As Droid Detecting Stealthy Behaviors in Android Applications
As. Droid: Detecting Stealthy Behaviors in Android Applications by User Interface and Program Behavior Contradiction Jianjun Huang, Xiangyu Zhang, Lin Tan, Peng Wang, Bin Liang Purdue University of Waterloo Renmin University of China
Motivation q Stealthy behaviors in Android apps Premium rate Phone number Send SMS to You didn’t see Send request to me Respond with malicious app Malicious Web site
Motivation q Stealthy behaviors in Android apps Q 52 -64% of existing malwares send stealthy premium rate SMS messages or make phone calls (A. P. Felt. SPSM’ 11, Y. Zhou. S&P’ 12) Q Stealthy HTTP requests are also very common undesirable behaviors in malware (A. P. Felt. SPSM’ 11) v A kind of malware making stealthy HTTP connections caused 8 million dollars loss in March 2010 in China (news in SINA. com)
Motivation q Challenges Q Malicious behaviors appear to be indistinguishable from that of benign apps Q Existing techniques are insufficient in detecting stealthy behaviors v Access control by setting application privileges n Very coarse-grained v Taint analysis n Stealthy behaviors may not leak any information v Blacklisting premium-rate phone numbers n Non-trivial to keep a blacklist up-to-date
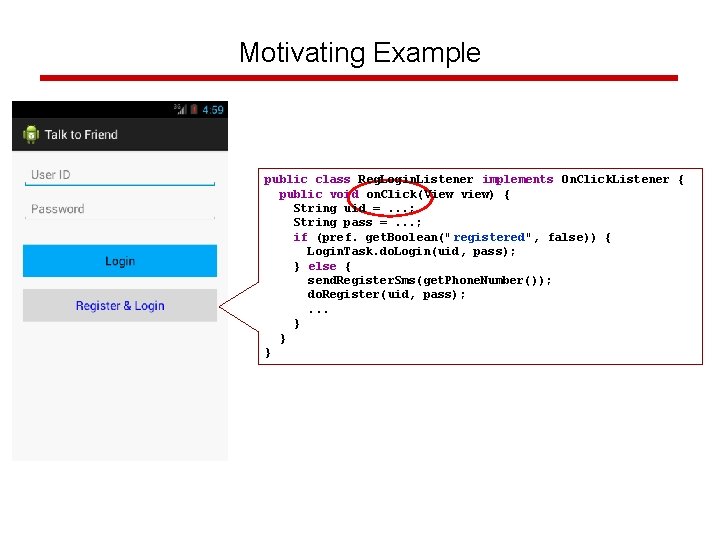
Motivating Example public class Reg. Login. Listener implements On. Click. Listener { public void on. Click(View view) { on. Click String uid =. . . ; String pass =. . . ; if (pref. get. Boolean("registered", false)) { Login. Task. do. Login(uid, pass); } else { send. Register. Sms(get. Phone. Number()); do. Register(uid, pass); . . . } } }
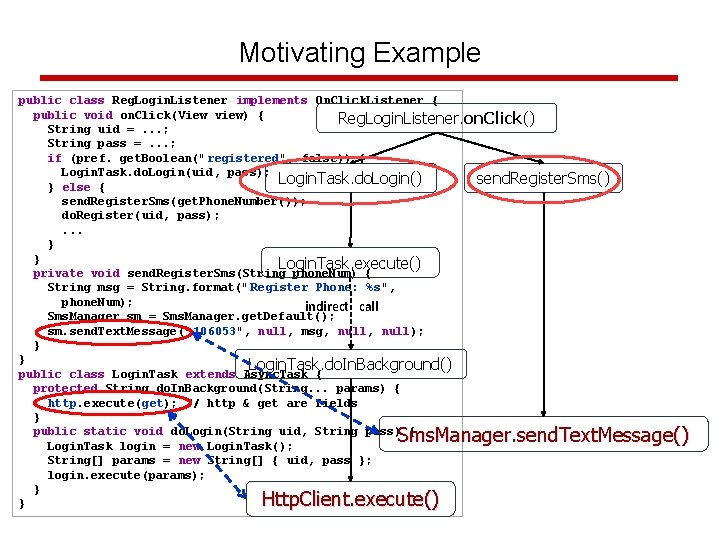
Motivating Example public class Reg. Login. Listener implements On. Click. Listener { public void on. Click(View view) { on. Click Reg. Login. Listener. on. Click() String uid =. . . ; String pass =. . . ; if (pref. get. Boolean("registered", false)) { Login. Task. do. Login(uid, pass); send. Register. Sms() Login. Task. do. Login() } else { send. Register. Sms(get. Phone. Number()); do. Register(uid, pass); . . . } } Login. Task. execute() private void send. Register. Sms(String phone. Num) { String msg = String. format(" Register Phone: %s", phone. Num); indirect call Sms. Manager sm = Sms. Manager. get. Default(); sm. send. Text. Message(" 106053", null, msg, null); } } Login. Task. do. In. Background() public class Login. Task extends Async. Task { protected String do. In. Background(String. . . params) { http. execute(get); // http & get are fields } public static void do. Login(String uid, String pass) { Login. Task login = new Login. Task(); String[] params = new String[] { uid, pass }; login. execute(params); } } Sms. Manager. send. Text. Message() Http. Client. execute()
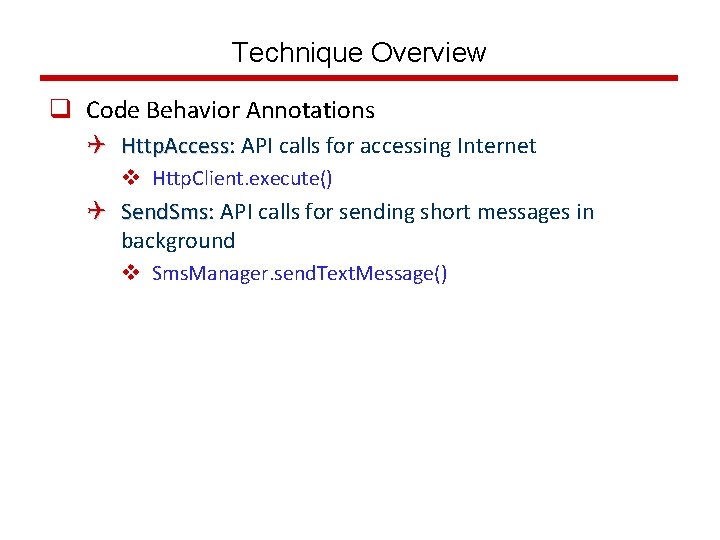
Technique Overview q Code Behavior Annotations Q Http. Access: Http. Access API calls for accessing Internet v Http. Client. execute() Q Send. Sms: Send. Sms API calls for sending short messages in background v Sms. Manager. send. Text. Message()
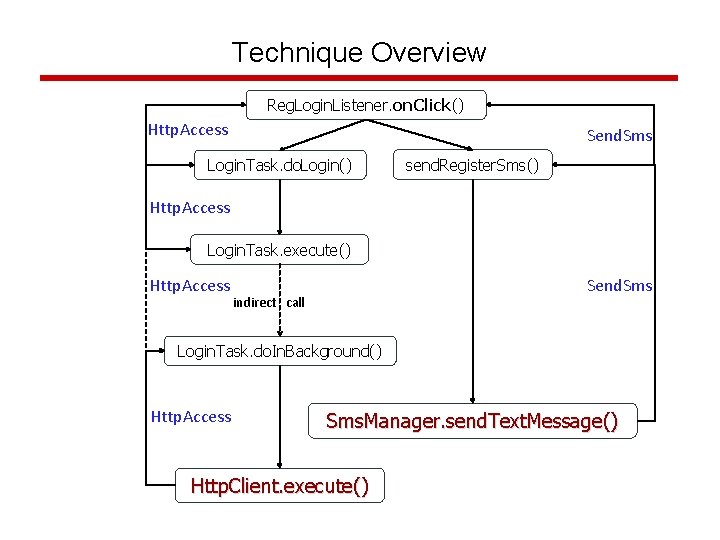
Technique Overview Reg. Login. Listener. on. Click() Http. Access Send. Sms Login. Task. do. Login() send. Register. Sms() Http. Access Login. Task. execute() Http. Access Send. Sms indirect call Login. Task. do. In. Background() Http. Access Sms. Manager. send. Text. Message() Http. Client. execute()
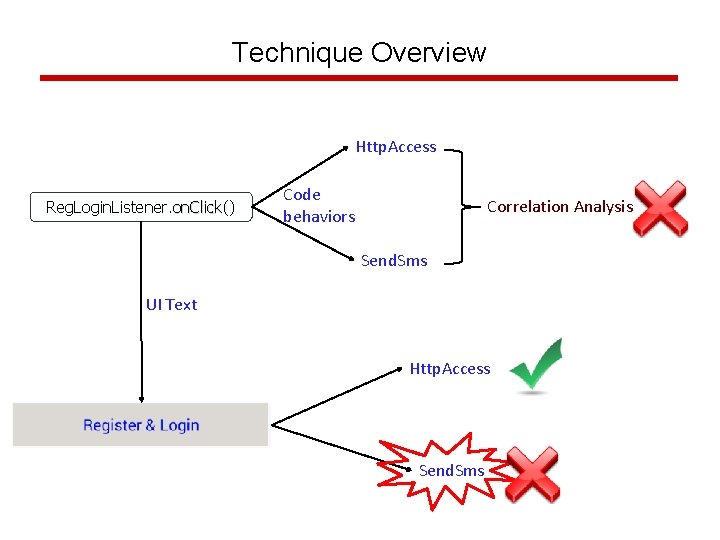
Technique Overview Http. Access Reg. Login. Listener. on. Click() on. Click Code behaviors Correlation Analysis Send. Sms UI Text Http. Access Send. Sms
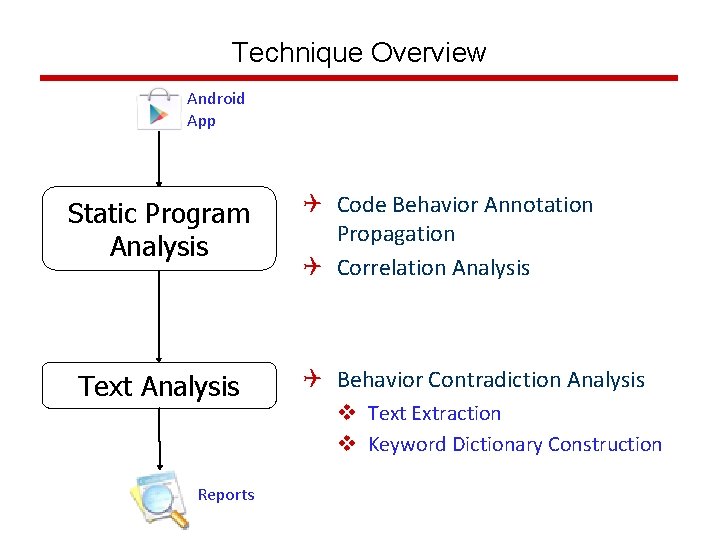
Technique Overview Android App Static Program Analysis Text Analysis Reports Q Code Behavior Annotation Propagation Q Correlation Analysis Q Behavior Contradiction Analysis v Text Extraction v Keyword Dictionary Construction
