Security Protocols Theyre so NOT Easy Lecture Motivation
- Slides: 30
Security Protocols: They’re so NOT Easy!
Lecture Motivation l In the last lecture we looked at some high-level descriptions of key distribution and agreement schemes. l These protocols cannot be used as they were stated. l In implementation of the actual protocol, there are many situations one should be careful of. l In this lecture, we will look at some common protocol failures that arise when trying to implement security protocols l We will then look at some specific examples of security protocols
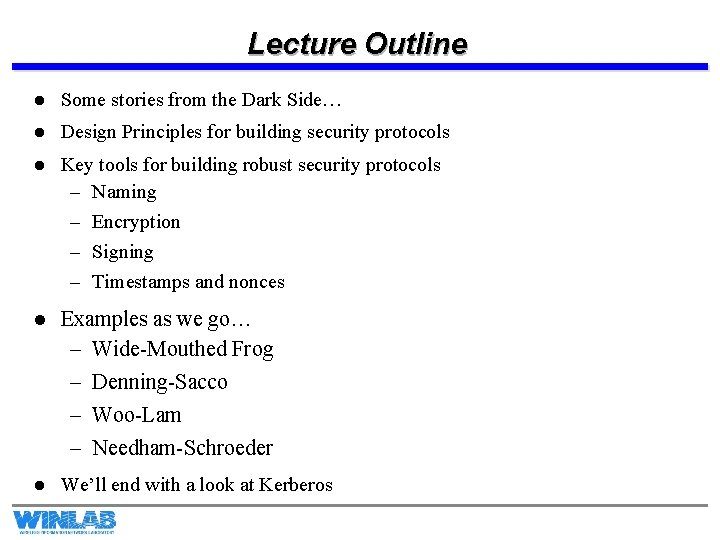
Lecture Outline l Some stories from the Dark Side… l Design Principles for building security protocols l Key tools for building robust security protocols – Naming – Encryption – Signing – Timestamps and nonces l Examples as we go… – Wide-Mouthed Frog – Denning-Sacco – Woo-Lam – Needham-Schroeder l We’ll end with a look at Kerberos
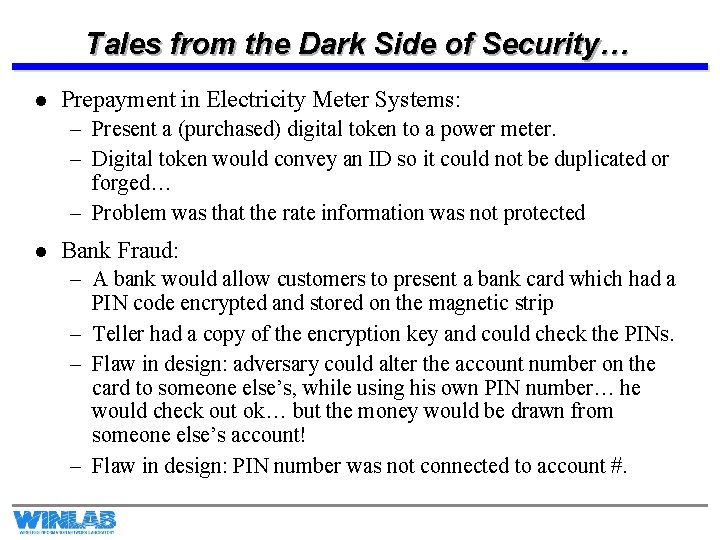
Tales from the Dark Side of Security… l Prepayment in Electricity Meter Systems: – Present a (purchased) digital token to a power meter. – Digital token would convey an ID so it could not be duplicated or forged… – Problem was that the rate information was not protected l Bank Fraud: – A bank would allow customers to present a bank card which had a PIN code encrypted and stored on the magnetic strip – Teller had a copy of the encryption key and could check the PINs. – Flaw in design: adversary could alter the account number on the card to someone else’s, while using his own PIN number… he would check out ok… but the money would be drawn from someone else’s account! – Flaw in design: PIN number was not connected to account #.
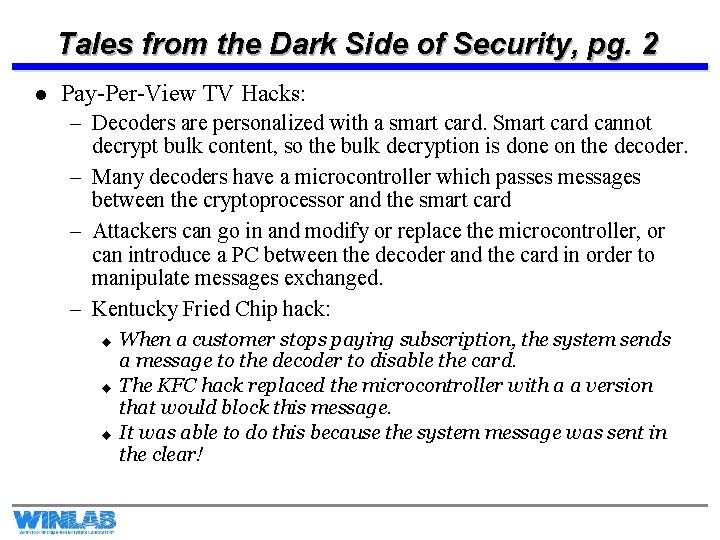
Tales from the Dark Side of Security, pg. 2 l Pay-Per-View TV Hacks: – Decoders are personalized with a smart card. Smart card cannot decrypt bulk content, so the bulk decryption is done on the decoder. – Many decoders have a microcontroller which passes messages between the cryptoprocessor and the smart card – Attackers can go in and modify or replace the microcontroller, or can introduce a PC between the decoder and the card in order to manipulate messages exchanged. – Kentucky Fried Chip hack: u u u When a customer stops paying subscription, the system sends a message to the decoder to disable the card. The KFC hack replaced the microcontroller with a a version that would block this message. It was able to do this because the system message was sent in the clear!
