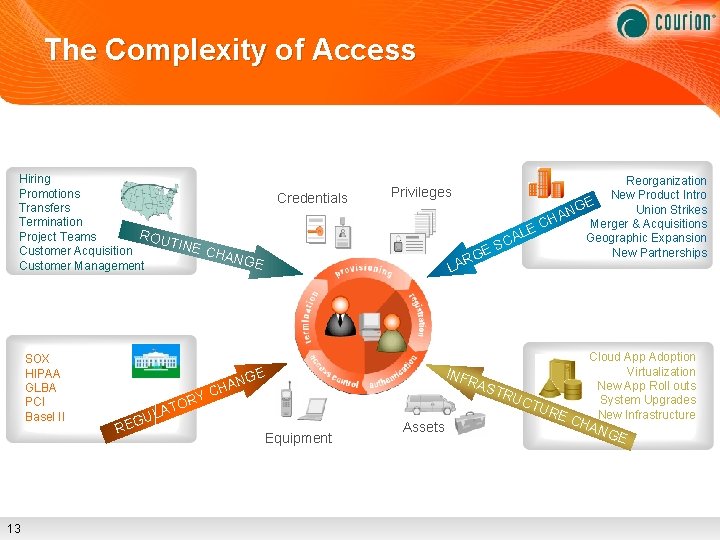
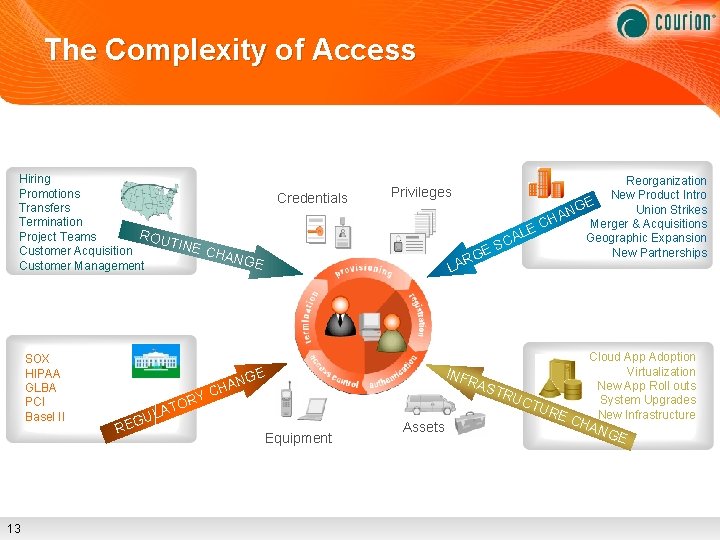
The Complexity of Access Hiring Promotions Transfers Termination ROU Project Teams TINE Customer Acquisition CHA NGE Customer Management SOX HIPAA GLBA PCI Basel II 13 RY O T A Credentials R LA GE N HA C UL G RE Reorganization New Product Intro GE Union Strikes N A H Merger & Acquisitions EC L Geographic Expansion CA S New Partnerships GE Privileges Equipment Assets Cloud App Adoption Virtualization INF RAS New App Roll outs TRU System Upgrades CTU RE New Infrastructure CH ANG E
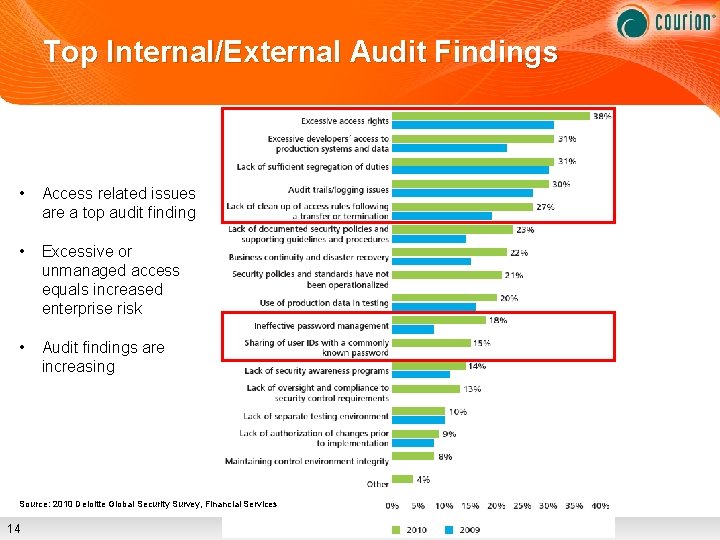
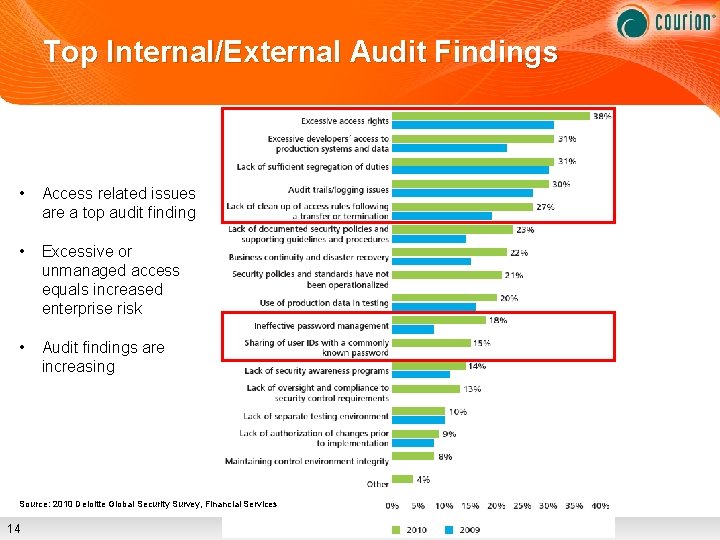