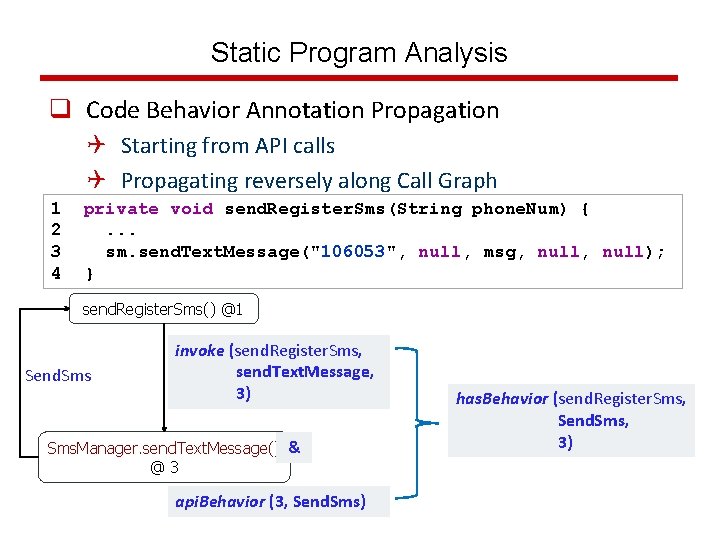
Static Program Analysis q Code Behavior Annotation Propagation Q Starting from API calls Q Propagating reversely along Call Graph 1 2 3 4 private void send. Register. Sms(String phone. Num) {. . . sm. send. Text. Message("106053", null, msg, null); } send. Register. Sms() @1 Send. Sms invoke (send. Register. Sms, send. Text. Message, 3) Sms. Manager. send. Text. Message() & @3 api. Behavior (3, Send. Sms) has. Behavior (send. Register. Sms, Send. Sms, 3)
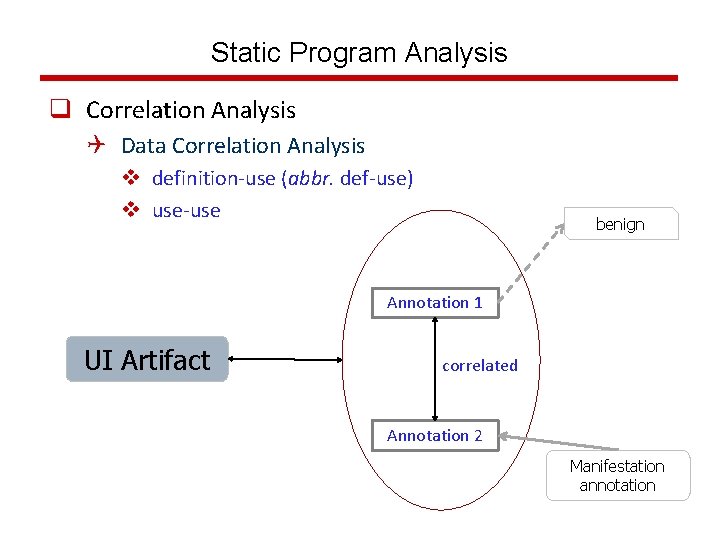
Static Program Analysis q Correlation Analysis Q Data Correlation Analysis v definition-use (abbr. def-use) v use-use benign Annotation 1 UI Artifact correlated Annotation 2 Manifestation annotation
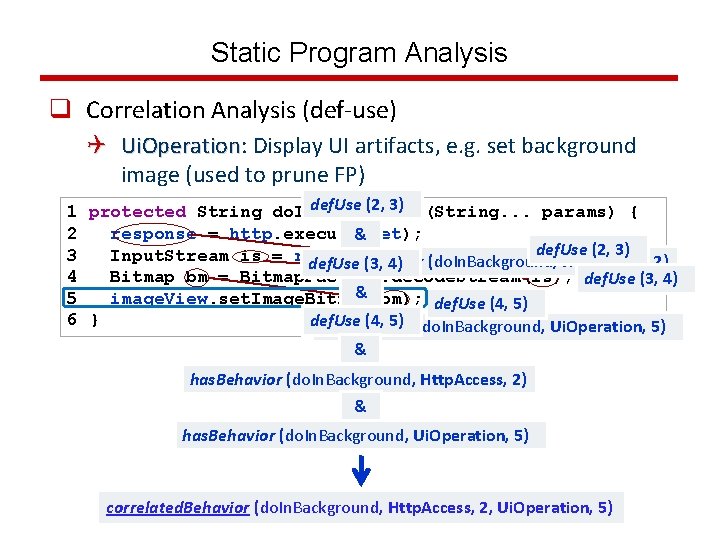
Static Program Analysis q Correlation Analysis (def-use) Q Ui. Operation: Ui. Operation Display UI artifacts, e. g. set background image (used to prune FP) def. Use (2, 3) 1 protected String do. In. Background(String. . . params) { 2 response = http. execute(get); & def. Use (2, 3) 3 Input. Stream is = response. get. Content(); has. Behavior (do. In. Background, Http. Access, 2) def. Use (3, 4) 4 Bitmap bm = Bitmap. Factory. decode. Stream(is); def. Use (3, 4) & 5 image. View. set. Image. Bitmap(bm); def. Use (4, 5) 6 } def. Use (4, 5) (do. In. Background, Ui. Operation, 5) has. Behavior & has. Behavior (do. In. Background, Http. Access, 2) & has. Behavior (do. In. Background, Ui. Operation, 5) correlated. Behavior (do. In. Background, Http. Access, 2, Ui. Operation, 5)
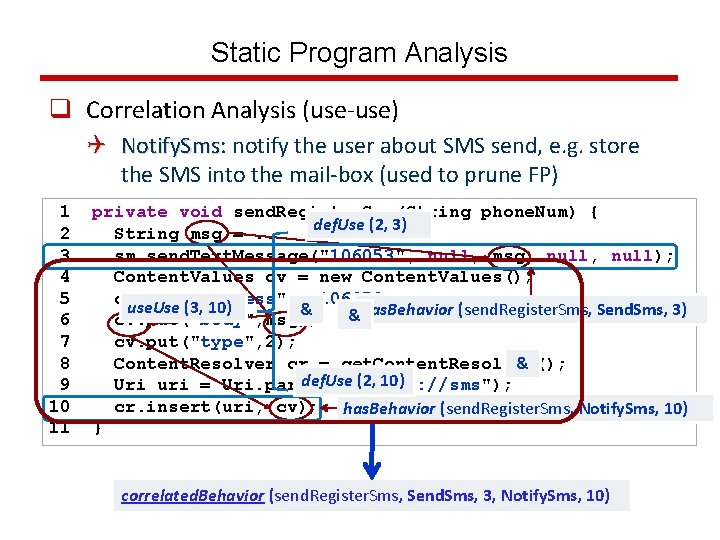
Static Program Analysis q Correlation Analysis (use-use) Q Notify. Sms: Notify. Sms notify the user about SMS send, e. g. store the SMS into the mail-box (used to prune FP) 1 2 3 4 5 6 7 8 9 10 11 private void send. Register. Sms(String phone. Num) { String msg =. . . def. Use (2, 3) sm. send. Text. Message("106053", null, msg, null); Content. Values cv = new Content. Values(); cv. put("address", "106053"); use. Use (3, 10) & & has. Behavior (send. Register. Sms, Send. Sms, 3) cv. put("body", msg); cv. put("type", 2); Content. Resolver cr = get. Content. Resolver(); & def. Use (2, 10) Uri uri = Uri. parse("content: //sms"); cr. insert(uri, cv); has. Behavior (send. Register. Sms, Notify. Sms, 10) } correlated. Behavior (send. Register. Sms, Send. Sms, 3, Notify. Sms, 10)
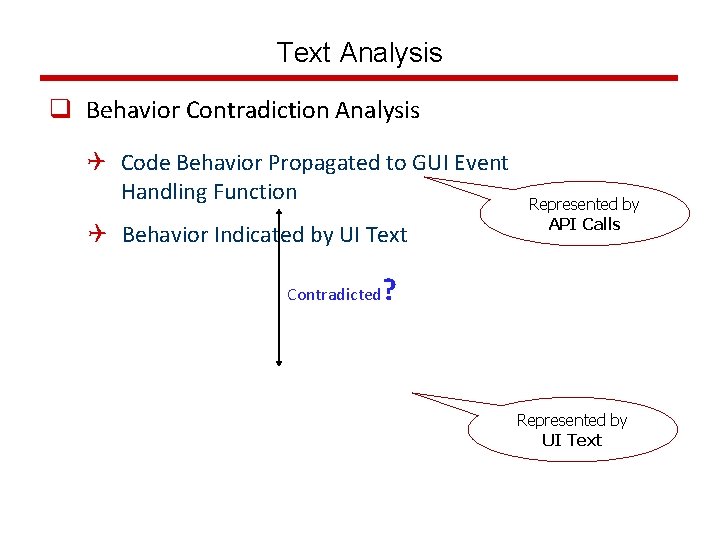