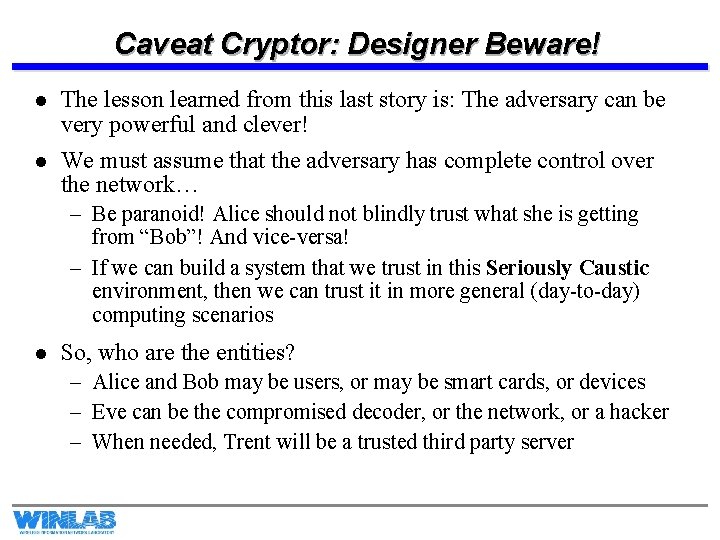
Caveat Cryptor: Designer Beware! l The lesson learned from this last story is: The adversary can be very powerful and clever! l We must assume that the adversary has complete control over the network… – Be paranoid! Alice should not blindly trust what she is getting from “Bob”! And vice-versa! – If we can build a system that we trust in this Seriously Caustic environment, then we can trust it in more general (day-to-day) computing scenarios l So, who are the entities? – Alice and Bob may be users, or may be smart cards, or devices – Eve can be the compromised decoder, or the network, or a hacker – When needed, Trent will be a trusted third party server
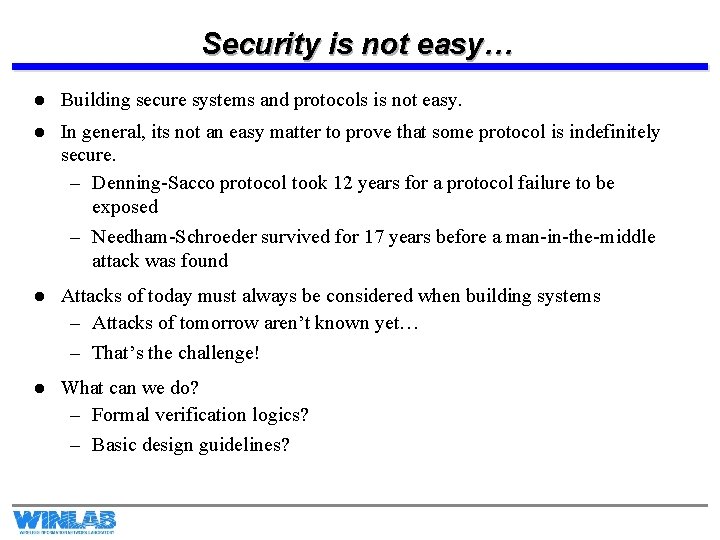
Security is not easy… l Building secure systems and protocols is not easy. l In general, its not an easy matter to prove that some protocol is indefinitely secure. – Denning-Sacco protocol took 12 years for a protocol failure to be exposed – Needham-Schroeder survived for 17 years before a man-in-the-middle attack was found l Attacks of today must always be considered when building systems – Attacks of tomorrow aren’t known yet… – That’s the challenge! l What can we do? – Formal verification logics? – Basic design guidelines?
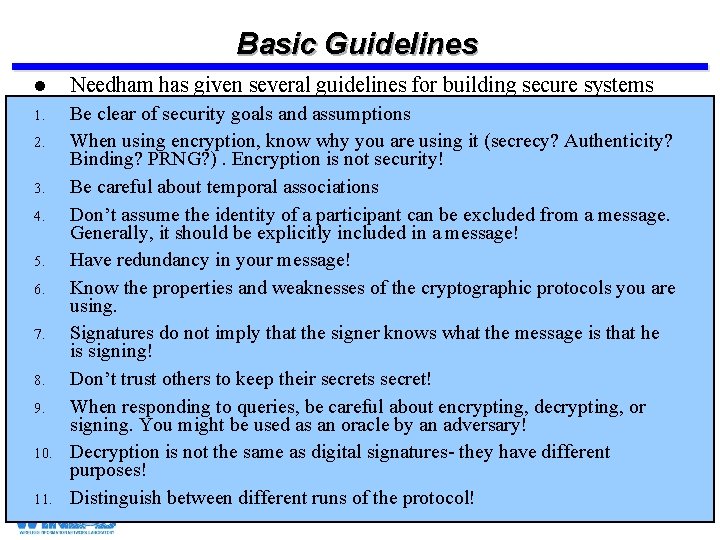
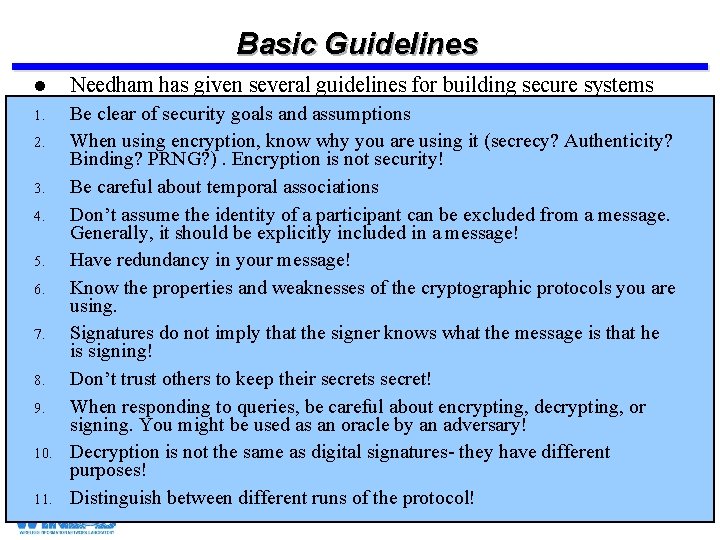
Basic Guidelines l Needham has given several guidelines for building secure systems 1. Be clear of security goals and assumptions When using encryption, know why you are using it (secrecy? Authenticity? Binding? PRNG? ). Encryption is not security! Be careful about temporal associations Don’t assume the identity of a participant can be excluded from a message. Generally, it should be explicitly included in a message! Have redundancy in your message! Know the properties and weaknesses of the cryptographic protocols you are using. Signatures do not imply that the signer knows what the message is that he is signing! Don’t trust others to keep their secrets secret! When responding to queries, be careful about encrypting, decrypting, or signing. You might be used as an oracle by an adversary! Decryption is not the same as digital signatures- they have different purposes! Distinguish between different runs of the protocol! 2. 3. 4. 5. 6. 7. 8. 9. 10. 11.
Other Considerations l KISS (Keep It Simple Stupid) is often desirable from an engineering point of view… – Its generally BAD from a security point of view! – Removing some data fields because they seem like they can be inferred (and thus shorten the message) can result in severe protocol failures! l Formal methods are helpful, but are at still at a young stage of development – For information on formal models, look Kailar’s logic in R. Kailar, “Reasoning about accountability in protocols for electronic commerce, ” 1995 IEEE Symposium on Security and Privacy
Why these rules? How to use them? l The previous two slides gave guidelines, but not did not say why we should follow these guidelines. l We are going to look at several examples of protocols that, at first glance, looked OK… but flaws were uncovered later. l These examples will illustrate why we need to be careful, and why these rules are important. l In order to carry out these guidelines, we need some tools, so we will introduce various tools in the process to fix these protocols.
