Public Key Cryptography David Brumley dbrumleycmu edu Carnegie
Public Key Cryptography David Brumley dbrumley@cmu. edu Carnegie Mellon University Credits: Many slides from Dan Boneh’s June 2012 Coursera crypto class, which is awesome!
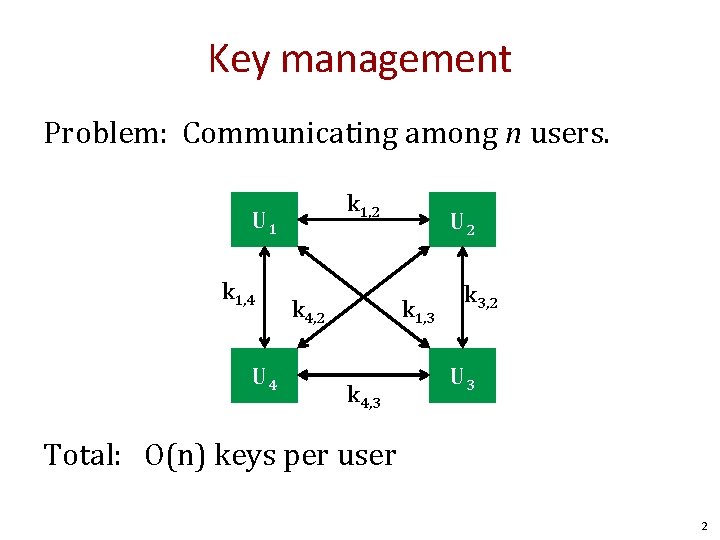
Key management Problem: Communicating among n users. k 1, 2 U 1 k 1, 4 U 4 k 4, 2 U 2 k 1, 3 k 4, 3 k 3, 2 U 3 Total: O(n) keys per user 2
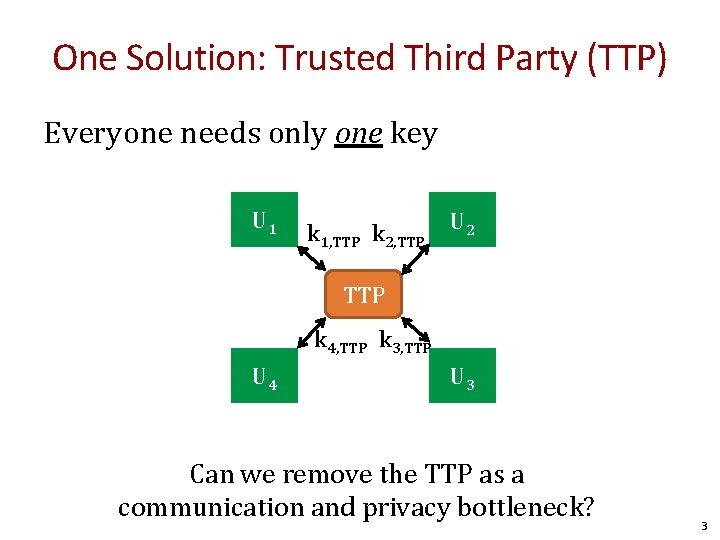
One Solution: Trusted Third Party (TTP) Everyone needs only one key U 1 k 1, TTP k 2, TTP U 2 TTP k 4, TTP k 3, TTP U 4 U 3 Can we remove the TTP as a communication and privacy bottleneck? 3
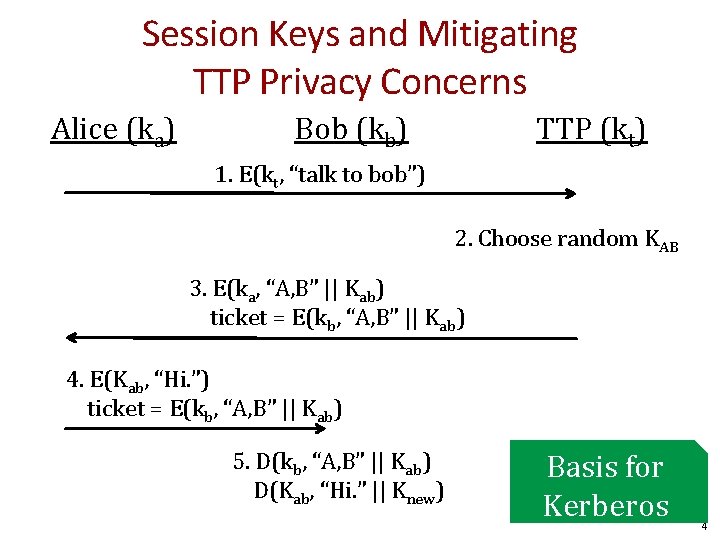
Session Keys and Mitigating TTP Privacy Concerns Alice (ka) Bob (kb) TTP (kt) 1. E(kt, “talk to bob”) 2. Choose random KAB 3. E(ka, “A, B” || Kab) ticket = E(kb, “A, B” || Kab) 4. E(Kab, “Hi. ”) ticket = E(kb, “A, B” || Kab) 5. D(kb, “A, B” || Kab) D(Kab, “Hi. ” || Knew) Basis for Kerberos 4
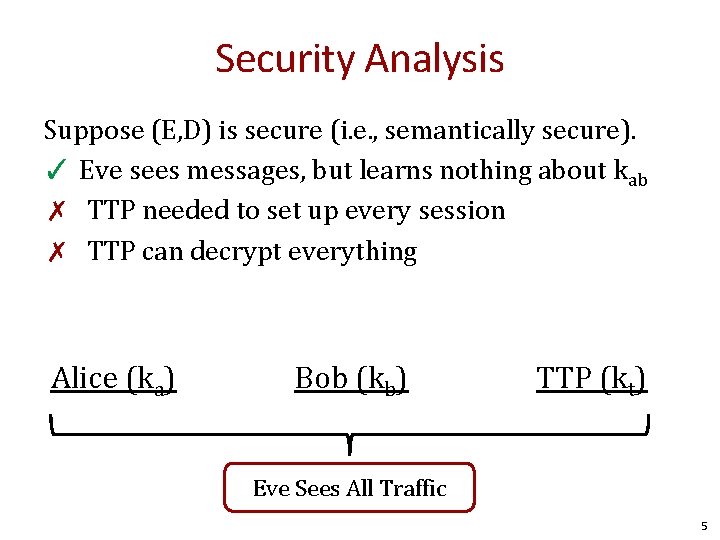
Security Analysis Suppose (E, D) is secure (i. e. , semantically secure). ✓ Eve sees messages, but learns nothing about kab ✗ TTP needed to set up every session ✗ TTP can decrypt everything Alice (ka) Bob (kb) TTP (kt) Eve Sees All Traffic 5
Key question Can we generate shared keys without an online trusted 3 rd party? Answer: yes! Starting point of public-key cryptography: • Merkle (1974), Diffie-Hellman (1976), RSA (1977) • More recently: ID-based enc. (BF 2001), Functional enc. (BSW 2011) 6
The Diffie-Hellman Protocol Whitfield Diffie Martin Hellman 7
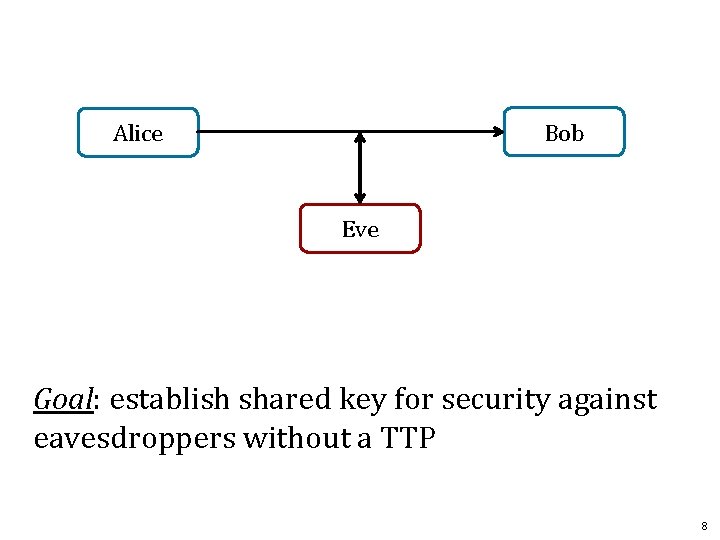
Bob Alice Eve Goal: establish shared key for security against eavesdroppers without a TTP 8
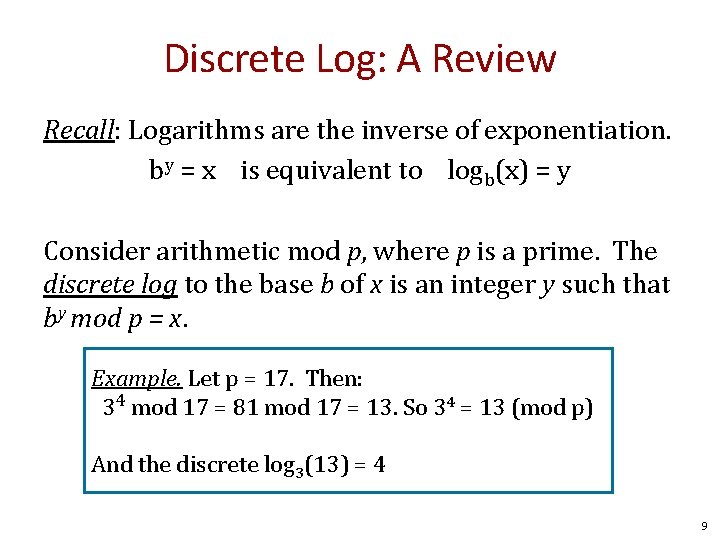
Discrete Log: A Review Recall: Logarithms are the inverse of exponentiation. by = x is equivalent to logb(x) = y Consider arithmetic mod p, where p is a prime. The discrete log to the base b of x is an integer y such that by mod p = x. Example. Let p = 17. Then: 34 mod 17 = 81 mod 17 = 13. So 34 = 13 (mod p) And the discrete log 3(13) = 4 9
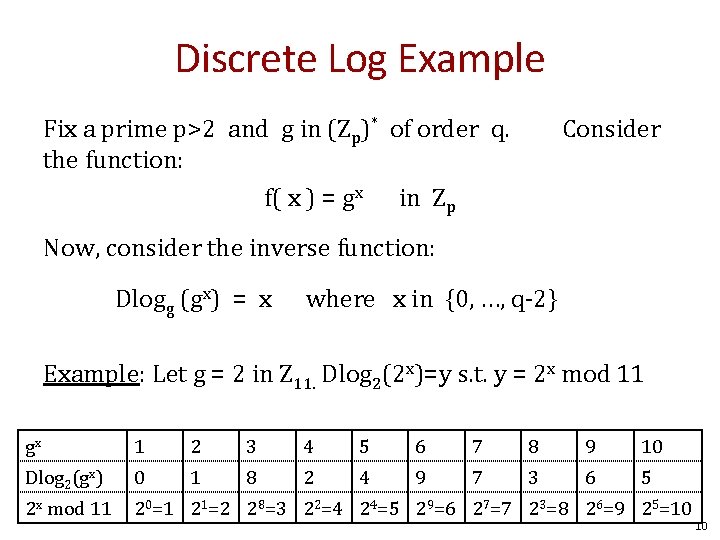