Top Internal/External Audit Findings • Access related issues are a top audit finding • Excessive or unmanaged access equals increased enterprise risk • Audit findings are increasing Source: 2010 Deloitte Global Security Survey, Financial Services 14
15

16

17

Access Assurance Internal & External Users Have the Right Access… Ensure the Right People… To the Right Resources… …and are doing the Right Things with it! 18
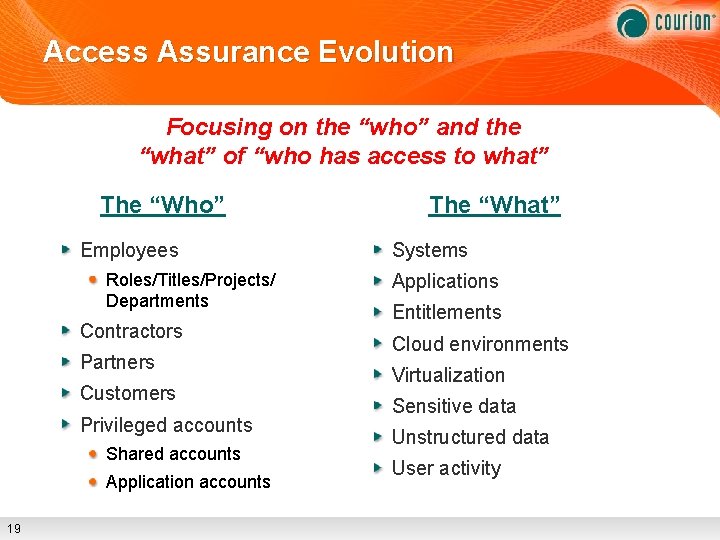
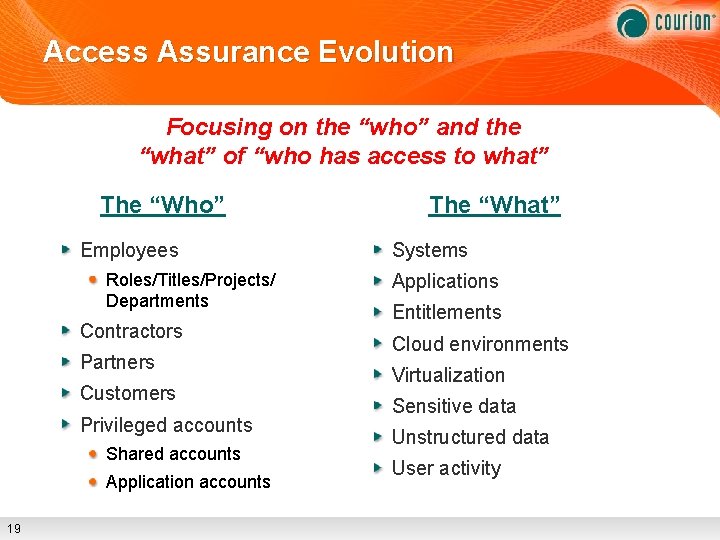
Access Assurance Evolution Focusing on the “who” and the “what” of “who has access to what” The “Who” Employees Roles/Titles/Projects/ Departments Contractors Partners Customers Privileged accounts