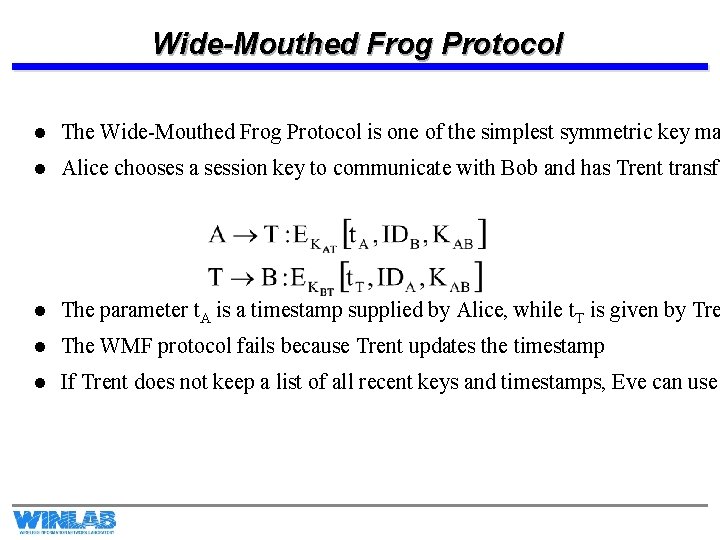
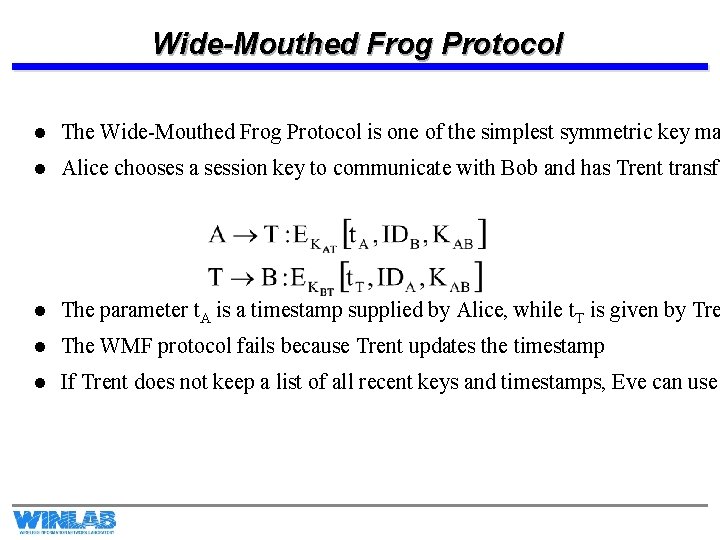
Wide-Mouthed Frog Protocol l The Wide-Mouthed Frog Protocol is one of the simplest symmetric key ma l Alice chooses a session key to communicate with Bob and has Trent transfe l The parameter t. A is a timestamp supplied by Alice, while t. T is given by Tre l The WMF protocol fails because Trent updates the timestamp l If Trent does not keep a list of all recent keys and timestamps, Eve can use
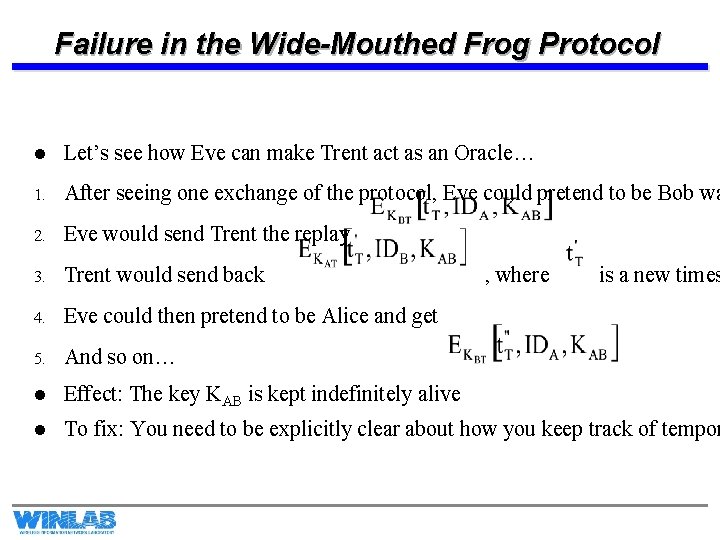
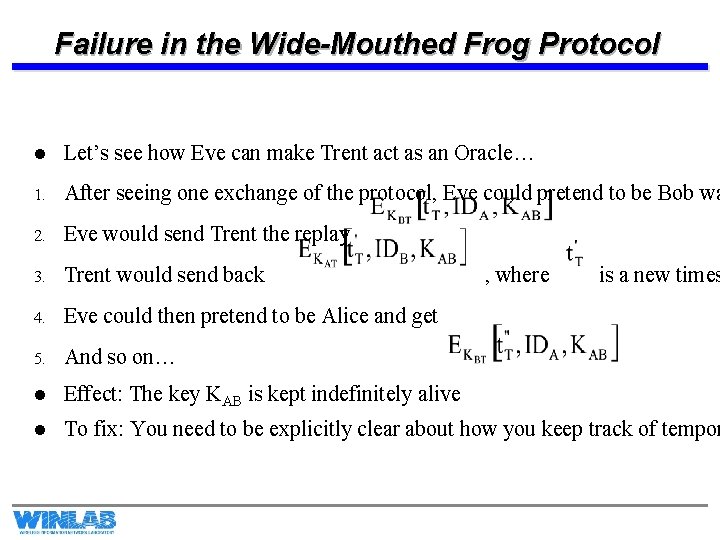
Failure in the Wide-Mouthed Frog Protocol l Let’s see how Eve can make Trent act as an Oracle… 1. After seeing one exchange of the protocol, Eve could pretend to be Bob wa 2. Eve would send Trent the replay 3. Trent would send back 4. Eve could then pretend to be Alice and get 5. And so on… l Effect: The key KAB is kept indefinitely alive l To fix: You need to be explicitly clear about how you keep track of tempor , where is a new times
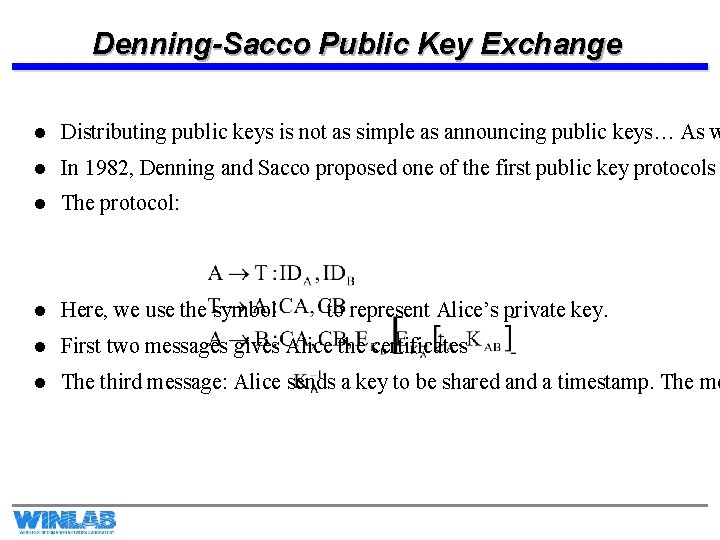
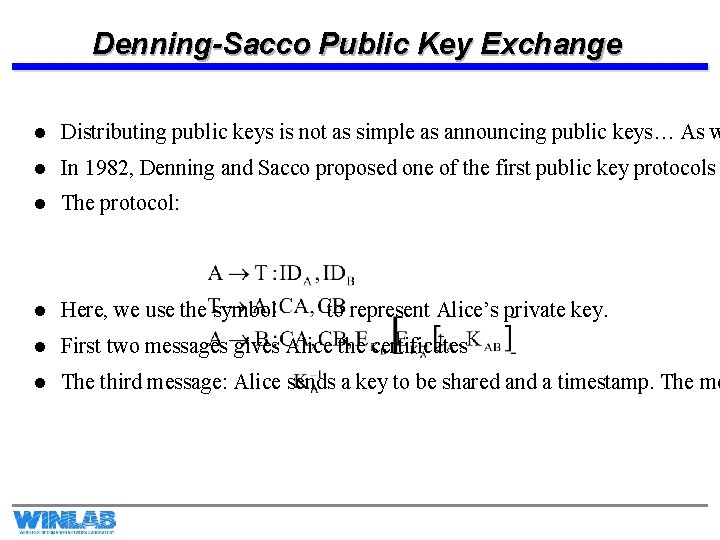
Denning-Sacco Public Key Exchange l Distributing public keys is not as simple as announcing public keys… As w l In 1982, Denning and Sacco proposed one of the first public key protocols l The protocol: l Here, we use the symbol l First two messages gives Alice the certificates l The third message: Alice sends a key to be shared and a timestamp. The me to represent Alice’s private key.