Text Analysis q Behavior Contradiction Analysis Q Code Behavior Propagated to GUI Event Handling Function Q Behavior Indicated by UI Text Contradicted Represented by API Calls ? Represented by UI Text
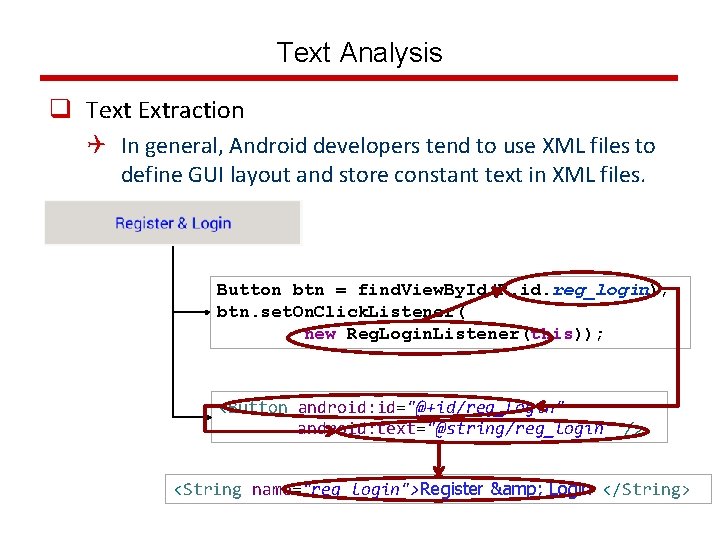
Text Analysis q Text Extraction Q In general, Android developers tend to use XML files to define GUI layout and store constant text in XML files. Button btn = find. View. By. Id(R. id. reg_login); btn. set. On. Click. Listener( new Reg. Login. Listener(this)); <Button android: id="@+id/reg_login" android: text="@string/reg_login" /> <String name="reg_login">Register & Login </String>
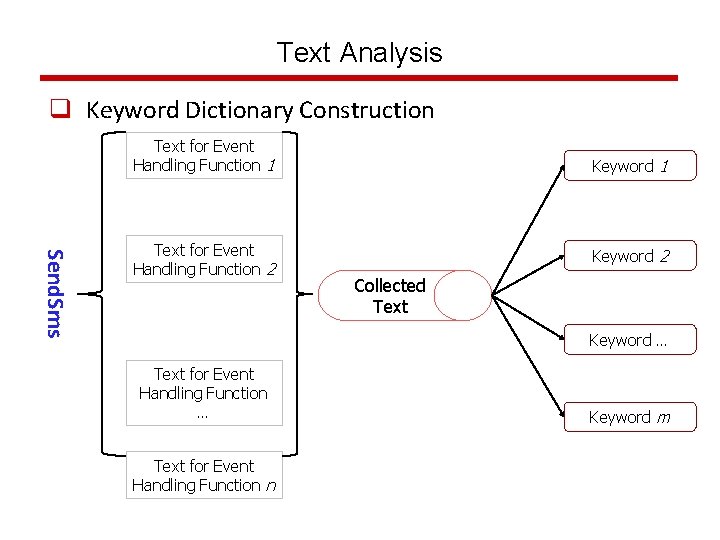
Text Analysis q Keyword Dictionary Construction Text for Event Handling Function 1 Send. Sms Text for Event Handling Function 2 Keyword 1 Keyword 2 Collected Text Keyword … Text for Event Handling Function n Keyword m
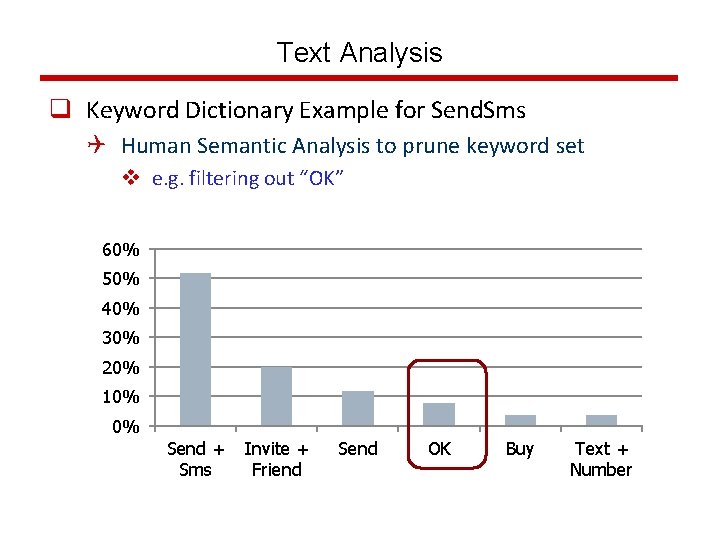
Text Analysis q Keyword Dictionary Example for Send. Sms Q Human Semantic Analysis to prune keyword set v e. g. filtering out “OK” 60% 50% 40% 30% 20% 10% 0% Send + Sms Invite + Friend Send OK Buy Text + Number
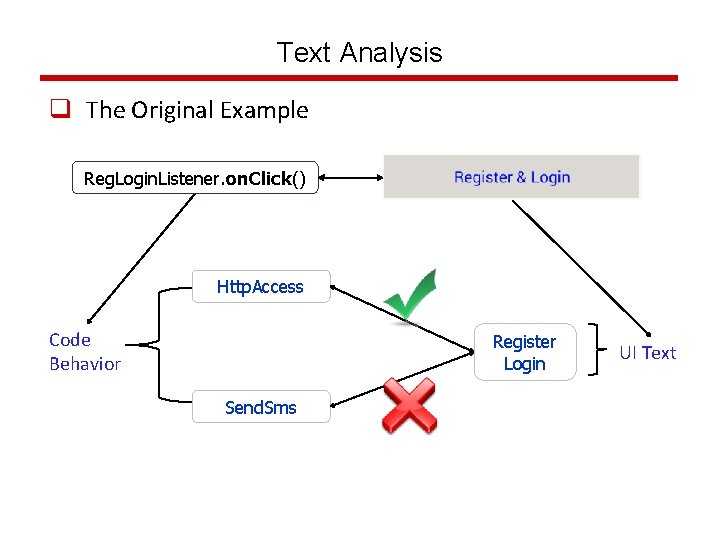
Text Analysis q The Original Example Reg. Login. Listener. on. Click() Http. Access Code Behavior Register Login Send. Sms UI Text
