Transport Layer Ilam University Dr Mozafar BagMohammadi 1
Transport Layer Ilam University Dr. Mozafar Bag-Mohammadi 1
Outline n n Connection Establishment/Termination Sliding Window Revisited Flow Control Adaptive Timeout 2
End-to-End Protocols n Underlying best-effort network q q q n drop messages re-orders messages delivers duplicate copies of a given message limits messages to some finite size delivers messages after an arbitrarily long delay Common end-to-end services q q q q guarantee message delivery deliver messages in the same order they are sent deliver at most one copy of each message support arbitrarily large messages support synchronization allow the receiver to flow control the sender support multiple application processes on each host 3
Transport Layer Function(s) n n Multiplexing/demultiplexing between network application processes. Others? q q q n n Error Detection within a segment Reliability Flow Control. Congestion control. Connection Management. Difference between Error detection and reliability? Difference between flow control and congestion control? 4
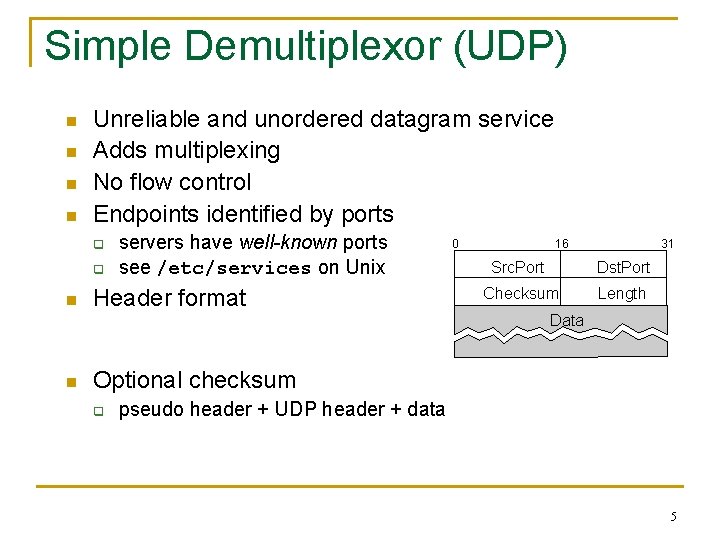
Simple Demultiplexor (UDP) n n Unreliable and unordered datagram service Adds multiplexing No flow control Endpoints identified by ports q q n n servers have well-known ports see /etc/services on Unix Header format 0 16 31 Src. Port Dst. Port Checksum Length Data Optional checksum q pseudo header + UDP header + data 5