Discrete Log Example Fix a prime p>2 and g in (Zp)* of order q. the function: f( x ) = gx in Zp Consider Now, consider the inverse function: Dlogg (gx) = x where x in {0, …, q-2} Example: Let g = 2 in Z 11. Dlog 2(2 x)=y s. t. y = 2 x mod 11 gx 1 2 3 4 5 6 7 8 9 10 Dlog 2(gx) 0 1 8 2 4 9 7 3 6 5 2 x mod 11 20=1 21=2 28=3 22=4 24=5 29=6 27=7 23=8 26=9 25=10 10
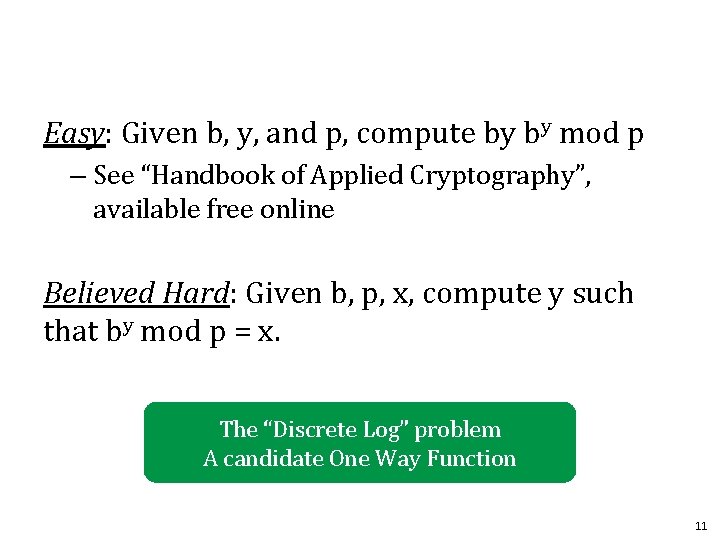
Easy: Given b, y, and p, compute by by mod p – See “Handbook of Applied Cryptography”, available free online Believed Hard: Given b, p, x, compute y such that by mod p = x. The “Discrete Log” problem A candidate One Way Function 11
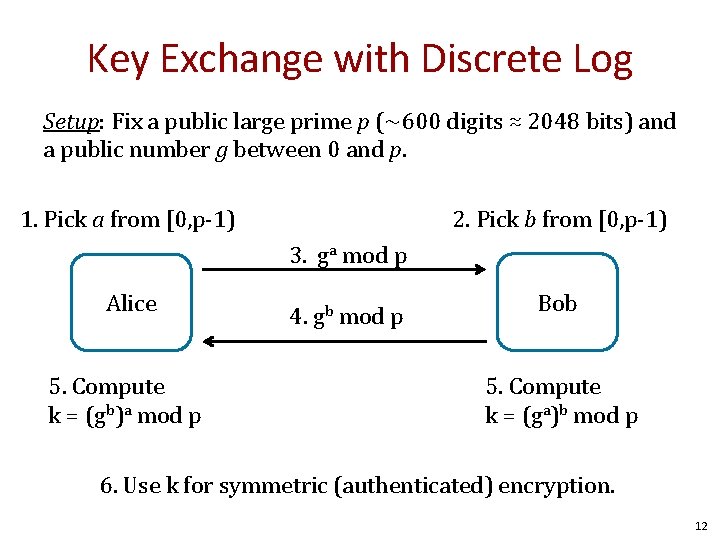
Key Exchange with Discrete Log Setup: Fix a public large prime p (~600 digits ≈ 2048 bits) and a public number g between 0 and p. 1. Pick a from [0, p-1) 2. Pick b from [0, p-1) 3. ga mod p Alice 5. Compute k = (gb)a mod p 4. gb mod p Bob 5. Compute k = (ga)b mod p 6. Use k for symmetric (authenticated) encryption. 12
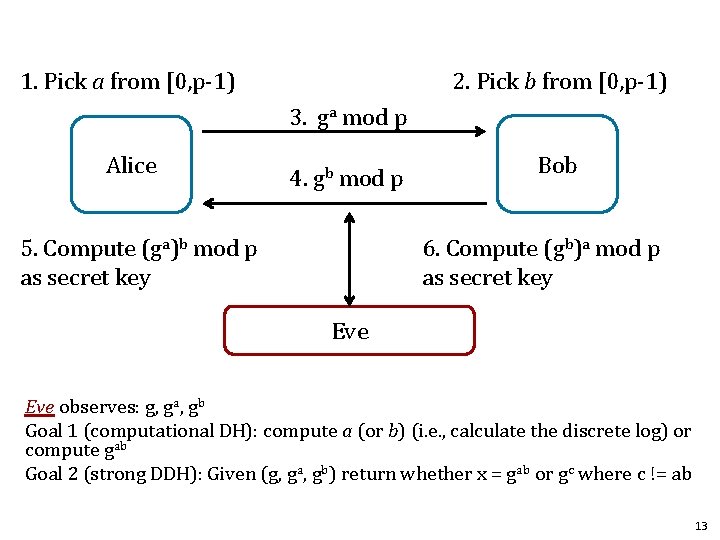
1. Pick a from [0, p-1) 2. Pick b from [0, p-1) 3. ga mod p Alice 4. gb mod p 5. Compute (ga)b mod p as secret key Bob 6. Compute (gb)a mod p as secret key Eve observes: g, ga, gb Goal 1 (computational DH): compute a (or b) (i. e. , calculate the discrete log) or compute gab Goal 2 (strong DDH): Given (g, ga, gb) return whether x = gab or gc where c != ab 13
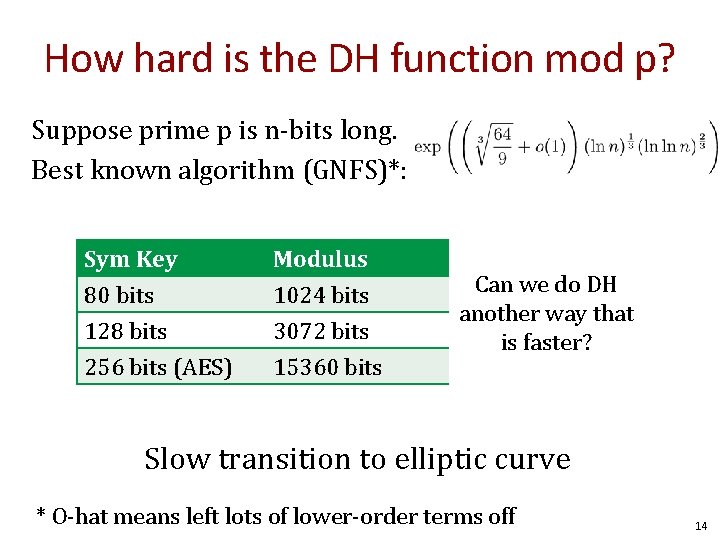
How hard is the DH function mod p? Suppose prime p is n-bits long. Best known algorithm (GNFS)*: Sym Key 80 bits 128 bits 256 bits (AES) Modulus 1024 bits 3072 bits 15360 bits Elliptic Curve Canbits we do DH 160 another way that 256 isbits faster? 512 bits Slow transition to elliptic curve * O-hat means left lots of lower-order terms off 14
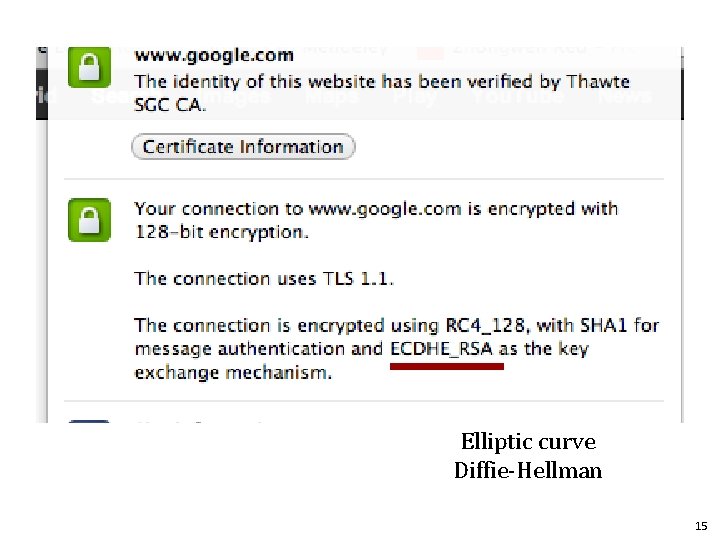
Elliptic curve Diffie-Hellman 15
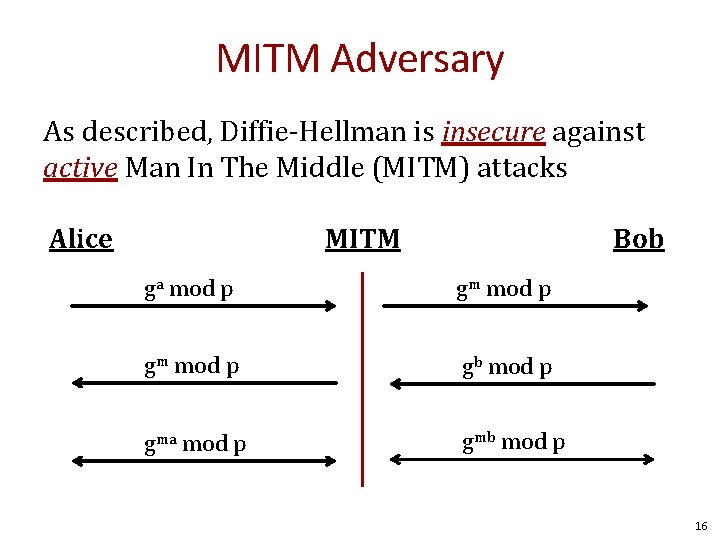
MITM Adversary As described, Diffie-Hellman is insecure against active Man In The Middle (MITM) attacks Alice MITM Bob ga mod p gm mod p gb mod p gma mod p gmb mod p 16
Public Key Encryption 17
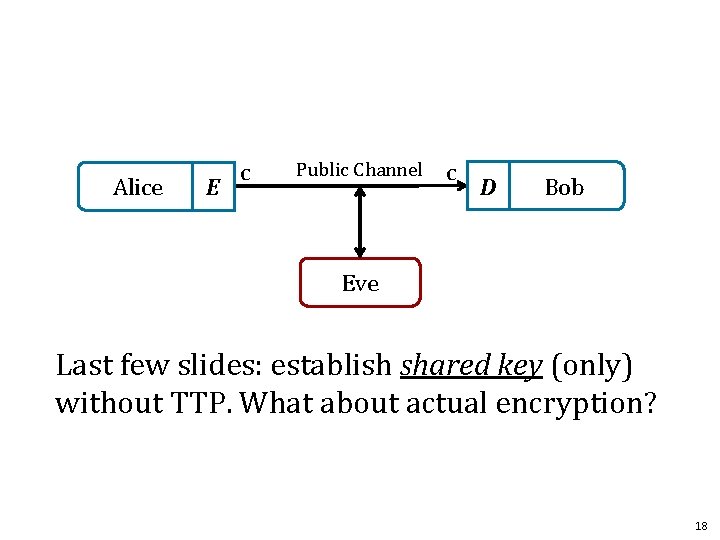
Alice E c Public Channel c D Bob Eve Last few slides: establish shared key (only) without TTP. What about actual encryption? 18
