A Flexible Remote User Authentication Scheme Using Smart
A Flexible Remote User Authentication Scheme Using Smart Cards Source:ACM SIGOPS Operating Systems Review, July 2002 Author:Cheng-Chi Lee, Min-Shiang Hwang, Wei-Peng Yang Speaker:Yi-Chun Lo Team member: Sheng-Lung Cheng, Liang-Chi Chen Date: 12/22/2003
Outline n n Introduction Literature Reviews n n n The Hwang-Li’s Scheme The Sun’s Scheme Our Scheme Security Analysis Efficiency Conclusions
Introduction n Based on El. Gamal’s cryptosystem, Hwang and Li proposed a remote user authentication scheme using smart cards [6]. Sun proposed an efficient remote use authentication scheme using smart cards [9]. We shall propose a new scheme that allows users to freely choose and change their passwords without significantly increasing the computation cost.
Literature Reviews- The Hwang-Li’s Scheme n Registration Phase n :a secret key for the server P:a large prime number of 1024 bits Login Phase n n n Randomly choose an integer r Calculate where T is the current date and time, and ⊕ denotes an exclusive operation
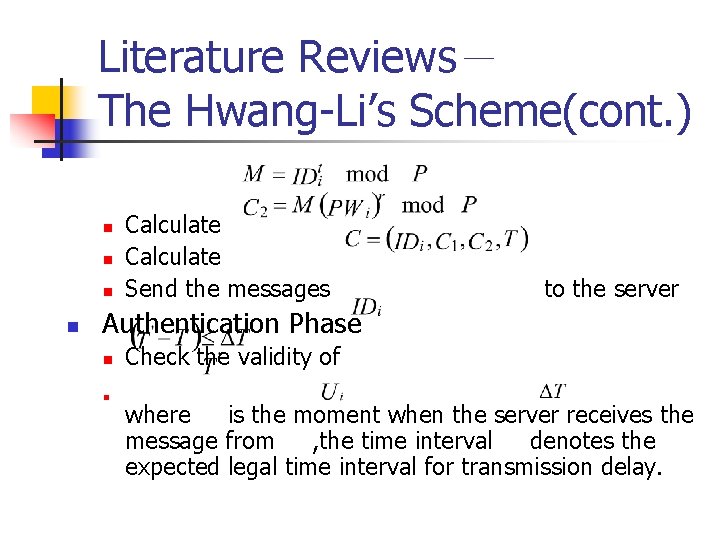