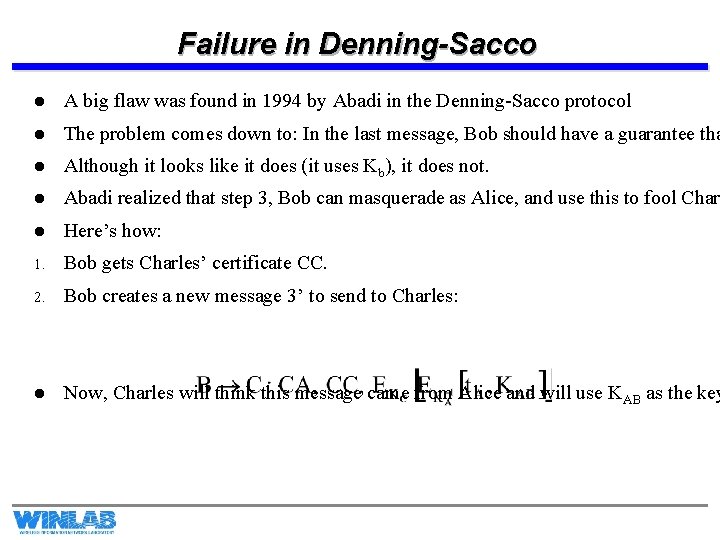
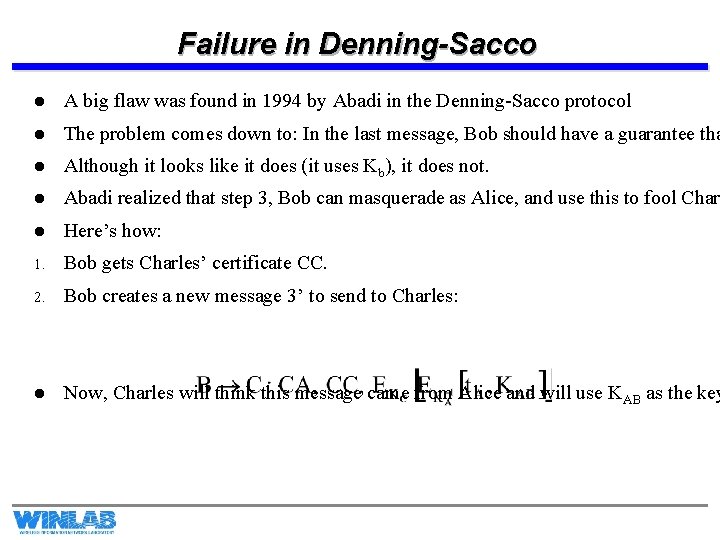
Failure in Denning-Sacco l A big flaw was found in 1994 by Abadi in the Denning-Sacco protocol l The problem comes down to: In the last message, Bob should have a guarantee tha l Although it looks like it does (it uses Kb), it does not. l Abadi realized that step 3, Bob can masquerade as Alice, and use this to fool Char l Here’s how: 1. Bob gets Charles’ certificate CC. 2. Bob creates a new message 3’ to send to Charles: l Now, Charles will think this message came from Alice and will use KAB as the key
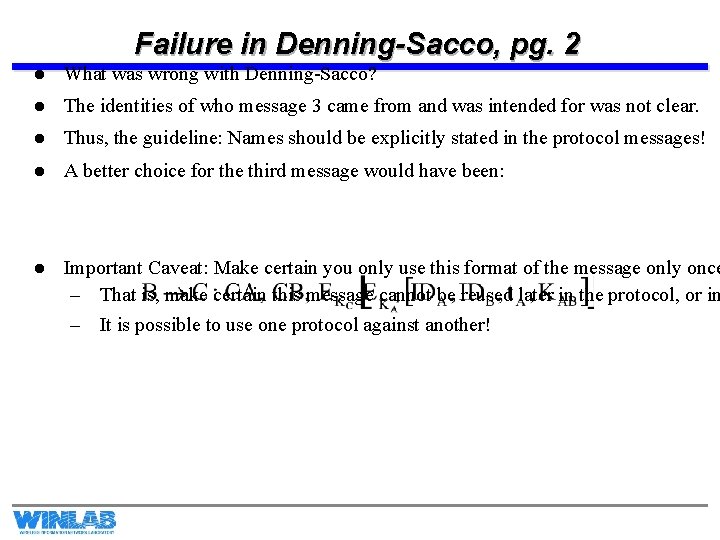
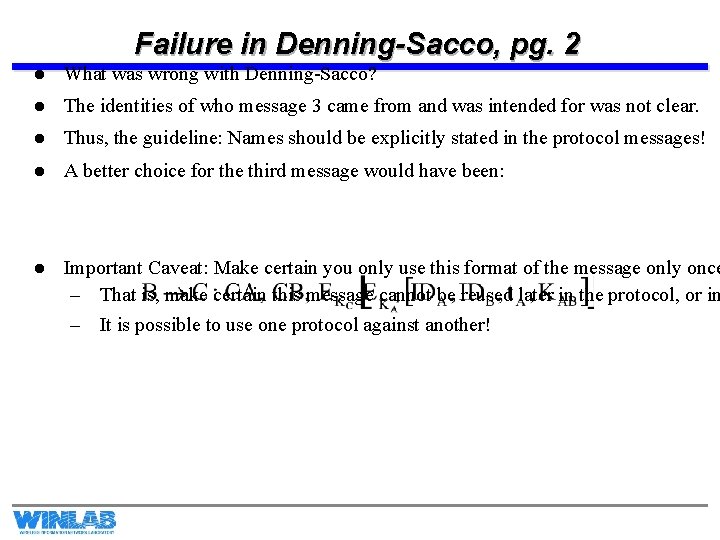
Failure in Denning-Sacco, pg. 2 l What was wrong with Denning-Sacco? l The identities of who message 3 came from and was intended for was not clear. l Thus, the guideline: Names should be explicitly stated in the protocol messages! l A better choice for the third message would have been: l Important Caveat: Make certain you only use this format of the message only once – That is, make certain this message cannot be reused later in the protocol, or in – It is possible to use one protocol against another!
