The Proxy Pattern SE2811 Dr Mark L Hornick
- Slides: 14
The Proxy Pattern SE-2811 Dr. Mark L. Hornick 1
The Proxy Pattern has many variations, but in general: The Proxy Pattern uses an proxy object as a surrogate (aka stand-in or placeholder) that acts like another object SE-2811 Dr. Mark L. Hornick 2
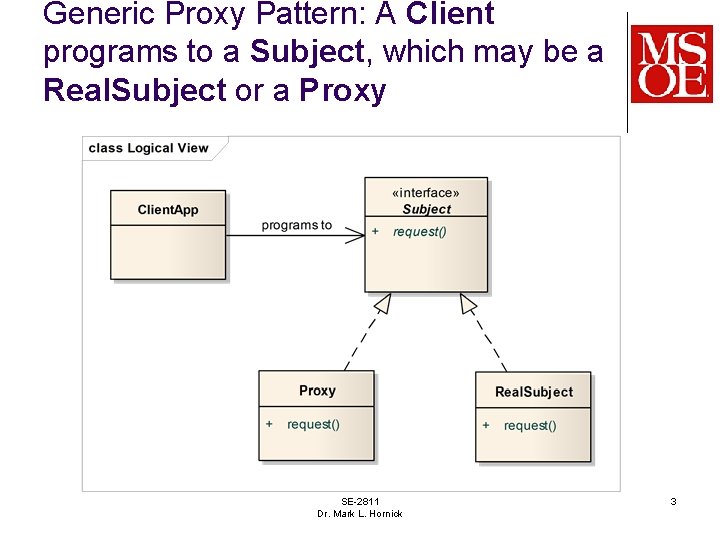
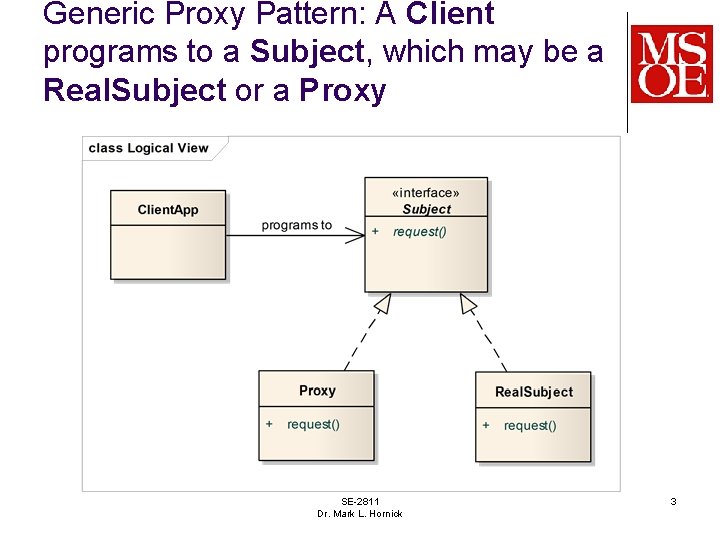
Generic Proxy Pattern: A Client programs to a Subject, which may be a Real. Subject or a Proxy SE-2811 Dr. Mark L. Hornick 3
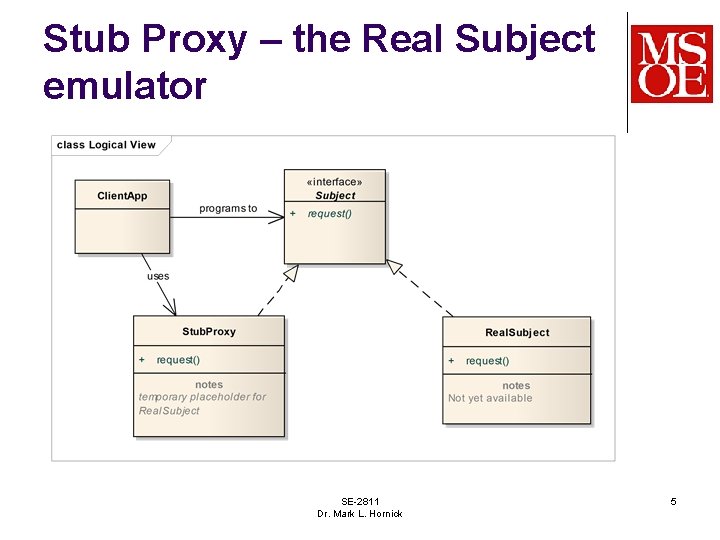
