Security Overview of Dynamics AX and D 365

- Slides: 23
Security Overview of Dynamics AX and D 365 FO Alex Meyer Director of Dynamics AX/365 FO Development Fastpath, Inc. meyer@gofastpath. com Twitter: @alexmeyer_ITGuy Blog: d 365 foblog. com
Agenda • • Welcome AX 2012 Security Model Overview D 365 FO Security Model Overview Security Development Tool Demo Common Data Service GDPR Features Questions
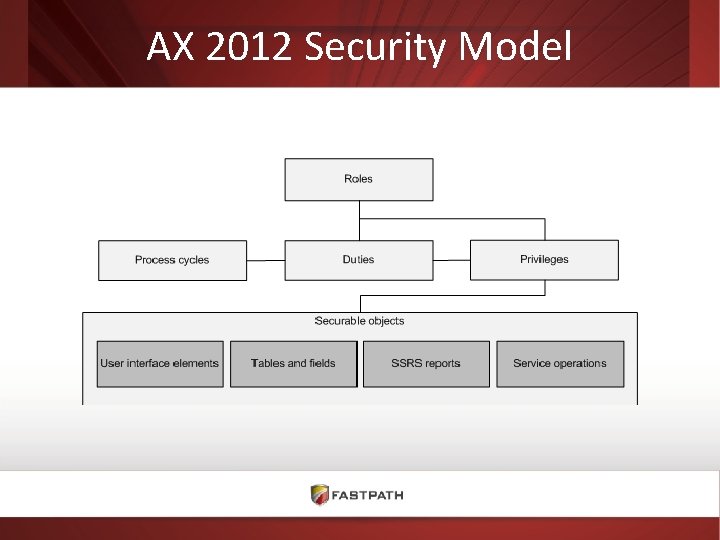
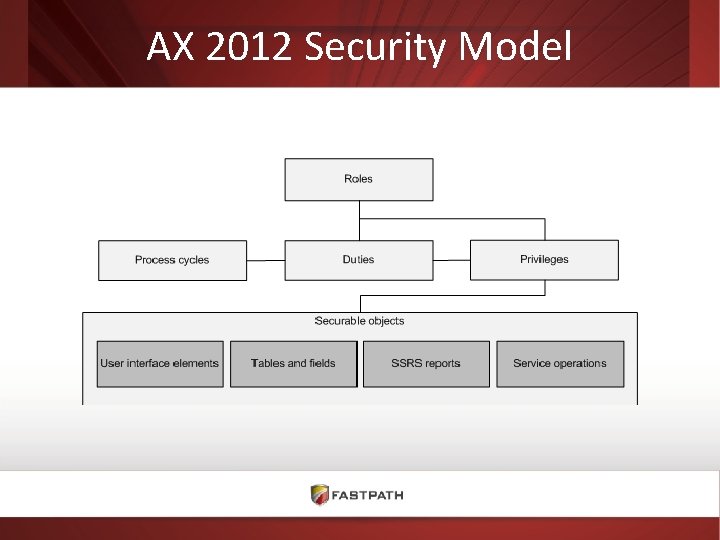
AX 2012 Security Model
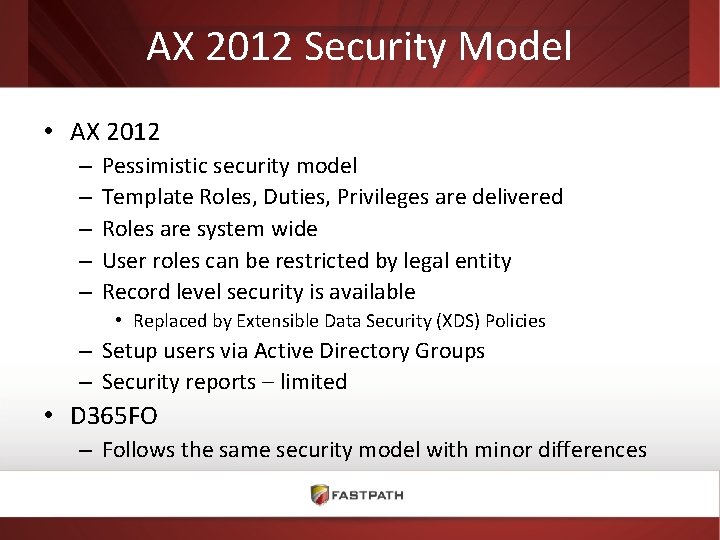
AX 2012 Security Model • AX 2012 – – – Pessimistic security model Template Roles, Duties, Privileges are delivered Roles are system wide User roles can be restricted by legal entity Record level security is available • Replaced by Extensible Data Security (XDS) Policies – Setup users via Active Directory Groups – Security reports – limited • D 365 FO – Follows the same security model with minor differences
