Skip List Hashing CSE POSTECH Introduction l l
![What Can Go Wrong? - Collision (72, e) (33, c) [0] l l [1] What Can Go Wrong? - Collision (72, e) (33, c) [0] l l [1]](https://slidetodoc.com/presentation_image_h/d140ba185c95e06f6af17935b3af7b0b/image-18.jpg)
![What Can Go Wrong? - Overflow (72, e) (33, c) [0] l l 19 What Can Go Wrong? - Overflow (72, e) (33, c) [0] l l 19](https://slidetodoc.com/presentation_image_h/d140ba185c95e06f6af17935b3af7b0b/image-19.jpg)
![Performance of Linear Probing (72, e) (33, c) [0] l l l 29 [2] Performance of Linear Probing (72, e) (33, c) [0] l l l 29 [2]](https://slidetodoc.com/presentation_image_h/d140ba185c95e06f6af17935b3af7b0b/image-29.jpg)
![Expected (Average) Performance (72, e) (33, c) [0] l l 30 [1] (3, d) Expected (Average) Performance (72, e) (33, c) [0] l l 30 [1] (3, d)](https://slidetodoc.com/presentation_image_h/d140ba185c95e06f6af17935b3af7b0b/image-30.jpg)
- Slides: 36
Skip List & Hashing CSE, POSTECH
Introduction l l l The search operation on a sorted array using the binary search method takes O(logn) The search operation on a sorted chain takes O(n) How can we improve the search performance of a sorted chain? By putting additional pointers in some of the chain nodes l 2 Chains augmented with additional forward pointers are called skip lists
Dictionary l l A dictionary is a collection of elements Each element has a field called key – l l Every key is usually distinct Typical dictionary operations are: – – – 3 (key, value) Determine whether or not the dictionary is empty Determine the dictionary size (i. e. , # of pairs) Insert a pair into the dictionary Search the pair with a specified key Delete the pair with a specified key
Accessing Dictionary Elements l Random Access – l Sequential Access – – 4 Any element in the dictionary can be retrieved by simply performing a search on its key Elements are retrieved one by one in ascending order of the key field Sequential Access Operations: Ø Begin – retrieves the element with smallest key Ø Next – retrieves the next element
Dictionary with Duplicates l l Keys are not required to be distinct Word dictionary is such an example – – – 5 Pairs are of the form (word, meaning) May have two or more entries for the same word For example, the meanings of the word, rank: l (rank, a relative position in a society) l (rank, an official position or grade) l (rank, to give a particular order or position to) l etc.
Application of Dictionary l Collection of student records in a class – – l l 6 (key, value) = (student-number, a list of assignment and exam marks) All keys are distinct Get the element whose key is Tiger Woods Update the element whose key is Seri Pak Read Examples 10. 1, 10. 2 & 10. 3 Exercise: Give other real-world applications of dictionaries and/or dictionaries with duplicates
Dictionary – ADT & Class Definition l l 7 See ADT 10. 1 for the abstract data type Dictionary See Program 10. 1 for the abstract class Dictionary
Dictionary as an Ordered Linear List l l l L = (e 1, e 2, e 3, …, en) Each ei is a pair (key, value) Array or chain representation – – l 8 unsorted array: unsorted chain: O(n) search time O(logn) search time O(n) search time See Program 10. 2 (find), 10. 3 (insert), 10. 4 (erase) of the class sorted. Chain
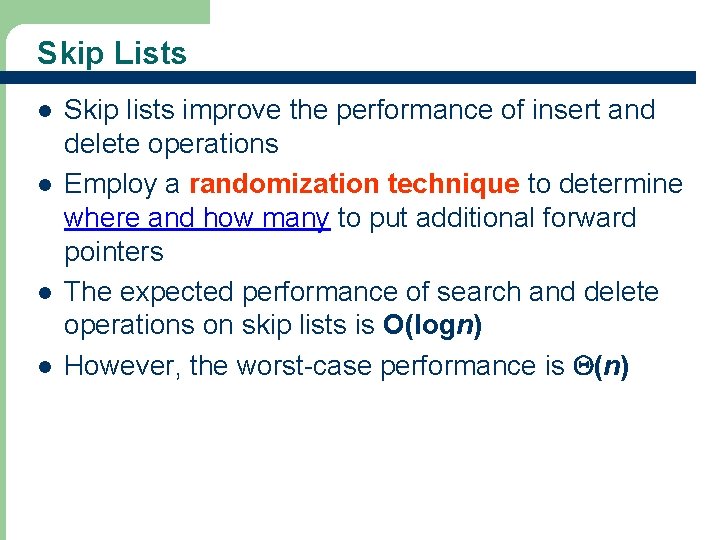
Skip Lists l l 9 Skip lists improve the performance of insert and delete operations Employ a randomization technique to determine where and how many to put additional forward pointers The expected performance of search and delete operations on skip lists is O(logn) However, the worst-case performance is (n)
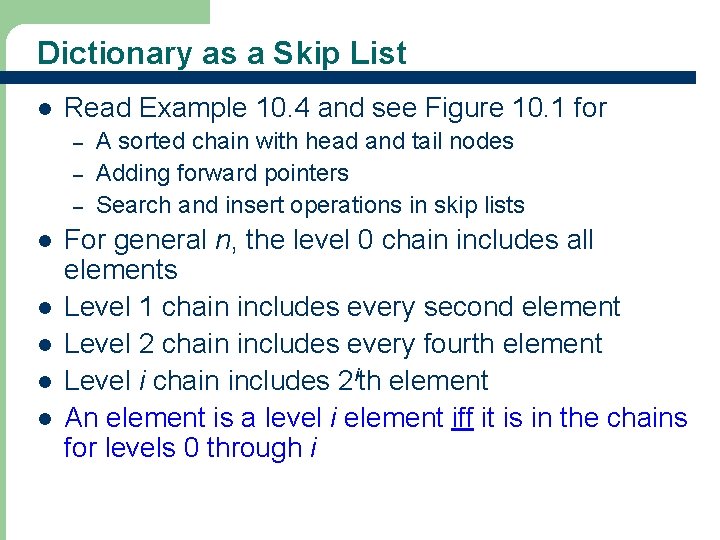
Dictionary as a Skip List l Read Example 10. 4 and see Figure 10. 1 for – – – l l l 10 A sorted chain with head and tail nodes Adding forward pointers Search and insert operations in skip lists For general n, the level 0 chain includes all elements Level 1 chain includes every second element Level 2 chain includes every fourth element Level i chain includes 2 ith element An element is a level i element iff it is in the chains for levels 0 through i
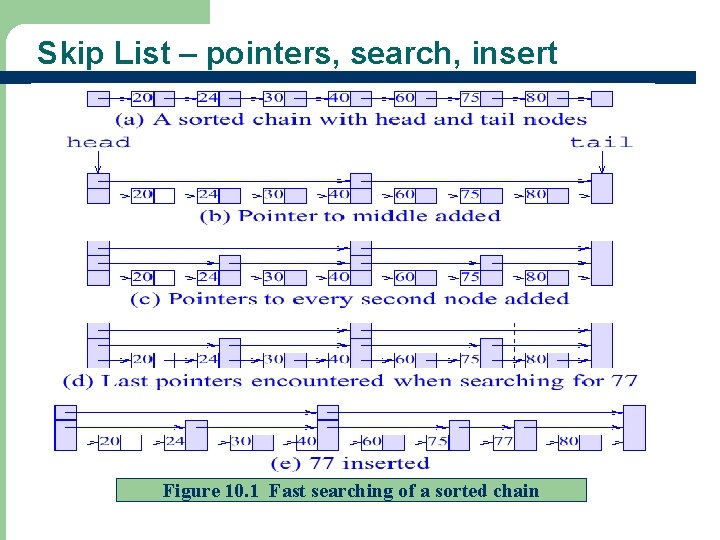
Skip List – pointers, search, insert Figure 10. 1 Fast searching of a sorted chain 11
Skip List – Insertions & Deletions l l l 12 When insertions or deletions occur, we require O(n) work to maintain the structure of skip lists When an insertion is made, the pair level is i with probability 1/2 i We can assign the newly inserted pair at level i with probability pi For general p, the number of chain levels is log 1/pn + 1 See Figure 10. 1(d) for inserting 77 We have no control over the structure that is left following a deletion
Skip List – Assigning Levels l l l The level assignment of newly inserted pair is done using a random number generator (0 to RAND_MAX) The probability that the next random number is Cutoff = p * RAND_MAX is p The following is used to assign a level number int lev = 0 while (rand() <= Cut. Off) lev++; l l 13 In a regular skip list structure with N pairs, the maximum level is log 1/p. N - 1 Read Example 10. 5
Skip List – Class definition l l l 14 The class definition for skip. Node is in Program 10. 5 The data members of the class skip. List is defined in Program 10. 6 See Program 10. 7 – 10. 12 for skip. List operations
Hash Table l l 15 A hash table is an alternative method for representing a dictionary In a hash table, a hash function is used to map keys into positions in a table. This act is called hashing The ideal hashing case: if a pair p has the key k and f is the hash function, then p is stored in position f(k) of the table Hash table is used in many real world applications!