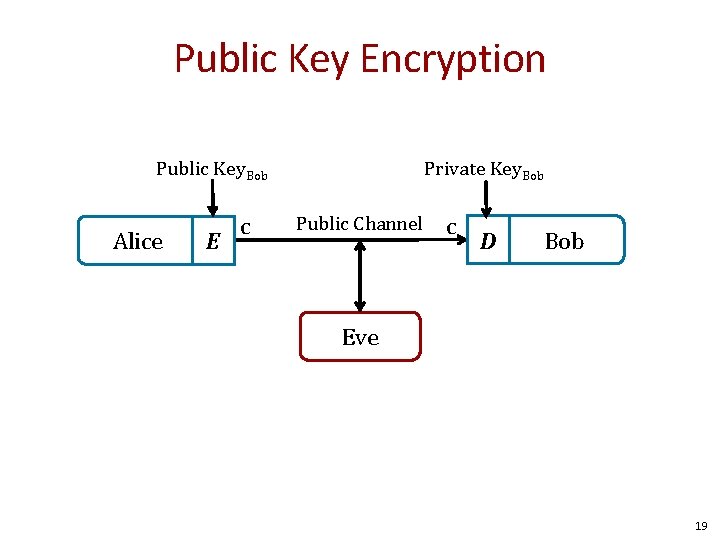
Public Key Encryption Public Key. Bob Alice E c Private Key. Bob Public Channel c D Bob Eve 19
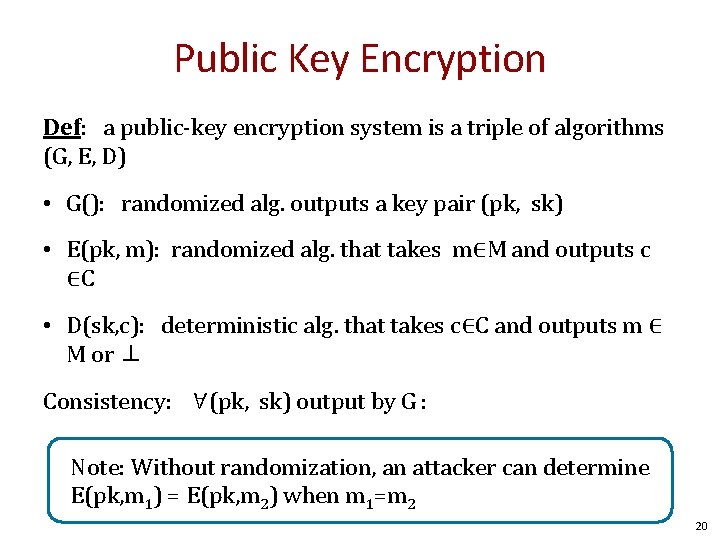
Public Key Encryption Def: a public-key encryption system is a triple of algorithms (G, E, D) • G(): randomized alg. outputs a key pair (pk, sk) • E(pk, m): randomized alg. that takes m∈M and outputs c ∈C • D(sk, c): deterministic alg. that takes c∈C and outputs m ∈ M or ⊥ Consistency: ∀(pk, sk) output by G : ∀m∈M: D(sk, E(pk, m) ) = m Note: Without randomization, an attacker can determine E(pk, m 1) = E(pk, m 2) when m 1=m 2 20
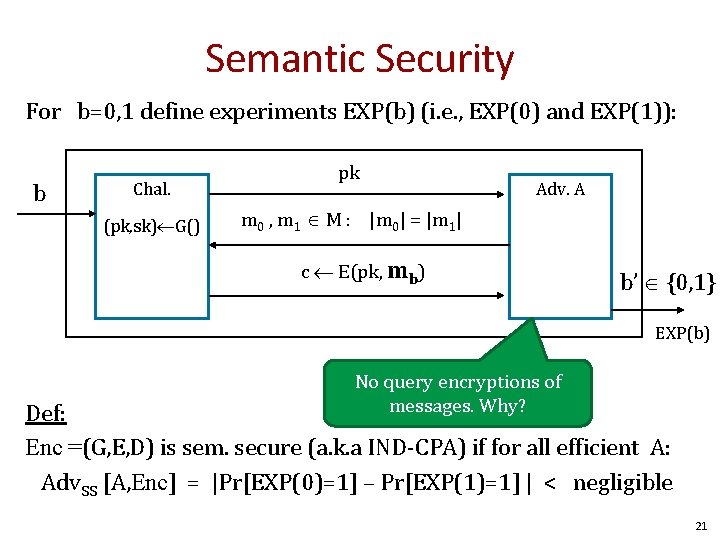
Semantic Security For b=0, 1 define experiments EXP(b) (i. e. , EXP(0) and EXP(1)): b Chal. (pk, sk) G() pk Adv. A m 0 , m 1 M : |m 0| = |m 1| c E(pk, mb) b’ {0, 1} EXP(b) No query encryptions of messages. Why? Def: Enc =(G, E, D) is sem. secure (a. k. a IND-CPA) if for all efficient A: Adv. SS [A, Enc] = |Pr[EXP(0)=1] – Pr[EXP(1)=1] | < negligible 21
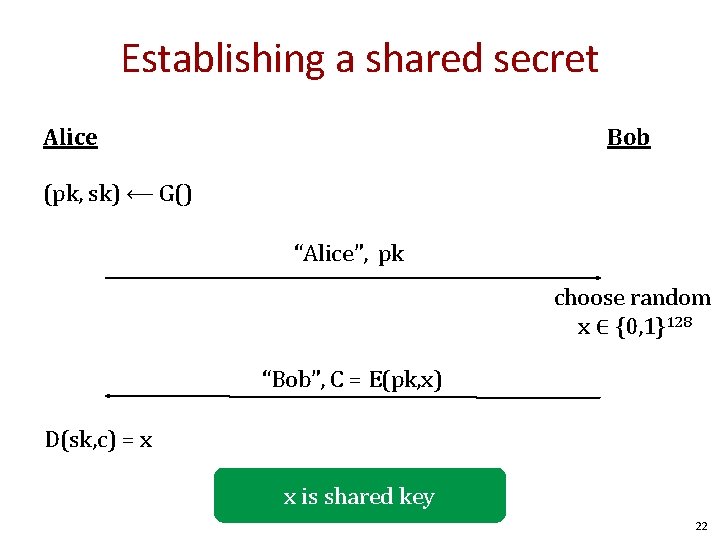
Establishing a shared secret Alice Bob (pk, sk) ⟵ G() “Alice”, pk choose random x ∈ {0, 1}128 “Bob”, C = E(pk, x) D(sk, c) = x x is shared key 22
Security (eavesdropping) Adversary sees pk, E(pk, x) and wants x ∈M Semantic security means the adversary cannot distinguish { pk, E(pk, x), x } from { pk, E(pk, x), rand∈M } Note: protocol is also vulnerable to MITM attack 23
Public key encryption: constructions Constructions generally rely on hard problems from number theory and algebra 24
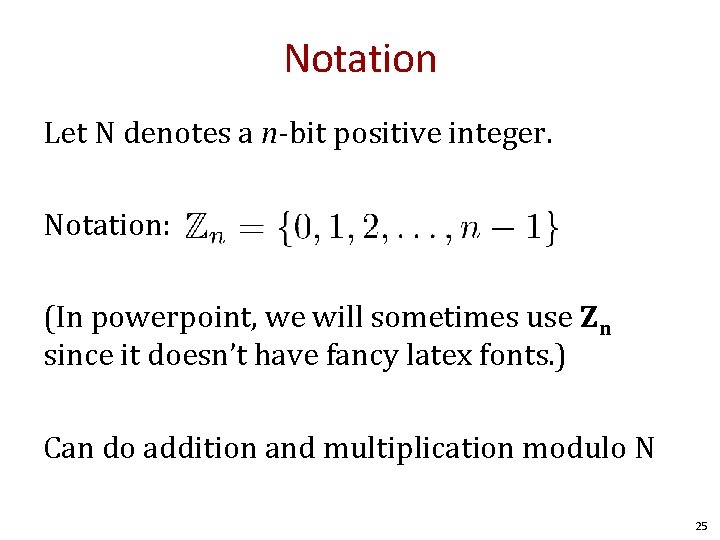
Notation Let N denotes a n-bit positive integer. Notation: (In powerpoint, we will sometimes use Zn since it doesn’t have fancy latex fonts. ) Can do addition and multiplication modulo N 25
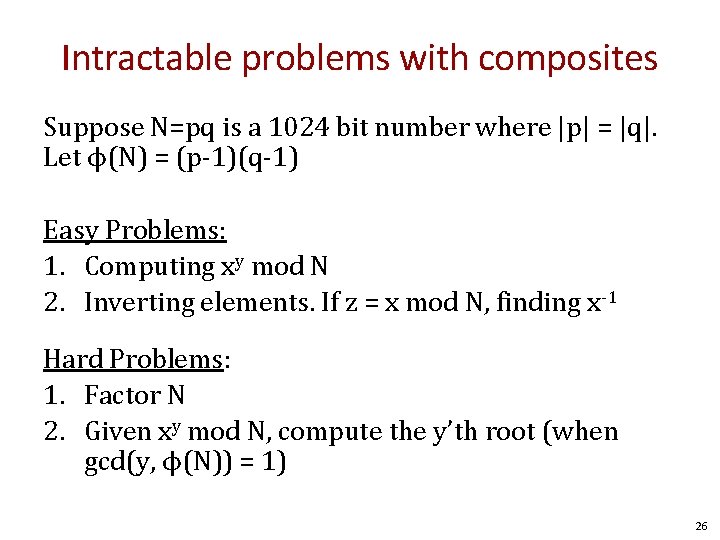
Intractable problems with composites Suppose N=pq is a 1024 bit number where |p| = |q|. Let ϕ(N) = (p-1)(q-1) Easy Problems: 1. Computing xy mod N 2. Inverting elements. If z = x mod N, finding x-1 Hard Problems: 1. Factor N 2. Given xy mod N, compute the y’th root (when gcd(y, ϕ(N)) = 1) 26
