Web Application Bug Hunting About Me Who I

Web Application Bug Hunting
About Me. . . Who I am: Who I am NOT: • Nick Wender • Software Engineer at Tech. Smith • Amateur bug bounty hunter • Not a tester! • Not a security expert • Not a web expert
About You. . . • How many testers? • Any developers? • Any managers? • Who works with web applications?
About this talk. . . • Topic is too large for this talk • Hopefully a good introduction. . . • … And you leave knowing your next steps
Overview • Web application overview • Common vulnerabilities • Looking for bugs & useful tools • Resources
Web Application Overview
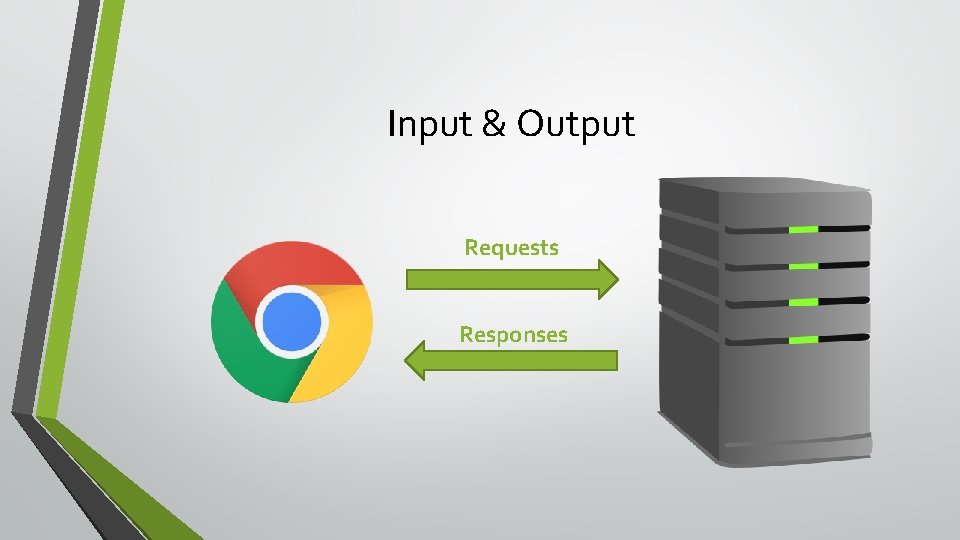
Input & Output Requests Responses
In Browser
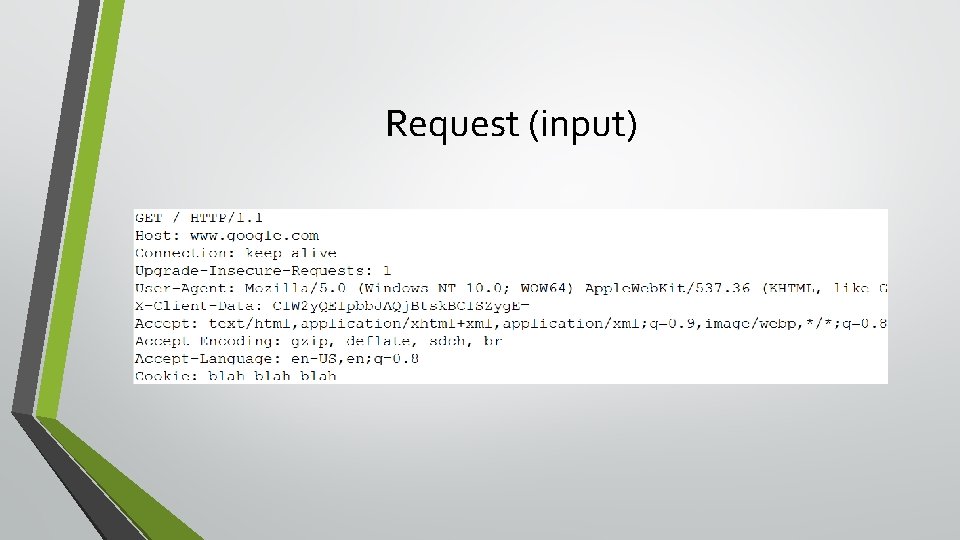
Request (input)
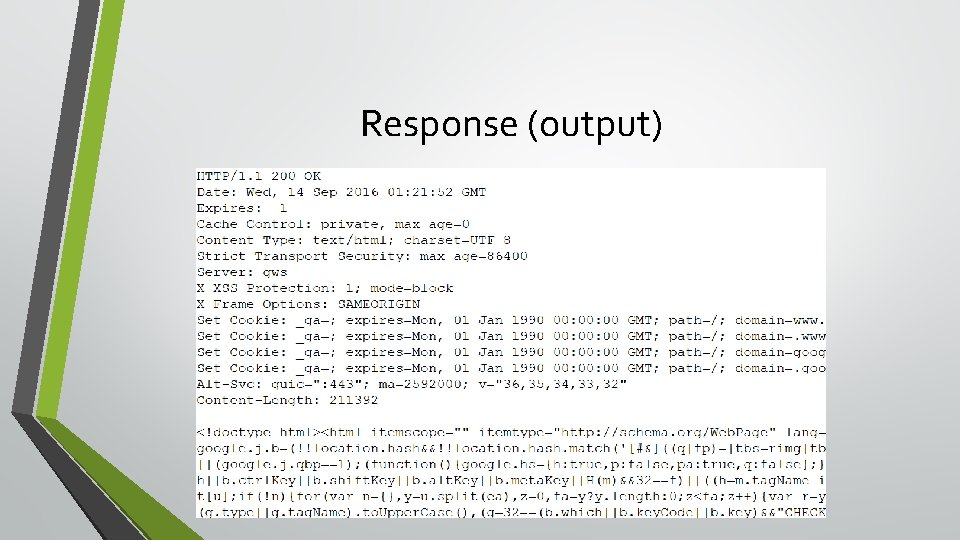
Response (output)
Access Control • Web apps need to give you a way to prove who you are • Often use cookies or request headers