Hash Table l Hash Table Operations – – – Search: compute f(k) and see if a pair exists Insert: compute f(k) and place it in that position Delete: compute f(k) and delete the pair in that position l In ideal situation, hash table search, insert or delete takes (1) l Read Examples 10. 6 & 10. 7 16
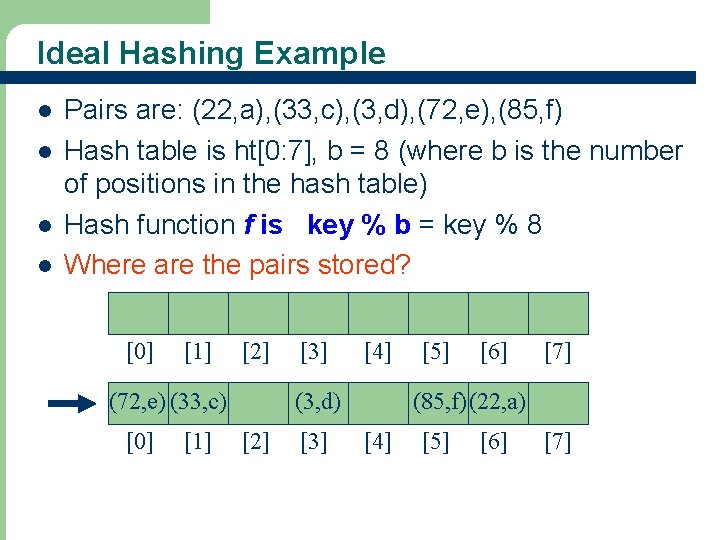
Ideal Hashing Example l l Pairs are: (22, a), (33, c), (3, d), (72, e), (85, f) Hash table is ht[0: 7], b = 8 (where b is the number of positions in the hash table) Hash function f is key % b = key % 8 Where are the pairs stored? [0] [1] [2] (72, e) (33, c) [0] 17 [1] [3] [4] (3, d) [2] [3] [5] [6] [7] (85, f) (22, a) [4] [5] [6] [7]
![What Can Go Wrong Collision 72 e 33 c 0 l l 1 What Can Go Wrong? - Collision (72, e) (33, c) [0] l l [1]](https://slidetodoc.com/presentation_image_h/d140ba185c95e06f6af17935b3af7b0b/image-18.jpg)
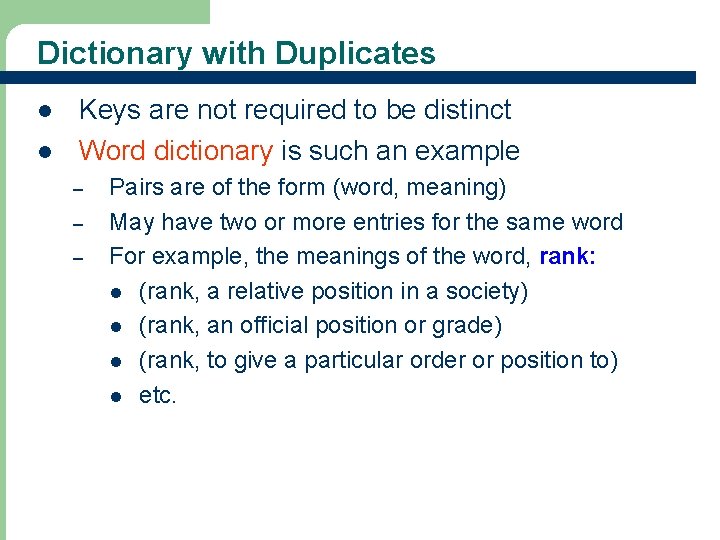
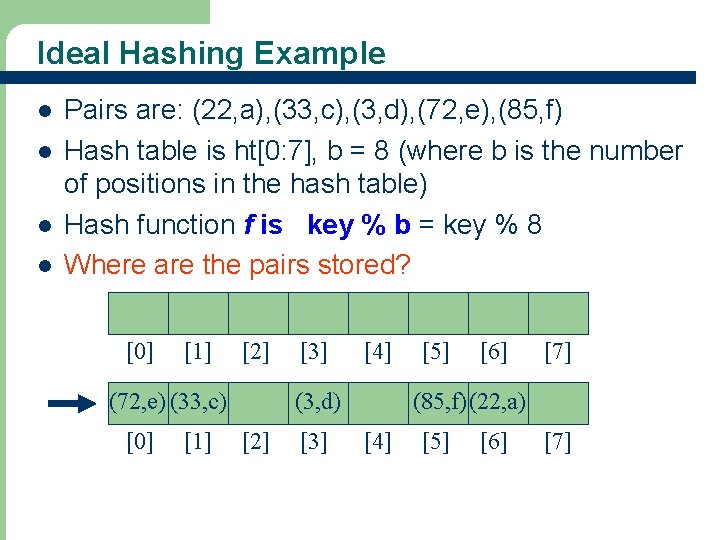
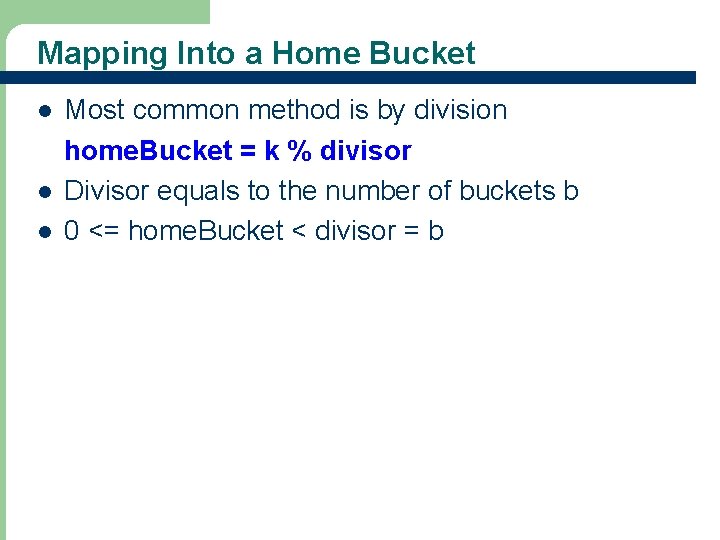
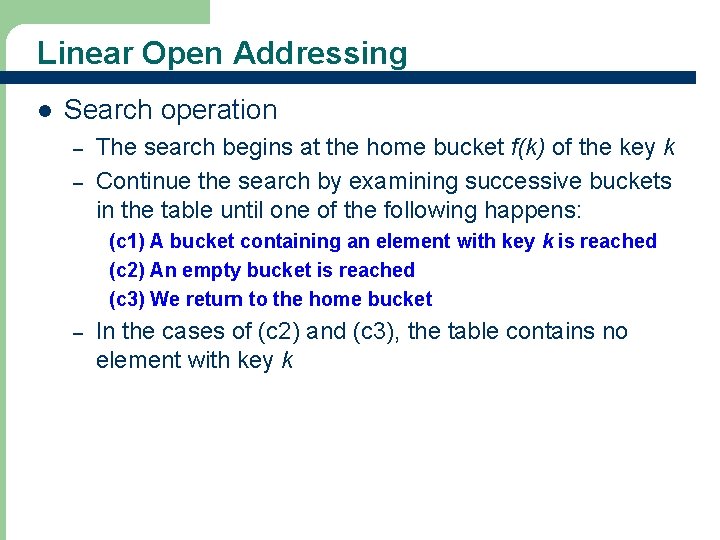
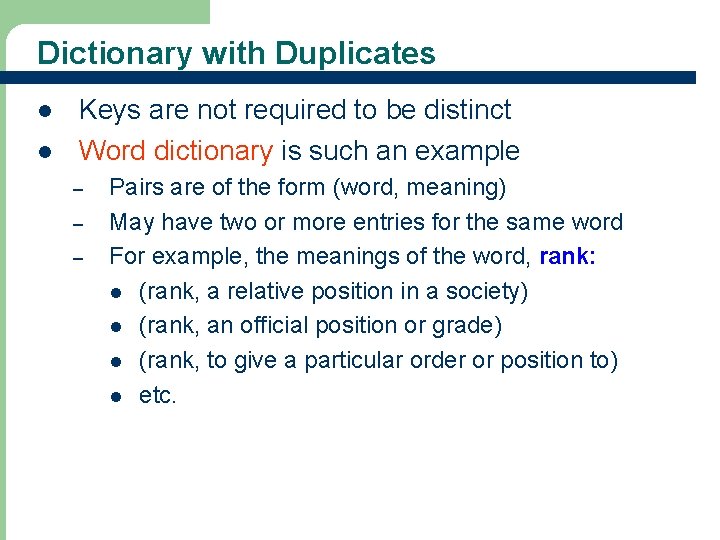
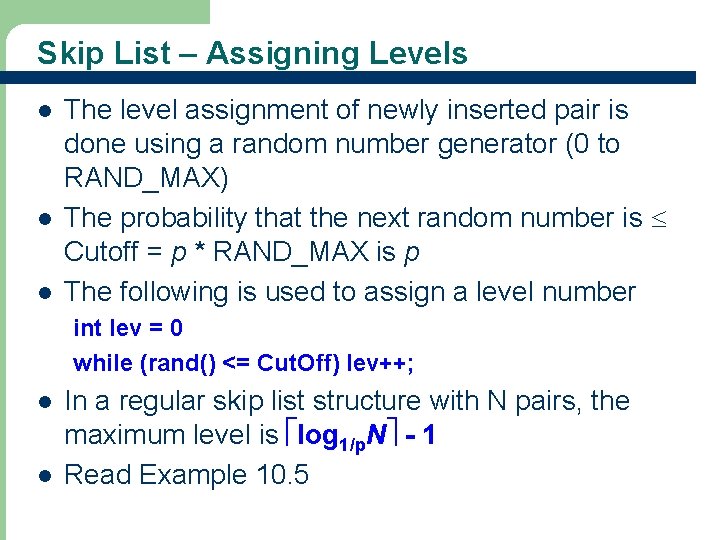
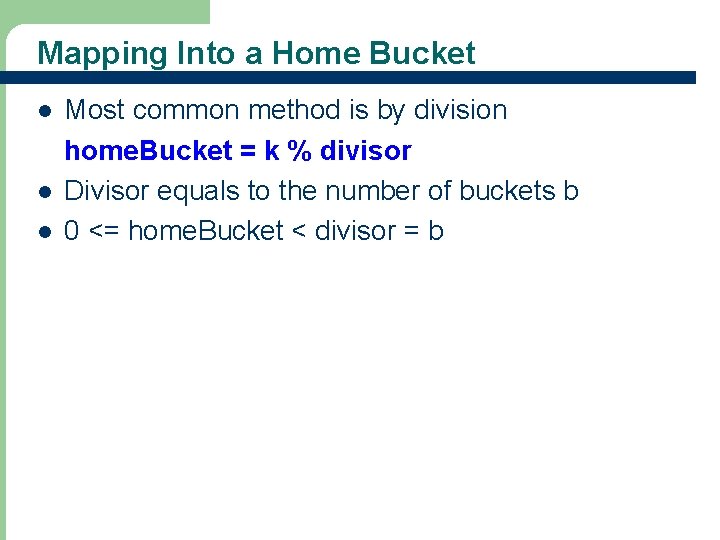
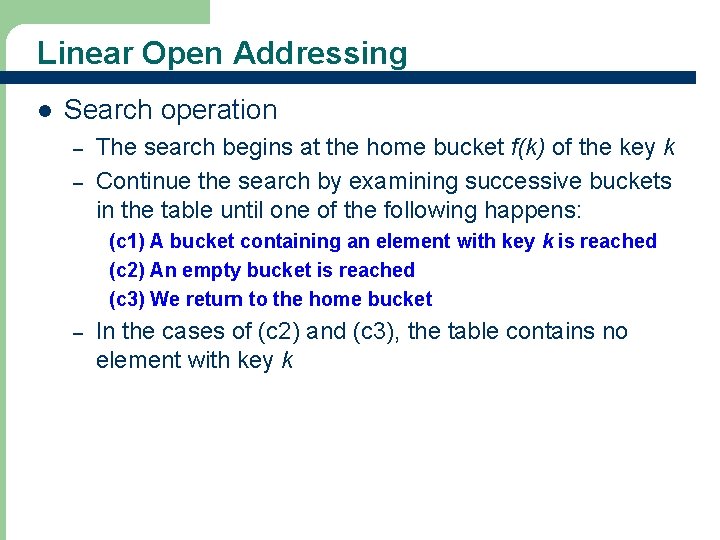