The factoring problem Gauss (1805): “The problem of distinguishing prime numbers from composite numbers and of resolving the latter into their prime factors is known to be one of the most important and useful in arithmetic. ” Current world record: RSA-768 (232 digits) • Work: two years on hundreds of machines • Factoring a 1024 -bit integer: about 1000 times harder ⇒ likely possible this decade 27
RSA and Trapdoors 28
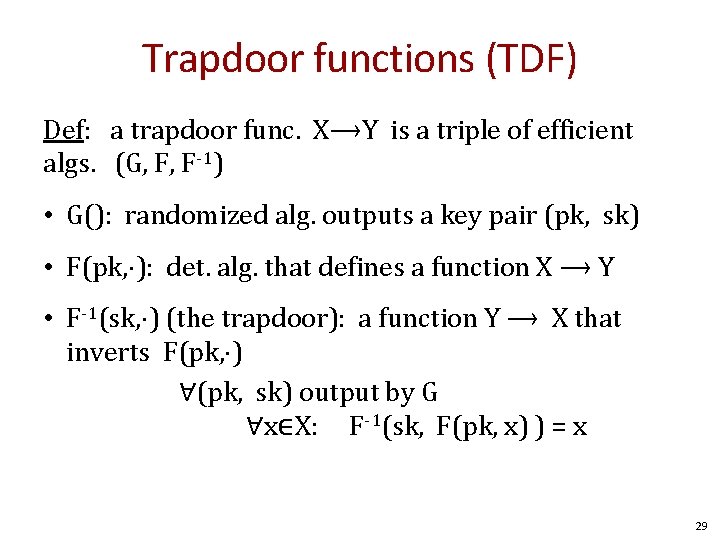
Trapdoor functions (TDF) Def: a trapdoor func. X⟶Y is a triple of efficient algs. (G, F, F-1) • G(): randomized alg. outputs a key pair (pk, sk) • F(pk, ⋅): det. alg. that defines a function X ⟶ Y • F-1(sk, ⋅) (the trapdoor): a function Y ⟶ X that inverts F(pk, ⋅) ∀(pk, sk) output by G ∀x∈X: F-1(sk, F(pk, x) ) = x 29
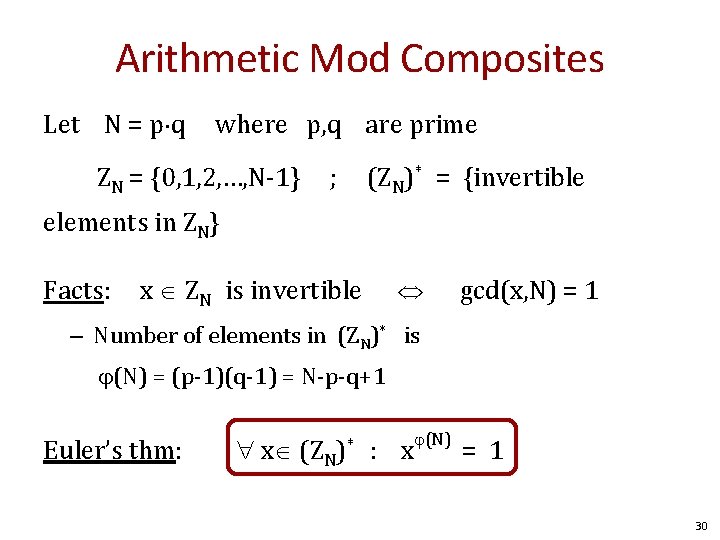
Arithmetic Mod Composites Let N = p q where p, q are prime ZN = {0, 1, 2, …, N-1} ; (ZN)* = {invertible elements in ZN} Facts: x ZN is invertible gcd(x, N) = 1 – Number of elements in (ZN)* is (N) = (p-1)(q-1) = N-p-q+1 Euler’s thm: x (ZN)* : x (N) = 1 30
The RSA trapdoor permutation First published in Scientific American, Aug. 1977 Very widely used: – SSL/TLS: certificates and key-exchange – Secure e-mail and file systems … many others 31
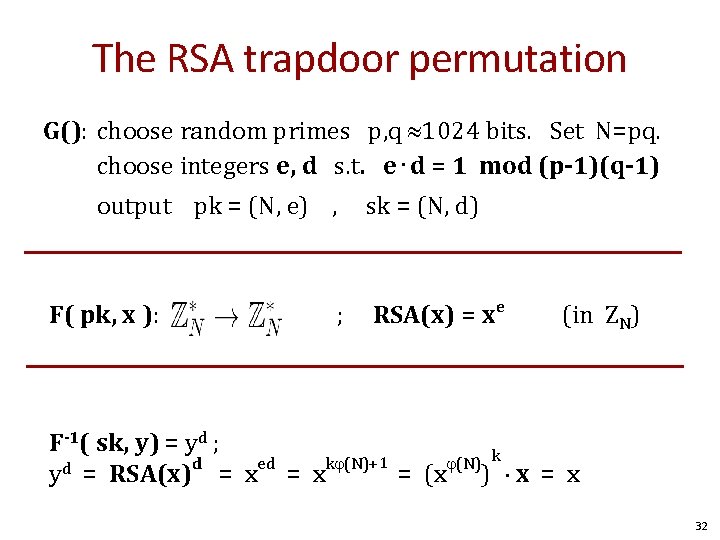
The RSA trapdoor permutation G(): choose random primes p, q 1024 bits. Set N=pq. choose integers e, d s. t. e⋅d = 1 mod (p-1)(q-1) output pk = (N, e) , F( pk, x ): ; sk = (N, d) RSA(x) = xe (in ZN) F-1( sk, y) = yd ; d ed k (N)+1 (N) k d y = RSA(x) = x = (x ) x = x 32
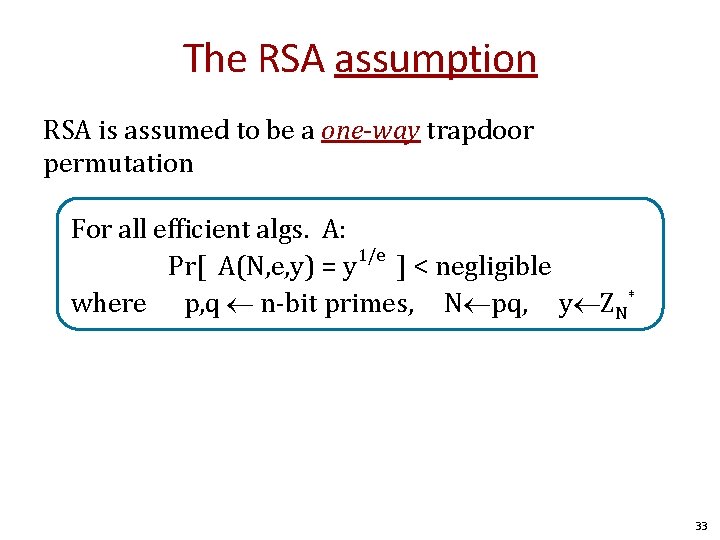
The RSA assumption RSA is assumed to be a one-way trapdoor permutation For all efficient algs. A: Pr[ A(N, e, y) = y 1/e ] < negligible where p, q n-bit primes, N pq, y ZN* 33
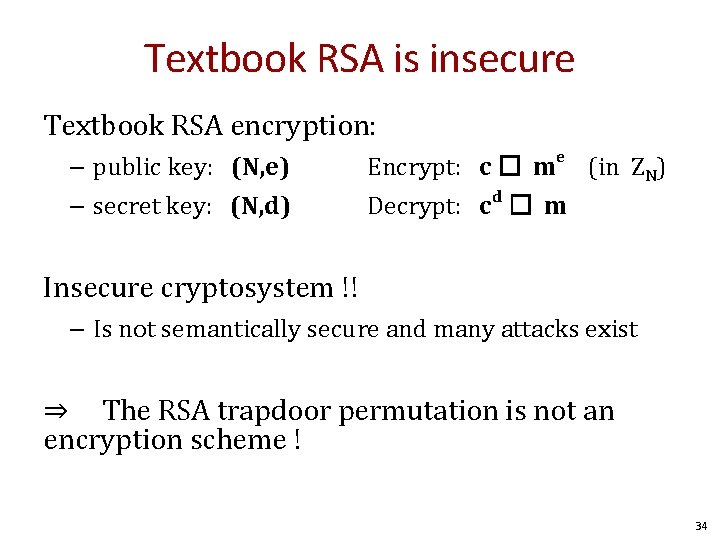
Textbook RSA is insecure Textbook RSA encryption: – public key: (N, e) – secret key: (N, d) Encrypt: c � me (in ZN) Decrypt: cd � m Insecure cryptosystem !! – Is not semantically secure and many attacks exist ⇒ The RSA trapdoor permutation is not an encryption scheme ! 34
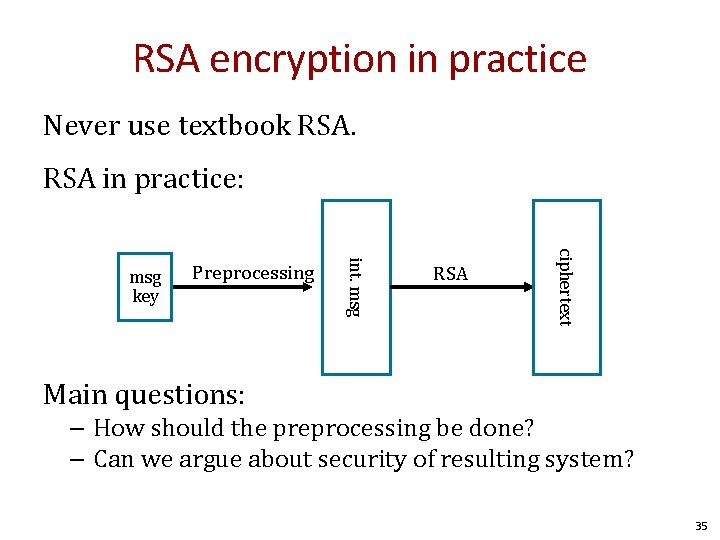