Literature Reviews- The Hwang-Li’s Scheme(cont. ) n n Calculate Send the messages to the server Authentication Phase n n Check the validity of where is the moment when the server receives the message from , the time interval denotes the expected legal time interval for transmission delay.
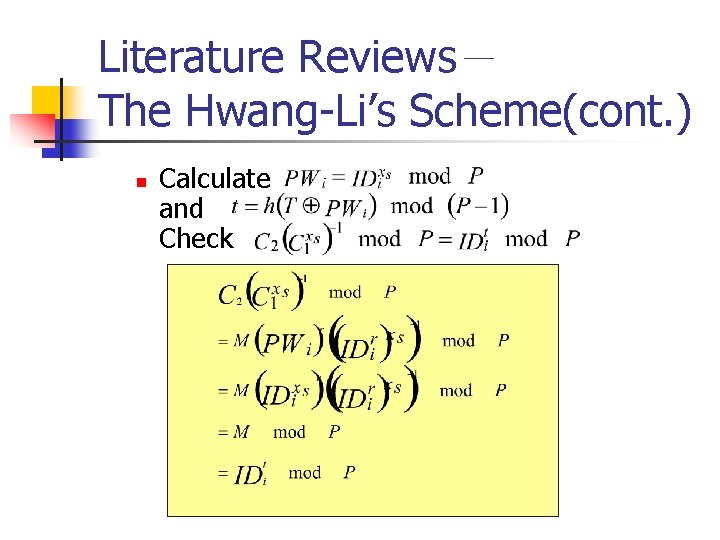
Literature Reviews- The Hwang-Li’s Scheme(cont. ) n Calculate and Check
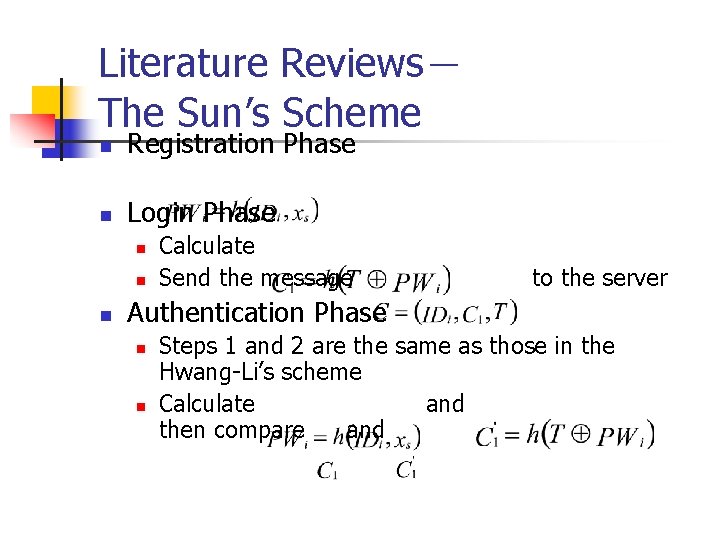
Literature Reviews- The Sun’s Scheme n Registration Phase n Login Phase n n n Calculate Send the message to the server Authentication Phase n n Steps 1 and 2 are the same as those in the Hwang-Li’s scheme Calculate and then compare and
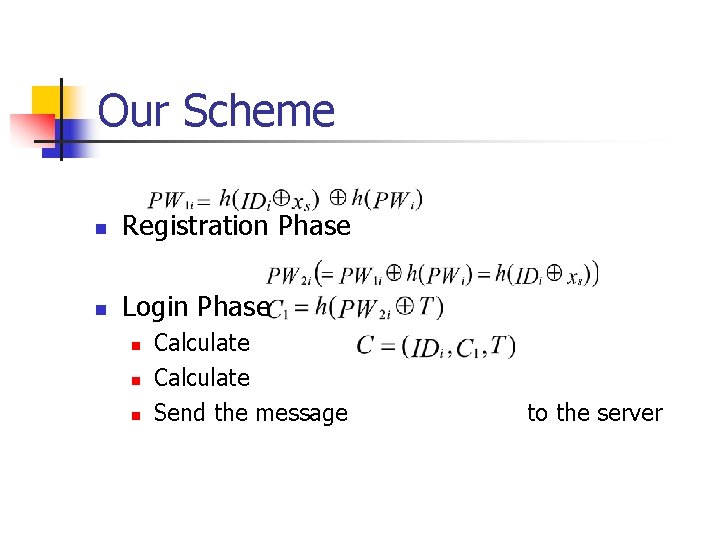
Our Scheme n Registration Phase n Login Phase n n n Calculate Send the message to the server
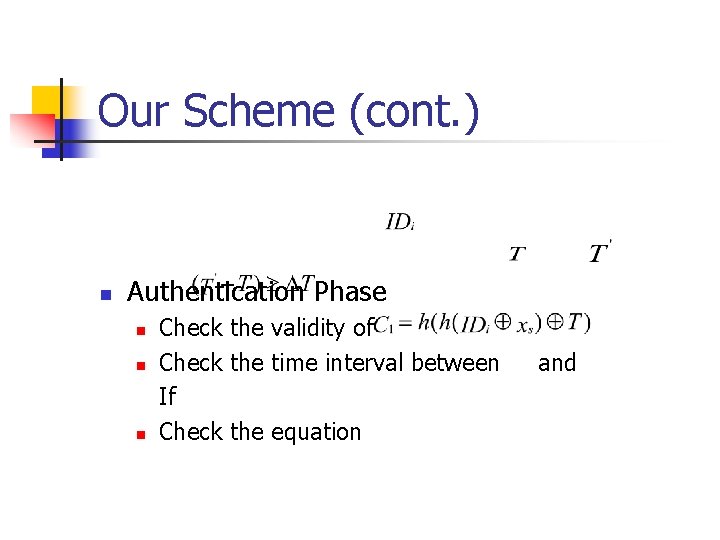
Our Scheme (cont. ) n Authentication Phase n n n Check the validity of Check the time interval between If Check the equation and
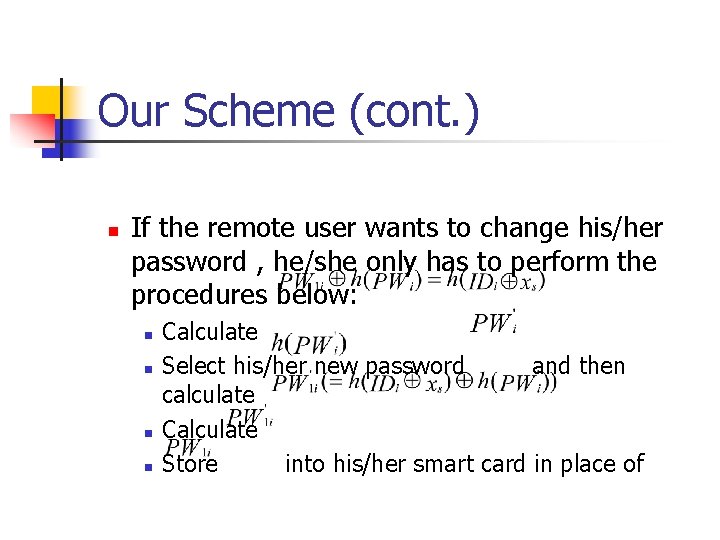
Our Scheme (cont. ) n If the remote user wants to change his/her password , he/she only has to perform the procedures below: n n Calculate Select his/her new password and then calculate Calculate Store into his/her smart card in place of