What Can Go Wrong? - Collision (72, e) (33, c) [0] l l [1] (3, d) [2] [3] (85, f) (22, a) [4] [5] [6] [7] Where does (25, g) go? The home bucket for (25, g) is already occupied by (33, c) This situation is called collision l Keys that have the same home bucket are called synonyms – 18 25 and 33 are synonyms with respect to the hash function that is in use
![What Can Go Wrong Overflow 72 e 33 c 0 l l 19 What Can Go Wrong? - Overflow (72, e) (33, c) [0] l l 19](https://slidetodoc.com/presentation_image_h/d140ba185c95e06f6af17935b3af7b0b/image-19.jpg)
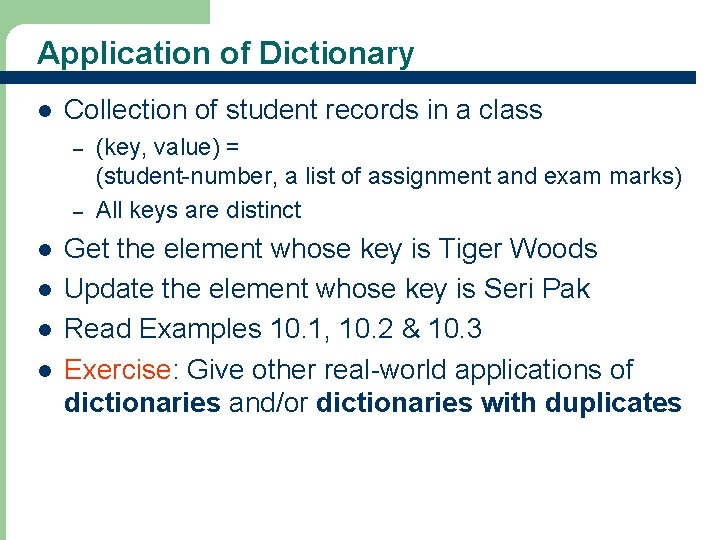
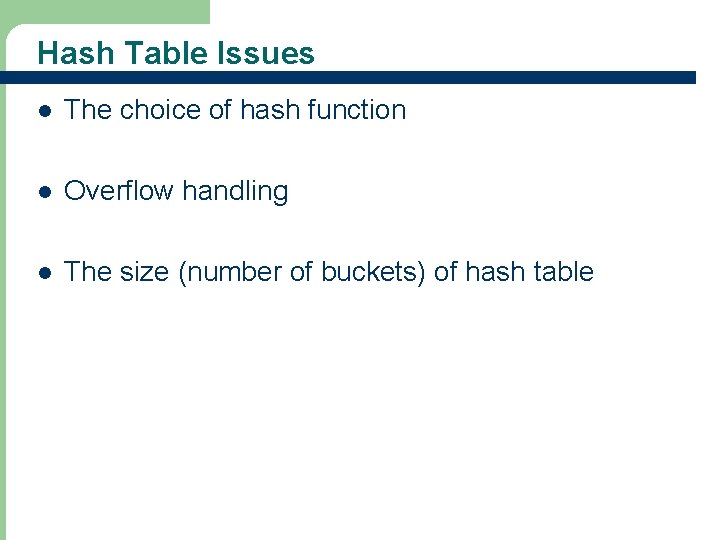
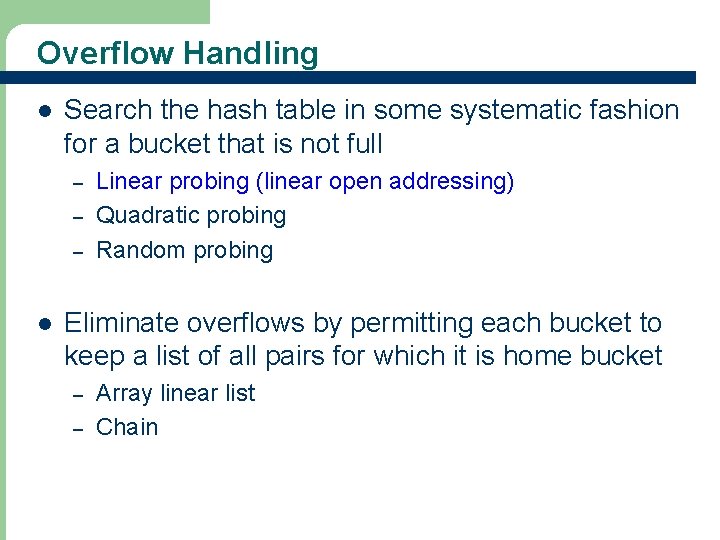
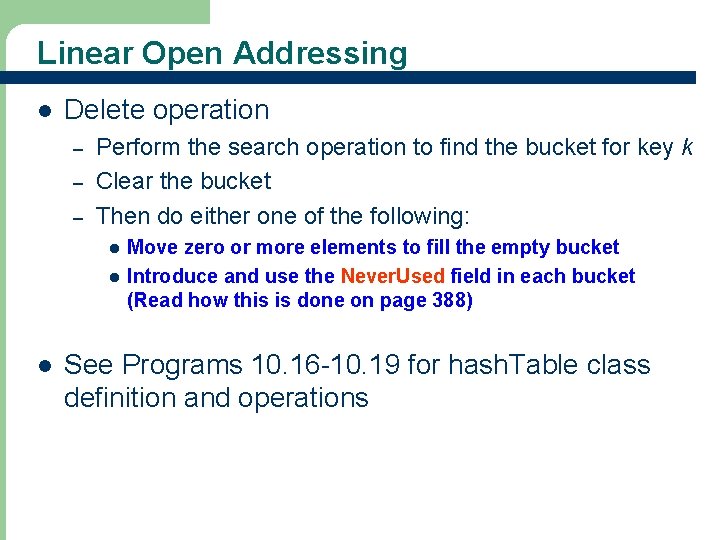
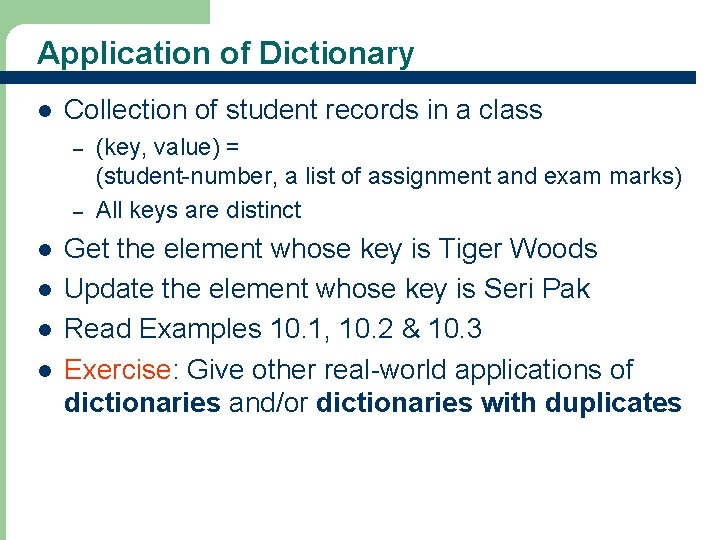
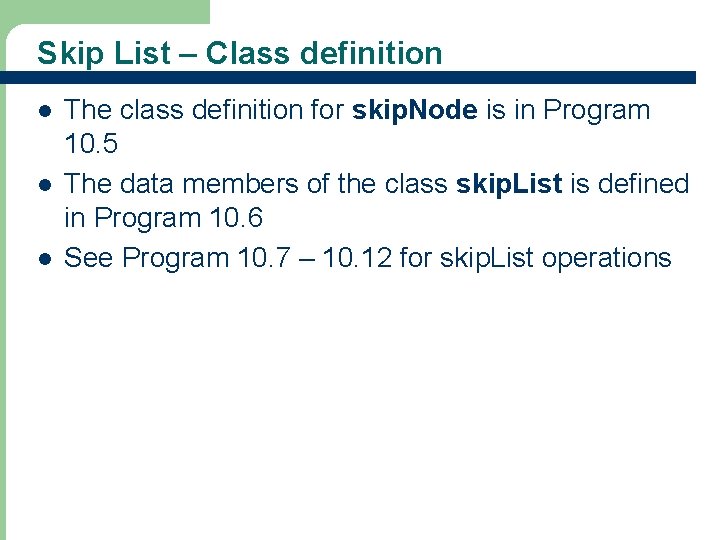
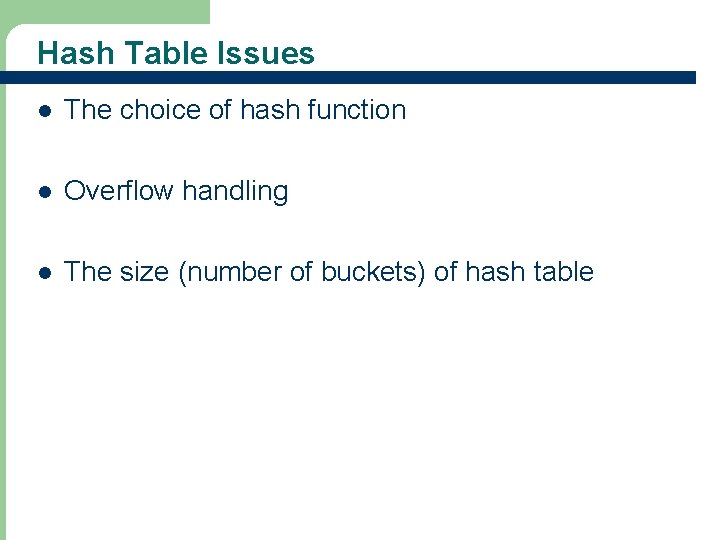
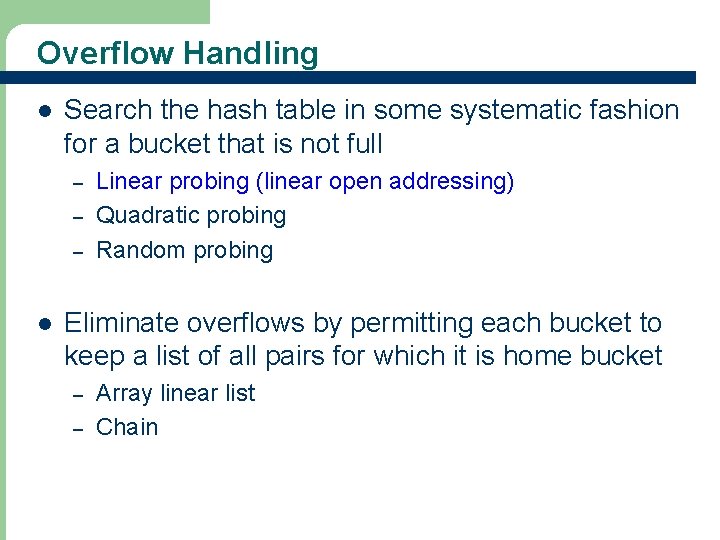
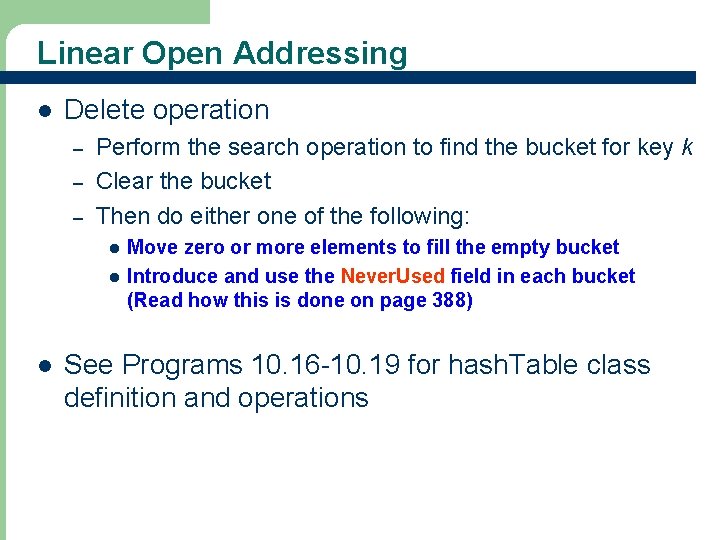
What Can Go Wrong? - Overflow (72, e) (33, c) [0] l l 19 [1] (3, d) [2] [3] (85, f) (22, a) [4] [5] [6] [7] A collision occurs when the home bucket for a new pair is occupied by a pair with different key An overflow occurs when there is no space in the home bucket for the new pair When a bucket can hold only one pair, collisions and overflows occur together Need a method to handle overflows
