A Flexible Biometrics Remote User Authentication Scheme Source
A Flexible Biometrics Remote User Authentication Scheme Source: Computer Standards and Interfaces, Vol. 21, Issue 1, pp. 19 -23, Nov. 2004 Authors: Chu-Hsing Lin, Yi-Yi Lai Speaker: Chia-Chi Wu Date : 10/21/2004 1
Outline n n The Lee-Ryu-Yoo scheme Cryptanalysis of the Lee-Ryu-Yoo scheme The enhance scheme Conclusions 2
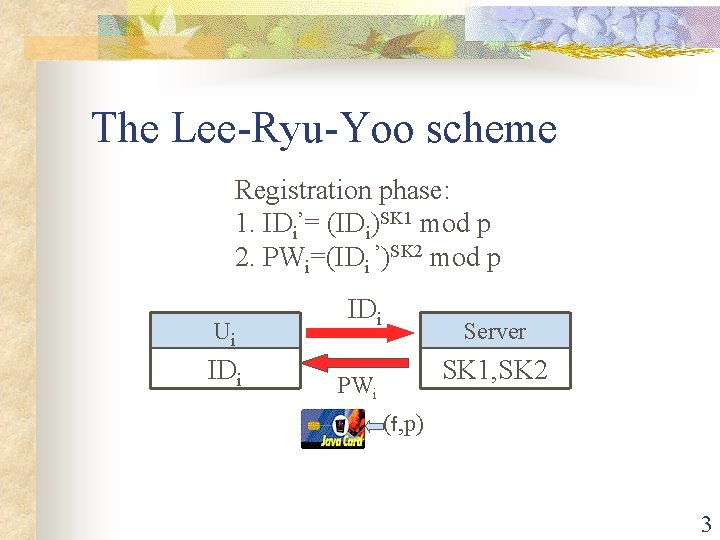
The Lee-Ryu-Yoo scheme Registration phase: 1. IDi’= (IDi)SK 1 mod p 2. PWi=(IDi ’)SK 2 mod p Ui IDi Server SK 1, SK 2 PWi (f, p) 3
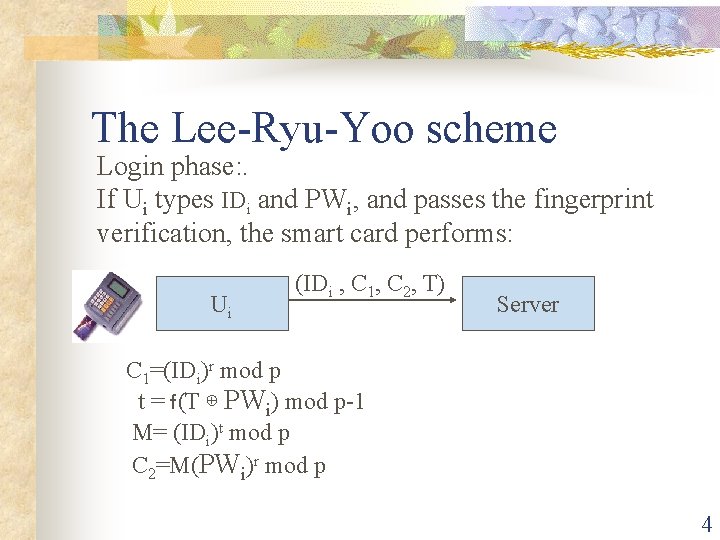
The Lee-Ryu-Yoo scheme Login phase: . If Ui types IDi and PWi, and passes the fingerprint verification, the smart card performs: Ui (IDi , C 1, C 2, T) Server C 1=(IDi)r mod p t = f(T ⊕ PWi) mod p-1 M= (IDi)t mod p C 2=M(PWi)r mod p 4
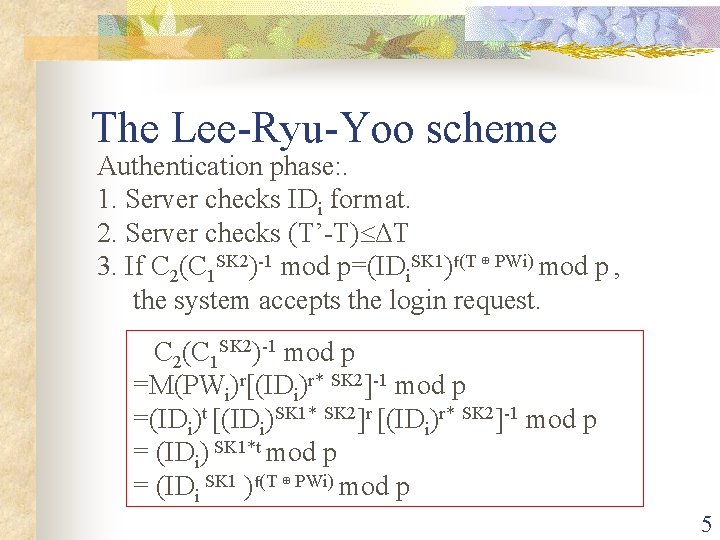