Shared accounts Application accounts 19 The “What” Systems Applications Entitlements Cloud environments Virtualization Sensitive data Unstructured data User activity
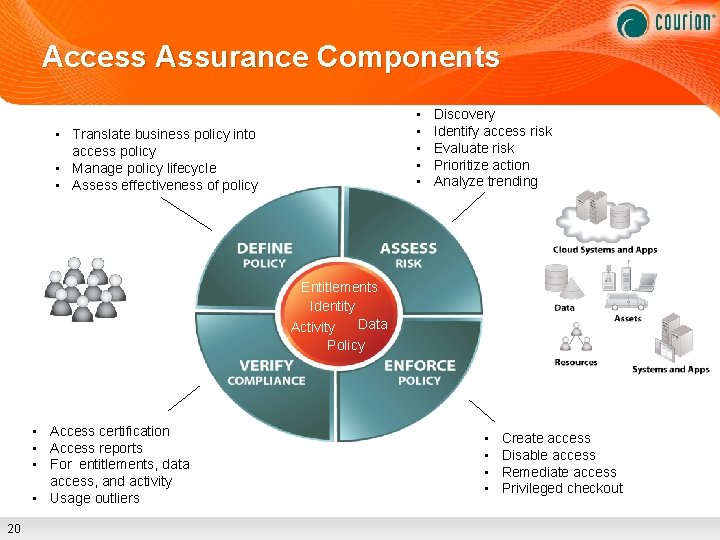
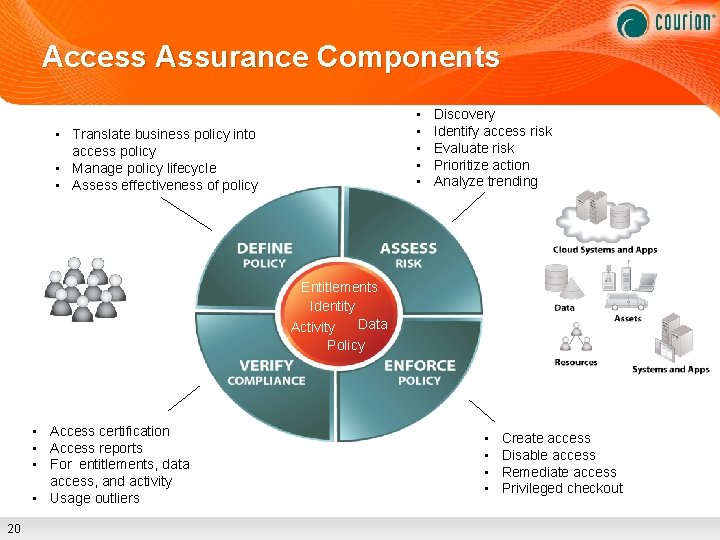
Access Assurance Components • • • Translate business policy into access policy • Manage policy lifecycle • Assess effectiveness of policy Discovery Identify access risk Evaluate risk Prioritize action Analyze trending Entitlements Identity Data Activity Policy • Access certification • Access reports • For entitlements, data access, and activity • Usage outliers 20 • • Create access Disable access Remediate access Privileged checkout
