The Zig Bee Networking Layer Speaker Chang KaiJia
The Zig. Bee Networking Layer Speaker : Chang Kai-Jia Date : 2010/5/26 1
Contents � Zig. Bee and IEEE 802. 15. 4 � Forming, Joining, and Rejoining Zig. Bee Networks ◦ Forming Networks ◦ Joining Networks ◦ Rejoining Networks � Zig. Bee Address Assignment � Broadcasts � Mesh Routing � Zig. Bee Over-the-Air Frames � Zig. Bee Stack Profiles 2
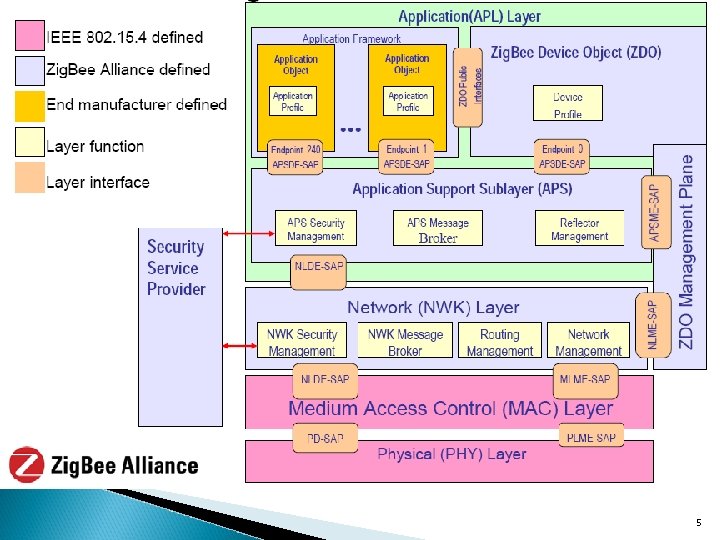
5
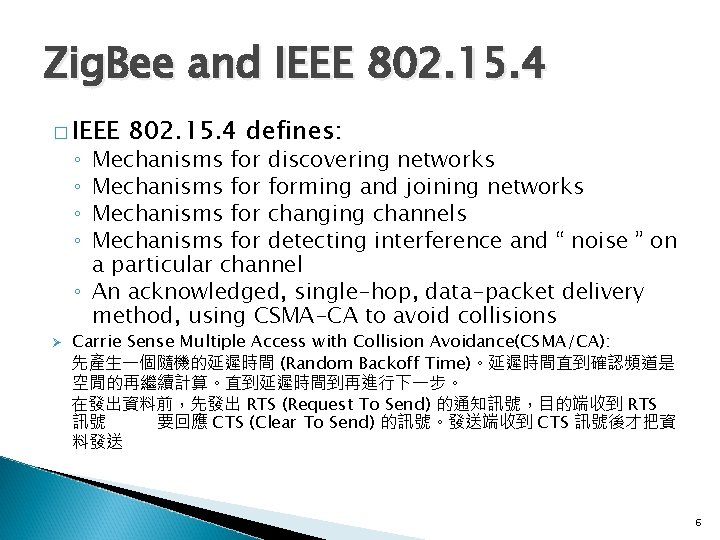
Zig. Bee and IEEE 802. 15. 4 � IEEE 802. 15. 4 defines: Mechanisms for discovering networks Mechanisms forming and joining networks Mechanisms for changing channels Mechanisms for detecting interference and “ noise ” on a particular channel ◦ An acknowledged, single-hop, data-packet delivery method, using CSMA-CA to avoid collisions ◦ ◦ Ø Carrie Sense Multiple Access with Collision Avoidance(CSMA/CA): 先產生一個隨機的延遲時間 (Random Backoff Time)。延遲時間直到確認頻道是 空閒的再繼續計算。直到延遲時間到再進行下一步。 在發出資料前,先發出 RTS (Request To Send) 的通知訊號,目的端收到 RTS 訊號後必須要回應 CTS (Clear To Send) 的訊號。發送端收到 CTS 訊號後才把資 料發送出去。 6