The Lee-Ryu-Yoo scheme Authentication phase: . 1. Server checks IDi format. 2. Server checks (T’-T) ΔT 3. If C 2(C 1 SK 2)-1 mod p=(IDi. SK 1)f(T ⊕ PWi) mod p , the system accepts the login request. C 2(C 1 SK 2)-1 mod p =M(PWi)r[(IDi)r* SK 2]-1 mod p =(IDi)t [(IDi)SK 1* SK 2]r [(IDi)r* SK 2]-1 mod p = (IDi) SK 1*t mod p = (IDi SK 1 )f(T ⊕ PWi) mod p 5
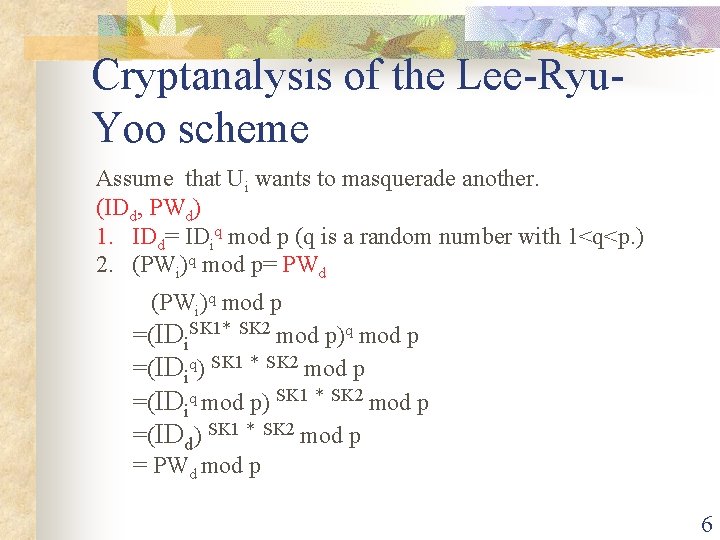
Cryptanalysis of the Lee-Ryu. Yoo scheme Assume that Ui wants to masquerade another. (IDd, PWd) 1. IDd= IDiq mod p (q is a random number with 1<q<p. ) 2. (PWi)q mod p= PWd (PWi)q mod p =(IDi. SK 1* SK 2 mod p)q mod p =(IDiq) SK 1 * SK 2 mod p =(IDiq mod p) SK 1 * SK 2 mod p =(IDd) SK 1 * SK 2 mod p = PWd mod p 6
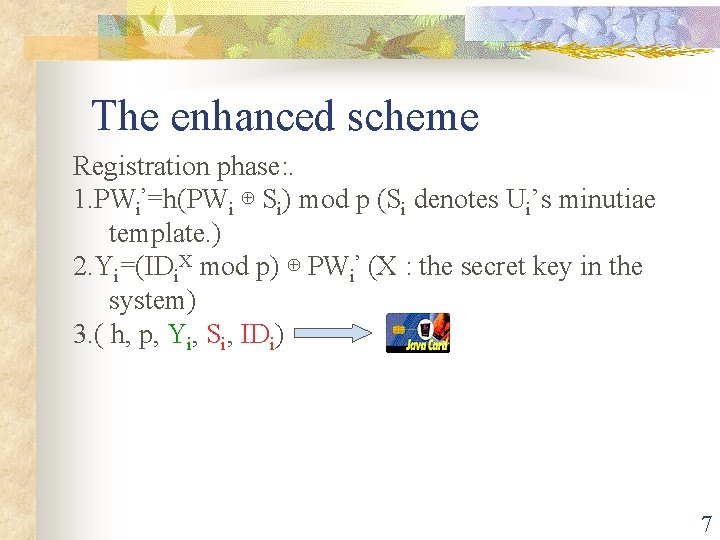
The enhanced scheme Registration phase: . 1. PWi’=h(PWi ⊕ Si) mod p (Si denotes Ui’s minutiae template. ) 2. Yi=(IDi. X mod p) ⊕ PWi’ (X : the secret key in the system) 3. ( h, p, Yi, Si, IDi) 7
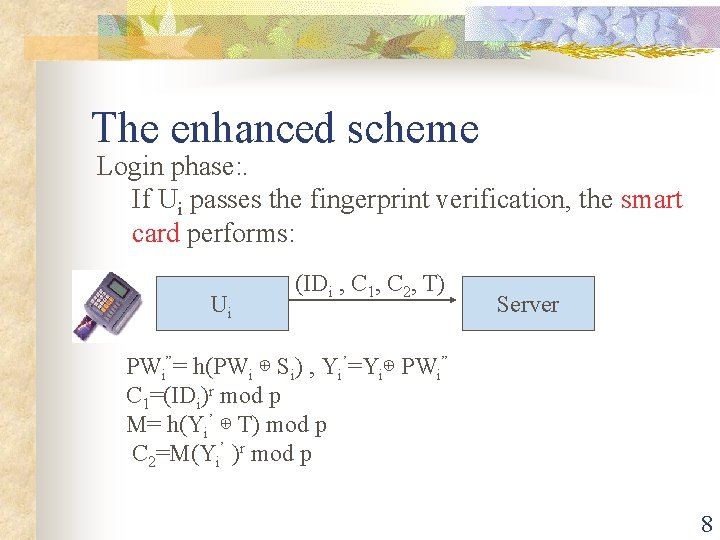
The enhanced scheme Login phase: . If Ui passes the fingerprint verification, the smart card performs: Ui (IDi , C 1, C 2, T) Server PWi”= h(PWi ⊕ Si) , Yi’=Yi⊕ PWi” C 1=(IDi)r mod p M= h(Yi’ ⊕ T) mod p C 2=M(Yi’ )r mod p 8