Using UDP n Non-standard protocols can be implemented on top of UDP. q q q n Non-standard = non-TCP in practice use the port addressing provided by UDP implement their own reliability, flow control, ordering, congestion control ? Examples: q q q remote procedure calls multimedia distributed computing 6
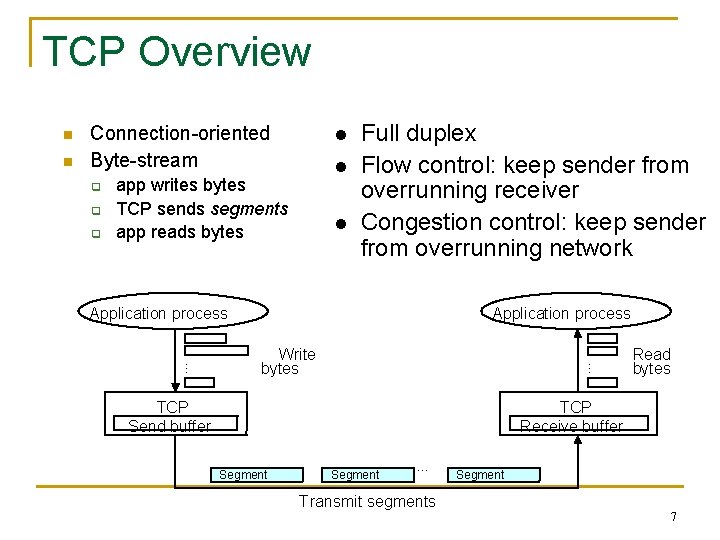
TCP Overview q q q l l app writes bytes TCP sends segments app reads bytes l Full duplex Flow control: keep sender from overrunning receiver Congestion control: keep sender from overrunning network Application process Write bytes … n Connection-oriented Byte-stream … n TCP Send buffer Read bytes TCP Receive buffer Segment … Segment Transmit segments 7
High level TCP Characteristics n Connection-oriented reliable byte-stream protocol. q n Two way connections. q q n Used for file transfers, telnet, web access, …. control information for one direction piggy-backed on data flow in other direction header fields fall in three classes: general, forward flow, opposite flow Protocol has evolved over time and will continue to do so. q q Nearly impossible to change the header Uses options to add information to the header Change processing at endpoints Backward compatibility is what makes it TCP 8