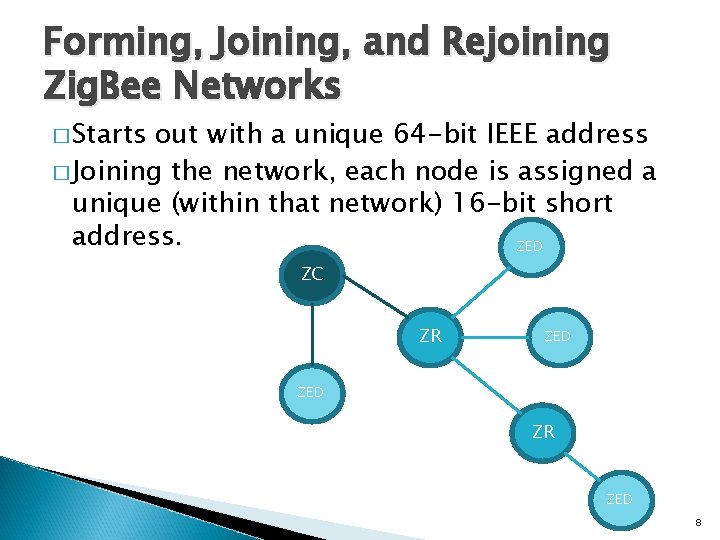
Forming, Joining, and Rejoining Zig. Bee Networks � Starts out with a unique 64 -bit IEEE address � Joining the network, each node is assigned a unique (within that network) 16 -bit short address. ZED ZC ZR ZED 8
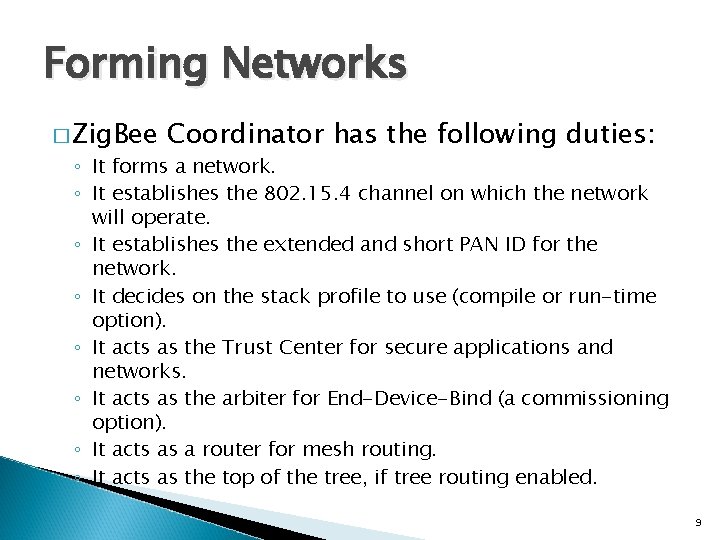
Forming Networks � Zig. Bee Coordinator has the following duties: ◦ It forms a network. ◦ It establishes the 802. 15. 4 channel on which the network will operate. ◦ It establishes the extended and short PAN ID for the network. ◦ It decides on the stack profile to use (compile or run-time option). ◦ It acts as the Trust Center for secure applications and networks. ◦ It acts as the arbiter for End-Device-Bind (a commissioning option). ◦ It acts as a router for mesh routing. ◦ It acts as the top of the tree, if tree routing enabled. 9
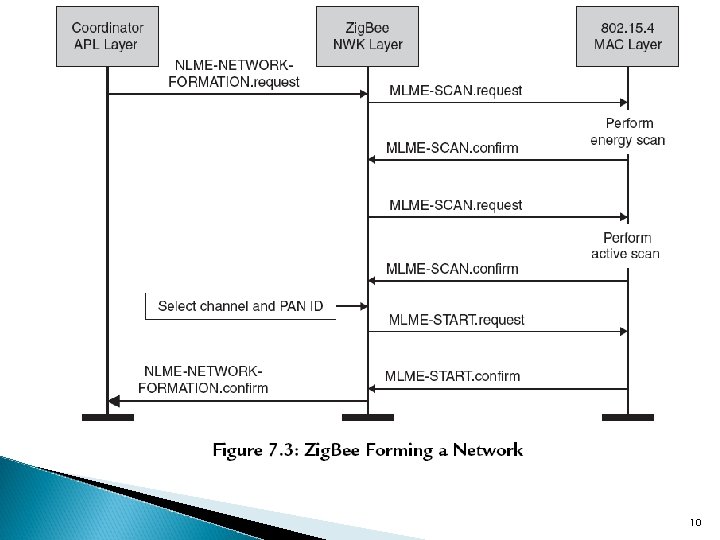
10
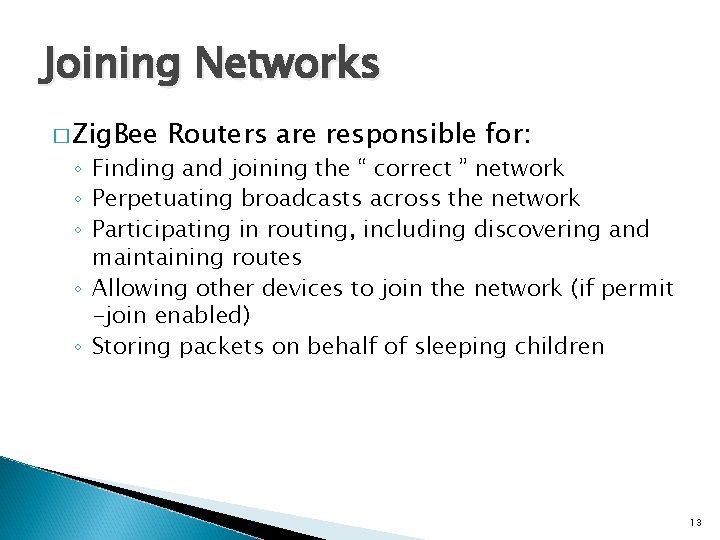
Joining Networks � Zig. Bee Routers are responsible for: ◦ Finding and joining the “ correct ” network ◦ Perpetuating broadcasts across the network ◦ Participating in