An IT View 21
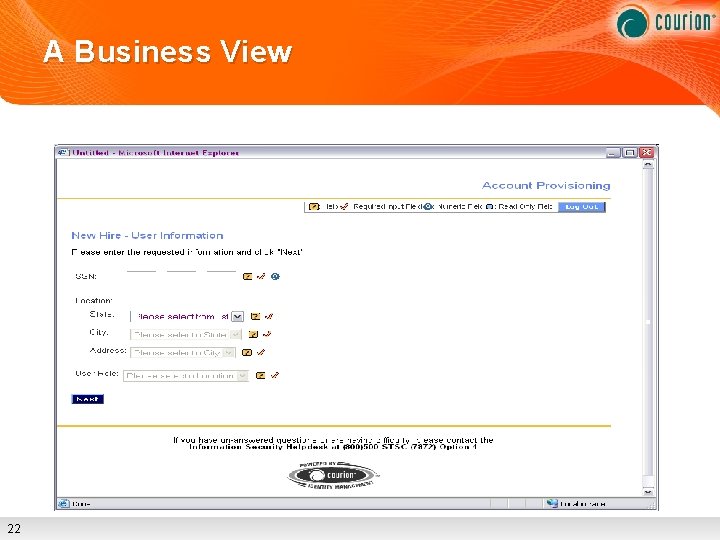
A Business View 22
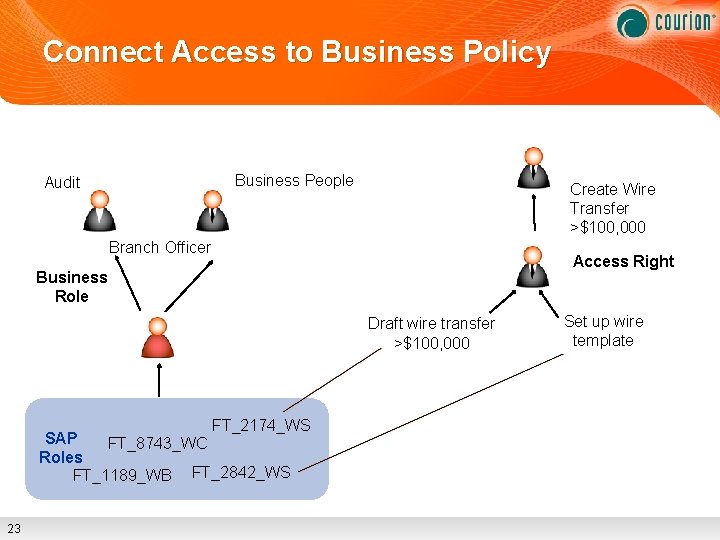
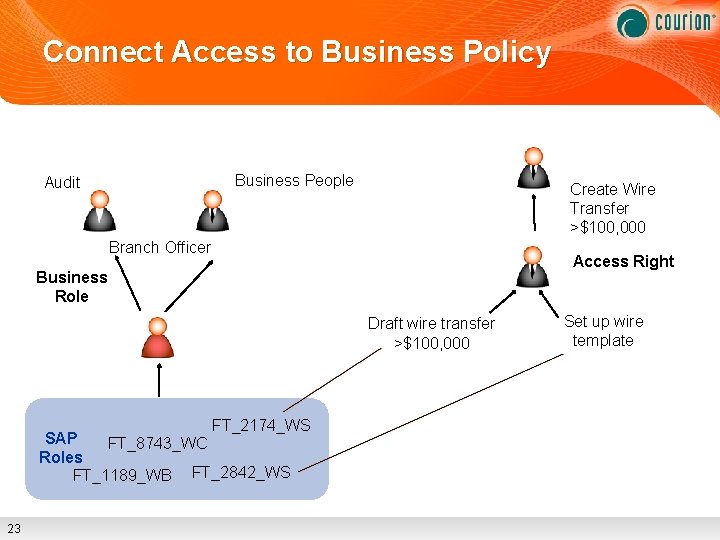
Connect Access to Business Policy Business People Audit Create Wire Transfer >$100, 000 Branch Officer Access Right Business Role Draft wire transfer >$100, 000 FT_2174_WS SAP FT_8743_WC Roles FT_1189_WB FT_2842_WS 23 Set up wire template
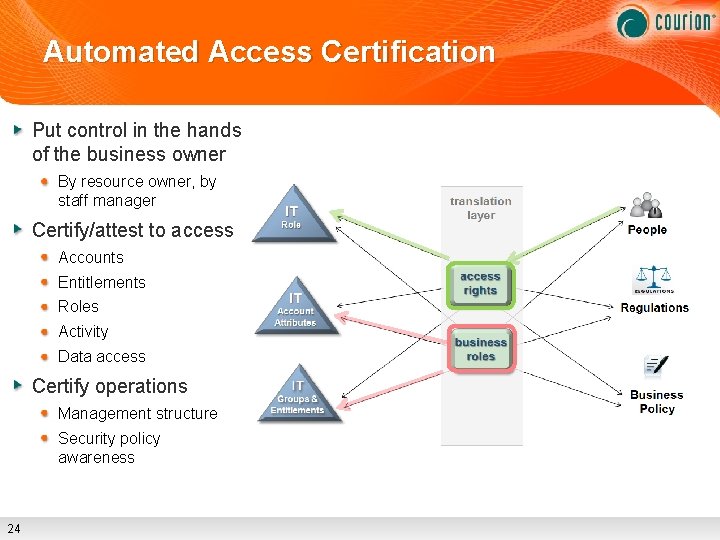
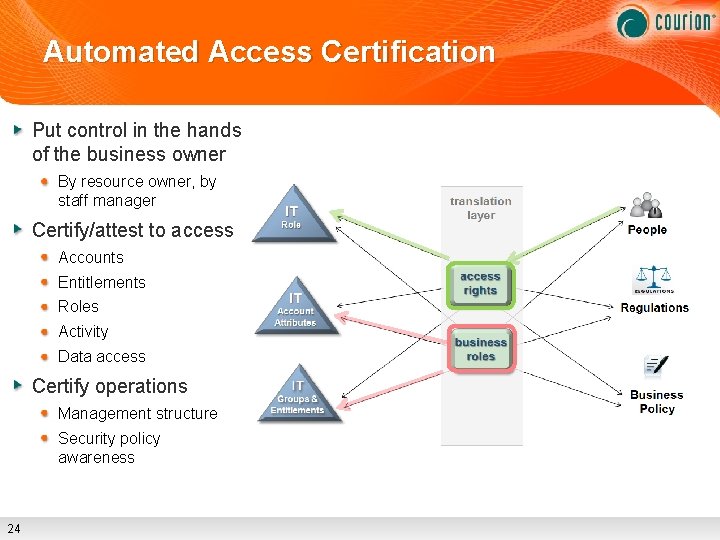
Automated Access Certification Put control in the hands of the business owner By resource owner, by staff manager Certify/attest to access Accounts Entitlements Roles Activity Data access Certify operations Management structure Security policy awareness 24