RSA encryption in practice Never use textbook RSA in practice: RSA ciphertext Preprocessing int. msg key Main questions: – How should the preprocessing be done? – Can we argue about security of resulting system? 35
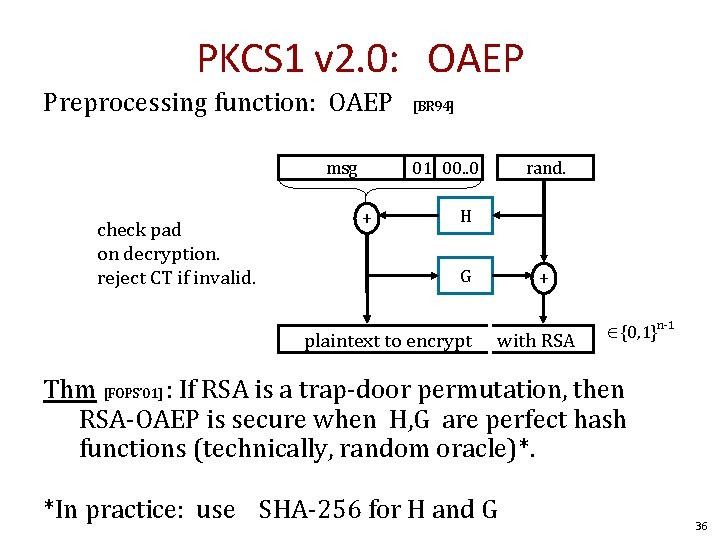
PKCS 1 v 2. 0: OAEP Preprocessing function: OAEP msg check pad on decryption. reject CT if invalid. [BR 94] 01 00. . 0 + rand. H G plaintext to encrypt + with RSA {0, 1}n-1 Thm [FOPS’ 01] : If RSA is a trap-door permutation, then RSA-OAEP is secure when H, G are perfect hash functions (technically, random oracle)*. *In practice: use SHA-256 for H and G 36
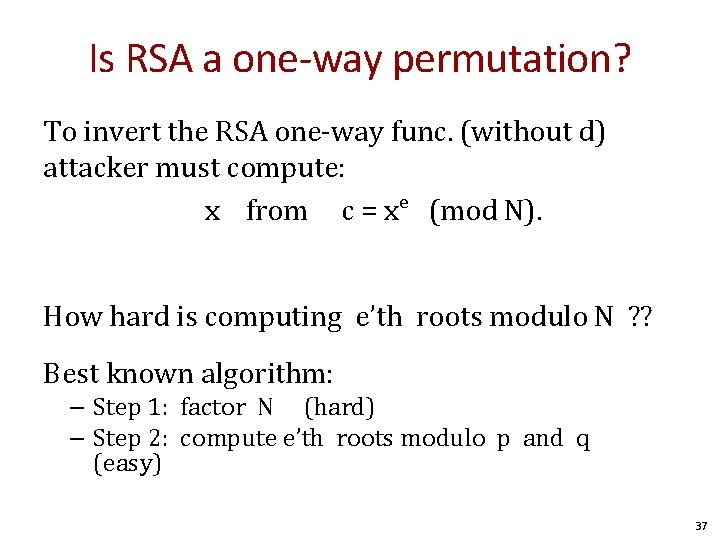
Is RSA a one-way permutation? To invert the RSA one-way func. (without d) attacker must compute: x from c = xe (mod N). How hard is computing e’th roots modulo N ? ? Best known algorithm: – Step 1: factor N (hard) – Step 2: compute e’th roots modulo p and q (easy) 37
38
![Implementation attacks Timing attack: [Kocher et al. 1997], [BB’ 04] The time it takes Implementation attacks Timing attack: [Kocher et al. 1997], [BB’ 04] The time it takes](http://slidetodoc.com/presentation_image_h/2076103c2539709f56f98f69a7953b1d/image-39.jpg)
Implementation attacks Timing attack: [Kocher et al. 1997], [BB’ 04] The time it takes to compute cd (mod N) can expose d. Power attack: [Kocher et al. 1999] The power consumption of a smartcard while it is computing cd (mod N) can expose d. Faults attack: [BDL’ 97] d A computer error during c (mod N) can expose d. (common defense: check output with 10% slowdown) 39
Extra slides if time 40
![RSA Key Generation Trouble [Heninger et al. /Lenstra et al. ] Open. SSL RSA RSA Key Generation Trouble [Heninger et al. /Lenstra et al. ] Open. SSL RSA](http://slidetodoc.com/presentation_image_h/2076103c2539709f56f98f69a7953b1d/image-41.jpg)
RSA Key Generation Trouble [Heninger et al. /Lenstra et al. ] Open. SSL RSA key generation (abstract): prng. seed(seed) p = prng. generate_random_prime() prng. add_randomness(bits) q = prng. generate_random_prime() N = p*q Suppose poor entropy at startup: • Same p will be generated by multiple devices, but different q • N 1 , N 2 : RSA keys from different devices ⇒ gcd(N 1, N 2) = p 41
