Mobile Payments Mobile Identity Management Mobile Signatures Copyright
Mobile Payments Mobile Identity Management Mobile Signatures © Copyright Valimo Wireless Ltd, 2006
Valimo Wireless § …is a Finnish company specialized in developing software for performing and securing transactions in fixed and mobile networks § …main customer segments are telecom operators, large enterprises and service providers in finance, government, health care, betting and media
Topics § Need § Key Drivers for Mobile Signature Services - Bank - Mobile Operator - Government § Short Overview of the ETSI — MSS Concept § How the SIM Card and Mobile Network Operator's Infrastructure Plays a Key Role § User experience
Urgent need! § Industry has a demand to know the user and get his approval for actions. § We must be sure that the user is who he claims to be. § We must get user’s approval in a way that user can not claim afterwards that it did not happen. § Needs to support mass-market.
Key Stakeholders § Bank § Internet Bank & e. Payment Services § Customer base § Mobile Operator § Network Infrastucture § Subscribers § Government § More and more public services moving to Web. Strong authentication a must! § Consumer § User of the value added services
Valimo Need & Key Drivers Banks
VISA & Mastercard fraud figures § 40 million credit cards hacked in 2005 § Breach at 3 rd party payment processor affects 22 million VISA cards and 14 million Master. Cards § 70% of the losses caused by use of counterfeit cards § e-Commerce is the next target Source: Jani Kallio, Security Manager, Luottokunta Eurocard Oy, Finland
Online fraud figures in UK § 2004 frauds £ 5 million § 2005 £ 30 million § 2006 EMV launched, POS card frauds going rapidly down, Online services on target § Latest news (BBC 1 Nov. 7 th): Online frauds already doubled comparing to 2005 § What it will be at the end of 2006? Source: FSA & BBC, UK
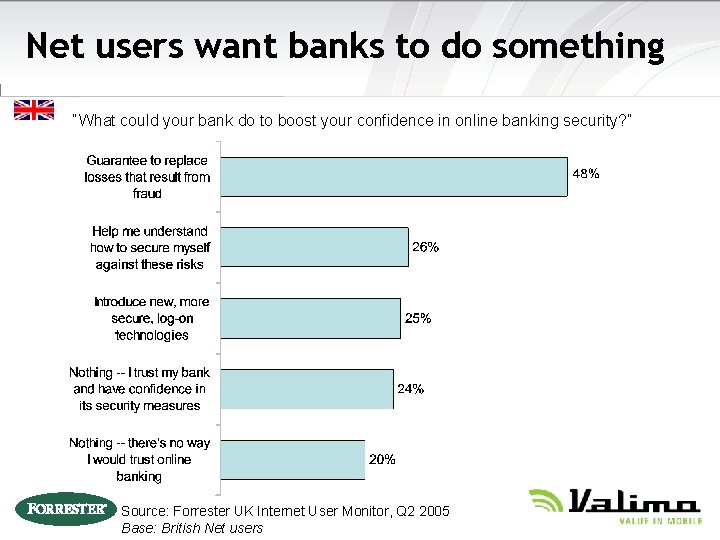