4 The Stub Proxy is a (temporary) placeholder for the Real Subject Sometimes the Real Subject is not available l For example: still under development The Stub Proxy can provide implementation of the Subject interface to varying degrees: 1. 2. 3. Just enough to compile without error To allow rudimentary Subject functionality To provide a complete emulation of the Real. Subject
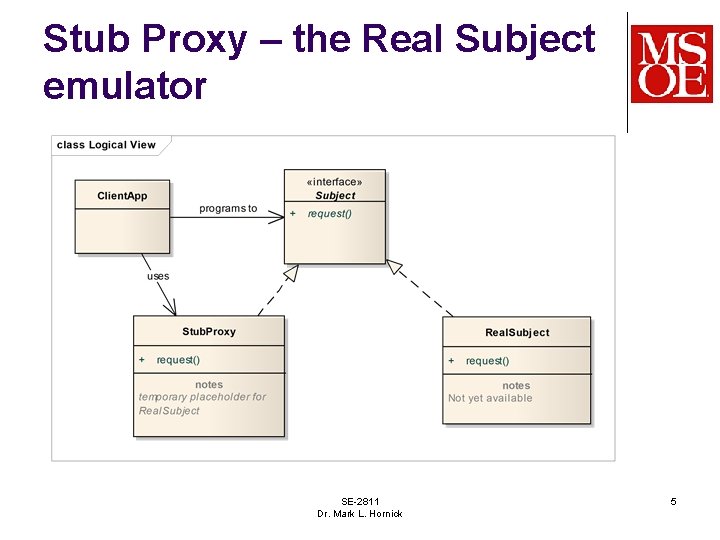
Stub Proxy – the Real Subject emulator SE-2811 Dr. Mark L. Hornick 5
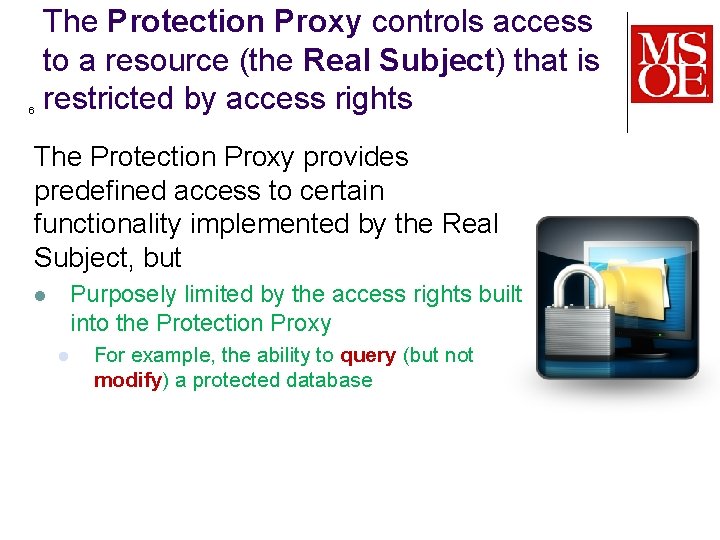
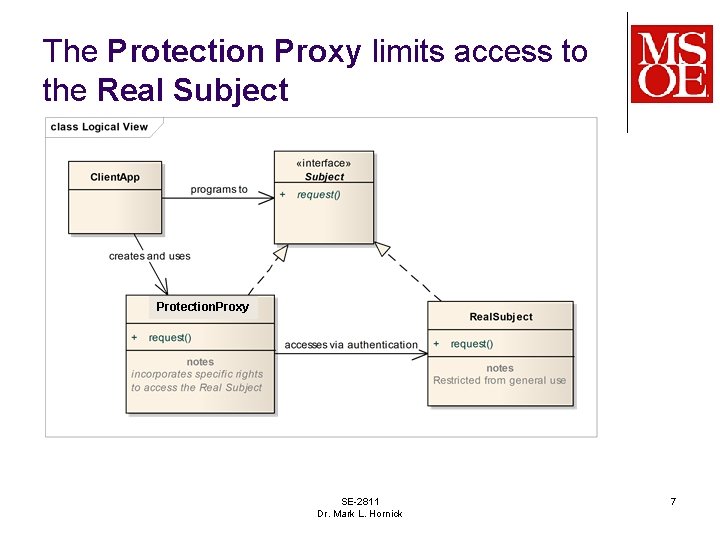