routing, including discovering and maintaining routes ◦ Allowing other devices to join the network (if permit -join enabled) ◦ Storing packets on behalf of sleeping children 13
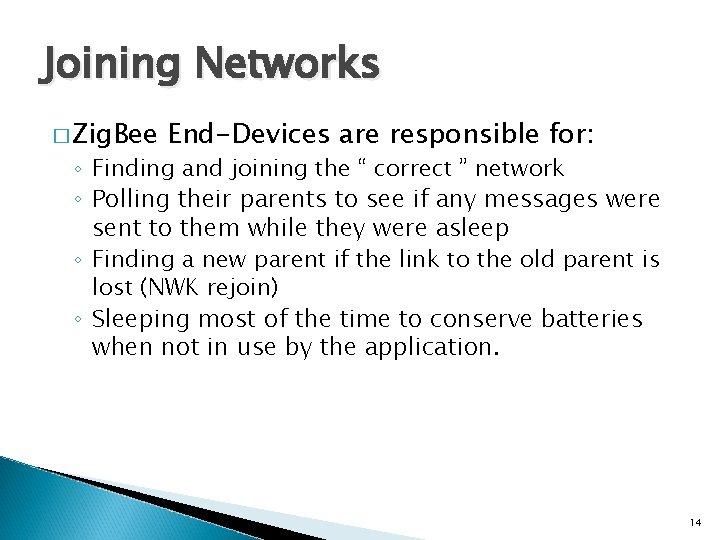
Joining Networks � Zig. Bee End-Devices are responsible for: ◦ Finding and joining the “ correct ” network ◦ Polling their parents to see if any messages were sent to them while they were asleep ◦ Finding a new parent if the link to the old parent is lost (NWK rejoin) ◦ Sleeping most of the time to conserve batteries when not in use by the application. 14
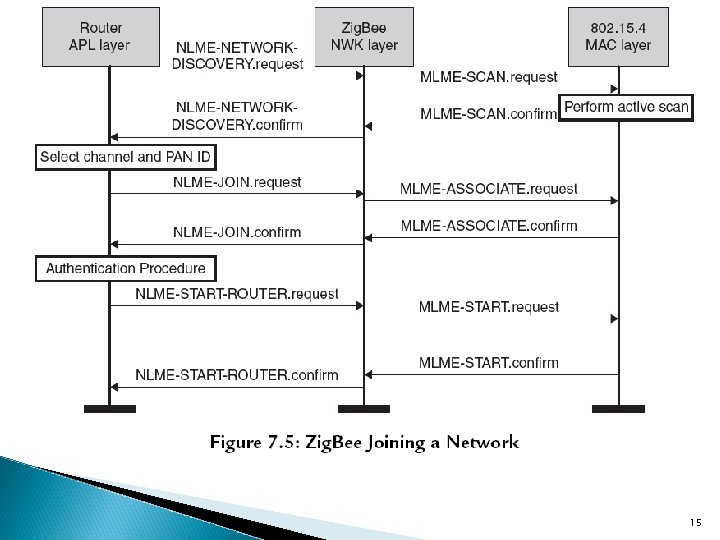
15
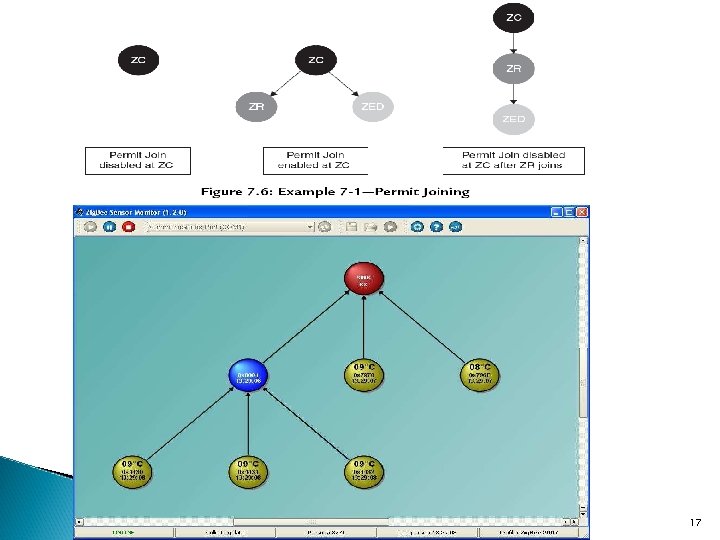
17
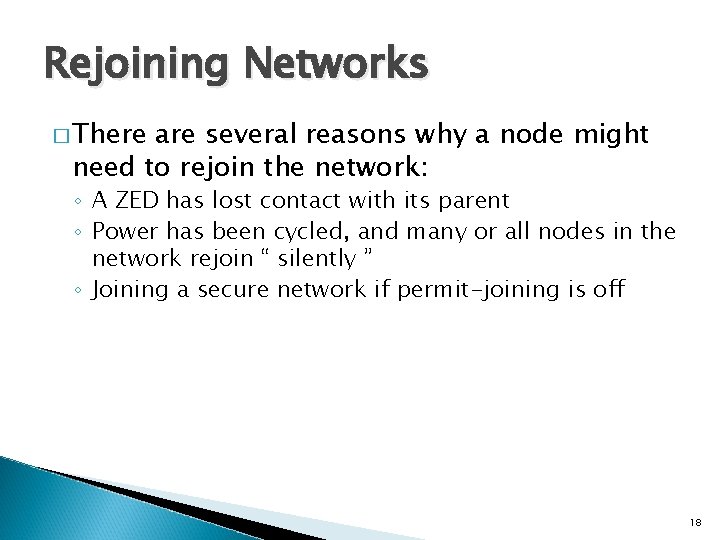
Rejoining Networks � There are several reasons why a node might need to rejoin the network: ◦ A ZED has lost contact with its parent ◦ Power has been cycled, and many or all nodes in the network rejoin “ silently ” ◦ Joining a secure network if permit-joining is off 18
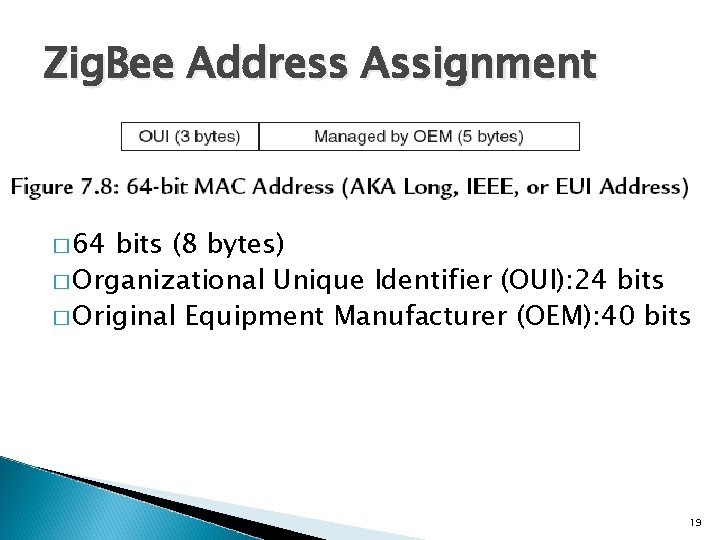