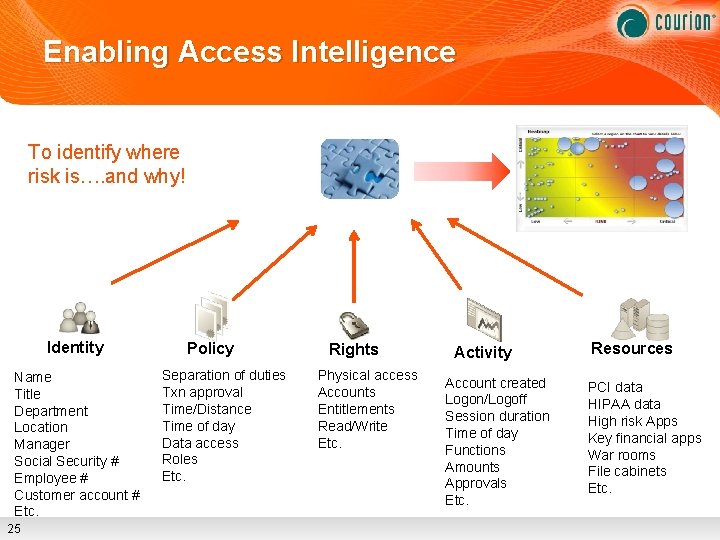
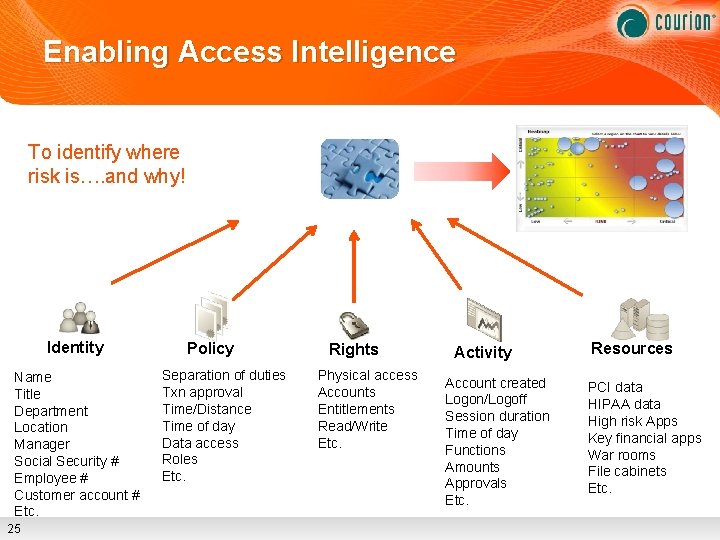
Enabling Access Intelligence To identify where risk is…. and why! Identity Name Title Department Location Manager Social Security # Employee # Customer account # Etc. 25 Policy Separation of duties Txn approval Time/Distance Time of day Data access Roles Etc. Rights Physical access Accounts Entitlements Read/Write Etc. Activity Account created Logon/Logoff Session duration Time of day Functions Amounts Approvals Etc. Resources PCI data HIPAA data High risk Apps Key financial apps War rooms File cabinets Etc.