Net users want banks to do something “What could your bank do to boost your confidence in online banking security? ” Source: Forrester UK Internet User Monitor, Q 2 2005 Base: British Net users
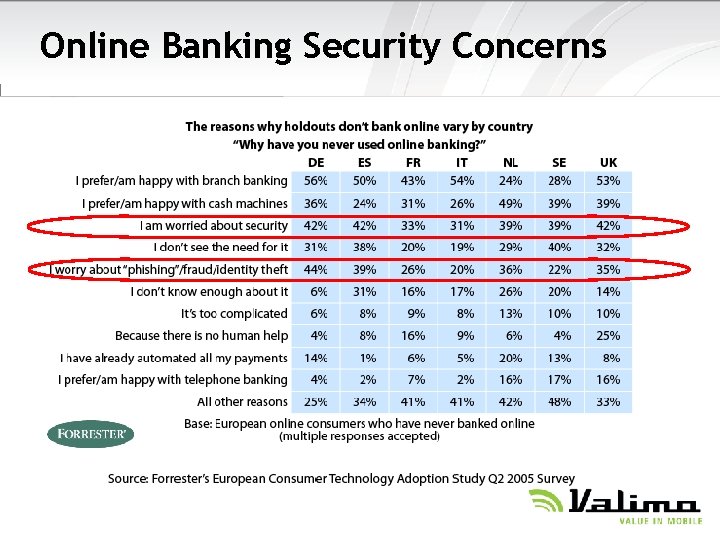
Online Banking Security Concerns
Key Drivers, Banks The mobile phone is a trusted device that provides anywhere, anytime access to confidential, personal and business content and guarantees integrity and non-repudiation of electronic transactions
Key Drivers, Banks § Authentication through different channel than the service § Makes phishing and Man-in-the-Middle impossible

Key Drivers, Banks § Legally binding transactions and agreements by mobile phone. § (non-repudiation)
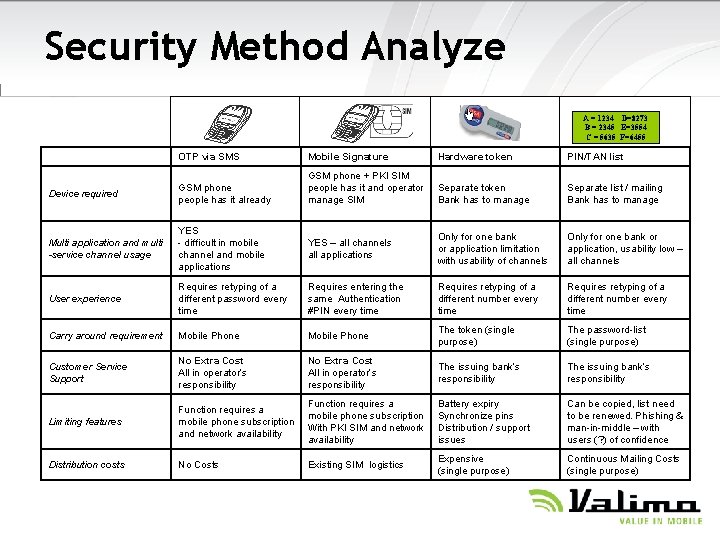
Security Method Analyze A = 1234 D=8273 B = 2345 E=3554 C = 5635 F=6455 OTP via SMS Mobile Signature Hardware token PIN/TAN list Device required GSM phone people has it already GSM phone + PKI SIM people has it and operator manage SIM Separate token Bank has to manage Separate list / mailing Bank has to manage Multi application and multi -service channel usage YES - difficult in mobile channel and mobile applications YES – all channels all applications Only for one bank or application limitation with usability of channels Only for one bank or application, usability low – all channels User experience Requires retyping of a different password every time Requires entering the same Authentication #PIN every time Requires retyping of a different number every time Carry around requirement Mobile Phone The token (single purpose) The password-list (single purpose) Customer Service Support No Extra Cost All in operator’s responsibility The issuing bank’s responsibility Limiting features Function requires a mobile phone subscription and network availability Function requires a mobile phone subscription With PKI SIM and network availability Battery expiry Synchronize pins Distribution / support issues Can be copied, list need to be renewed. Phishing & man-in-middle – with users (? ) of confidence Distribution costs No Costs Existing SIM logistics Expensive (single purpose) Continuous Mailing Costs (single purpose)