Data Link Versus Transport n Potentially connects many different hosts (logical connection) q n Potentially different RTT q n n need explicit connection establishment and termination need adaptive timeout mechanism Potentially reordering packets. (How far? ), Maximum segment life time. Currently 120 sec. Potentially long delay in network q q q need to be prepared for arrival of very old packets Delay X bandwidth? Buffer size 9
Data Link Versus Transport (cont) n Potentially different capacity at destination q n need to accommodate different node capacity Potentially different network capacity q need to be prepared for network congestion 10
Data delivery in TCP n n TCP is byte oriented, however transmit data in segments (messages). How TCP knows the time for delivery? q q q Maximum Segment Size (MSS) Timer Pushed by the application. Like telnet. 11
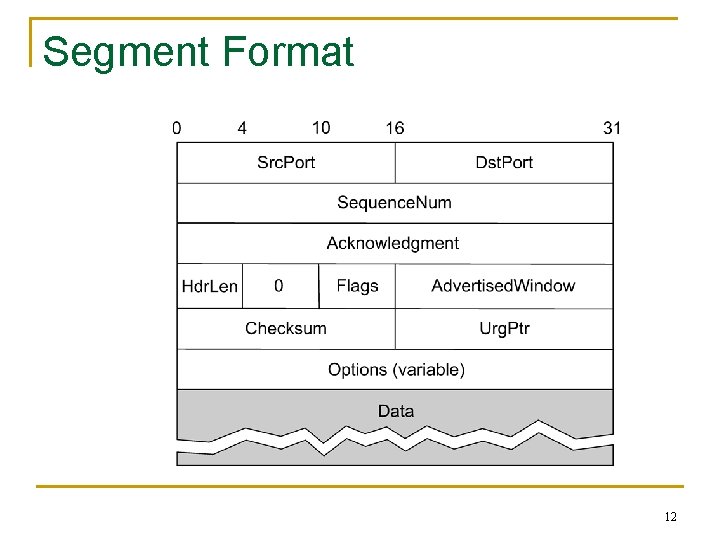
Segment Format 12
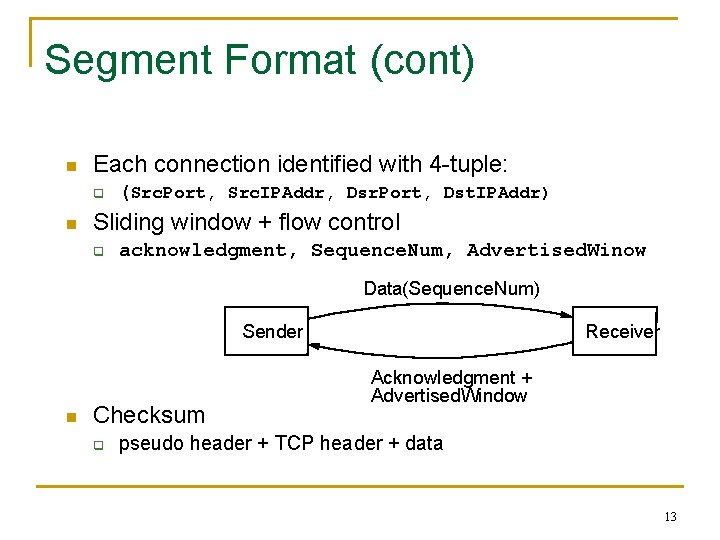
Segment Format (cont) n Each connection identified with 4 -tuple: q n (Src. Port, Src. IPAddr, Dsr. Port, Dst. IPAddr) Sliding window + flow control q acknowledgment, Sequence. Num, Advertised. Winow Data(Sequence. Num) Sender n Checksum q Receiver Acknowledgment + Advertised. Window pseudo header + TCP header + data 13
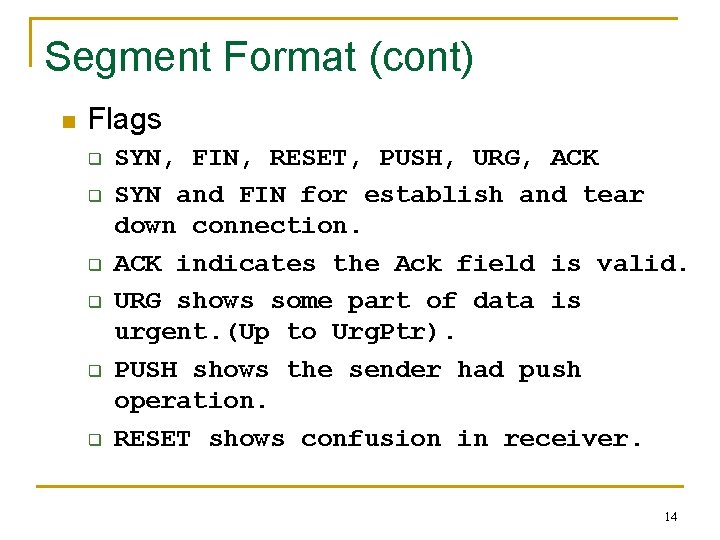
Segment Format (cont) n Flags q q q SYN, FIN, RESET, PUSH, URG, ACK SYN and FIN for establish and tear down connection. ACK indicates the Ack field is valid. URG shows some part of data is urgent. (Up to Urg. Ptr). PUSH shows the sender had push operation. RESET shows confusion in receiver. 14