6 The Protection Proxy controls access to a resource (the Real Subject) that is restricted by access rights The Protection Proxy provides predefined access to certain functionality implemented by the Real Subject, but Purposely limited by the access rights built into the Protection Proxy l l For example, the ability to query (but not modify) a protected database
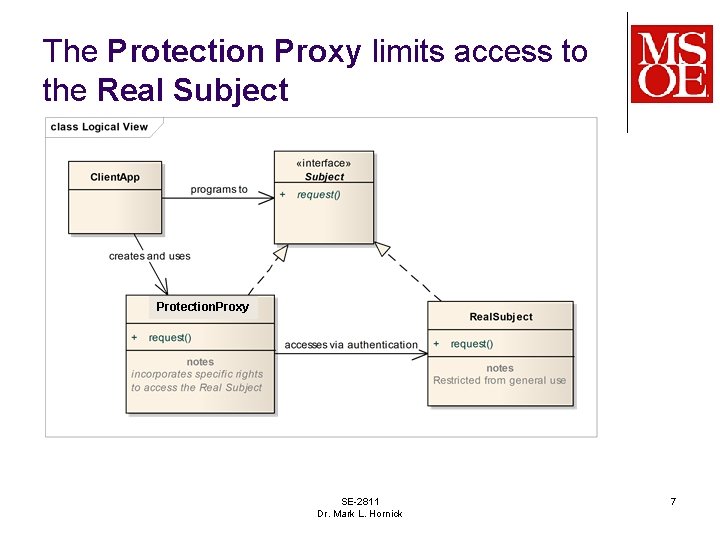
The Protection Proxy limits access to the Real Subject Protection. Proxy SE-2811 Dr. Mark L. Hornick 7
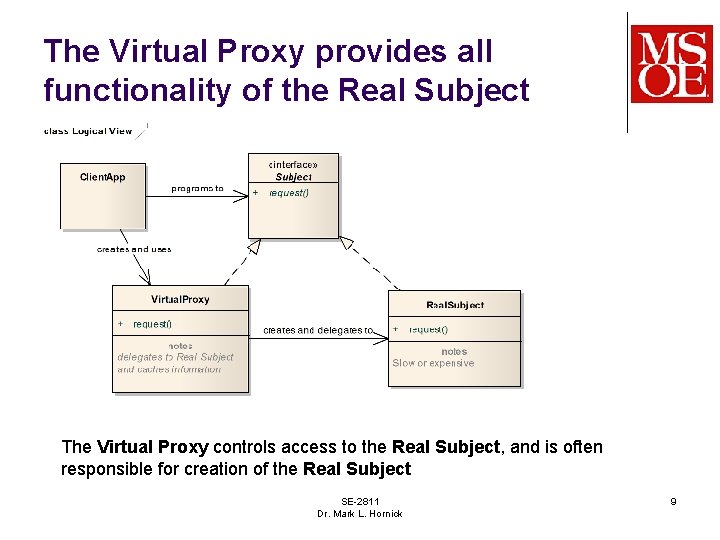
