Scaling Network Verification Plotkin Bjorner Lopes Rybalchenko Varghese
Scaling Network Verification (Plotkin, Bjorner, Lopes, Rybalchenko, Varghese, POPL 2016) - exploiting regularities in networks - symmetries and surgeries 1
Plan of lectures so far • Lecture 1 -2 : Motivation, IP review • Lectures 3 -9: Data Plane Verification, from black box (Anteater) to customized (HSA) to retrofitted (No. D) to symmetries for faster verification • Lecture 10: Other networks (cellular), other planes (control vs data), other methods (formal methods bug finding) 2
Creative Process: Keep track of spine • The spine is the strong idea that keeps a work together, an underlying theme • If you identify it early, you can keep track of it as the work evolves. • Example 1: Dance in which humility conquers hubris. Based on Euripedes • When it finished, hard for audience to see spine but obvious to creator. 3
Spines of some papers • Header Space Analysis: Analyze reachability using sets of packets regardless of layers • Atomic Predicates: Faster to precompute the header equivalence classes • No. D: Datalog is just fine and more expressive if we add a data structure and an operator • Symmetries: Design patterns give complex networks have an underlying simplicity 4
PORTRAIT ON LEAVING AMERICA: CHAPLIN WAS ANGRY. . . BUT AVEDON WAS DETERMINED. . . EVENTUALLY CHAPLIN DROPPED HIS GUARD 5
How “Vulcanized Rubber” was Made • Goodyear spends years finding a durable rubber (planning) • Drops Sulphur + gum on a hot stove and finds it chars (Accident) • Goodyear realizes if charring can stop (know amazing when you see it) • Goodyear spends years in Woburn perfecting the process (plan, work, again!) 6
Other Examples in Class • Sonu Mishra is stuck in traffic and thinks of wireless networks and rateless codes • After finishing work on IP lookups, I hear Lampson say “either security or speed” • Your personal examples 7
How “Symmetries” was Made • Gordon Plotkin visit to MSR. They fire all lab members • Gordon and I begin to talk about network verification • Nuno comes to visit and we discuss idea of using symmetry as No. D is too slow • Nikolaj comes to visit and quickly writes a script and discovers near symmetry 8
. . . How does this paper relate to paper on Atomic Predicates? 9
State Space Factoring • State of model as in model checking, NOD, and HSA is a located packet (h, p): (header, port) • Atomic predicates is about equivalence classes on headers • Symmetries in our paper is about equivalence classes on ports and rule sets. Orthogonal • But paper is also about surgeries. Reducing a complex network to a simpler one 10
Why needed. . . • Header space equivalencing: 1 query in < 1 sec. Major improvement over standard verification tools like SAT solvers and model checkers • But large data centers: 100, 000 hosts, 1 million rules, 1000 s of routers, 100 bits of header • So N^2 pairs takes 5 days to verify all specs. Scaling the N^2 overhead is what paper is about 11
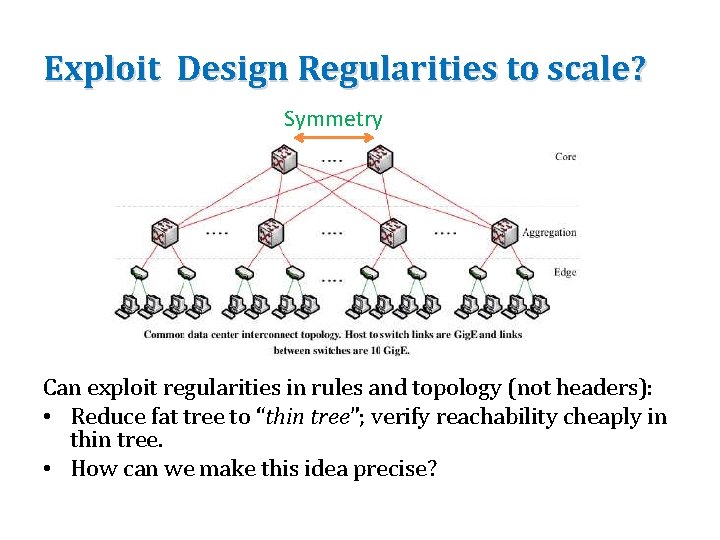
Exploit Design Regularities to scale? Symmetry Can exploit regularities in rules and topology (not headers): • Reduce fat tree to “thin tree”; verify reachability cheaply in thin tree. • How can we make this idea precise?