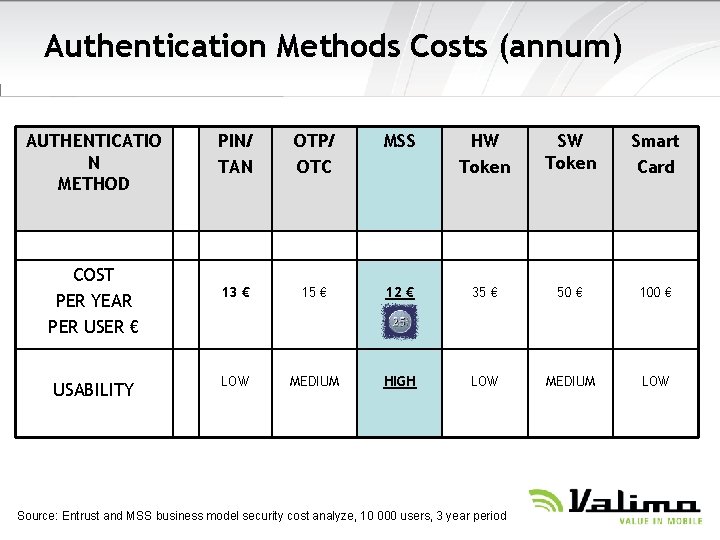
Authentication Methods Costs (annum) AUTHENTICATIO N METHOD COST PER YEAR PER USER € USABILITY PIN/ TAN OTP/ OTC MSS HW Token Smart Card 13 € 15 € 12 € 35 € 50 € 100 € LOW MEDIUM HIGH LOW MEDIUM LOW Source: Entrust and MSS business model security cost analyze, 10 000 users, 3 year period
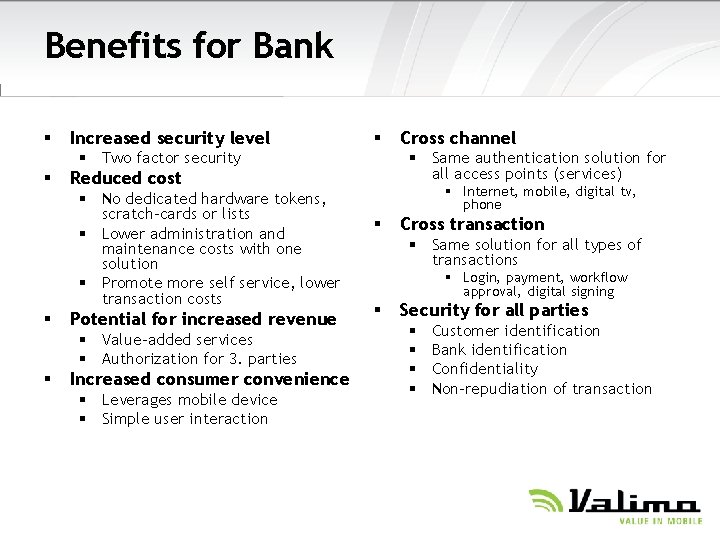
Benefits for Bank § Increased security level § § Two factor security § § Potential for increased revenue § Value-added services § Authorization for 3. parties § § Same authentication solution for all access points (services) Reduced cost § No dedicated hardware tokens, scratch-cards or lists § Lower administration and maintenance costs with one solution § Promote more self service, lower transaction costs Increased consumer convenience § Leverages mobile device § Simple user interaction Cross channel § Internet, mobile, digital tv, phone § Cross transaction § Same solution for all types of transactions § Login, payment, workflow approval, digital signing § Security for all parties § § Customer identification Bank identification Confidentiality Non-repudiation of transaction
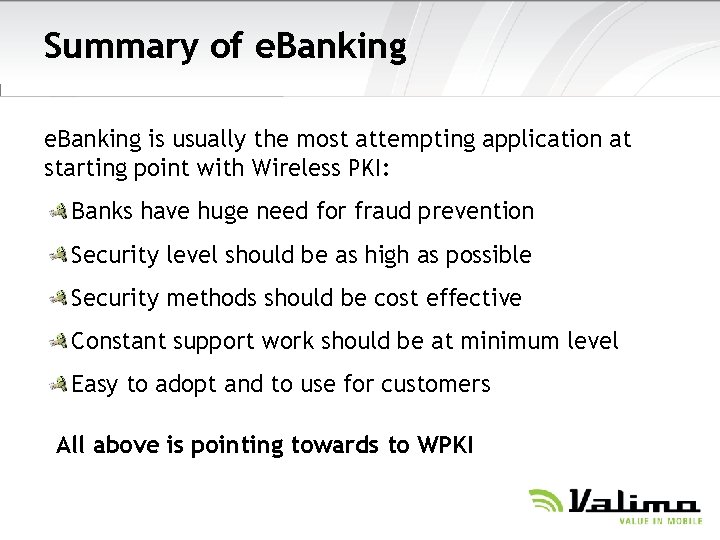
Summary of e. Banking is usually the most attempting application at starting point with Wireless PKI: Banks have huge need for fraud prevention Security level should be as high as possible Security methods should be cost effective Constant support work should be at minimum level Easy to adopt and to use for customers All above is pointing towards to WPKI
Valimo Need & Key Drivers Mobile Operators
Need! § § After recent years heavy investments to 3 G licenses/network development and heavy price competition, operators are in deep need of new revenue streams New innovative value added services are the only way to generate such streams Services must support mass-market most widely, meaning corporate, governmental and financial market applications At the same time, number transferability has become a big influencer around Western Countries, causing rising churn rate