8 The Virtual Proxy controls access to a resource (the Real Subject) that is expensive to create or use The Virtual Proxy provides access to all of the functionality implemented by the Real Subject, but l l More quicky/cheaply Acts as a surrogate until the Real Subject becomes available
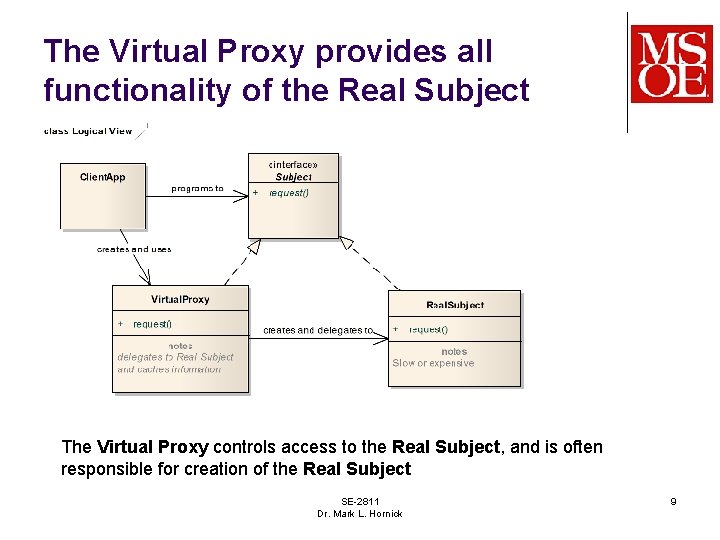
The Virtual Proxy provides all functionality of the Real Subject The Virtual Proxy controls access to the Real Subject, and is often responsible for creation of the Real Subject SE-2811 Dr. Mark L. Hornick 9
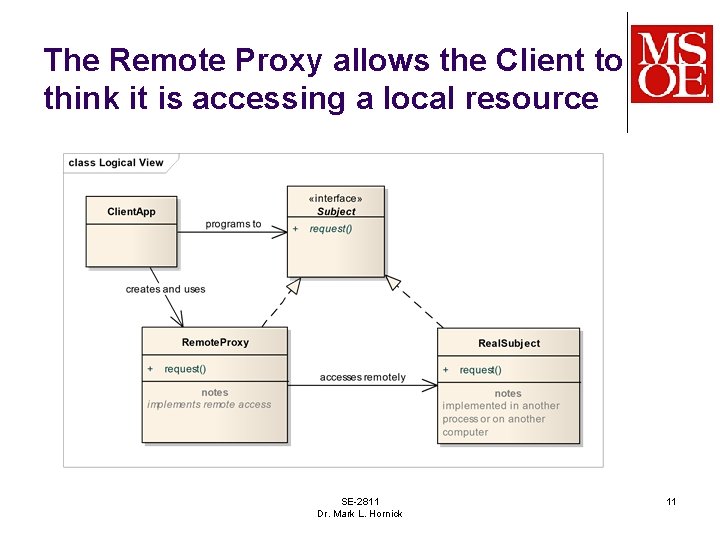
10 The Remote Proxy provides local access to a remote resource (the Real Subject) The Remote