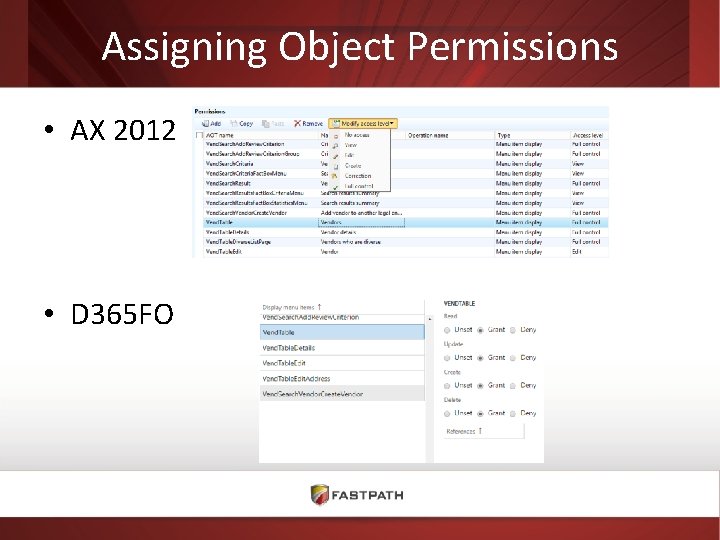
Assigning Object Permissions • AX 2012 • D 365 FO
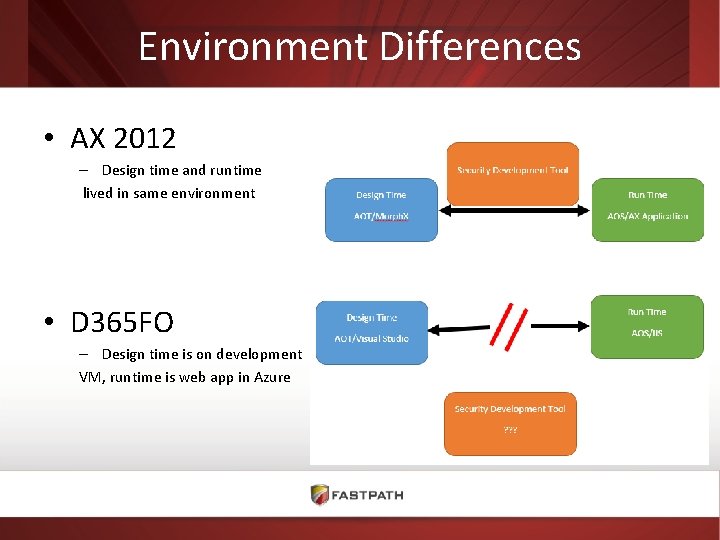
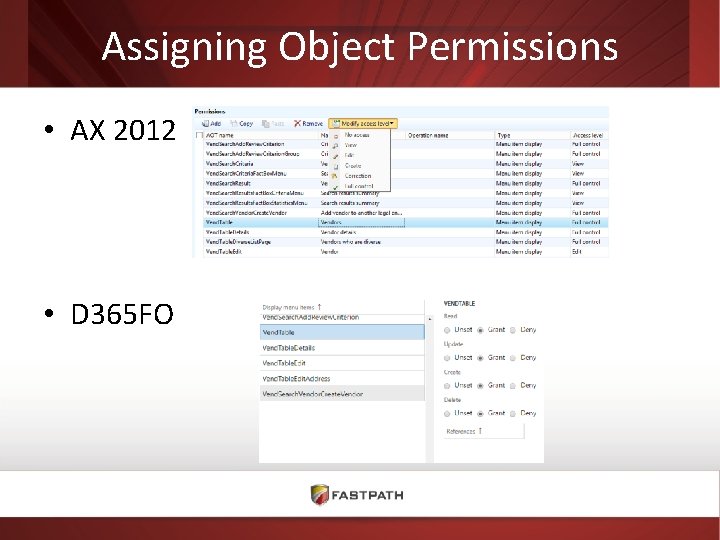
Environment Differences • AX 2012 – Design time and runtime lived in same environment • D 365 FO – Design time is on development VM, runtime is web app in Azure
D 365 FO Data Security • Transparent Data Encryption – Data and logs in Azure SQL are encrypted at rest • Table Permissions Framework (TPF) – Used for High Business Impact (HBI) data – Users must be given explicit access to field otherwise it will be hidden – Can be applied at field level • Extensible Data Security (XDS) still available
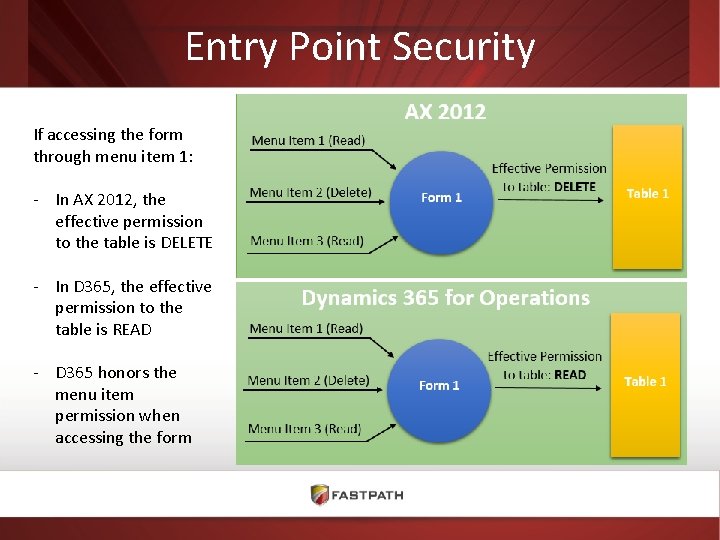
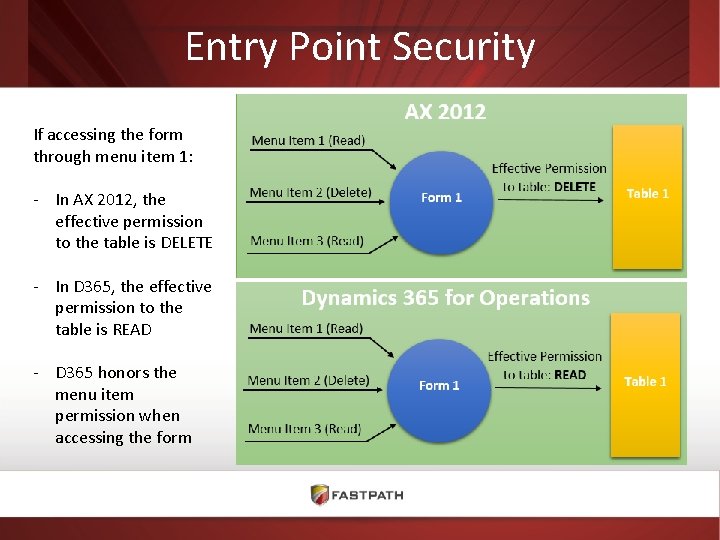
Entry Point Security If accessing the form through menu item 1: - In AX 2012, the effective permission to the table is DELETE - In D 365, the effective permission to the table is READ - D 365 honors the menu item permission when accessing the form
Data Entities • New to Dynamics 365 • Encapsulates a business concept that may exist across multiple tables with Dynamics 365 • Allows for easy CRUD operations (especially from outside of Dynamics 365) • Template Data Entities come out of the box, can create customized ones as well • Have their own security property called Integration Mode
Security Development Tool in AX • • ‘Beta’ tool from Microsoft Security reporting Task Recording Test workspace – Reduces need for test user accounts – Limitations • Cannot open test multi-role assignment (Can use sub-roles) • Does not work if you use AD Groups for user provisioning • Licensing • D 365 – Where’d it go?
