Secure Remote User Authentication Scheme Using Bilinear Pairings
Secure Remote User Authentication Scheme Using Bilinear Pairings Department of Computer Engineering, Kyungpook National University Author : Eun-Jun Yoon, Wan-Soo Lee, Kee-Young Yoo Speaker : Wan-Soo Lee (complete 2@infosec. knu. ac. kr) Date : 2007. 05. 10. (Thu)
Contents q Introduction q Review of Das et al. ’s scheme q Cryptanalysis of Das el al. ’s scheme q Impersonation attack q Off-Line password guessing attack q Proposed scheme q Conclusion Information Security Lab. 2/15
Introduction q Remote user authentication q Along with confidentiality and integrity, for systems that allow remote access over untrustworthy networks, like the Internet q Das et al. ’s scheme (In 2006) q proposed a remote user authentication scheme using bilinear pairing q Our refutation q Insecure against the impersonation attack and off-line password guessing attack Information Security Lab. 3/15
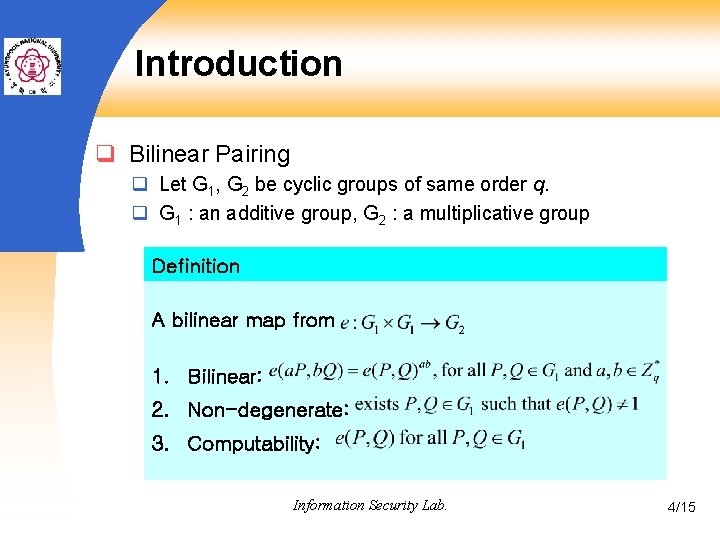
Introduction q Bilinear Pairing q Let G 1, G 2 be cyclic groups of same order q. q G 1 : an additive group, G 2 : a multiplicative group Definition A bilinear map from 1. Bilinear: 2. Non-degenerate: 3. Computability: Information Security Lab. 4/15
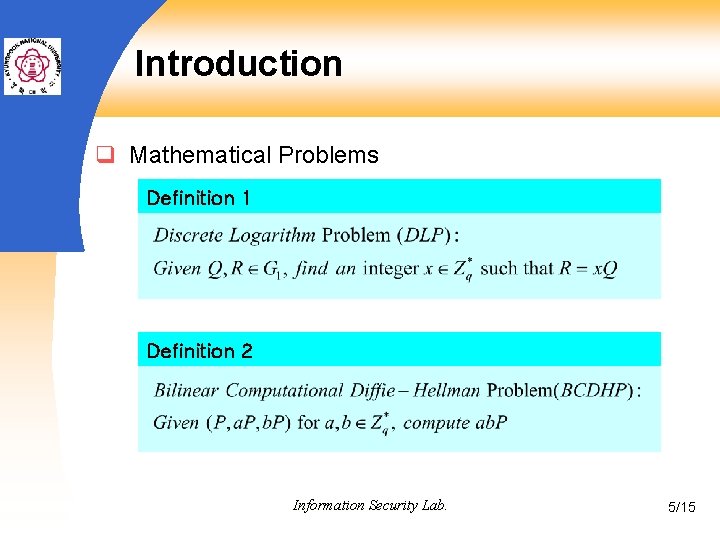
Introduction q Mathematical Problems Definition 1 Definition 2 Information Security Lab. 5/15
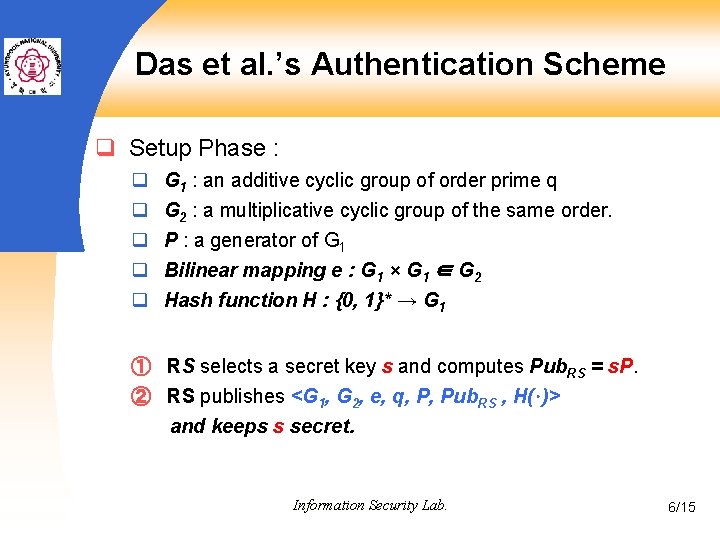
Das et al. ’s Authentication Scheme q Setup Phase : q q q G 1 : an additive cyclic group of order prime q G 2 : a multiplicative cyclic group of the same order. P : a generator of G 1 Bilinear mapping e : G 1 × G 1 ∈ G 2 Hash function H : {0, 1}* → G 1 ① RS selects a secret key s and computes Pub. RS = s. P. ② RS publishes <G 1, G 2, e, q, P, Pub. RS , H(·)> and keeps s secret. Information Security Lab. 6/15
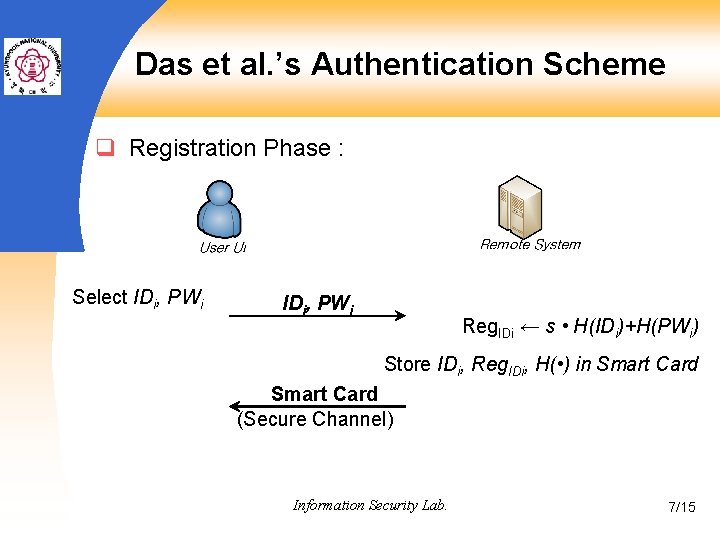
