Review Software Security David Brumley dbrumleycmu edu Carnegie
Review: Software Security David Brumley dbrumley@cmu. edu Carnegie Mellon University
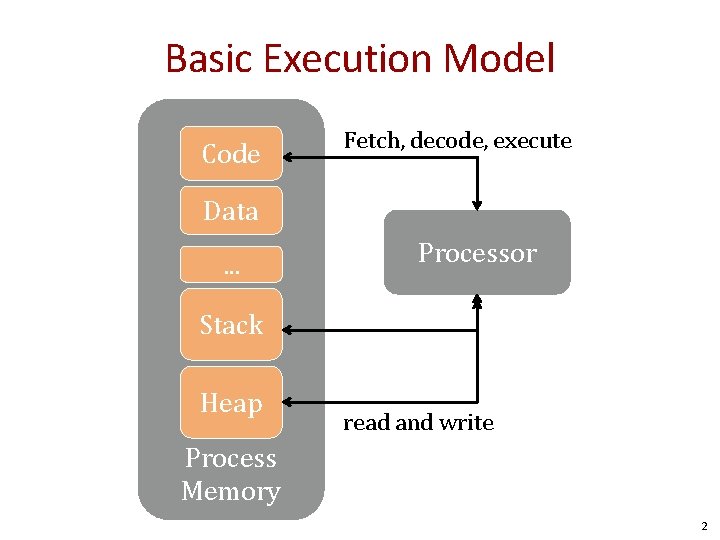
Basic Execution Model Code Fetch, decode, execute Data. . . Processor Stack Heap read and write Process Memory 2
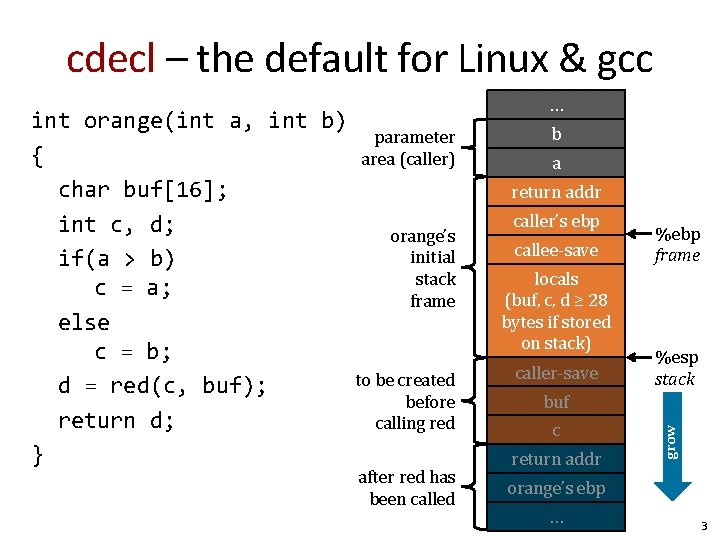
cdecl – the default for Linux & gcc parameter area (caller) b a return addr orange’s initial stack frame to be created before calling red after red has been called caller’s ebp callee-save locals (buf, c, d ≥ 28 bytes if stored on stack) caller-save %ebp frame %esp stack buf c return addr grow int orange(int a, int b) { char buf[16]; int c, d; if(a > b) c = a; else c = b; d = red(c, buf); return d; } … orange’s ebp … 3
Be prepared to draw and analyze stack diagrams 4
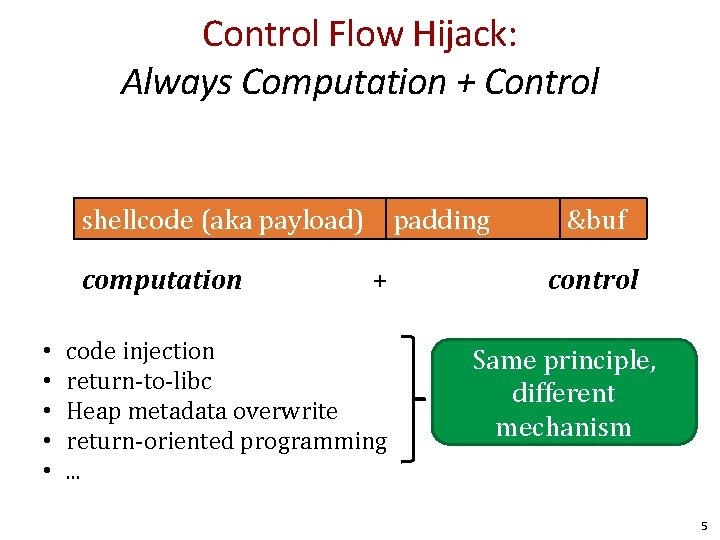
Control Flow Hijack: Always Computation + Control shellcode (aka payload) computation • • • padding + code injection return-to-libc Heap metadata overwrite return-oriented programming. . . &buf control Same principle, different mechanism 5