Demo
Common Data Service • Centralized database to aggregate data from multiple systems • Includes mappings from source to destination environments • Comes out of the box with standard entities called the Common Data Model, can also create custom elements • Being transitioned to new version called Common Data Service for Apps (built on XRM platform with Power Apps front-end) • Since CDS is built on XRM platform, security model follows CRM security model • • Roles -> Privileges Sharing Access Levels: Global, Deep, Local, Basic, None
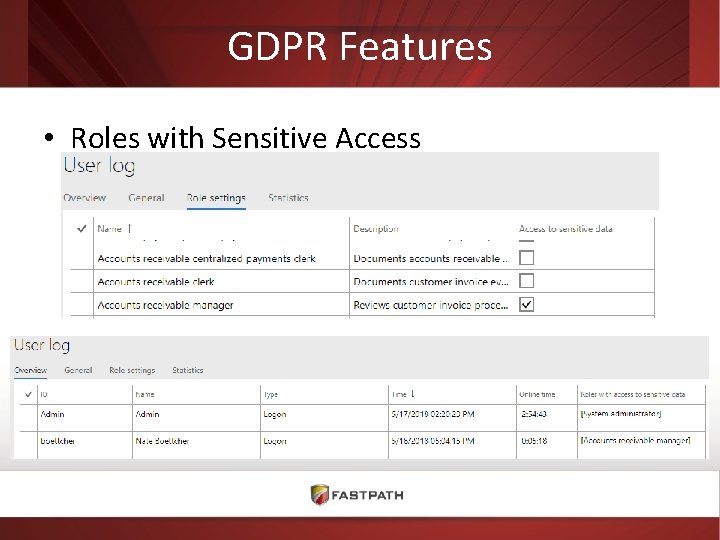
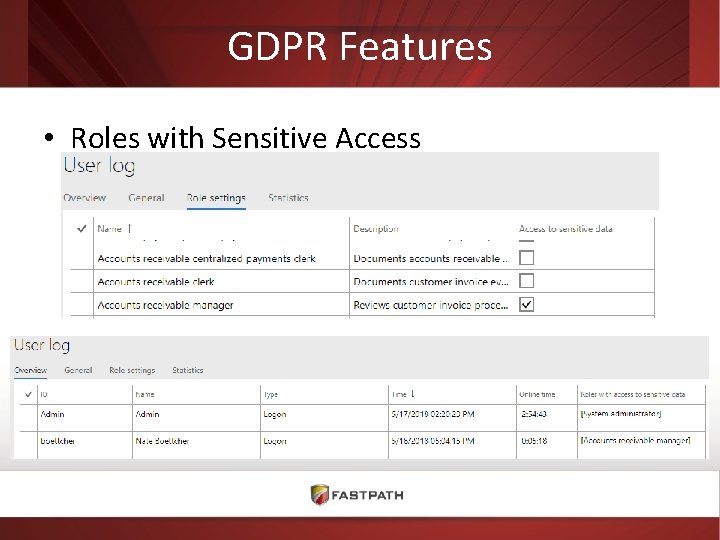
GDPR Features • Roles with Sensitive Access
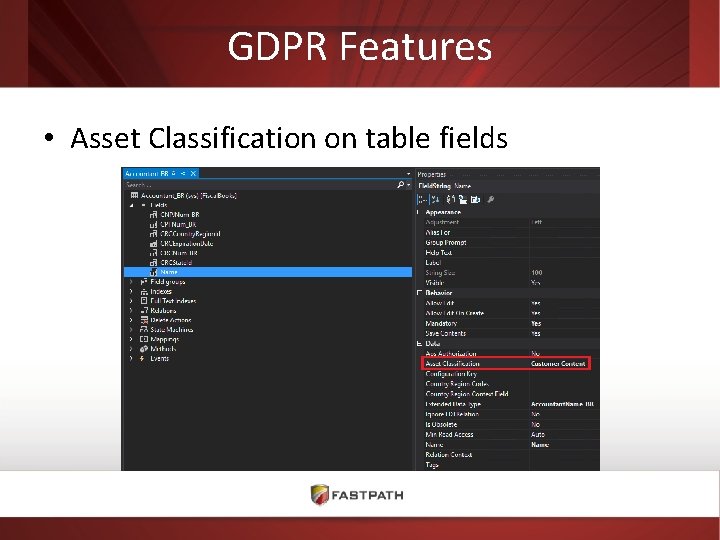
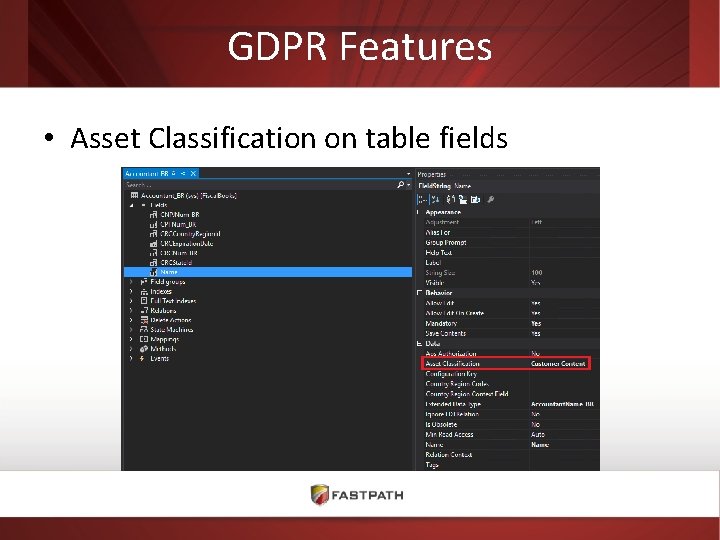
GDPR Features • Asset Classification on table fields
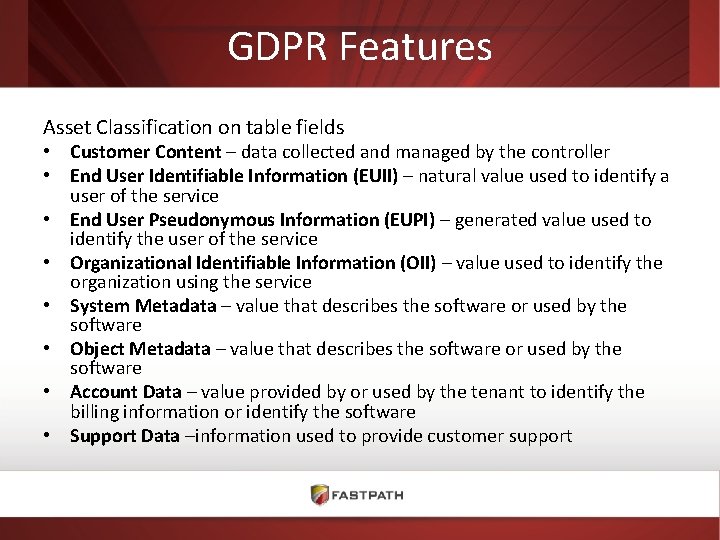
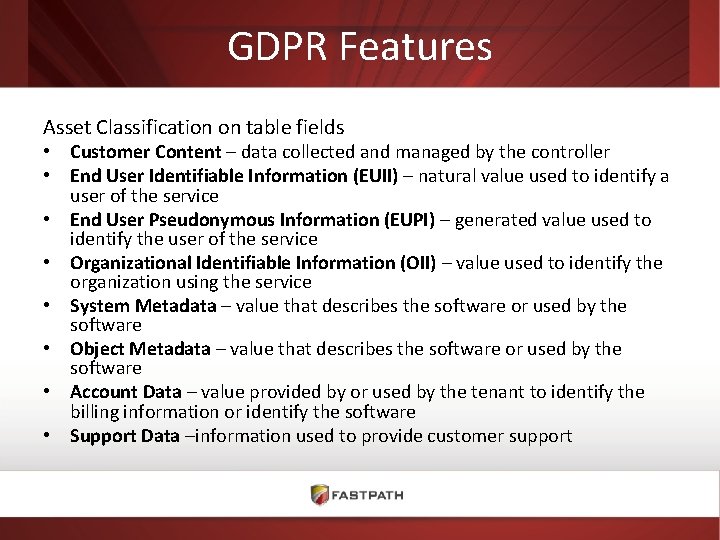