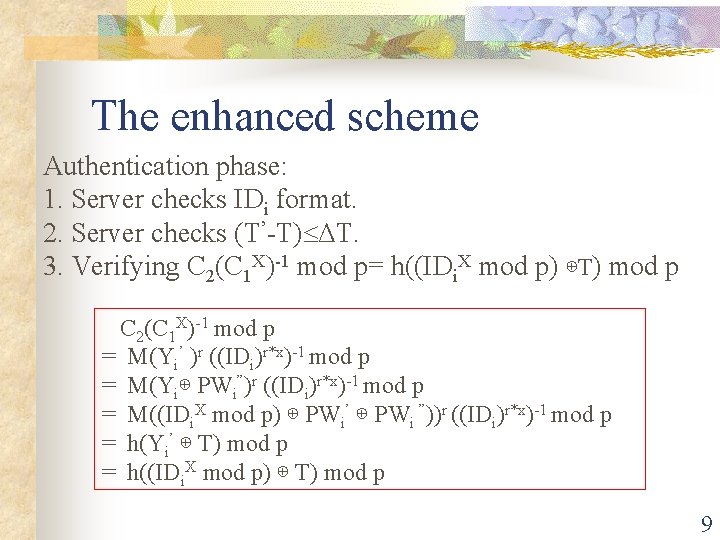
The enhanced scheme Authentication phase: 1. Server checks IDi format. 2. Server checks (T’-T) ΔT. 3. Verifying C 2(C 1 X)-1 mod p= h((IDi. X mod p) ⊕T) mod p C 2(C 1 X)-1 mod p = M(Yi’ )r ((IDi)r*x)-1 mod p = M(Yi⊕ PWi”)r ((IDi)r*x)-1 mod p = M((IDi. X mod p) ⊕ PWi’ ⊕ PWi ”))r ((IDi)r*x)-1 mod p = h(Yi’ ⊕ T) mod p = h((IDi. X mod p) ⊕ T) mod p 9
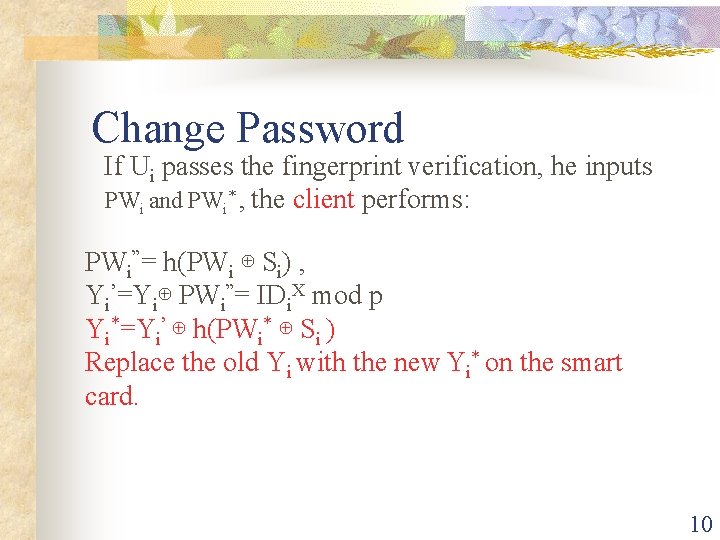
Change Password If Ui passes the fingerprint verification, he inputs PWi and PWi* , the client performs: PWi”= h(PWi ⊕ Si) , Yi’=Yi⊕ PWi”= IDi. X mod p Yi*=Yi’ ⊕ h(PWi* ⊕ Si ) Replace the old Yi with the new Yi* on the smart card. 10
Conclusions n n n The Lee-Ryu-Yoo scheme is vulnerable to masquerade attack. The enhance scheme allows users to choose and change their passwords conveniently. The system keeps only one secret key. 11
- Slides: 11