Key Drivers, Mobile Operators § Mobile operator needs to offer many new high security services § Business and consumer customers
Key Drivers, Mobile Operators § SIM-card with digital keys linked to a mobile signature service may reduce frequent changes of a mobile operator
Mobile PKI § § Public Key Infrastructure is a ideal technical solution for this need. Everyone has Mobile Phone – implementing PKI on SIM/UICC card is the ideal solution. PKI on Mobile Terminal is called Wireless PKI or WPKI and sometimes Mobile PKI is just an enabler to services.
Valimo Need & Key Drivers Government
Key Drivers, Government § All possible Governmental & Municipal services will be on Web § Any service containing sensitive information (financial, health, etc. ) must have strong authentication in place § National level e. ID is/will be based on PKI solution
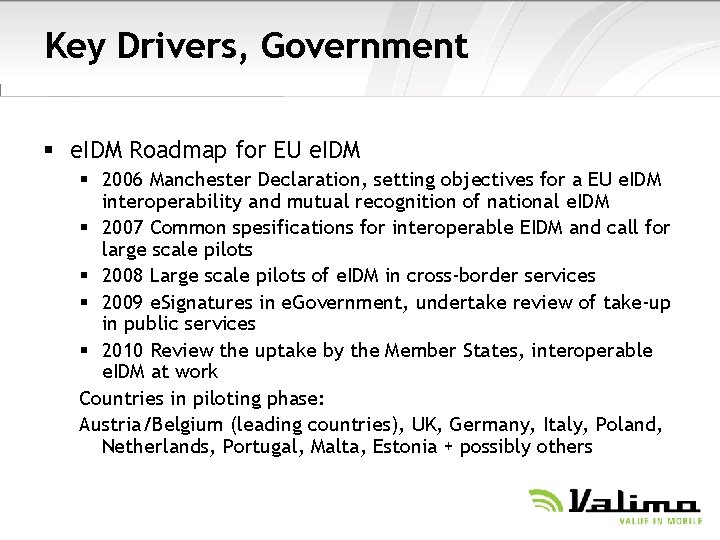
Key Drivers, Government § e. IDM Roadmap for EU e. IDM § 2006 Manchester Declaration, setting objectives for a EU e. IDM interoperability and mutual recognition of national e. IDM § 2007 Common spesifications for interoperable EIDM and call for large scale pilots § 2008 Large scale pilots of e. IDM in cross-border services § 2009 e. Signatures in e. Government, undertake review of take-up in public services § 2010 Review the uptake by the Member States, interoperable e. IDM at work Countries in piloting phase: Austria/Belgium (leading countries), UK, Germany, Italy, Poland, Netherlands, Portugal, Malta, Estonia + possibly others
Valimo Mobile PKI ETSI MSS (Mobile Signature Service)
Mobile PKI § § Public Key Infrastructure is a ideal technical solution for this need. Everyone has Mobile Phone – implementing PKI on SIM/UICC card is the ideal solution. PKI on Mobile Terminal is called Wireless PKI or WPKI and sometimes Mobile PKI is just an enabler to services.