![RSA Key Generation Trouble [Heninger et al. /Lenstra et al. ] Experiment: factors 0. RSA Key Generation Trouble [Heninger et al. /Lenstra et al. ] Experiment: factors 0.](http://slidetodoc.com/presentation_image_h/2076103c2539709f56f98f69a7953b1d/image-42.jpg)
RSA Key Generation Trouble [Heninger et al. /Lenstra et al. ] Experiment: factors 0. 4% of public HTTPS keys! Lesson: Make sure random number generator is properly seeded when generating keys 42

Questions? 43
END
Number Theory Primer 45
Background We will use a bit of number theory to construct: – Key exchange protocols – Digital signatures – Public-key encryption More info: http: //shoup. net/ntb-v 2. pdf http: //cseweb. ucsd. edu/~mihir/cse 107/ and other places across the web. 46
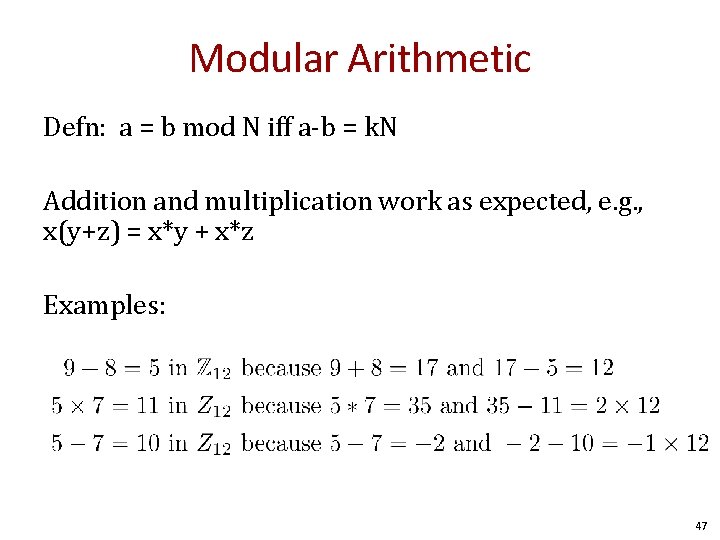
Modular Arithmetic Defn: a = b mod N iff a-b = k. N Addition and multiplication work as expected, e. g. , x(y+z) = x*y + x*z Examples: 47
Greatest Common Divisor Def: for integers x, y, gcd(x, y) is the greatest common divisor of x and y. Fact: for all integers x, y there exists integers a, b such that: a*x +b*y = gcd(x, y) and a, b can be found efficiently with the extended Euclidian algorithm Example: gcd(12, 18) = 6 2*12 + (-1)*18 = 6 Def: If gcd(x, y) = 1, then we say x and y are relative primes. 48
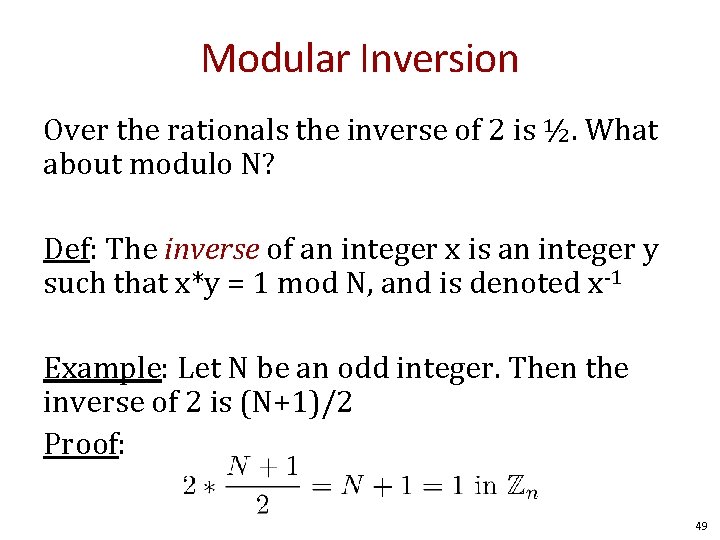
Modular Inversion Over the rationals the inverse of 2 is ½. What about modulo N? Def: The inverse of an integer x is an integer y such that x*y = 1 mod N, and is denoted x-1 Example: Let N be an odd integer. Then the inverse of 2 is (N+1)/2 Proof: 49
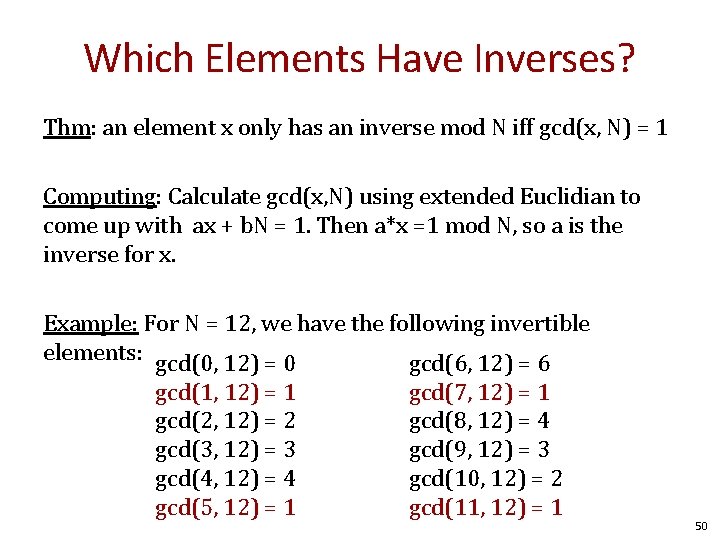
Which Elements Have Inverses? Thm: an element x only has an inverse mod N iff gcd(x, N) = 1 Computing: Calculate gcd(x, N) using extended Euclidian to come up with ax + b. N = 1. Then a*x =1 mod N, so a is the inverse for x. Example: For N = 12, we have the following invertible elements: gcd(0, 12) = 0 gcd(6, 12) = 6 gcd(1, 12) = 1 gcd(2, 12) = 2 gcd(3, 12) = 3 gcd(4, 12) = 4 gcd(5, 12) = 1 gcd(7, 12) = 1 gcd(8, 12) = 4 gcd(9, 12) = 3 gcd(10, 12) = 2 gcd(11, 12) = 1 50
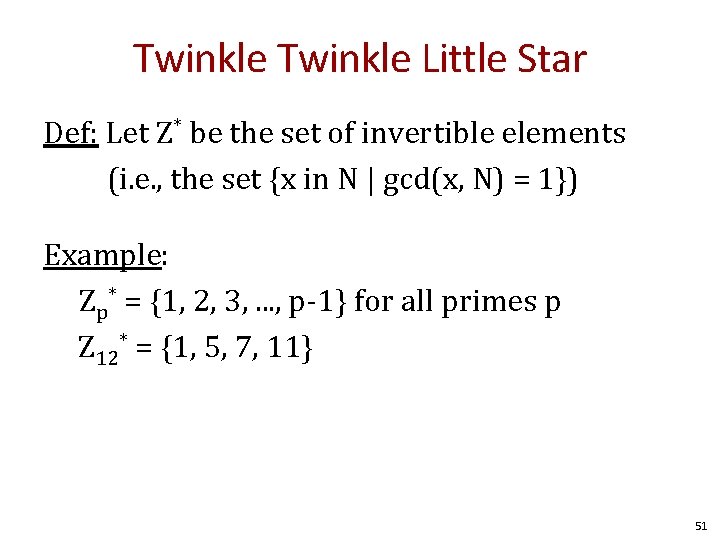
Twinkle Little Star Def: Let Z* be the set of invertible elements (i. e. , the set {x in N | gcd(x, N) = 1}) Example: Zp* = {1, 2, 3, . . . , p-1} for all primes p Z 12* = {1, 5, 7, 11} 51