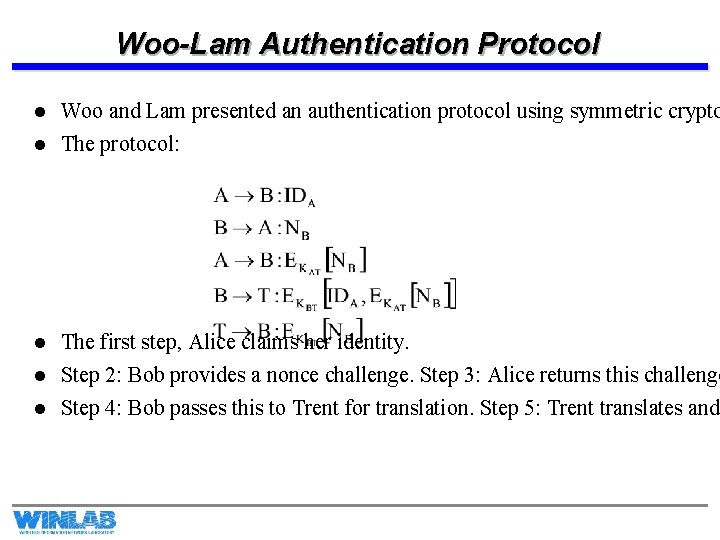
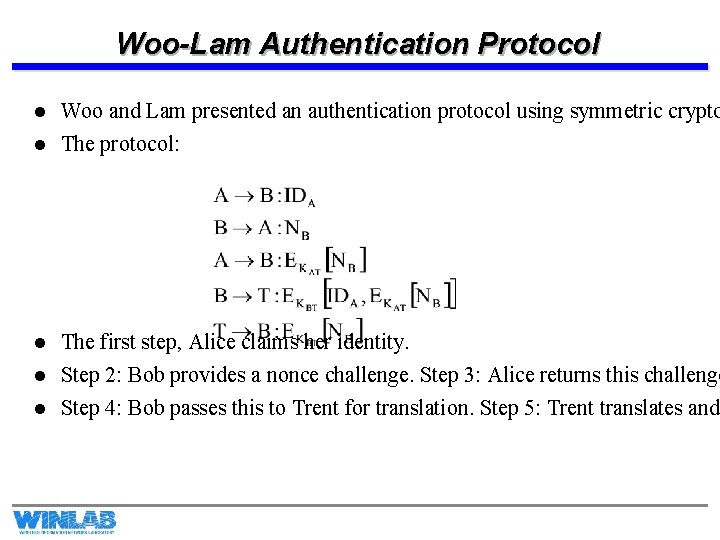
Woo-Lam Authentication Protocol l Woo and Lam presented an authentication protocol using symmetric crypto l The protocol: l The first step, Alice claims her identity. Step 2: Bob provides a nonce challenge. Step 3: Alice returns this challenge Step 4: Bob passes this to Trent for translation. Step 5: Trent translates and l l
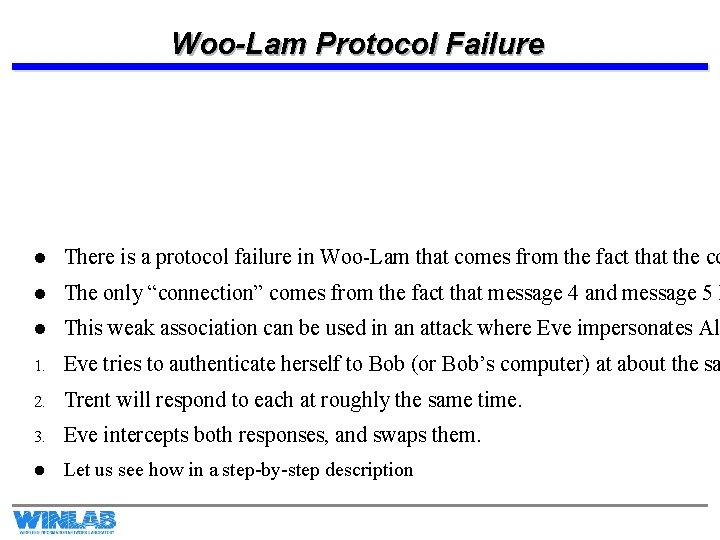
Woo-Lam Protocol Failure l There is a protocol failure in Woo-Lam that comes from the fact that the co l The only “connection” comes from the fact that message 4 and message 5 h l This weak association can be used in an attack where Eve impersonates Al 1. Eve tries to authenticate herself to Bob (or Bob’s computer) at about the sa 2. Trent will respond to each at roughly the same time. 3. Eve intercepts both responses, and swaps them. l Let us see how in a step-by-step description
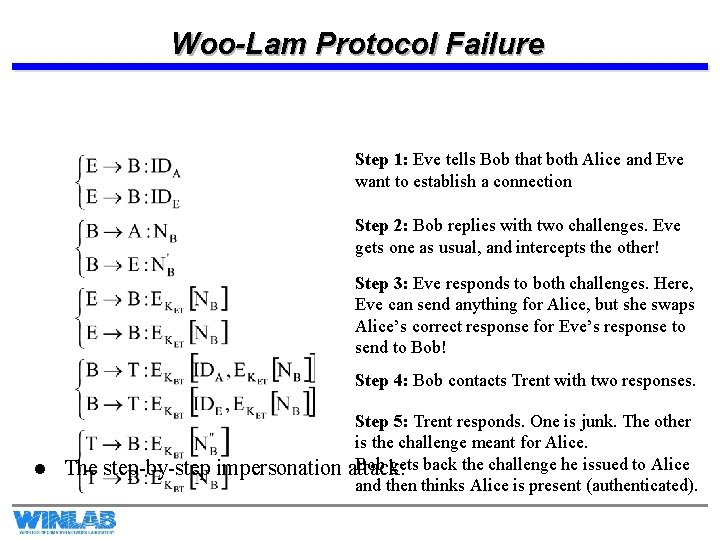
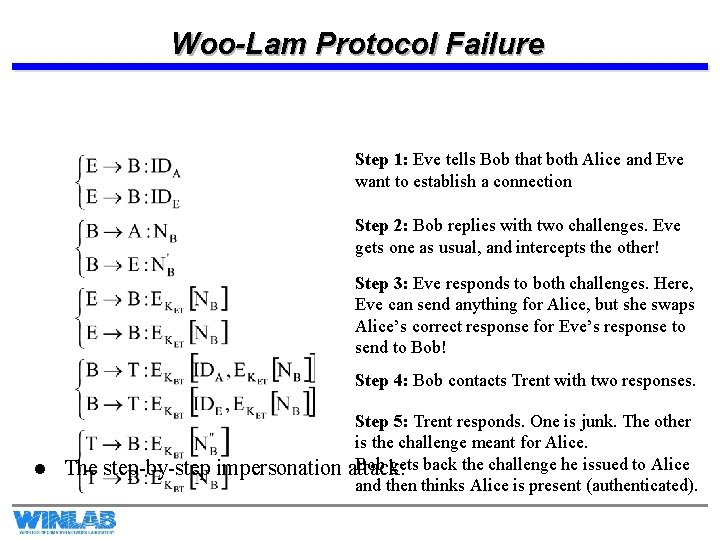
Woo-Lam Protocol Failure Step 1: Eve tells Bob that both Alice and Eve want to establish a connection Step 2: Bob replies with two challenges. Eve gets one as usual, and intercepts the other! Step 3: Eve responds to both challenges. Here, Eve can send anything for Alice, but she swaps Alice’s correct response for Eve’s response to send to Bob! Step 4: Bob contacts Trent with two responses. l The step-by-step impersonation Step 5: Trent responds. One is junk. The other is the challenge meant for Alice. Bob gets back the challenge he issued to Alice attack: and then thinks Alice is present (authenticated).