Hash Table Issues l The choice of hash function l Overflow handling l The size (number of buckets) of hash table 20
Hash Functions l 1. 2. Two parts Convert key into an integer in case the key is not Map an integer into a home bucket – 21 f(k) is an integer in the range [0, b-1], where b is the number of buckets in the table
Converting String to Integer l l l Let us assume that each character is 2 bytes long Let us assume that an integer is 4 bytes long A 2 character string s may be converted into a unique 4 byte integer using the following code: int answer = (int) s[0]; answer = (answer << 16) + (int) s[1]; l l 22 In this case, strings that are longer than 2 characters do not have a unique integer representation Read Example 10. 8 and see Program 10. 13
Mapping Into a Home Bucket l l l 23 Most common method is by division home. Bucket = k % divisor Divisor equals to the number of buckets b 0 <= home. Bucket < divisor = b
Overflow Handling l Search the hash table in some systematic fashion for a bucket that is not full – – – l Eliminate overflows by permitting each bucket to keep a list of all pairs for which it is home bucket – – 24 Linear probing (linear open addressing) Quadratic probing Random probing Array linear list Chain
Hashing with Linear Open Addressing l l If a collision occurs, insert the entry into the next available bucket regarding the table as circular Example – – – 25 the size of hash table b = 11 f(k) = k % b after inserting the three keys 80, 40, and 65
Linear Open Addressing l Example after inserting the two keys 58 (collision) and 24 – – 26 after inserting the key 35 (collision)
Linear Open Addressing l Search operation – – The search begins at the home bucket f(k) of the key k Continue the search by examining successive buckets in the table until one of the following happens: (c 1) A bucket containing an element with key k is reached (c 2) An empty bucket is reached (c 3) We return to the home bucket – 27 In the cases of (c 2) and (c 3), the table contains no element with key k
Linear Open Addressing l Delete operation – – – Perform the search operation to find the bucket for key k Clear the bucket Then do either one of the following: l l l 28 Move zero or more elements to fill the empty bucket Introduce and use the Never. Used field in each bucket (Read how this is done on page 388) See Programs 10. 16 -10. 19 for hash. Table class definition and operations