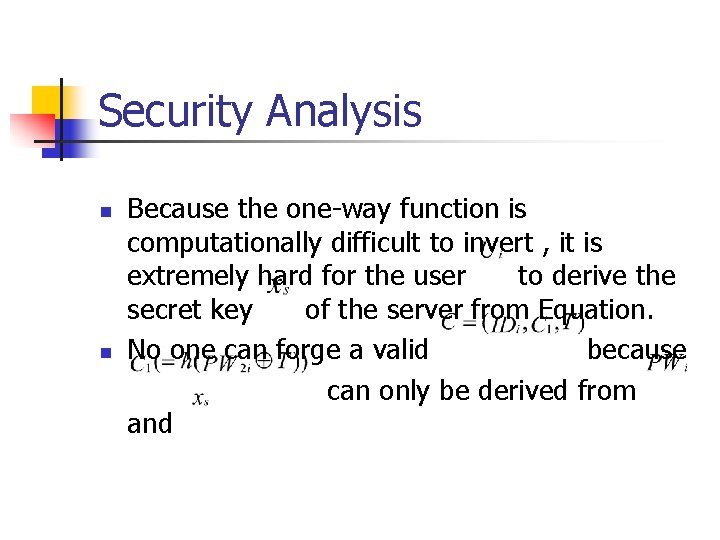
Security Analysis n n Because the one-way function is computationally difficult to invert , it is extremely hard for the user to derive the secret key of the server from Equation. No one can forge a valid because can only be derived from and
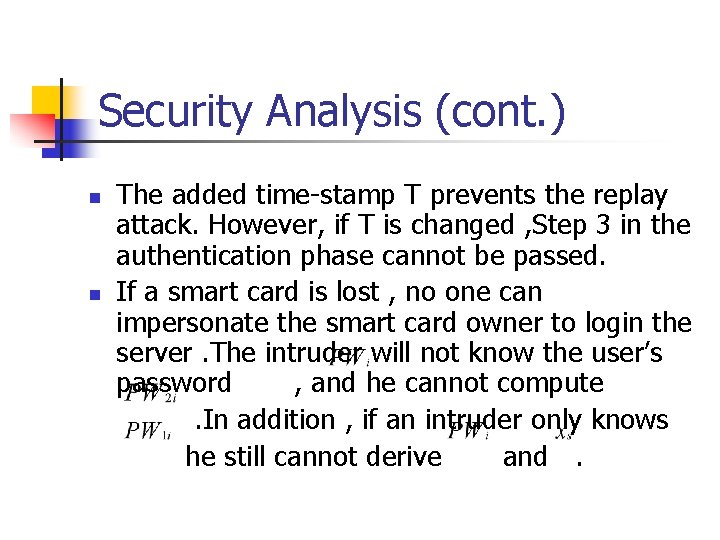
Security Analysis (cont. ) n n The added time-stamp T prevents the replay attack. However, if T is changed , Step 3 in the authentication phase cannot be passed. If a smart card is lost , no one can impersonate the smart card owner to login the server. The intruder will not know the user’s password , and he cannot compute. In addition , if an intruder only knows he still cannot derive and.
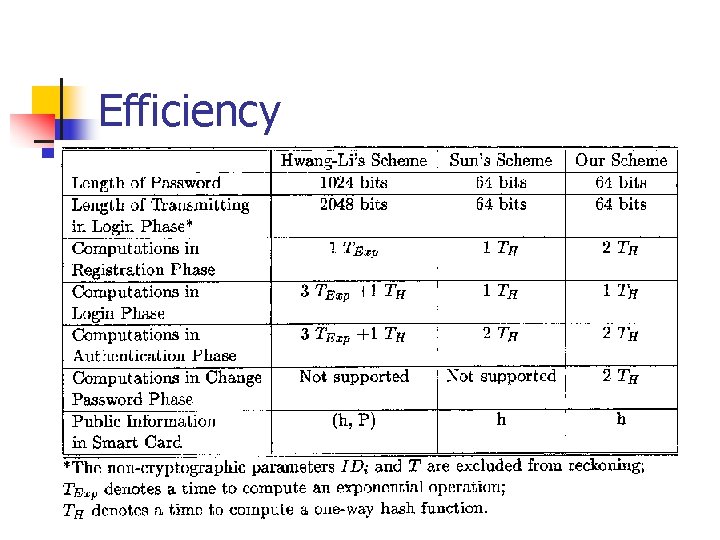
Efficiency
Conclusion n n In this article , we have proposed a simple and efficient remote user authentication scheme. The proposed scheme has succeeded in allowing a user to freely change and choose his password without significantly increasing the computation cost.
- Slides: 14