Mobile PKI § § § In year 2000 Valimo started to develop Mobile Signing solution By that time, no standards for interfaces were existing, solutions were only proprietary First commercial deliveries 2002 ETSI published MSS Standards ETSI 102 206 ETSI 102 207 ETSI 102 204 ETSI 102 203 Now all running systems are upgraded to ETSI Standards based solution
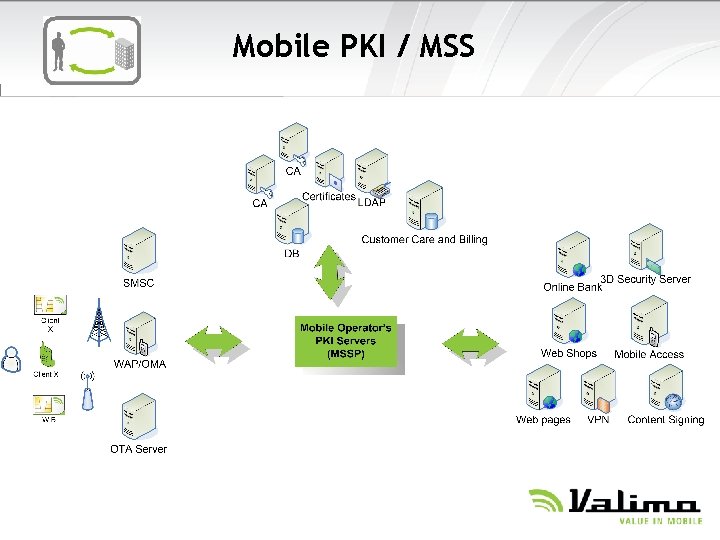
Mobile PKI / MSS
Simplicity in Authentication § All You need for secure authentication is one SIMcard. Insert your Authentication PIN code: ****
Legally Binding § Legally binding agreements by mobile phone. § The non-repudiation § Official Identity (issued by Government with Mobile Operators) § Or Corporate Identity (issued by Corporate with Mobile Operator) Insert your Signature PIN code: ******
Hiding Mobile PKI Complexity § Simultaneous support for multiple Certificate Authorities § No technology or policy constraints
ETSI MSSP (Mobile Signature Service Provider) is based on four entities: - Home Entity (has connection to individual clients) - Acquiring Entity (acquires signatures) - Routing Entity (handles roaming in multiple operator environments) - Verification