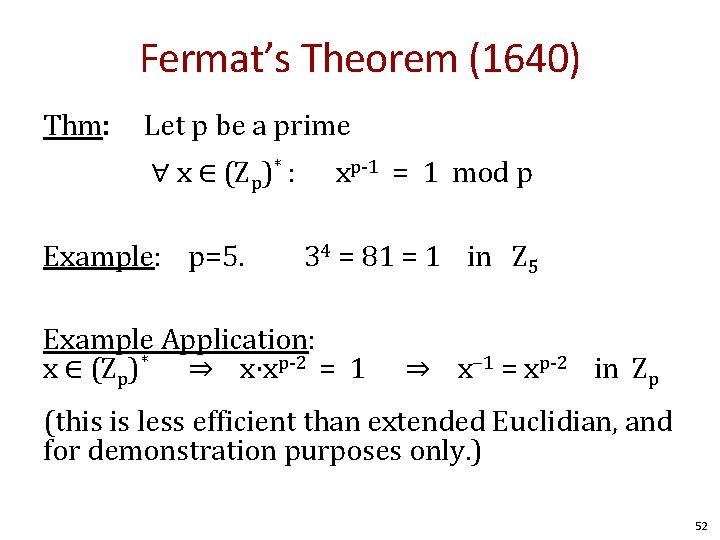
Fermat’s Theorem (1640) Thm: Let p be a prime ∀ x ∈ (Zp)* : Example: p=5. xp-1 = 1 mod p 34 = 81 = 1 in Z 5 Example Application: x ∈ (Zp)* ⇒ x⋅xp-2 = 1 ⇒ x− 1 = xp-2 in Zp (this is less efficient than extended Euclidian, and for demonstration purposes only. ) 52
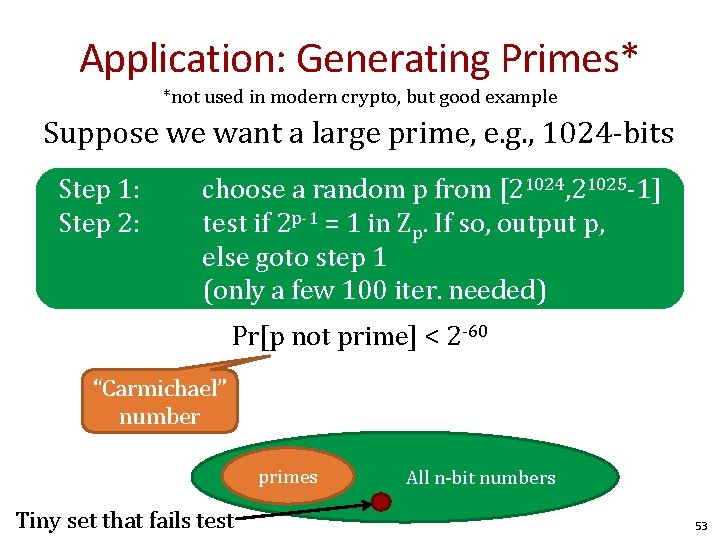
Application: Generating Primes* *not used in modern crypto, but good example Suppose we want a large prime, e. g. , 1024 -bits Step 1: Step 2: choose a random p from [21024, 21025 -1] test if 2 p-1 = 1 in Zp. If so, output p, else goto step 1 (only a few 100 iter. needed) Pr[p not prime] < 2 -60 “Carmichael” number primes Tiny set that fails test All n-bit numbers 53
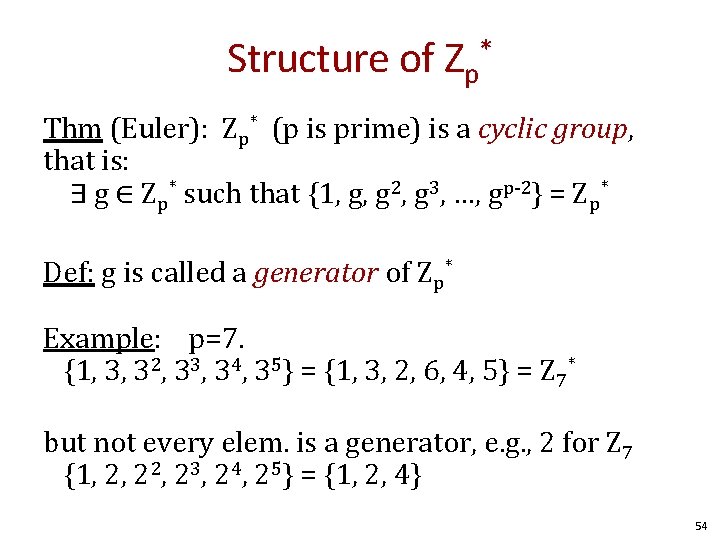
Structure of Zp* Thm (Euler): Zp* (p is prime) is a cyclic group, that is: ∃ g ∈ Zp* such that {1, g, g 2, g 3, …, gp-2} = Zp* Def: g is called a generator of Zp* Example: p=7. {1, 3, 32, 33, 34, 35} = {1, 3, 2, 6, 4, 5} = Z 7* but not every elem. is a generator, e. g. , 2 for Z 7 {1, 2, 23, 24, 25} = {1, 2, 4} 54
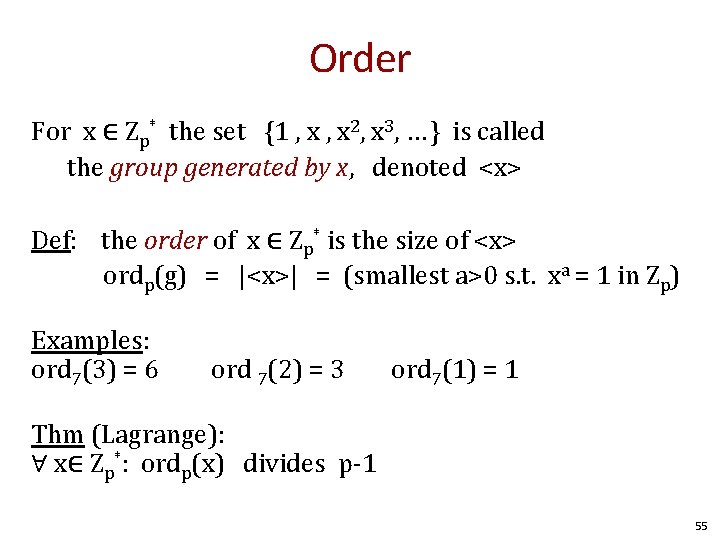
Order For x ∈ Zp* the set {1 , x 2, x 3, … } is called the group generated by x, denoted <x> Def: the order of x ∈ Zp* is the size of <x> ordp(g) = |<x>| = (smallest a>0 s. t. xa = 1 in Zp) Examples: ord 7(3) = 6 ord 7(2) = 3 ord 7(1) = 1 Thm (Lagrange): ∀ x∈ Zp*: ordp(x) divides p-1 55
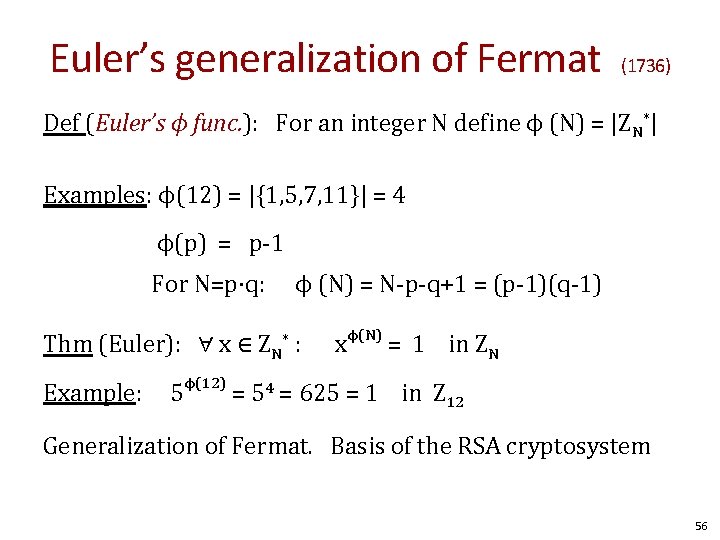
Euler’s generalization of Fermat (1736) Def (Euler’s ϕ func. ): For an integer N define ϕ (N) = |ZN*| Examples: ϕ(12) = |{1, 5, 7, 11}| = 4 ϕ(p) = p-1 For N=p⋅q: ϕ (N) = N-p-q+1 = (p-1)(q-1) Thm (Euler): ∀ x ∈ ZN : * Example: x ϕ(N) = 1 in ZN 5ϕ(12) = 54 = 625 = 1 in Z 12 Generalization of Fermat. Basis of the RSA cryptosystem 56
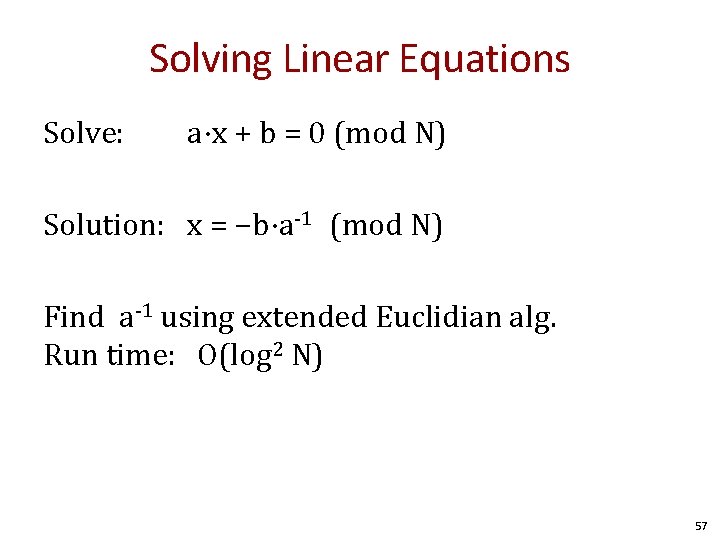
Solving Linear Equations Solve: a⋅x + b = 0 (mod N) Solution: x = −b⋅a-1 (mod N) Find a-1 using extended Euclidian alg. Run time: O(log 2 N) 57
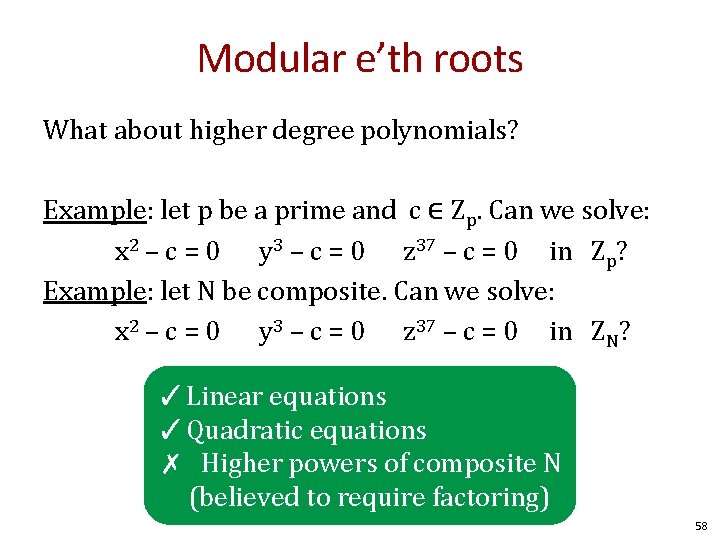