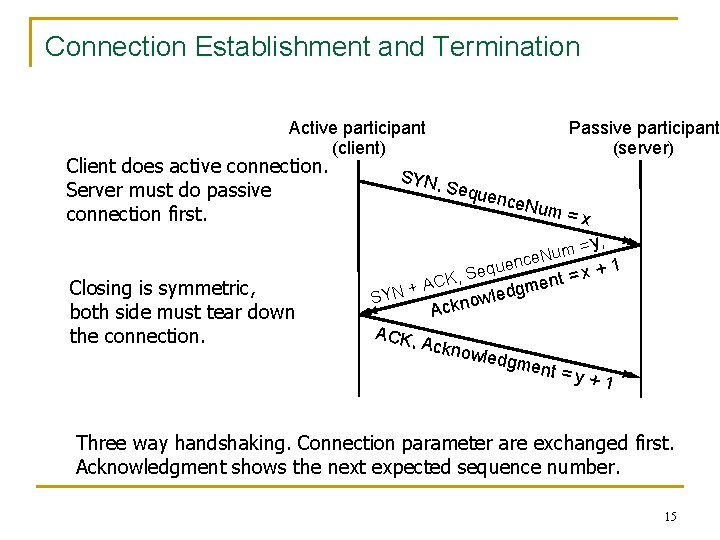
Connection Establishment and Termination Active participant (client) Client does active connection. Server must do passive connection first. Passive participant (server) SYN, S eque nce. N u m=x = m u N nce Closing is symmetric, both side must tear down the connection. SYN + ACK, que e S , ACK dgm e l w o ckn y, x+ = t n e 1 A Ackno wledg ment =y+1 Three way handshaking. Connection parameter are exchanged first. Acknowledgment shows the next expected sequence number. 15
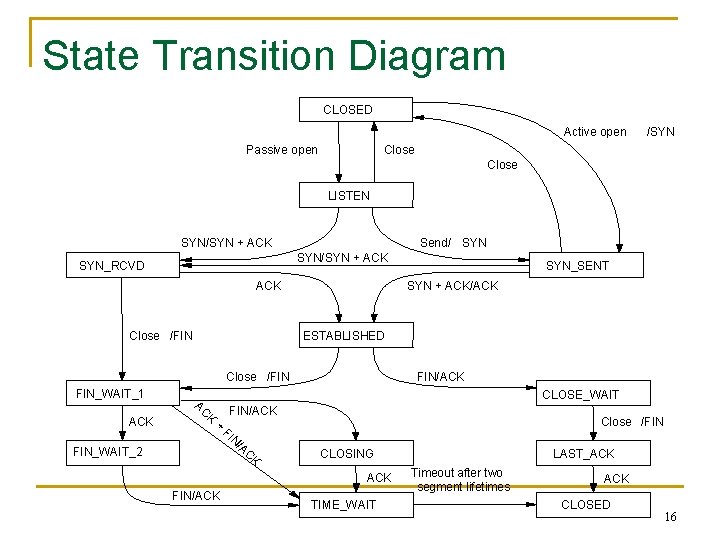
State Transition Diagram CLOSED Active open Passive open /SYN Close LISTEN SYN/SYN + ACK Send/ SYN/SYN + ACK SYN_RCVD ACK Close /FIN SYN + ACK/ACK ESTABLISHED Close /FIN FIN_WAIT_1 ACK SYN_SENT FIN/ACK CLOSE_WAIT AC K + FIN/ACK FI Close /FIN N FIN_WAIT_2 /A C K CLOSING ACK FIN/ACK TIME_WAIT LAST_ACK Timeout after two segment lifetimes ACK CLOSED 16
State Transition (cont) n n Sliding window is in ESTABLISHED. All connections start with CLOSED. Arcs are tagged with event/action. Triggering a transition. q q Arriving a segment from a peer. Envoking by an application. 17
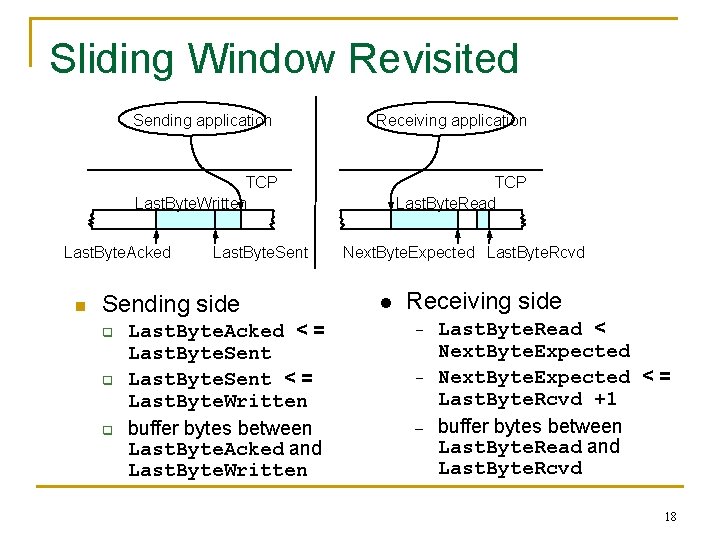