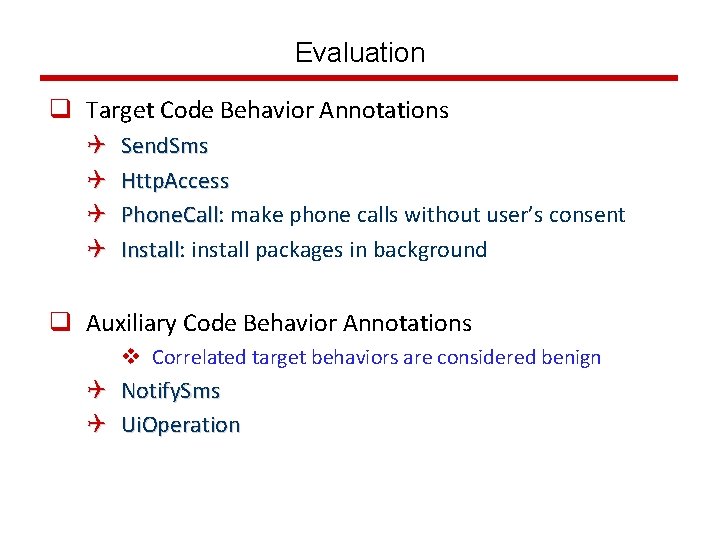
Evaluation q Target Code Behavior Annotations Q Q Send. Sms Http. Access Phone. Call: Phone. Call make phone calls without user’s consent Install: Install install packages in background q Auxiliary Code Behavior Annotations v Correlated target behaviors are considered benign Q Notify. Sms Q Ui. Operation
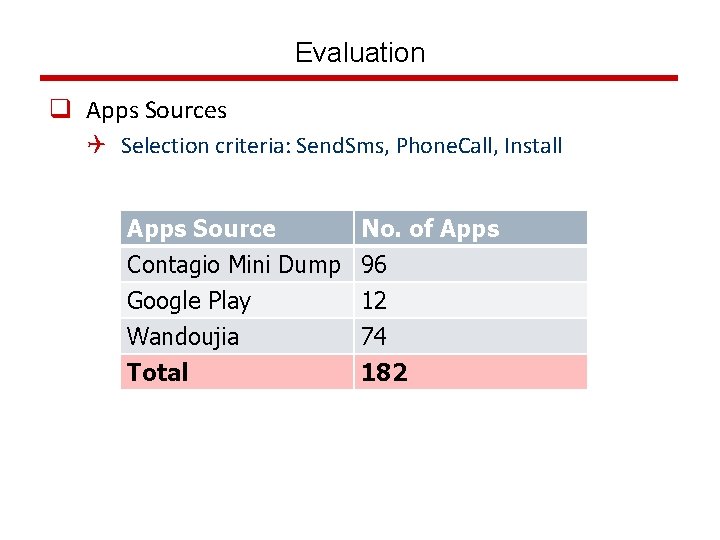
Evaluation q Apps Sources Q Selection criteria: Send. Sms, Phone. Call, Install Apps Source Contagio Mini Dump Google Play Wandoujia No. of Apps 96 12 74 Total 182
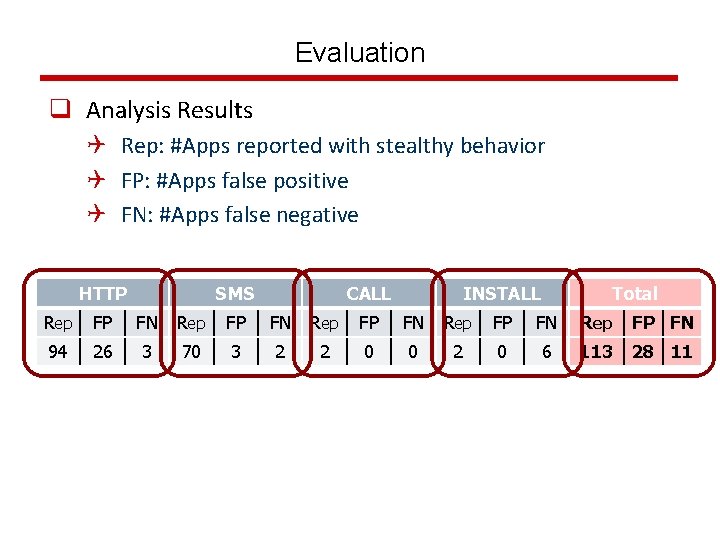
Evaluation q Analysis Results Q Rep: #Apps reported with stealthy behavior Q FP: #Apps false positive Q FN: #Apps false negative HTTP SMS CALL INSTALL Total Rep FP FN Rep FP FN 94 26 3 70 3 2 2 0 0 2 0 6 113 28 11
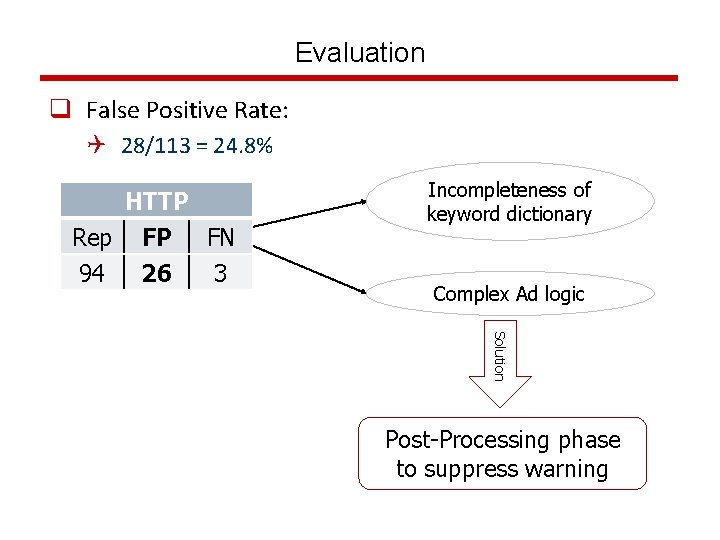
Evaluation q False Positive Rate: Q 28/113 = 24. 8% HTTP Rep FP FN 94 26 3 Incompleteness of keyword dictionary Complex Ad logic Solution Post-Processing phase to suppress warning
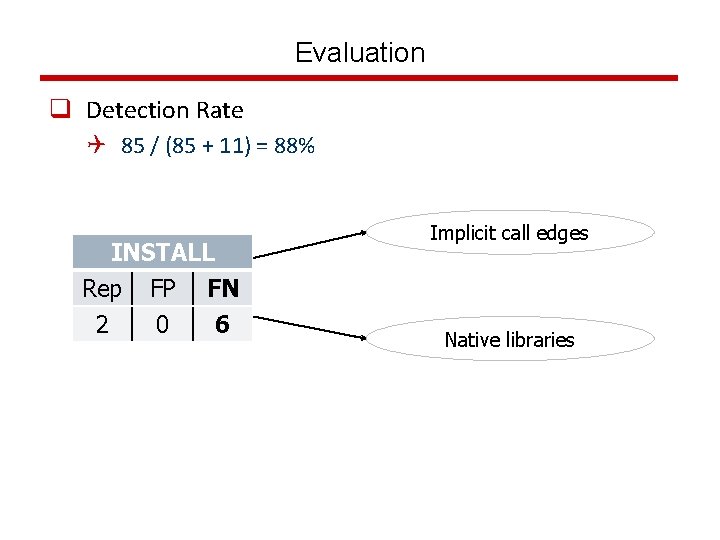
Evaluation q Detection Rate Q 85 / (85 + 11) = 88% INSTALL Rep FP FN 2 0 6 Implicit call edges Native libraries
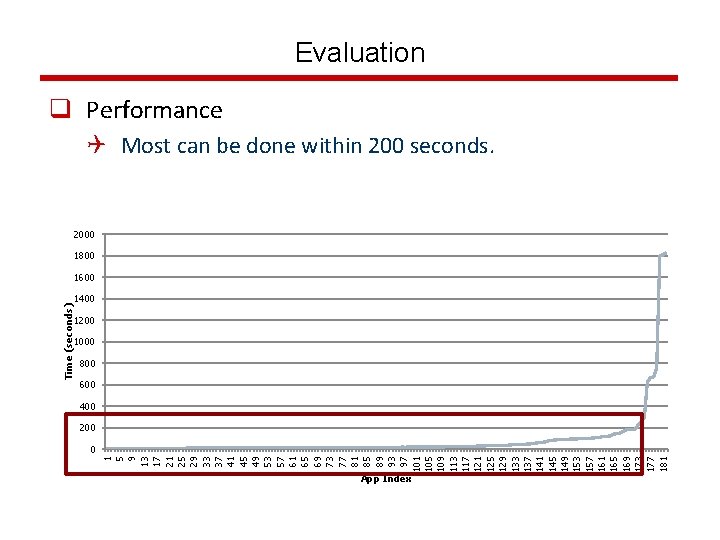