Proxy handles the details of accessing a remote resource Remote Access can be implemented in many different ways, using different communication protocols l l l Simple sockets Remote Method Invocation HTTP-based (e. g. web-services) …
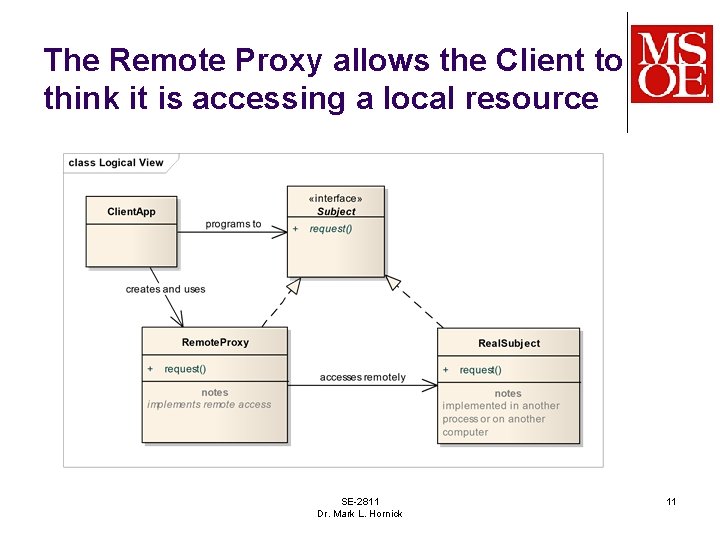
The Remote Proxy allows the Client to think it is accessing a local resource SE-2811 Dr. Mark L. Hornick 11
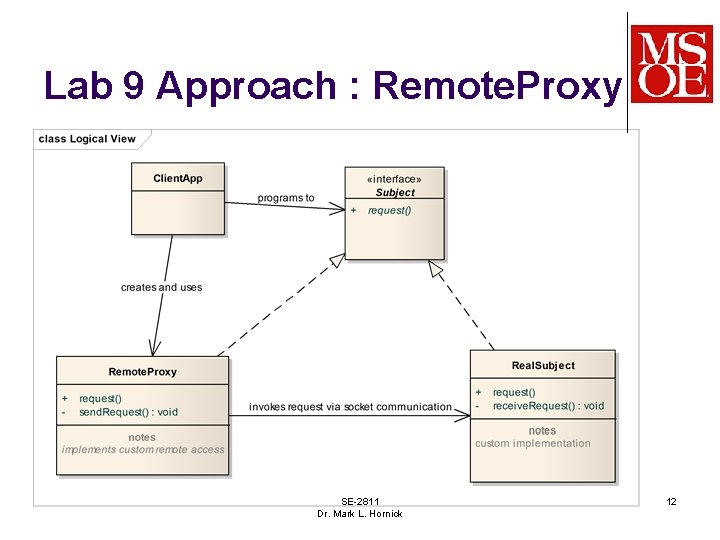
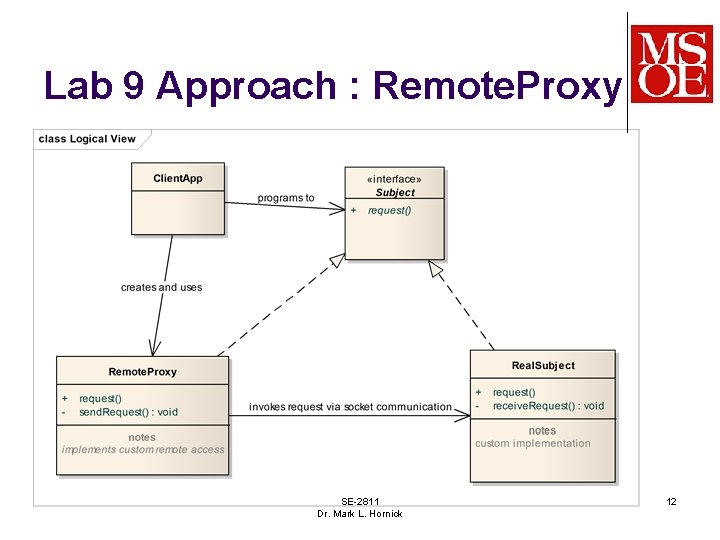
Lab 9 Approach : Remote. Proxy SE-2811 Dr. Mark L. Hornick 12
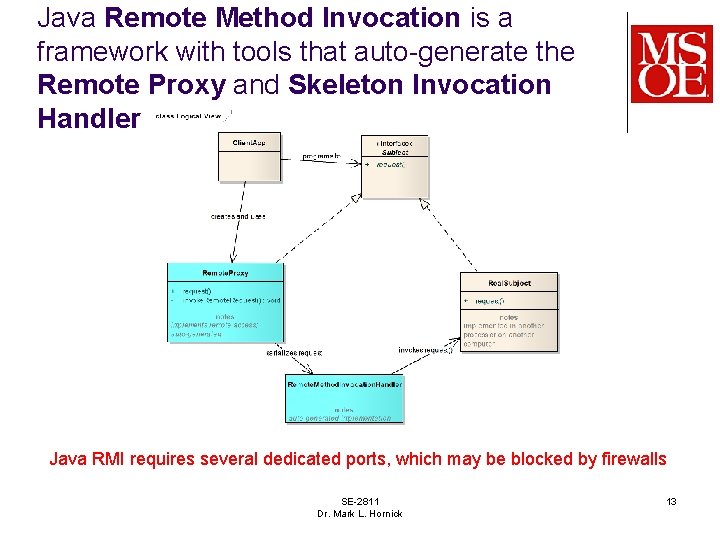