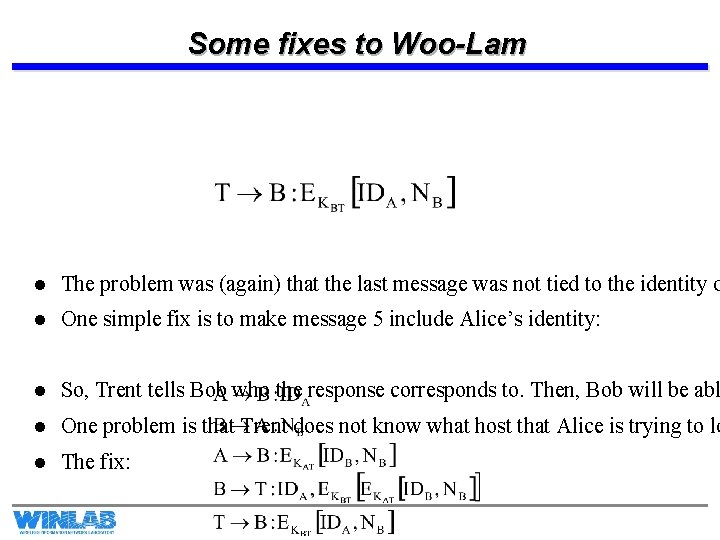
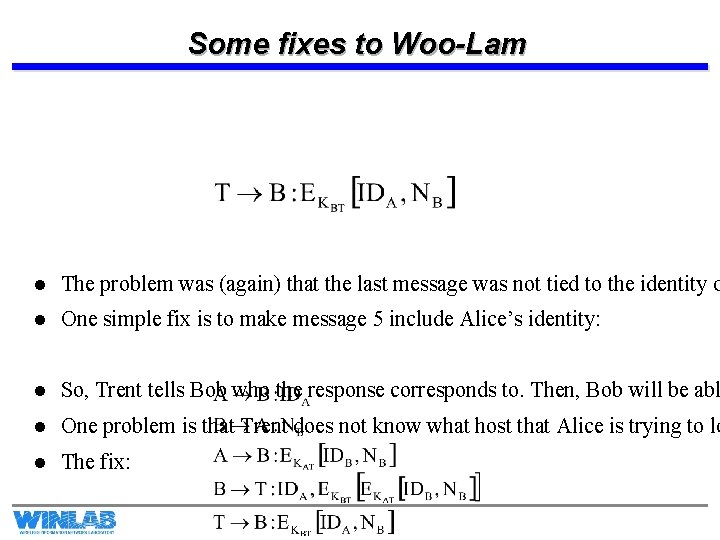
Some fixes to Woo-Lam l The problem was (again) that the last message was not tied to the identity o l One simple fix is to make message 5 include Alice’s identity: l So, Trent tells Bob who the response corresponds to. Then, Bob will be abl l One problem is that Trent does not know what host that Alice is trying to lo l The fix:
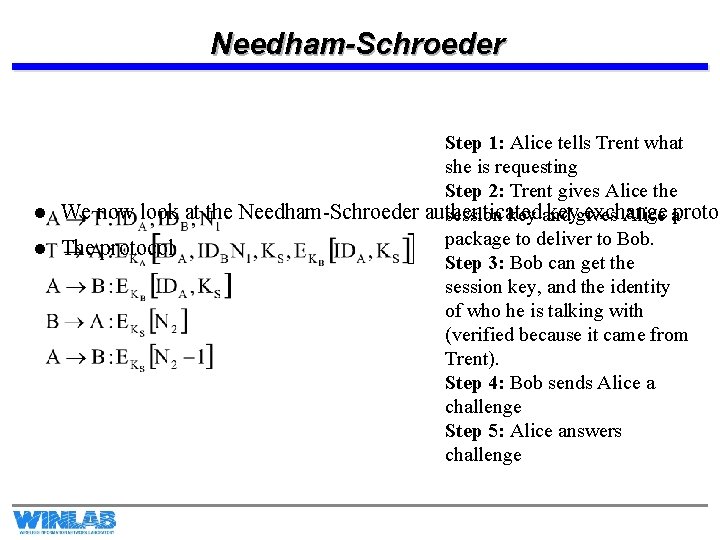
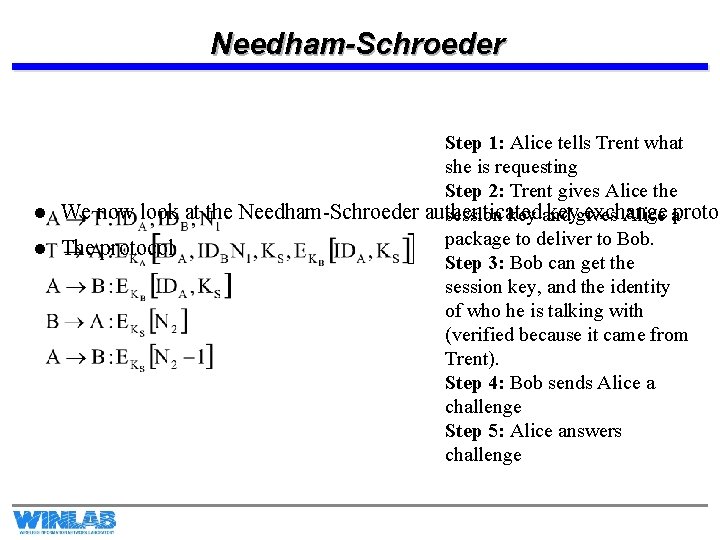
Needham-Schroeder Step 1: Alice tells Trent what she is requesting Step 2: Trent gives Alice the l We now look at the Needham-Schroeder authenticated keygives exchange session key and Alice aprotoc package to deliver to Bob. l The protocol Step 3: Bob can get the session key, and the identity of who he is talking with (verified because it came from Trent). Step 4: Bob sends Alice a challenge Step 5: Alice answers challenge
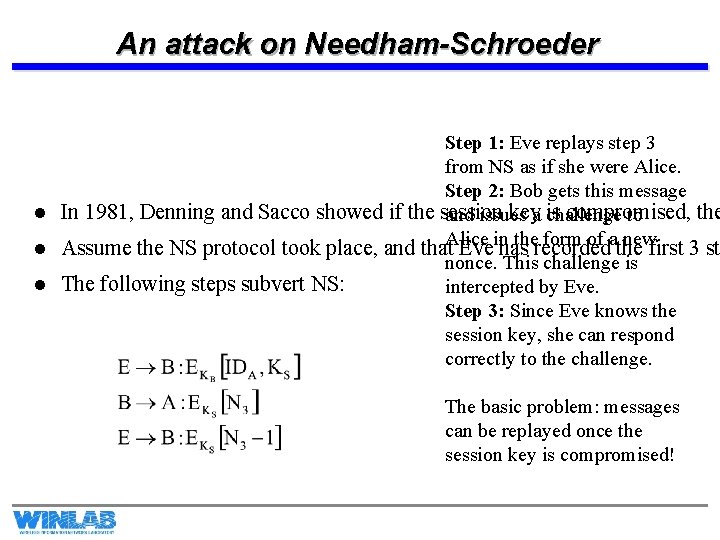
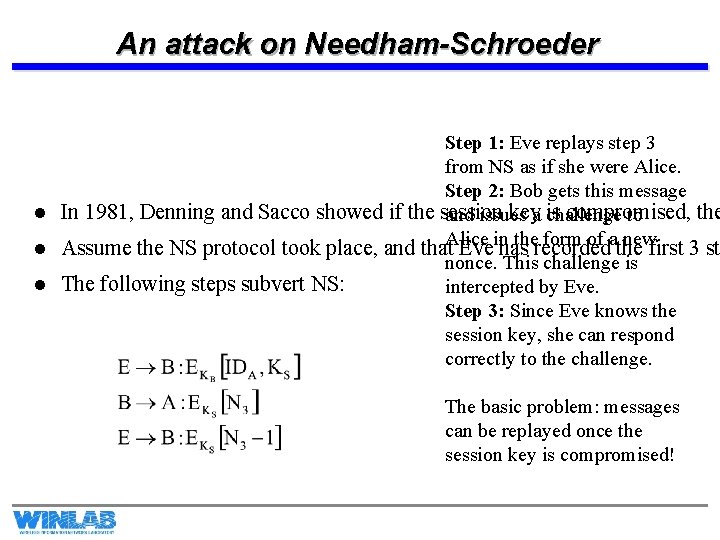
An attack on Needham-Schroeder Step 1: Eve replays step 3 from NS as if she were Alice. Step 2: Bob gets this message l In 1981, Denning and Sacco showed if the session keya challenge is compromised, the and issues to Alice in the form of a new l Assume the NS protocol took place, and that Eve has recorded the first 3 st nonce. This challenge is l The following steps subvert NS: intercepted by Eve. Step 3: Since Eve knows the session key, she can respond correctly to the challenge. The basic problem: messages can be replayed once the session key is compromised!