1 5 9 13 17 21 25 29 33 37 41 45 49 53 57 61 65 69 73 77 81 85 89 93 97 101 105 109 113 117 121 125 129 133 137 141 145 149 153 157 161 165 169 173 177 181 Time (seconds) Evaluation q Performance Q Most can be done within 200 seconds. 2000 1800 1600 1400 1200 1000 800 600 400 200 0 App Index
Limitations q Textual keywords analysis is insufficient Q More advanced text analysis or image analysis q Future adversary may obfuscate a malicious app to induce bogus correlations Q Leverage testing or symbolic analysis
Related Work q Taint Analysis Q Taint. Droid (W. Enck et al. OSDI’ 10) Q Flow. Droid (C. Fritz et al. Tech. Rep) q Malicious SMS/Phone. Call Detection Q Hardcoded number (W. Enck et al. Security’ 11) q Stealthy Behavior Detection Q Absence of data dependence path between user input/action and a sensitive function (K. Elish et al. Mo. ST’ 12) q Text Analysis Q Whyper (R. Pandita et al. Security’ 13)
Conclusion q We presented As. Droid to detect stealthy behaviors in Android apps. q The key idea is to identify contradiction between program behavior and user interface text. Q Static program analysis is applied for correlation analysis between code behaviors. Q Text analysis is utilized for contradiction analysis.
END Questions?
- Slides: 29