Entity may be as part of first two. All above may be combined together or alternatively be separate entities (like for example a bank having Acquiring Entity which connects to operator’s Home Entity) § § ETSI Standards include interfaces between entities and for integrating any application to use mobile signature service
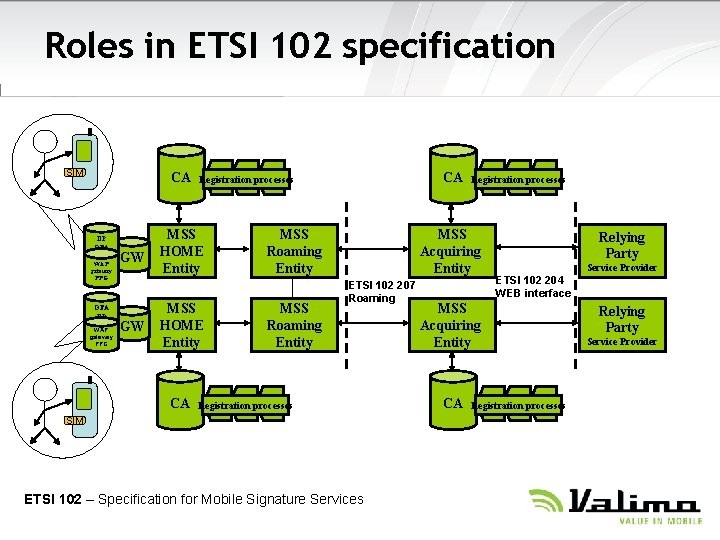
Roles in ETSI 102 specification SIM CA DP OTA WAP gateway PPG OTA DP WAP gateway PPG GW GW MSS HOME Entity CA CA Registration processes MSS Roaming Entity Registration processes MSS Acquiring Entity ETSI 102 207 Roaming Registration processes SIM ETSI 102 – Specification for Mobile Signature Services Relying Party Service Provider ETSI 102 204 WEB interface MSS Acquiring Entity CA Registration processes Relying Party Service Provider
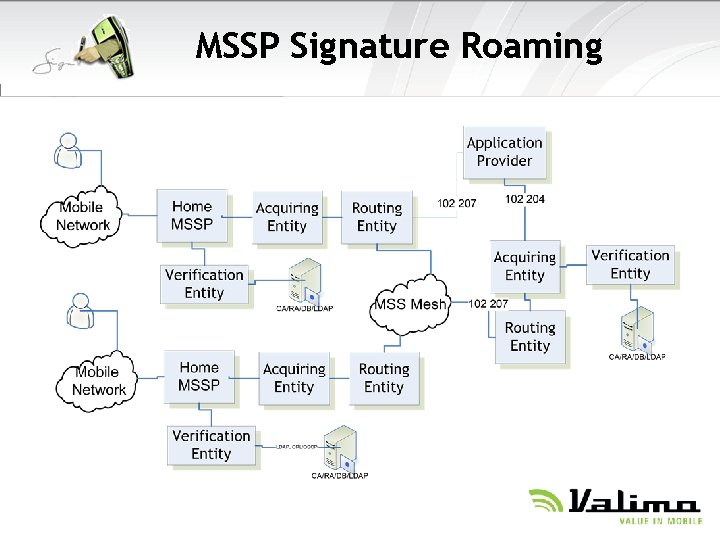
MSSP Signature Roaming
Valimo Mobile Operator’s Key Role
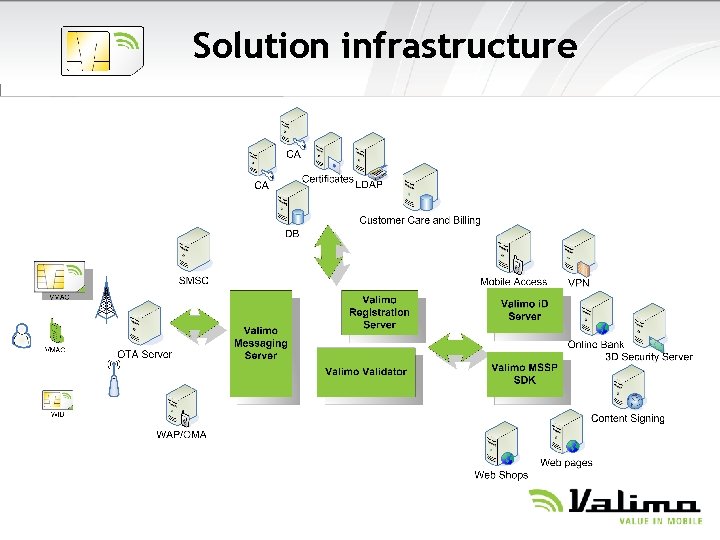
Solution infrastructure
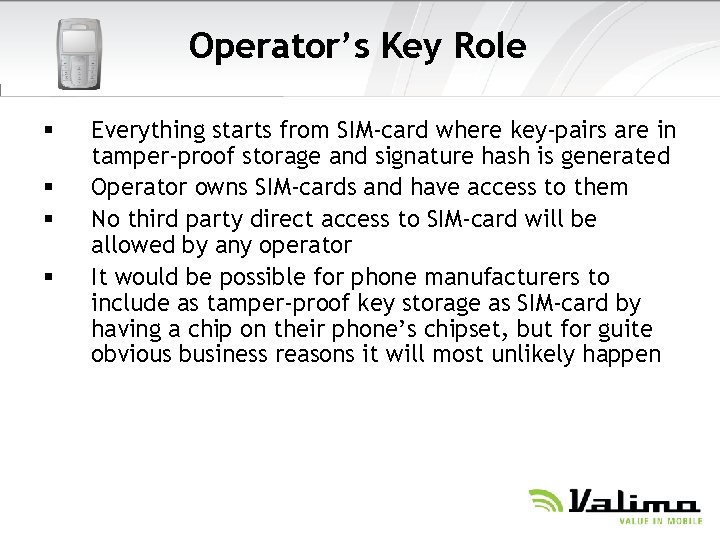