Model checking had used symmetry • Long ago model checking had suggested using symmetries to reduce search space • Consider N dining philosophers who need both forks to eat • Can permute philosophers and get equivalent executions 13
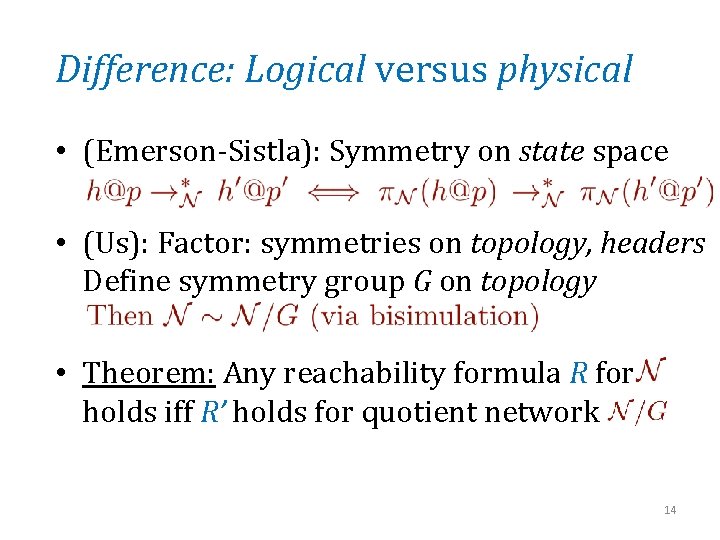
Difference: Logical versus physical • (Emerson-Sistla): Symmetry on state space • (Us): Factor: symmetries on topology, headers Define symmetry group G on topology • Theorem: Any reachability formula R for holds iff R’ holds for quotient network 14
Why is a logic needed? • We want to transform a complex network into simple using symmetries & surgeries • We want to prove that all properties of a certain type hold in C iff it holds in S • The logic defines the “properties of a certain type” Like CTL but specialized • The logic needs a definition in terms of a machine model: the state machine 15
What is bisimulation • Showing two state machines can match each other in terms of output • Two state machines A and B: define a relation between states in A and B (p, q) • Then if p transitions to p’ on x, then q transitions to q’ and (p’, q’) in relation • And vice versa. Only a proof technique that our reductions are correct. Can ignore!! 16
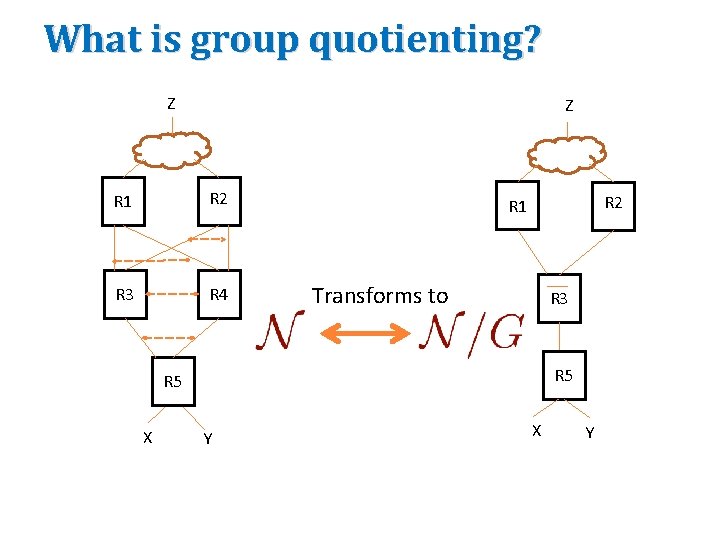
What is group quotienting? Z Z R 1 R 2 R 3 R 4 R 2 R 1 Transforms to R 3 R 5 X Y
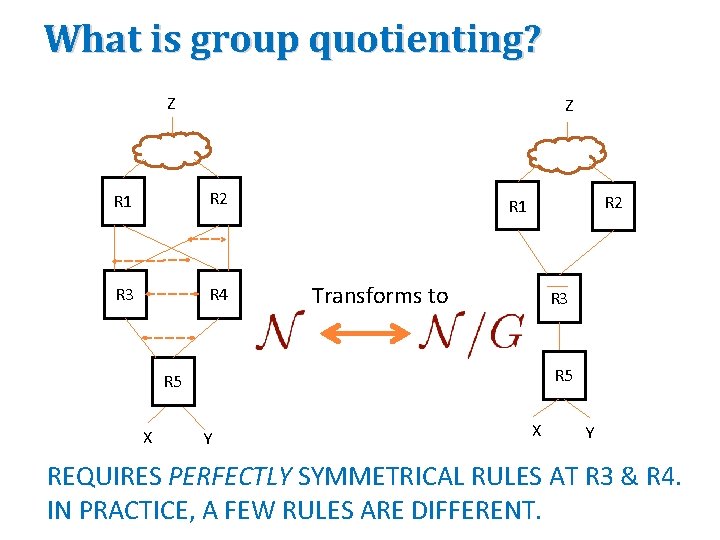
What is group quotienting? Z Z R 1 R 2 R 3 R 4 R 2 R 1 Transforms to R 3 R 5 X Y REQUIRES PERFECTLY SYMMETRICAL RULES AT R 3 & R 4. IN PRACTICE, A FEW RULES ARE DIFFERENT.