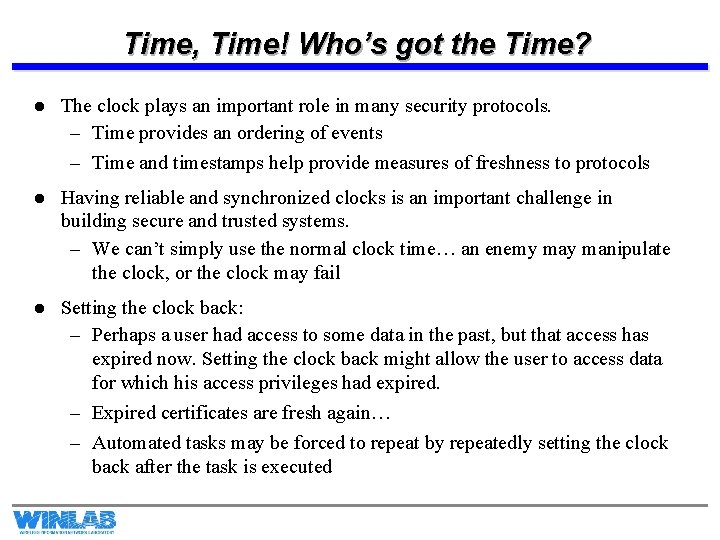
Time, Time! Who’s got the Time? l The clock plays an important role in many security protocols. – Time provides an ordering of events – Time and timestamps help provide measures of freshness to protocols l Having reliable and synchronized clocks is an important challenge in building secure and trusted systems. – We can’t simply use the normal clock time… an enemy manipulate the clock, or the clock may fail l Setting the clock back: – Perhaps a user had access to some data in the past, but that access has expired now. Setting the clock back might allow the user to access data for which his access privileges had expired. – Expired certificates are fresh again… – Automated tasks may be forced to repeat by repeatedly setting the clock back after the task is executed
Time, Time! Who’s got the Time? Pg. 2 l Stop the time: – An adversary may freeze the clock and thereby cause audit logs to become ambiguous – Actions, such as refreshes, no longer happen. l Setting the clock ahead: – Denial of service attacks are possible: Certificates automatically expire! – Many situations involve release of confidential information at a specified time in the future… moving the clock ahead forces the release of this information! – In auction-based systems, if you can alter the auction-system clock forward, you can deny many rivals the opportunity to get last-bids in.
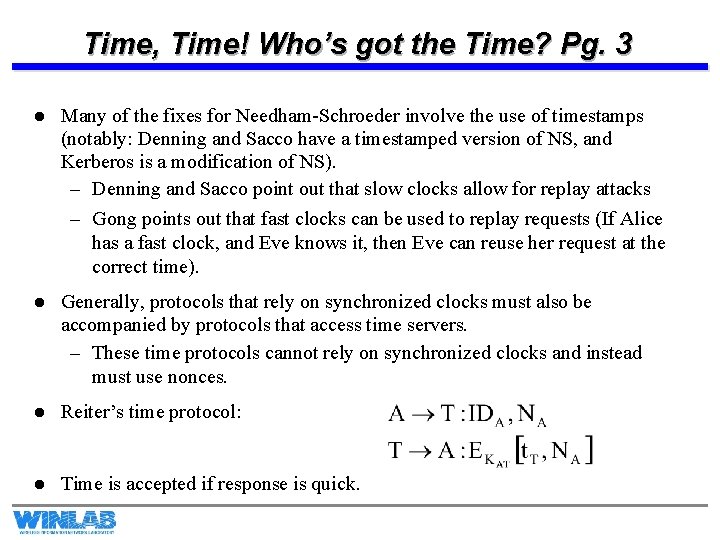
Time, Time! Who’s got the Time? Pg. 3 l Many of the fixes for Needham-Schroeder involve the use of timestamps (notably: Denning and Sacco have a timestamped version of NS, and Kerberos is a modification of NS). – Denning and Sacco point out that slow clocks allow for replay attacks – Gong points out that fast clocks can be used to replay requests (If Alice has a fast clock, and Eve knows it, then Eve can reuse her request at the correct time). l Generally, protocols that rely on synchronized clocks must also be accompanied by protocols that access time servers. – These time protocols cannot rely on synchronized clocks and instead must use nonces. l Reiter’s time protocol: l Time is accepted if response is quick.
Kerberos l l l Kerberos is a real-world implementation of a symmetric cryptographic protocol that provides authentication and security during key exchange between users in a network. It is, basically, a real-world implementation of Needham-Schroeder with some appropriate fixes. Kerberos grew out of MIT’s Project Athena, whose purpose was to integrate a network of computer workstations and allow students to access files easily from anywhere on the network. Kerberos is based upon a client-server model. Actors: – Cliff: The Client, wants to use a service – Serge: The service server – Trent: A Trusted Authority (also called an Authentication Server) – Grant: Ticket Granting Server There are two versions of Kerberos in use (Version 4 and Version 5). We will discuss the basics common to them both.
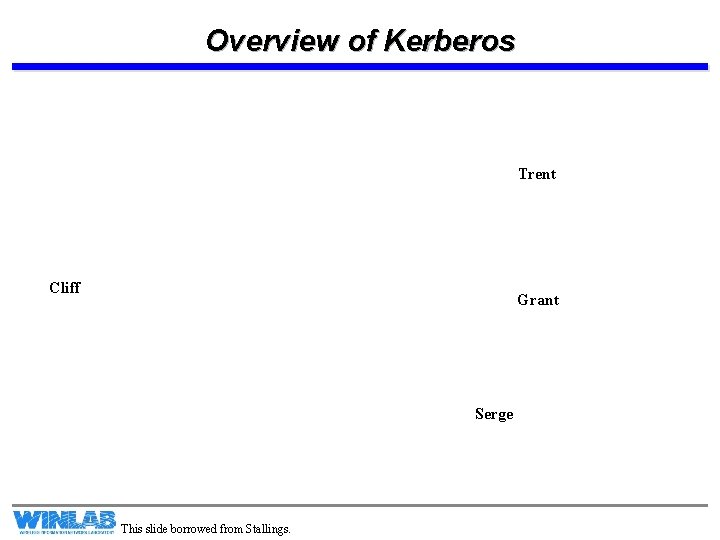
Overview of Kerberos Trent Cliff Grant Serge This slide borrowed from Stallings.