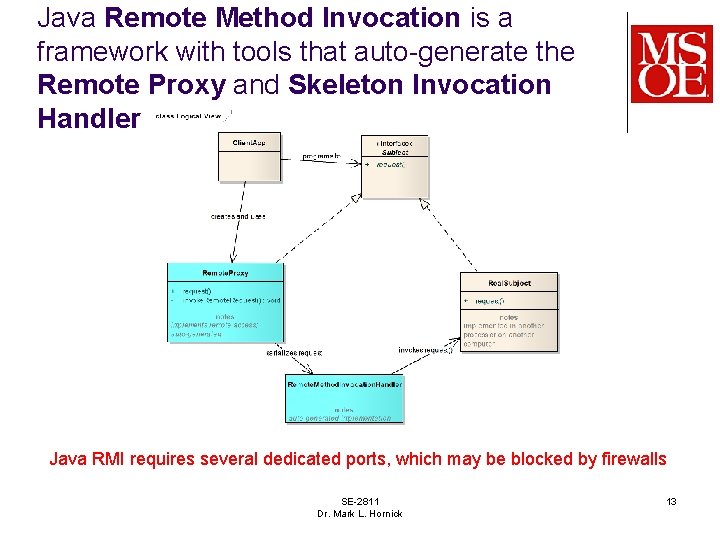
Java Remote Method Invocation is a framework with tools that auto-generate the Remote Proxy and Skeleton Invocation Handler Java RMI requires several dedicated ports, which may be blocked by firewalls SE-2811 Dr. Mark L. Hornick 13
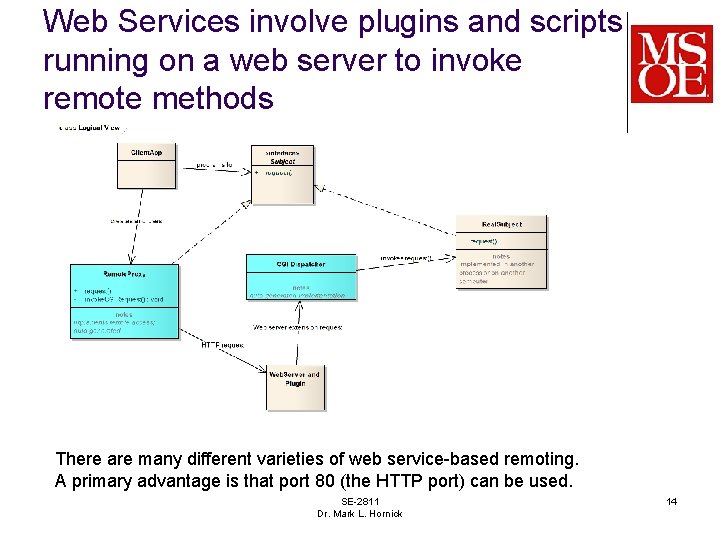
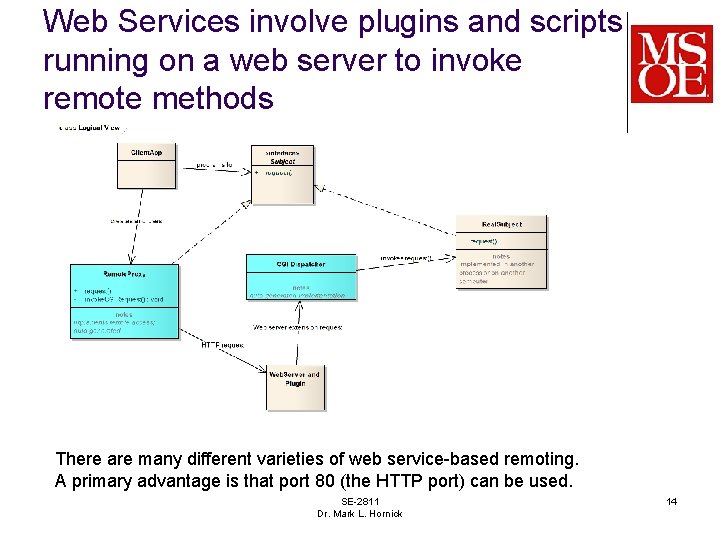
Web Services involve plugins and scripts running on a web server to invoke remote methods There are many different varieties of web service-based remoting. A primary advantage is that port 80 (the HTTP port) can be used. SE-2811 Dr. Mark L. Hornick 14