Das et al. ’s Authentication Scheme q Registration Phase : Select IDi, PWi Reg. IDi ← s • H(IDi)+H(PWi) Store IDi, Reg. IDi, H( • ) in Smart Card (Secure Channel) Information Security Lab. 7/15
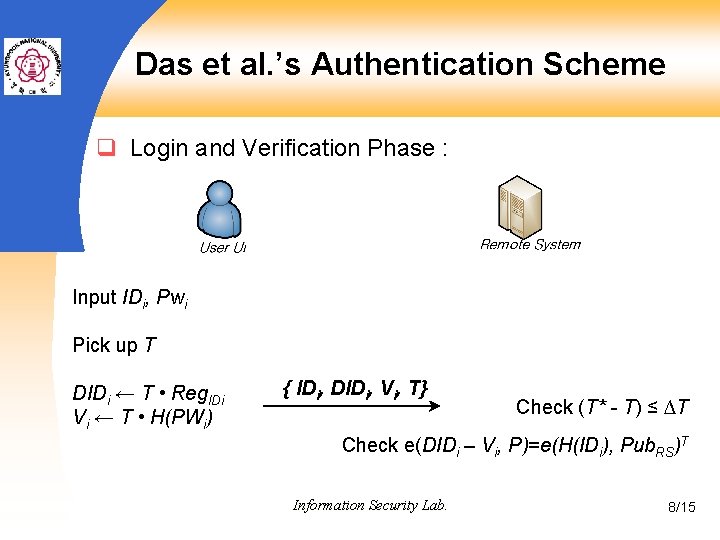
Das et al. ’s Authentication Scheme q Login and Verification Phase : Input IDi, Pwi Pick up T DIDi ← T • Reg. IDi Vi ← T • H(PWi) { IDi, DIDi, Vi, T} Check (T* - T) ≤ ∆T Check e(DIDi – Vi, P)=e(H(IDi), Pub. RS)T Information Security Lab. 8/15
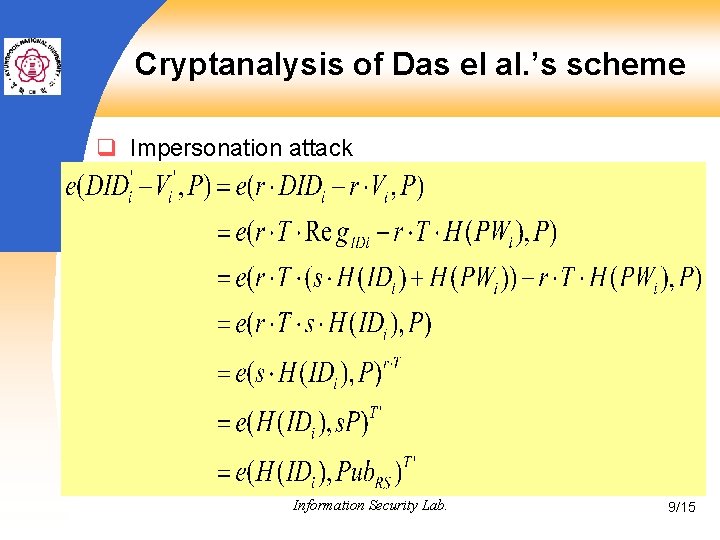
Cryptanalysis of Das el al. ’s scheme q Impersonation attack { IDi, DID’i, V’i, T’} { IDi, DIDi, Vi, T} Information Security Lab. 9/15
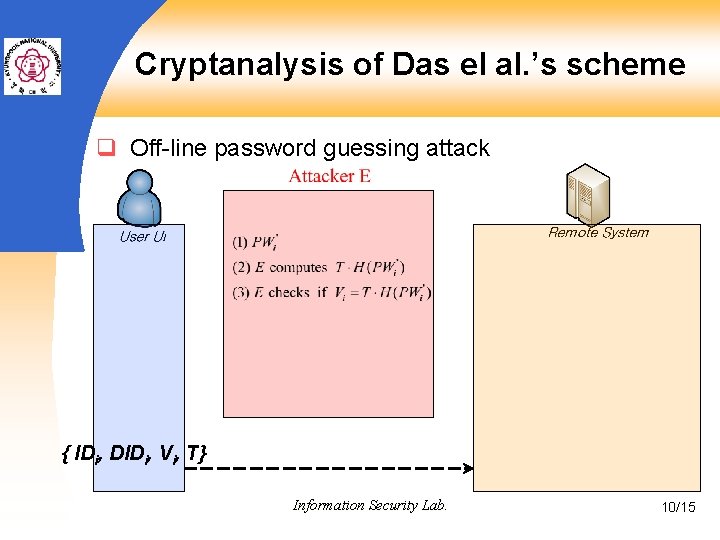
Cryptanalysis of Das el al. ’s scheme q Off-line password guessing attack { IDi, DIDi, Vi, T} Information Security Lab. 10/15
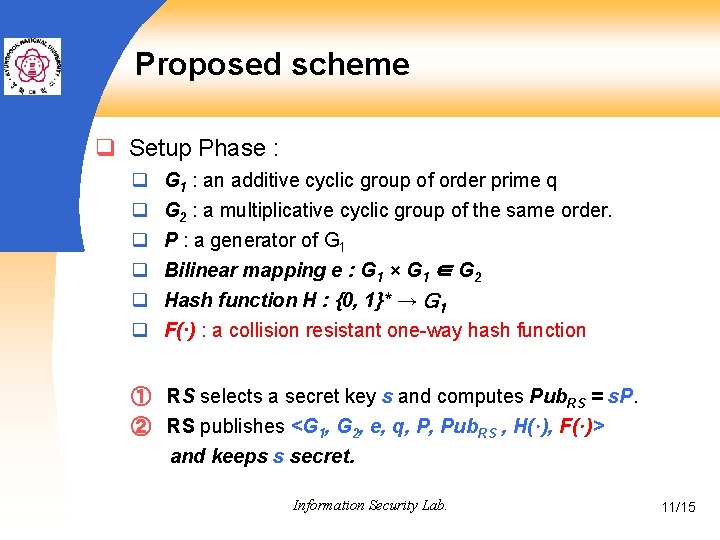