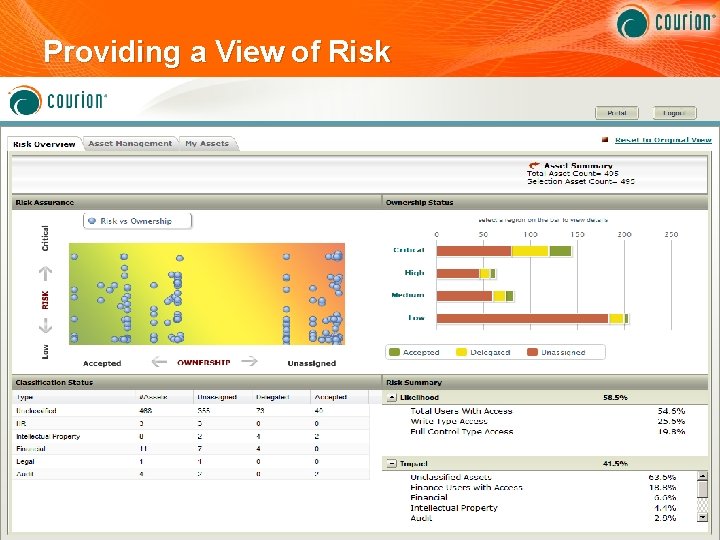
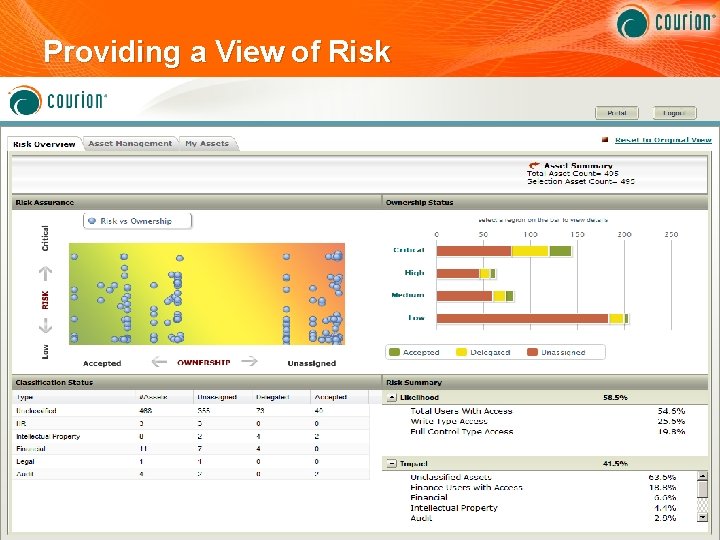
Providing a View of Risk 26
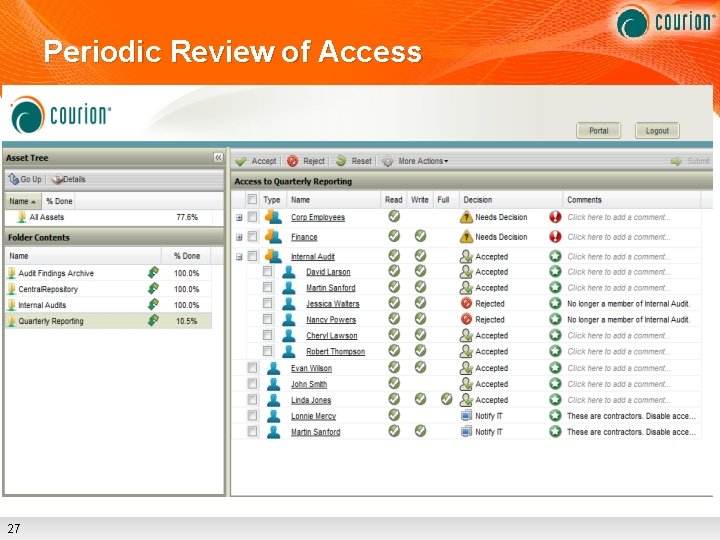
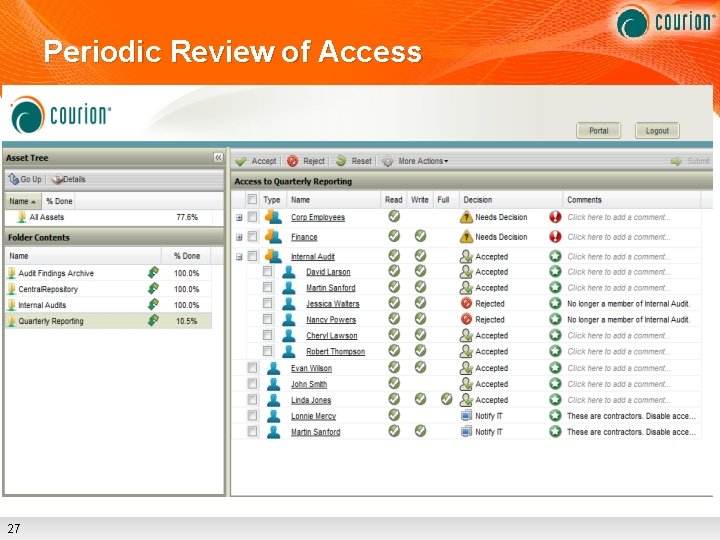
Periodic Review of Access 27
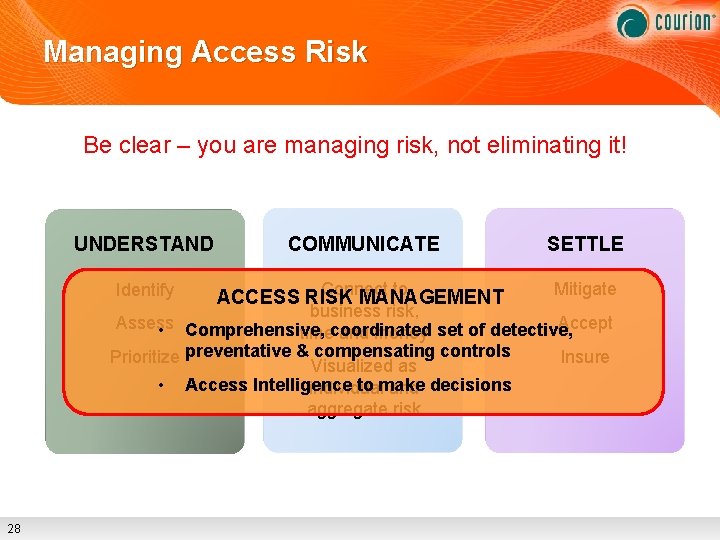
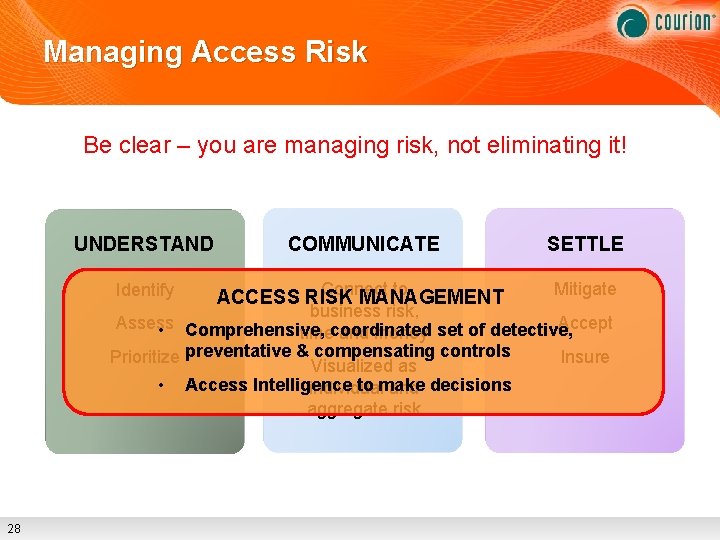
Managing Access Risk Be clear – you are managing risk, not eliminating it! UNDERSTAND COMMUNICATE SETTLE Identify Connect to ACCESS RISK MANAGEMENT Mitigate business risk, Accept Assess • Comprehensive, timecoordinated and money set of detective, Insure Prioritize preventative & compensating controls Visualized as • Access Intelligence to make individual and decisions aggregate risk 28