GDPR Features Asset Classification on table fields • Customer Content – data collected and managed by the controller • End User Identifiable Information (EUII) – natural value used to identify a user of the service • End User Pseudonymous Information (EUPI) – generated value used to identify the user of the service • Organizational Identifiable Information (OII) – value used to identify the organization using the service • System Metadata – value that describes the software or used by the software • Object Metadata – value that describes the software or used by the software • Account Data – value provided by or used by the tenant to identify the billing information or identify the software • Support Data –information used to provide customer support

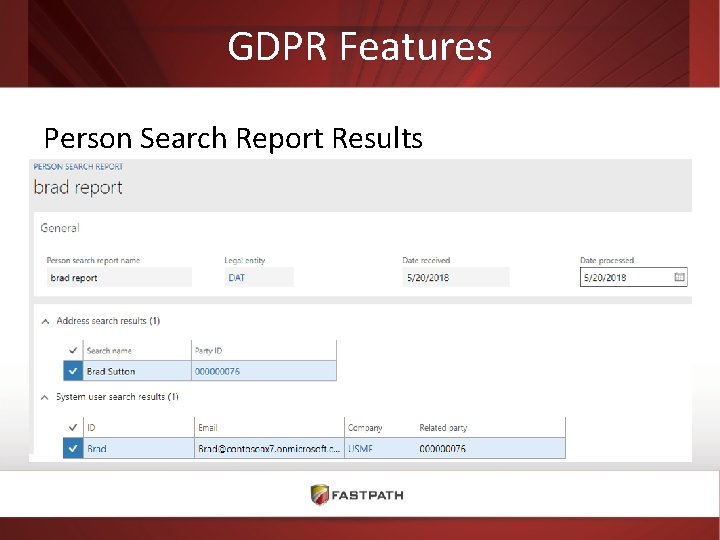
GDPR Features Person Search Report
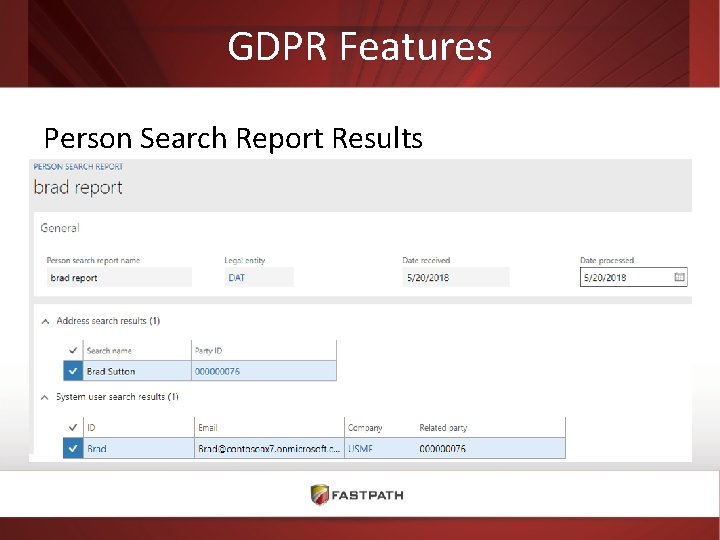
GDPR Features Person Search Report Results
Common Security Challenges • Access security is low priority for project team • Everyone assigned System Administrator • Security is in the domain of IT/Sys Admin not BPOs • Expensive customizations in place of security • No consideration for segregation of duties • Process controls not part of the design • Dilution of ‘go-live’ security design