Proposed scheme q Setup Phase : q q q G 1 : an additive cyclic group of order prime q G 2 : a multiplicative cyclic group of the same order. P : a generator of G 1 Bilinear mapping e : G 1 × G 1 ∈ G 2 Hash function H : {0, 1}* → G 1 F(·) : a collision resistant one-way hash function ① RS selects a secret key s and computes Pub. RS = s. P. ② RS publishes <G 1, G 2, e, q, P, Pub. RS , H(·), F(·)> and keeps s secret. Information Security Lab. 11/15
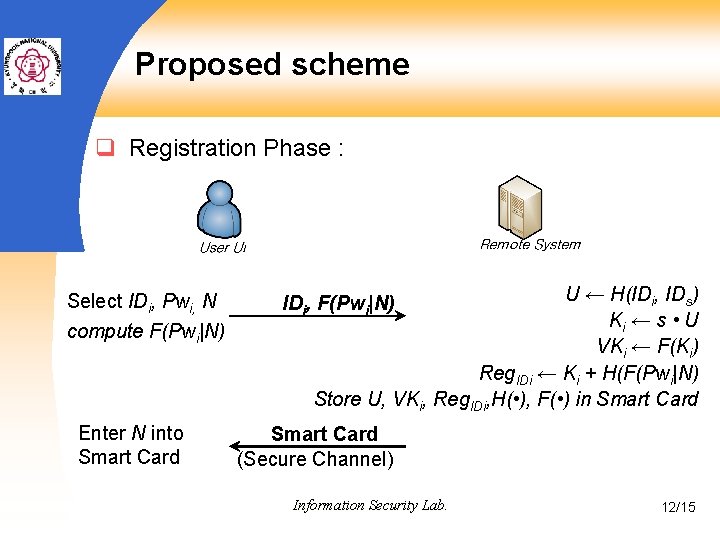
Proposed scheme q Registration Phase : Select IDi, Pwi, N compute F(Pwi|N) Enter N into Smart Card U ← H(IDi, IDs) Ki ← s • U VKi ← F(Ki) Reg. IDi ← Ki + H(F(Pwi|N) Store U, VKi, Reg. IDi, H( • ), F( • ) in Smart Card IDi, F(Pwi|N) Smart Card (Secure Channel) Information Security Lab. 12/15
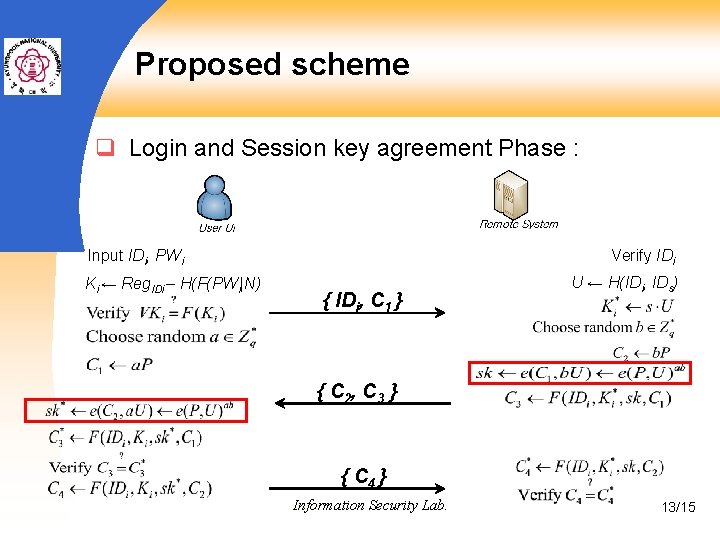
Proposed scheme q Login and Session key agreement Phase : Input IDi, PWi Ki ← Reg. IDi – H(F(PWi|N) Verify IDi { IDi, C 1 } U ← H(IDi, IDs) { C 2 , C 3 } { C 4 } Information Security Lab. 13/15
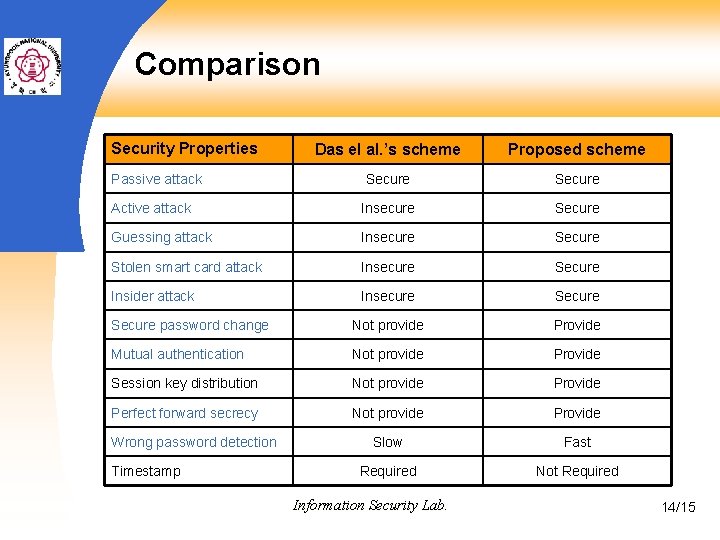