Common Vulnerabilities
Some Security Terms • Vulnerability vs. Bug • Exploit • Risk
Common Vulnerabilities • Who has heard of the OWASP Top 10? • Ten most common web application vulnerabilities • Let's get familiar with a couple. . .
Vulnerabilities • Cross-Site Scripting (XSS) • Insecure Direct Object Reference (IDOR)
Cross-Site Scripting (XSS) • Injection of Java. Script • Often allows attacks against other users • Wide ranging possibilities for attackers
Cross-Site Scripting (XSS) • https: //hackerone. com/reports/125027 • Attacker could hijack developer accounts and apps
XSS Example #1
XSS Example #1 • Hacker. One researcher albinowax found XSS on developer. uber. com • https: //hackerone. com/reports/125027 • Could have been used to take control of developers accounts and apps • Consequence of not sanitizing user input • Uber paid a $3, 000 bounty
XSS Example #2
XSS Example #2 • Hacker. One researcher siddiki found XSS through insecure redirect on love. uber. com • https: //hackerone. com/reports/117068 • Failure to sanitize redirect parameter • Could use javascript: //alert('XSS example') • Uber paid a $3, 000 bounty
Insecure Direct Object Reference (IDOR) • Failure to ensure authorization • Consequences wide ranging • Easy to find and easy to exploit
IDOR Example #1
IDOR Example #1 • Hacker. One researcher tfairane found way to chane any Vimeo user's password • https: //hackerone. com/reports/42587 • Used reset password feature, only required knowing other user's ID • Account IDs could be looked up on another page • Vimeo paid a $5, 000 bounty
IDOR Example #2
• IDOR Example #2 • Hacker. One researcher secgeek found way to delete any user's credit card from ads. twitter. com • https: //hackerone. com/reports/27404 • Simply had to change credit card identifier • Credit card identifiers were just 6 numbers • Twitter paid a $2, 800 bounty
Needle in Haystack • The flaws may be simple • Finding them is where the work lies
Looking for Bugs
Looking for bugs is. . . • … about testing assumptions • … often tedious • … often boring • … rewarding when you find a good bug
Disclaimer • Assuming you have permission to look for flaws
Useful tools • Intercepting proxy • • Great for observing requests & responses Great for bypassing client-side validation and controls Fiddler on Windows Charles on Mac • Browser dev tools • Edit. This. Cookie
Simple Steps 1. Gather information 2. Identify requests of interest 3. Replay and evaluate
Gather Information • Start your proxy • Interact with the website through your browser
Interesting Requests • Review the requests your proxy captured • Think about: "What happens if I change this? "
Interesting Requests: XSS • Requests that accept your input • Commenting, user profile, and so on • Look for responses or pages where your input comes back • Especially interesting if shown to other users
Interesting Requests: IDOR • For insecure direct object reference • • Data or account modification Retrieval of sensitive information • Think about "How does the site know I am authorized? "
Replay and Evaluate • Use proxy to replay requests • Modify requests • Observe the responses
Replay and Evaluate: IDOR • Remove or change authorization from request • Modify resource identifiers or other parameters • Should be rejected
Replay and Evaluate: XSS • Try submitting Java. Script or HTML • https: //www. owasp. org/index. php/XSS_Filter_Evasion_Cheat_Sheet • Should be safely displayed • Very much depends on context
Automation • Automation is a time saver • Use it to augment your testing • Plenty of good vulnerability scanners available • Use them if you want • Make effort to understand verify what scanners find
I've found a vulnerability, now what? • Proof of concept exploit is pretty much necessary • Describe the impact and consequences • Demos can be effective to drive the point home • Relate to similar bug in Big Company XYZ
Additional Resources Where can I learn more?
Books • Web Application Hacker's Handbook by Dafydd Stuttard • Tangled Webs by Michal Zalewski
Online • • Too many to list, honestly! Troy Hunt @albinowax @filedescriptor Hacker. One "Hacktivity" Reddit r/netsec Pluralsight - Highly recommend Troy Hunt's courses

Hands-on • Google Gruyere • Google XSS Game • Damn Vulnerable Web App
- Slides: 45