Sliding Window Revisited Sending application Receiving application TCP Last. Byte. Written Last. Byte. Acked n Last. Byte. Sent Sending side q q q Last. Byte. Acked < = Last. Byte. Sent < = Last. Byte. Written buffer bytes between Last. Byte. Acked and Last. Byte. Written TCP Last. Byte. Read Next. Byte. Expected Last. Byte. Rcvd l Receiving side – – – Last. Byte. Read < Next. Byte. Expected < = Last. Byte. Rcvd +1 buffer bytes between Last. Byte. Read and Last. Byte. Rcvd 18
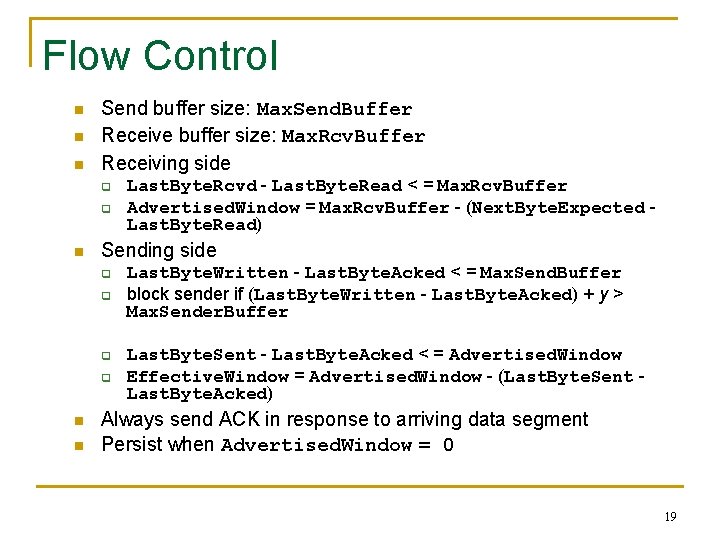
Flow Control n n n Send buffer size: Max. Send. Buffer Receive buffer size: Max. Rcv. Buffer Receiving side q q n Sending side q q n n Last. Byte. Rcvd - Last. Byte. Read < = Max. Rcv. Buffer Advertised. Window = Max. Rcv. Buffer - (Next. Byte. Expected Last. Byte. Read) Last. Byte. Written - Last. Byte. Acked < = Max. Send. Buffer block sender if (Last. Byte. Written - Last. Byte. Acked) + y > Max. Sender. Buffer Last. Byte. Sent - Last. Byte. Acked < = Advertised. Window Effective. Window = Advertised. Window - (Last. Byte. Sent Last. Byte. Acked) Always send ACK in response to arriving data segment Persist when Advertised. Window = 0 19
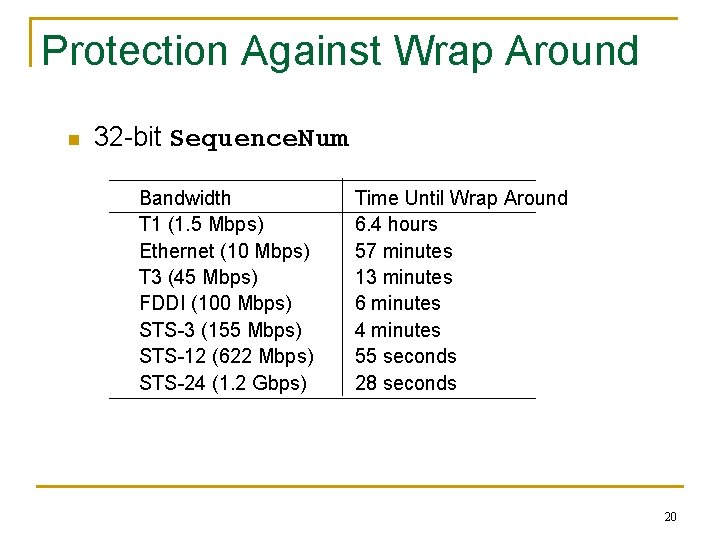
Protection Against Wrap Around n 32 -bit Sequence. Num Bandwidth T 1 (1. 5 Mbps) Ethernet (10 Mbps) T 3 (45 Mbps) FDDI (100 Mbps) STS-3 (155 Mbps) STS-12 (622 Mbps) STS-24 (1. 2 Gbps) Time Until Wrap Around 6. 4 hours 57 minutes 13 minutes 6 minutes 4 minutes 55 seconds 28 seconds 20
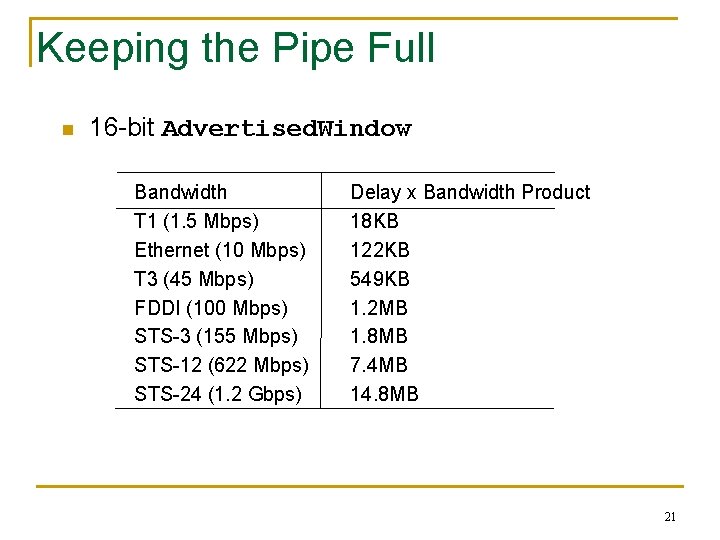