![Performance of Linear Probing 72 e 33 c 0 l l l 29 2 Performance of Linear Probing (72, e) (33, c) [0] l l l 29 [2]](https://slidetodoc.com/presentation_image_h/d140ba185c95e06f6af17935b3af7b0b/image-29.jpg)
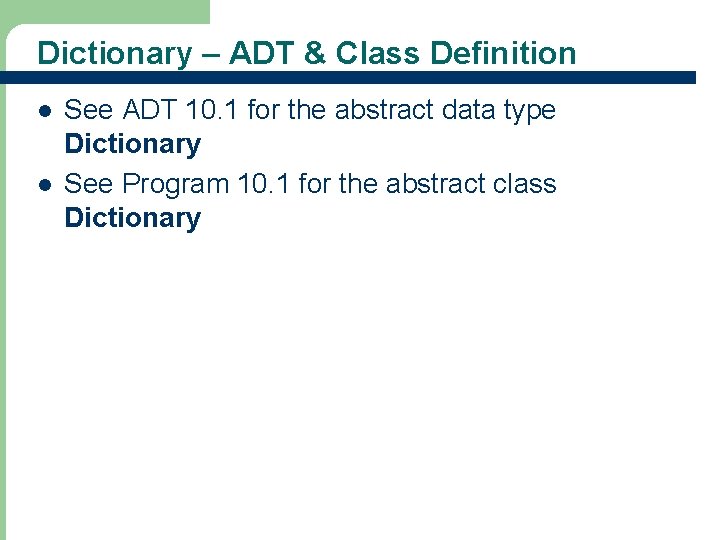
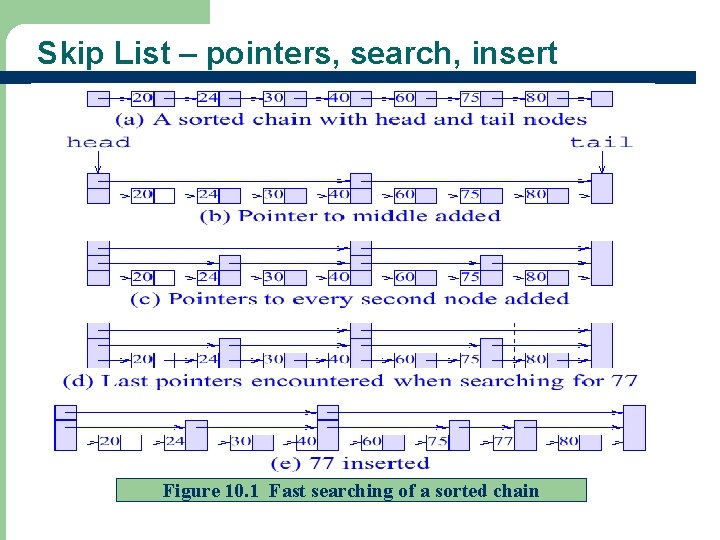
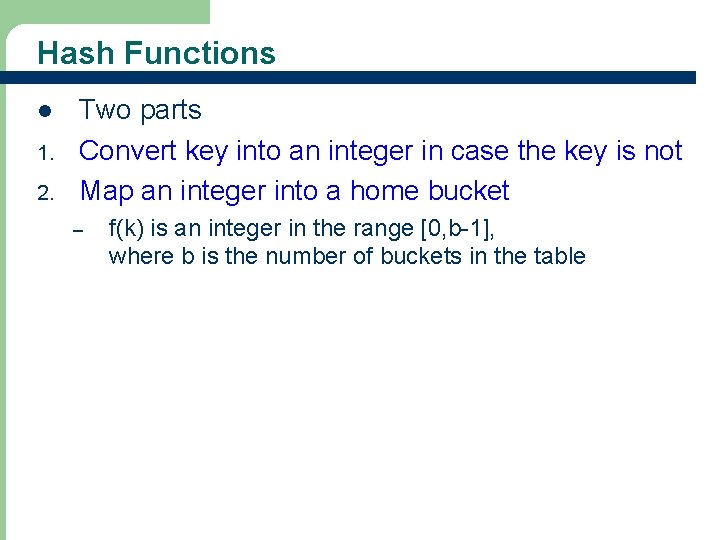
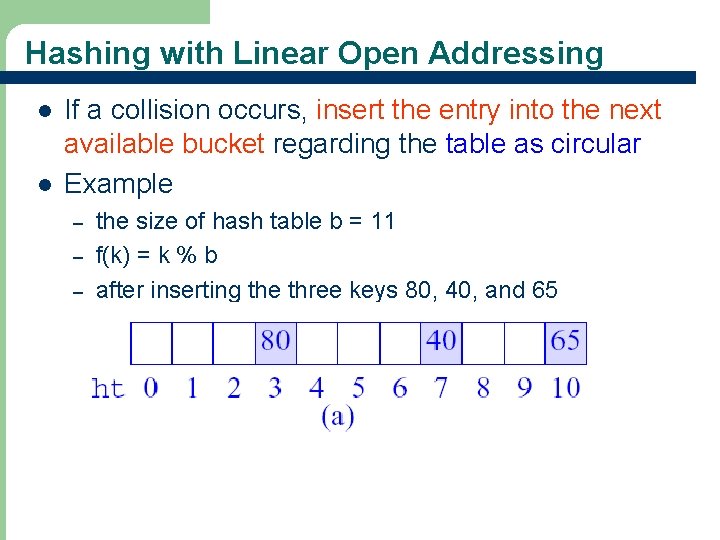
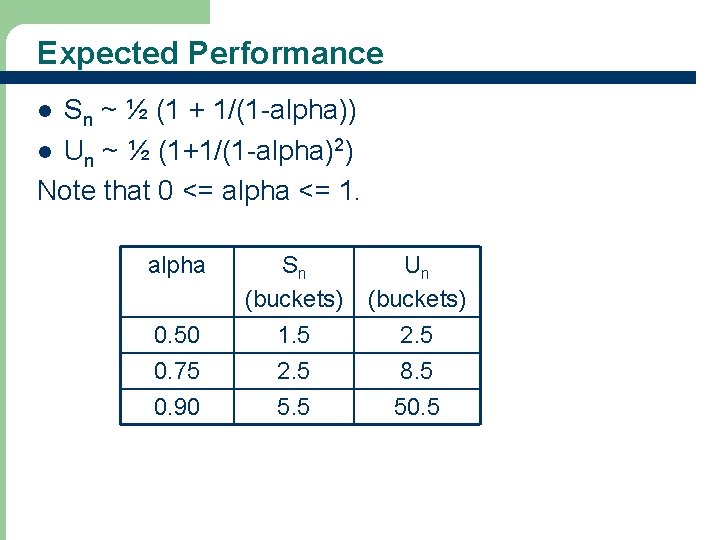
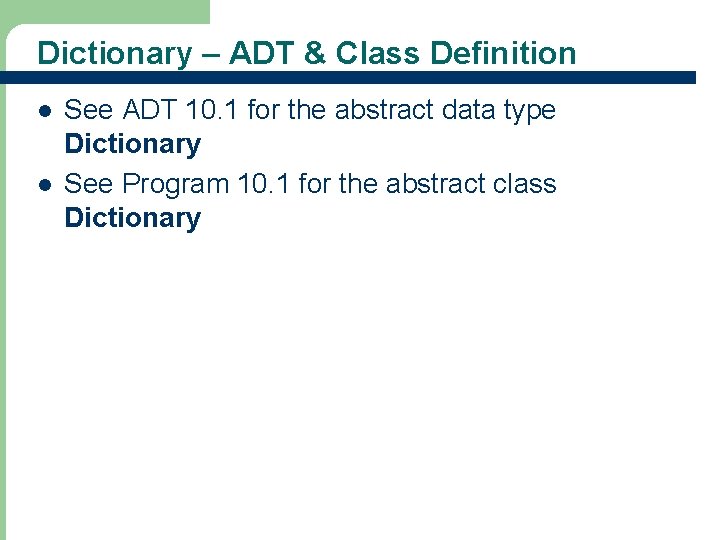
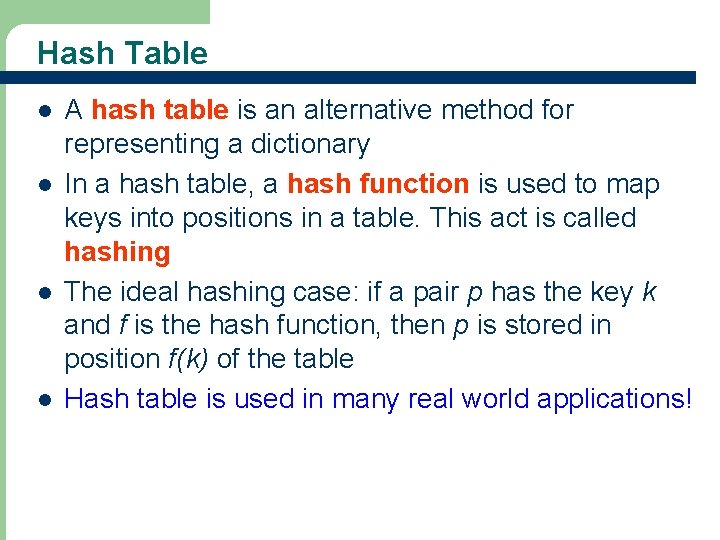
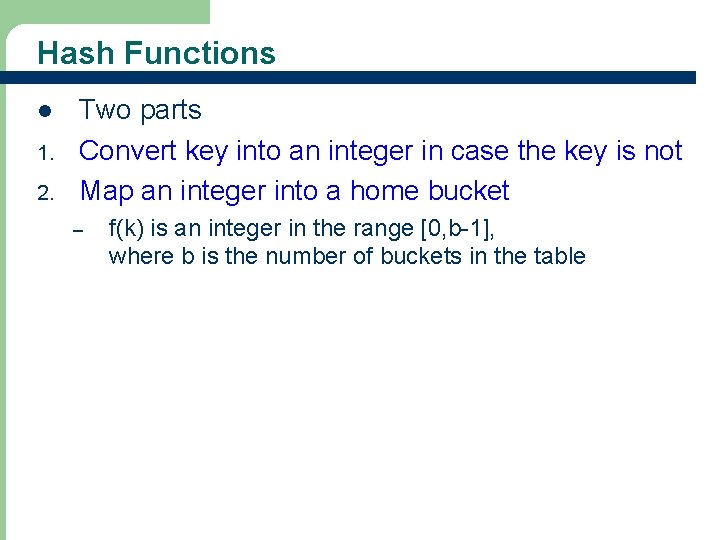
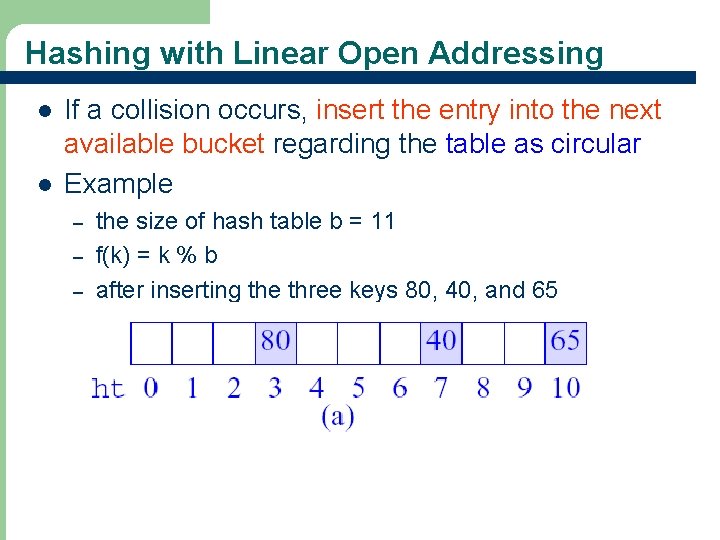
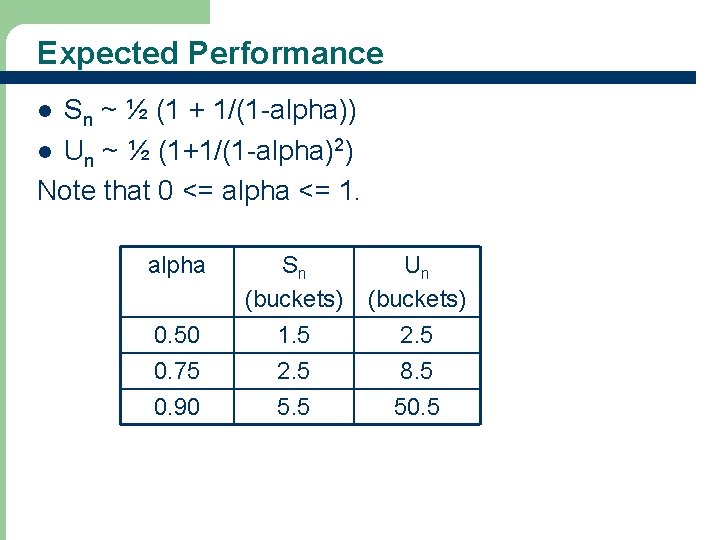
Performance of Linear Probing (72, e) (33, c) [0] l l l 29 [2] [3] (85, f) (22, a) [4] [5] [6] [7] The worst-case search/insert/delete time is (n), where n is the number of pairs in the table When does the worst-case happen? When l [1] (3, d) all n key values have the same home bucket For the worst case, the performance of hash table and linear list are the same However, for average performance, hashing is much better
![Expected Average Performance 72 e 33 c 0 l l 30 1 3 d Expected (Average) Performance (72, e) (33, c) [0] l l 30 [1] (3, d)](https://slidetodoc.com/presentation_image_h/d140ba185c95e06f6af17935b3af7b0b/image-30.jpg)