Reviewing Security • • Take a risk based approach to reviews Monitor and report on user access BPOs should review access Update process controls and SOD rules to reflect security changes
Resources • Book – Security and Audit Field Manual for Microsoft Dynamics 365 Finance and Operations • 2 nd Edition available at Summit Phoenix www. gofastpath. com/d 365 book • Whitepaper – Develop and Implement Least Privilege Security for Dynamics 365 for Finance and Operations www. gofastpath. com/d 365 -least-privilege • Security Matrix – AX 2012 https: //www. gofastpath. com/ax-2012 -security-matrix – D 365 FO https: //www. gofastpath. com/d 365 fo-security-matrix
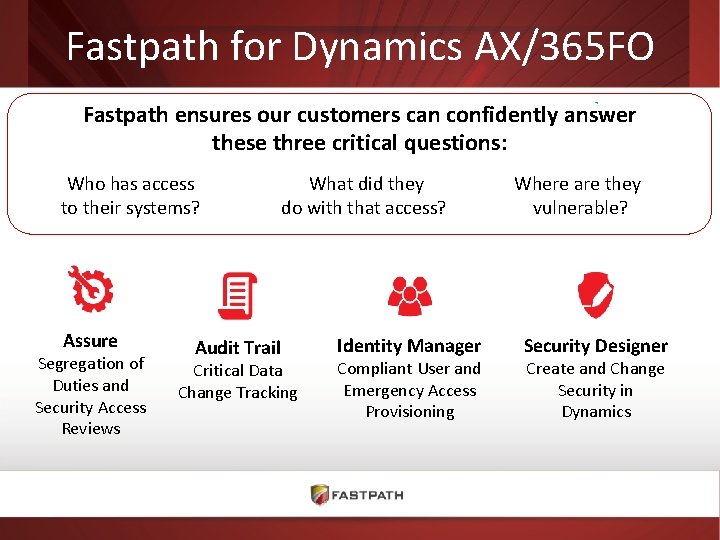
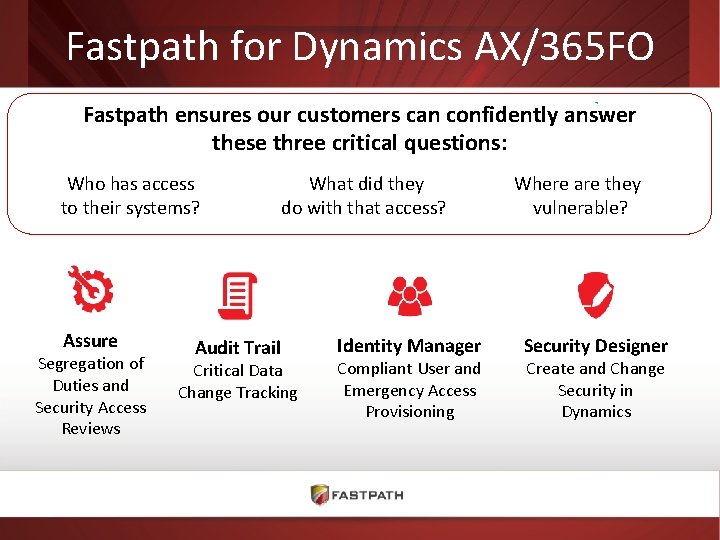
Fastpath for Dynamics AX/365 FO Fastpath ensures our customers can confidently answer these three critical questions: Who has access to their systems? Assure Segregation of Duties and Security Access Reviews Audit Trail What did they do with that access? Critical Data Change Tracking Identity Manager Compliant User and Emergency Access Provisioning Where are they vulnerable? Security Designer Create and Change Security in Dynamics
Links • • • • Dynamics 365 For Operations Blog (Personal Blog) You. Tube Tutorial on Simulating the Security Development Tool in Dynamics 365 for Operations (5: 35) D 365 Wiki Task Recorder in Microsoft Dynamics 365 for Operations Security Development Tool User Guide Microsoft Dynamics AX 2012 R 3 Licensing Guide Introduction to Microsoft Dynamics 365 licensing Dynamics AX Server Team Blog Role-based Security Use Patterns for Developers Developing Extensible Data Security Policies Security Roles & Licensing Whitepaper Table Permissions Framework Transparent Data Encryption Understanding Security in Microsoft Dynamics AX 2009
Questions? Alex Meyer Director of Dynamics AX/365 FO Development Fastpath, Inc. meyer@gofastpath. com Twitter: @alexmeyer_ITGuy Blog: d 365 foblog. com