Comparison Security Properties Das el al. ’s scheme Proposed scheme Secure Active attack Insecure Secure Guessing attack Insecure Stolen smart card attack Insecure Secure Insider attack Insecure Secure password change Not provide Provide Mutual authentication Not provide Provide Session key distribution Not provide Perfect forward secrecy Not provide Provide Slow Fast Required Not Required Passive attack Wrong password detection Timestamp Information Security Lab. 14/15
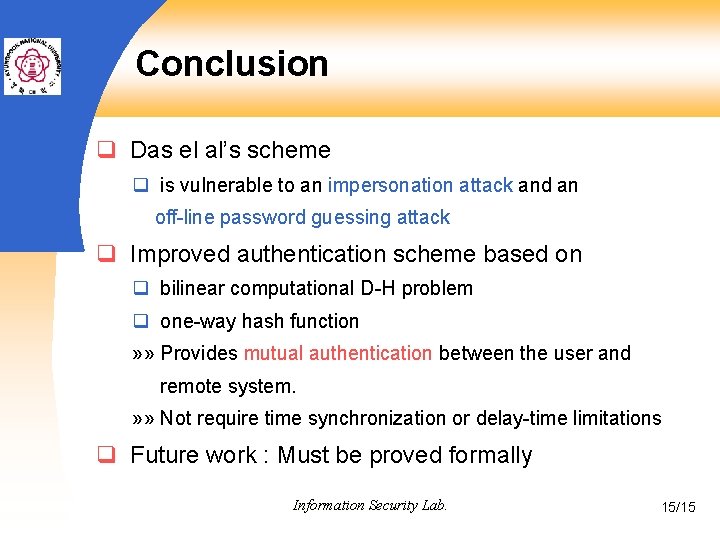
Conclusion q Das el al’s scheme q is vulnerable to an impersonation attack and an off-line password guessing attack q Improved authentication scheme based on q bilinear computational D-H problem q one-way hash function » » Provides mutual authentication between the user and remote system. » » Not require time synchronization or delay-time limitations q Future work : Must be proved formally Information Security Lab. 15/15
Q&A Thank you Information Security Lab. 16/15
- Slides: 16