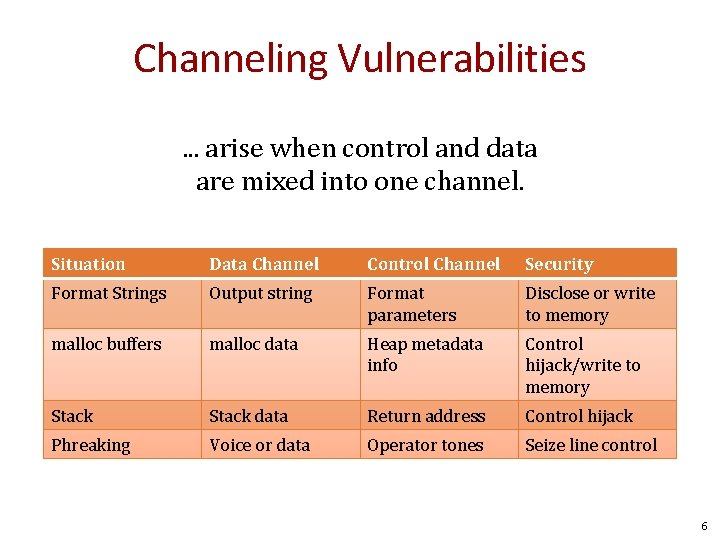
Channeling Vulnerabilities. . . arise when control and data are mixed into one channel. Situation Data Channel Control Channel Security Format Strings Output string Format parameters Disclose or write to memory malloc buffers malloc data Heap metadata info Control hijack/write to memory Stack data Return address Control hijack Phreaking Voice or data Operator tones Seize line control 6
Buffer overflows • Gaining control through. . . – Overwriting saved return addresses – Overwriting function pointers 7
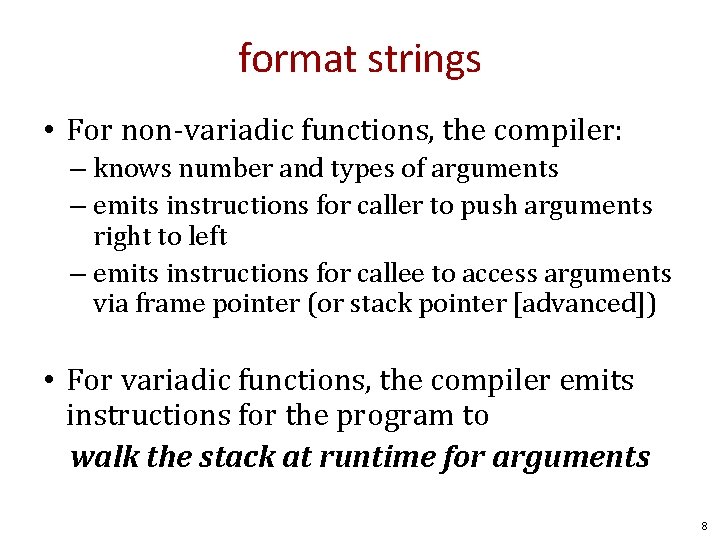
format strings • For non-variadic functions, the compiler: – knows number and types of arguments – emits instructions for caller to push arguments right to left – emits instructions for callee to access arguments via frame pointer (or stack pointer [advanced]) • For variadic functions, the compiler emits instructions for the program to walk the stack at runtime for arguments 8
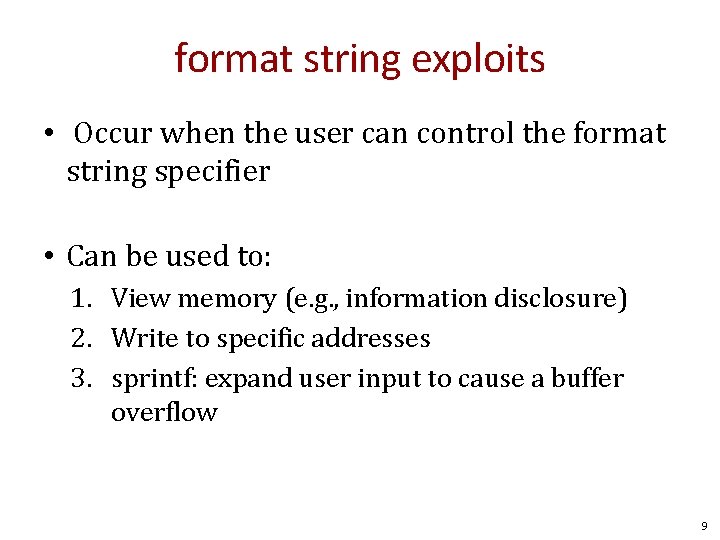