Operator’s Key Role § § Everything starts from SIM-card where key-pairs are in tamper-proof storage and signature hash is generated Operator owns SIM-cards and have access to them No third party direct access to SIM-card will be allowed by any operator It would be possible for phone manufacturers to include as tamper-proof key storage as SIM-card by having a chip on their phone’s chipset, but for guite obvious business reasons it will most unlikely happen
Issuing § SIM/UICC card containing Private Keys are normally issued by Mobile Operators § Identity is based on Certificates issued by CAs. § CA can be § § Official Governmental CA Mobile Operator CA Corporate CA 3 rd party CA § Certificates are not on SIM/UICC, they are on CA’s directory on the network.
Valimo User experience e. Banking
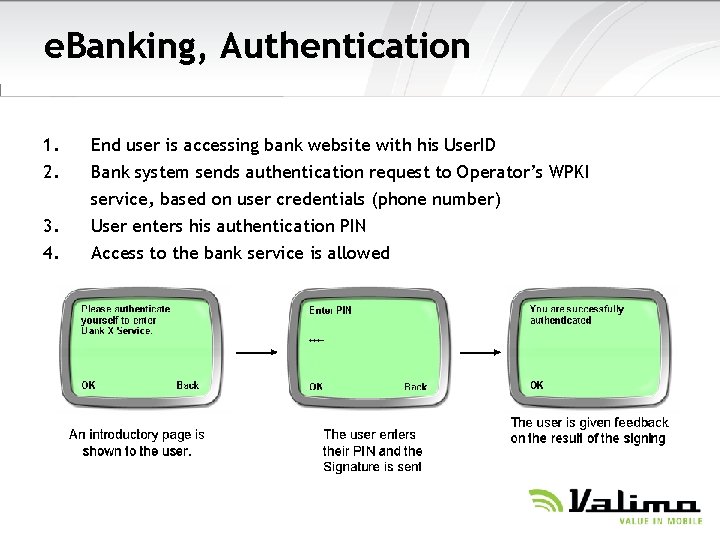
e. Banking, Authentication 1. 2. 3. 4. End user is accessing bank website with his User. ID Bank system sends authentication request to Operator’s WPKI service, based on user credentials (phone number) User enters his authentication PIN Access to the bank service is allowed
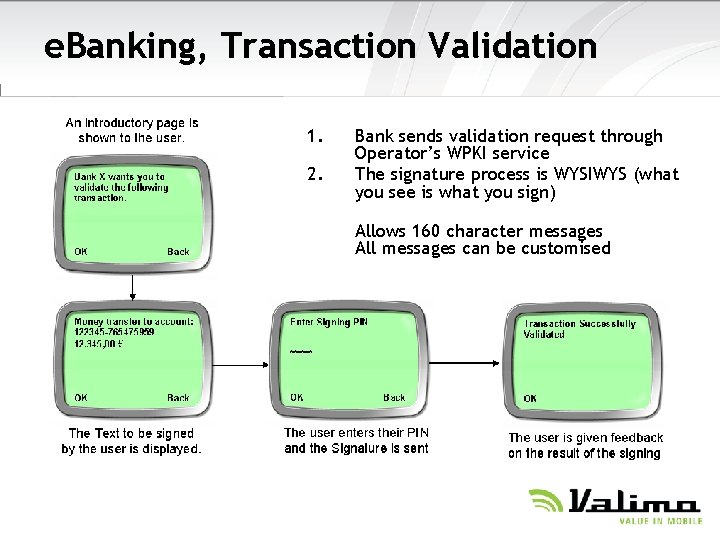
e. Banking, Transaction Validation 1. 2. Bank sends validation request through Operator’s WPKI service The signature process is WYSIWYS (what you see is what you sign) Allows 160 character messages All messages can be customised