Zig. Bee Address Assignment � 64 bits (8 bytes) � Organizational Unique Identifier (OUI): 24 bits � Original Equipment Manufacturer (OEM): 40 bits 19
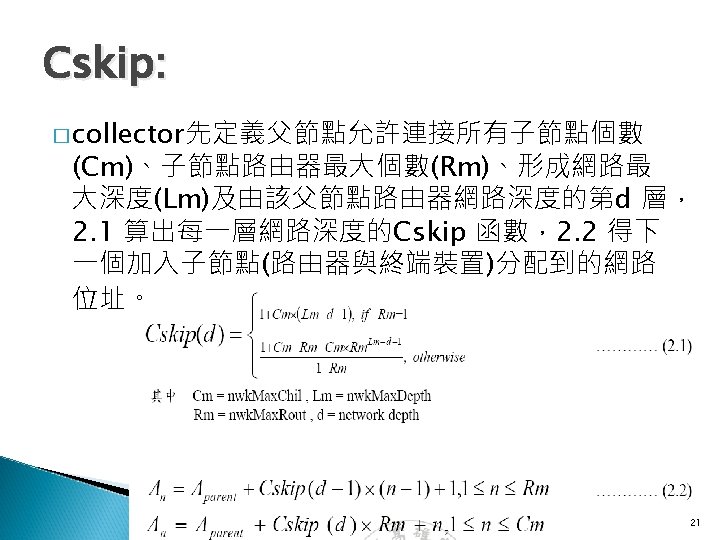
� Zig. Bee uses one of two address schemes to assign the short address: ◦ Cskip �Cskip address assignment, available in stack profile 0 x 01 (the stack profile simply called Zig. Bee) �stack profile 0 x 01 uses a calculated number for each “ depth ” (the number of hops from the Zig. Bee Coordinator), called Cskip (child skip). �allows tree routing in addition to mesh. ◦ Stochastic (random) �Stochastic addressing is available in stack profile 0 x 02 (the stack profile called Zig. Bee Pro). 20
Zig. Bee Packet Routing � Zig. Bee employs a variety of methods for routing packets from one node to another: ◦ Broadcasting (from one to many nodes) ◦ Mesh routing (unicast from one node to another) ◦ Tree routing (unicast from one node to another, stack profile 0 x 01 only) ◦ Source routing (unicast from one node to another, stack profile 0 x 02 only) 23