Keeping the Pipe Full n 16 -bit Advertised. Window Bandwidth T 1 (1. 5 Mbps) Ethernet (10 Mbps) T 3 (45 Mbps) FDDI (100 Mbps) STS-3 (155 Mbps) STS-12 (622 Mbps) STS-24 (1. 2 Gbps) Delay x Bandwidth Product 18 KB 122 KB 549 KB 1. 2 MB 1. 8 MB 7. 4 MB 14. 8 MB 21
TCP Extensions n n Implemented as header options Store timestamp in outgoing segments Extend sequence space with 32 -bit timestamp (PAWS) Shift (scale) advertised window 22
Adaptive Retransmission (Original Algorithm) n n Measure Sample. RTT for each segment/ ACK pair Compute weighted average of RTT q q - n Est. RTT = a x Est. RTT + b x Sample. RTT where a + b = 1 a between 0. 8 and 0. 9 b between 0. 1 and 0. 2 Set timeout based on Est. RTT q Time. Out = 2 x Est. RTT 23
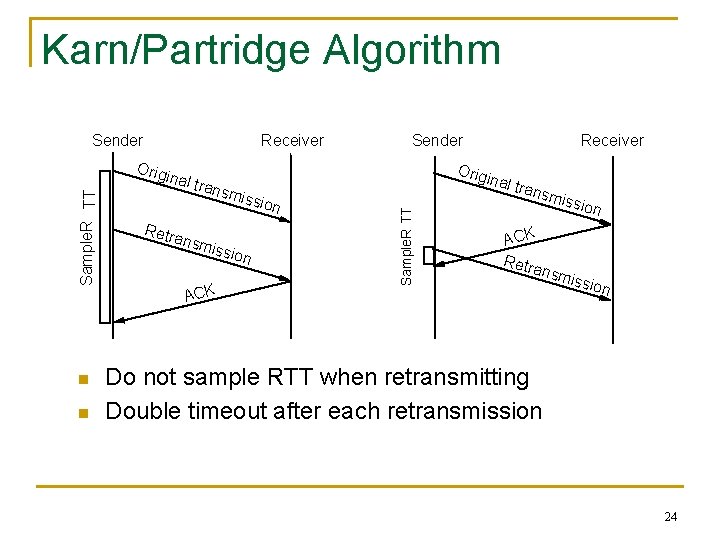
Karn/Partridge Algorithm Sender Receiver n n inal t inal rans m Retr issio n ansm issio n ACK Receiver Orig Sample. R TT Orig Sender trans miss ion ACK Retr ansm is sion Do not sample RTT when retransmitting Double timeout after each retransmission 24
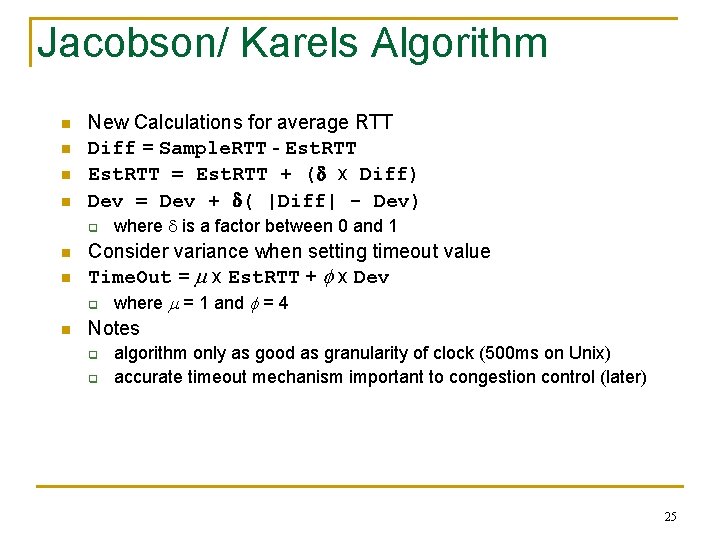
Jacobson/ Karels Algorithm n n New Calculations for average RTT Diff = Sample. RTT - Est. RTT = Est. RTT + (d x Diff) Dev = Dev + d( |Diff| - Dev) q n n n where d is a factor between 0 and 1 Consider variance when setting timeout value Time. Out = m x Est. RTT + f x Dev q where m = 1 and f = 4 Notes q q algorithm only as good as granularity of clock (500 ms on Unix) accurate timeout mechanism important to congestion control (later) 25
- Slides: 25