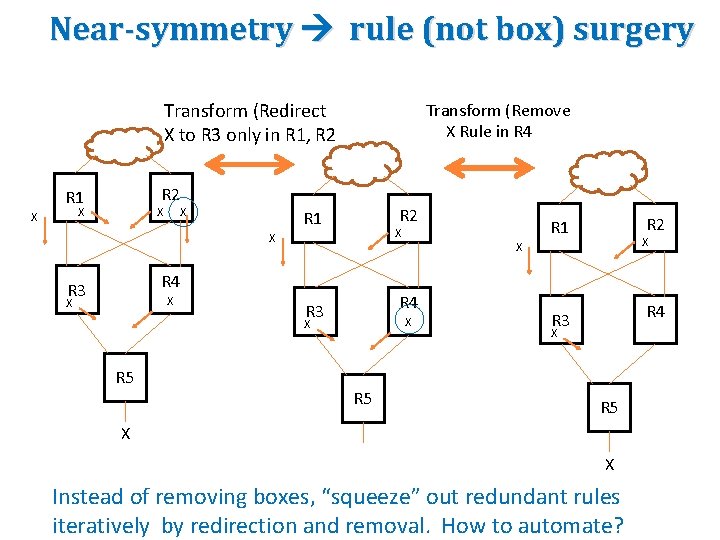
Near-symmetry rule (not box) surgery Transform (Redirect X to R 3 only in R 1, R 2 R 1 X X Transform (Remove X Rule in R 4 X R 2 R 1 X X X R 4 R 3 X X R 5 X X R 4 R 3 R 2 R 1 X R 4 R 3 X R 5 X X Instead of removing boxes, “squeeze” out redundant rules iteratively by redirection and removal. How to automate?
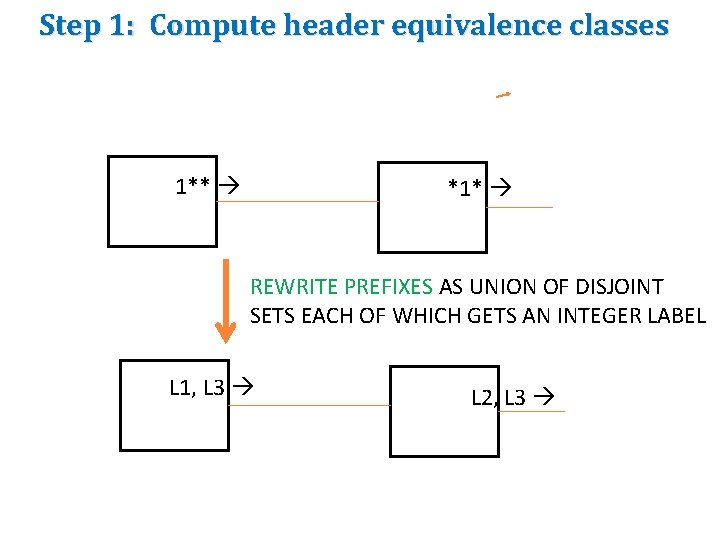
Step 1: Compute header equivalence classes 1** *1* REWRITE PREFIXES AS UNION OF DISJOINT SETS EACH OF WHICH GETS AN INTEGER LABEL L 1, L 3 L 2, L 3
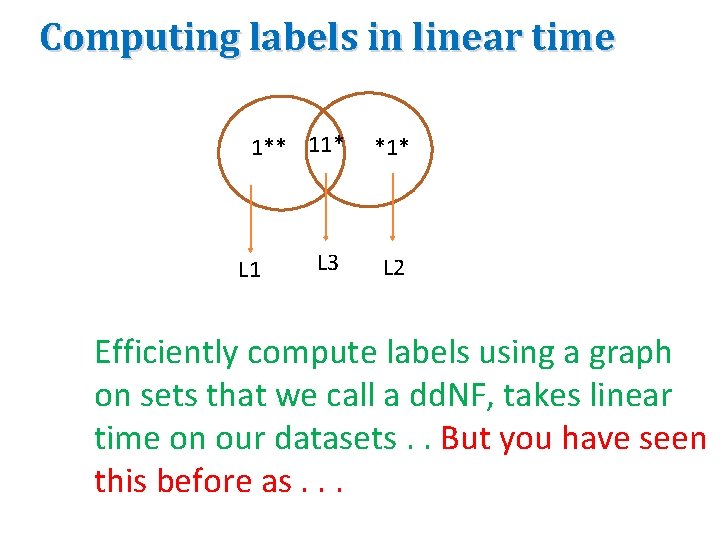
Computing labels in linear time 1** 11* *1* L 3 L 2 L 1 Efficiently compute labels using a graph on sets that we call a dd. NF, takes linear time on our datasets. . But you have seen this before as. . .