Broadcasts � Zig. Bee does allow a radius of 0 x 00, which is a special flag that means to repeat the broadcast for the entire network. � This radius set from 0 x 01 to 0 xff, to indicate an actual maximum distance. � There are three special Zig. Bee broadcast modes: ◦ 0 xffff—broadcast to all nodes (even sleeping ZEDs) ◦ 0 xfffd—broadcast to all awake devices (including Rx. On. Idle =TRUE ZEDs) ◦ 0 xfffc—broadcast to all routers (excludes all ZEDs) Ø Ch 4 -Zig. Bee Applications 24
Broadcasts � The Broadcast Transaction Table(BTT) is a critical component of broadcasting. � Broadcasting transmits from one node to many nodes, up to the entire network. � Use broadcasts sparingly, as they consume a lot of bandwidth and resources. � Broadcasts are slow compared to unicasts. Ø Appendix A, “ Zig. Bee 2007 and Zig. Bee Pro, “ 25
Broadcast Transaction Table(BTT) � The record that was created actually goes into a table called the Broadcast Transaction Table or BTT. ◦ when a broadcast is transmitted, all devices that receive it will broadcast a copy. ◦ Each time a copy of the broadcast arrives, the address of the sender will be added to the BTT to mark that it has relayed the broadcast. ◦ After a broadcast timeout, if all neighbors haven’t relayed the broadcast, meaning they aren’t present in the BTT, then the original sender will need to do a broadcast retry. 26
Mesh Routing � In Zig. Bee mesh: ◦ The algorithm is based on the publicly available Advanced Adhoc On-Demand Distance Vectoring (AODV). ◦ All routers are peers. ◦ The route is distributed: Each node in the route keeps track of the next hop for the route in a routing table. ◦ Routes are unidirectional (a route must be discovered each way for bidirectional communication). ◦ Routes are like goat trails: they continue to be used until they fail. ◦ Failed routes are communicated back to the originating node, allowing it to discover a new route. Ø Ad hoc On-Demand Distance Vector (AODV): RFC 3561 27
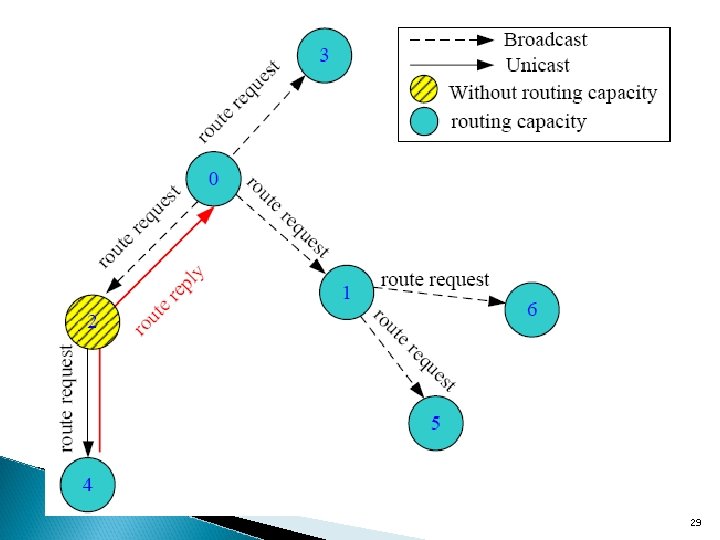
29
Mesh Routing � Routes are discovered automatically by Zig. Bee. � Zig. Bee Mesh route discovery is initiated when a node sends a packet to another node. � Routes are discovered along the least cost path. 31
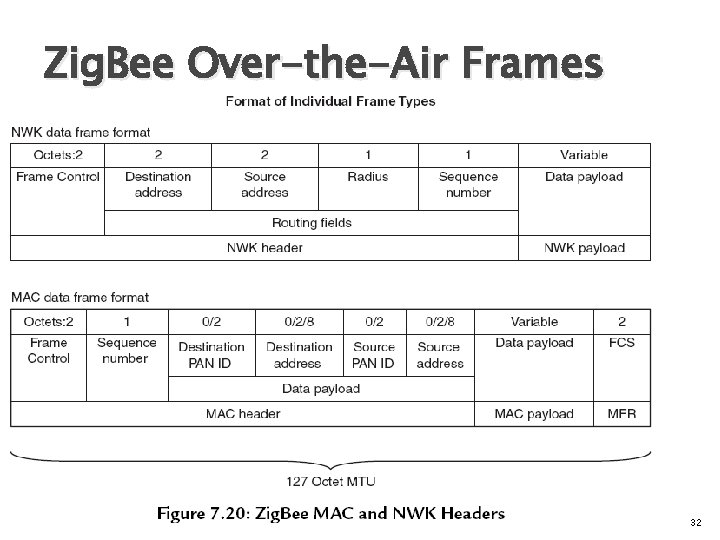