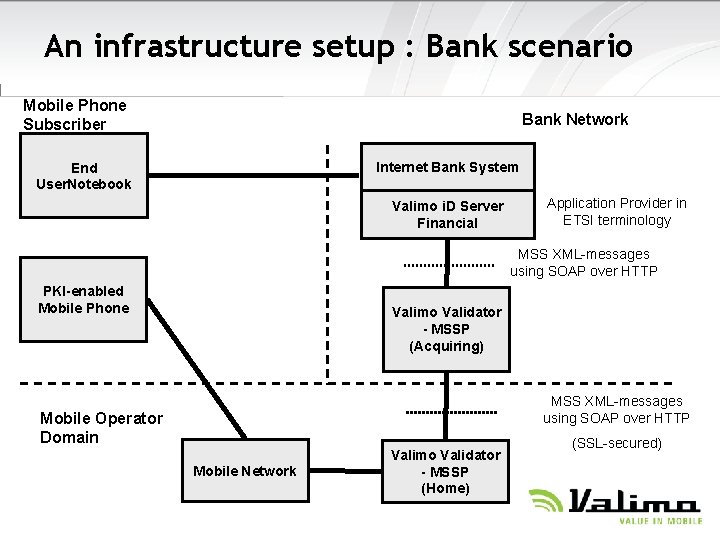
An infrastructure setup : Bank scenario Mobile Phone Subscriber Bank Network Internet Bank System End User. Notebook Valimo i. D Server Financial Application Provider in ETSI terminology MSS XML-messages using SOAP over HTTP PKI-enabled Mobile Phone Valimo Validator - MSSP (Acquiring) MSS XML-messages using SOAP over HTTP Mobile Operator Domain Mobile Network Valimo Validator - MSSP (Home) (SSL-secured)
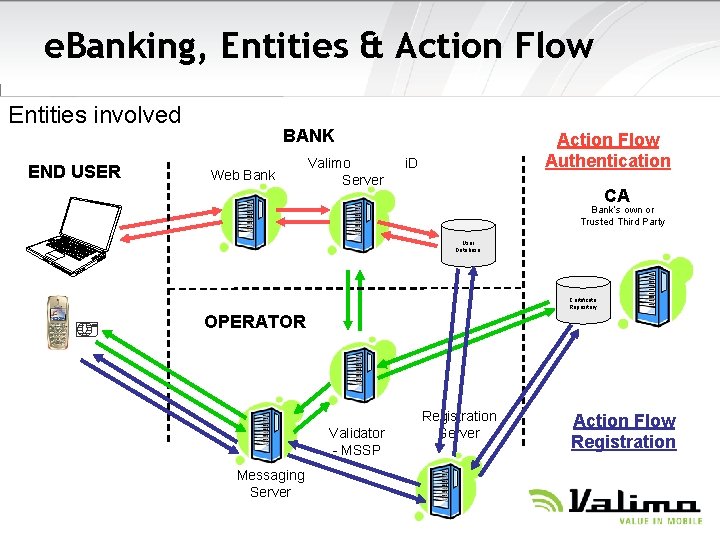
e. Banking, Entities & Action Flow Entities involved END USER BANK Web Bank Action Flow Authentication Valimo i. D Server CA Bank’s own or Trusted Third Party User Database Certificate Repository OPERATOR Validator - MSSP Messaging Server Registration Server Action Flow Registration
Our Mobile Vision mobile phone is a trusted device, providing anywhere, anytime access to confidential personal and business content, and easily performs secure transactions. THANK YOU! Erkki Saharanta, Valimo Wireless Ltd +358 44 344 5564 erkki. saharanta@valimo. com www. valimo. com
- Slides: 45