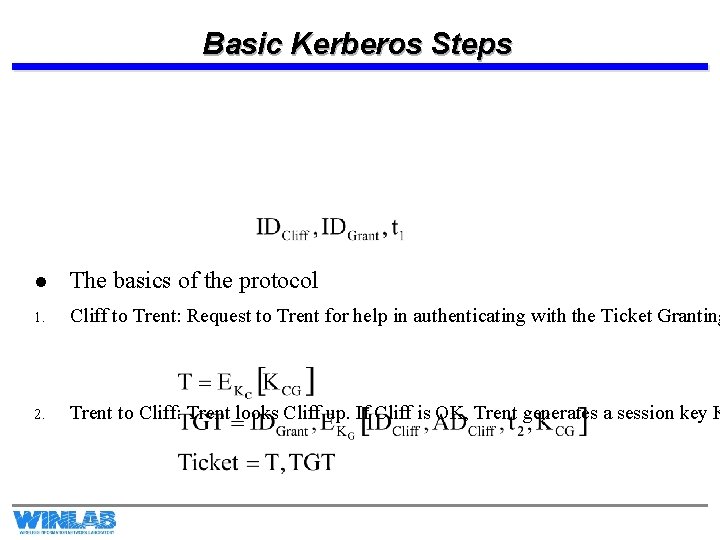
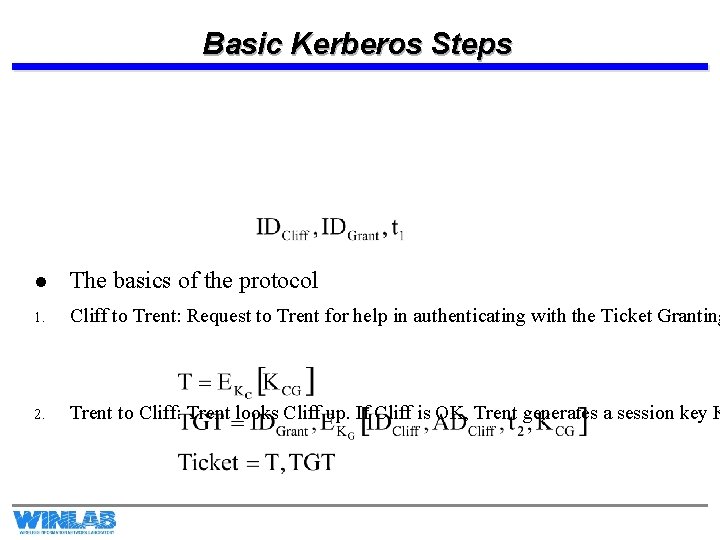
Basic Kerberos Steps l The basics of the protocol 1. Cliff to Trent: Request to Trent for help in authenticating with the Ticket Granting 2. Trent to Cliff: Trent looks Cliff up. If Cliff is OK, Trent generates a session key K
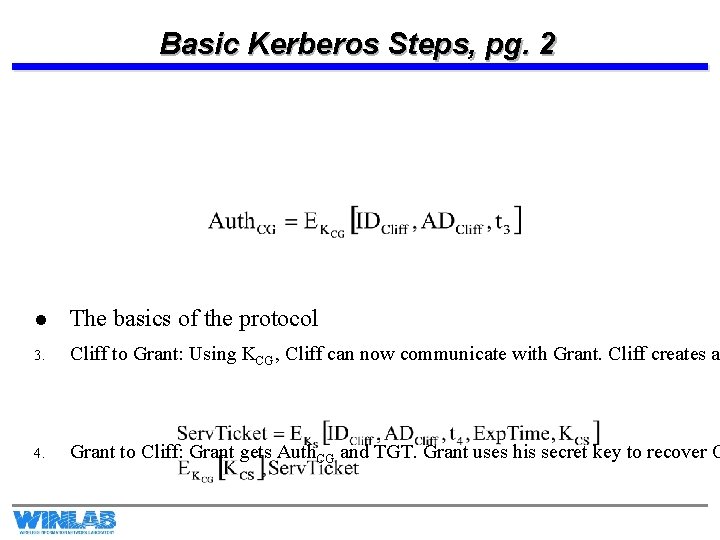
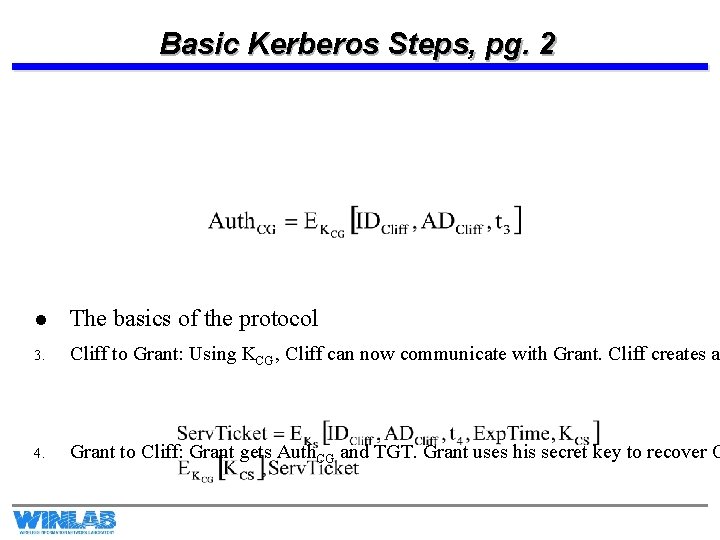
Basic Kerberos Steps, pg. 2 l The basics of the protocol 3. Cliff to Grant: Using KCG, Cliff can now communicate with Grant. Cliff creates a 4. Grant to Cliff: Grant gets Auth. CG and TGT. Grant uses his secret key to recover C
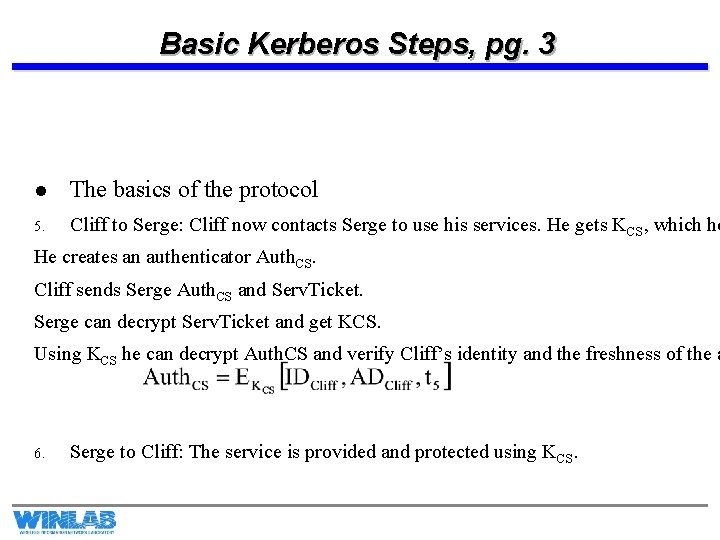
Basic Kerberos Steps, pg. 3 l The basics of the protocol 5. Cliff to Serge: Cliff now contacts Serge to use his services. He gets KCS, which he He creates an authenticator Auth. CS. Cliff sends Serge Auth. CS and Serv. Ticket. Serge can decrypt Serv. Ticket and get KCS. Using KCS he can decrypt Auth. CS and verify Cliff’s identity and the freshness of the a 6. Serge to Cliff: The service is provided and protected using KCS.
A few last remarks about Kerberos l Lifetime of authenticators is a challenge – Too short and you will repeatedly have to enter your password – Too long and the security is weakened… there is a greater opportunity for replay attacks. l The actual implementation details and exact protocol messages are more involved than was just described There are differences between V. 4 and V. 5 – Encryption modes (V. 4 uses DES, and uses a mode of operation called Propagating Block Chaining. PCBC is known to have a weakness to interchange attacks. V. 5 uses CBC and allows you to specify encryption algorithm. ) – Double encryptions (message 2 and 4) are not necessary – V. 4 strictly is for IP based networks – Many other little differences… l l Note: A paper is placed on website describing Kerberos V. 4