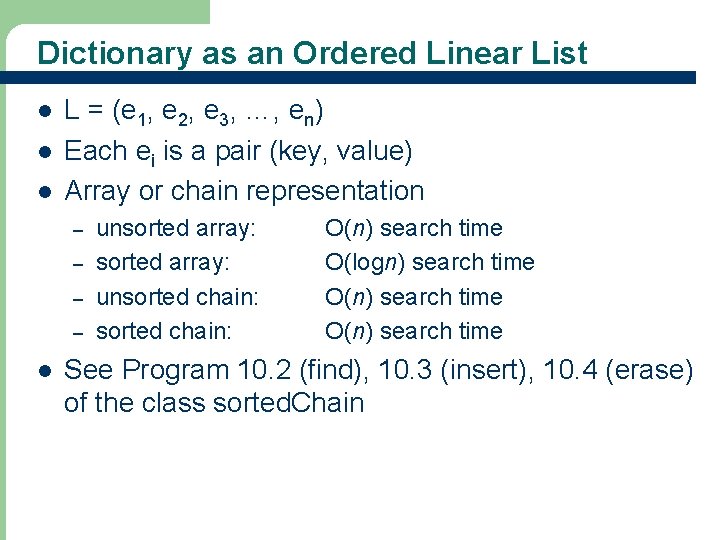
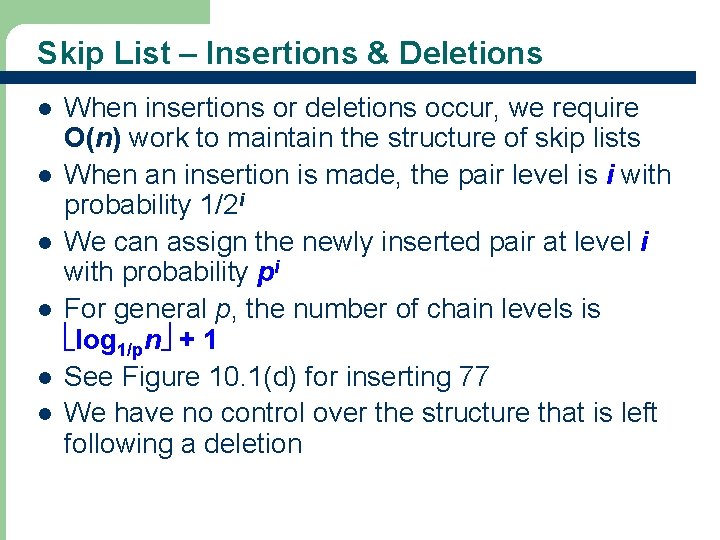
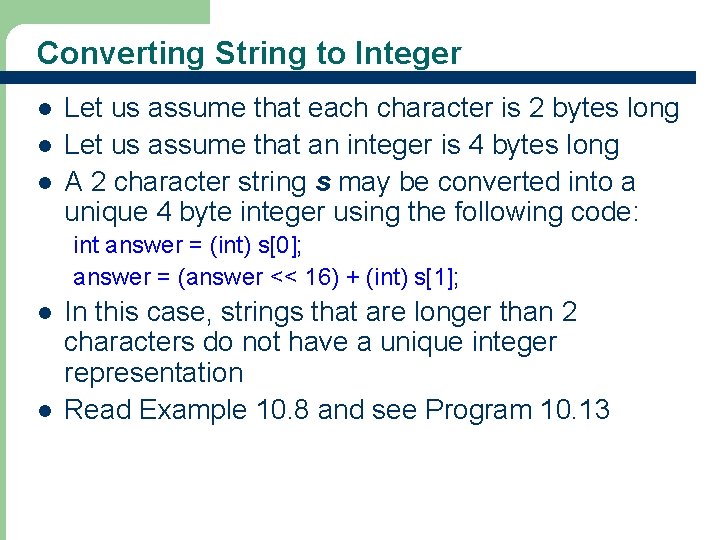
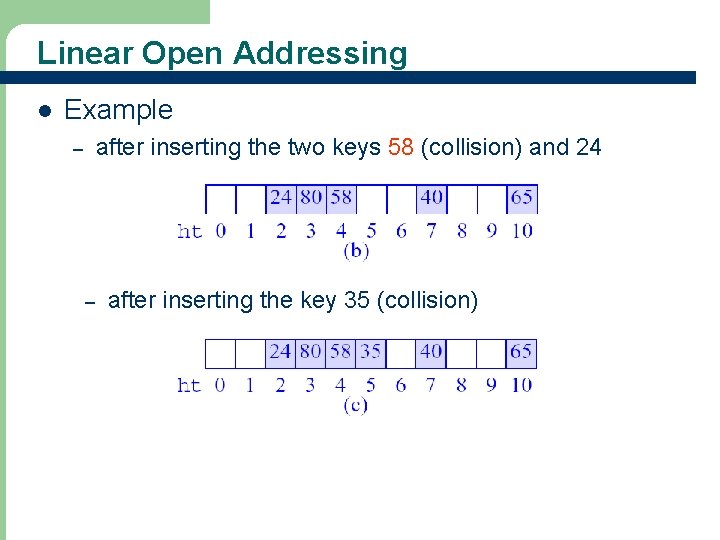
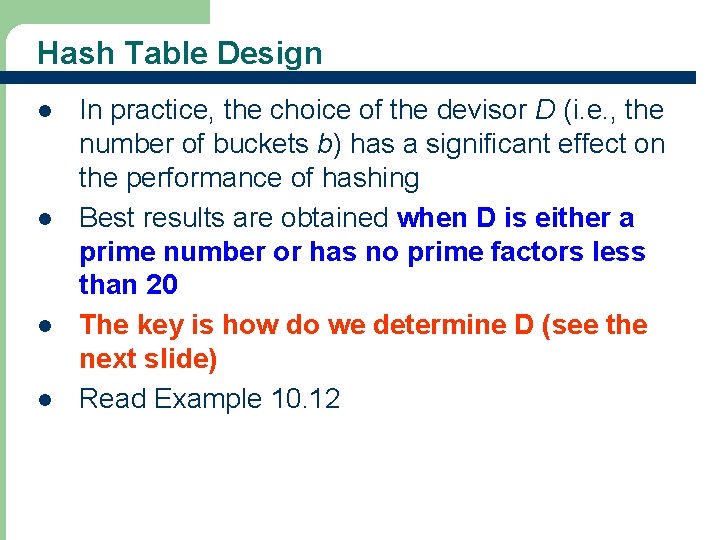
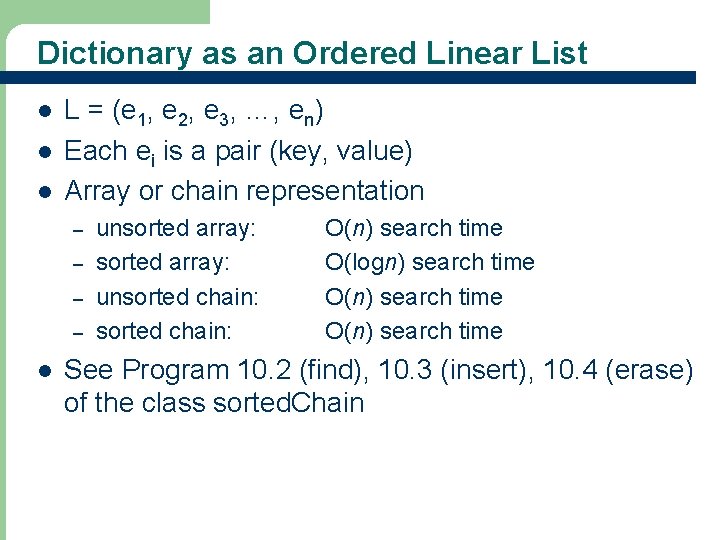
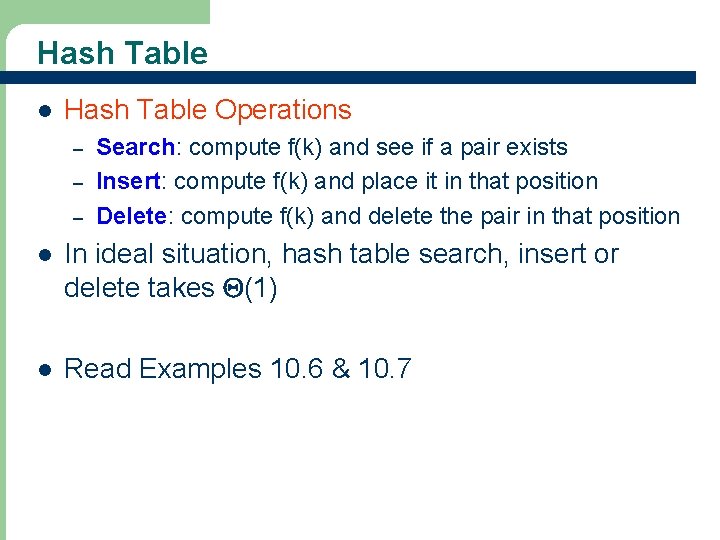
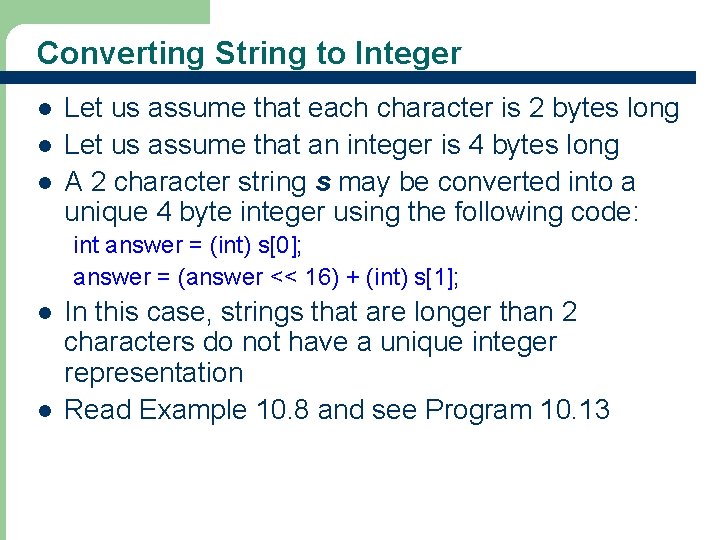
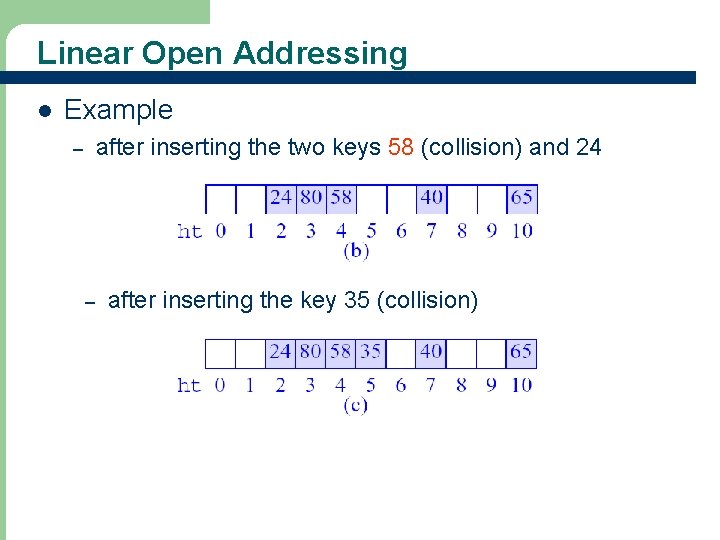
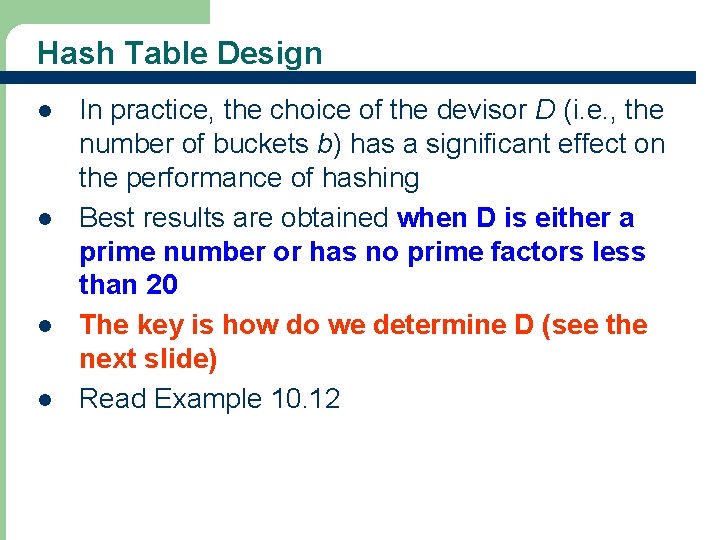
Expected (Average) Performance (72, e) (33, c) [0] l l 30 [1] (3, d) [2] [3] (85, f) (22, a) [4] [5] [6] [7] alpha = loading factor = n / b Sn = average number of buckets examined in a successful search Un = average number of buckets examined in an unsuccessful search Time to insert and delete is governed by Un.
Expected Performance Sn ~ ½ (1 + 1/(1 -alpha)) l Un ~ ½ (1+1/(1 -alpha)2) Note that 0 <= alpha <= 1. l alpha 31 0. 50 0. 75 Sn (buckets) 1. 5 2. 5 Un (buckets) 2. 5 8. 5 0. 90 5. 5 50. 5
Hash Table Design l l 32 In practice, the choice of the devisor D (i. e. , the number of buckets b) has a significant effect on the performance of hashing Best results are obtained when D is either a prime number or has no prime factors less than 20 The key is how do we determine D (see the next slide) Read Example 10. 12
Methods for Determining D Method 1: l First, determine what constitutes acceptable performance. l Use the formulas Un and Sn, determine the largest alpha that can be used. l From the value of n and the computed value of alpha, obtain the smallest permissible value for b. Method 2: l Begin with the largest possible value for b as determined by the max. amount of space available. l Then find the largest D no larger than this largest value that is either a prime or has no factors smaller than 20. 33
Hashing with Chains l l 34 Hash table can handle overflows using chaining Each bucket keeps a chain of all pairs for which it is the home bucket (see Figure 10. 3) The chain may or may not be sorted by key See Program 10. 20 for hash. Chains methods
Hash Table with Sorted Chains l Put in pairs whose keys are 6, 12, 34, 29, 28, 11, 23, 7, 0, 33, 30, 45 l Home bucket = key % 17. 35
Exercise & Reading l Exercise – l 36 Suppose we are hashing integers with a 7 -bucket hash table using the hash function f(k) = k % 7. (a) Show the hash table if 1, 8, 23, 40, 51, 69, 70 are to be inserted. Use the linear open addressing method to resolve collisions. (b) Repeat part (a) using chaining to resolve collisions. Assume the chain is sorted. Read Chapter 10