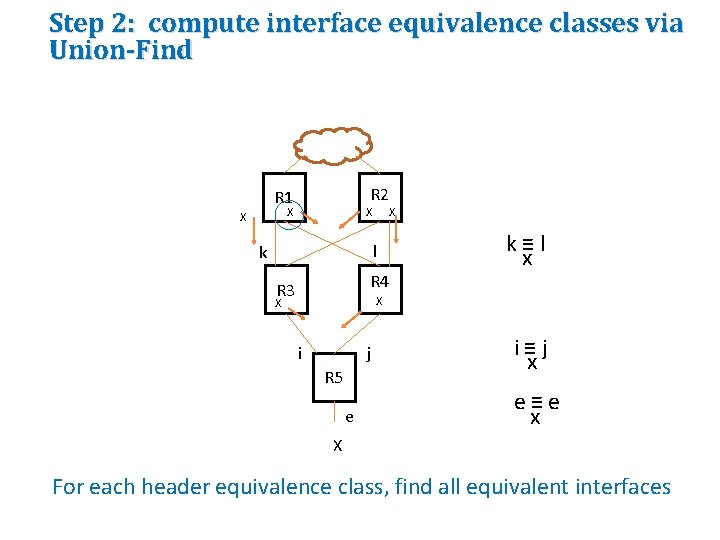
Step 2: compute interface equivalence classes via Union-Find R 2 R 1 X X X l k R 4 R 3 k≡l x X X i j R 5 e i≡j x e≡e x X For each header equivalence class, find all equivalent interfaces
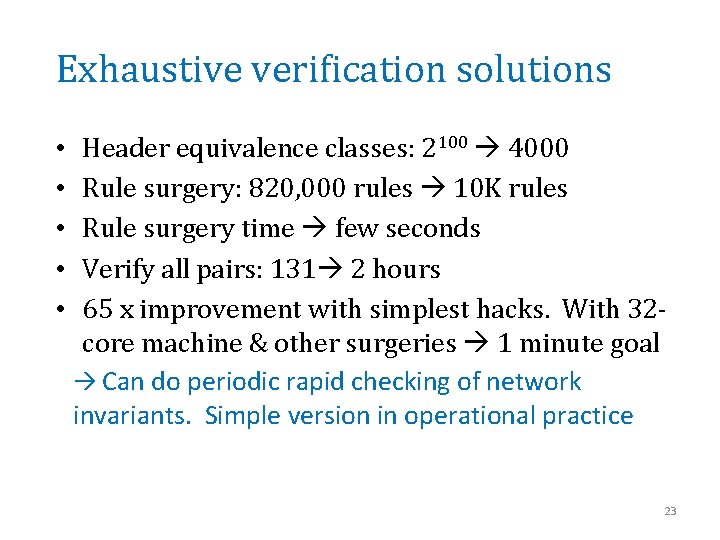
Exhaustive verification solutions • • • Header equivalence classes: 2100 4000 Rule surgery: 820, 000 rules 10 K rules Rule surgery time few seconds Verify all pairs: 131 2 hours 65 x improvement with simplest hacks. With 32 core machine & other surgeries 1 minute goal Can do periodic rapid checking of network invariants. Simple version in operational practice 23
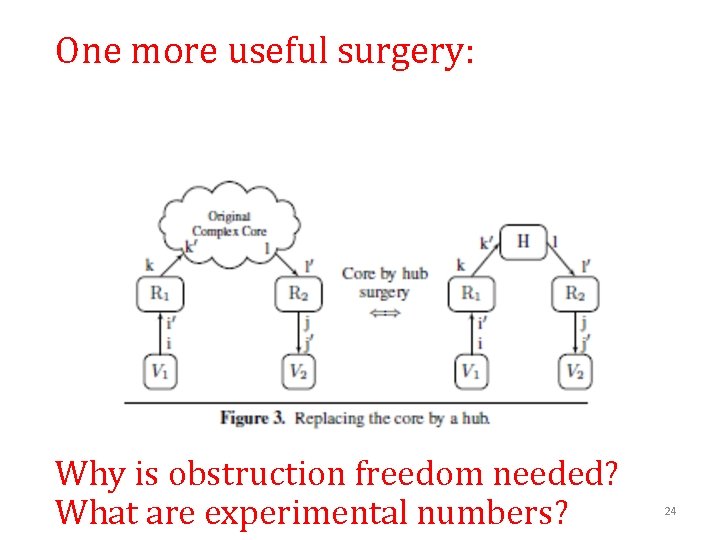
One more useful surgery: Why is obstruction freedom needed? What are experimental numbers? 24
More questions • Other surgeries? • What are criticisms of paper? • What are criticism of evaluation? 25
- Slides: 25