Modular e’th roots What about higher degree polynomials? Example: let p be a prime and c ∈ Zp. Can we solve: x 2 – c = 0 y 3 – c = 0 z 37 – c = 0 in Zp? Example: let N be composite. Can we solve: x 2 – c = 0 y 3 – c = 0 z 37 – c = 0 in ZN? ✓Linear equations ✓Quadratic equations ✗ Higher powers of composite N (believed to require factoring) 58
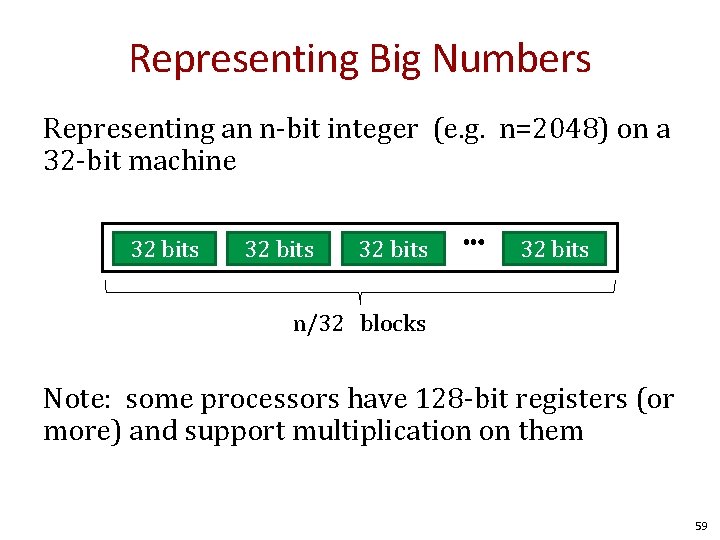
Representing Big Numbers Representing an n-bit integer (e. g. n=2048) on a 32 -bit machine 32 bits ⋯ 32 bits n/32 blocks Note: some processors have 128 -bit registers (or more) and support multiplication on them 59
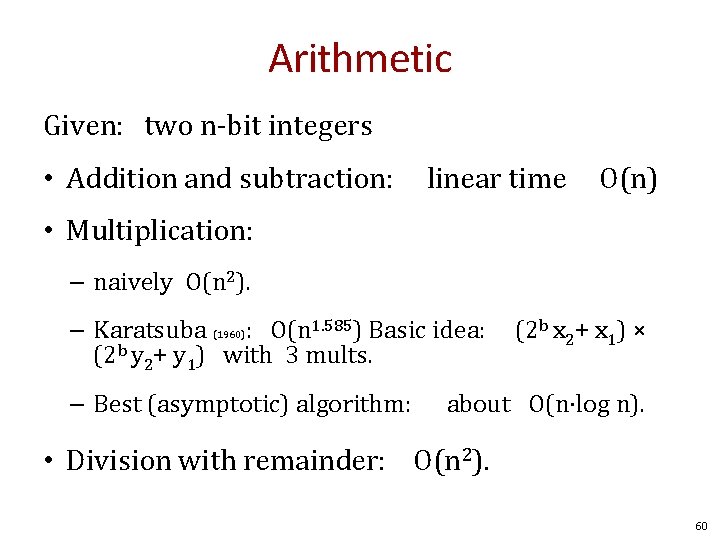
Arithmetic Given: two n-bit integers • Addition and subtraction: linear time O(n) • Multiplication: – naively O(n 2). – Karatsuba (1960): O(n 1. 585) Basic idea: (2 b y 2+ y 1) with 3 mults. – Best (asymptotic) algorithm: (2 b x 2+ x 1) × about O(n⋅log n). • Division with remainder: O(n 2). 60
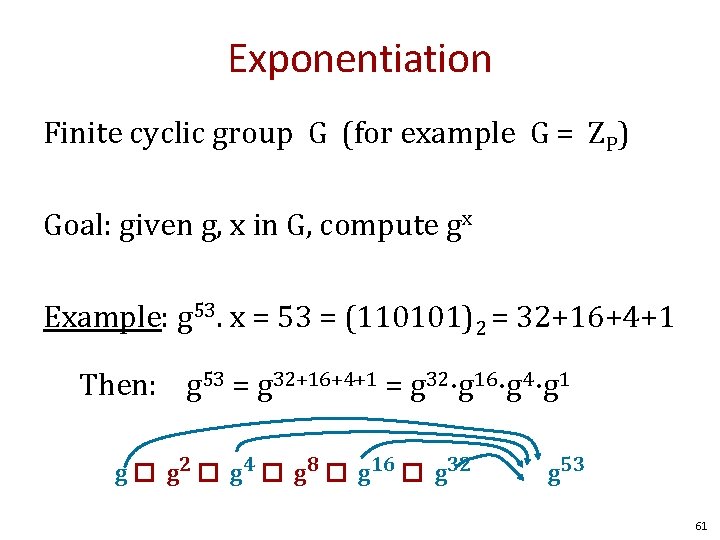
Exponentiation Finite cyclic group G (for example G = ZP) Goal: given g, x in G, compute gx Example: g 53. x = 53 = (110101)2 = 32+16+4+1 Then: g 53 = g 32+16+4+1 = g 32⋅g 16⋅g 4⋅g 1 g � g 2 � g 4 � g 8 � g 16 � g 32 g 53 61
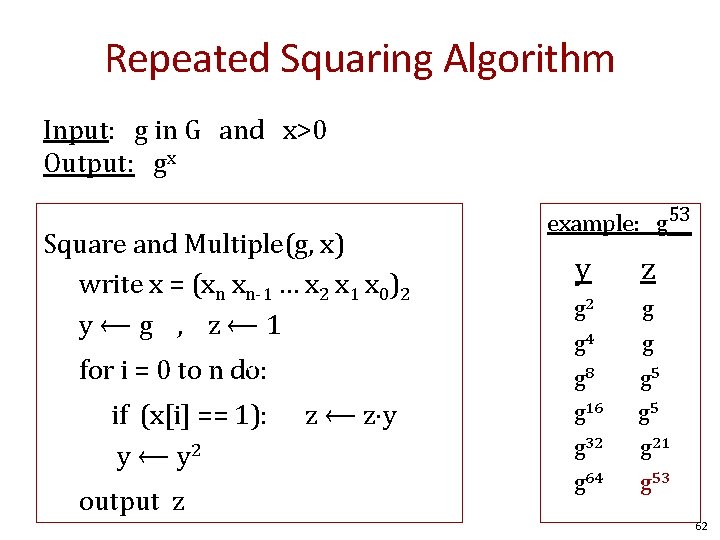
Repeated Squaring Algorithm Input: g in G and x>0 Output: gx Square and Multiple(g, x) write x = (xn xn-1 … x 2 x 1 x 0)2 y⟵g , z⟵ 1 d for i = 0 to n do: if (x[i] == 1): y ⟵ y 2 output z z ⟵ z⋅y example: g 53 y z g 2 g 4 g 8 g 16 g 32 g 64 g g g 5 g 21 g 53 62
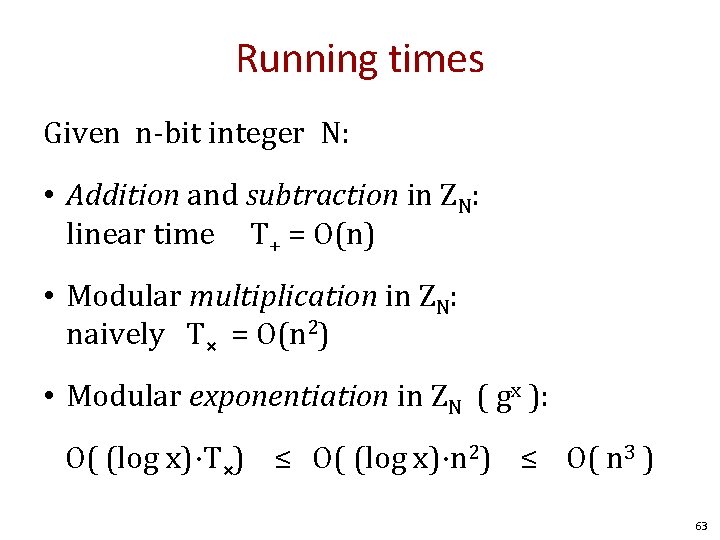
Running times Given n-bit integer N: • Addition and subtraction in ZN: linear time T+ = O(n) • Modular multiplication in ZN: naively T× = O(n 2) • Modular exponentiation in ZN ( gx ): O( (log x)⋅T×) ≤ O( (log x)⋅n 2) ≤ O( n 3 ) 63
Easy and Hard Problems 64
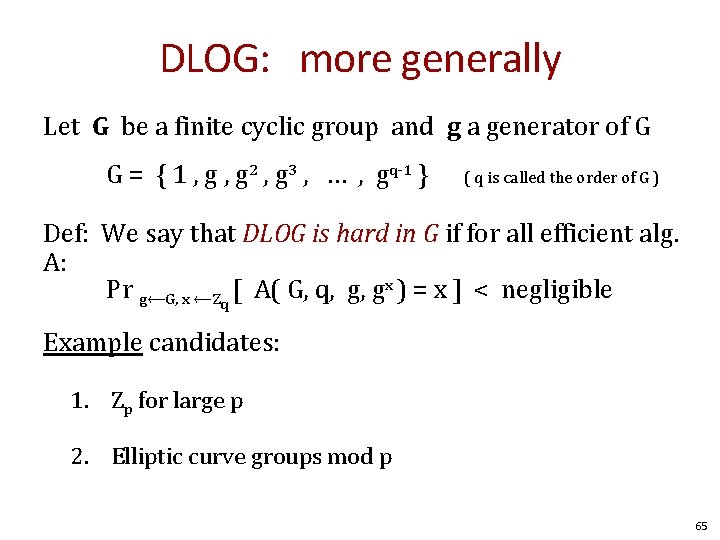
DLOG: more generally Let G be a finite cyclic group and g a generator of G G = { 1 , g 2 , g 3 , … , gq-1 } ( q is called the order of G ) Def: We say that DLOG is hard in G if for all efficient alg. A: Pr g⟵G, x ⟵Zq [ A( G, q, g, gx ) = x ] < negligible Example candidates: 1. Zp for large p 2. Elliptic curve groups mod p 65
Easy problem Given composite N=pq, where p and q are large primes, and x in ZN find x-1 in ZN 66
- Slides: 66