Zig. Bee Over-the-Air Frames 32
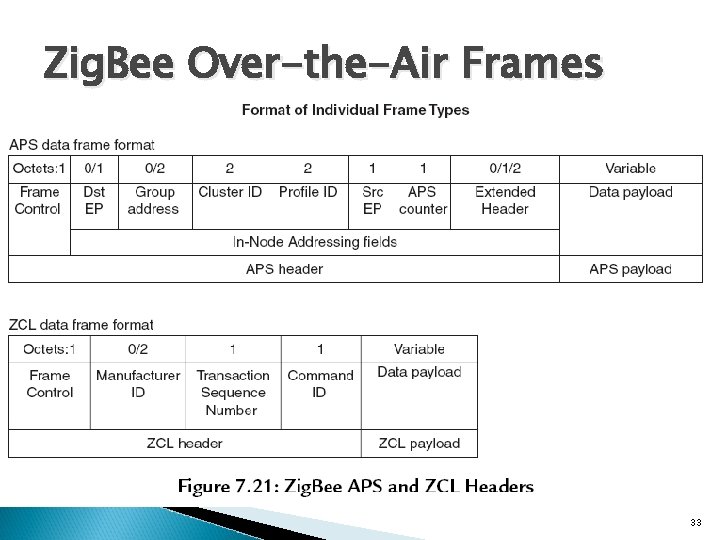
Zig. Bee Over-the-Air Frames 33
Zig. Bee Stack Profiles � Stack profile 0 x 01 tends to be used in applications where cost is one of the major concerns. Its main characteristics are: ◦ ◦ Predictable address assignment Tree routing Smaller code size Up to 10 hops in the network 34
Zig. Bee Stack Profiles � Stack profile 0 x 02 tends be used where cost is less of an issue, and larger networks are more important. Its main characteristics are: ◦ ◦ ◦ Random (stochastic) address assignment Source routing Multicast Larger code size Up to 30 hops in the network 35
Zig. Bee Stack Profiles � There are two Zig. Bee stack profiles: 0 x 01 (Zig. Bee) and 0 x 02 (Zig. Bee Pro). � Stack Profiles define alternate routing methods and maximum number of hops. � Zig. Bee nodes may join either stack profile. 36
Reference: � The Handoff Procedure for Real Time Voice Communication in Zig. Bee Environment � Efficient Mechanism for GTS Allocation (EMGA) in. IEEE 802. 15. 4 LR-WPAN 38
- Slides: 32