format string exploits • Occur when the user can control the format string specifier • Can be used to: 1. View memory (e. g. , information disclosure) 2. Write to specific addresses 3. sprintf: expand user input to cause a buffer overflow 9
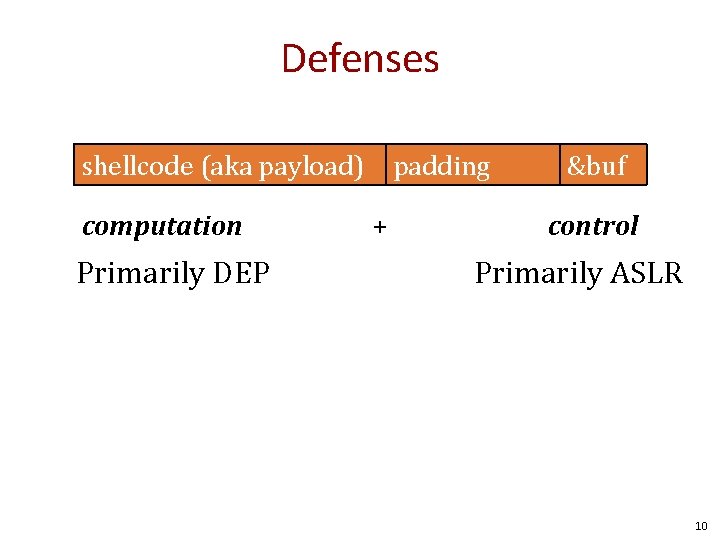
Defenses shellcode (aka payload) computation Primarily DEP padding + &buf control Primarily ASLR 10
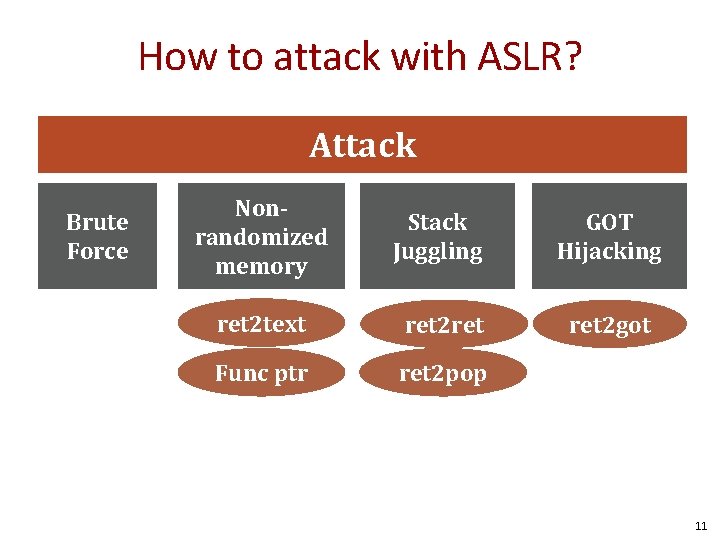
How to attack with ASLR? Attack Brute Force Nonrandomized memory Stack Juggling GOT Hijacking ret 2 text ret 2 ret 2 got Func ptr ret 2 pop 11
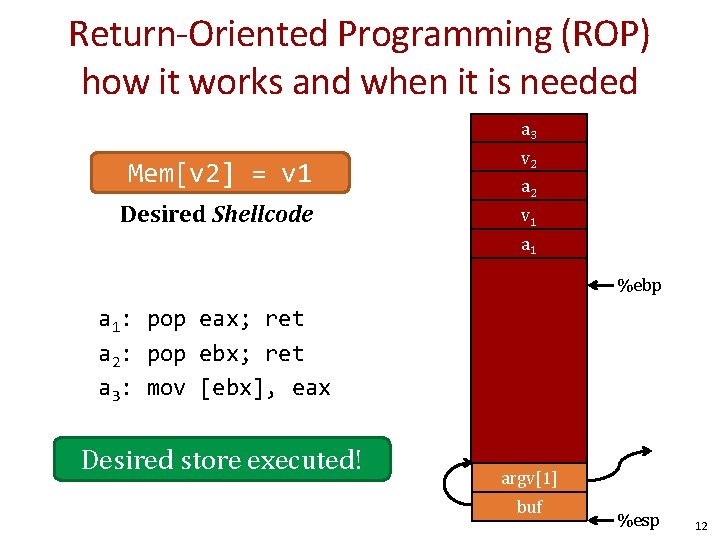
Return-Oriented Programming (ROP) how it works and when it is needed a 3 Mem[v 2] = v 1 Desired Shellcode v… 2 argv a 2 argc v 1 return a 1 addr caller’s ebp %ebp a 1: pop eax; ret a 2: pop ebx; ret a 3: mov [ebx], eax Desired store executed! buf (64 bytes) argv[1] buf %esp 12
CFI • Sound/Complete • Sensitivity in program analysis • CFI instrumentation • CFI assumptions 13
Test • In-class • Timed • Closed book, closed note, closed computer Good Luck! 14

Questions? 15
END

Thought 17
- Slides: 17